DMARC Fully Implemented on Two Thirds of U.S. Government Domains
22.9.2018 securityweek Safety
DMARC has been fully implemented on roughly two thirds of U.S. government domains, but agencies have less than a month to roll out the email security standard on the remaining websites.
The Binding Operational Directive (BOD) 18-01, issued by the DHS in October 2017, instructs all federal agencies to start using web and email security technologies such as HTTPS, STARTTLS, SPF and DMARC.
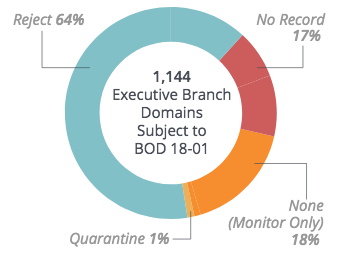
DMARC (Domain-based Message Authentication, Reporting and Conformance) is an email authentication, policy, and reporting protocol designed to detect and prevent email spoofing. Organizations can set the DMARC policy to “none” to only monitor unauthenticated emails, “quarantine” to send them to the spam or junk folder, or “reject” to completely block their delivery.
The DHS has instructed federal agencies to fully implement DMARC (i.e. set their DMARC policy to “reject”) on all .gov domains by October 16, 2018.
Email threat protection company Agari has been monitoring progress and, according to its latest report, as of September 14, DMARC had been fully implemented on 64% of 1,144 domains. DMARC has been rolled out with at least a “none” policy on 83% of domains.
“This is significantly better adoption than the commercial sector, where two-thirds (67%) of the Fortune 500 have not published any DMARC policy,” Agari said in its report.
The government organizations that have implemented a “reject” policy on less than half of their domains include the Consumer Financial Protection Bureau, the Department of Commerce, the Department of Energy, and the Executive Office of the President.
The security firm pointed out that of the 417 executive branch domains that have not implemented a “reject” policy, 89% are actively sending emails, which could hamper compliance efforts.
“With less than one month until the final BOD 18-01 deadline, the U.S. Government has made tremendous strides forward in its DMARC adoption and compliance efforts. Most federal agencies and the citizens they serve are now realizing the benefits of DMARC,” Agari said. “Executive branch agencies such as the Department of Health and Human Services have implemented a ‘p=reject’ policy across hundreds of domains to automatically block phishing email attacks and prevent domain spoofing. Yet hundreds of other federal domains still remain vulnerable to these attacks.”
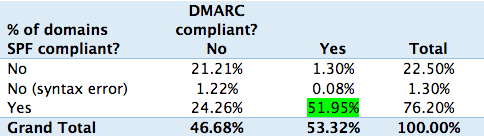
Proofpoint has also recently published a report on DMARC adoption and compliance with BOD 18-01, but the company also took into account the implementation of the Sender Policy Framework (SPF), which along with DomainKeys Identified Mail (DKIM) forms the foundation of DMARC. Proofpoint analyzed the full set of federal civilian domains provided by the federal government, which includes 200 additional domains compared to what Agari has been monitoring.
Data from Proofpoint shows that nearly 52% of all domains have both a valid SPF record and the DMARC policy set to “reject.” However, only 34 of the 133 agencies under the BOD mandate, representing roughly 24%, were fully compliant at the time of the study.