Phishers Use 'ZeroFont' Technique to Bypass Office 365 Protections
20.6.18 securityweek Phishing
Cybercriminals have been leveraging a technique that involves manipulating font sizes in an effort to increase the chances of their phishing emails bypassing the protections implemented by Microsoft in Office 365.
According to cloud security company Avanan, one of the phishing protections in Office 365 involves natural language processing in order to identify text typically used in fraudulent or malicious emails.
For instance, researchers say the system flags emails mentioning “Apple” or “Microsoft” but not coming from legitimate domains, or messages referencing user accounts, password resets or financial requests.
In recent attacks spotted by Avanan, cybercriminals sent out phishing emails in which some of the content is set to be displayed with zero-size font using <span style="FONT-SIZE: 0px">. The security firm has dubbed this technique ZeroFont.
The email looks normal to the user, but Microsoft’s filters read the entire text, even if it’s displayed with a font size of “0”. The user sees this:
But Microsoft’s systems will analyze the following text, which includes strings that are invisible to the user due to the "FONT-SIZE: 0px" attribute:
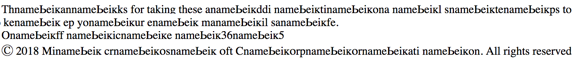
“Microsoft can not identify this as a spoofing email because it cannot see the word ‘Microsoft’ in the un-emulated version. Essentially, the ZeroFont attack makes it possible to display one message to the anti-phishing filters and another to the end user,” Avanan’s Yoav Nathaniel said in a blog post.
Last month, Avanan reported that cybercriminals had been splitting malicious URLs in an effort to bypass the Safe Links security feature in Office 365.