23.3.23 Android The Hacker News
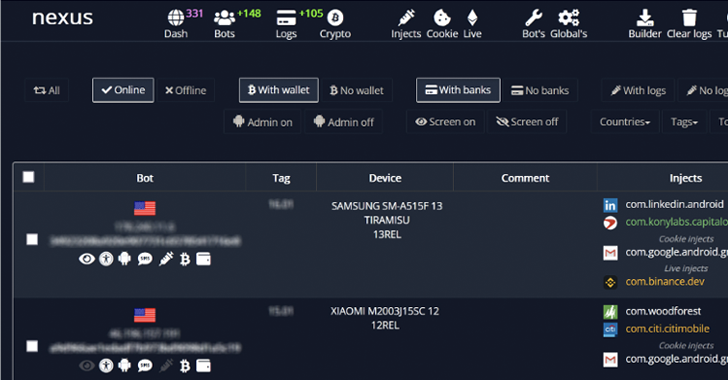
An emerging Android banking trojan dubbed Nexus has already been adopted by several threat actors to target 450 financial applications and conduct fraud.
Nexus: A New Rising Android Banking Trojan Targeting 450 Financial Apps
23.3.23 Android The Hacker News
An emerging Android banking trojan dubbed Nexus has already been adopted by several threat actors to target 450 financial applications and conduct fraud.
"Nexus appears to be in its early stages of development," Italian cybersecurity firm Cleafy said in a report published this week.
"Nexus provides all the main features to perform ATO attacks (Account Takeover) against banking portals and cryptocurrency services, such as credentials stealing and SMS interception."
The trojan, which appeared in various hacking forums at the start of the year, is advertised as a subscription service to its clientele for a monthly fee of $3,000. Details of the malware were first documented by Cyble earlier this month.
However, there are indications that the malware may have been used in real-world attacks as early as June 2022, at least six months before its official announcement on darknet portals.
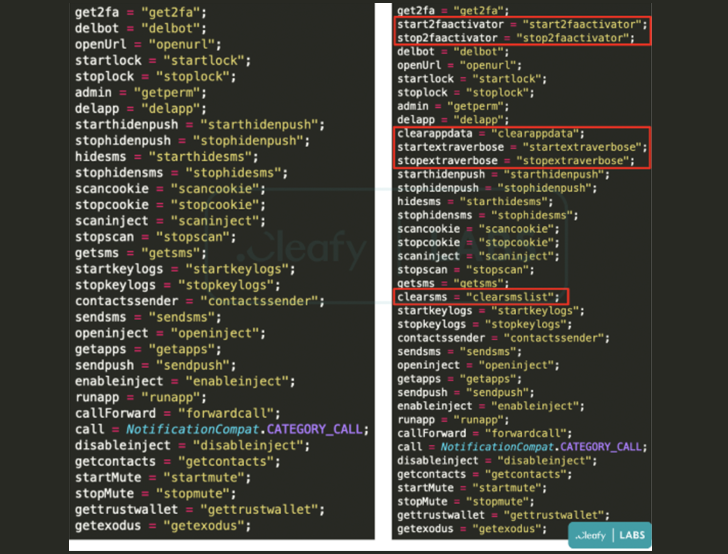
It's also said to overlap with another banking trojan dubbed SOVA, reusing parts of its source code and incorporating a ransomware module that appears to be under active development.
A point worth mentioning here is that Nexus is the same malware that Cleafy initially classified as a new variant of SOVA (dubbed v5) in August 2022.
Interestingly, the Nexus authors have laid out explicit rules that prohibit the use of its malware in Azerbaijan, Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Russia, Tajikistan, Uzbekistan, Ukraine, and Indonesia.
The malware, like other banking trojans, contains features to take over accounts related to banking and cryptocurrency services by performing overlay attacks and keylogging to steal users' credentials.
Furthermore, it's capable of reading two-factor authentication (2FA) codes from SMS messages and the Google Authenticator app through the abuse of Android's accessibility services.
Some new additions to the list of functionalities is its ability to remove received SMS messages, activate or stop the 2FA stealer module, and update itself by periodically pinging a command-and-control (C2) server.
"The [Malware-as-a-Service] model allows criminals to monetize their malware more efficiently by providing a ready-made infrastructure to their customers, who can then use the malware to attack their targets," the researchers said.