How to Mitigate the Threat Cryptocurrency Mining Poses to Enterprise Security
6.2.2018 thehackernews CoinMine

The growing popularity of Bitcoin and other cryptocurrencies is generating curiosity—and concern—among security specialists. Crypto mining software has been found on user machines, often installed by botnets. Organizations need to understand the risks posed by this software and what actions, if any, should be taken.
To better advise our readers, we reached out to the security researchers at Cato Networks. Cato provides a cloud-based SD-WAN that includes FireWall as a Service (FWaaS). Its research team, Cato Research Labs, maintains the company's Cloud IPS, and today released a list of crypto mining pool addresses that you can use as a blacklist in your firewall. (To download the list, visit this page.)
Cato Research Labs determined crypto mining represents a moderate threat to the organization. Immediate disruption of the organization infrastructure or loss of sensitive data is not likely to be a direct outcome of crypto mining.
However, there are significant risks of increased facility cost that must be addressed.
Understanding Blockchain and Crypto Mining
Crypto mining is the process of validating cryptocurrency transactions and adding encrypted blocks to the blockchain. Miners solve a hash to establish a valid block, receiving a reward for their efforts. The more blocks mined, the more difficult and resource-intensive becomes solving the hash to mine a new block.
Today, the mining process can require years with an off-the-shelf computer. To get around the problem, miners use custom hardware to accelerate the mining process, as well as forming "mining pools" where collections of computers work together to calculate the hash.
The more compute resources contributed to the pool, the greater the chance of mining a new block and collecting the reward. It's this search for more compute resources that have led some miners to exploit enterprise and cloud networks.
Participating in mining pools requires computers run native or JavaScript-based mining software (see Figure 1). Both will use the Stratum protocol to distribute computational tasks among the computers in the mining pool using TCP or HTTP/S (technically, WebSockets over HTTP/S).

Figure 1: An example of a website running JavaScript-based mining software. Typically, websites do not ask for permission.
Native mining software will typically use long-lasting TCP connections, running Stratum over TCP; JavaScript-based software will usually rely on shorter-lived connections and run Stratum over HTTP/S.
The Risk Crypto Mining Poses to the Enterprise
Mining software poses a risk to the organization on two accounts. In all cases, mining software is highly compute-intensive, which can slow down an employee’s machine. Running CPUs with a “high-load” for an extended period of time will increase electricity costs and may also shorten the life of the processor or the battery within laptops.
Mining software is also being distributed by some botnets. Native mining software accesses the underlying operating system in a way similar to how botnet-delivered malware exploits a victim’s machine. As such, the presence of native mining software may indicate a compromised device.
How To Protect Against Crypto Mining
Cato Research Labs recommends blocking crypto mining on your network. This can be done by disrupting the process of joining and communicating with the mining pool.
The deep packet inspection (DPI) engine in many firewalls can be used to detect and block Stratum over TCP. Alternatively, you can block the addresses and domains for joining public mining pools.
Approach 1: Blocking Unencrypted Stratum Sessions with DPI
DPI engines can disrupt blockchain communications by blocking Stratum over TCP. Stratum uses a publish/subscribe architecture where servers send messages (publish) to subscribed clients. Blocking the subscription or publishing process will prevent Stratum from operating across the network.
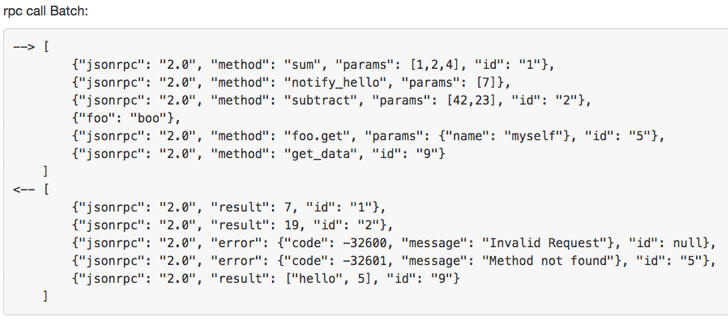
DPI rules should be configured for JSON. Stratum payloads are simple, readable JSON-RPC messages (see Figure 2).
Stratum uses a request/response over JSON-RPC:
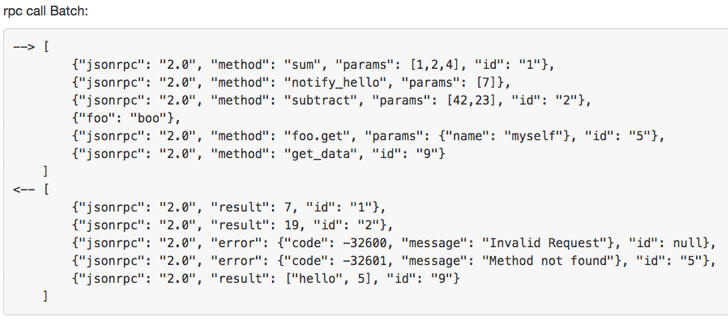
Figure 2: Detail of a JSON-RPC batch call (reference: http://www.jsonrpc.org/specification)
A subscription request to join a pool will have the following entities: id, method, and params (see Figure 3). Configure DPI rules to look for these parameters to block Stratum over unencrypted TCP.
{"id": 1, "method": "mining.subscribe", "params": []}
Three parameters are used in a subscription request message when joining a pool.
Approach 2: Blocking Public Mining Pool Addresses
However, some mining pools create secure, Stratum channels. This is particularly true for JavaScript-based applications that often run Stratum over HTTPS.
Detecting Stratum, in that case, will be difficult for DPI engines who do not decrypt TLS traffic at scale. (For the record, Cato IPS can decrypt TLS sessions at scale.) In those cases, organizations should block the IP addresses and domains that form the public blockchain pools.
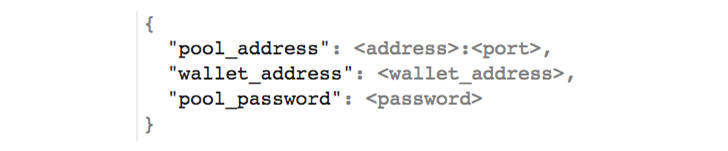
To determine the IP addresses to block, look at the configuration information needed to join a mining pool. Mining software requires miners to fill in the following details:
the appropriate pool address (domain or IP)
a wallet address to receive equity
the password for joining the pool
The configuration information is usually passed via JSON or via command-line arguments (see Figure 3).
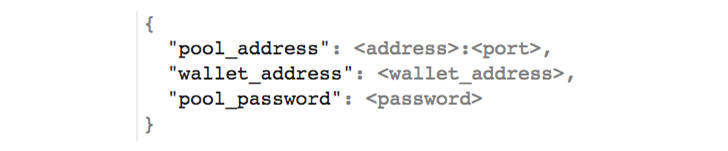
Figure 3: A JSON file providing the necessary miner pool configuration
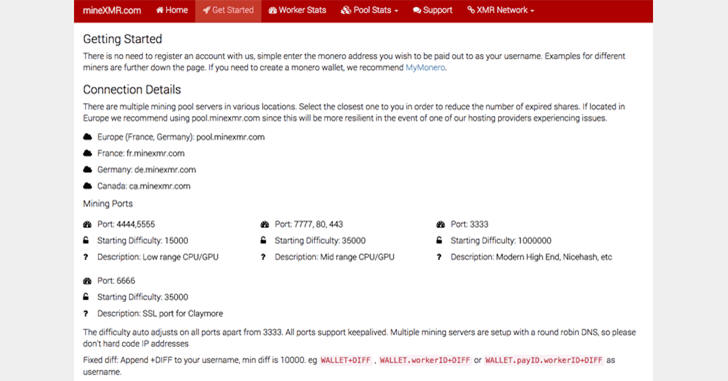
Organizations could configure firewall rules to use a blacklist and block the relevant addresses. In theory, such a list should be easy to create as the necessary information is publicly available. Most mining pools publish their details over the Internet in order to attract miners to their networks (see Figure 4).
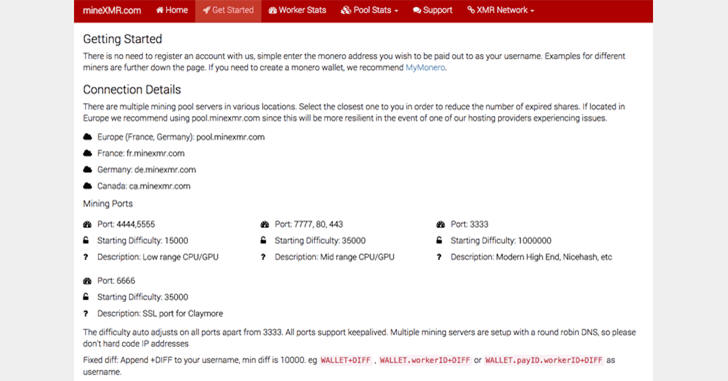
Figure 4: Public addresses for mining pools are well advertised as demonstrated by mineXMR.com’s “Getting Started” page
Despite extensive research, though, Cato Research Labs could not find a reliable feed of mining pool addresses. Without such a list, collecting the target mining pool addresses for blocking would be time-consuming.
IT professionals would be forced to manually enter in public addresses, which will likely change or increase, requiring constant maintenance and updates.
Cato Research Labs Publishes List of Mining Pool Addresses
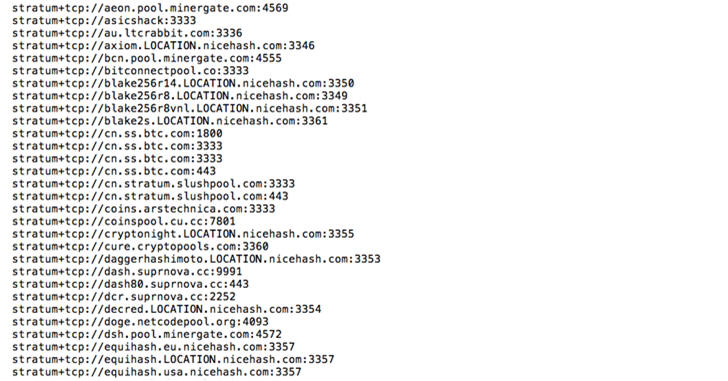
To address the issue, Cato Research Labs generated its own list of mining pool addresses for use by the greater community. Using Google to identify sites and then employing scraping techniques, Cato researchers were able to extract pool addresses for many mining pools.
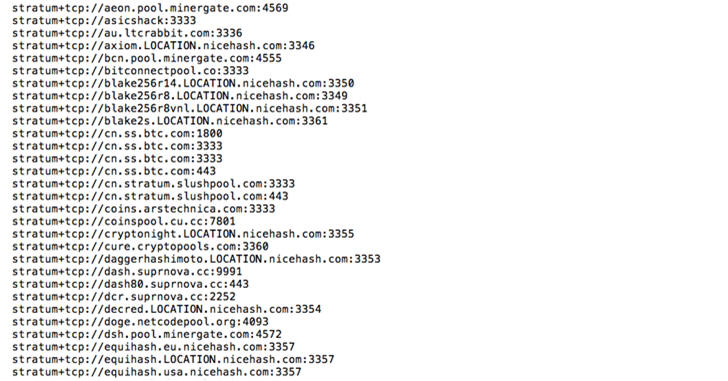
Figure 5: Partial list of mining pool addresses compiled by Cato Research Labs
Cato researchers wrote code that leveraged those results to develop a mining-pool address feed. Today, the list identifies hundreds of pool addresses (see Figure 5) and should be suitable for most DPI rule engines. See here for the full list.
Final Thoughts
The combined risk of impairing devices, increasing costs, and botnet infections led Cato Research Labs to strongly recommend IT prevent and remove crypto mining from enterprise networks.
Should software-mining applications be found on the network, Cato Research Labs strongly recommends investigating active malware infections and cleaning those machines to reduce any risk to organization's data.
Cato Research Labs provided a list of address that can be used towards that goal, blocking access to public blockchain pools. But there's always a chance of new pools or addresses, which is why Cato Research Labs strongly recommend constructing rules using a DPI engine with sufficient encrypted-session capacity.
Grammarly Rushes to Patch Flaw Exposing User Data
6.2.2018 securityweek Vulnerebility
Google Project Zero researcher Tavis Ormandy discovered a vulnerability in the online grammar checker Grammarly that could have been exploited by malicious websites to access user data. The app’s developers quickly patched the flaw after learning of its existence.
Ormandy found that the Grammarly browser extension, which has roughly 20 million users on Chrome and 645,000 on Firefox, exposed authentication tokens to third-party websites.
An attacker could have obtained authentication tokens and used them to access the target’s Grammarly.com account simply by getting them to visit a specially crafted website. This was a serious flaw considering that some Grammarly accounts could contain highly sensitive information.
“I'm calling this a high severity bug, because it seems like a pretty severe violation of user expectations,” Ormandy said in an advisory. “Users would not expect that visiting a website gives it permission to access documents or data they've typed into other websites.”
In a blog post covering the Google researcher’s findings, Sophos expert Paul Ducklin explained how authentication tokens work.
“An authentication token is a one-time cryptographic string that is set by a server as a browser cookie after you’ve successfully logged into a website. Your browser sends that cookie back to the site with every subsequent web transaction, thus signalling to the server that it’s you coming back for more,” Ducklin said. “Without this sort of arrangement, you’d have to supply your username and password for every web request you wanted to make.”
Ducklin highlighted that online services should protect these tokens by using HTTPS, and by enforcing the same-origin policy (SOP), which prevents websites from interacting with each other.
Ormandy reported the vulnerability to Grammarly on Friday and the company said it rolled out a fix within hours. Users are not required to take any action as the affected browser extensions should be updated automatically.
Grammarly pointed out that the security hole only affected text saved in the Grammarly Editor, and it did not impact Grammarly Keyboard, the Microsoft Office add-in, or any text typed in websites while using the extension.
“At this time, Grammarly has no evidence that any user information was compromised by this issue,” Grammarly said. “We’re continuing to monitor actively for any unusual activity.”
This is not the first vulnerability disclosed by Ormandy this year. He has also reported finding a critical remote code execution vulnerability in the Transmission BitTorrent client, and a code execution flaw affecting all games from Blizzard.
Crypto-mining Botnet Targets Android Devices
6.2.2018 securityweek Android
A new crypto-mining botnet has been growing and targeting Android devices with an open ADB port, Qihoo 360's NetLab researchers reveal.
The attacks started last week, targeting port 5555, which is the working port for the adb debug interface on Android devices. While this port should be normally closed on all devices, sometimes it could remain open, thus allowing devices to be compromised.
Courtesy of scanning code borrowed from the infamous Mirai botnet – which targets Internet of Things (IoT) devices – the new threat can spread as a worm, NetLab reports. Each of the infected bots would continue to scan for open 5555 adb ports to spread further.
This is the first time the Mirai code has been reused to target Android devices, the researchers point out.
The infection appears to have started on January 21, 2018, and the researchers say that the number of attacks has increased recently.
As of February 4, between 2,700 and 5,500 devices had been affected by the botnet, with most of them located in China (40%) and South Korea (31%) – based on the scanning IP addresses targeted devices include smartphones and smart TVs (TV set-top boxes), the security researchers say.
It appears that the botnet isn’t targeting vulnerabilities affecting only specific devices, mainly because models from a broad range of manufacturers have been already impacted. However, the security firm hasn’t provided details on the impacted device models.
The purpose of the newly created botnet, NetLab reports, is to mine for the Monero crypto-currency. The malware’s configuration shows the use of two mining pools, but both groups of devices are using the same wallet address.
The researchers revealed that no payment had been made to the used wallet by the time of their report, but also said they would continue watching and analyzing the threat to provide additional details.
Popular British hacktivist Lauri Love will not be extradited to US, UK Court Ruled
6.2.2018 securityaffairs Crime
The popular British hacker Lauri Love (33) will not be extradited to stand trial in the US, the High Court of England and Wales ruled.
Lauri Love was accused of hacking into United States government websites, will not be extradited to stand trial in the U.S., the High Court of England and Wales ruled today.
The list of victims of the hacker includes the FBI, the Federal Reserve Bank, US Missile Defence Agency, National Aeronautics and Space Administration (NASA), and the US Missile Defence Agency.
The decision of the Lauri Love’s extradition was taken at Westminster Magistrates’ Court in London in 2016, by District Judge Nina Tempia. If extradited, Love risks a sentence to up to 99 years in prison and a potential fine of up to $9 million.
Actually, the man would face a prison sentence in the UK following his five years of legal battle.
US Prosecutors believe that Lauri Love is a member of a hacker crew, they sustain that he was also involved in the OpLastResort campaign launched by Anonymous against the US Government.
Lord Chief Justice Lord Burnett of Maldon and Justice Ouseley halted the extradition after heard Lauri Love suffered severe mental illness, including Asperger syndrome, and depression, they fear the man should commit suicide if extradited.
“There have not been any incidents of self-harm in the past but I accept Mr Love has experienced suicidal thoughts intermittently, both in the past and now. Mr Love denied any suggestion that he had exaggerated his symptoms and his suicide risk which I accept given the medical evidence.” the High Court ruled on Monday.
“I also accept Professor Baron-Cohen and Professor Kopelman’s evidence that he would attempt suicide before extradition to the United States. Both are of the opinion he would be at high risk of suicide. I accept Professor BaronCohen’s oral evidence that Mr Love’s intention is not a reflection of a voluntary plan or act but due to his mental health being dependant on him being at home with his parents and not being detained for an indefinite period.”
The court recognized that extradition would be “oppressive” due to the man’s health conditions. Love supporters that were present in the court applauded the judgment.
The Crown Prosecution Service (CPS), which acts on behalf of the US authorities, would examine the judgment before deciding whether to appeal the high court decision to the supreme court.
“I’m thankful for all the support we’ve had, without which I’m not sure I would have made it this far.” commented Love expressing gratitude to the judges.
The judgment was accepted with joy in the hacking community and by human rights advocates.
ADB.Miner, the Android mining botnet that targets devices with ADB interface open
6.2.2018 securityaffairs BotNet
Security researchers at Qihoo 360’s Netlab have spotted a new Android mining botnet that targets devices with ADB interface open.
Security researchers at Qihoo 360’s Netlab have spotted a new Android mining botnet over the weekend. The malicious code ADB.Miner targets Android devices by scanning for open ADB debugging interface (port 5555) and infects them with a Monero cryptocurrency miner.
The port 5555 is the working port ADB debug interface on Android device that should be shut down normally. The devices infected by ADB.miner are devices where users or vendors have voluntary enabled the debugging port 5555.
“Spread of time : the earliest time of infection can be traced back to near January 31. This current wave of helminthic infections has been detected by our system from around 15:00 on the afternoon of 2018-02-03 and is still on the rise.” reads the analysis published by Netlab.
“Infected port : 5555, is the working port adb debug interface on Android device, the port should be shut down normally, but unknown part of the cause led to the wrong port opened.”
Starting from February 3, the expert noticed a rapid growth of the volume of scan traffic on port 5555 associated with the ADB.Miner:
Once the ADB.Miner has infected a device, the compromised system start scanning the Internet for other devices to infect.
According to the experts, ADB.miner borrowed the scanning code implemented by the Mirai botnet, this is the first time that the Mirai code is used by an Android threat.
The researchers did not reveal the way the malware infects the Android devices, it is likely it exploits a flaw in the ADB interface.
The number of infected devices is rapidly growing, according to different caliber statistics, there are 2.75 ~ 5.5k, and this figure is rapidly growing.
The two sources reported by Netlab are:
Statistics from scanmon : 2.75k, mainly from China (40%) and South Korea (31%).
Statistics from our botnet tracking system: 5.5k
At the time of writing the number of ADB.miner scans reached 75,900 unique IP addresses.
Most IP addresses scanning the port 5555 are located in China (~40%) and South Korea (~30%).
The operators of the botnet are using the following Monero wallet address:
44XT4KvmobTQfeWa6PCQF5RDosr2MLWm43AsaE3o5iNRXXTfDbYk2VPHTVedTQHZyfXNzMn8YYF2466d3FSDT7gJS8gdHAr
That still has not received the first payment for the mine.
Prediktivní antimalwarovou ochranu s podporou hlubokého učení má Sophos
6.2.2018 SecurityWorld Zabezpečení
Technologie hlubokého učení, kterou Intercept X nově využívá, je podle výrobce výrazně účinnější než tradiční strojové učení. Sophos je tak prý schopen nabídnout vysokou míru detekce infekci při nízkém stupni falešně pozitivních zjištění.
Dostupnost svého produktu Intercept X, který pro detekci malware využívá neuronové sítě s technologií hlubokého učení, oznámil Sophos. Hluboké učení přináší masivně škálovatelnou detekci, která se učí na celém dostupném spektru hrozeb.
Díky svým schopnostem zpracovávat stovky miliónů vzorků může být technologie hlubokého učení – ve srovnání s tradičním strojovým učením – přesnější i rychlejší a také méně náchylnější na falešně pozitivní zjištění.
“Úspěšnost tradičních modelů strojového učení velmi silně závisí na výběru atributů použitých pro tréning a tím se do celého systémů vnáší vliv lidského faktoru. Přidáváním nových dat navíc složitost těchto modelů neustále roste, systémy opírající se o gigabajty dat jsou těžkopádné a pomalé. Problémem je i velká míra falešně pozitivních zjištění, díky kterým musí administrátoři posuzovat, zda je daný software legitimní nebo jde o malware. A důsledkem tohoto jejich vytížení je nižší produktivita IT oddělení,“ vysvětluje Tony Palmer, analytik společnosti Enterprise Strategy Group (ESG).
Neuronová síť v Intercept X podle něj využívá technologii hlubokého učení, která je oproti tradičním modelům navržená tak, aby se učila na základě zkušeností a hledala vzájemné souvislosti mezi pozorovaným chováním a malware.
Tyto korelace podle Palmera umožňují dosahovat vysoké přesnosti jak v případě identifikace již existujícího, tak i dosud nezveřejněného (zero-day) malware. Významným přínosem je prý i snížení výskytu falešně pozitivních zjištění.
Součástí nové verze Intercept X jsou I inovace v oblasti boje proti ransomwarU i ochrany proti zneužívání zranitelností. Nechybí ani mechanismy pro aktivní boj s hackerskými pokusy, jako je například ochrana proti krádežím přihlašovacích údajů.
Jde o důležitá vylepšení, protože právě krádeže identit jsou stále častějším nástrojem, který kybernetičtí zločinci využívají pro průnik do chráněné informační architektury, ve které se pak mohou pochybovat jako zcela legitimní uživatelé. Nový Intercept X umí tato podezřelá chování odhalit a předejít možným důsledkům.
Intercept X lze nasadit prostřednictvím cloudové konzole Sophos Central, a to vedle jakékoli stávající softwarové ochrany koncových bodů – míru bezpečnosti tak lze zvýšit prakticky okamžitě. Při použití ve spojení s firewally Sophos XG přináší Intercept X NAVÍC výhody synchronizované ochrany, které ještě více posílí bezpečnost dané informační architektury.
Nové funkce a vlastnosti Intercept X jsou podle výrobce ty níže uvedené.
Detekce malware pomocí strojového učení:
Hluboké učení umí odhalit známý i dosud neznámý malware i potenciálně nežádoucí aplikace ještě před jejich spuštěním, a to bez využívání identifikačních vzorů
Model si vystačí s méně než 20 MB a nevyžaduje časté aktualizace dat
Aktivní opatření
Ochrana před krádeží přihlašovacích údajů – nový Intercept X zabraňuje zjišťování hesel a dalších přihlašovacích informací z paměti, registrů i úložišť a předchází tak mechanismům, které využívá například nástroj Mimikatz.
Zjišťování přítomnosti cizích programových částí propašovaných do jiných aplikacích, což je technika využívaná pro přetrvávající hrozby a vyhýbání se antivirovým kontrolám.
Ochrana před zneužitím APC (Application Procedure Calls), tedy před útoky typu AtomBombing a mechanismy šíření, které byly využité například u hrozeb WannaCry a NotPetya. Útočníci tato volání zneužili prostřednictvím exploitů EternalBlue a DoublePulsar a mohli tak škodlivý kód provést pomocí jiného procesu.
Nové a vylepšené techniky proti zneužívání zranitelností
Ochrana před migracemi škodlivých procesů, která detekuje vzdálené zneužívání dynamických knihoven, tedy techniky pro přesouvání mezi procesy běžícími na konkrétním systému.
Ochrana před zvyšováním oprávnění, která brání tomu, aby neprivilegované procesy získaly přístup k chráněným částem systému.
Pokročilejší omezování aplikací
Omezování aplikací na úrovni prohlížeče, které brání nežádoucímu spouštění příkazů PowerShell
Omezování HTA aplikací, které brání nežádoucímu chování stejně, jako by šlo o prohlížeč.
Zero-Day Attack Prompts Emergency Patch for Bitmessage Client
14.2.2018 securityweek Vulnerebility
An emergency update released on Tuesday for the PyBitmessage application patches a critical remote code execution vulnerability that has been exploited in attacks.
Bitmessage is a decentralized and trustless communications protocol that can be used for sending encrypted messages to one or multiple users. PyBitmessage is the official client for Bitmessage.
Bitmessage developers have issued a warning for a zero-day flaw that has been exploited against some users running PyBitmessage 0.6.2.
The security hole, described as a message encoding bug, has been patched with the release of version 0.6.3.2, but since PyBitmessage 0.6.1 is not affected by the flaw, downgrading is also an option for mitigating potential attacks.
Code patches were released on Tuesday, and binary files for Windows and macOS are expected to become available on Wednesday.
One of the individuals targeted in the zero-day attacks was Bitmessage core developer Peter Šurda. The developer told users not to contact him on his old address and admitted that his keys were most likely compromised. A new support address has been added to PyBitmessage 0.6.3.2.
“If you have a suspicion that your computer was compromised, please change all your passwords and create new bitmessage keys,” Surda said.
According to Šurda, the attacker exploited the vulnerability in an effort to create a remote shell and steal bitcoins from Electrum wallets.
“The exploit is triggered by a malicious message if you're the recipient (including joined chans),” the developer explained. “The attacker ran an automated script but also opened, or tried to open, a remote reverse shell. The automated script looked in ~/.electrum/wallets, but when using the reverse shell he had access to other files as well.”
The investigation into these attacks is ongoing and Bitmessage developers have promised to share more information as it becomes available.
Bitmessage has become increasingly popular in the past years following reports that the U.S. National Security Agency and other intelligence agencies are conducting mass surveillance. While the protocol is often used by people looking to protect their privacy, it has also been leveraged by cybercriminals, including in ransomware attacks for communications between victims and the hackers.
Zero-Day in Telegram's Windows Client Exploited for Months
14.2.2018 securityweek Exploit
A zero-day vulnerability impacting Telegram Messenger’s Windows client had been exploited in malicious attacks for months before being discovered and addressed.
Exploitation of the bug involves the use of a classic right-to-left override attack when a file is sent using the messenger service. The special nonprinting right-to-left override (RLO) character represented as ‘U+202E’ is used to reverse the order of the characters following it in the string.
Cybercriminals have discovered that they could leverage the character to mislead victims by hiding the name and extension of an executable file. Thus, if an application is vulnerable to the attack, the filename and extension would be displayed either incompletely or in reverse.
According to Kaspersky, which observed the attacks abusing the flaw, the attack chain involves sending malware in a message, but using the special character to hide it. A JS file could be renamed as photo_high_re*U+202E*gnp.js, which would make Telegram display the string gnp.js in reverse, thus appearing to the unsuspecting user as a PNG image file instead.
The actual file, however, isn’t modified, but remains the same JS file that it always was. If the user clicks on it, a standard Windows security notification would appear – as long as it hasn’t been previously disabled in the system’s settings –, informing the user that it is a JavaScript file.
Kaspersky learned of the issue in October 2017 and, after an investigation into the matter, discovered that cybercriminals had been abusing it since at least March 2017, in a multitude of attack scenarios.
Some of the incidents, the researchers say, resulted in the attackers taking control of the victim’s system. For that, however, analysis of the target system’s environment and the installation of additional modules was necessary.
Such an attack starts with an initial downloader being sent to the target. It would achieve persistence and then begin checking for commands arriving from the control bot. The loader could silently deploy malicious tools such as backdoors, loggers, and other malware on the target system.
The vulnerability was also abused in attacks involving miners, Kaspersky says. The infection would start with an SFX archive with a script designed to launch a BAT file posing as an executable. The program would first open a decoy file, when it would launch two miners as services, using the nssm.exe utility for this operation.
One of the programs was nheq.exe, an Equihash miner for NiceHash (it mined Zcash in the observed attack), while the other was taskmgn.exe, a popular miner implementing the CryptoNight algorithm and used to mine Fantomcoin and Monero.
In some attacks, the batch script had extra capabilities, being able to disable Windows security features and to download an additional payload from a malicious FTP server. The payload contained more miners and a Remote Manipulator System (RMS) client for subsequent remote access.
On the malicious FTP server, the researchers discovered archives containing Telegram directories stolen from the victims, some of which were created in March 2017. Inside the archives, Kaspersky found “an encrypted local cache containing different files used in personal communications: documents, videos and audio records and photos.”
In another attack scenario, an SFX archive launching a VBScript was observed. It too would open a decoy image to distract the user, then fetch and run the payload, another SFX archive containing a script designed to control the launch of the miner CryptoNight (csrs.exe). The script monitors the task list and terminates the miner if a task manager (taskmgr.exe, processhacker.exe) is on that list.
“It appears that only Russian cybercriminals were aware of this vulnerability, with all the exploitation cases that we detected occurring in Russia. Also, while conducting a detailed research of these attacks we discovered a lot of artifacts that pointed to involvement by Russian cybercriminals,” Kaspersky says.
The researchers couldn’t determine which versions of Telegram were affected by the vulnerability, but they believe that the exploitation of flawed Windows clients started in March 2017. Telegram was informed on the bug and has since addressed it in its products.
New AndroRAT Variant Emerges
14.2.2018 securityweek Vulnerebility Virus
A newly discovered variant of the AndroRAT off-the-shelf mobile malware can inject root exploits to perform malicious tasks, Trend Micro reports.
The updated malware version targets CVE-2015-1805, a publicly disclosed vulnerability that can be abused to achieve privilege escalation on older Android devices. By injecting root exploits, the threat can perform silent installation, shell command execution, WiFi password collection, and screen capture, security researchers have discovered.
First observed in 2012, AndroRAT was initially a university project, designed as an open-source client/server application to offer remote control of a device. It didn’t take long for cybercriminals to find the tool appealing and start using it in attacks.
The same as other Remote Access Tools (RATs), the malware gains root access in order to take control over the target system.
The newly observed version of the tool masquerades as a utility app called TrashCleaner, which the researchers believe is delivered from a malicious URL. When first executed, TrashCleaner prompts the user to install a Chinese-labeled calculator app, hides its icon from the device’s UI, and activates the RAT in the background.
“The configurable RAT service is controlled by a remote server, which could mean that commands may be issued to trigger different actions. The variant activates the embedded root exploit when executing privileged actions,” Trend Micro notes.
The malware can perform a broad range of actions previously observed in the original AndroRAT, including audio recording, photo taking, and system information theft (phone model, number, IMEI, etc.). It also steals WiFi names, call logs, mobile network cell location, GPS location, contacts, files on the device, list of running apps, and SMS messages, while keeping an eye on all incoming and outgoing SMS.
The threat is also capable of obtaining mobile network information, storage capacity, root status, list of installed applications, web browsing history from pre-installed browsers, and calendar events. Additionally, it can record calls, upload files to the device, capture photos using the front camera, delete and send forged SMS messages, take screenshots, execute shell commands, steal WiFi passwords, and silently enable accessibility services for a keylogger.
While the targeted vulnerability (CVE-2015-1805) was patched in early 2016, devices that are no longer updated regularly continue to be exposed to this new AndroRAT variant.
To avoid being targeted by the threat, users should avoid downloading and installing applications from third-party app stores. Installing the latest security updates and keeping all applications on the device updated at all times should also reduce the risk of being affected, the security researchers point out.
Adobe Patches 39 Vulnerabilities in Acrobat and Reader
14.2.2018 securityweek Vulnerebility
Updates released on Tuesday by Adobe for its Acrobat, Acrobat Reader and Experience Manager products patch more than 40 vulnerabilities, but none of them appear to have been exploited for malicious purposes.
The company fixed a total of 39 flaws in its Acrobat and Reader products for Windows and Mac. The security holes, rated important and critical with a priority rating of 2, have been described as security mitigation bypass, heap overflow, use-after-free, out-of-bounds read, and out-of-bounds write weaknesses that can be exploited for privilege escalation or arbitrary code execution.
The flaws impact version 2018.009.20050 and earlier of Acrobat DC Continuous Track, version 2017.011.30070 and earlier of Acrobat 2017, and versions 2015.006.30394 and earlier of Acrobat DC Classic Track.
More than half of the vulnerabilities were reported to Adobe by employees of China-based Tencent. The disclosure was often made through Trend Micro’s Zero Day Initiative (ZDI).
As for Experience Manager, the latest version of the enterprise content management solution patches two vulnerabilities, including a reflected cross-site scripting (XSS) issue rated moderate, and an important XSS in the Apache Sling XSS protection API.
According to Adobe, exploitation of these flaws could allow attackers to obtain sensitive information. The company has not credited anyone for the Experience Manager security holes.
Earlier this month, Adobe issued an emergency update for Flash Player after learning that threat actors believed to be working on behalf of North Korea had been exploiting a zero-day vulnerability in attacks aimed at South Korea.
The group believed to be behind the attacks is tracked by FireEye as “TEMP.Reaper” and by Cisco Talos as “Group 123.”
Microsoft Patches 50 Flaws in Windows, Office, Browsers
14.2.2018 securityweek Vulnerebility
Microsoft’s Patch Tuesday updates for February 2018 address 50 vulnerabilities in Windows, Office and the company’s web browsers, but this time the list does not appear to include any zero-day flaws.
Fourteen of the security holes have been rated critical, including an information disclosure flaw in Edge, a memory corruption in Outlook, a remote code execution vulnerability in Windows’ StructuredQuery component, and several memory corruptions in the scripting engines used by Edge and Internet Explorer.
One vulnerability, CVE-2018-0771, was publicly disclosed before Microsoft released patches. The issue is a Same-Origin Policy (SOP) bypass that exists due to the way Edge handles requests of different origins.
“An attacker who successfully exploited the vulnerability could force the browser to send data that would otherwise be restricted,” Microsoft said. The company believes it’s unlikely that this flaw, which it has rated “important,” will be exploited in attacks.
Two of the most interesting issues patched this month are Outlook vulnerabilities discovered by Microsoft’s own Nicolas Joly. One of the flaws, CVE-2018-0852, can be exploited to execute arbitrary code in the context of a user’s session by getting the target to open a specially crafted file with an affected version of Outlook.
“What’s truly frightening with this bug is that the Preview Pane is an attack vector, which means simply viewing an email in the Preview Pane could allow code execution,” explained Dustin Childs of the Zero Day Initiative (ZDI). “The end user targeted by such an attack doesn’t need to open or click on anything in the email – just view it in the Preview Pane. If this bug turns into active exploits – and with this attack vector, exploit writers will certainly try – unpatched systems will definitely suffer.”
The second Outlook vulnerability found by Joly is a privilege escalation issue (CVE-2018-0850) that can be leveraged to force Outlook to load a local or remote message store. The flaw can be exploited by sending a specially crafted email to an Outlook user.
“The email would need to be fashioned in a manner that forces Outlook to load a message store over SMB. Outlook attempts to open the pre-configured message on receipt of the email. You read that right – not viewing, not previewing, but upon receipt. That means there’s a potential for an attacker to exploit this merely by sending an email,” Childs said, pointing out that such a vulnerability would have earned Joly a prize in ZDI’s Pwn2Own competition.
Microsoft’s Patch Tuesday updates fix a total of 34 important and two moderate severity vulnerabilities.
Earlier this month, Microsoft updated the Adobe Flash Player components used by its products to address two vulnerabilities, including a zero-day believed to have been exploited by North Korean threat actors. Adobe on Tuesday released updates for its Acrobat, Reader and Experience Manager products to address 41 security bugs.
A new variant of the dreaded AndroRAT malware appeared in threat landscape
14.2.2018 securityaffairs Android
Security researchers from Trend Micro detected a new variant of the popular AndroRAT Android RAT in the criminal ecosystem.
Security experts from Trend Micro reported the availability of a new variant of the popular AndroRAT.
The malware was first born in 2012 as a university project, designed as an open-source client/server application to offer remote control of a device. Unfortunately, hackers noticed the capabilities of the threat and started using it.
The new version includes the code to trigger the CVE-2015-1805, it is a local elevation of privilege flaw that affects the kernel of the Android OS of certain devices.
The vulnerability is ranked as critical and can be exploited by rooting applications that users have installed on their devices to elevate privileges and run arbitrary code on the vulnerable device.
The security flaw is very old, it was discovered in the upstream Linux kernel years ago and fixed in April 2014. Unfortunately, the flaw was underestimated until last early 2016 when the C0RE Team reported to Google that it was possible to exploit it to target the Android OS.
All unpatched Android devices running OS based on kernel versions 3.4, 3.10 and 3.14, including all Nexus devices are vulnerable to the CVE-2015-1805 vulnerability.
“Trend Micro detected a new variant of Android Remote Access Tool (AndroRAT) (identified as ANDROIDOS_ANDRORAT.HRXC) that has the ability to inject root exploits to perform malicious tasks such as silent installation, shell command execution, WiFi password collection, and screen capture.” states the analysis published by Trend Micro.
The new AndroRAT variant masquerades as a utility app called TrashCleaner that is likely delivered from a malicious URL. Once launched, the TrashCleaner will prompt the user to install a Chinese-labeled calculator app, hide its icon from the device’s UI, and activates the RAT in the background.

The new variant included the following additional features:
Theft of mobile network information, storage capacity, rooted or not
Theft of list of installed applications
Theft of web browsing history from pre-installed browsers
Theft of calendar events
Record calls
Upload files to victim device
Use front camera to capture high resolution photos
Delete and send forged SMS
Screen capture
Shell command execution
Theft of WiFi passwords
Enabling accessibility services for a key logger silently
Experts recommend downloading apps only from official stores and keeping updated the OS and the apps.
Necurs botnet is behind seasonal campaigns of Valentine’s Day-themed spam
14.2.2018 securityaffairs BotNet
Necurs botnet made headline again, the experts at IBM X-Force research team observed a spike in seasonal campaigns of Valentine’s Day-themed spam emails.
Necurs botnet made headline again, the experts at IBM X-Force research team observed a spike in the activity of the infamous botnet.
Necurs was not active for a long period at the beginning of 2017 and resumed it activity in April 2017. The Necurs botnet was used in the past months to push many other malware, including Locky, Jaff, GlobeImposter, Dridex , Scarab and the Trickbot.
Scammers are mow using the Necurs botnet to send out an amazing number of messages offering companionship waiting for Valentine’s day.
Crooks are using the spam messages to trick victims into sharing personal photos that are used later by cybercriminals to blackmail the victims.
According to the IBM X-Force team, the campaign started in mid-January, it leverages the overall Necurs botnet that is composed of 6 million bots.
“The current campaign from Necurs reached over 230 million spam messages within a matter of two weeks as the botnet spewed tens of millions of messages in two major bouts. The first surge started on Jan. 16 and ran through Jan. 18; the second started on Jan. 27 and died down on Feb. 3.” reads the analysis published by X-Force researchers.
The expert spotted two current campaigns that sent out a total 230 million spam messages in 14 days-period.

The first campaign reached a peak between Jan. 16 and Jan. 18 and the second one began on Jan. 27 and lasted through Feb. 3. Researchers observed an average 30 million spam messages were sent each day.
“Looking at the messages being sent out in excess of 30 million emails a day, the current campaign delivers short email blurbs from supposed Russian women living in the U.S. While typical spam email is notorious for bad spelling and grammar, these samples are rather well-worded.” continues the analysis.”
The experts determined that the spam messages are being sent from about 950,000 unique IP addresses, Most of IP are hosted in Vietnam and India while the top sender IP address is hosted via a Pakistani-based ISP.
“Together, Vietnam and India hosted 55 percent of the IPs from which the spam originated. It’s worth noting that spammers constantly shuffle the resources they leverage and the originating IPs logged in one campaign are not likely to be used in the next one. This is how fraudsters avoid blacklists and blocking.” added the researchers.
After the takedowns of the Andromeda and Avalanche botnets, Necurs remains the largest spam distributor in the cybercrime ecosystem. Crooks will continue to leverage the Necurs botnet for their spam campaigns, for this reason, the most effective countermeasure is to increase employee awareness on such kind of threats.
Hackers in the Russian underground exploited a Telegram Zero-Day vulnerability to deliver malware
14.2.2018 securityaffairs Exploit Virus
Security researcher Alexey Firsh at Kaspersky Lab last discovered a Telegram zero-day in the desktop Windows version that was exploited in attacks in the wild.
Security researcher Alexey Firsh at Kaspersky Lab last discovered a zero-day vulnerability in the desktop Windows version of the popular Telegram instant messaging app.
The bad news is that the Telegram zero-day flaw was being exploited by threat actors in the wild to deliver cryptocurrency miners for Monero and ZCash.
According to the expert, hackers have actively exploited the vulnerability since at least March 2017. Attackers tricked victims into downloading cryptocurrency miners or to establish a backdoor.
“In October 2017, we learned of a vulnerability in Telegram Messenger’s Windows client that was being exploited in the wild. It involves the use of a classic right-to-left override attack when a user sends files over the messenger service.” reads the analysis of the expert.
The flaw is related to the way Telegram Windows client handles the RLO (right-to-left override) Unicode character (U+202E), which is used for any language that uses a right to left writing mode, like Arabic or Hebrew.
The attackers used a hidden RLO Unicode character in the file name that reversed the order of the characters, in this way the file name could be renamed. In a real attack scenario, then the attackers sent the file to the target recipient.
The crooks craft a malicious code to be sent in a message, let assume it is a JS file that is renamed as follows:
evil.js -> photo_high_re*U+202E*gnp.js (— *U+202E* is the RLO character)
The RLO character included in the file name is used by an attacker to display the string gnp.js in reverse masquerading the fact that the file is a js and tricking the victims into believing that it is a harmless .png image.

When the user clicks on the file, Windows displays a security notification if it hasn’t been disabled in the system’s settings.

If the user ignores the notification and clicks on ‘Run’, the malicious code executed.
The expert reported the Telegram zero-day to the company that promptly patched the flaw.
“Kaspersky Lab reported the vulnerability to Telegram and, at the time of publication, the zero-day flaw has not since been observed in messenger’s products.” states the analysis published by Kaspersky.
“During their analysis, Kaspersky Lab experts identified several scenarios of zero-day exploitation in the wild by threat actors.”
The analysis of the servers used by the attackers revealed the presence of archives containing a Telegram’s local cache, this means that threat actors exploited the flaw to steal data from the victims.
In another attack scenario, crooks triggered the flaw to install a malware that leverages the Telegram API as a command and control mechanism.
“Secondly, upon successful exploitation of the vulnerability, a backdoor that used the Telegram API as a command and control protocol was installed, resulting in the hackers gaining remote access to the victim’s computer. After installation, it started to operate in a silent mode, which allowed the threat actor to remain unnoticed in the network and execute different commands including the further installation of spyware tools.” continues the analysis.
According to the researcher, the flaw was known only in the Russia crime community, it was not triggered by other crooks.
To mitigate the attack, download and open files only from trusted senders.
The security firm also recommended users to avoid sharing any sensitive personal information in messaging apps and make sure to have a good antivirus software from reliable company installed on your systems.