5.12.23 BigBrothers The Hacker News

A previously undocumented threat actor has been linked to a cyber attack targeting an aerospace organization in the U.S. as part of what's suspected to be a cyber espionage mission.
New Threat Actor 'AeroBlade' Emerges in Espionage Attack on U.S. Aerospace
5.12.23 BigBrothers The Hacker News
A previously undocumented threat actor has been linked to a cyber attack targeting an aerospace organization in the U.S. as part of what's suspected to be a cyber espionage mission.
The BlackBerry Threat Research and Intelligence team is tracking the activity cluster as AeroBlade. Its origin is currently unknown and it's not clear if the attack was successful.
"The actor used spear-phishing as a delivery mechanism: A weaponized document, sent as an email attachment, contains an embedded remote template injection technique and a malicious VBA macro code, to deliver the next stage to the final payload execution," the company said in an analysis published last week.
The network infrastructure used for the attack is said to have gone live around September 2022, with the offensive phase of the intrusion occurring nearly a year later in July 2023, but not before the adversary took steps to improvise its toolset to make it more stealthy in the intervening time period.
The initial attack, which took place in September 2022, commenced with a phishing email bearing a Microsoft Word attachment that, when opened, used a technique called remote template injection to retrieve a next-stage payload that's executed after the victim enables macros.
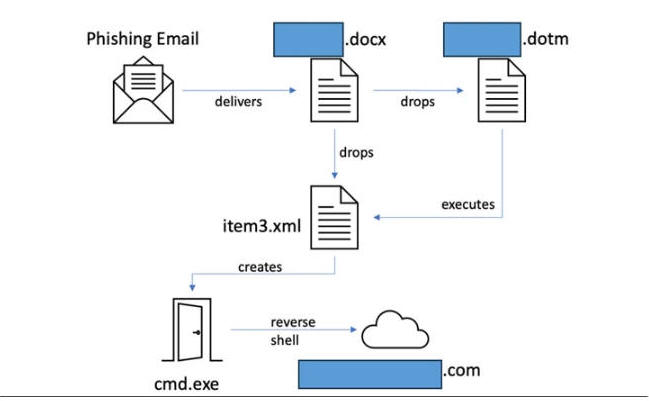
The attack chain ultimately led to the deployment of a dynamic-link library (DLL) that functions as a reverse shell, connecting to a hard-coded command-and-control (C2) server and transmitting system information to the attackers.
The information gathering capabilities also include enumerating the complete list of directories on the infected host, indicating that this could be a reconnaissance effort carried out to see if the machine hosts any valuable data and aid its operators in strategizing their next steps.
"Reverse shells allow attackers to open ports to the target machines, forcing communication and enabling a complete takeover of the device," Dmitry Bestuzhev, senior director of cyber threat intelligence at BlackBerry, said. "It is therefore a severe security threat."
The heavily obfuscated DLL also comes fitted with anti-analysis and anti-disassembly techniques to make it challenging to detect and take apart, while also skipping execution on sandboxed environments. Persistence is accomplished by means of a Task Scheduler, in which a task named "WinUpdate2" is created to run every day at 10:10 a.m.
"During the time that elapsed between the two campaigns we observed, the threat actor put considerable effort into developing additional resources to ensure they could secure access to the sought-after information, and that they could exfiltrate it successfully," Bestuzhev said.