21.7.23 Virus The Hacker News
The defense sector in Ukraine and Eastern Europe has been targeted by a novel .NET-based backdoor called DeliveryCheck (aka CAPIBAR or GAMEDAY) that's capable of delivering next-stage payloads.
Turla's New DeliveryCheck Backdoor Breaches Ukrainian Defense Sector
21.7.23 Virus The Hacker News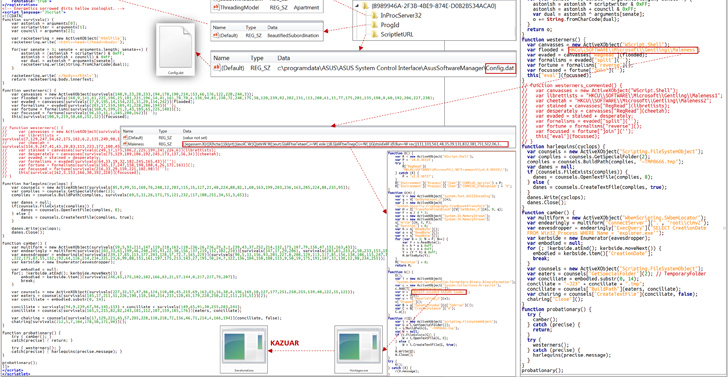
The defense sector in Ukraine and Eastern Europe has been targeted by a novel .NET-based backdoor called DeliveryCheck (aka CAPIBAR or GAMEDAY) that's capable of delivering next-stage payloads.
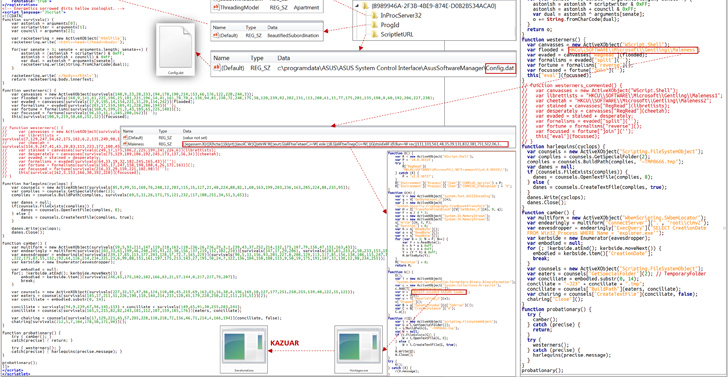
The Microsoft threat intelligence team, in collaboration with the Computer Emergency Response Team of Ukraine (CERT-UA), attributed the attacks to a Russian nation-state actor known as Turla, which is also tracked under the names Iron Hunter, Secret Blizzard (formerly Krypton), Uroburos, Venomous Bear, and Waterbug. It's linked to Russia's Federal Security Service (FSB).
"DeliveryCheck is distributed via email as documents with malicious macros," the company said in a series of tweets. "It persists via a scheduled task that downloads and launches it in memory. It also contacts a C2 server to retrieve tasks, which can include the launch of arbitrary payloads embedded in XSLT stylesheets."
Successful initial access is also accompanied in some cases by the distribution of a known Turla implant dubbed Kazuar, which is equipped to steal application configuration files, event logs, and a wide range of data from web browsers.
The ultimate goal of the attacks is to exfiltrate messages from the Signal messaging app for Windows, enabling the adversary to access sensitive conversations, documents, and images on targeted systems.
A noteworthy aspect of DeliveryCheck is its ability to breach Microsoft Exchange servers to install a server-side component using PowerShell Desired State Configuration (DSC), a PowerShell management platform that helps administrators to automate the configuration of Windows systems.
"DSC generates a Managed Object Format (MOF) file containing a PowerShell script that loads the embedded .NET payload into memory, effectively turning a legitimate server into a malware C2 center," Microsoft explained.
The disclosure comes as the Cyber Police of Ukraine dismantled a massive bot farm with more than 100 individuals allegedly spreading hostile propaganda justifying the Russian invasion, leaking personal information belonging to Ukrainian citizens, and engaging in various fraud schemes.
As part of the operation, searches were carried out in 21 locations, leading to the seizure of computer equipment, mobile phones, more than 250 GSM gateways, and about 150,000 SIM cards belonging to different mobile operators.