More than 1,700 valid Telnet credentials for IoT devices leaked online
27.8.2017 securityaffairs IoT
Security researchers are warning of the availability online of a list of IoT devices and associated telnet credentials.
The list has been available on Pastebin since June, but last week it was also shared via Twitter by the researcher Ankit Anubhav becoming rapidly viral.
The original list was posted by someone who has previously published a dump of valid log-in credentials and also the source code of a botnet.

Ankit Anubhav @ankit_anubhav
33000+ telnet credentials of IoT devices exposed on pastebin.
Link : https://pastebin.com/p5teudX0 #iot #hacking #malware #infosec @newskysecurity
9:34 PM - Aug 24, 2017
11 11 Replies 436 436 Retweets 422 422 likes
Twitter Ads info and privacy
It is a gift for hackers, more than 1,700 IoT devices could easily take over and recruit them part of a botnet that could be used to power a DDoS attack.
The list has more than 22,000 views as of Saturday afternoon, while only 1,000 users have seen it since last Thursday.

Many IoT devices included in the list have default and well-known credentials (i.e., admin:admin, root:root, or no authentication required).
Top five credentials were:
root:[blank]—782
admin:admin—634
root:root—320
admin:default—21
default:[blank]—18
The popular researcher Victor Gevers, the founder of the GDI Foundation, analyzed the list and confirmed it is composed of more than 8200 unique IP addresses, about 2.174 are accessible via Telnet with the leaked credentials.
24 Aug
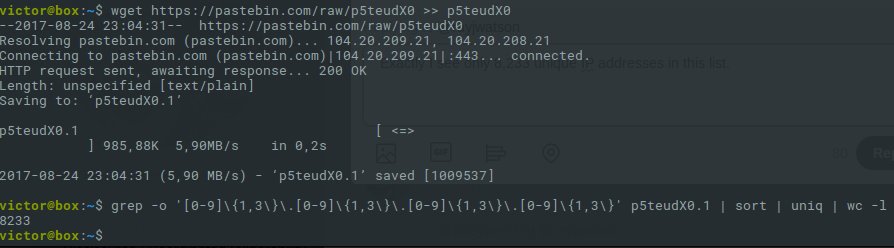
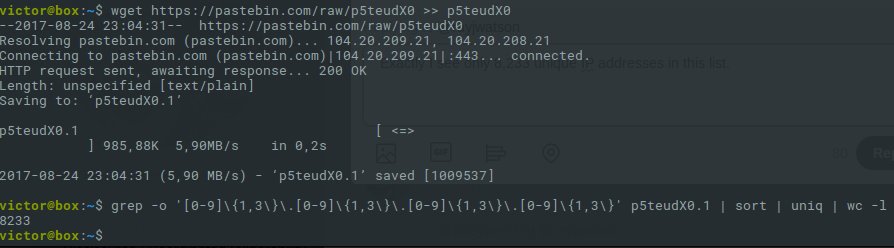
Victor Gevers @0xDUDE
Replying to @rayjwatson
Actually I see only 8,233 unique IP addresses in this dump? pic.twitter.com/Uydz0366Z3
Victor Gevers @0xDUDE
From the 8,233 hosts about 2,174 are still running an open telnet services and some of them still accessible with the leaked credentials. pic.twitter.com/umbNhYwAGV
2:44 PM - Aug 25, 2017

2 2 Replies 6 6 Retweets 10 10 likes
Twitter Ads info and privacy
According to the researchers, most of the reachable IPs (61 percent) were located in China.
The list of the 33,000 IP addresses includes many duplicates, it is likely they were already abused by hackers in the wild.
The Pastebin also includes numerous scripts, titled “Easy To Root Kit,” “Mirai Bots,” “Mirai-CrossCompiler,” “Apache Struts 2 RCE Auto-Exploiter v2),” “Slowloris DDoS Attack Script.”