
In a hypothetical attack scenario, a bad actor could enter the license plate of a Kia vehicle in a custom dashboard, retrieve the victim's information, and then execute commands on the vehicle after around 30 seconds.
Exploit 2024 2023 2022 2021 2020
Hackers Could Have Remotely Controlled Kia Cars Using Only License Plates
26.9.24 Exploit The Hacker News
Cybersecurity researchers have disclosed a set of now patched vulnerabilities in Kia vehicles that, if successfully exploited, could have allowed remote control over key functions simply by using only a license plate.
"These attacks could be executed remotely on any hardware-equipped vehicle in about 30 seconds, regardless of whether it had an active Kia Connect subscription," security researchers Neiko Rivera, Sam Curry, Justin Rhinehart, and Ian Carroll said.
The issues impact almost all vehicles made after 2013, even letting attackers covertly gain access to sensitive information including the victim's name, phone number, email address, and physical address.
Essentially, this could then be abused by the adversary to add themselves as an "invisible" second user on the car without the owner's knowledge.
The crux of the research is that the issues exploit the Kia dealership infrastructure ("kiaconnect.kdealer[.]com") used for vehicle activations to register for a fake account via an HTTP request and then generate access tokens.
The token is subsequently used in conjunction with another HTTP request to a dealer APIGW endpoint and the vehicle identification number (VIN) of a car to obtain the vehicle owner's name, phone number, and email address.
What's more, the researchers found that it's possible to gain access to a victim's vehicle by as trivially as issuing four HTTP requests, and ultimately executing internet-to-vehicle commands -
Generate the dealer token and retrieve the "token" header from the HTTP response using the aforementioned method
Fetch victim's email address and phone number
Modify owner's previous access using leaked email address and VIN number to add the attacker as the primary account holder
Add attacker to victim vehicle by adding an email address under their control as the primary owner of the vehicle, thereby allowing for running arbitrary commands
"From the victim's side, there was no notification that their vehicle had been accessed nor their access permissions modified," the researchers pointed out.
"An attacker could resolve someone's license plate, enter their VIN through the API, then track them passively and send active commands like unlock, start, or honk."

In a hypothetical attack scenario, a bad actor could enter the license plate of a Kia vehicle in a custom dashboard, retrieve the victim's information, and then execute commands on the vehicle after around 30 seconds.
Following responsible disclosure in June 2024, the flaws were addressed by Kia as of August 14, 2024. There is no evidence that these vulnerabilities were ever exploited in the wild.
"Cars will continue to have vulnerabilities, because in the same way that Meta could introduce a code change which would allow someone to take over your Facebook account, car manufacturers could do the same for your vehicle," the researchers said.
Cybersecurity Researchers Warn of New Rust-Based Splinter Post-Exploitation Tool
25.9.24 Exploit The Hacker News
Cybersecurity researchers have flagged the discovery of a new post-exploitation red team tool called Splinter in the wild.
Palo Alto Networks Unit 42 shared its findings after it discovered the program on several customers' systems.
"It has a standard set of features commonly found in penetration testing tools and its developer created it using the Rust programming language," Unit 42's Dominik Reichel said. "While Splinter is not as advanced as other well-known post-exploitation tools like Cobalt Strike, it still presents a potential threat to organizations if it is misused."
Penetration testing tools are often used for red team operations to flag potential security issues in a company's network. However, such adversary simulation tools can also be weaponized by threat actors to their advantage.
Unit 42 said it has not detected any threat actor activity associated with the Splinter tool set. There is no information as yet on who developed the tool.
Artifacts unearthed by the cybersecurity firm reveal that they are "exceptionally large," coming in around 7 MB, primarily owing to the presence of 61 Rust crates within it.
Splinter is no different than other post-exploitation frameworks in that it comes with a configuration that includes information about the command-and-control (C2) server, which is parsed in order to establish contact with the server using HTTPS.
"Splinter implants are controlled by a task-based model, which is common among post-exploitation frameworks," Reichel noted. "It obtains its tasks from the C2 server the attacker has defined."
Some of the functions of the tool include executing Windows commands, running modules via remote process injection, uploading and downloading files, collecting cloud service account info, and deleting itself from the system.
"The increasing variety underscores the importance of staying up to date on prevention and detection capabilities, since criminals are likely to adopt any techniques that are effective for compromising organizations," Reichel said.
The disclosure comes as Deep Instinct detailed two attack methods that could be exploited by threat actors to achieve stealthy code injection and privilege escalation by leveraging an RPC interface in Microsoft Office and a malicious shim, respectively.
"We applied a malicious shim in a process without registering an SDB file on the system," researchers Ron Ben-Yizhak and David Shandalov said. "We effectively bypassed EDR detection by writing to a child process and loading the target DLL from the suspended child process before any EDR hook can be established."
In July 2024, Check Point also shed light on a new process injection technique called Thread Name-Calling that allows to implant of a shellcode into a running process by abusing the API for thread descriptions while bypassing endpoint protection products.
"As new APIs are added to Windows, new ideas for injection techniques are appearing," security researcher Aleksandra "Hasherezade" Doniec said.
"Thread Name-Calling uses some of the relatively new APIs. However, it cannot avoid incorporating older well-known components, such as APC injections – APIs which should always be taken into consideration as a potential threat. Similarly, the manipulation of access rights within a remote process is a suspicious activity."
Ivanti Warns of Active Exploitation of Newly Patched Cloud Appliance Vulnerability
14.9.24 Exploit The Hacker News
Ivanti has revealed that a newly patched security flaw in its Cloud Service Appliance (CSA) has come under active exploitation in the wild.
The high-severity vulnerability in question is CVE-2024-8190 (CVSS score: 7.2), which allows remote code execution under certain circumstances.
"An OS command injection vulnerability in Ivanti Cloud Services Appliance versions 4.6 Patch 518 and before allows a remote authenticated attacker to obtain remote code execution," Ivanti noted in an advisory released earlier this week. "The attacker must have admin level privileges to exploit this vulnerability."
The flaw impacts Ivanti CSA 4.6, which has currently reached end-of-life status, requiring that customers upgrade to a supported version going forward. That said, it has been addressed in CSA 4.6 Patch 519.
"With the end-of-life status this is the last fix that Ivanti will backport for this version," the Utah-based IT software company added. "Customers must upgrade to Ivanti CSA 5.0 for continued support."
"CSA 5.0 is the only supported version and does not contain this vulnerability. Customers already running Ivanti CSA 5.0 do not need to take any additional action."
On Friday, Ivanti updated its advisory to note that it observed confirmed exploitation of the flaw in the wild targeting a "limited number of customers."
It did not reveal additional specifics related to the attacks or the identity of the threat actors weaponizing it, however, a number of other vulnerabilities in Ivanti products have been exploited as a zero-day by China-nexus cyberespionage groups.
The development has prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to add the shortcoming to its Known Exploited Vulnerabilities (KEV) catalog, requiring federal agencies to apply the fixes by October 4, 2024.
The disclosure also comes as cybersecurity company Horizon3.ai posted a detailed technical analysis of a critical deserialization vulnerability (CVE-2024-29847, CVSS score: 10.0) impacting Endpoint Manager (EPM) that results in remote code execution.
Apple Vision Pro Vulnerability Exposed Virtual Keyboard Inputs to Attackers
14.9.24 Exploit The Hacker News
Details have emerged about a now-patched security flaw impacting Apple's Vision Pro mixed reality headset that, if successfully exploited, could allow malicious attackers to infer data entered on the device's virtual keyboard.
The attack, dubbed GAZEploit, has been assigned the CVE identifier CVE-2024-40865.
"A novel attack that can infer eye-related biometrics from the avatar image to reconstruct text entered via gaze-controlled typing," a group of academics from the University of Florida, CertiK Skyfall Team, and Texas Tech University said.
"The GAZEploit attack leverages the vulnerability inherent in gaze-controlled text entry when users share a virtual avatar."
Following responsible disclosure, Apple addressed the issue in visionOS 1.3 released on July 29, 2024. It described the vulnerability as impacting a component called Presence.
"Inputs to the virtual keyboard may be inferred from Persona," it said in a security advisory, adding it resolved the problem by "suspending Persona when the virtual keyboard is active."
In a nutshell, the researchers found that it was possible to analyze a virtual avatar's eye movements (or "gaze") to determine what the user wearing the headset was typing on the virtual keyboard, effectively compromising their privacy.
As a result, a threat actor could, hypothetically, analyze virtual avatars shared via video calls, online meeting apps, or live streaming platforms and remotely perform keystroke inference. This could then be exploited to extract sensitive information such as passwords.
The attack, in turn, is accomplished by means of a supervised learning model trained on Persona recordings, eye aspect ratio (EAR), and eye gaze estimation to differentiate between typing sessions and other VR-related activities (e.g., watching movies or playing games).
In the subsequent step, the gaze estimation directions on the virtual keyboard are mapped to specific keys in order to determine the potential keystrokes in a manner such that it also takes into account the keyboard's location in the virtual space.
"By remotely capturing and analyzing the virtual avatar video, an attacker can reconstruct the typed keys," the researchers said. "Notably, the GAZEploit attack is the first known attack in this domain that exploits leaked gaze information to remotely perform keystroke inference."
Progress WhatsUp Gold Exploited Just Hours After PoC Release for Critical Flaw
14.9.24 Exploit The Hacker News
Malicious actors are likely leveraging publicly available proof-of-concept (PoC) exploits for recently disclosed security flaws in Progress Software WhatsUp Gold to conduct opportunistic attacks.
The activity is said to have commenced on August 30, 2024, a mere five hours after a PoC was released for CVE-2024-6670 (CVSS score: 9.8) by security researcher Sina Kheirkhah of the Summoning Team, who is also credited with discovering and reporting CVE-2024-6671 (CVSS scores: 9.8).
Both the critical vulnerabilities, which allow an unauthenticated attacker to retrieve a user's encrypted password, were patched by Progress in mid-August 2024.
"The timeline of events suggests that despite the availability of patches, some organizations were unable to apply them quickly, leading to incidents almost immediately following the PoC's publication," Trend Micro researchers Hitomi Kimura and Maria Emreen Viray said in a Thursday analysis.
The attacks observed by the cybersecurity company involve bypassing WhatsUp Gold authentication to exploit the Active Monitor PowerShell Script and ultimately download various remote access tools for gaining persistence on the Windows host.
This includes Atera Agent, Radmin, SimpleHelp Remote Access, and Splashtop Remote, with both Atera Agent and Splashtop Remote installed by means of a single MSI installer file retrieved from a remote server.

"The polling process NmPoller.exe, the WhatsUp Gold executable, seems to be able to host a script called Active Monitor PowerShell Script as a legitimate function," the researchers explained. "The threat actors in this case chose it to perform for remote arbitrary code execution."
While no follow-on exploitation actions have been detected, the use of several remote access software points to the involvement of a ransomware actor.
This is the second time security vulnerabilities in WhatsUp Gold have been actively weaponized in the wild. Early last month, the Shadowserver Foundation said it had observed exploitation attempts against CVE-2024-4885 (CVSS score: 9.8), another critical bug that was resolved by Progress in June 2024.
The disclosure comes weeks after Trend Micro also revealed that threat actors are exploiting a now-patched security flaw in Atlassian Confluence Data Center and Confluence Server (CVE-2023-22527, CVSS score: 10.0) to deliver the Godzilla web shell.
"The CVE-2023-22527 vulnerability continues to be widely exploited by a wide range of threat actors who abuse this vulnerability to perform malicious activities, making it a significant security risk to organizations worldwide," the company said.
North Korean Hackers Deploy FudModule Rootkit via Chrome Zero-Day Exploit
1.9.24 Exploit The Hacker News
A recently patched security flaw in Google Chrome and other Chromium web browsers was exploited as a zero-day by North Korean actors in a campaign designed to deliver the FudModule rootkit.
The development is indicative of the persistent efforts made by the nation-state adversary, which had made a habit of incorporating rafts of Windows zero-day exploits into its arsenal in recent months.
Microsoft, which detected the activity on August 19, 2024, attributed it to a threat actor it tracks as Citrine Sleet (formerly DEV-0139 and DEV-1222), which is also known as AppleJeus, Labyrinth Chollima, Nickel Academy, and UNC4736. It's assessed to be a sub-cluster within the Lazarus Group (aka Diamond Sleet and Hidden Cobra).
It's worth mentioning that the use of the AppleJeus malware has been previously also attributed by Kaspersky to another Lazarus subgroup called BlueNoroff (aka APT38, Nickel Gladstone, and Stardust Chollima), indicative of the infrastructure and toolset sharing between these threat actors.
"Citrine Sleet is based in North Korea and primarily targets financial institutions, particularly organizations and individuals managing cryptocurrency, for financial gain," the Microsoft Threat Intelligence team said.
"As part of its social engineering tactics, Citrine Sleet has conducted extensive reconnaissance of the cryptocurrency industry and individuals associated with it."
The attack chains typically involve setting up fake websites masquerading as legitimate cryptocurrency trading platforms that seek to trick users into installing weaponized cryptocurrency wallets or trading applications that facilitate the theft of digital assets.
The observed zero-day exploit attack by Citrine Sleet involved the exploitation of CVE-2024-7971, a high-severity type confusion vulnerability in the V8 JavaScript and WebAssembly engine that could allow threat actors to gain remote code execution (RCE) in the sandboxed Chromium renderer process. It was patched by Google as part of updates released last week.
As previously stated by The Hacker News, CVE-2024-7971 is the third actively exploited type confusion bug in V8 that Google resolved this year after CVE-2024-4947 and CVE-2024-5274.
It's currently not clear how widespread these attacks were or who was targeted, but the victims are said to have been directed to a malicious website named voyagorclub[.]space likely through social engineering techniques, thereby triggering an exploit for CVE-2024-7971.
The RCE exploit, for its part, paves the way for the retrieval of shellcode containing a Windows sandbox escape exploit (CVE-2024-38106) and the FudModule rootkit, which is used to establish admin-to-kernel access to Windows-based systems to allow read/write primitive functions and perform [direct kernel object manipulation]."
CVE-2024-38106, a Windows kernel privilege escalation bug, is one of the six actively exploited security flaws that Microsoft remediated as part of its August 2024 Patch Tuesday update. That said, the Citrine Sleet-linked exploitation of the flaw has been found to have occurred after the fix was released.
"This may suggest a 'bug collision,' where the same vulnerability is independently discovered by separate threat actors, or knowledge of the vulnerability was shared by one vulnerability researcher to multiple actors," Microsoft said.
CVE-2024-7971 is also the third vulnerability that North Korean threat actors have leveraged this year to drop the FudModule rootkit, following CVE-2024-21338 and CVE-2024-38193, both of which are privilege escalation flaws in the built-in Windows drivers and were fixed by Microsoft in February and August.
"The CVE-2024-7971 exploit chain relies on multiple components to compromise a target, and this attack chain fails if any of these components are blocked, including CVE-2024-38106," the company said.
"Zero-day exploits necessitate not only keeping systems up to date, but also security solutions that provide unified visibility across the cyberattack chain to detect and block post-compromise attacker tools and malicious activity following exploitation."
Russian Hackers Exploit Safari and Chrome Flaws in High-Profile Cyberattack
30.8.24 Exploit The Hacker News
Cybersecurity researchers have flagged multiple in-the-wild exploit campaigns that leveraged now-patched flaws in Apple Safari and Google Chrome browsers to infect mobile users with information-stealing malware.
"These campaigns delivered n-day exploits for which patches were available, but would still be effective against unpatched devices," Google Threat Analysis Group (TAG) researcher Clement Lecigne said in a report shared with The Hacker News.
The activity, observed between November 2023 and July 2024, is notable for delivering the exploits by means of a watering hole attack on Mongolian government websites, cabinet.gov[.]mn and mfa.gov[.]mn.
The intrusion set has been attributed with moderate confidence to a Russian state-backed threat actor codenamed APT29 (aka Midnight Blizzard), with parallels observed between the exploits used in the campaigns and those previously linked to commercial surveillance vendors (CSVs) Intellexa and NSO Group, indicating exploit reuse.
The vulnerabilities at the center of the campaigns are listed below -
CVE-2023-41993 - A WebKit flaw that could result in arbitrary code execution when processing specially crafted web content (Fixed by Apple in iOS 16.7 and Safari 16.6.1 in September 2023)
CVE-2024-4671 - A use-after-free flaw in Chrome's Visuals component that could result in arbitrary code execution (Fixed by Google in Chrome version 124.0.6367.201/.202 for Windows and macOS, and version 124.0.6367.201 for Linux in May 2024)
CVE-2024-5274 - A type confusion flaw in the V8 JavaScript and WebAssembly engine that could result in arbitrary code execution (Fixed by Google in Chrome version 125.0.6422.112/.113 for Windows and macOS, and version 125.0.6422.112 for Linux in May 2024)
The November 2023 and February 2024 campaigns are said to have involved the compromises of the two Mongolian government websites – both in the first and only mfa.gov[.]mn in the latter – to deliver an exploit for CVE-2023-41993 by means of a malicious iframe component pointing to an actor-controlled domain.

"When visited with an iPhone or iPad device, the watering hole sites used an iframe to serve a reconnaissance payload, which performed validation checks before ultimately downloading and deploying another payload with the WebKit exploit to exfiltrate browser cookies from the device," Google said.
The payload is a cookie stealer framework that Google TAG previously detailed in connection with the 2021 exploitation of an iOS zero-day (CVE-2021-1879) to harvest authentication cookies from several popular websites, including Google, Microsoft, LinkedIn, Facebook, Yahoo, GitHub, and Apple iCloud, and send them via WebSocket to an attacker-controlled IP address.
"The victim would need to have a session open on these websites from Safari for cookies to be successfully exfiltrated," Google noted at the time, adding "attackers used LinkedIn messaging to target government officials from western European countries by sending them malicious links."
The fact that the cookie stealer module also singles out the website "webmail.mfa.gov[.]mn" suggests that Mongolian government employees were a likely target of the iOS campaign.
The mfa.gov[.]mn website was infected a third time in July 2024 to inject JavScript code that redirected Android users using Chrome to a malicious link that served an exploit chain combining the flaws CVE-2024-5274 and CVE-2024-4671 to deploy a browser information stealing payload.

In particular, the attack sequence uses CVE-2024-5274 to compromise the renderer and CVE-2024-4671 to achieve a sandbox escape vulnerability, ultimately making it possible to break out of Chrome site isolation protections and deliver a stealer malware that can pilfer cookies, passwords, credit card data, browser history, and trust tokens.
"This campaign delivers a simple binary deleting all Chrome Crash reports and exfiltrating the following Chrome databases back to the track-adv[.]com server – similar to the basic final payload seen in the earlier iOS campaigns," Google TAG noted.
The tech giant further said the exploits used in the November 2023 watering hole attack and by Intellexa in September 2023 share the same trigger code, a pattern also observed in the triggers for CVE-2024-5274 used in the July 2024 watering hole attack and by NSO Group in May 2024.
What's more, the exploit for CVE-2024-4671 is said to share similarities with a previous Chrome sandbox escape that Intellexa was discovered as using in the wild in connection with another Chrome flaw CVE-2021-37973, which was addressed by Google in September 2021.
While it's currently not clear how the attackers managed to acquire the exploits for the three flaws, the findings make it amply clear that nation-state actors are using n-day exploits that were originally used as zero-days by CSVs.
It, however, raises the possibility that the exploits may have been procured from a vulnerability broker who previously sold them to the spyware vendors as zero-days, a steady supply of which keeps the ball rolling as Apple and Google shore up defenses.
"Moreover, watering hole attacks remain a threat where sophisticated exploits can be utilized to target those that visit sites regularly, including on mobile devices," the researchers said. "Watering holes can still be an effective avenue for n-day exploits by mass targeting a population that might still run unpatched browsers."
Chinese Hackers Exploit Zero-Day Cisco Switch Flaw to Gain System Control
23.8.24 Exploit The Hacker News
Details have emerged about a China-nexus threat group's exploitation of a recently disclosed, now-patched security flaw in Cisco switches as a zero-day to seize control of the appliance and evade detection.
The activity, attributed to Velvet Ant, was observed early this year and involved the weaponization of CVE-2024-20399 (CVSS score: 6.0) to deliver bespoke malware and gain extensive control over the compromised system, facilitating both data exfiltration and persistent access.
"The zero-day exploit allows an attacker with valid administrator credentials to the Switch management console to escape the NX-OS command line interface (CLI) and execute arbitrary commands on the Linux underlying operating system," cybersecurity company Sygnia said in a report shared with The Hacker News.
Velvet Ant first caught the attention of researchers at the Israeli cybersecurity company in connection with a multi-year campaign that targeted an unnamed organization located in East Asia by leveraging legacy F5 BIG-IP appliances as a vantage point for setting up persistence on the compromised environment.
The threat actor's stealthy exploitation of CVE-2024-20399 came to light early last month, prompting Cisco to issue security updates to release the flaw.

Notable among the tradecraft is the level of sophistication and shape-shifting tactics adopted by the group, initially infiltrating new Windows systems before moving to legacy Windows servers and network devices in an attempt to fly under the radar.
"The transition to operating from internal network devices marks yet another escalation in the evasion techniques used in order to ensure the continuation of the espionage campaign," Sygnia said.
The latest attack chain entails breaking into a Cisco switch appliance using CVE-2024-20399 and conducting reconnaissance activities, subsequently pivoting to more network devices and ultimately executing a backdoor binary by means of a malicious script.
The payload, dubbed VELVETSHELL, is an amalgamation of two open-source tools, a Unix backdoor named Tiny SHell and a proxy utility called 3proxy. It also supports capabilities to execute arbitrary commands, download/upload files, and establish tunnels for proxying network traffic.
"The modus-operandi of 'Velvet Ant' highlights risks and questions regarding third-party appliances and applications that organizations onboard," the company said. "Due to the 'black box' nature of many appliances, each piece of hardware or software has the potential to turn into the attack surface that an adversary is able to exploit."
Hackers Exploit PHP Vulnerability to Deploy Stealthy Msupedge Backdoor
21.8.24 Exploit The Hacker News
A previously undocumented backdoor named Msupedge has been put to use against a cyber attack targeting an unnamed university in Taiwan.
"The most notable feature of this backdoor is that it communicates with a command-and-control (C&C) server via DNS traffic," the Symantec Threat Hunter Team, part of Broadcom, said in a report shared with The Hacker News.
The origins of the backdoor are presently unknown as are the objectives behind the attack.
The initial access vector that likely facilitated the deployment of Msupedge is said to involve the exploitation of a recently disclosed critical flaw impacting PHP (CVE-2024-4577, CVSS score: 9.8), which could be used to achieve remote code execution.
The backdoor in question is a dynamic-link library (DLL) that's installed in the paths "csidl_drive_fixed\xampp\" and "csidl_system\wbem\." One of the DLLs, wuplog.dll, is launched by the Apache HTTP server (httpd). The parent process for the second DLL is unclear.
The most notable aspect of Msupedge is its reliance on DNS tunneling for communication with the C&C server, with code based on the open-source dnscat2 tool.
"It receives commands by performing name resolution," Symantec noted. "Msupedge not only receives commands via DNS traffic but also uses the resolved IP address of the C&C server (ctl.msedeapi[.]net) as a command."
Specifically, the third octet of the resolved IP address functions as a switch case that determines the behavior of the backdoor by subtracting seven from it and using its hexadecimal notation to trigger appropriate responses. For example, if the third octet is 145, the newly derived value translates to 138 (0x8a).
The commands supported by Msupedge are listed below -
0x8a: Create a process using a command received via a DNS TXT record
0x75: Download file using a download URL received via a DNS TXT record
0x24: Sleep for a predetermined time interval
0x66: Sleep for a predetermined time interval
0x38: Create a temporary file "%temp%\1e5bf625-1678-zzcv-90b1-199aa47c345.tmp" whose purpose is unknown
0x3c: Delete the file "%temp%\1e5bf625-1678-zzcv-90b1-199aa47c345.tmp"
The development comes as the UTG-Q-010 threat group has been linked to a new phishing campaign that leverages cryptocurrency- and job-related lures to distribute an open-source malware called Pupy RAT.
"The attack chain involves the use of malicious .lnk files with an embedded DLL loader, ending up in Pupy RAT payload deployment," Symantec said. "Pupy is a Python-based Remote Access Trojan (RAT) with functionality for reflective DLL loading and in-memory execution, among others."
Thousands of Oracle NetSuite Sites at Risk of Exposing Customer Information
20.8.24 Exploit The Hacker News
Oracle NetSuite Sites
Cybersecurity researchers are warning about the discovery of thousands of externally-facing Oracle NetSuite e-commerce sites that have been found susceptible to leaking sensitive customer information.
"A potential issue in NetSuite's SuiteCommerce platform could allow attackers to access sensitive data due to misconfigured access controls on custom record types (CRTs)," AppOmni's Aaron Costello said.
It's worth emphasizing here that the issue is not a security weakness in the NetSuite product, but rather a customer misconfiguration that can lead to leakage of confidential data. The information exposed includes full addresses and mobile phone numbers of registered customers of the e-commerce sites.
The attack scenario detailed by AppOmni exploits CRTs that employ table-level access controls with the "No Permission Required" access type, which grants unauthenticated users access to data by making use of NetSuite's record and search APIs.
That said, for this attack to succeed, there are a number of prerequisites, the foremost being need for the attacker to know the name of CRTs in use.
To mitigate the risk, it's recommended that site administrators tighten access controls on CRTs, set sensitive fields to "None" for public access, and consider temporarily taking impacted sites offline to prevent data exposure.
"The easiest solution from a security standpoint may involve changing the Access Type of the record type definition to either 'Require Custom Record Entries Permission' or 'Use Permission List,'" Costello said.
The disclosure comes as Cymulate detailed a way to manipulate the credential validation process in Microsoft Entra ID (formerly Azure Active Directory) and circumvent authentication in hybrid identity infrastructures, allowing attackers to sign in with high privileges inside the tenant and establish persistence.
The attack, however, requires an adversary to have admin access on a server hosting a Pass-Through Authentication (PTA) agent, a module that allows users to sign in to both on-premises and cloud-based applications using Entra ID. The issue is rooted in Entra ID when syncing multiple on-premises domains to a single Azure tenant.
"This issue arises when authentication requests are mishandled by pass-through authentication (PTA) agents for different on-prem domains, leading to potential unauthorized access," security researchers Ilan Kalendarov and Elad Beber said.
"This vulnerability effectively turns the PTA agent into a double agent, allowing attackers to log in as any synced AD user without knowing their actual password; this could potentially grant access to a global admin user if such privileges were assigned."
Xeon Sender Tool Exploits Cloud APIs for Large-Scale SMS Phishing Attacks
20.8.24 Exploit The Hacker NewsSMS Phishing Attacks
Malicious actors are using a cloud attack tool named Xeon Sender to conduct SMS phishing and spam campaigns on a large scale by abusing legitimate services.
"Attackers can use Xeon to send messages through multiple software-as-a-service (SaaS) providers using valid credentials for the service providers," SentinelOne security researcher Alex Delamotte said in a report shared with The Hacker News.
Examples of the services used to facilitate the en masse distribution of SMS messages include Amazon Simple Notification Service (SNS), Nexmo, Plivo, Proovl, Send99, Telesign, Telnyx, TextBelt, Twilio.
It's important to note here that the activity does not exploit any inherent weaknesses in these providers. Rather, the tool uses legitimate APIs to conduct bulk SMS spam attacks.
It joins tools like SNS Sender that have increasingly become a way to send bulk smishing messages and ultimately capture sensitive information from targets.
Distributed via Telegram and hacking forums, with one of the older versions crediting a Telegram channel devoted to advertising cracked hacktools. The most recent version, available for download as a ZIP file, attributes itself to a Telegram channel named Orion Toolxhub (oriontoolxhub) that has 200 members.
Orion Toolxhub was created on February 1, 2023. It has also freely made available other software for brute-force attacks, reverse IP address lookups, and others such as a WordPress site scanner, a PHP web shell, a Bitcoin clipper, and a program called YonixSMS that purports to offer unlimited SMS sending capabilities.
Xeon Sender is also referred to as XeonV5 and SVG Sender. Early versions of the Python-based program have been detected as early as 2022. It has since been repurposed by several threat actors for their own purposes.
"Another incarnation of the tool is hosted on a web server with a GUI," Delamotte said. "This hosting method removes a potential barrier to access, enabling lower skilled actors who may not be comfortable with running Python tools and troubleshooting their dependencies."
Xeon Sender, regardless of the variant used, offers its users a command-line interface that can be used to communicate with the backend APIs of the chosen service provider and orchestrate bulk SMS spam attacks.
This also means that the threat actors are already in possession of the necessary API keys required to access the endpoints. The crafted API requests also include the sender ID, the message contents, and one of the phone numbers selected from a predefined list present in a text file.
Xeon Sender, besides its SMS sending methods, incorporates features to validate Nexmo and Twilio account credentials, generate phone numbers for a given country code and area code, and check if a provided phone number is valid.
Despite a lack of finesse associated with the tool, SentinelOne said the source code is replete with ambiguous variables like single letters or a letter plus a number to make debugging a lot more challenging.
"Xeon Sender largely uses provider-specific Python libraries to craft API requests, which presents interesting detection challenges," Delamotte said. "Each library is unique, as are the provider's logs. It may be difficult for teams to detect abuse of a given service."
"To defend against threats like Xeon Sender, organizations should monitor activity related to evaluating or modifying SMS sending permissions or anomalous changes to distribution lists, such as a large upload of new recipient phone numbers."
Attackers Exploit Public .env Files to Breach Cloud Accounts in Extortion Campaign
17.8.24 Exploit The Hacker News
A large-scale extortion campaign has compromised various organizations by taking advantage of publicly accessible environment variable files (.env) that contain credentials associated with cloud and social media applications.
"Multiple security missteps were present in the course of this campaign, including the following: Exposing environment variables, using long-lived credentials, and absence of least privilege architecture," Palo Alto Networks Unit 42 said in a Thursday report.
The campaign is notable for setting its attack infrastructure within the infected organizations' Amazon Web Services (AWS) environments and using them as a launchpad for scanning more than 230 million unique targets for sensitive data.
With 110,000 domains targeted, the malicious activity is said to have netted over 90,000 unique variables in the .env files, out of which 7,000 belonged to organizations' cloud services and 1,500 variables are linked to social media accounts.
"The campaign involved attackers successfully ransoming data hosted within cloud storage containers," Unit 42 said. "The event did not include attackers encrypting the data before ransom, but rather they exfiltrated the data and placed the ransom note in the compromised cloud storage container."
The most striking aspect of the attacks is that it doesn't rely on security vulnerabilities or misconfigurations in cloud providers' services, but rather stems from the accidental exposure of .env files on unsecured web applications to gain initial access.
A successful breach of a cloud environment paves the way for extensive discovery and reconnaissance steps with an aim to broaden their foothold, with the threat actors weaponizing AWS Identity and Access Management (IAM) access keys to create new roles and escalate their privileges.
The new IAM role with administrative permissions is then used to create new AWS Lambda functions to initiate an automated internet-wide scanning operation containing millions of domains and IP addresses.
"The script retrieved a list of potential targets from a publicly accessible third-party S3 bucket exploited by the threat actor," Unit 42 researchers Margaret Zimmermann, Sean Johnstone, William Gamazo, and Nathaniel Quist said.
"The list of potential targets the malicious lambda function iterated over contained a record of victim domains. For each domain in the list, the code performed a cURL request, targeting any environment variable files exposed at that domain, (i.e., https://<target>/.env)."
Should the target domain host an exposed environment file, the cleartext credentials contained within the file are extracted and stored in a newly created folder within another threat actor-controlled public AWS S3 bucket. The bucket has since been taken down by AWS.
The attack campaign has been found to specifically single out instances where the .env files contain Mailgun credentials, indicating an effort on the part of the adversary to leverage them for sending phishing emails from legitimate domains and bypass security protections.
The infection chain ends with the threat actor exfiltrating and deleting sensitive data from the victim's S3 bucket, and uploading a ransom note that urges them to contact and pay a ransom to avoid selling the information on the dark web.
The financial motivations of the attack are also evident in the threat actor's failed attempts to create new Elastic Cloud Compute (EC2) resources for illicit cryptocurrency mining.
It's currently not clear who is behind the campaign, in part due to the use of VPNs and the TOR network to conceal their true origin, although Unit 42 said it detected two IP addresses that were geolocated in Ukraine and Morocco as part of the lambda function and S3 exfiltration activities, respectively.
"The attackers behind this campaign likely leveraged extensive automation techniques to operate successfully and rapidly," the researchers said. "This indicates that these threat actor groups are both skilled and knowledgeable in advanced cloud architectural processes and techniques."
CISA Warns of Hackers Exploiting Legacy Cisco Smart Install Feature
9.8.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has disclosed that threat actors are abusing the legacy Cisco Smart Install (SMI) feature with the aim of accessing sensitive data.
The agency said it has seen adversaries "acquire system configuration files by leveraging available protocols or software on devices, such as abusing the legacy Cisco Smart Install feature."
It also said it continues to observe weak password types used on Cisco network devices, thereby exposing them to password-cracking attacks. Password types refer to algorithms that are used to secure a Cisco device's password within a system configuration file.
Threat actors who are able to gain access to the device in this manner would be able to easily access system configuration files, facilitating a deeper compromise of the victim networks.
"Organizations must ensure all passwords on network devices are stored using a sufficient level of protection," CISA said, adding it recommends "type 8 password protection for all Cisco devices to protect passwords within configuration files."
It is also urging enterprises to review the National Security Agency's (NSA) Smart Install Protocol Misuse advisory and Network Infrastructure Security Guide for configuration guidance.
Additional best practices include the use of a strong hashing algorithm to store passwords, avoiding password reuse, assigning strong and complex passwords, and refraining from using group accounts that do not provide accountability.
The development comes as Cisco warned of the public availability of a proof-of-concept (PoC) code for CVE-2024-20419 (CVSS score: 10.0), a critical flaw impacting Smart Software Manager On-Prem (Cisco SSM On-Prem) that could enable a remote, unauthenticated attacker to change the password of any users.
The networking equipment major has also alerted of multiple critical shortcomings (CVE-2024-20450, CVE-2024-20452, and CVE-2024-20454, CVSS scores: 9.8) in Small Business SPA300 Series and SPA500 Series IP Phones that could permit an attacker to execute arbitrary commands on the underlying operating system or cause a denial-of-service (DoS) condition.
"These vulnerabilities exist because incoming HTTP packets are not properly checked for errors, which could result in a buffer overflow," Cisco said in a bulletin published on August 7, 2024.
"An attacker could exploit this vulnerability by sending a crafted HTTP request to an affected device. A successful exploit could allow the attacker to overflow an internal buffer and execute arbitrary commands at the root privilege level."
The company said it does not intend to release software updates to address the flaws, as the appliances have reached end-of-life (EoL) status, necessitating that users transition to newer models.
New Linux Kernel Exploit Technique 'SLUBStick' Discovered by Researchers
7.8.24 Exploit The Hacker News
Cybersecurity researchers have shed light on a novel Linux kernel exploitation technique dubbed SLUBStick that could be exploited to elevate a limited heap vulnerability to an arbitrary memory read-and-write primitive.
"Initially, it exploits a timing side-channel of the allocator to perform a cross-cache attack reliably," a group of academics from the Graz University of Technology said [PDF]. "Concretely, exploiting the side-channel leakage pushes the success rate to above 99% for frequently used generic caches."
Memory safety vulnerabilities impacting the Linux kernel have limited capabilities and are a lot more challenging to exploit owing to security features like Supervisor Mode Access Prevention (SMAP), Kernel address space layout randomization (KASLR), and kernel control flow integrity (kCFI).

While software cross-cache attacks have been devised as a way to counter kernel hardening strategies like coarse-grained heap separation, studies have shown that existing methods only have a success rate of only 40%.
SLUBStick has been demonstrated on versions 5.19 and 6.2 of the Linux kernel using nine security flaws (e.g., double free, use-after-free, and out-of-bounds write) discovered between 2021 and 2023, leading to privilege escalation to root with no authentication and container escapes.
The core idea behind the approach is to offer the ability to modify kernel data and obtain an arbitrary memory read-and- write primitive in a manner that reliably surmounts existing defences like KASLR.
However for this to work, the threat model assumes the presence of a heap vulnerability in the Linux kernel and that an unprivileged user has code execution capabilities.
"SLUBStick exploits more recent systems, including v5.19 and v6.2, for a wide variety of heap vulnerabilities," the researchers said.
Hackers Exploit Misconfigured Jupyter Notebooks with Repurposed Minecraft DDoS Tool
4.8.24 Exploit The Hacker News
Cybersecurity researchers have disclosed details of a new distributed denial-of-service (DDoS) attack campaign targeting misconfigured Jupyter Notebooks.
The activity, codenamed Panamorfi by cloud security firm Aqua, utilizes a Java-based tool called mineping to launch a TCP flood DDoS attack. Mineping is a DDoS package designed for Minecraft game servers.
Attack chains entail the exploitation of internet-exposed Jupyter Notebook instances to run wget commands for fetching a ZIP archive hosted on a file-sharing site called Filebin.
Cybersecurity
The ZIP file contains two Java archive (JAR) files, conn.jar and mineping.jar, with the former used to establish connections to a Discord channel and trigger the execution of the mineping.jar package.
"This attack aims to consume the resources of the target server by sending a large number of TCP connection requests," Aqua researcher Assaf Morag said. "The results are written to the Discord channel."

The attack campaign has been attributed to a threat actor who goes by the name yawixooo, whose GitHub account has a public repository containing a Minecraft server properties file.
This is not the first time internet-accessible Jupyter Notebooks have been targeted by adversaries. In October 2023, a Tunisian threat dubbed Qubitstrike was observed breaching Jupyter Notebooks in an attempt to illicitly mine cryptocurrency and breach cloud environments.
Proofpoint Email Routing Flaw Exploited to Send Millions of Spoofed Phishing Emails
29.7.24 Exploit The Hacker News
An unknown threat actor has been linked to a massive scam campaign that exploited an email routing misconfiguration in email security vendor Proofpoint's defenses to send millions of messages spoofing various popular companies like Best Buy, IBM, Nike, and Walt Disney, among others.
"These emails echoed from official Proofpoint email relays with authenticated SPF and DKIM signatures, thus bypassing major security protections — all to deceive recipients and steal funds and credit card details," Guardio Labs researcher Nati Tal said in a detailed report shared with The Hacker News.
The cybersecurity company has given the campaign the name EchoSpoofing. The activity is believed to have commenced in January 2024, with the threat actor exploiting the loophole to send as many as three million emails per day on average, a number that hit a peak of 14 million in early June as Proofpoint began to enact countermeasures.
"The most unique and powerful part of this domain is the spoofing method – leaving almost no chance to realize this is not a genuine email sent from those companies," Tal told the publication.
"This EchoSpoofing concept is really powerful. It's kind of strange it is being used for large-scale phishing like this instead of a boutique spear-phishing campaign – where an attacker can swiftly take any real company team member's identity and send emails to other co-workers – eventually, through high-quality social engineering, get access to internal data or credentials and even compromise the entire company.
The technique, which involves the threat actor sending the messages from an SMTP server on a virtual private server (VPS), is notable for the fact that it complies with authentication and security measures such as SPF and DKIM, which are short for Sender Policy Framework and DomainKeys Identified Mail, respectively, and refer to authentication methods that are designed to prevent attackers from imitating a legitimate domain.
Cybersecurity
It all goes back to the fact that these messages are routed from various adversary-controlled Microsoft 365 tenants, which are then relayed through Proofpoint enterprise customers' email infrastructures to reach users of free email providers such as Yahoo!, Gmail, and GMX.
This is the result of what Guardio described as a "super-permissive misconfiguration flaw" in Proofpoint servers ("pphosted.com") that essentially allowed spammers to take advantage of the email infrastructure to send the messages.
"The root cause is a modifiable email routing configuration feature on Proofpoint servers to allow relay of organizations' outbound messages from Microsoft 365 tenants, but without specifying which M365 tenants to allow," Proofpoint said in a coordinated disclosure report shared with The Hacker News.
"Any email infrastructure that offers this email routing configuration feature can be abused by spammers."

Put differently, an attacker can weaponize the shortcoming to set up rogue Microsoft 365 tenants and deliver spoofed email messages to Proofpoint's relay servers, from where they are "echoed back" as genuine digital missives impersonating the customers' domains.
This, in turn, is accomplished by configuring the Exchange Server's outgoing email connector directly to the vulnerable pphosted.com endpoint associated with the customer. Furthermore, a cracked version of a legitimate email delivery software called PowerMTA is used for sending the messages.

"The spammer used a rotating series of leased virtual private servers (VPS) from several providers, using many different IP addresses to initiate quick bursts of thousands of messages at a time from their SMTP servers, sent to Microsoft 365 to be relayed to Proofpoint-hosted customer servers," Proofpoint said.
"Microsoft 365 accepted these spoofed messages and sent them to these customers' email infrastructures to be relayed. When customer domains were spoofed while relaying through the matching customer's email infrastructure, DKIM signing was also applied as the messages transited through the Proofpoint infrastructure, making the spam messages more deliverable."
It's being suspected that EchoSpoofing was intentionally chosen by the operators as a way to generate illegal revenue as well as avoid the risk of exposure for extended periods of time, as directly targeting the companies via this modus operandi could have drastically increased the chances of getting detected, effectively imperiling the entire scheme.
That having said, it's currently not clear who is behind the campaign. Proofpoint said the activity does not overlap with any known threat actor or group.
"In March, Proofpoint researchers identified spam campaigns being relayed through a small number of Proofpoint customers' email infrastructure by sending spam from Microsoft 365 tenants," it said in a statement. "All analyses indicate this activity was conducted by one spam actor, whose activity we do not attribute to a known entity."
"Since discovering this spam campaign, we have worked diligently to provide corrective instructions, including implementing a streamlined administrative interface for customers to specify which M365 tenants are allowed to relay, with all other M365 tenants denied by default."
Proofpoint emphasized that no customer data was exposed, nor did any of them experience loss of data, as a result of these campaigns. It further noted that it reached out to some of its customers directly to change their settings to stop the effectiveness of the outbound relay spam activity.
"As we started to block the spammer's activity, the spammer accelerated its testing and moved quickly to other customers," the company pointed out. "We established a continuous process of identifying the customers affected each day, re-prioritizing outreach to fix configurations."
To cut down on spam, it's urging VPS providers to limit their users' ability to send large volumes of messages from SMTP servers hosted on their infrastructure. It's also calling on email service providers to restrict the capabilities of free trial and newly created unverified tenants to send bulk outbound email messages as well as prevent them from sending messages that spoof a domain for which they do not have proven ownership.
"For CISOs, the main takeaway here is to take extra care of their organization's cloud posture – specifically with the use of 3rd party services that become the backbone of your company's networking and communication methods," Tal said. "Specifically in the realm of emails, always maintain a feedback loop and control of your own – even if you trust your email provider fully."
"And as for other companies providing this kind of backbone services – just like Proofpoint did, they must be vigilant and proactive in thinking of all possible types of threats in the first place. Not only threats that directly affect their customers but the wider public as well.
"This is crucial for the safety of all of us and companies that create and operate the backbone of the internet, even if privately held, have the highest responsibility on it. Just like one said, in a different context entirely yet so relevant here: 'With great powers, comes great responsibility.'"
Microsoft Defender Flaw Exploited to Deliver ACR, Lumma, and Meduza Stealers
25.7.24 Exploit The Hacker News
A now-patched security flaw in the Microsoft Defender SmartScreen has been exploited as part of a new campaign designed to deliver information stealers such as ACR Stealer, Lumma, and Meduza.
Fortinet FortiGuard Labs said it detected the stealer campaign targeting Spain, Thailand, and the U.S. using booby-trapped files that exploit CVE-2024-21412 (CVSS score: 8.1).
The high-severity vulnerability allows an attacker to sidestep SmartScreen protection and drop malicious payloads. Microsoft addressed this issue as part of its monthly security updates released in February 2024.
"Initially, attackers lure victims into clicking a crafted link to a URL file designed to download an LNK file," security researcher Cara Lin said. "The LNK file then downloads an executable file containing an [HTML Application] script."
The HTA file serves as a conduit to decode and decrypt PowerShell code responsible for fetching a decoy PDF file and a shellcode injector that, in turn, either leads to the deployment of Meduza Stealer or Hijack Loader, which subsequently launches ACR Stealer or Lumma.
ACR Stealer, assessed to be an evolved version of the GrMsk Stealer, was advertised in late March 2024 by a threat actor named SheldIO on the Russian-language underground forum RAMP.
"This ACR stealer hides its [command-and-control] with a dead drop resolver (DDR) technique on the Steam community website," Lin said, calling out its ability to siphon information from web browsers, crypto wallets, messaging apps, FTP clients, email clients, VPN services, and password managers.

It's worth noting that recent Lumma Stealer attacks have also been observed utilizing the same technique, making it easier for the adversaries to change the C2 domains at any time and render the infrastructure more resilient, according to the AhnLab Security Intelligence Center (ASEC).
The disclosure comes as CrowdStrike has revealed that threat actors are leveraging last week's outage to distribute a previously undocumented information stealer called Daolpu, making it the latest example of the ongoing fallout stemming from the faulty update that has crippled millions of Windows devices.
The attack involves the use of a macro-laced Microsoft Word document that masquerades as a Microsoft recovery manual listing legitimate instructions issued by the Windows maker to resolve the issue, leveraging it as a decoy to activate the infection process.
The DOCM file, when opened, runs the macro to retrieve a second-stage DLL file from a remote that's decoded to launch Daolpu, a stealer malware equipped to harvest credentials and cookies from Google Chrome, Microsoft Edge, Mozilla Firefox, and other Chromium-based browsers.
It also follows the emergence of new stealer malware families such as Braodo and DeerStealer, even as cyber criminals are exploiting malvertising techniques promoting legitimate software such as Microsoft Teams to deploy Atomic Stealer.
"As cyber criminals ramp up their distribution campaigns, it becomes more dangerous to download applications via search engines," Malwarebytes researcher Jérôme Segura said. "Users have to navigate between malvertising (sponsored results) and SEO poisoning (compromised websites)."
CISA Warns of Actively Exploited RCE Flaw in GeoServer GeoTools Software
16.7.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a critical security flaw impacting OSGeo GeoServer GeoTools to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
GeoServer is an open-source software server written in Java that allows users to share and edit geospatial data. It is the reference implementation of the Open Geospatial Consortium (OGC) Web Feature Service (WFS) and Web Coverage Service (WCS) standards.
The vulnerability, tracked as CVE-2024-36401 (CVSS score: 9.8), concerns a case of remote code execution that could be triggered through specially crafted input.
"Multiple OGC request parameters allow Remote Code Execution (RCE) by unauthenticated users through specially crafted input against a default GeoServer installation due to unsafely evaluating property names as XPath expressions," according to an advisory released by the project maintainers earlier this month.
The shortcoming has been addressed in versions 2.23.6, 2.24.4, and 2.25.2. Security researcher Steve Ikeoka has been credited with reporting the flaw.
It's currently not clear how the vulnerability is being exploited in the wild. GeoServer noted that the issue is "confirmed to be exploitable through WFS GetFeature, WFS GetPropertyValue, WMS GetMap, WMS GetFeatureInfo, WMS GetLegendGraphic and WPS Execute requests."
Also patched by maintainers is another critical flaw (CVE-2024-36404, CVSS score: 9.8) that could also result in RCE "if an application uses certain GeoTools functionality to evaluate XPath expressions supplied by user input." It has been resolved in versions 29.6, 30.4, and 31.2.
In light of the active abuse of CVE-2024-36401, federal agencies are required to apply the vendor-provided fixes by August 5, 2024.
The development comes as reports have emerged about the active exploitation of a remote code execution vulnerability in the Ghostscript document conversion toolkit (CVE-2024-29510) that could be leveraged to escape the -dSAFER sandbox and run arbitrary code.
The vulnerability, addressed in version 10.03.1 following responsible disclosure by Codean Labs on March 14, 2024, has since been weaponized to obtain shell access to vulnerable systems, according to ReadMe developer Bill Mill.
PHP Vulnerability Exploited to Spread Malware and Launch DDoS Attacks
11.7.24 Exploit The Hacker News
Multiple threat actors have been observed exploiting a recently disclosed security flaw in PHP to deliver remote access trojans, cryptocurrency miners, and distributed denial-of-service (DDoS) botnets.
The vulnerability in question is CVE-2024-4577 (CVSS score: 9.8), which allows an attacker to remotely execute malicious commands on Windows systems using Chinese and Japanese language locales. It was publicly disclosed in early June 2024.
"CVE-2024-4577 is a flaw that allows an attacker to escape the command line and pass arguments to be interpreted directly by PHP," Akamai researchers Kyle Lefton, Allen West, and Sam Tinklenberg said in a Wednesday analysis. "The vulnerability itself lies in how Unicode characters are converted into ASCII."
The web infrastructure company said it began observing exploit attempts against its honeypot servers targeting the PHP flaw within 24 hours of it being public knowledge.
This included exploits designed to deliver a remote access trojan called Gh0st RAT, cryptocurrency miners like RedTail and XMRig, and a DDoS botnet named Muhstik.
"The attacker sent a request similar to the others seen previous RedTail operations, abusing the soft hyphen flaw with '%ADd,' to execute a wget request for a shell script," the researchers explained. "This script makes an additional network request to the same Russia-based IP address to retrieve an x86 version of the RedTail crypto-mining malware."
Last month, Imperva also revealed that CVE-2024-4577 is being exploited by TellYouThePass ransomware actors to distribute a .NET variant of the file-encrypting malware.
Users and organizations relying on PHP are recommended to update their installations to the latest version to safeguard against active threats.
"The continuously shrinking time that defenders have to protect themselves after a new vulnerability disclosure is yet another critical security risk," the researchers said. "This is especially true for this PHP vulnerability because of its high exploitability and quick adoption by threat actors."
The disclosure comes as Cloudflare said it recorded a 20% year-over-year increase in DDoS attacks in the second quarter of 2024, and that it mitigated 8.5 million DDoS attacks during the first six months. In comparison, the company blocked 14 million DDoS attacks for the entirety of 2023.
"Overall, the number of DDoS attacks in Q2 decreased by 11% quarter-over-quarter, but increased 20% year-over-year," researchers Omer Yoachimik and Jorge Pacheco said in the DDoS threat report for Q2 2024.
What's more, known DDoS botnets accounted for half of all HTTP DDoS attacks. Fake user agents and headless browsers (29%), suspicious HTTP attributes (13%), and generic floods (7%) were the other prominent HTTP DDoS attack vectors.
The most attacked country during the time period was China, followed by Turkey, Singapore, Hong Kong, Russia, Brazil, Thailand, Canada, Taiwan, and Kyrgyztan. Information technology and services, telecom, consumer goods, education, construction, and food and beverage emerged as the top sectors targeted by DDoS attacks.
"Argentina was ranked as the largest source of DDoS attacks in the second quarter of 2024," the researchers said. "Indonesia followed closely in second place, followed by the Netherlands in third."
8220 Gang Exploits Oracle WebLogic Server Flaws for Cryptocurrency Mining
28.6.24 Exploit The Hacker News
Security researchers have shed more light on the cryptocurrency mining operation conducted by the 8220 Gang by exploiting known security flaws in the Oracle WebLogic Server.
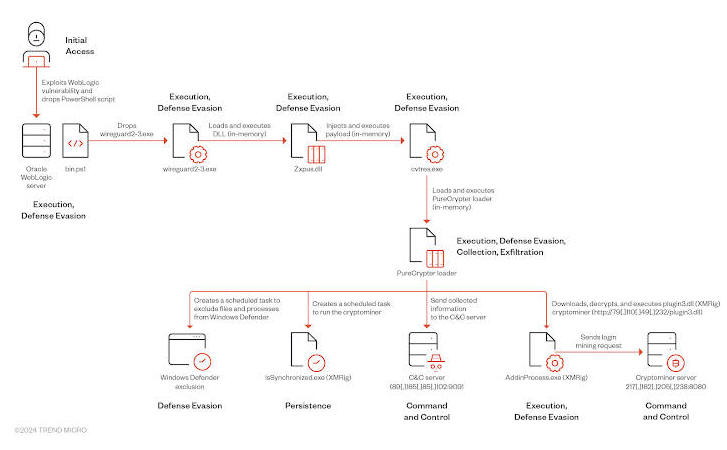
"The threat actor employs fileless execution techniques, using DLL reflective and process injection, allowing the malware code to run solely in memory and avoid disk-based detection mechanisms," Trend Micro researchers Ahmed Mohamed Ibrahim, Shubham Singh, and Sunil Bharti said in a new analysis published today.
The cybersecurity firm is tracking the financially motivated actor under the name Water Sigbin, which is known to weaponize vulnerabilities in Oracle WebLogic Server such as CVE-2017-3506, CVE- 2017-10271, and CVE-2023-21839 for initial access and drop the miner payload via multi-stage loading technique.
A successful foothold is followed by the deployment of PowerShell script that's responsible for dropping a first-stage loader ("wireguard2-3.exe") that mimics the legitimate WireGuard VPN application, but, in reality, launches another binary ("cvtres.exe") in memory by means of a DLL ("Zxpus.dll").
Cybersecurity
The injected executable serves as a conduit to load the PureCrypter loader ("Tixrgtluffu.dll") that, in turn, exfiltrates hardware information to a remote server and creates scheduled tasks to run the miner as well as excludes the malicious files from Microsoft Defender Antivirus.
In response, the command-and-control (C2) server responds with an encrypted message containing the XMRig configuration details, following which the loader retrieves and executes the miner from an attacker-controlled domain by masquerading it as "AddinProcess.exe," a legitimate Microsoft binary.
The development comes as the QiAnXin XLab team detailed a new installer tool used by the 8220 Gang called k4spreader since at least February 2024 to deliver the Tsunami DDoS botnet and the PwnRig mining program.
The malware, which is currently under development and has a shell version, has been leveraging security flaws such as Apache Hadoop YARN, JBoss, and Oracle WebLogic Server to infiltrate susceptible targets.
"k4spreader is written in cgo, including system persistence, downloading and updating itself, and releasing other malware for execution," the company said, adding it's also designed to disable the firewall, terminate rival botnets (e.g., kinsing), and printing operational status.
New SnailLoad Attack Exploits Network Latency to Spy on Users' Web Activities
28.6.24 Exploit The Hacker News
A group of security researchers from the Graz University of Technology have demonstrated a new side-channel attack known as SnailLoad that could be used to remotely infer a user's web activity.
"SnailLoad exploits a bottleneck present on all Internet connections," the researchers said in a study released this week.
"This bottleneck influences the latency of network packets, allowing an attacker to infer the current network activity on someone else's Internet connection. An attacker can use this information to infer websites a user visits or videos a user watches."
A defining characteristic of the approach is that it obviates the need for carrying out an adversary-in-the-middle (AitM) attack or being in physical proximity to the Wi-Fi connection to sniff network traffic.
Cybersecurity
Specifically, it entails tricking a target into loading a harmless asset (e.g., a file, an image, or an ad) from a threat actor-controlled server, which then exploits the victim's network latency as a side channel to determine online activities on the victim system.
To perform such a fingerprinting attack and glean what video or a website a user might be watching or visiting, the attacker conducts a series of latency measurements of the victim's network connection as the content is being downloaded from the server while they are browsing or viewing.
It then involves a post-processing phase that employs a convolutional neural network (CNN) trained with traces from an identical network setup to make the inference with an accuracy of up to 98% for videos and 63% for websites.
In other words, due to the network bottleneck on the victim's side, the adversary can deduce the transmitted amount of data by measuring the packet round trip time (RTT). The RTT traces are unique per video and can be used to classify the video watched by the victim.
The attack is so named because the attacking server transmits the file at a snail's pace in order to monitor the connection latency over an extended period of time.
"SnailLoad requires no JavaScript, no form of code execution on the victim system, and no user interaction but only a constant exchange of network packets," the researchers explained, adding it "measures the latency to the victim system and infers the network activity on the victim system from the latency variations."
"The root cause of the side-channel is buffering in a transport path node, typically the last node before the user's modem or router, related to a quality-of-service issue called bufferbloat."
The disclosure comes as academics have disclosed a security flaw in the manner router firmware handles Network Address Translation (NAT) mapping that could be exploited by an attacker connected to the same Wi-Fi network as the victim to bypass built-in randomization in the Transmission Control Protocol (TCP).
Cybersecurity
"Most routers, for performance reasons, do not rigorously inspect the sequence numbers of TCP packets," the researchers said. "Consequently, this introduces serious security vulnerabilities that attackers can exploit by crafting forged reset (RST) packets to maliciously clear NAT mappings in the router."
The attack essentially allows the threat actor to infer the source ports of other client connections as well as steal the sequence number and acknowledgment number of the normal TCP connection between the victim client and the server in order to perform TCP connection manipulation.
The hijacking attacks targeting TCP could then be weaponized to poison a victim's HTTP web page or stage denial-of-service (DoS) attacks, per the researchers, who said patches for the vulnerability are being readied by the OpenWrt community as well as router vendors like 360, Huawei, Linksys, Mercury, TP-Link, Ubiquiti, and Xiaomi.
Exploit Attempts Recorded Against New MOVEit Transfer Vulnerability - Patch ASAP!
27.6.24 Exploit The Hacker News
A newly disclosed critical security flaw impacting Progress Software MOVEit Transfer is already seeing exploitation attempts in the wild shortly after details of the bug were publicly disclosed.
The vulnerability, tracked as CVE-2024-5806 (CVSS score: 9.1), concerns an authentication bypass that impacts the following versions -
From 2023.0.0 before 2023.0.11
From 2023.1.0 before 2023.1.6, and
From 2024.0.0 before 2024.0.2
"Improper authentication vulnerability in Progress MOVEit Transfer (SFTP module) can lead to Authentication Bypass," the company said in an advisory released Tuesday.
Progress has also addressed another critical SFTP-associated authentication bypass vulnerability (CVE-2024-5805, CVSS score: 9.1) affecting MOVEit Gateway version 2024.0.0.
Successful exploitation of the flaws could allow attackers to bypass SFTP authentication and gain access to MOVEit Transfer and Gateway systems.
watchTowr Labs has since published additional technical specifics about CVE-2024-5806, with security researchers Aliz Hammond and Sina Kheirkhah noting that it could be weaponized to impersonate any user on the server.
The company further described the flaw as comprising two separate vulnerabilities, one in Progress MOVEit and the other in the IPWorks SSH library.
"While the more devastating vulnerability, the ability to impersonate arbitrary users, is unique to MOVEit, the less impactful (but still very real) forced authentication vulnerability is likely to affect all applications that use the IPWorks SSH server," the researchers said.
Progress Software said the shortcoming in the third-party component "elevates the risk of the original issue" if left unpatched, urging customers to follow the below two steps -
Block public inbound RDP access to MOVEit Transfer server(s)
Limit outbound access to only known trusted endpoints from MOVEit Transfer server(s)
According to Rapid7, there are three prerequisites to leveraging CVE-2024-5806: Attackers need to have knowledge of an existing username, the target account can authenticate remotely, and the SFTP service is publicly accessible over the internet.
As of June 25, data gathered by Censys shows that there are around 2,700 MOVEit Transfer instances online, most of them located in the U.S., the U.K., Germany, the Netherlands, Canada, Switzerland, Australia, France, Ireland, and Denmark.
With another critical issue in MOVEit Transfer widely abused in a spate of Cl0p ransomware attacks last year (CVE-2023-34362, CVSS score: 9.8), it's essential that users move quickly to update to the latest versions.
The development comes as the U.S. and Infrastructure Security Agency (CISA) revealed that its Chemical Security Assessment Tool (CSAT) was targeted earlier this January by an unknown threat actor by taking advantage of security flaws in the Ivanti Connect Secure (ICS) appliance (CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893).
"This intrusion may have resulted in the potential unauthorized access of Top-Screen surveys, Security Vulnerability Assessments, Site Security Plans, Personnel Surety Program (PSP) submissions, and CSAT user accounts," the agency said, adding it found no evidence of data exfiltration.
Update#
Progress Software, in a statement shared with The Hacker News, said "we have not received any reports that these vulnerabilities have been exploited and we are not aware of any direct operational impact to customers."
(The story has been updated after publication to emphasize that the attacks are exploitation attempts at this stage.)
Hackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
27.4.24 Exploit The Hacker News
Threat actors are attempting to actively exploit a critical security flaw in the ValvePress Automatic plugin for WordPress that could allow site takeovers.
The shortcoming, tracked as CVE-2024-27956, carries a CVSS score of 9.9 out of a maximum of 10. It impacts all versions of the plugin prior to 3.92.0. The issue has been resolved in version 3.92.1 released on February 27, 2024, although the release notes make no mention of it.
"This vulnerability, a SQL injection (SQLi) flaw, poses a severe threat as attackers can exploit it to gain unauthorized access to websites, create admin‑level user accounts, upload malicious files, and potentially take full control of affected sites," WPScan said in an alert this week.
According to the Automattic-owned company, the issue is rooted in the plugin's user authentication mechanism, which can be trivially circumvented to execute arbitrary SQL queries against the database by means of specially crafted requests.
In the attacks observed so far, CVE-2024-27956 is being used to unauthorized database queries and create new admin accounts on susceptible WordPress sites (e.g., names starting with "xtw"), which could then be leveraged for follow-on post-exploitation actions.
This includes installing plugins that make it possible to upload files or edit code, indicating attempts to repurpose the infected sites as stagers.
"Once a WordPress site is compromised, attackers ensure the longevity of their access by creating backdoors and obfuscating the code," WPScan said. "To evade detection and maintain access, attackers may also rename the vulnerable WP‑Automatic file, making it difficult for website owners or security tools to identify or block the issue."
The file in question is "/wp‑content/plugins/wp‑automatic/inc/csv.php," which is renamed to something like "/wp‑content/plugins/wp‑automatic/inc/csv65f82ab408b3.php."
That said, it's possible that the threat actors are doing so in an attempt to prevent other attackers from exploiting the sites already under their control.
CVE-2024-27956 was publicly disclosed by WordPress security firm Patchstack on March 13, 2024. Since then, more than 5.5 million attack attempts to weaponize the flaw have been detected in the wild.
The disclosure comes as severe bugs have been disclosed in plugins like Email Subscribers by Icegram Express (CVE-2024-2876, CVSS score: 9.8), Forminator (CVE-2024-28890, CVSS score: 9.8), and User Registration (CVE-2024-2417, CVSS score: 8.8) that could be used to extract sensitive data like password hashes from the database, upload arbitrary files, and grant an authenticator user admin privileges.
Patchstack has also warned of an unpatched issue in the Poll Maker plugin (CVE-2024-32514, CVSS score: 9.9) that allows for authenticated attackers, with subscriber-level access and above, to upload arbitrary files on the affected site's server, leading to remote code execution.
MITRE Corporation Breached by Nation-State Hackers Exploiting Ivanti Flaws
23.4.24 Exploit The Hacker News
The MITRE Corporation revealed that it was the target of a nation-state cyber attack that exploited two zero-day flaws in Ivanti Connect Secure appliances starting in January 2024.
The intrusion led to the compromise of its Networked Experimentation, Research, and Virtualization Environment (NERVE), an unclassified research and prototyping network.
The unknown adversary "performed reconnaissance of our networks, exploited one of our Virtual Private Networks (VPNs) through two Ivanti Connect Secure zero-day vulnerabilities, and skirted past our multi-factor authentication using session hijacking," Lex Crumpton, a defensive cyber operations researcher at the non-profit, said last week.
The attack entailed the exploitation of CVE-2023-46805 (CVSS score: 8.2) and CVE-2024-21887 (CVSS score: 9.1), which could be weaponized by threat actors to bypass authentication and run arbitrary commands on the infected system.
Upon gaining initial access, the threat actors moved laterally and breached its VMware infrastructure using a compromised administrator account, ultimately paving the way for the deployment of backdoors and web shells for persistence and credential harvesting.
"NERVE is an unclassified collaborative network that provides storage, computing, and networking resources," MITRE said. "Based on our investigation to date, there is no indication that MITRE's core enterprise network or partners' systems were affected by this incident."
The organization said that it has since taken steps to contain the incident, and that it undertook response and recovery efforts as well as forensic analysis to identify the extent of the compromise.
The initial exploitation of the twin flaws has been attributed to a cluster tracked by cybersecurity company Volexity under the name UTA0178, a nation-state actor likely linked to China. Since then, several other China-nexus hacking groups have joined the exploitation bandwagon, according to Mandiant.
"No organization is immune from this type of cyber attack, not even one that strives to maintain the highest cybersecurity possible," Jason Providakes, president and CEO of MITRE, said.
"We are disclosing this incident in a timely manner because of our commitment to operate in the public interest and to advocate for best practices that enhance enterprise security as well as necessary measures to improve the industry's current cyber defense posture."
Critical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
20.4.24 Exploit The Hacker News
Users of the CrushFTP enterprise file transfer software are being urged to update to the latest version following the discovery of a security flaw that has come under targeted exploitation in the wild.
"CrushFTP v11 versions below 11.1 have a vulnerability where users can escape their VFS and download system files," CrushFTP said in an advisory released Friday. "This has been patched in v11.1.0."
That said, customers who are operating their CrushFTP instances within a DMZ (demilitarized zone) restricted environment are protected against the attacks.
Simon Garrelou of Airbus CERT has been credited with discovering and reporting the flaw. It has yet to be assigned a CVE identifier.
Cybersecurity company CrowdStrike, in a post shared on Reddit, said it has observed an exploit for the flaw being used in the wild in a "targeted fashion."

These intrusions are said to have mainly targeted U.S. entities, with the intelligence gathering activity suspected to be politically motivated.
"CrushFTP users should continue to follow the vendor's website for the most up-to-date instructions and prioritize patching," CrowdStrike said.
Hackers Exploit OpenMetadata Flaws to Mine Crypto on Kubernetes
18.4.24 Exploit The Hacker News
Threat actors are actively exploiting critical vulnerabilities in OpenMetadata to gain unauthorized access to Kubernetes workloads and leverage them for cryptocurrency mining activity.
That's according to the Microsoft Threat Intelligence team, which said the flaws have been weaponized since the start of April 2024.
OpenMetadata is an open-source platform that operates as a metadata management tool, offering a unified solution for data asset discovery, observability, and governance.
The flaws in question – all discovered and credited to security researcher Alvaro Muñoz – are listed below -
CVE-2024-28847 (CVSS score: 8.8) - A Spring Expression Language (SpEL) injection vulnerability in PUT /api/v1/events/subscriptions (fixed in version 1.2.4)
CVE-2024-28848 (CVSS score: 8.8) - A SpEL injection vulnerability in GET /api/v1/policies/validation/condition/<expr> (fixed in version 1.2.4)
CVE-2024-28253 (CVSS score: 8.8) - A SpEL injection vulnerability in PUT /api/v1/policies (fixed in version 1.3.1)
CVE-2024-28254 (CVSS score: 8.8) - A SpEL injection vulnerability in GET /api/v1/events/subscriptions/validation/condition/<expr> (fixed in version 1.2.4)
CVE-2024-28255 (CVSS score: 9.8) - An authentication bypass vulnerability (fixed in version 1.2.4)
Successful exploitation of the vulnerabilities could allow a threat actor to bypass authentication and achieve remote code execution.
The modus operandi uncovered by Microsoft entails the targeting of internet-exposed OpenMetadata workloads that have been left unpatched to gain code execution on the container running the OpenMetadata image.
Upon gaining an initial foothold, the threat actors have been observed carrying out reconnaissance activities to determine their level of access to the compromised environment and gather details about the network and hardware configuration, operating system version, the number of active users, and the environment variables.
"This reconnaissance step often involves contacting a publicly available service," security researchers Hagai Ran Kestenberg and Yossi Weizman said.
"In this specific attack, the attackers send ping requests to domains that end with oast[.]me and oast[.]pro, which are associated with Interactsh, an open-source tool for detecting out-of-band interactions."

In doing so, the idea is to validate network connectivity from the infiltrated system to attacker-controlled infrastructure without raising any red flags, thereby giving threat actors the confidence to establish command-and-control (C2) communications and deploy additional payloads.
The end goal of the attacks is to retrieve and deploy a Windows or Linux variant of the crypto-mining malware from a remote server located in China, depending on the operating system.
Once the miner is launched, the initial payloads are removed from the workload, and the attackers initiate a reverse shell for their remote server using the Netcat tool, permitting them to commandeer the system. Persistence is achieved by setting cron jobs to run the malicious code at predefined intervals.
Interestingly, the threat actor also leaves behind a personal note telling that they are poor and that they need the money to buy a car and a suite. "I don't want to do anything illegal," the note reads.
OpenMetadata users are advised to switch to strong authentication methods, avoid using default credentials, and update their images to the latest version.
"This attack serves as a valuable reminder of why it's crucial to stay compliant and run fully patched workloads in containerized environments," the researchers said.
The development comes as publicly accessible Redis servers that have the authentication feature disabled or have unpatched flaws are being targeted to install Metasploit Meterpreter payloads for post-exploitation.
"When Metasploit is installed, the threat actor can take control of the infected system and also dominate the internal network of an organization using the various features offered by the malware," the AhnLab Security Intelligence Center (ASEC) said.
It also follows a report from WithSecure that detailed how search permissions on Docker directories could be abused to achieve privilege escalation. It's worth pointing out that the issue (CVE-2021-41091, CVSS score: 6.3) was previously flagged by CyberArk in February 2022, and addressed by Docker in version 20.10.9.
"The setting of the searchable bit for other users on /var/lib/docker/ and child directories can allow for a low-privileged attacker to gain access to various containers' filesystems," WithSecure said.
Researchers Uncover First Native Spectre v2 Exploit Against Linux Kernel
10.4.24 Exploit The Hacker News
Cybersecurity researchers have disclosed what they say is the "first native Spectre v2 exploit" against the Linux kernel on Intel systems that could be exploited to read sensitive data from the memory.
The exploit, called Native Branch History Injection (BHI), can be used to leak arbitrary kernel memory at 3.5 kB/sec by bypassing existing Spectre v2/BHI mitigations, researchers from Systems and Network Security Group (VUSec) at Vrije Universiteit Amsterdam said in a new study.
The shortcoming is being tracked as CVE-2024-2201.
BHI was first disclosed by VUSec in March 2022, describing it as a technique that can get around Spectre v2 protections in modern processors from Intel, AMD, and Arm.
While the attack leveraged extended Berkeley Packet Filters (eBPFs), Intel's recommendations to address the problem, among other things, was to disable Linux's unprivileged eBPFs.
"Privileged managed runtimes that can be configured to allow an unprivileged user to generate and execute code in a privileged domain -- such as Linux's 'unprivileged eBPF' -- significantly increase the risk of transient execution attacks, even when defenses against intra-mode [Branch Target Injection] are present," Intel said at the time.
"The kernel can be configured to deny access to unprivileged eBPF by default, while still allowing administrators to enable it at runtime where needed." Native BHI neutralizes this countermeasure by showing that BHI is possible without eBPF. It impacts all Intel systems that are susceptible to BHI. As a result, it makes it possible for an attacker with access to CPU resources to influence speculative execution paths via malicious software installed on a machine with the goal of extracting sensitive data that are associated with a different process. "Existing mitigation techniques of disabling privileged eBPF and enabling (Fine)IBT are insufficient in stopping BHI exploitation against the kernel/hypervisor," the CERT Coordination Center (CERT/CC) said in an advisory. "An unauthenticated attacker can exploit this vulnerability to leak privileged memory from the CPU by speculatively jumping to a chosen gadget." The disclosure comes weeks after IBM and VUSec detailed GhostRace (CVE-2024-2193), a variant of Spectre v1 that employs a combination of speculative execution and race conditions to leak data from contemporary CPU architectures. It also follows new research from ETH Zurich that disclosed a family of attacks dubbed Ahoi Attacks that could be used to compromise hardware-based trusted execution environments (TEEs) and break confidential virtual machines (CVMs) like AMD Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) and Intel Trust Domain Extensions (TDX). The attacks, codenamed Heckler and WeSee, make use of malicious interrupts to break the integrity of CVMs, potentially allowing threat actors to remotely log in and gain elevated access, as well as perform arbitrary read, write, and code injection to disable firewall rules and open a root shell. "For Ahoi Attacks, an attacker can use the hypervisor to inject malicious interrupts to the victim's vCPUs and trick it into executing the interrupt handlers," the researchers said. "These interrupt handlers can have global effects (e.g., changing the register state in the application) that an attacker can trigger to compromise the victim's CVM." In response to the findings, AMD said the vulnerability is rooted in the Linux kernel implementation of SEV-SNP and that fixes addressing some of the issues have been upstreamed to the main Linux kernel.
The flaw has been confirmed to affect Illumos, Intel, Red Hat, SUSE Linux, Triton Data Center, and Xen. AMD, in a bulletin, said it's "aware of any impact" on its products.
Critical 'BatBadBut' Rust Vulnerability Exposes Windows Systems to Attacks
10.4.24 Exploit The Hacker News
A critical security flaw in the Rust standard library could be exploited to target Windows users and stage command injection attacks.
The vulnerability, tracked as CVE-2024-24576, has a CVSS score of 10.0, indicating maximum severity. That said, it only impacts scenarios where batch files are invoked on Windows with untrusted arguments.
"The Rust standard library did not properly escape arguments when invoking batch files (with the bat and cmd extensions) on Windows using the Command API," the Rust Security Response working group said in an advisory released on April 9, 2024.
"An attacker able to control the arguments passed to the spawned process could execute arbitrary shell commands by bypassing the escaping."
The flaw impacts all versions of Rust before 1.77.2. Security researcher RyotaK has been credited with discovering and reporting the bug to the CERT Coordination Center (CERT/CC).
RyotaK said the vulnerability – codenamed BatBadBut – impacts several programming languages and that it arises when the "programming language wraps the CreateProcess function [in Windows] and adds the escaping mechanism for the command arguments."
But in light of the fact that not every programming language has addressed the problem, developers are being recommended to exercise caution when executing commands on Windows.
"To prevent the unexpected execution of batch files, you should consider moving the batch files to a directory that is not included in the PATH environment variable," RyotaK said in a word of advice to users.
"In this case, the batch files won't be executed unless the full path is specified, so the unexpected execution of batch files can be prevented."
Hackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
7.4.24 Exploit The Hacker News
Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites.
The attack leverages CVE-2024-20720 (CVSS score: 9.1), which has been described by Adobe as a case of "improper neutralization of special elements" that could pave the way for arbitrary code execution.
It was addressed by the company as part of security updates released on February 13, 2024.
Sansec said it discovered a "cleverly crafted layout template in the database" that's being used to automatically inject malicious code to execute arbitrary commands.
"Attackers combine the Magento layout parser with the beberlei/assert package (installed by default) to execute system commands," the company said.
"Because the layout block is tied to the checkout cart, this command is executed whenever <store>/checkout/cart is requested."
The command in question is sed, which is used to insert a code execution backdoor that's then responsible for delivering a Stripe payment skimmer to capture and exfiltrate financial information to another compromised Magento store.
The development comes as the Russian government has charged six people for using skimmer malware to steal credit card and payment information from foreign e-commerce stores at least since late 2017.
The suspects are Denis Priymachenko, Alexander Aseyev, Alexander Basov, Dmitry Kolpakov, Vladislav Patyuk, and Anton Tolmachev. Recorded Future News reported that the arrests were made a year ago, citing court documents.
"As a result, members of the hacker group illegally took possession of information about almost 160 thousand payment cards of foreign citizens, after which they sold them through shadow internet sites," the Prosecutor General's Office of the Russian Federation said.
Hackers Exploiting Popular Document Publishing Sites for Phishing Attacks
19.3.24 Exploit The Hacker News
Threat actors are leveraging digital document publishing (DDP) sites hosted on platforms like FlipSnack, Issuu, Marq, Publuu, RelayTo, and Simplebooklet for carrying out phishing, credential harvesting, and session token theft, once again underscoring how threat actors are repurposing legitimate services for malicious ends.
"Hosting phishing lures on DDP sites increases the likelihood of a successful phishing attack, since these sites often have a favorable reputation, are unlikely to appear on web filter blocklists, and may instill a false sense of security in users who recognize them as familiar or legitimate," Cisco Talos researcher Craig Jackson said last week.
While adversaries have used popular cloud-based services such as Google Drive, OneDrive, Dropbox, SharePoint, DocuSign, and Oneflow to host phishing documents in the past, the latest development marks an escalation designed to evade email security controls.
DDP services allow users to upload and share PDF files in a browser-based interactive flipbook format, adding page flip animations and other skeuomorphic effects to any catalog, brochure, or magazine.
Threat actors have been found to abuse the free tier or a no-cost trial period offered by these services to create multiple accounts and publish malicious documents.
Besides exploiting their favorable domain reputation, the attackers take advantage of the fact that DDP sites facilitate transient file hosting, thereby allowing published content to automatically become unavailable after a predefined expiration date and time.

What's more, productivity features baked into DDP sites like Publuu could act as a deterrent, preventing the extraction and detection of malicious links in phishing messages.
In the incidents analyzed by Cisco Talos, DDP sites are integrated into the attack chain in the secondary or intermediate stage, typically by embedding a link to a document hosted on a legitimate DDP site in a phishing email.
The DDP-hosted document serves as a gateway to an external, adversary-controlled site either directly by clicking on a link included in the decoy file, or through a series of redirects that also require solving CAPTCHAs to thwart automated analysis efforts.
The final landing page is a bogus site mimicking the Microsoft 365 login page, thus allowing the attackers to steal credentials or session tokens.
"DDP sites could represent a blind spot for defenders, because they are unfamiliar to trained users and unlikely to be flagged by email and web content filtering controls," Jackson said.
"DDP sites create advantages for threat actors seeking to thwart contemporary phishing protections. The same features and benefits that attract legitimate users to these sites can be abused by threat actors to increase the efficacy of a phishing attack."
QEMU Emulator Exploited as Tunneling Tool to Breach Company Network
8.3.24 Exploit The Hacker News
Threat actors have been observed leveraging the QEMU open-source hardware emulator as tunneling software during a cyber attack targeting an unnamed "large company" to connect to their infrastructure.
While a number of legitimate tunneling tools like Chisel, FRP, ligolo, ngrok, and Plink have been used by adversaries to their advantage, the development marks the first QEMU that has been used for this purpose.
"We found that QEMU supported connections between virtual machines: the -netdev option creates network devices (backend) that can then connect to the virtual machines," Kaspersky researchers Grigory Sablin, Alexander Rodchenko, and Kirill Magaskin said.
"Each of the numerous network devices is defined by its type and supports extra options."
In other words, the idea is to create a virtual network interface and a socket-type network interface, thereby allowing the virtual machine to communicate with any remote server.
The Russian cybersecurity company said it was able to use QEMU to set up a network tunnel from an internal host within the enterprise network that didn't have internet access to a pivot host with internet access, which connects to the attacker's server on the cloud running the emulator.

The findings show that threat actors are continuously diversifying their attack strategies to blend their malicious traffic with actual activity and meet their operational goals.
"Malicious actors using legitimate tools to perform various attack steps is nothing new to incident response professionals," the researchers said.
"This further supports the concept of multi-level protection, which covers both reliable endpoint protection, and specialized solutions for detecting and protecting against complex and targeted attacks including human-operated ones."
CISA Warns of Actively Exploited JetBrains TeamCity Vulnerability
8.3.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a critical security flaw impacting JetBrains TeamCity On-Premises software to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
The vulnerability, tracked as CVE-2024-27198 (CVSS score: 9.8), refers to an authentication bypass bug that allows for a complete compromise of a susceptible server by a remote unauthenticated attacker.
It was addressed by JetBrains earlier this week alongside CVE-2024-27199 (CVSS score: 7.3), another moderate-severity authentication bypass flaw that allows for a "limited amount" of information disclosure and system modification.
"The vulnerabilities may enable an unauthenticated attacker with HTTP(S) access to a TeamCity server to bypass authentication checks and gain administrative control of that TeamCity server," the company noted at the time.

Threat actors have been observed weaponizing the twin flaws to deliver Jasmin ransomware as well as create hundreds of rogue user accounts, according to CrowdStrike and LeakIX. The Shadowserver Foundation said it detected exploitation attempts starting from March 4, 2024.
Statistics shared by GreyNoise show that CVE-2024-27198 has come under broad exploitation from over a dozen unique IP addresses shortly after public disclosure of the flaw.
In light of active exploitation, users running on-premises versions of the software are advised to apply the updates as soon as possible to mitigate potential threats. Federal agencies are required to patch their instances by March 28, 2024.
Hackers Exploit Misconfigured YARN, Docker, Confluence, Redis Servers for Crypto Mining
7.3.24 Exploit The Hacker News
Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an emerging malware campaign designed to deliver a cryptocurrency miner and spawn a reverse shell for persistent remote access.
"The attackers leverage these tools to issue exploit code, taking advantage of common misconfigurations and exploiting an N-day vulnerability, to conduct Remote Code Execution (RCE) attacks and infect new hosts," Cado security researcher Matt Muir said in a report shared with The Hacker News.
The activity has been codenamed Spinning YARN by the cloud security company, with overlaps to cloud attacks attributed to TeamTNT, WatchDog, and a cluster dubbed Kiss-a-dog.
It all starts with deploying four novel Golang payloads that are capable of automating the identification and exploitation of susceptible Confluence, Docker, Hadoop YARN, and Redis hosts. The spreader utilities leverage masscan or pnscan to hunt for these services.
"For the Docker compromise, the attackers spawn a container and escape from it onto the underlying host," Muir explained.
The initial access then paves the way for the deployment of additional tools to install rootkits like libprocesshider and diamorphine to conceal malicious processes, drop the Platypus open-source reverse shell utility, and ultimately launch the XMRig miner.
"It's clear that attackers are investing significant time into understanding the types of web-facing services deployed in cloud environments, keeping abreast of reported vulnerabilities in those services and using this knowledge to gain a foothold in target environments," the company said.
The development comes as Uptycs revealed 8220 Gang's exploitation of known security flaws in Apache Log4j (CVE-2021-44228) and Atlassian Confluence Server and Data Center (CVE-2022-26134) as part of a wave of assaults targeting cloud infrastructure from May 2023 through February 2024.
"By leveraging internet scans for vulnerable applications, the group identifies potential entry points into cloud systems, exploiting unpatched vulnerabilities to gain unauthorized access," security researchers Tejaswini Sandapolla and Shilpesh Trivedi said.
"Once inside, they deploy a series of advanced evasion techniques, demonstrating a profound understanding of how to navigate and manipulate cloud environments to their advantage. This includes disabling security enforcement, modifying firewall rules, and removing cloud security services, thereby ensuring their malicious activities remain undetected."
The attacks, which single out both Windows and Linux hosts, aim to deploy a cryptocurrency miner, but not before taking a series of steps that prioritize stealth and evasion.
It also follows the abuse of cloud services primarily meant for artificial intelligence (AI) solutions to drop cryptocurrency miners as well as host malware.
"With both mining and AI requiring access to large amounts of GPU processing power, there's a certain degree of transferability to their base hardware environments," HiddenLayer noted last year.
Cado, in its H2 2023 Cloud Threat Findings Report, noted that threat actors are increasingly targeting cloud services that require specialist technical knowledge to exploit, and that cryptojacking is no longer the only motive.
"With the discovery of new Linux variants of ransomware families, such as Abyss Locker, there is a worrying trend of ransomware on Linux and ESXi systems," it said. "Cloud and Linux infrastructure is now subject to a broader variety of attacks."
Critical JetBrains TeamCity On-Premises Flaws Could Lead to Server Takeovers
5.3.24 Exploit The Hacker News
A new pair of security vulnerabilities have been disclosed in JetBrains TeamCity On-Premises software that could be exploited by a threat actor to take control of affected systems.
The flaws, tracked as CVE-2024-27198 (CVSS score: 9.8) and CVE-2024-27199 (CVSS score: 7.3), have been addressed in version 2023.11.4. They impact all TeamCity On-Premises versions through 2023.11.3.
"The vulnerabilities may enable an unauthenticated attacker with HTTP(S) access to a TeamCity server to bypass authentication checks and gain administrative control of that TeamCity server," JetBrains said in an advisory released Monday.
TeamCity Cloud instances have already been patched against the two flaws. Cybersecurity firm Rapid7, which discovered and reported the issues on February 20, 2024, said CVE-2024-27198 is a case of authentication bypass that allows for a complete compromise of a susceptible server by a remote unauthenticated attacker.
"Compromising a TeamCity server allows an attacker full control over all TeamCity projects, builds, agents and artifacts, and as such is a suitable vector to position an attacker to perform a supply chain attack," the company noted.
CVE-2024-27199, also an authentication bypass flaw, stems from a path traversal issue that can permit an unauthenticated attacker to replace the HTTPS certificate in a vulnerable TeamCity server with a certificate of their choosing via the "/app/https/settings/uploadCertificate" endpoint and even alter the port number the HTTPS service listens on.
A threat actor could leverage the vulnerability to perform a denial-of-service against the TeamCity server by either changing the HTTPS port number, or by uploading a certificate that will fail client-side validation. Alternatively, the uploaded certificate could be used for adversary-in-the-middle scenarios if it's trusted by the clients.
"This authentication bypass allows for a limited number of authenticated endpoints to be reached without authentication," Rapid7 said of the shortcoming.
"An unauthenticated attacker can leverage this vulnerability to both modify a limited number of system settings on the server, as well as disclose a limited amount of sensitive information from the server."
The development comes nearly a month after JetBrains released fixes to contain another flaw (CVE-2024-23917, CVSS score: 9.8) that could also enable an unauthenticated attacker to gain administrative control of TeamCity servers.
With security vulnerabilities in JetBrains TeamCity having come under active exploitation last year by North Korean and Russian threat actors, it's essential that users take steps to update their servers immediately.
Five Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
1.3.24 Exploit The Hacker News
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in Ivanti Connect Secure and Ivanti Policy Secure gateways, noting that the Integrity Checker Tool (ICT) can be deceived to provide a false sense of security.
"Ivanti ICT is not sufficient to detect compromise and that a cyber threat actor may be able to gain root-level persistence despite issuing factory resets," the agencies said.
To date, Ivanti has disclosed five security vulnerabilities impacting its products since January 10, 2024, out of which four have come under active exploitation by multiple threat actors to deploy malware -
CVE-2023-46805 (CVSS score: 8.2) - Authentication bypass vulnerability in web component
CVE-2024-21887 (CVSS score: 9.1) - Command injection vulnerability in web component
CVE-2024-21888 (CVSS score: 8.8) - Privilege escalation vulnerability in web component
CVE-2024-21893 (CVSS score: 8.2) - SSRF vulnerability in the SAML component
CVE-2024-22024 (CVSS score: 8.3) - XXE vulnerability in the SAML component
Mandiant, in an analysis published this week, described how an encrypted version of malware known as BUSHWALK is placed in a directory excluded by ICT in /data/runtime/cockpit/diskAnalysis.
The directory exclusions were also previously highlighted by Eclypsium this month, stating the tool skips a dozen directories from being scanned, thus allowing an attacker to leave behind backdoors in one of these paths and still pass the integrity check.
"The safest course of action for network defenders is to assume a sophisticated threat actor may deploy rootkit level persistence on a device that has been reset and lay dormant for an arbitrary amount of time," agencies from Australia, Canada, New Zealand, the U.K., and the U.S. said.
They also urged organizations to "consider the significant risk of adversary access to, and persistence on, Ivanti Connect Secure and Ivanti Policy Secure gateways when determining whether to continue operating these devices in an enterprise environment."
Ivanti, in response to the advisory, said it's not aware of any instances of successful threat actor persistence following the implementation of security updates and factory resets. It's also releasing a new version of ICT that it said "provides additional visibility into a customer's appliance and all files that are present on the system."
Lazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks
1.3.24 Exploit The Hacker News
The notorious Lazarus Group actors exploited a recently patched privilege escalation flaw in the Windows Kernel as a zero-day to obtain kernel-level access and disable security software on compromised hosts.
The vulnerability in question is CVE-2024-21338 (CVSS score: 7.8), which can permit an attacker to gain SYSTEM privileges. It was resolved by Microsoft earlier this month as part of Patch Tuesday updates.
"To exploit this vulnerability, an attacker would first have to log on to the system," Microsoft said. "An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system."
While there were no indications of active exploitation of CVE-2024-21338 at the time of the release of the updates, Redmond on Wednesday revised its "Exploitability assessment" for the flaw to "Exploitation Detected."
It’s currently not clear when the attacks took place, but the vulnerability is said to have been introduced in Window 10, version 1703 (RS2/15063) when the 0x22A018 IOCTL (short for input/output control) handler was first implemented.
Cybersecurity vendor Avast, which discovered an in-the-wild admin-to-kernel exploit for the bug, said the kernel read/write primitive achieved by weaponizing the flaw allowed the Lazarus Group to "perform direct kernel object manipulation in an updated version of their data-only FudModule rootkit."
The FudModule rootkit was first reported by ESET and AhnLab in October 2022 as capable of disabling the monitoring of all security solutions on infected hosts by means of what's called a Bring Your Own Vulnerable Driver (BYOVD) attack, wherein an attacker implants a driver susceptible to a known or zero-day flaw to escalate privileges.
What makes the latest attack significant is that it goes "beyond BYOVD by exploiting a zero-day in a driver that's known to be already installed on the target machine." That susceptible driver is appid.sys, which is crucial to the functioning of a Windows component called AppLocker that's responsible for application control.

The real-world exploit devised by the Lazarus Group entails using CVE-2024-21338 in the appid.sys driver to execute arbitrary code in a manner that bypasses all security checks and runs the FudModule rootkit.
"FudModule is only loosely integrated into the rest of Lazarus' malware ecosystem and that Lazarus is very careful about using the rootkit, only deploying it on demand under the right circumstances," security researcher Jan Vojtěšek said, describing the malware as under active development.
Besides taking steps to sidestep detection by disabling system loggers, FudModule is engineered to turn off specific security software such as AhnLab V3 Endpoint Security, CrowdStrike Falcon, HitmanPro, and Microsoft Defender Antivirus (formerly Windows Defender).
The development marks a new level of technical sophistication associated with North Korean hacking groups, continuously iterating its arsenal for improved stealth and functionality. It also illustrates the elaborate techniques employed to hinder detection and make their tracking much harder.
The adversarial collective's cross-platform focus is also exemplified by the fact that it has been observed using bogus calendar meeting invite links to stealthily install malware on Apple macOS systems, a campaign that was previously documented by SlowMist in December 2023.
"Lazarus Group remains among the most prolific and long-standing advanced persistent threat actors," Vojtěšek said. "The FudModule rootkit serves as the latest example, representing one of the most complex tools Lazarus holds in their arsenal."
Raspberry Robin Malware Upgrades with Discord Spread and New Exploits
10.2.24 Exploit The Hacker News
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues to be refined and improved to make it stealthier than before.
This means that "Raspberry Robin has access to an exploit seller or its authors develop the exploits themselves in a short period of time," Check Point said in a report this week.
Raspberry Robin (aka QNAP worm), first documented in 2021, is an evasive malware family that's known to act as one of the top initial access facilitators for other malicious payloads, including ransomware.
Attributed to a threat actor named Storm-0856 (previously DEV-0856), it's propagated via several entry vectors, including infected USB drives, with Microsoft describing it as part of a "complex and interconnected malware ecosystem" with ties to other e-crime groups like Evil Corp, Silence, and TA505.
Raspberry Robin's use of one-day exploits such as CVE-2020-1054 and CVE-2021-1732 for privilege escalation was previously highlighted by Check Point in April 2023.
The cybersecurity firm, which detected "large waves of attacks" since October 2023, said the threat actors have implemented additional anti-analysis and obfuscation techniques to make it harder to detect and analyze.
"Most importantly, Raspberry Robin continues to use different exploits for vulnerabilities either before or only a short time after they were publicly disclosed," it noted.
"Those one-day exploits were not publicly disclosed at the time of their use. An exploit for one of the vulnerabilities, CVE-2023-36802, was also used in the wild as a zero-day and was sold on the dark web."
A report from Cyfirma late last year revealed that an exploit for CVE-2023-36802 was being advertised on dark web forums in February 2023. This was seven months before Microsoft and CISA released an advisory on active exploitation. It was patched by the Windows maker in September 2023.

Raspberry Robin is said to have started utilizing an exploit for the flaw sometime in October 2023, the same month a public exploit code was made available, as well as for CVE-2023-29360 in August. The latter was publicly disclosed in June 2023, but an exploit for the bug did not appear until September 2023.
It's assessed that the threat actors purchase these exploits rather than developing them in-house owing to the fact that they are used as an external 64-bit executable and are not as heavily obfuscated as the malware's core module.
"Raspberry Robin's ability to quickly incorporate newly disclosed exploits into its arsenal further demonstrates a significant threat level, exploiting vulnerabilities before many organizations have applied patches," the company said.
One of the other significant changes concerns the initial access pathway itself, leveraging rogue RAR archive files containing Raspberry Robin samples that are hosted on Discord.
Also modified in the newer variants is the lateral movement logic, which now uses PAExec.exe instead of PsExec.exe, and the command-and-control (C2) communication method by randomly choosing a V3 onion address from a list of 60 hardcoded onion addresses.
"It starts with trying to contact legitimate and well-known Tor domains and checking if it gets any response," Check Point explained. "If there is no response, Raspberry Robin doesn't try to communicate with the real C2 servers."
Fortinet Warns of Critical FortiOS SSL VPN Flaw Likely Under Active Exploitation
9.2.24 Exploit The Hacker News
Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in the wild.
The vulnerability, CVE-2024-21762 (CVSS score: 9.6), allows for the execution of arbitrary code and commands.
"A out-of-bounds write vulnerability [CWE-787] in FortiOS may allow a remote unauthenticated attacker to execute arbitrary code or command via specially crafted HTTP requests," the company said in a bulletin released Thursday.
It further acknowledged that the issue is "potentially being exploited in the wild," without giving additional specifics about how it's being weaponized and by whom.
The following versions are impacted by the vulnerability. It's worth noting that FortiOS 7.6 is not affected.
FortiOS 7.4 (versions 7.4.0 through 7.4.2) - Upgrade to 7.4.3 or above
FortiOS 7.2 (versions 7.2.0 through 7.2.6) - Upgrade to 7.2.7 or above
FortiOS 7.0 (versions 7.0.0 through 7.0.13) - Upgrade to 7.0.14 or above
FortiOS 6.4 (versions 6.4.0 through 6.4.14) - Upgrade to 6.4.15 or above
FortiOS 6.2 (versions 6.2.0 through 6.2.15) - Upgrade to 6.2.16 or above
FortiOS 6.0 (versions 6.0 all versions) - Migrate to a fixed release
The development comes as Fortinet issued patches for CVE-2024-23108 and CVE-2024-23109, impacting FortiSIEM supervisor, allowing a remote unauthenticated attacker to execute unauthorized commands via crafted API requests.
Earlier this week, the Netherlands government revealed a computer network used by the armed forces was infiltrated by Chinese state-sponsored actors by exploiting known flaws in Fortinet FortiGate devices to deliver a backdoor called COATHANGER.
The company, in a report published this week, divulged that N-day security vulnerabilities in its software, such as CVE-2022-42475 and CVE-2023-27997, are being exploited by multiple activity clusters to target governments, service providers, consultancies, manufacturing, and large critical infrastructure organizations.
Previously, Chinese threat actors have been linked to the zero-day exploitation of security flaws in Fortinet appliances to deliver a wide range of implants, such as BOLDMOVE, THINCRUST, and CASTLETAP.
It also follows an advisory from the U.S. government about a Chinese nation-state group dubbed Volt Typhoon, which has targeted critical infrastructure in the country for long-term undiscovered persistence by taking advantage of known and zero-day flaws in networking appliances such as those from Fortinet, Ivanti Connect Secure, NETGEAR, Citrix, and Cisco for initial access.
China, which has denied the allegations, accused the U.S. of conducting its own cyber attacks.
If anything, the campaigns waged by China and Russia underscore the growing threat faced by internet-facing edge devices in recent years owing to the fact that such technologies lack endpoint detection and response (EDR) support, making them ripe for abuse.
"These attacks demonstrate the use of already resolved N-day vulnerabilities and subsequent [living-off-the-land] techniques, which are highly indicative of the behavior employed by the cyber actor or group of actors known as Volt Typhoon, which has been using these methods to target critical infrastructure and potentially other adjacent actors," Fortinet said.
Critical Patches Released for New Flaws in Cisco, Fortinet, VMware Products
8.2.24 Exploit The Hacker News
Cisco, Fortinet, and VMware have released security fixes for multiple security vulnerabilities, including critical weaknesses that could be exploited to perform arbitrary actions on affected devices.
The first set from Cisco consists of three flaws – CVE-2024-20252 and CVE-2024-20254 (CVSS score: 9.6) and CVE-2024-20255 (CVSS score: 8.2) – impacting Cisco Expressway Series that could allow an unauthenticated, remote attacker to conduct cross-site request forgery (CSRF) attacks.
All the issues, which were found during internal security testing, stem from insufficient CSRF protections for the web-based management interface that could permit an attacker to perform arbitrary actions with the privilege level of the affected user.
"If the affected user has administrative privileges, these actions could include modifying the system configuration and creating new privileged accounts," Cisco said about CVE-2024-20252 and CVE-2024-20254.
On the other hand, successful exploitation of CVE-2024-20255 targeting a user with administrative privileges could enable the threat actor to overwrite system configuration settings, resulting in a denial-of-service (DoS) condition.
Another crucial difference between the two sets of flaws is that while the former two affect Cisco Expressway Series devices in the default configuration, CVE-2024-20252 only impacts them if the cluster database (CDB) API feature has been enabled. It's disabled by default.
Patches for the vulnerabilities are available in Cisco Expressway Series Release versions 14.3.4 and 15.0.0.
Fortinet, for its part, has released a second round of updates to address what are bypasses for a previously disclosed critical flaw (CVE-2023-34992, CVSS score: 9.7) in FortiSIEM supervisor that could result in the execution of arbitrary code, according to Horizon3.ai researcher Zach Hanley.
Tracked as CVE-2024-23108 and CVE-2024-23109 (CVSS scores: 9.8), the flaws "may allow a remote unauthenticated attacker to execute unauthorized commands via crafted API requests."
It's worth noting that Fortinet resolved another variant of CVE-2023-34992 by closing out CVE-2023-36553 (CVSS score: 9.3) in November 2023. The two new vulnerabilities are/will be plugged in the following versions -
FortiSIEM version 7.1.2 or above
FortiSIEM version 7.2.0 or above (upcoming)
FortiSIEM version 7.0.3 or above (upcoming)
FortiSIEM version 6.7.9 or above (upcoming)
FortiSIEM version 6.6.5 or above (upcoming)
FortiSIEM version 6.5.3 or above (upcoming), and
FortiSIEM version 6.4.4 or above (upcoming)
Completing the trifecta is VMware, which has warned of five moderate-to-important severity flaws in Aria Operations for Networks (formerly vRealize Network Insight) -
CVE-2024-22237 (CVSS score: 7.8) - Local privilege escalation vulnerability that allows a console user to gain regular root access
CVE-2024-22238 (CVSS score: 6.4) - Cross-site scripting (XSS) vulnerability that allows a malicious actor with admin privileges to inject malicious code into user profile configurations
CVE-2024-22239 (CVSS score: 5.3) - Local privilege escalation vulnerability that allows a console user to gain regular shell access
CVE-2024-22240 (CVSS score: 4.9) - Local file read vulnerability that allows a malicious actor with admin privileges to access sensitive information
CVE-2024-22241 (CVSS score: 4.3) - Cross-site scripting (XSS) vulnerability that allows a malicious actor with admin privileges to inject malicious code and take over the user account
To mitigate the risks, all users of VMware Aria Operations for Networks version 6.x are being recommended to upgrade to version 6.12.0.
Considering the history of exploitation when it comes to Cisco, Fortinet, and VMware flaws, patching is a necessary and crucial first step that organizations need to take to handle the shortcomings.
Chinese Hackers Exploited FortiGate Flaw to Breach Dutch Military Network
7.2.24 Exploit The Hacker News
Chinese state-backed hackers broke into a computer network that's used by the Dutch armed forces by targeting Fortinet FortiGate devices.
"This [computer network] was used for unclassified research and development (R&D)," the Dutch Military Intelligence and Security Service (MIVD) said in a statement. "Because this system was self-contained, it did not lead to any damage to the defense network." The network had less than 50 users.
The intrusion, which took place in 2023, leveraged a known critical security flaw in FortiOS SSL-VPN (CVE-2022-42475, CVSS score: 9.3) that allows an unauthenticated attacker to execute arbitrary code via specially crafted requests.
Successful exploitation of the flaw paved the way for the deployment of a backdoor dubbed COATHANGER from an actor-controlled server that's designed to grant persistent remote access to the compromised appliances.
"The COATHANGER malware is stealthy and persistent," the Dutch National Cyber Security Centre (NCSC) said. "It hides itself by hooking system calls that could reveal its presence. It survives reboots and firmware upgrades."
COATHANGER is distinct from BOLDMOVE, another backdoor linked to a suspected China-based threat actor that's known to have exploited CVE-2022-42475 as a zero-day in attacks targeting a European government entity and a managed service provider (MSP) located in Africa as early as October 2022.
The development marks the first time the Netherlands has publicly attributed a cyber espionage campaign to China. Reuters, which broke the story, said the malware is named after a code snippet that contained a line from Lamb to the Slaughter, a short story by British author Roald Dahl.
It also arrives days after U.S. authorities took steps to dismantle a botnet comprising out-of-date Cisco and NetGear routers that were used by Chinese threat actors like Volt Typhoon to conceal the origins of malicious traffic.
Last year, Google-owned Mandiant revealed that a China-nexus cyber espionage group tracked as UNC3886 exploited zero-days in Fortinet appliances to deploy THINCRUST and CASTLETAP implants for executing arbitrary commands received from a remote server and exfiltrating sensitive data.
Recent SSRF Flaw in Ivanti VPN Products Undergoes Mass Exploitation
6.2.24 Exploit The Hacker News
A recently disclosed server-side request forgery (SSRF) vulnerability impacting Ivanti Connect Secure and Policy Secure products has come under mass exploitation.
The Shadowserver Foundation said it observed exploitation attempts originating from more than 170 unique IP addresses that aim to establish a reverse shell, among others.
The attacks exploit CVE-2024-21893 (CVSS score: 8.2), an SSRF flaw in the SAML component of Ivanti Connect Secure, Policy Secure, and Neurons for ZTA that allows an attacker to access otherwise restricted resources without authentication.
Ivanti had previously divulged that the vulnerability had been exploited in targeted attacks aimed at a "limited number of customers," but cautioned the status quo could change post public disclosure.
That's exactly what appears to have happened, especially following the release of a proof-of-concept (PoC) exploit by cybersecurity firm Rapid7 last week.
The PoC involves fashioning an exploit chain that combines CVE-2024-21893 with CVE-2024-21887, a previously patched command injection flaw, to achieve unauthenticated remote code execution.
It's worth noting here that CVE-2024-21893 is an alias for CVE-2023-36661 (CVSS score: 7.5), an SSRF vulnerability present in the open-source Shibboleth XMLTooling library. It was fixed by the maintainers in June 2023 with the release of version 3.2.4.
Security researcher Will Dormann further pointed out other out-of-date open-source components used by Ivanti VPN appliances, such as curl 7.19.7, openssl 1.0.2n-fips, perl 5.6.1, psql 9.6.14, cabextract 0.5, ssh 5.3p1, and unzip 6.00, thus opening the door for more attacks.
The development comes as threat actors have found a way to bypass Ivanti's initial mitigation, prompting the Utah-based company to release a second mitigation file. As of February 1, 2024, it has begun releasing official patches to address all the vulnerabilities.
Last week, Google-owned Mandiant revealed that several threat actors are leveraging CVE-2023-46805 and CVE-2024-21887 to deploy an array of custom web shells tracked as BUSHWALK, CHAINLINE, FRAMESTING, and LIGHTWIRE.
Palo Alto Networks Unit 42 said it observed 28,474 exposed instances of Ivanti Connect Secure and Policy Secure in 145 countries between January 26 and 30, 2024, with 610 compromised instances detected in 44 countries as of January 23, 2024.
New Mispadu Banking Trojan Exploiting Windows SmartScreen Flaw
5.2.24 Exploit The Hacker News
The threat actors behind the Mispadu banking Trojan have become the latest to exploit a now-patched Windows SmartScreen security bypass flaw to compromise users in Mexico.
The attacks entail a new variant of the malware that was first observed in 2019, Palo Alto Networks Unit 42 said in a report published last week.
Propagated via phishing mails, Mispadu is a Delphi-based information stealer known to specifically infect victims in the Latin American (LATAM) region. In March 2023, Metabase Q revealed that Mispadu spam campaigns harvested no less than 90,000 bank account credentials since August 2022.
It's also part of the larger family of LATAM banking malware, including Grandoreiro, which was dismantled by Brazilian law enforcement authorities last week.
The latest infection chain identified by Unit 42 employs rogue internet shortcut files contained within bogus ZIP archive files that leverage CVE-2023-36025 (CVSS score: 8.8), a high-severity bypass flaw in Windows SmartScreen. It was addressed by Microsoft in November 2023.
"This exploit revolves around the creation of a specifically crafted internet shortcut file (.URL) or a hyperlink pointing to malicious files that can bypass SmartScreen's warnings," security researchers Daniela Shalev and Josh Grunzweig said.
"The bypass is simple and relies on a parameter that references a network share, rather than a URL. The crafted .URL file contains a link to a threat actor's network share with a malicious binary."
Mispadu, once launched, reveals its true colors by selectively targeting victims based on their geographic location (i.e., Americas or Western Europe) and system configurations, and then proceeds to establish contact with a command-and-control (C2) server for follow-on data exfiltration.
In recent months, the Windows flaw has been exploited in the wild by multiple cybercrime groups to deliver DarkGate and Phemedrone Stealer malware in recent months.
Mexico has also emerged as a top target for several campaigns over the past year that have been found to propagate information stealers and remote access trojans like AllaKore RAT, AsyncRAT, Babylon RAT. This constitutes a financially-motivated group dubbed TA558 that has attacked the hospitality and travel sectors in the LATAM region since 2018.
The development comes as Sekoia detailed the inner workings of DICELOADER (aka Lizar or Tirion), a time-tested custom downloader used by the Russian e-crime group tracked as FIN7. The malware has been observed delivered via malicious USB drives (aka BadUSB) in the past.
"DICELOADER is dropped by a PowerShell script along with other malware of the intrusion set's arsenal such as Carbanak RAT," the French cybersecurity firm said, calling out its sophisticated obfuscation methods to conceal the C2 IP addresses and the network communications.
It also follows AhnLab's discovery of two new malicious cryptocurrency mining campaigns that employ booby-trapped archives and game hacks to deploy miner malware that mine Monero and Zephyr.
Warning: New Malware Emerges in Attacks Exploiting Ivanti VPN Vulnerabilities
2.2.24 Exploit The Hacker News
Google-owned Mandiant said it identified new malware employed by a China-nexus espionage threat actor known as UNC5221 and other threat groups during post-exploitation activity targeting Ivanti Connect Secure VPN and Policy Secure devices.
This includes custom web shells such as BUSHWALK, CHAINLINE, FRAMESTING, and a variant of LIGHTWIRE.
"CHAINLINE is a Python web shell backdoor that is embedded in a Ivanti Connect Secure Python package that enables arbitrary command execution," the company said, attributing it to UNC5221, adding it also detected multiple new versions of WARPWIRE, a JavaScript-based credential stealer.
The infection chains entail a successful exploitation of CVE-2023-46805 and CVE-2024-21887, which allow an unauthenticated threat actor to execute arbitrary commands on the Ivanti appliance with elevated privileges.
The flaws have been abused as zero-days since early December 2023. Germany's Federal Office for Information Security (BSI) said it's aware of "multiple compromised systems" in the country.
BUSHWALK, written in Perl and deployed by circumventing the Ivanti-issued mitigations in highly-targeted attacks, is embedded into a legitimate Connect Secure file named "querymanifest.cgi" and offers the ability to read or write to files to a server.
On the other hand, FRAMESTING is a Python web shell embedded in an Ivanti Connect Secure Python package (located in the following path "/home/venv3/lib/python3.6/site-packages/cav-0.1-py3.6.egg/cav/api/resources/category.py") that enables arbitrary command execution.
Mandiant's analysis of the ZIPLINE passive backdoor has also uncovered its use of "extensive functionality to ensure the authentication of its custom protocol used to establish command-and-control (C2)."
Furthermore, the attacks are characterized by the use of open-source utilities like Impacket, CrackMapExec, iodine, and Enum4linux to support post-exploitation activity on Ivanti CS appliances, including network reconnaissance, lateral movement, and data exfiltration within victim environments.
Ivanti has since disclosed two more security flaws, CVE-2024-21888 and CVE-2024-21893, the latter of which has come under active exploitation targeting a "limited number of customers." The company has also released the first round of fixes to address the four vulnerabilities.
UNC5221 is said to target a wide range of industries that are of strategic interest to China, with its infrastructure and tooling overlapping with past intrusions linked to China-based espionage actors.
"Linux-based tools identified in incident response investigations use code from multiple Chinese-language Github repositories," Mandiant said. "UNC5221 has largely leveraged TTPs associated with zero-day exploitation of edge infrastructure by suspected PRC nexus actors."
RunC Flaws Enable Container Escapes, Granting Attackers Host Access
1.2.24 Exploit The Hacker News
Multiple security vulnerabilities have been disclosed in the runC command line tool that could be exploited by threat actors to escape the bounds of the container and stage follow-on attacks.
The vulnerabilities, tracked as CVE-2024-21626, CVE-2024-23651, CVE-2024-23652, and CVE-2024-23653, have been collectively dubbed Leaky Vessels by cybersecurity vendor Snyk.
"These container escapes could allow an attacker to gain unauthorized access to the underlying host operating system from within the container and potentially permit access to sensitive data (credentials, customer info, etc.), and launch further attacks, especially when the access gained includes superuser privileges," the company said in a report shared with The Hacker News.
runC is a tool for spawning and running containers on Linux. It was originally developed as part of Docker and later spun out into a separate open-source library in 2015.
A brief description of each of the flaws is below -
CVE-2024-21626 - WORKDIR: Order of operations container breakout
CVE-2024-23651 - Mount Cache Race
CVE-2024-23652 - Buildkit Build-time Container Teardown Arbitrary Delete
CVE-2024-23653 - Buildkit GRPC SecurityMode Privilege Check
The most severe of the flaws is CVE-2024-21626, which could result in a container escape centered around the `WORKDIR` command.
"This could occur by running a malicious image or by building a container image using a malicious Dockerfile or upstream image (i.e. when using `FROM`)," Snyk said.
There is no evidence that any of the newly discovered shortcomings have been exploited in the wild to date. That said, the issues have been addressed in runC version 1.1.12 released today.
"Because these vulnerabilities affect widely used low-level container engine components and container build tools, Snyk strongly recommends that users check for updates from any vendors providing their container runtime environments, including Docker, Kubernetes vendors, cloud container services, and open source communities," the company said.
In February 2019, runC maintainers addressed another high-severity flaw (CVE-2019-5736, CVSS score: 8.6) that could be abused by an attacker to break out of the container and obtain root access on the host.
Alert: Ivanti Discloses 2 New Zero-Day Flaws, One Under Active Exploitation
1.2.24 Exploit The Hacker News
Ivanti is alerting of two new high-severity flaws in its Connect Secure and Policy Secure products, one of which is said to have come under targeted exploitation in the wild.
The list of vulnerabilities is as follows -
CVE-2024-21888 (CVSS score: 8.8) - A privilege escalation vulnerability in the web component of Ivanti Connect Secure (9.x, 22.x) and Ivanti Policy Secure (9.x, 22.x) allows a user to elevate privileges to that of an administrator
CVE-2024-21893 (CVSS score: 8.2) - A server-side request forgery vulnerability in the SAML component of Ivanti Connect Secure (9.x, 22.x), Ivanti Policy Secure (9.x, 22.x) and Ivanti Neurons for ZTA allows an attacker to access certain restricted resources without authentication
The Utah-based software company said it found no evidence of customers being impacted by CVE-2024-21888 so far, but acknowledged "the exploitation of CVE-2024-21893 appears to be targeted."
It further noted that it "expects the threat actor to change their behavior and we expect a sharp increase in exploitation once this information is public."
In tandem to the public disclosure of the two new vulnerabilities, Ivanti has released fixes for Connect Secure versions 9.1R14.4, 9.1R17.2, 9.1R18.3, 22.4R2.2 and 22.5R1.1, and ZTA version 22.6R1.3.
"Out of an abundance of caution, we are recommending as a best practice that customers factory reset their appliance before applying the patch to prevent the threat actor from gaining upgrade persistence in your environment," it said. "Customers should expect this process to take 3-4 hours."
As temporary workarounds to address CVE-2024-21888 and CVE-2024-21893, users are recommended to import the "mitigation.release.20240126.5.xml" file.
The latest development comes as two other flaws in the same product – CVE-2023-46805 and CVE-2024-21887 – have come under broad exploitation by multiple threat actors to deploy backdoors, cryptocurrency miners, and a Rust-based loader called KrustyLoader.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA), in a fresh advisory published today, said adversaries are leveraging the two shortcomings to capture credentials and drop web shells that enable further compromise of enterprise networks.
"Some threat actors have recently developed workarounds to current mitigations and detection methods and have been able to exploit weaknesses, move laterally, and escalate privileges without detection," the agency said.
"Sophisticated threat actors have subverted the external integrity checker tool (ICT), further minimizing traces of their intrusion."
CISA Issues Emergency Directive to Federal Agencies on Ivanti Zero-Day Exploits
20.1.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive urging Federal Civilian Executive Branch (FCEB) agencies to implement mitigations against two actively exploited zero-day flaws in Ivanti Connect Secure (ICS) and Ivanti Policy Secure (IPS) products.
The development came after the vulnerabilities – an authentication bypass (CVE-2023-46805) and a code injection bug (CVE-2024-21887) – came under widespread exploitation of vulnerabilities by multiple threat actors. The flaws allow a malicious actor to craft malicious requests and execute arbitrary commands on the system.
The U.S. company acknowledged in an advisory that it has witnessed a "sharp increase in threat actor activity" starting on January 11, 2024, after the shortcomings were publicly disclosed.
"Successful exploitation of the vulnerabilities in these affected products allows a malicious threat actor to move laterally, perform data exfiltration, and establish persistent system access, resulting in full compromise of target information systems," the agency said.
Ivanti, which is expected to release an update to address the flaws next week, has made available a temporary workaround through an XML file that can be imported into affected products to make necessary configuration changes.
CISA is urging organizations running ICS to apply the mitigation and run an External Integrity Checker Tool to identify signs of compromise, and if found, disconnect them from the networks and reset the device, followed by importing the XML file.
In addition, FCEB entities are urged to revoke and reissue any stored certificates, reset the admin enable password, store API keys, and reset the passwords of any local user defined on the gateway.
Cybersecurity firms Volexity and Mandiant have observed attacks weaponizing the twin flaws to deploy web shells and passive backdoors for persistent access to compromised appliances. As many as 2,100 devices worldwide are estimated to have been compromised to date.
The initial attack wave identified in December 2023 has been attributed to a Chinese nation-state group that is being tracked as UTA0178. Mandiant is keeping tabs on the activity under the moniker UNC5221, although it has not been linked to any specific group or country.
Threat intelligence firm GreyNoise said it has also observed the vulnerabilities being abused to drop persistent backdoors and XMRig cryptocurrency miners, indicating opportunistic exploitation by bad actors for financial gain.
Zero-Day Alert: Update Chrome Now to Fix New Actively Exploited Vulnerability
17.1.24 Exploit The Hacker News
Google on Tuesday released updates to fix four security issues in its Chrome browser, including an actively exploited zero-day flaw.
The issue, tracked as CVE-2024-0519, concerns an out-of-bounds memory access in the V8 JavaScript and WebAssembly engine, which can be weaponized by threat actors to trigger a crash.
"By reading out-of-bounds memory, an attacker might be able to get secret values, such as memory addresses, which can be bypass protection mechanisms such as ASLR in order to improve the reliability and likelihood of exploiting a separate weakness to achieve code execution instead of just denial of service," according to MITRE's Common Weakness Enumeration (CWE).
Additional details about the nature of the attacks and the threat actors that may be exploiting them have withheld in an attempt to prevent further exploitation. The issue was reported anonymously on January 11, 2024.
"Out-of-bounds memory access in V8 in Google Chrome prior to 120.0.6099.224 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page," reads a description of the flaw on the NIST's National Vulnerability Database (NVD).
The development marks the first actively exploited zero-day to be patched by Google in Chrome in 2024. Last year, the tech giant resolved a total of 8 such actively exploited zero-days in the browser.
Users are recommended to upgrade to Chrome version 120.0.6099.224/225 for Windows, 120.0.6099.234 for macOS, and 120.0.6099.224 for Linux to mitigate potential threats.
Users of Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi are also advised to apply the fixes as and when they become available.
Alert: Over 178,000 SonicWall Firewalls Potentially Vulnerable to Exploits - Act Now
17.1.24 Exploit The Hacker News
Over 178,000 SonicWall firewalls exposed over the internet are exploitable to at least one of the two security flaws that could be potentially exploited to cause a denial-of-service (DoS) condition and remote code execution (RCE).
"The two issues are fundamentally the same but exploitable at different HTTP URI paths due to reuse of a vulnerable code pattern," Jon Williams, a senior security engineer at Bishop Fox, said in a technical analysis shared with The Hacker News.
The vulnerabilities in question are listed below -
CVE-2022-22274 (CVSS score: 9.4) - A stack-based buffer overflow vulnerability in the SonicOS via HTTP request allows a remote, unauthenticated attacker to cause DoS or potentially result in code execution in the firewall.
CVE-2023-0656 (CVSS score: 7.5) - A stack-based buffer overflow vulnerability in the SonicOS allows a remote, unauthenticated attacker to cause DoS, which could result in a crash.
While there are no reports of exploitation of the flaws in the wild, a proof-of-concept (PoC) for CVE-2023-0656 was published by the SSD Secure Disclosure team in April 2023.
The cybersecurity firm revealed that the issues could be weaponized by bad actors to trigger repeated crashes and force the appliance to get into maintenance mode, requiring administrative action to restore normal functionality.
"Perhaps most astonishing was the discovery that over 146,000 publicly-accessible devices are vulnerable to a bug that was published almost two years ago," Williams said.
The development comes as watchTowr Labs uncovered multiple stack-based buffer overflow flaws in the SonicOS management web interface and SSL VPN portal that could lead to a firewall crash.
To safeguard against possible threats, it's recommended to update to the last version and ensure that the management interface isn't exposed to the internet.
Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families
13.1.24 Exploit The Hacker News
As many as five different malware families were deployed by suspected nation-state actors as part of post-exploitation activities leveraging two zero-day vulnerabilities in Ivanti Connect Secure (ICS) VPN appliances since early December 2023.
"These families allow the threat actors to circumvent authentication and provide backdoor access to these devices," Mandiant said in an analysis published this week. The Google-owned threat intelligence firm is tracking the threat actor under the moniker UNC5221.
The attacks leverage an exploit chain comprising an authentication bypass flaw (CVE-2023-46805) and a code injection vulnerability (CVE-2024-21887) to take over susceptible instances.
Volexity, which attributed the activity to a suspected Chinese espionage actor named UTA0178, said the twin flaws were used to gain initial access, deploy webshells, backdoor legitimate files, capture credentials and configuration data, and pivot further into the victim environment.
According to Ivanti, the intrusions impacted less than 10 customers, indicating that this could be a highly-targeted campaign. Patches for the two vulnerabilities (informally called ConnectAround) are expected to become available in the week of January 22.
Mandiant's analysis of the attacks has revealed the presence of five different custom malware families, besides injecting malicious code into legitimate files within ICS and using other legitimate tools like BusyBox and PySoxy to facilitate subsequent activity.
"Due to certain sections of the device being read-only, UNC5221 leveraged a Perl script (sessionserver.pl) to remount the filesystem as read/write and enable the deployment of THINSPOOL, a shell script dropper that writes the web shell LIGHTWIRE to a legitimate Connect Secure file, and other follow-on tooling," the company said.
LIGHTWIRE is one of the two web shells, the other being WIREFIRE, which are "lightweight footholds" designed to ensure persistent remote access to compromised devices. While LIGHTWIRE is written in Perl CGI, WIREFIRE is implemented in Python.
Also used in the attacks are a JavaScript-based credential stealer dubbed WARPWIRE and a passive backdoor named ZIPLINE that's capable of downloading/uploading files, establishing a reverse shell, creating a proxy server, and setting up a tunneling server to dispatch traffic between multiple endpoints.
"This indicates that these are not opportunistic attacks, and UNC5221 intended to maintain its presence on a subset of high priority targets that it compromised after a patch was inevitably released," Mandiant further added.
UNC5221 has not been linked to any previously known group or a particular country, although the targeting of edge infrastructure by weaponizing zero-day flaws and the use of compromise command-and-control (C2) infrastructure to bypass detection bears all the hallmarks of an advanced persistent threat (APT).
"UNC5221's activity demonstrates that exploiting and living on the edge of networks remains a viable and attractive target for espionage actors," Mandiant said.
Act Now: CISA Flags Active Exploitation of Microsoft SharePoint Vulnerability
12.1.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security vulnerability impacting Microsoft SharePoint Server to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.
The issue, tracked as CVE-2023-29357 (CVSS score: 9.8), is a privilege escalation flaw that could be exploited by an attacker to gain administrator privileges. Microsoft released patches for the bug as part of its June 2023 Patch Tuesday updates.
"An attacker who has gained access to spoofed JWT authentication tokens can use them to execute a network attack which bypasses authentication and allows them to gain access to the privileges of an authenticated user," Redmond said. "The attacker needs no privileges nor does the user need to perform any action."
Security researcher Nguyễn Tiến Giang (Jang) of StarLabs SG demonstrated an exploit for the flaw at the Pwn2Own Vancouver hacking contest last year, earning a $100,000 prize.
The pre-authenticated remote code execution chain combines authentication bypass (CVE-2023–29357) with a code injection bug (CVE-2023-24955, CVSS score: 7.2), the latter of which was patched by Microsoft in May 2023.
"The process of discovering and crafting the exploit chain consumed nearly a year of meticulous effort and research to complete the full exploit chain," Tiến Giang noted in a technical report published in September 2023.
Additional specifics of the real-world exploitation of CVE-2023–29357 and the identity of the threat actors that may be abusing them are presently unknown. That said, federal agencies are recommended to apply the patches by January 31, 2024, to secure against the active threat.
New PoC Exploit for Apache OfBiz Vulnerability Poses Risk to ERP Systems
12.1.24 Exploit The Hacker News
Cybersecurity researchers have developed a proof-of-concept (PoC) code that exploits a recently disclosed critical flaw in the Apache OfBiz open-source Enterprise Resource Planning (ERP) system to execute a memory-resident payload.
The vulnerability in question is CVE-2023-51467 (CVSS score: 9.8), a bypass for another severe shortcoming in the same software (CVE-2023-49070, CVSS score: 9.8) that could be weaponized to bypass authentication and remotely execute arbitrary code.
While it was fixed in Apache OFbiz version 18.12.11 released last month, threat actors have been observed attempting to exploit the flaw, targeting vulnerable instances.
The latest findings from VulnCheck show that CVE-2023-51467 can be exploited to execute a payload directly from memory, leaving little to no traces of malicious activity.
Security flaws disclosed in Apache OFBiz (e.g., CVE-2020-9496) have been exploited by threat actors in the past, including by threat actors associated with the Sysrv botnet. Another three-year-old bug in the software (CVE-2021-29200) has witnessed exploitation attempts from 29 unique IP addresses over the past 30 days, per data from GreyNoise.
What's more, Apache OFBiz was also one of the first products to have a public exploit for Log4Shell (CVE-2021-44228), illustrating that it continues to be of interest to both defenders and attackers alike.

CVE-2023-51467 is no exception, with details about a remote code execution endpoint ("/webtools/control/ProgramExport") as well as PoC for command execution emerging merely days after public disclosure.
While security guardrails (i.e., Groovy sandbox) have been erected such that they block any attempts to upload arbitrary web shells or run Java code via the endpoint, the incomplete nature of the sandbox means that an attacker could run curl commands and obtain a bash reverse shell on Linux systems.
"For an advanced attacker, though, these payloads aren't ideal," VulnCheck's Chief Technology Officer Jacob Baines said. "They touch the disk and rely on Linux-specific behavior."
The Go-based exploit devised by VulnCheck is a cross-platform solution that works on both Windows and Linux as well as gets around the denylist by taking advantage of groovy.util.Eval functions to launch an in-memory Nashorn reverse shell as the payload.
"OFBiz is not widely popular, but it has been exploited in the past. There is a fair deal of hype around CVE-2023-51467 but no public weaponized payload, which called into question if it was even possible," Baines said. "We've concluded that not only is it possible, but we can achieve arbitrary in memory code execution."
Turkish Hackers Exploiting Poorly Secured MS SQL Servers Across the Globe
10.1.24 Exploit The Hacker News
Poorly secured Microsoft SQL (MS SQL) servers are being targeted in the U.S., European Union, and Latin American (LATAM) regions as part of an ongoing financially motivated campaign to gain initial access.
"The analyzed threat campaign appears to end in one of two ways, either the selling of 'access' to the compromised host, or the ultimate delivery of ransomware payloads," Securonix researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a technical report shared with The Hacker News.
The campaign, linked to actors of Turkish origin, has been codenamed RE#TURGENCE by the cybersecurity firm.
Initial access to the servers entails conducting brute-force attacks, followed by the use of xp_cmdshell configuration option to run shell commands on the compromised host. This activity mirrors that of a prior campaign dubbed DB#JAMMER that came to light in September 2023.
This stage paves the way for the retrieval of a PowerShell script from a remote server that's responsible for fetching an obfuscated Cobalt Strike beacon payload.
The post-exploitation toolkit is then used to download the AnyDesk remote desktop application from a mounted network share for accessing the machine and downloading additional tools such as Mimikatz to harvest credentials and Advanced Port Scanner to carry out reconnaissance.

Lateral movement is accomplished by means of a legitimate system administration utility called PsExec, which can execute programs on remote Windows hosts.
That attack chain, ultimately, culminates with the deployment of Mimic ransomware, a variant of which was also used in the DB#JAMMER campaign.
“The indicators as well as malicious TTPs used in the two campaigns are completely different, so there is a very high chance these are two disparate campaigns,” Kolesnikov told The Hacker News.
“More specifically, while the initial infiltration methods are similar, DB#JAMMER was slightly more sophisticated and used tunneling. RE#TURGENCE is more targeted and tends to use legitimate tools and remote monitoring and management, such as AnyDesk, in an attempt to blend in with normal activity.”
Securonix said it uncovered an operational security (OPSEC) blunder made by the threat actors that allowed it to monitor clipboard activity owing to the fact that the clipboard sharing feature of AnyDesk was enabled.
This made it possible to glean their Turkish origins and their online alias atseverse, which also corresponds to a profile on Steam and a Turkish hacking forum called SpyHack.
"Always refrain from exposing critical servers directly to the internet," the researchers cautioned. "With the case of RE#TURGENCE attackers were directly able to brute force their way into the server from outside the main network."
SMTP Smuggling: New Flaw Lets Attackers Bypass Security and Spoof Emails
3.1.24 Exploit The Hacker News
A new exploitation technique called Simple Mail Transfer Protocol (SMTP) smuggling can be weaponized by threat actors to send spoofed emails with fake sender addresses while bypassing security measures.
"Threat actors could abuse vulnerable SMTP servers worldwide to send malicious emails from arbitrary email addresses, allowing targeted phishing attacks," Timo Longin, a senior security consultant at SEC Consult, said in an analysis published last month.
SMTP is a TCP/IP protocol used to send and receive email messages over a network. To relay a message from an email client (aka mail user agent), an SMTP connection is established between the client and server in order to transmit the actual content of the email.
The server then relies on what's called a mail transfer agent (MTA) to check the domain of the recipient's email address, and if it's different from that of the sender, it queries the domain name system (DNS) to look up the MX (mail exchanger) record for the recipient's domain and complete the mail exchange.
The crux of SMTP smuggling is rooted in the inconsistencies that arise when outbound and inbound SMTP servers handle end-of-data sequences differently, potentially enabling threat actors to break out of the message data, "smuggle" arbitrary SMTP commands, and even send separate emails.

It borrows the concept from a known attack method referred to as HTTP request smuggling, which takes advantage of discrepancies in the interpretation and processing of the "Content-Length" and "Transfer-Encoding" HTTP headers to prepend an ambiguous request to the inbound request chain.
Specifically, it exploits security flaws in messaging servers from Microsoft, GMX, and Cisco to send emails spoofing millions of domains. Also impacted are SMTP implementations from Postfix and Sendmail.
This allows for sending forged emails that seemingly look like they are originating from legitimate senders and defeat checks in place erected to ensure the authenticity of incoming messages – i.e., DomainKeys Identified Mail (DKIM), Domain-based Message Authentication, Reporting and Conformance (DMARC), and Sender Policy Framework (SPF).
While Microsoft and GMX have rectified the issues, Cisco said the findings do not constitute a "vulnerability, but a feature and that they will not change the default configuration." As a result, inbound SMTP smuggling to Cisco Secure Email instances is still possible with default configurations.
As a fix, SEC Consult recommends Cisco users change their settings from "Clean" to "Allow" in order to avoid receiving spoofed emails with valid DMARC checks.