Software Supply Chain Increasingly Targeted in Attacks: Survey
23.7.18 securityweek Hacking
Organizations increasingly have to deal with cyberattacks targeting the software supply chain and in many cases they are not adequately prepared to respond to such incidents, according to a report published on Monday by endpoint security firm CrowdStrike.
In supply chain attacks, malicious actors target software makers in an effort to modify their products so that they perform malicious actions of provide a backdoor into the targeted environment.
The NotPetya attack, which involved a Ukrainian tax software firm, and the CCleaner incident, which involved hacking of distribution servers at Piriform, are some of the most well-known examples, but supply chain attacks are becoming increasingly common.
Vanson Bourne, on behalf of CrowdStrike, surveyed 1,300 senior IT decision makers and security professionals in the U.S., Canada, Mexico, the U.K., Australia, Japan, Germany and Singapore in April and May.
The Securing the Supply Chain report shows that roughly one-third of organizations are concerned about supply chain attacks, with 18% and 38% saying that the risk is high and moderate, respectively.
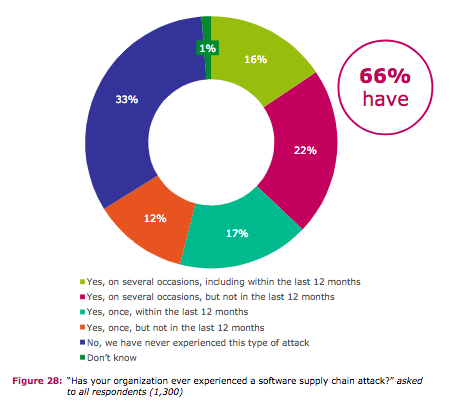
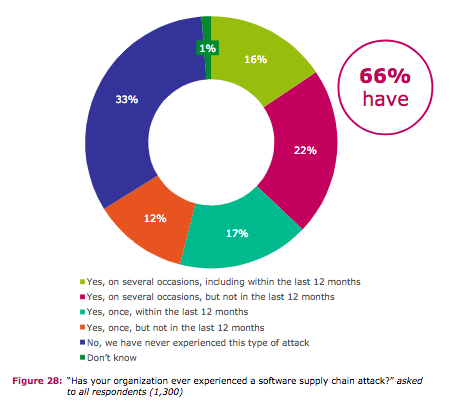
Approximately two-thirds of respondents have experienced some form of supply chain attack. The biotechnology and pharmaceutical sector takes the lead with 82% of organizations encountering such an incident, including 45% being hit in the last 12 months. Other sectors more likely to encounter supply chain attacks include hospitality, entertainment and media (74%), IT and technology (74%), engineering (73%), healthcare (70%) and insurance (68%).
On average, organizations believe it would take them 10 hours to detect an incident, 13 hours to react, 15 hours to respond, and 25 hours to remediate it, which totals 63 hours, the report shows.
A vast majority of respondents that have encountered a supply chain incident reported a financial impact, with an average cost of roughly $1.1 million. The highest costs were reported by the hospitality, entertainment and media sector ($1.44 million) and the lowest in the government sector ($329,000).
Some companies have also paid a ransom to recover from a supply chain attack, with many respondents saying their own organization or others in their industry had paid.
In addition to financial loss, organizations experienced various types of drawbacks following an attack, including the necessity to completely rebuild IT systems (36%), spend more on security (36%), and service/operations disruption (34%).
When it comes to response strategies, over one-third of respondents said they had a comprehensive strategy in place when they suffered an attack and more than half had some level of response pre-planned.
Trust in suppliers is not very high, with only 35% of respondents saying they had been totally certain they would be informed of a cybersecurity incident. On the other hand, 39% of those surveyed said they had lost trust in a supplier over the past year.
Less than a third of the organizations that took part in the survey vetted all suppliers in the past 12 months, and the high profile attacks that came to light last year made the vetting process more rigorous in 59% of cases. Executives have also started changing their attitude in regards to this threat, with 31% becoming more involved, 49% planning to become more involved, and 13% taking more of an interest.