Hackers Abusing Cloudflare Tunnels for Covert Communications
8.8.23 Hacking The Hacker News
New research has revealed that threat actors are abusing Cloudflare Tunnels to establish covert communication channels from compromised hosts and retain persistent access.
"Cloudflared is functionally very similar to ngrok," Nic Finn, a senior threat intelligence analyst at GuidePoint Security, said. "However, Cloudflared differs from ngrok in that it provides a lot more usability for free, including the ability to host TCP connectivity over cloudflared."
A command-line tool for Cloudflare Tunnel, cloudflared allows users to create secure connections between an origin web server and Cloudflare's nearest data center so as to hide the web server IP addresses as well as block volumetric distributed denial-of-service (DDoS) and brute-force login attacks.
For a threat actor with elevated access on an infected host, this feature presents a lucrative approach to set up a foothold by generating a token required to establish the tunnel from the victim machine.
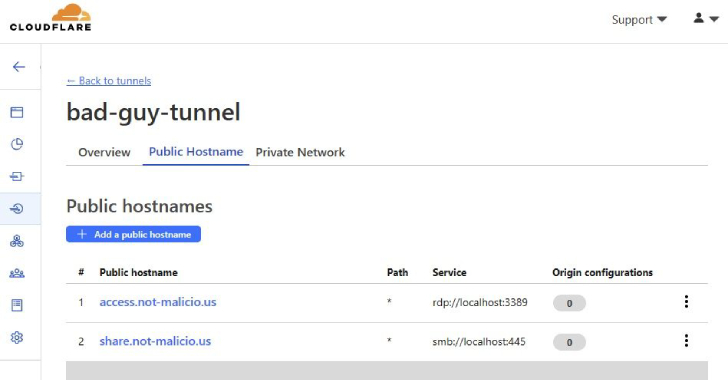
"The tunnel updates as soon as the configuration change is made in the Cloudflare Dashboard, allowing TAs to enable functionality only when they want to conduct activities on the victim machine, then disable functionality to prevent exposure of their infrastructure," Finn explained.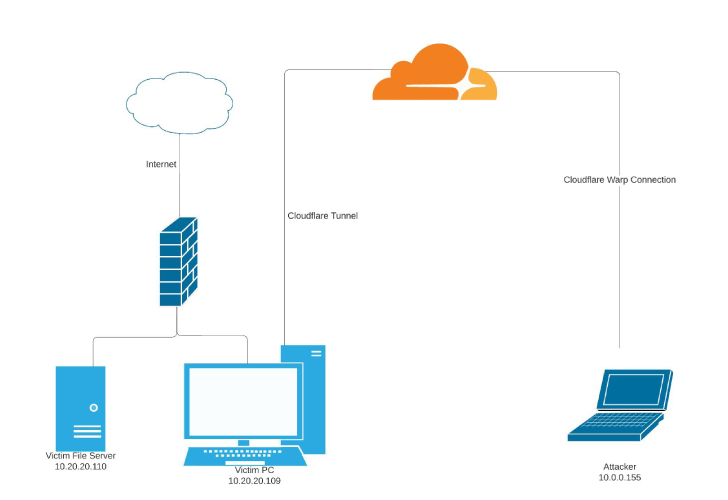
"For example, the TA could enable RDP connectivity, collect information from the victim machine, then disable RDP until the following day, thus lowering the chance of detection or the ability to observe the domain utilized to establish the connection."
Even more troublingly, the adversary could take advantage of the tunnel's Private Networks functionality to stealthily access an range of IP addresses (i.e., endpoints within a local network) as if they were "physically collocated with the victim machine hosting the tunnel."
That said, the technique has already found takers in the wild. Earlier this year, Phylum and Kroll detailed two different software supply chain attacks targeting the Python Package Index (PyPI) repository in which fraudulent packages were observed downloading cloudflared to remotely access the endpoint via a Flask web application.
"Organizations using Cloudflare services legitimately could potentially limit their services to specific data centers and generate detections for traffic like Cloudflared tunnels that route to anywhere except their specified data centers," Finn said. "This method might aid in the detection of unauthorized tunnels."
To identify possible misuse of cloudflared, it's recommended that organizations implement adequate logging mechanisms to monitor for anomalous commands, DNS queries, and outbound connections, alongside blocking attempts to download the executable.