18.4.24 Virus The Hacker News

Malicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
18.4.24 Virus The Hacker News
A new Google malvertising campaign is leveraging a cluster of domains mimicking a legitimate IP scanner software to deliver a previously unknown backdoor dubbed MadMxShell.
"The threat actor registered multiple look-alike domains using a typosquatting technique and leveraged Google Ads to push these domains to the top of search engine results targeting specific search keywords, thereby luring victims to visit these sites," Zscaler ThreatLabz researchers Roy Tay and Sudeep Singh said.
As many as 45 domains are said to have been registered between November 2023 and March 2024, with the sites masquerading as port scanning and IT management software such as Advanced IP Scanner, Angry IP Scanner, IP scanner PRTG, and ManageEngine.
While this is not the first time threat actors are banking on malvertising techniques to serve malware via lookalike sites, the development marks the first time the delivery vehicle is being used to propagate a sophisticated Windows backdoor.
Thus, users who end up searching for such tools are displayed bogus sites that include JavaScript code designed to download a malicious file ("Advanced-ip-scanner.zip") upon clicking the download button.
Present within the ZIP archive is a DLL file ("IVIEWERS.dll") and an executable ("Advanced-ip-scanner.exe"), the latter of which uses DLL side-loading to load the DLL and activate the infection sequence.
The DLL file is responsible for injecting the shellcode into the "Advanced-ip-scanner.exe" process via a technique called process hollowing, following which the injected EXE file unpacks two additional files – OneDrive.exe and Secur32.dll.
OneDrive.exe, a legitimate signed Microsoft binary, is then abused to sideload Secur32.dll, and ultimately execute the shellcode backdoor, but not before setting up persistence on the host by means of a scheduled task and disabling Microsoft Defender Antivirus.
The backdoor – so named for its use of DNS MX queries for command-and-control (C2) – is designed to gather system information, run commands via cmd.exe, and perform basic file manipulation operations such as reading, writing, and deleting files.
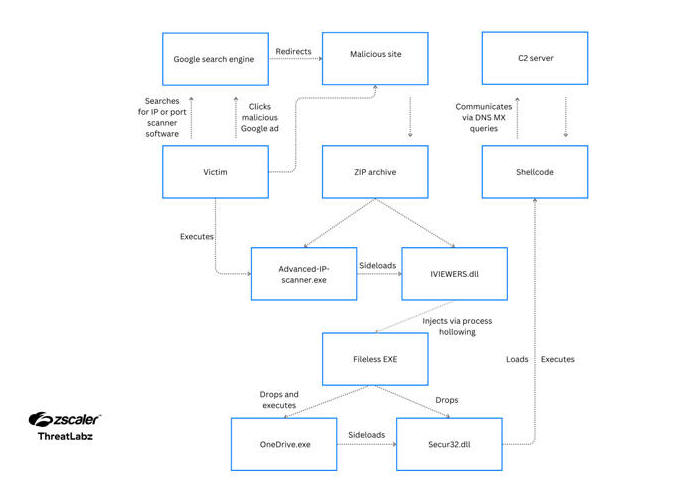
It sends requests to the C2 server ("litterbolo[.]com") by encoding the data in the subdomain(s) of the Fully Qualified Domain Name (FQDN) in a DNS mail exchange (MX) query packet and receives commands encoded within the response packet.
"The backdoor uses techniques such as multiple stages of DLL side-loading and DNS tunneling for command-and-control (C2) communication as a means to evade endpoint and network security solutions, respectively," Tay and Singh said.
"In addition, the backdoor uses evasive techniques like anti-dumping to prevent memory analysis and hinder forensics security solutions."
There is currently no indication of where the malware operators originate from or what their intentions are, but Zscaler said it identified two accounts created by them on criminal underground forums like blackhatworld[.]com and social-eng[.]ru using the email address wh8842480@gmail[.]com, which was also used to register a domain spoofing Advanced IP Scanner.
Specifically, the threat actor has been found engaging in posts offering ways to set up unlimited Google AdSense threshold accounts way back in June 2023, indicating their interest in launching their own long-lasting malvertising campaign.
"Google Ads threshold accounts and techniques for abusing them are often traded on BlackHat forums," the researchers said. "Many times they offer a way for the threat actor to add as many credits as possible to run Google Ads campaigns."
"This allows the threat actors to run campaigns without actually paying until the threshold limit. A reasonably high threshold limit lets the threat actor run the ad campaign for a significant amount of time."