689,272 plaintext records of Amex India customers exposed online
9.11.18 securityaffairs Hacking Incindent
Records associated with 689,272 plaintext records Amex India customers were exposed online via unsecured MongoDB server.
Personal details of nearly 700,000 American Express (Amex India) India customers were exposed online via an unsecured MongoDB server.
The huge trove of data was discovered by Bob Diachenko from cybersecurity firm Hacken, most of the records were encrypted, but 689,272 records were stored in plaintext.
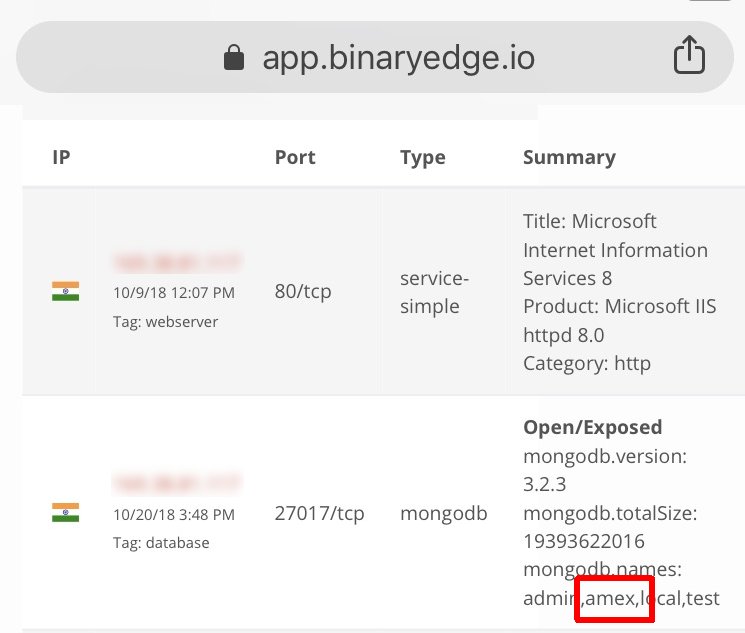
The expert located the database by using IoT search engines such as Shodan and BinaryEdge.io.
“On 23rd October I discovered an unprotected Mongo DB which allowed millions of records to be viewed, edited and accessed by anybody who might have discovered this vulnerability. The records appeared to be from an American Express branch in India.” states the blog post published by Diachenko.
AMEX records american express
689,272 plaintext records included personal details of Amex India customers’ phone numbers, names, email addresses, and ‘type of card’ description fields.
The archive included 2,332,115 records containing encrypted data (i.e. names, addresses, Aadhaar numbers, PAN card numbers, and phone numbers.
Bob Diachenko
@MayhemDayOne
Seems like @AmexIndia exposed its #MongoDB for a while, with some really sensitive data (base64 encrypted). Now secured (just when I was preparing responsible disclosure), but question remains how long it was open. Found with @binaryedgeio engine.
42
10:12 AM - Oct 25, 18
35 people are talking about this
Twitter Ads info and privacy
“Upon closer examination, I am inclined to believe that the database was not managed by AmEx itself but instead by one their subcontractors who were responsible for SEO or lead generation. I came to this conclusion since many of the entries contained fields such as ‘campaignID’, ‘prequalstatus’ and ‘leadID’ etc.” added Diachenko.
Diachenko promptly reported his findings to Amex India that immediately took down the server. At the time of writing is not clear how much time the server remained exposed online, Amex India that investigated the case declared that it did not discover any “evidence of unauthorized access.”
“We applaud AmEx’s rapid response to this issue, noting they immediately took down that server upon notification and began further investigations.” Diachenko concluded.
“As we learned from this incident, one never knows when transient firewall rules may inadvertently expose your development machines to the public. In this case, it appears to have only exposed some long-lost personal information of an unknown number of AmEx India customers, but for others, it could be critical intellectual property or even your entire subscriber base that is at risk of being exposed.”