13.10.23 Virus The Hacker News

A malicious package hosted on the NuGet package manager for the .NET Framework has been found to deliver a remote access trojan called SeroXen RAT.
Malicious NuGet Package Targeting .NET Developers with SeroXen RAT
13.10.23 Virus The Hacker News
A malicious package hosted on the NuGet package manager for the .NET Framework has been found to deliver a remote access trojan called SeroXen RAT.
The package, named Pathoschild.Stardew.Mod.Build.Config and published by a user named Disti, is a typosquat of a legitimate package called Pathoschild.Stardew.ModBuildConfig, software supply chain security firm Phylum said in a report today.
While the real package has received nearly 79,000 downloads to date, the malicious variant is said to have artificially inflated its download count after being published on October 6, 2023, to surpass 100,000 downloads.
The profile behind the package has published six other packages that have attracted no less than 2.1 million downloads cumulatively, four of which masquerade as libraries for various crypto services like Kraken, KuCoin, Solana, and Monero, but are also designed to deploy SeroXen RAT.
The attack chain is initiated during installation of the package by means of a tools/init.ps1 script that's designed to achieve code execution without triggering any warning, a behavior previously disclosed by JFrog in March 2023 as being exploited to retrieve next-stage malware.
"Although it is deprecated – the init.ps1 script is still honored by Visual Studio, and will run without any warning when installing a NuGet package," JFrog said at the time. "Inside the .ps1 file, an attacker can write arbitrary commands."
In the package analyzed by Phylum, the PowerShell script is used to download a file named x.bin from a remote server that, in reality, is a heavily-obfuscated Windows Batch script, which, in turn, is responsible for constructing and executing another PowerShell script to ultimately deploy the SeroXen RAT.
An off-the-shelf malware, SeroXen RAT is offered for sale for $60 for a lifetime bundle, making it easily accessible to cyber criminals. It's a fileless RAT that combines the functions of Quasar RAT, the r77 rootkit, and the Windows command-line tool NirCmd.
"The discovery of SeroXen RAT in NuGet packages only underscores how attackers continue to exploit open-source ecosystems and the developers that use them," Phylum said.
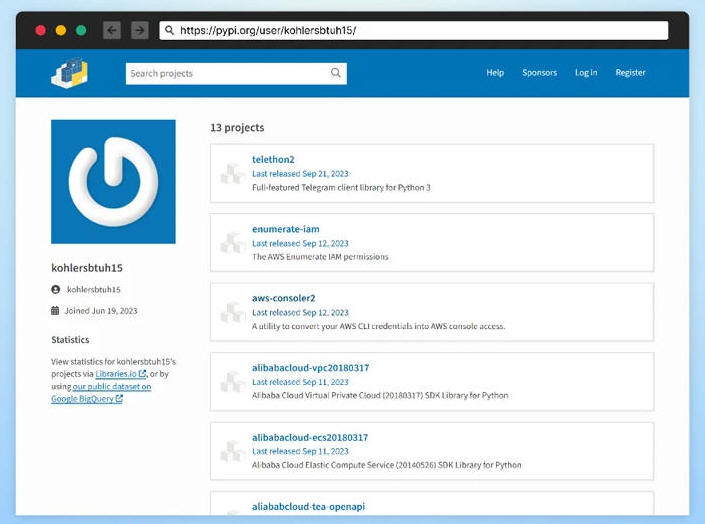
The development comes as the company detected seven malicious packages on the Python Package Index (PyPI) repository that impersonate legitimate offerings from cloud service providers such as Aliyun, Amazon Web Services (AWS), and Tencent Cloud to surreptitiously transmit the credentials to an obfuscated remote URL.
The names of the packages are listed below -
tencent-cloud-python-sdk
python-alibabacloud-sdk-core
alibabacloud-oss2
python-alibabacloud-tea-openapi
aws-enumerate-iam
enumerate-iam-aws
alisdkcore
"In this campaign, the attacker is exploiting a developer's trust, taking an existing, well-established codebase and inserting a single bit of malicious code aimed at exfiltrating sensitive cloud credentials," Phylum noted.
"The subtlety lies in the attacker's strategy of preserving the original functionality of the packages, attempting to fly under the radar, so to speak. The attack is minimalistic and simple, yet effective."
Checkmarx, which shared additional details of the same campaign, said it's also designed to target Telegram via a deceptive package named telethon2, which aims to mimic telethon, a Python library to interact with Telegram's API.
A majority of the downloads of the counterfeit libraries have originated from the U.S., followed by China, Singapore, Hong Kong, Russia, and France.
"Rather than performing automatic execution, the malicious code within these packages was strategically hidden within functions, designed to trigger only when these functions were called," the company said. "The attackers leveraged Typosquatting and StarJacking techniques to lure developers to their malicious packages."
Earlier this month, Checkmarx further exposed a relentless and progressively sophisticated campaign aimed at PyPI to seed the software supply chain with 271 malicious Python packages in order to steal sensitive data and cryptocurrency from Windows hosts.
The packages, which also came fitted with functions to dismantle system defenses, were collectively downloaded approximately 75,000 times before being taken down.
Update#
All the remaining six packages published by Disti, KucoinExchange.net, Kraken.Exchange, SolanaWallet, Modern.Winform.UI, Monero, and DiscordsRpc, are now no longer available on NuGet.