21.2.24 APT The Hacker News
New Report Reveals North Korean Hackers Targeting Defense Firms Worldwide
21.2.24 APT The Hacker News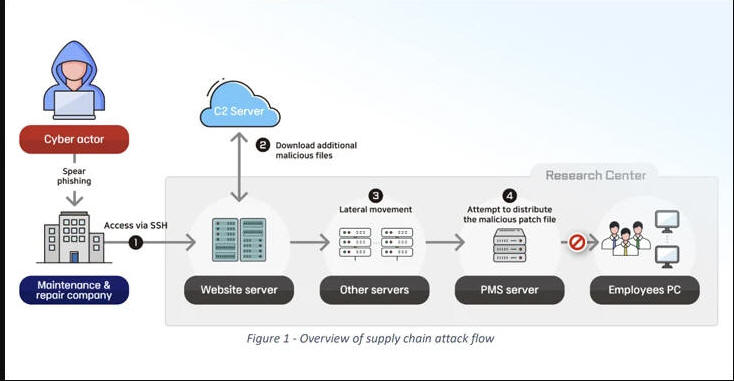
North Korean state-sponsored threat actors have been attributed to a cyber espionage campaign targeting the defense sector across the world.
In a joint advisory published by Germany's Federal Office for the Protection of the Constitution (BfV) and South Korea's National Intelligence Service (NIS), the agencies said the goal of the attacks is to plunder advanced defense technologies in a "cost-effective" manner.
"The regime is using the military technologies to modernize and improve the performance of conventional weapons and to develop new strategic weapon systems including ballistic missiles, reconnaissance satellites and submarines," they noted.
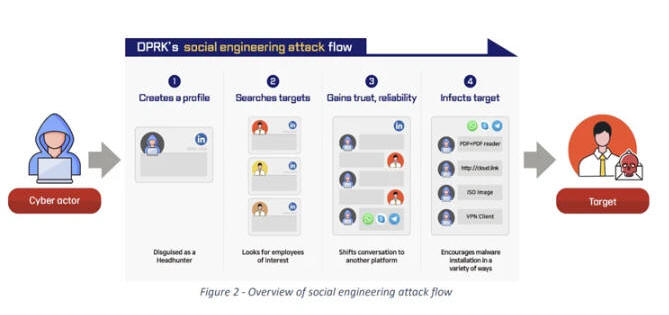
The infamous Lazarus Group has been blamed for one of the two hacking incidents, which involved the use of social engineering to infiltrate the defense sector as part of a long-standing operation called Dream Job. The campaign has been ongoing since August 2020 over several waves.
In these attacks, the threat actors either create a fake profile or leverage legitimate-but-compromised profiles on platforms like LinkedIn to approach prospective targets and build trust with them, before offering lucrative job opportunities and shifting the conversation to a different messaging service like WhatsApp to initiate the recruitment process.
Victims are then sent coding assignments and job offer documents laden with malware that, when launched, activate the infection procedure to compromise their computers.
"Universally, the circumstance that employees usually do not talk to their colleagues or employer about job offers plays into the hands of the attacker," the agencies said.
"The Lazarus Group changed its tools throughout the campaign and demonstrated more than once that it is capable of developing whatever is necessary to suit the situation."
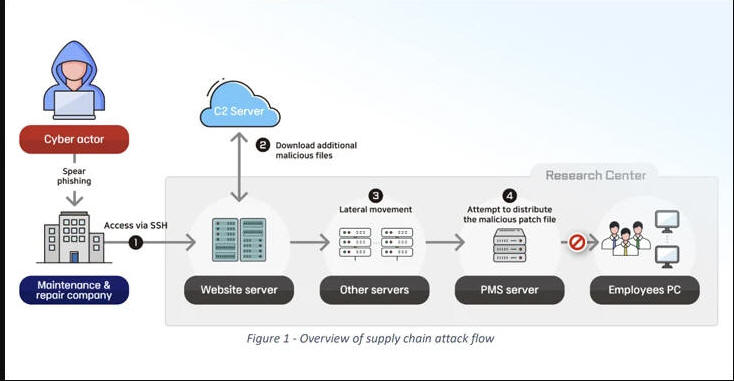
The second case concerns an intrusion into a defense research center towards the end of 2022 by executing a software supply chain attack against an unnamed company responsible for maintaining one of the research center's web servers.
"The cyber actor further infiltrated the research facility by deploying remote-control malware through a patch management system (PMS) of the research center, and stole various account information of business portals and email contents," the BfV and NIS said.
The breach, which was carried by another North Korea-based threat actor, unfolded over five stages -
Hack into the web server maintenance company, steal SSH credentials, and gain remote access to the research center's server
Download additional malicious tooling using curl commands, including a tunneling software and a Python-based downloader
Conduct lateral movement and plunder employee account credentials
Leverage the stolen security manager's account information to unsuccessfully distribute a trojanized update that comes with capabilities to upload and download files, execute code, and to collect system information
Persist within target environment by weaponizing a file upload vulnerability in the website to deploy a web shell for remote access and send spear-phishing emails
"The actor avoided carrying out a direct attack against its target, which maintained a high level of security, but rather made an initial attack against its vendor, the maintenance and repair company," the agencies explained. "This indicates that the actor took advantage of the trustful relationship between the two entities."
The security bulletin is the second to be published by BfV and NIS in as many years. In March 2023, the agencies warned of Kimsuky actors using rogue browser extensions to steal users' Gmail inboxes. Kimsuky was sanctioned by the U.S. government in November 2023.
The development comes as blockchain analytics firm Chainalysis revealed that the Lazarus Group has switched to using YoMix bitcoin mixer to launder stolen proceeds following the shutdown of Sinbad late last year, indicating their ability to adapt their modus operandi in response to law enforcement actions.
"Sinbad became a preferred mixer for North Korea-affiliated hackers in 2022, soon after the sanctioning of Tornado Cash, which had previously been the go-to for these sophisticated cybercriminals," the company said. "With Sinbad out of the picture, Bitcoin-based mixer YoMix has acted as a replacement."
The malicious activities are the work of a plethora of North Korean hacking units operating under the broad Lazarus umbrella, which are known to engage in an array of hacking operations ranging from cyber espionage to cryptocurrency thefts, ransomware, and supply chain attacks to achieve their strategic goals.