All SweynTooth flaws basically reside in the way software development kits (SDKs) used by multiple system-on-a-chip (SoC) have implemented Bluetooth Low Energy (BLE) wireless communication technology—powering at least 480 distinct products from several vendors including Samsung, FitBit and Xiaomi.
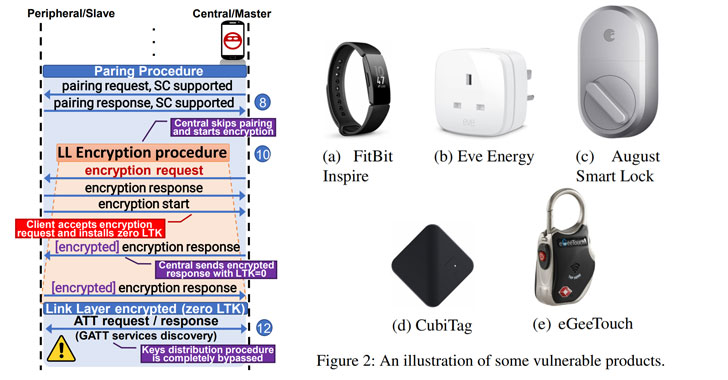
According to the researchers, hackers in close physical proximity to vulnerable devices can abuse this vulnerability to remotely trigger deadlocks, crashes, and even bypass security in BLE products, allowing them to arbitrary read or write access to device's functions that are otherwise only allowed to be accessed by an authorized user.
"As of today, SweynTooth vulnerabilities are found in the BLE SDKs sold by major SoC vendors, such as Texas Instruments, NXP, Cypress, Dialog Semiconductors, Microchip, STMicroelectronics and Telink Semiconductor," the researchers from the Singapore University of Technology and Design said.
Here is a list and brief information on all 12 SweynTooth vulnerabilities:
Link Layer Length Overflow (CVE-2019-16336, CVE-2019-17519) — These allow attackers in radio range to trigger a buffer overflow by manipulating the LL Length Field, primarily leading to a denial of service attacks.
Link Layer LLID deadlock (CVE-2019-17061, CVE-2019-17060) — These trigger deadlock state when a device receives a packet with the LLID field cleared.
Truncated L2CAP (CVE-2019-17517) — This flaw results due to a lack of checks while processing an L2CAP packet, causing a denial of service and crash of the device.
Silent Length Overflow (CVE-2019-17518) — A buffer overflow occurs when a certain packet payload with higher than expected LL Length is sent, the peripheral crashes.
Invalid Connection Request (CVE-2019-19195) — When devices do not properly handle some connection parameters while the central attempts a connection to the peripheral, they could lead to Deadlock state.
Unexpected Public Key Crash (CVE-2019-17520) — This bug is present in the implementation of the legacy pairing procedure, which is handled by the Secure Manager Protocol (SMP) implementation, and can be used to perform DoS and possibly restart products.
Sequential ATT Deadlock (CVE-2019-19192) — This flaw lets attackers deadlock the peripheral by sending just two consecutive ATT request packets in each connection event.
Invalid L2CAP fragment (CVE-2019-19195) — improper handling of the PDU size of the packets can lead to deadlock behavior.
Key Size Overflow (CVE-2019-19196) — This overflow in the device memory issue is a combination of multiple bugs found during the pairing procedure of devices, resulting in a crash.
Zero LTK Installation (CVE-2019-19194) — This critical vulnerability is a variation of one of the Key Size Overflow. It affects all products using Telink SMP implementation with support for secure connection enabled.
The detailed report says affected products include consumer electronics, smart home devices, wearables, and are also being used in the logistics and healthcare industry, malfunctioning of which can lead to hazardous situations.

"The most critical devices that could be severely impacted by SweynTooth are the medical products. VivaCheck Laboratories, which manufacture Blood Glucose Meters, has many products listed to use DA14580," the researchers said.
"Hence all these products are potentially vulnerable to the Truncated L2CAP attack. Even worse, Syqe Medical Ltd. and their programmable drug delivery inhalation platform (Syqe Inhaler v01) is affected alongside the latest pacemaker related products from Medtronic Inc."
According to the report, researchers disclosed these flaws last year to all affect vendors, many of which have now released patches for their respective SoCs.
Wheres, products developed by some SoC vendors, including Dialog, Microchip, and STMicroelectronics, are unpatched at the time of the disclosure.