9.11.23 Virus The Hacker News

A new set of malicious Python packages has slithered their way to the Python Package Index (PyPI) repository with the ultimate aim of stealing sensitive information from compromised developer systems.
Beware, Developers: BlazeStealer Malware Discovered in Python Packages on PyPI
9.11.23 Virus The Hacker News
A new set of malicious Python packages has slithered their way to the Python Package Index (PyPI) repository with the ultimate aim of stealing sensitive information from compromised developer systems.
The packages masquerade as seemingly innocuous obfuscation tools, but harbor a piece of malware called BlazeStealer, Checkmarx said in a report shared with The Hacker News.
"[BlazeStealer] retrieves an additional malicious script from an external source, enabling a Discord bot that gives attackers complete control over the victim's computer," security researcher Yehuda Gelb said.
The campaign, which commenced in January 2023, entails a total of eight packages named Pyobftoexe, Pyobfusfile, Pyobfexecute, Pyobfpremium, Pyobflite, Pyobfadvance, Pyobfuse, and pyobfgood, the last of which was published in October.
These modules come with setup.py and init.py files that are designed to retrieve a Python script hosted on transfer[.]sh, which gets executed immediately upon their installation.
Called BlazeStealer, the malware runs a Discord bot and enables the threat actor to harvest a wide range of information, including passwords from web browsers and screenshots, execute arbitrary commands, encrypt files, and deactivate Microsoft Defender Antivirus on the infected host.
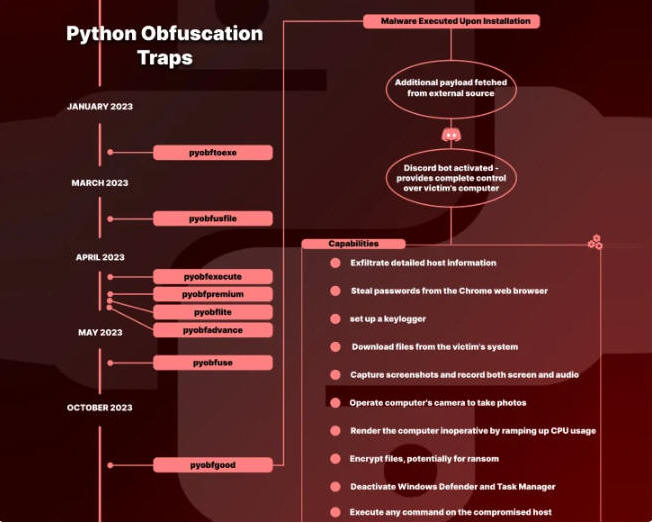
What's more, it can render the computer unusable by ramping up CPU usage, inserting a Windows Batch script in the startup directory to shut down the machine, and even forcing a blue screen of death (BSoD) error.
"It stands to reason that developers engaged in code obfuscation are likely dealing with valuable and sensitive information, and therefore, to a hacker, this translates to a target worth pursuing," Gelb noted.
A majority of downloads associated with the rogue packages originated from the U.S., followed by China, Russia, Ireland, Hong Kong, Croatia, France, and Spain. They were collectively downloaded 2,438 times before being taken down.
"The open-source domain remains a fertile ground for innovation, but it demands caution," Gelb said. "Developers must remain vigilant, and vet the packages prior to consumption."
The development comes as software supply chain security firm Phylum discovered a collection of crypto-themed npm modules – puma-com, erc20-testenv, blockledger, cryptotransact, and chainflow – with capabilities to stealthily deliver a next-stage malware.
In recent years, open-source repositories have emerged as a lucrative way for threat actors to spread malware. According to Phylum's Evolution of Software Supply Chain Security Report for Q3 2023, 13,708 packages across multiple ecosystems were found to execute suspicious code during installation.
"1,481 packages surreptitiously downloaded and executed code from a remote source," the company said last month. "10,201 packages referenced known malicious URLs, [and] 2,598 typosquat packages were identified."