
USBHarpoon a look-like charging cable that can hack into your computer
26.8.18 securityaffairs Attack
A team of security experts has devised a rogue USB charging cable named USBHarpoon that can be used to compromise a computer in just a few seconds.
The team was composed of Olaf Tan and Dennis Goh of RFID Research Group, Vincent Yiu of SYON Security, and the popular Kevin Mitnick.
The USBHarpoon takes inspiration on the BadUSB project built by researchers at Security Research Labs lead by Karsten Nohl.
Nohl demonstrated that to turn one device type into another, USB controller chips in peripherals need to be reprogrammed. Unfortunately, many USB controller chips, including those in thumb drives, have no protection from such reprogramming.
USBHarpoon leverages on a charging cable instead of a USB drive to make the dirty job and hack into a computer.
The cable was modified to allow both data and power to pass through, in this way it is impossible for a victim to note any suspicious behavior.
A weaponized charging cable is not a novelty, a security researcher that goes online with the Twitter handle MG posted two videos that show the BadUSB cables he has built. The cable allows MD to carry out HID attacks when plugged into a computer’s USB port.
MG
@_MG_
HID attacks via USB drives have become too suspicious. What about embedding the attack inside a USB cable?
Just a quick test for a few things I'm hoping to make over the next month.
8:40 AM - Jan 1, 18
4,759
3,002 people are talking about this
Twitter Ads info and privacy
MG
@_MG_
BadUSB Cable #2. HID attack through an Apple MacBook USB-C charger. Great for shared workspaces!
Build info coming this month. Still working out some things. These cables work on just about any device with a USB port (Mac/Win/Linux, phones too)
6:51 PM - Jan 6, 18
4,883
3,710 people are talking about this
Twitter Ads info and privacy
MG demonstrated that his BadUSB cable would work with a 24-pin USB-C connector which is used in MacBook chargers. MG added that it “work on just about any device with a USB port,” including mobile devices.
Mitnick asked MG to build a cable for him to use in a keynote speech to demonstrate new attack methods, but he did not receive it in time for his speech.

Mitnick contacted the researcher Dennis Goh to build a cable to use in the attack, then Goh accepted and worked with Olaf Tan to build the USBHarpoon.
Once MG has seen the USBHarpoon, commented that the cable is the same he designed which images he shared with Mitnick.
jermainlaforce
@jermainlaforce
· Aug 21, 18
Replying to @kevinmitnick
@_MG_ @LucaBongiorni @P4wnP1
MG
@_MG_
Heh, looks like the same boots I showed Kevin earlier this year, but with tape holding together? Just use some potting compound to seal it!
Hey @vysecurity did you do anything besides adding 2 resistors for charge pass through? That seems to work fine. Data passthrough though... pic.twitter.com/69slNg2U0O
12:30 AM - Aug 21, 18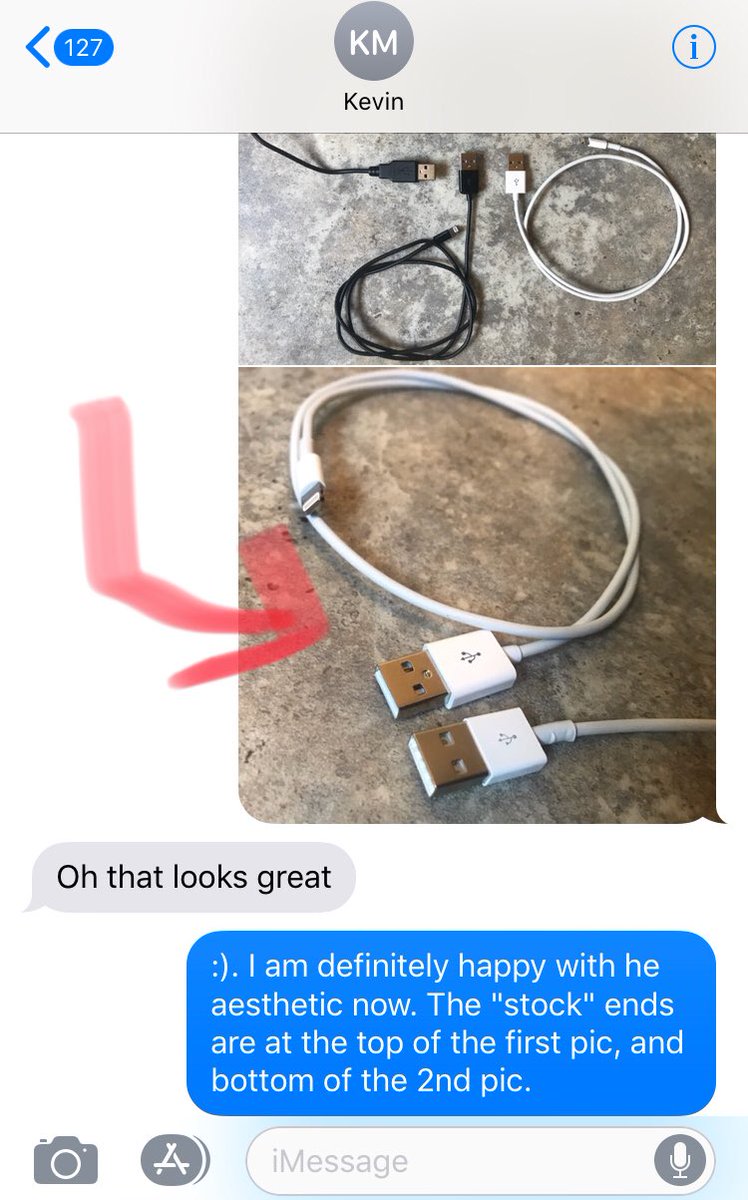
See MG's other Tweets
Twitter Ads info and privacy
Yiu confirmed that his cable was not inspired by the MG’s research, anyway he credited the original work from MG once he learned about it.
The USBHarpoon works on unlocked machines, it allows the attackers to launch commands that download and execute a malicious code.
Yiu published a short video to show how USBHarpoon works. The video PoC shows a drone connected to a Windows PC and sends it commands to list content in a folder on the system drive.
Experts noticed that on Windows, the commands are launched within the Run prompt, while on Mac and Linux they are launched from a terminal.
The attack is any way visible to the owner of the machine, for this reason, to make the attack stealth it is necessary to devise a method to hide the interaction with the system, for example, to run the attack when the victim is not around the machine.
The team of researchers is currently searching for methods to trigger the attack in a stealthy way, for example, involving as attack vectors Bluetooth and radio signals.
As mitigation, the experts suggest the adoption of USB condoms, also known as data-blocking device that works by blocking the data pins on a USB cable.
Anyway, MG published a video PoC that shows how USB condoms can be bypassed as well.
MG
@_MG_
#3 - BadUSB Cables wouldn't be complete without BadUSB Condoms.
Tempted to get a run of these made for the vendor area at the next security con.
3:19 AM - Jan 13, 18
388
165 people are talking about this
Twitter Ads info and privacy
USBHarpoon is the demonstration that USB devices can be used as attack vectors difficult to detect.