Chinese Hackers Exploit VMware Zero-Day to Backdoor Windows and Linux Systems
15.6.23 Vulnerebility The Hacker News
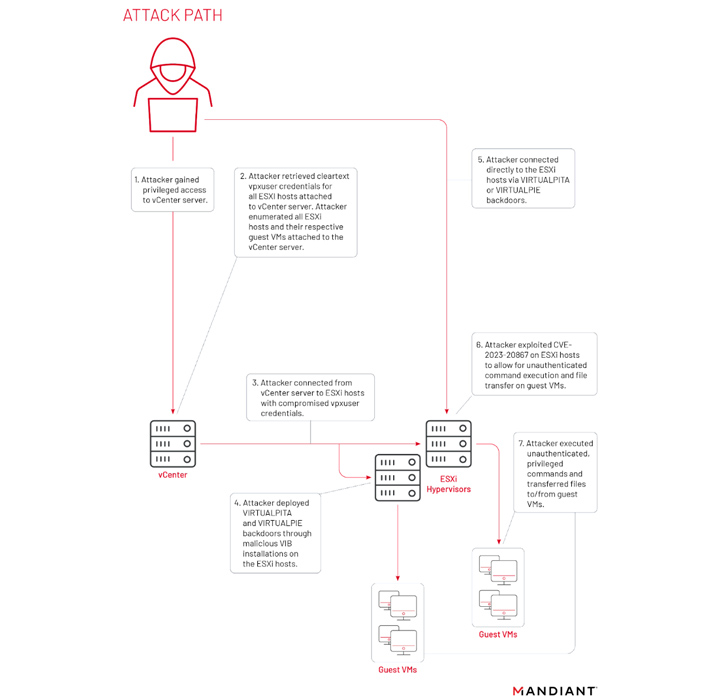
The Chinese state-sponsored group known as UNC3886 has been found to exploit a zero-day flaw in VMware ESXi hosts to backdoor Windows and Linux systems.
The VMware Tools authentication bypass vulnerability, tracked as CVE-2023-20867 (CVSS score: 3.9), "enabled the execution of privileged commands across Windows, Linux, and PhotonOS (vCenter) guest VMs without authentication of guest credentials from a compromised ESXi host and no default logging on guest VMs," Mandiant said.
UNC3886 was initially documented by the Google-owned threat intelligence firm in September 2022 as a cyber espionage actor infecting VMware ESXi and vCenter servers with backdoors named VIRTUALPITA and VIRTUALPIE.
Earlier this March, the group was linked to the exploitation of a now-patched medium-severity security flaw in the Fortinet FortiOS operating system to deploy implants on the network appliances and interact with the aforementioned malware.
The threat actor has been described as a "highly adept" adversarial collective targeting defense, technology, and telecommunication organizations in the U.S., Japan, and the Asia-Pacific region.
"The group has access to extensive research and support for understanding the underlying technology of appliances being targeted," Mandiant researchers said, calling out its pattern of weaponizing flaws in firewall and virtualization software that do not support EDR solutions.
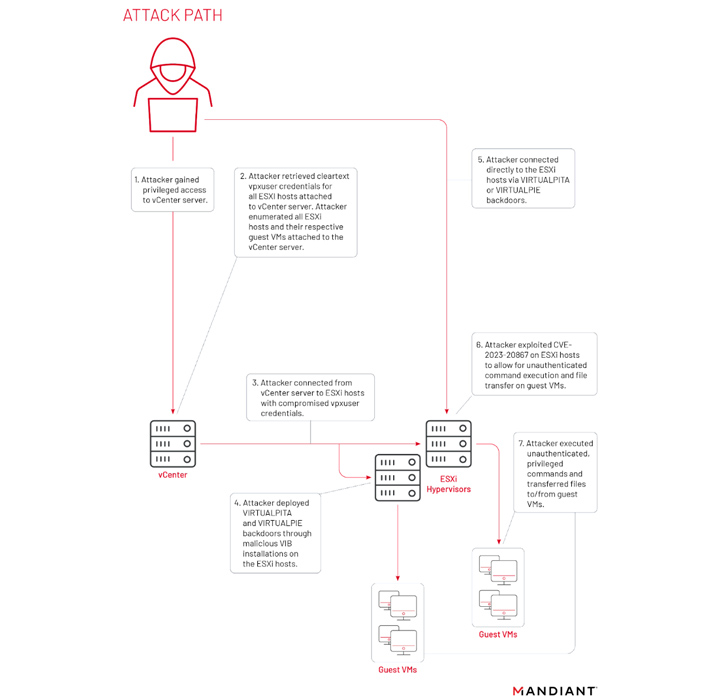
As part of its efforts to exploit ESXi systems, the threat actor has also been observed harvesting credentials from vCenter servers as well as abusing CVE-2023-20867 to execute commands and transfer files to and from guest VMs from a compromised ESXi host.
A notable aspect of UNC3886's tradecraft is its use of Virtual Machine Communication Interface (VMCI) sockets for lateral movement and continued persistence, thereby allowing it to establish a covert channel between the ESXi host and its guest VMs.
"This open communication channel between guest and host, where either role can act as client or server, has enabled a new means of persistence to regain access on a backdoored ESXi host as long as a backdoor is deployed and the attacker gains initial access to any guest machine," the company said.
The development comes as Summoning Team researcher Sina Kheirkhah disclosed three different flaws in VMware Aria Operations for Networks (CVE-2023-20887, CVE-2023-20888, and CVE-2023-20889) that could result in remote code execution.
"UNC3886 continues to present challenges to investigators by disabling and tampering with logging services, selectively removing log events related to their activity," it further added. "The threat actors' retroactive cleanup performed within days of past public disclosures on their activity indicates how vigilant they are."