4.3.24 Exploit The Hacker News

How Cybercriminals are Exploiting India's UPI for Money Laundering Operations
4.3.24 Exploit The Hacker News
Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme.
The malicious application, called XHelper, is a "key tool for onboarding and managing these money mules," CloudSEK researchers Sparsh Kulshrestha, Abhishek Mathew, and Santripti Bhujel said in a report.
Details about the scam first emerged in late October 2023, when Chinese cyber criminals were found to take advantage of the fact that Indian Unified Payments Interface (UPI) service providers operate without coverage under the Prevention of Money Laundering Act (PMLA) to initiate illegal transactions under the guise of offering an instant loan.
The ill-gotten proceeds from the operation are transferred to other accounts belonging to hired mules, who are recruited from Telegram in return for commissions ranging from 1-2% of the total transaction amounts.
"Central to this operation are Chinese payment gateways exploiting the QR code feature of UPI with precision," the cybersecurity company noted at the time.
"The scheme leveraged a network exceeding hundreds of thousands of compromised 'money mule' accounts to funnel illicit funds through fraudulent payment channels, ultimately transferring them back to China."
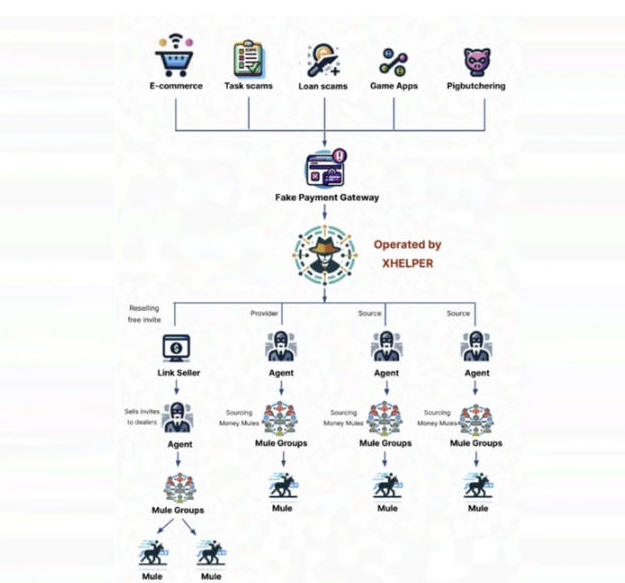
These mules are efficiently managed using XHelper, which also facilitates the technology behind fake payment gateways used in pig butchering and other scams. The app is distributed via websites masquerading as legitimate businesses under the guise of "Money Transfer Business."
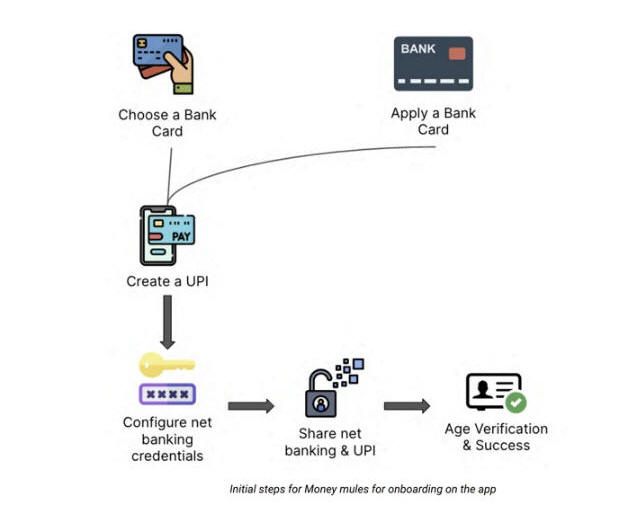
The app further offers the capability for mules to track their earnings and streamline the whole process of payouts and collection. This involves an initial setup process where they are asked to register their unique UPI IDs in a particular format and configure online banking credentials.
While payouts mandate the swift transfer of funds to pre-designated accounts within 10 minutes, collection orders are more passive in nature, with the registered accounts receiving incoming funds from other scammers utilizing the platform.
"Money mules activate order intake within the XHelper app, enabling them to receive and fulfill money laundering tasks," the researchers said. "The system automatically assigns orders, potentially based on predetermined criteria or mule profiles."
Once an illicit fund transfer is executed using the linked bank account, mules are also expected to upload proof of the transaction in the form of screenshots, which are then validated in exchange for financial rewards, thereby incentivizing continued participation.
XHelper's features also extend to inviting others to join as agents, who are in charge of recruiting the mules. It manifests as a referral system that allows them to get bonuses for each new recruit, thus driving an ever-expanding network of agents and mules.
"This referral system follows a pyramid-like structure, fueling mass recruitment of both agents and money mules, amplifying the reach of illicit activities," the researchers said. "Agents, in turn, recruit more mules and invite additional agents, perpetuating the growth of this interconnected network."
Another of XHelper's notable functions is to help train mules to efficiently launder stolen funds using a Learning Management System (LMS) that offers tutorials on opening fake corporate bank accounts (which have higher transaction limits), the different workflows, and ways to earn more commission.
Besides favoring the UPI feature built into legitimate banking apps for conducting the transfers, the platform acts as a hub for finding ways to get around account freezes to enable mules to continue their illegal activities. They are also given training to handle customer support calls made by banks for verifying suspicious transactions.
"While XHelper serves as a concerning example, it's crucial to recognize this isn't an isolated incident," CloudSEK said, adding it discovered a "growing ecosystem of similar applications facilitating money laundering across various scams."
In December 2023, Europol announced that 1,013 individuals were arrested in the second half of 2023 as part of a global effort to tackle money laundering. The international law enforcement operation also led to the identification of 10,759 money mules and 474 recruiters (aka herders).
The disclosure comes as Kaspersky revealed that malware, adware, and riskware attacks on mobile devices rose steadily from February 2023 until the end of the year.
"Android malware and riskware activity surged in 2023 after two years of relative calm, returning to early 2021 levels by the end of the year," the Russian security vendor noted. "Adware accounted for the majority of threats detected in 2023."