Virus 2024 2023 2022 2021 2020
Watering Hole Attack on Kurdish Sites Distributing Malicious APKs and Spyware
26.9.24 Virus The Hacker News
As many as 25 websites linked to the Kurdish minority have been compromised as part of a watering hole attack designed to harvest sensitive information for over a year and a half.
French cybersecurity firm Sekoia, which disclosed details of the campaign dubbed SilentSelfie, described the intrusion set as long-running, with first signs of infection detected as far back as December 2022.
The strategic web compromises are designed to deliver four different variants of an information-stealing framework, it added.
"These ranged from the simplest, which merely stole the user's location, to more complex ones that recorded images from the selfie camera and led selected users to install a malicious APK, i.e an application used on Android," security researchers Felix Aimé and Maxime A said in a Wednesday report.
Targeted websites include Kurdish press and media, Rojava administration and its armed forces, those related to revolutionary far-left political parties and organizations in Türkiye and Kurdish regions. Sekoia told The Hacker News that the exact method by which these websites were breached in the first place remains uncertain.
The attacks have not been attributed to any known threat actor or entity, indicating the emergence of a new threat cluster targeting the Kurdish community, which has been previously singled out by groups like StrongPity and BladeHawk.
Earlier this year, Dutch security firm Hunt & Hackett also revealed that Kurdish websites in the Netherlands were singled out by a Türkiye-nexus threat actor known as Sea Turtle.
The watering hole attacks are characterized by the deployment of a malicious JavaScript that's responsible for gathering various kinds of information from site visitors, including their location, device data (e.g., number of CPUs, battery status, browser language, etc.), and public IP address, among others.

One variant of the reconnaissance script found on three websites (rojnews[.]news, hawarnews[.]com, and targetplatform[.]net.) has also been observed redirecting users to rogue Android APK files, while some others include the ability for user tracking via a cookie named "sessionIdVal."
The Android app, per Sekoia's analysis, embeds the website itself as a WebView, while also clandestinely hoovering system information, contact lists, location, and files present in the external storage based on the permissions granted to it.
"It is worth noting that this malicious code doesn't have any persistence mechanism but is only executed when the user opens the RojNews application," the researchers pointed out.
"Once the user opens the application, and after 10 seconds, the LocationHelper service starts beaconning the background to the URL rojnews[.]news/wp-includes/sitemaps/ via HTTP POST requests, sharing the current location of the user and waiting for commands to execute."
Not much is known about who is behind SilentSelfie, but Sekoia has assessed that it could be the handiwork of the Kurdistan Regional Government of Iraq based on the arrest of RojNews journalist Silêman Ehmed by KDP forces in October 2023. He was sentenced to three years in prison in July 2024.
"Even though this watering hole campaign is of low sophistication, it is notable for the number of kurdish websites affected and its duration," the researchers said. "The campaign's low level of sophistication suggests it might be the work of an uncovered threat actor with limited capabilities and relatively new to the field."
Transportation Companies Hit by Cyberattacks Using Lumma Stealer and NetSupport Malware
25.9.24 Virus The Hacker News
Transportation and logistics companies in North America are the target of a new phishing campaign that delivers a variety of information stealers and remote access trojans (RATs).
The activity cluster, per Proofpoint, makes use of compromised legitimate email accounts belonging to transportation and shipping companies so as to inject malicious content into existing email conversations.
As many as 15 breached email accounts have been identified as used as part of the campaign. It's currently not clear how these accounts are infiltrated in the first place or who is behind the attacks.
"Activity which occurred from May to July 2024 predominately delivered Lumma Stealer, StealC, or NetSupport," the enterprise security firm said in an analysis published Tuesday.
"In August 2024, the threat actor changed tactics by employing new infrastructure and a new delivery technique, as well as adding payloads to deliver DanaBot and Arechclient2."
The attack chains involve sending messages bearing internet shortcut (.URL) attachments or Google Drive URLs leading to a .URL file that when launched, uses Server Message Block (SMB) to fetch the next-stage payload containing the malware from a remote share.
Some variants of the campaign observed in August 2024 have also latched onto a recently popular technique called ClickFix to trick victims into downloading the DanaBot malware under the pretext of addressing an issue with displaying document content in the web browser.
Specifically, this involves urging users to copy and paste a Base64-encoded PowerShell script into the terminal, thereby triggering the infection process.
"These campaigns have impersonated Samsara, AMB Logistic, and Astra TMS – software that would only be used in transport and fleet operations management," Proofpoint said.
"The specific targeting and compromises of organizations within transportation and logistics, as well as the use of lures that impersonate software specifically designed for freight operations and fleet management, indicates that the actor likely conducts research into the targeted company's operations before sending campaigns."
The disclosure comes amid the emergence of various stealer malware strains such as Angry Stealer, BLX Stealer (aka XLABB Stealer), Emansrepo Stealer, Gomorrah Stealer, Luxy, Poseidon, PowerShell Keylogger, QWERTY Stealer, Taliban Stealer, X-FILES Stealer, and a CryptBot-related variant dubbed Yet Another Silly Stealer (YASS).
It also follows the emergence of a new version of the RomCom RAT, a successor to PEAPOD (aka RomCom 4.0) codenamed SnipBot that's distributed via bogus links embedded within phishing emails. Some aspects of the campaign were previously highlighted by the Computer Emergency Response Team of Ukraine (CERT-UA) in July 2024.
"SnipBot gives the attacker the ability to execute commands and download additional modules onto a victim's system," Palo Alto Networks Unit 42 researchers Yaron Samuel and Dominik Reichel said.
"The initial payload is always either an executable downloader masked as a PDF file or an actual PDF file sent to the victim in an email that leads to an executable."
While systems infected with RomCom have also witnessed ransomware deployments in the past, the cybersecurity company pointed out the absence of this behavior, raising the possibility that the threat behind the malware, Tropical Scorpius (aka Void Rabisu), has shifted from pure financial gain to espionage.
Necro Android Malware Found in Popular Camera and Browser Apps on Play Store
25.9.24 Virus The Hacker News
Altered versions of legitimate Android apps associated with Spotify, WhatsApp, and Minecraft have been used to deliver a new version of a known malware loader called Necro.
Kaspersky said some of the malicious apps have also been found on the Google Play Store. They have been cumulatively downloaded 11 million times. They include -
Wuta Camera - Nice Shot Always (com.benqu.wuta) - 10+ million downloads
Max Browser-Private & Security (com.max.browser) - 1+ million downloads
As of writing, Max Browser is no longer available for download from the Play Store. Wuta Camera, on the other hand, has been updated (version 6.3.7.138) to remove the malware. The latest version of the app, 6.3.8.148, was released on September 8, 2024.
It's currently not clear how both the apps were compromised with the malware in the first place, although it's believed that a rogue software developer kit (SDK) for integrating advertising capabilities is the culprit.
Necro (not to be confused with a botnet of the same name) was first discovered by the Russian cybersecurity company in 2019 when it was hidden within a popular document scanning app called CamScanner.
CamScanner later blamed the issue on an advertisement SDK provided by a third-party named AdHub that it said contained a malicious module to retrieve next-stage malware from a remote server, essentially acting as a loader for all kinds of malware onto victim devices.

The new version of the malware is no different, although it packs in obfuscation techniques to evade detection, particularly leveraging steganography to hide payloads.
"The downloaded payloads, among other things, could display ads in invisible windows and interact with them, download and execute arbitrary DEX files, install applications it downloaded," Kaspersky researcher Dmitry Kalinin said.
It can also "open arbitrary links in invisible WebView windows and execute any JavaScript code in those, run a tunnel through the victim's device, and potentially subscribe to paid services."
One of the prominent delivery vehicles for Necro is modded versions of popular apps and games that are hosted on unofficial sites and app stores. Once downloaded, the apps initialize a module named Coral SDK, which, in turn, sends an HTTP POST request to a remote server.
The server subsequently responds with a link to a purported PNG image file hosted on adoss.spinsok[.]com, following which the SDK proceeds to extract the main payload – a Base64-encoded Java archive (JAR) file – from it.

Necro's malicious functions are realized through a set of additional modules (aka plugins) that are downloaded from the command-and-control (C2) server, allowing it to perform a wide range of actions on the infected Android device -
NProxy - Create a tunnel through the victim's device
island - Generate a pseudo-random number that's used as a time interval (in milliseconds) between displays of intrusive ads
web - Periodically contact a C2 server and execute arbitrary code with elevated permissions when loading specific links
Cube SDK - A helper module that loads other plugins to handle ads in the background
Tap - Download arbitrary JavaScript code and a WebView interface from the C2 server that are responsible for covertly loading and viewing ads
Happy SDK/Jar SDK - A module that combines NProxy and web modules with some minor differences
The discovery of Happy SDK has raised the possibility that the threat actors behind the campaign are experimenting with a non-modular version as well.
"This suggests that Necro is highly adaptable and can download different iterations of itself, perhaps to introduce new features," Kalinin said.
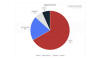
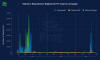
Telemetry data gathered by Kaspersky shows that it blocked over ten thousand Necro attacks worldwide between August 26 and September 15, 2024, with Russia, Brazil, Vietnam, Ecuador, Mexico, Taiwan, Spain, Malaysia, Italy, and Turkey accounting for the most number of attacks.
"This new version is a multi-stage loader that used steganography to hide the second-stage payload, a very rare technique for mobile malware, as well as obfuscation to evade detection," Kalinin said.
"The modular architecture gives the Trojan's creators a wide range of options for both mass and targeted delivery of loader updates or new malicious modules depending on the infected application."
New Octo2 Android Banking Trojan Emerges with Device Takeover Capabilities
24.9.24 Virus The Hacker News
Cybersecurity researchers have discovered a new version of an Android banking trojan called Octo that comes with improved capabilities to conduct device takeover (DTO) and perform fraudulent transactions.
The new version has been codenamed Octo2 by the malware author, Dutch security firm ThreatFabric said in a report shared with The Hacker News, adding campaigns distributing the malware have been spotted in European countries like Italy, Poland, Moldova, and Hungary.
"The malware developers took actions to increase the stability of the remote actions capabilities needed for Device Takeover attacks," the company said.
Some of the malicious apps containing Octo2 are listed below -
Europe Enterprise (com.xsusb_restore3)
Google Chrome (com.havirtual06numberresources)
NordVPN (com.handedfastee5)
Octo was first flagged by the company in early 2022, describing it as the work of a threat actor who goes by the online aliases Architect and goodluck. It has been assessed to be a "direct descendant" of the Exobot malware originally detected in 2016, which also spawned another variant dubbed Coper in 2021.
"Based on the source code of the banking Trojan Marcher, Exobot was maintained until 2018 targeting financial institutions with a variety of campaigns focused on Turkey, France and Germany as well as Australia, Thailand and Japan," ThreatFabric noted at the time.
"Subsequently, a 'lite' version of it was introduced, named ExobotCompact by its author, the threat actor known as 'android' on dark-web forums."
The emergence of Octo2 is said to have been primarily driven by the leak of the Octo source code earlier this year, leading other threat actors to spawn multiple variants of the malware.

Another major development is Octo's transition to a malware-as-a-service (MaaS) operation, per Team Cymru, enabling the developer to monetize the malware by offering it to cybercriminals who are looking to carry out information theft operations.
"When promoting the update, the owner of Octo announced that Octo2 will be available for users of Octo1 at the same price with early access," ThreatFabric said. "We can expect that the actors that were operating Octo1 will switch to Octo2, thus bringing it to the global threat landscape."
One of the significant improvements to Octo2 is the introduction of a Domain Generation Algorithm (DGA) to create the command-and-control (C2) server name, as well as improving its overall stability and anti-analysis techniques.
The rogue Android apps distributing the malware are created using a known APK binding service called Zombinder, which makes it possible to trojanize legitimate applications such that they retrieve the actual malware (in this case, Octo2) under the guise of installing a "necessary plugin."
"With the original Octo malware's source code already leaked and easily accessible to various threat actors, Octo2 builds on this foundation with even more robust remote access capabilities and sophisticated obfuscation techniques," ThreatFabric said.
"This variant's ability to invisibly perform on-device fraud and intercept sensitive data, coupled with the ease with which it can be customized by different threat actors, raises the stakes for mobile banking users globally."
New PondRAT Malware Hidden in Python Packages Targets Software Developers
23.9.24 Virus The Hacker News
Threat actors with ties to North Korea have been observed using poisoned Python packages as a way to deliver a new malware called PondRAT as part of an ongoing campaign.
PondRAT, according to new findings from Palo Alto Networks Unit 42, is assessed to be a lighter version of POOLRAT (aka SIMPLESEA), a known macOS backdoor that has been previously attributed to the Lazarus Group and deployed in attacks related to the 3CX supply chain compromise last year.
Some of these attacks are part of a persistent cyber attack campaign dubbed Operation Dream Job, wherein prospective targets are lured with enticing job offers in an attempt to trick them into downloading malware.
"The attackers behind this campaign uploaded several poisoned Python packages to PyPI, a popular repository of open-source Python packages," Unit 42 researcher Yoav Zemah said, linking the activity with moderate confidence to a threat actor called Gleaming Pisces.
The adversary is also tracked by the wider cybersecurity community under the names Citrine Sleet, Labyrinth Chollima, Nickel Academy, and UNC4736, a sub-cluster within the Lazarus Group that's also known for distributing the AppleJeus malware.
It's believed that the end goal of the attacks is to "secure access to supply chain vendors through developers' endpoints and subsequently gain access to the vendors' customers' endpoints, as observed in previous incidents."
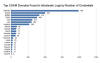
The list of malicious packages, now removed from the PyPI repository, is below -
real-ids (893 downloads)
coloredtxt (381 downloads)
beautifultext (736 downloads)
minisound (416 downloads)
The infection chain is fairly simple in that the packages, once downloaded and installed on developer systems, are engineered to execute an encoded next-stage that, in turn, runs the Linux and macOS versions of the RAT malware after retrieving them from a remote server.

Further analysis of PondRAT has revealed similarities with both POOLRAT and AppleJeus, with the attacks also distributing new Linux variants of POOLRAT.
"The Linux and macOS versions [of POOLRAT] use an identical function structure for loading their configurations, featuring similar method names and functionality," Zemah said.
"Additionally, the method names in both variants are strikingly similar, and the strings are almost identical. Lastly, the mechanism that handles commands from the [command-and-control server] is nearly identical."
PondRAT, a leaner version of POOLRAT, comes with capabilities to upload and download files, pause operations for a predefined time interval, and execute arbitrary commands.
"The evidence of additional Linux variants of POOLRAT showed that Gleaming Pisces has been enhancing its capabilities across both Linux and macOS platforms," Unit 42 said.
"The weaponization of legitimate-looking Python packages across multiple operating systems poses a significant risk to organizations. Successful installation of malicious third-party packages can result in malware infection that compromises an entire network."
The disclosure comes as KnowBe4, which was duped into hiring a North Korean threat actor as an employee, said more than a dozen companies "either hired North Korean employees or had been besieged by a multitude of fake resumes and applications submitted by North Koreans hoping to get a job with their organization."
It described the activity, tracked by CrowdStrike under the moniker Famous Chollima, as a "complex, industrial, scaled nation-state operation" and that it poses a "serious risk for any company with remote-only employees."
Chinese Hackers Exploit GeoServer Flaw to Target APAC Nations with EAGLEDOOR Malware
23.9.24 Virus The Hacker News
A suspected advanced persistent threat (APT) originating from China targeted a government organization in Taiwan, and possibly other countries in the Asia-Pacific (APAC) region, by exploiting a recently patched critical security flaw impacting OSGeo GeoServer GeoTools.
The intrusion activity, which was detected by Trend Micro in July 2024, has been attributed to a threat actor dubbed Earth Baxia.
"Based on the collected phishing emails, decoy documents, and observations from incidents, it appears that the targets are primarily government agencies, telecommunication businesses, and the energy industry in the Philippines, South Korea, Vietnam, Taiwan, and Thailand," researchers Ted Lee, Cyris Tseng, Pierre Lee, Sunny Lu, and Philip Chen said.
The discovery of lure documents in Simplified Chinese points to China being one of the affected countries as well, although the cybersecurity company said it does not have enough information to determine what sectors within the country have been singled out.
The multi-stage infection chain process leverages two different techniques, using spear-phishing emails and the exploitation of the GeoServer flaw (CVE-2024-36401, CVSS score: 9.8), to ultimately deliver Cobalt Strike and a previously unknown backdoor codenamed EAGLEDOOR, which allows for information gathering and payload delivery.
"The threat actor employs GrimResource and AppDomainManager injection to deploy additional payloads, aiming to lower the victim's guard," the researchers noted, adding the former method is used to download next-stage malware via a decoy MSC file dubbed RIPCOY embedded within a ZIP archive attachment.

It's worth mentioning here that Japanese cybersecurity company NTT Security Holdings recently detailed an activity cluster with links to APT41 that it said used the same two techniques to target Taiwan, the Philippines military, and Vietnamese energy organizations.
It's likely that these two intrusion sets are related, given the overlapping use of Cobalt Strike command-and-control (C2) domains that mimic Amazon Web Services, Microsoft Azure (e.g., "s3cloud-azure," "s2cloud-amazon," "s3bucket-azure," and "s3cloud-azure"), and Trend Micro itself ("trendmicrotech").
The end goal of the attacks is to deploy a custom variant of Cobalt Strike, which acts as a launchpad for the EAGLEDOOR backdoor ("Eagle.dll") via DLL side-loading.
The malware supports four methods to communicate with the C2 server over DNS, HTTP, TCP, and Telegram. While the first three protocols are used to transmit the victim status, the core functionality is realized through the Telegram Bot API to upload and download files, and execute additional payloads. The harvested data is exfiltrated via curl.exe.
"Earth Baxia, likely based in China, conducted a sophisticated campaign targeting government and energy sectors in multiple APAC countries," the researchers pointed out.
"They used advanced techniques like GeoServer exploitation, spear-phishing, and customized malware (Cobalt Strike and EAGLEDOOR) to infiltrate and exfiltrate data. The use of public cloud services for hosting malicious files and the multi-protocol support of EAGLEDOOR highlight the complexity and adaptability of their operations."
New Brazilian-Linked SambaSpy Malware Targets Italian Users via Phishing Emails
19.9.24 Virus The Hacker News
A previously undocumented malware called SambaSpy is exclusively targeting users in Italy via a phishing campaign orchestrated by a suspected Brazilian Portuguese-speaking threat actor.
"Threat actors usually try to cast a wide net to maximize their profits, but these attackers are focused on just one country," Kaspersky said in a new analysis. "It's likely that the attackers are testing the waters with Italian users before expanding their operation to other countries."
The starting point of the attack is a phishing email that either includes an HTML attachment or an embedded link that initiates the infection process. Should the HTML attachment be opened, a ZIP archive containing an interim downloader or dropper is used to deploy and launch the multi-functional RAT payload.
The downloader, for its part, is responsible for fetching the malware from a remote server. The dropper, on the other hand, does the same thing, but extracts the payload from the archive instead of retrieving it from an external location.
The second infection chain with the booby-trapped link is a lot more elaborate, as clicking it redirects the user to a legitimate invoice hosted on FattureInCloud if they are not the intended target.
In an alternate scenario, clicking on the same URL takes the victim to a malicious web server that serves an HTML page with JavaScript code featuring comments written in Brazilian Portuguese.
"It redirects users to a malicious OneDrive URL but only if they are running Edge, Firefox, or Chrome with their language set to Italian," the Russian cybersecurity vendor said. "If the users don't pass these checks, they stay on the page."
Users who meet these requirements are served a PDF document hosted on Microsoft OneDrive that instructs the users to click on a hyperlink to view the document, following which they are led to a malicious JAR file hosted on MediaFire containing either the downloader or the dropper as before.
A fully-featured remote access trojan developed in Java, SambaSpy is nothing short of a Swiss Army knife that can handle file system management, process management, remote desktop management, file upload/download, webcam control, keylogging and clipboard tracking, screenshot capture, and remote shell.
It's also equipped to load additional plugins at runtime by launching a file on the disk previously downloaded by the RAT, allowing it to augment its capabilities as needed. On top of that, it's designed to steal credentials from web browsers like Chrome, Edge, Opera, Brave, Iridium, and Vivaldi.

Infrastructure evidence suggests that the threat actor behind the campaign is also setting their sights on Brazil and Spain, pointing to an operational expansion.
"There are various connections with Brazil, such as language artifacts in the code and domains targeting Brazilian users," Kaspersky said. "This aligns with the fact that attackers from Latin America often target European countries with closely related languages, namely Italy, Spain, and Portugal."
New BBTok and Mekotio Campaigns Target Latin America#
The development comes weeks after Trend Micro warned of a surge in campaigns delivering banking trojans such as BBTok, Grandoreiro, and Mekotio targeting the Latin American region via phishing scams that utilize business transactions and judicial-related transactions as lures.
Mekotio "employs a new technique where the trojan's PowerShell script is now obfuscated, enhancing its ability to evade detection," the company said, highlighting BBTok's use of phishing links to download ZIP or ISO files containing LNK files that act as a trigger point for the infections.
The LNK file is used to advance to the next step by launching the legitimate MSBuild.exe binary, which is present within the ISO file. It subsequently loads a malicious XML file also hidden within the ISO archive, which then leverages rundll32.exe to launch the BBTok DLL payload.
"By using the legitimate Windows utility MSBuild.exe, attackers can execute their malicious code while evading detection," Trend Micro noted.
The attack chains associated with Mekotio commence with a malicious URL in the phishing email that, when clicked, directs the user to a bogus website that delivers a ZIP archive, which contains a batch file that's engineered to run a PowerShell script.
The PowerShell script acts as a second-stage downloader to launch the trojan by means of an AutoHotKey script, but not before conducting a reconnaissance of the victim environment to confirm it's indeed located in one of the targeted countries.
"More sophisticated phishing scams targeting Latin American users to steal sensitive banking credentials and carry out unauthorized banking transactions underscores the urgent need for enhanced cybersecurity measures against increasingly advanced methods employed by cybercriminals," Trend Micro researchers said.
"These trojans [have] grown increasingly adept at evading detection and stealing sensitive information while the gangs behind them become bolder in targeting larger groups for more profit."
TrickMo Android Trojan Exploits Accessibility Services for On-Device Banking Fraud
14.9.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new variant of an Android banking trojan called TrickMo that comes packed with new capabilities to evade analysis and display fake login screens to capture victims' banking credentials.
"The mechanisms include using malformed ZIP files in combination with JSONPacker," Cleafy security researchers Michele Roviello and Alessandro Strino said. "In addition, the application is installed through a dropper app that shares the same anti-analysis mechanisms."
"These features are designed to evade detection and hinder cybersecurity professionals' efforts to analyze and mitigate the malware."
TrickMo, first caught in the wild by CERT-Bund in September 2019, has a history of targeting Android devices, particularly targeting users in Germany to siphon one-time passwords (OTPs) and other two-factor authentication (2FA) codes to facilitate financial fraud.
The mobile-focused malware is assessed to be the work of the now-defunct TrickBot e-crime gang, over time continually improving its obfuscation and anti-analysis features to fly under the radar.
Notable among the features are its ability to record screen activity, log keystrokes, harvest photos and SMS messages, remotely control the infected device to conduct on-device fraud (ODF), and abuse Android's accessibility services API to carry out HTML overlay attacks as well as perform clicks and gestures on the device.
The malicious dropper app discovered by the Italian cybersecurity company masquerades as the Google Chrome web browser that, when launched after installation, urges the victim to update Google Play Services by clicking the Confirm button.

Should the user proceed with the update, an APK file containing the TrickMo payload is downloaded to the device under the guise of "Google Services," following which the user is asked to enable accessibility services for the new app.
"Accessibility services are designed to assist users with disabilities by providing alternative ways to interact with their devices," the researchers said. "However, when exploited by malicious apps like TrickMo, these services can grant extensive control over the device."
"This elevated permission allows TrickMo to perform various malicious actions, such as intercepting SMS messages, handling notifications to intercept or hide authentication codes, and executing HTML overlay attacks to steal user credentials. Additionally, the malware can dismiss keyguards and auto-accept permissions, enabling it to integrate seamlessly into the device's operations."
Furthermore, the abuse of the accessibility services allows the malware to disable crucial security features and system updates, auto-grant permissions at will, and prevent the uninstallation of certain apps.

Cleafy's analysis also uncovered misconfigurations in the command-and-control (C2) server that made it possible to access 12 GB worth of sensitive data exfiltrated from the devices, including credentials and pictures, without requiring any authentication.
The C2 server also hosts the HTML files used in the overlay attacks. These files encompass fake login pages for various services, counting banks such as ATB Mobile and Alpha Bank and cryptocurrency platforms like Binance.
The security lapse not only highlights the operational security (OPSEC) blunder on the part of the threat actors, but also puts the victims' data at risk of exploitation by other threat actors.
The wealth of information exposed from TrickMo's C2 infrastructure could be leveraged to commit identity theft, infiltrate various online accounts, conduct unauthorized fund transfers, and even make fraudulent purchases. Even worse, attackers could hijack the accounts and lock the victims out by resetting their passwords.
"Using personal information and images, the attacker can craft convincing messages that trick victims into divulging even more information or executing malicious actions," the researchers noted.
"Exploiting such comprehensive personal data results in immediate financial and reputational damage and long-term consequences for the victims, making recovery a complex and prolonged process."
The disclosure comes as Google has been plugging the security holes around sideloading to let third-party developers determine if their apps are sideloaded using the Play Integrity API and, if so, require users to download the apps from Google Play in order to continue using them.
New Android Malware 'Ajina.Banker' Steals Financial Data and Bypasses 2FA via Telegram
13.9.24 Virus The Hacker News
Bank customers in the Central Asia region have been targeted by a new strain of Android malware codenamed Ajina.Banker since at least November 2023 with the goal of harvesting financial information and intercepting two-factor authentication (2FA) messages.
Singapore-headquartered Group-IB, which discovered the threat in May 2024, said the malware is propagated via a network of Telegram channels set up by the threat actors under the guise of legitimate applications related to banking, payment systems, and government services, or everyday utilities.
"The attacker has a network of affiliates motivated by financial gain, spreading Android banker malware that targets ordinary users," security researchers Boris Martynyuk, Pavel Naumov, and Anvar Anarkulov said.
Targets of the ongoing campaign include countries such as Armenia, Azerbaijan, Iceland, Kazakhstan, Kyrgyzstan, Pakistan, Russia, Tajikistan, Ukraine, and Uzbekistan.
There is evidence to suggest that some aspects of the Telegram-based malware distribution process may have been automated for improved efficiency. The numerous Telegram accounts are designed to serve crafted messages containing links -- either to other Telegram channels or external sources -- and APK files to unwitting targets.
The use of links pointing to Telegram channels that host the malicious files has an added benefit in that it bypasses security measures and restrictions imposed by many community chats, thereby allowing the accounts to evade bans when automatic moderation is triggered.
Besides abusing the trust users place in legitimate services to maximize infection rates, the modus operandi also involves sharing the malicious files in local Telegram chats by passing them off as giveaways and promotions that claim to offer lucrative rewards and exclusive access to services.
"The use of themed messages and localized promotion strategies proved to be particularly effective in regional community chats," the researchers said. "By tailoring their approach to the interests and needs of the local population, Ajina was able to significantly increase the likelihood of successful infections."
The threat actors have also been observed bombarding Telegram channels with several messages using multiple accounts, at times simultaneously, indicating a coordinated effort that likely employs some sort of an automated distribution tool.
The malware in itself is fairly straightforward in that, once installed, it establishes contact with a remote server and requests the victim to grant it permission to access SMS messages, phone number APIs, and current cellular network information, among others.
Ajina.Banker is capable of gathering SIM card information, a list of installed financial apps, and SMS messages, which are then exfiltrated to the server.
New versions of the malware are also engineered to serve phishing pages in an attempt to collect banking information. Furthermore, they can access call logs and contacts, as well as abuse Android's accessibility services API to prevent uninstallation and grant themselves additional permissions.
Google told The Hacker News that it did not find any evidence of the malware being propagated via the Google Play Store and that Android users are protected against the threat by Google Play Protect, which is on by default on Android devices with Google Play Services.
"The hiring of Java coders, created Telegram bot with the proposal of earning some money, also indicates that the tool is in the process of active development and has support of a network of affiliated employees," the researchers said.
"Analysis of the file names, sample distribution methods, and other activities of the attackers suggests a cultural familiarity with the region in which they operate."
The disclosure comes as Zimperium uncovered links between two Android malware families tracked as SpyNote and Gigabud (which is part of the GoldFactory family that also includes GoldDigger).
"Domains with really similar structure (using the same unusual keywords as subdomains) and targets used to spread Gigabud samples and were also used to distribute SpyNote samples," the company said. "This overlap in distribution shows that the same threat actor is likely behind both malware families, pointing to a well-coordinated and broad campaign."
Beware: New Vo1d Malware Infects 1.3 Million Android-based TV Boxes Worldwide
13.9.24 Virus The Hacker News
Nearly 1.3 million Android-based TV boxes running outdated versions of the operating system and belonging to users spanning 197 countries have been infected by a new malware dubbed Vo1d (aka Void).
"It is a backdoor that puts its components in the system storage area and, when commanded by attackers, is capable of secretly downloading and installing third-party software," Russian antivirus vendor Doctor Web said in a report published today.
A majority of the infections have been detected in Brazil, Morocco, Pakistan, Saudi Arabia, Argentina, Russia, Tunisia, Ecuador, Malaysia, Algeria, and Indonesia.
It's currently not known what the source of the infection is, although it's suspected that it may have either involved an instance of prior compromise that allows for gaining root privileges or the use of unofficial firmware versions with built-in root access.
The following TV models have been targeted as part of the campaign -
KJ-SMART4KVIP (Android 10.1; KJ-SMART4KVIP Build/NHG47K)
R4 (Android 7.1.2; R4 Build/NHG47K)
TV BOX (Android 12.1; TV BOX Build/NHG47K)
The attack entails the substitution of the "/system/bin/debuggerd" daemon file (with the original file moved to a backup file named "debuggerd_real"), as well as the introduction of two new files – "/system/xbin/vo1d" and "/system/xbin/wd" – which contain the malicious code and operate concurrently.

"Before Android 8.0, crashes were handled by the debuggerd and debuggerd64 daemons," Google notes in its Android documentation. "In Android 8.0 and higher, crash_dump32 and crash_dump64 are spawned as needed."
Two different files shipped as part of the Android operating system – install-recovery.sh and daemonsu – have been modified as part of the campaign to trigger the execution of the malware by starting the "wd" module.
"The trojan's authors probably tried to disguise one if its components as the system program '/system/bin/vold,' having called it by the similar-looking name 'vo1d' (substituting the lowercase letter 'l' with the number '1')," Doctor Web said.
The "vo1d" payload, in turn, starts "wd" and ensures it's persistently running, while also downloading and running executables when instructed by a command-and-control (C2) server. Furthermore, it keeps tabs on specified directories and installs the APK files that it finds in them.
"Unfortunately, it is not uncommon for budget device manufacturers to utilize older OS versions and pass them off as more up-to-date ones to make them more attractive," the company said.
Update#
Google told The Hacker News that the infected TV models were not Play Protect certified Android devices and likely used source code from the Android Open Source Project code repository. The company’s entire statement is as follows -
“These off-brand devices discovered to be infected were not Play Protect certified Android devices. If a device isn't Play Protect certified, Google doesn’t have a record of security and compatibility test results. Play Protect certified Android devices undergo extensive testing to ensure quality and user safety. To help you confirm whether or not a device is built with Android TV OS and Play Protect certified, our Android TV website provides the most up-to-date list of partners. You can also take these steps to check if your device is Play Protect certified. ”
Blind Eagle Targets Colombian Insurance Sector with Customized Quasar RAT
9.9.24 Virus The Hacker News

The Colombian insurance sector is the target of a threat actor tracked as Blind Eagle with the end goal of delivering a customized version of a known commodity remote access trojan (RAT) known as Quasar RAT since June 2024.
"Attacks have originated with phishing emails impersonating the Colombian tax authority," Zscaler ThreatLabz researcher Gaetano Pellegrino said in a new analysis published last week.
The advanced persistent threat (APT), also known as AguilaCiega, APT-C-36, and APT-Q-98, has a track record of focusing on organizations and individuals in South America, particularly related to the government and finance sectors in Colombia and Ecuador.
The attack chains, as recently documented by Kaspersky, originate with phishing emails that entice recipients into clicking on malicious links that serve as the launchpad for the infection process.
The links, either embedded within a PDF attachment or directly in the email body, point to ZIP archives hosted on a Google Drive folder associated with a compromised account that belongs to a regional government organization in Colombia.
"The lure used by Blind Eagle involved sending a notification to the victim, claiming to be a seizure order due to outstanding tax payments," Pellegrino noted. "This is intended to create a sense of urgency and pressure the victim into taking immediate action."

The archive contains within it a Quasar RAT variant dubbed BlotchyQuasar, which packs in additional layers of obfuscation using tools like DeepSea or ConfuserEx to hinder analysis and reverse engineering efforts. It was previously detailed by IBM X-Force in July 2023.
The malware includes capabilities to log keystrokes, execute shell commands, steal data from web browsers and FTP clients, and monitor a victim's interactions with specific banking and payment services located in Colombia and Ecuador.
It also leverages Pastebin as a dead-drop resolver to fetch the command-and-control (C2) domain, with the threat actor leveraging Dynamic DNS (DDNS) services to host the C2 domain.
"Blind Eagle typically shields its infrastructure behind a combination of VPN nodes and compromised routers, primarily located in Colombia," Pellegrino said. "This attack demonstrates the continued use of this strategy."
New Android SpyAgent Malware Uses OCR to Steal Crypto Wallet Recovery Keys
9.9.24 Virus The Hacker News
Android device users in South Korea have emerged as a target of a new mobile malware campaign that delivers a new type of threat dubbed SpyAgent.
The malware "targets mnemonic keys by scanning for images on your device that might contain them," McAfee Labs researcher SangRyol Ryu said in an analysis, adding the targeting footprint has broadened in scope to include the U.K.
The campaign makes use of bogus Android apps that are disguised as seemingly legitimate banking, government facilities, streaming, and utility apps in an attempt to trick users into installing them. As many as 280 fake applications have been detected since the start of the year.
It all starts with SMS messages bearing booby-trapped links that urge users to download the apps in question in the form of APK files hosted on deceptive sites. Once installed, they are designed to request intrusive permissions to collect data from the devices.
This includes contacts, SMS messages, photos, and other device information, all of which is then exfiltrated to an external server under the threat actor's control.

The most notable feature is its ability to leverage optical character recognition (OCR) to steal mnemonic keys, which refer to a recovery or seed phrase that allows users to regain access to their cryptocurrency wallets.
Unauthorized access to the mnemonic keys could, therefore, allow threat actors to take control of the victims' wallets and siphon all the funds stored in them.
McAfee Labs said the command-and-control (C2) infrastructure suffered from serious security lapses that not only allowed navigating to the site's root directory without authentication, but also left exposed the gathered data from victims.
The server also hosts an administrator panel that acts as a one-stop shop to remotely commandeer the infected devices. The presence of an Apple iPhone device running iOS 15.8.2 with system language set to Simplified Chinese ("zh") in the panel is a sign that it may also be targeting iOS users.

"Originally, the malware communicated with its command-and-control (C2) server via simple HTTP requests," Ryu said. "While this method was effective, it was also relatively easy for security tools to track and block."
"In a significant tactical shift, the malware has now adopted WebSocket connections for its communications. This upgrade allows for more efficient, real-time, two-way interactions with the C2 server and helps it avoid detection by traditional HTTP-based network monitoring tools."
The development comes a little over a month after Group-IB exposed another Android remote access trojan (RAT) referred to as CraxsRAT targeting banking users in Malaysia since at least February 2024 using phishing websites. It's worth pointing out that CraxsRAT campaigns have also been previously found to have targeted Singapore no later than April 2023.
"CraxsRAT is a notorious malware family of Android Remote Administration Tools (RAT) that features remote device control and spyware capabilities, including keylogging, performing gestures, recording cameras, screens, and calls," the Singaporean company said.
"Victims that downloaded the apps containing CraxsRAT android malware will experience credentials leakage and their funds withdrawal illegitimately."
Malware Attackers Using MacroPack to Deliver Havoc, Brute Ratel, and PhantomCore
5.9.24 Virus The Hacker News

Threat actors are likely employing a tool designated for red teaming exercises to serve malware, according to new findings from Cisco Talos.
The program in question is a payload generation framework called MacroPack, which is used to generate Office documents, Visual Basic scripts, Windows shortcuts, and other formats for penetration testing and social engineering assessments. It was developed by French developer Emeric Nasi.
The cybersecurity company said it found artifacts uploaded to VirusTotal from China, Pakistan, Russia, and the U.S. that were all generated by MacroPack and used to deliver various payloads such as Havoc, Brute Ratel, and a new variant of PhantomCore, a remote access trojan (RAT) attributed to a hacktivist group named Head Mare.
"A common feature in all the malicious documents we dissected that caught our attention is the existence of four non-malicious VBA subroutines," Talos researcher Vanja Svajcer said.
"These subroutines appeared in all the samples and were not obfuscated. They also had never been used by any other malicious subroutines or anywhere else in any documents."
An important aspect to note here is that the lure themes spanning these documents are varied, ranging from generic topics that instruct users to enable macros to official-looking documents that appear to come from military organizations. This suggests the involvement of distinct threat actors.

Some of the documents have also been observed taking advantage of advanced features offered as part of MacroPack to bypass anti-malware heuristic detections by concealing the malicious functionality using Markov chains to create seemingly meaningful functions and variable names.
The attack chains, observed between May and July 2024, follow a three-step process that entails sending a booby-trapped Office document containing MacroPack VBA code, which then decodes a next-stage payload to ultimately fetch and execute the final malware.
The development is a sign that threat actors are constantly updating tactics in response to disruptions and taking more sophisticated approaches to code execution.
New Cross-Platform Malware KTLVdoor Discovered in Attack on Chinese Trading Firm
5.9.24 Virus The Hacker News
The Chinese-speaking threat actor known as Earth Lusca has been observed using a new backdoor dubbed KTLVdoor as part of a cyber attack targeting an unnamed trading company based in China.
The previously unreported malware is written in Golang, and thus is a cross-platform weapon capable of targeting both Microsoft Windows and Linux systems.
"KTLVdoor is a highly obfuscated malware that masquerades as different system utilities, allowing attackers to carry out a variety of tasks including file manipulation, command execution, and remote port scanning," Trend Micro researchers Cedric Pernet and Jaromir Horejsi said in an analysis published Wednesday.
Some of the tools KTLVdoor impersonates include sshd, Java, SQLite, bash, and edr-agent, among others, with the malware distributed in the form of dynamic-link library (.dll) or a shared object (.so).
Perhaps the most unusual aspect of the activity cluster is the discovery of more than 50 command-and-control (C&C) servers, all hosted at Chinese company Alibaba, that have been identified as communicating with variants of the malware, raising the possibility that the infrastructure could be shared with other Chinese threat actors.
Earth Lusca is known to be active since at least 2021, orchestrating cyber attacks against public and private sector entities across Asia, Australia, Europe, and North America. It's assessed to share some tactical overlaps with other intrusion sets tracked as RedHotel and APT27 (aka Budworm, Emissary Panda, and Iron Tiger).
KTLVdoor, the latest addition to the group's malware arsenal, is highly obfuscated and gets its name from the use of a marker called "KTLV" in its configuration file that includes various parameters necessary to meet its functions, including the C&C servers to connect to.
Once initialized, the malware initiates contact with the C&C server on a loop, awaiting further instructions to be executed on the compromised host. The supported commands allow it to download/upload files, enumerate the file system, launch an interactive shell, run shellcode, and initiate scanning using ScanTCP, ScanRDP, DialTLS, ScanPing, and ScanWeb, among others.
That having said, not much is known about how the malware is distributed and if it has been used to target other entities across the world.
"This new tool is used by Earth Lusca, but it might also be shared with other Chinese-speaking threat actors," the researchers noted. "Seeing that all C&C servers were on IP addresses from China-based provider Alibaba, we wonder if the whole appearance of this new malware and the C&C server could not be some early stage of testing new tooling."
New Malware Masquerades as Palo Alto VPN Targeting Middle East Users
30.8.24 Virus The Hacker News

Cybersecurity researchers have disclosed a new campaign that potentially targets users in the Middle East through malware that disguises itself as Palo Alto Networks GlobalProtect virtual private network (VPN) tool.
"The malware can execute remote PowerShell commands, download and exfiltrate files, encrypt communications, and bypass sandbox solutions, representing a significant threat to targeted organizations," Trend Micro researcher Mohamed Fahmy said in a technical report.
The sophisticated malware sample has been observed employing a two-stage process and involves setting up connections to command-and-control (C2) infrastructure that purports to be a company VPN portal, allowing the threat actors to operate freely without tripping any alarms.
The initial intrusion vector for the campaign is currently unknown, although it's suspected to involve the use of phishing techniques to deceive users into thinking that they are installing the GlobalProtect agent. The activity has not been attributed to a specific threat actor or group.
The starting point is a setup.exe binary that deploys the primary backdoor component called GlobalProtect.exe, which, when installed, initiates a beaconing process that alerts the operators of the progress.
The first-stage executable is also responsible for dropping two additional configuration files (RTime.conf and ApProcessId.conf) that are used to exfiltrate system information to a C2 server (94.131.108[.]78), including the victim's IP address, operating system information, username, machine name, and sleep time sequence.
"The malware implements an evasion technique to bypass behavior analysis and sandbox solutions by checking the process file path and the specific file before executing the main code block," Fahmy noted.
The backdoor serves as a conduit to upload files, download next-stage payloads, and execute PowerShell commands. The beaconing to the C2 server takes place by means of the Interactsh open-source project.
"The malware pivots to a newly registered URL, 'sharjahconnect' (likely referring to the U.A.E. emirate Sharjah), designed to resemble a legitimate VPN portal for a company based in the U.A.E.," Fahmy said.
"This tactic is designed to allow the malware's malicious activities to blend in with expected regional network traffic and enhance its evasion characteristics."
New Android Malware NGate Steals NFC Data to Clone Contactless Payment Cards
26.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered new Android malware that can relay victims' contactless payment data from physical credit and debit cards to an attacker-controlled device with the goal of conducting fraudulent operations.
The Slovak cybersecurity company is tracking the novel malware as NGate, stating it observed the crimeware campaign targeting three banks in Czechia.
The malware "has the unique ability to relay data from victims' payment cards, via a malicious app installed on their Android devices, to the attacker's rooted Android phone," researchers Lukáš Štefanko and Jakub Osmani said in an analysis.
The activity is part of a broader campaign that has been found to target financial institutions in Czechia since November 2023 using malicious progressive web apps (PWAs) and WebAPKs. The first recorded use of NGate was in March 2024.
The end goal of the attacks is to clone near-field communication (NFC) data from victims' physical payment cards using NGate and transmit the information to an attacker device that then emulates the original card to withdraw money from an ATM.
NGate has its roots in a legitimate tool named NFCGate, which was originally developed in 2015 for security research purposes by students of the Secure Mobile Networking Lab at TU Darmstadt.

The attack chains are believed to involve a combination of social engineering and SMS phishing to trick users into installing NGate by directing users to short-lived domains impersonating legitimate banking websites or official mobile banking apps available on the Google Play store.
As many as six different NGate apps have been identified to date between November 2023 and March 2024, when the activities came to a halt likely following the arrest of a 22-year-old by Czech authorities in connection with stealing funds from ATMs.
NGate, besides abusing the functionality of NFCGate to capture NFC traffic and pass it along to another device, prompts users to enter sensitive financial information, including banking client ID, date of birth, and the PIN code for their banking card. The phishing page is presented within a WebView.
"It also asks them to turn on the NFC feature on their smartphone," the researchers said. "Then, victims are instructed to place their payment card at the back of their smartphone until the malicious app recognizes the card."
The attacks further adopt an insidious approach in that victims, after having installed the PWA or WebAPK app through links sent via SMS messages, have their credentials phished and subsequently receive calls from the threat actor, who pretends to be a bank employee and informs them that their bank account had been compromised as a result of installing the app.
They are subsequently instructed to change their PIN and validate their banking card using a different mobile app (i.e., NGate), an installation link to which is also sent through SMS. There is no evidence that these apps were distributed through the Google Play Store.
"NGate uses two distinct servers to facilitate its operations," the researchers explained. "The first is a phishing website designed to lure victims into providing sensitive information and capable of initiating an NFC relay attack. The second is an NFCGate relay server tasked with redirecting NFC traffic from the victim's device to the attacker's."
The disclosure comes as Zscaler ThreatLabz detailed a new variant of a known Android banking trojan called Copybara that's propagated via voice phishing (vishing) attacks and lures them into entering their bank account credentials.
"This new variant of Copybara has been active since November 2023, and utilizes the MQTT protocol to establish communication with its command-and-control (C2) server," Ruchna Nigam said.
"The malware abuses the accessibility service feature that is native to Android devices to exert granular control over the infected device. In the background, the malware also proceeds to download phishing pages that imitate popular cryptocurrency exchanges and financial institutions with the use of their logos and application names.
New Linux Malware 'sedexp' Hides Credit Card Skimmers Using Udev Rules
25.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new stealthy piece of Linux malware that leverages an unconventional technique to achieve persistence on infected systems and hide credit card skimmer code.
The malware, attributed to a financially motivated threat actor, has been codenamed sedexp by Aon's Stroz Friedberg incident response services team.
"This advanced threat, active since 2022, hides in plain sight while providing attackers with reverse shell capabilities and advanced concealment tactics," researchers Zachary Reichert, Daniel Stein, and Joshua Pivirotto said.
It's not surprising that malicious actors are constantly improvising and refining their tradecraft, and have turned to novel techniques to evade detection.
What makes sedexp noteworthy is its use of udev rules to maintain persistence. Udev, replacement for the Device File System, offers a mechanism to identify devices based on their properties and configure rules to respond when there is a change in the device state, i.e., a device is plugged in or removed.
Each line in the udev rules file has at least once key-value pair, making it possible to match devices by name and trigger certain actions when various device events are detected (e.g., trigger an automatic backup when an external drive is attached).
"A matching rule may specify the name of the device node, add symbolic links pointing to the node, or run a specified program as part of the event handling," SUSE Linux notes in its documentation. "If no matching rule is found, the default device node name is used to create the device node."
The udev rule for sedexp -- ACTION=="add", ENV{MAJOR}=="1", ENV{MINOR}=="8", RUN+="asedexpb run:+" -- is set up such that the malware is run whenever /dev/random (corresponds to device minor number 8) is loaded, which typically occurs upon every reboot.
Put differently, the program specified in the RUN parameter is executed every time after a system restart.
The malware comes with capabilities to launch a reverse shell to facilitate remote access to the compromised host, as well as modify memory to conceal any file containing the string "sedexp" from commands like ls or find.
Stroz Friedberg said in the instances it investigated, the capability has been put to use to hide web shells, altered Apache configuration files, and the udev rule itself.
"The malware was used to hide credit card scraping code on a web server, indicating a focus on financial gain," the researchers said. "The discovery of sedexp demonstrates the evolving sophistication of financially motivated threat actors beyond ransomware."
New macOS Malware "Cthulhu Stealer" Targets Apple Users' Data
23.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new information stealer that's designed to target Apple macOS hosts and harvest a wide range of information, underscoring how threat actors are increasingly setting their sights on the operating system.
Dubbed Cthulhu Stealer, the malware has been available under a malware-as-a-service (MaaS) model for $500 a month from late 2023. It's capable of targeting both x86_64 and Arm architectures.
"Cthulhu Stealer is an Apple disk image (DMG) that is bundled with two binaries, depending on the architecture," Cato Security researcher Tara Gould said. "The malware is written in Golang and disguises itself as legitimate software."
Some of the software programs it impersonates include CleanMyMac, Grand Theft Auto IV, and Adobe GenP, the last of which is an open-source tool that patches Adobe apps to bypass the Creative Cloud service and activates them without a serial key.
Users who end up launching the unsigned file after explicitly allowing it to be run – i.e., bypassing Gatekeeper protections – are prompted to enter their system password, an osascript-based technique that has been adopted by Atomic Stealer, Cuckoo, MacStealer, and Banshee Stealer.
In the next step, a second prompt is presented to enter their MetaMask password. Cthulhu Stealer is also designed to harvest system information and dump iCloud Keychain passwords using an open-source tool called Chainbreaker.
The stolen data, which also comprises web browser cookies and Telegram account information, is compressed and stored in a ZIP archive file, after which it's exfiltrated to a command-and-control (C2) server.

"The main functionality of Cthulhu Stealer is to steal credentials and cryptocurrency wallets from various stores, including game accounts," Gould said.
"The functionality and features of Cthulhu Stealer are very similar to Atomic Stealer, indicating the developer of Cthulhu Stealer probably took Atomic Stealer and modified the code. The use of osascript to prompt the user for their password is similar in Atomic Stealer and Cthulhu, even including the same spelling mistakes."
The threat actors behind the malware are said to be no longer active, in part driven by disputes over payments that have led to accusations of exit scam by affiliates, resulting in the main developer being permanently banned from a cybercrime marketplace used to advertise the stealer.
Cthulhu Stealer isn't particularly sophisticated and lacks anti-analysis techniques that could allow it to operate stealthily. It is also short of any standout feature that distinguishes it from other similar offerings in the underground.
While threats to macOS are much less prevalent than to Windows and Linux, users are advised to download software only from trusted sources, stay away from installing unverified apps, and keep their systems up-to-date with the latest security updates.
The surge in macOS malware hasn't gone unnoticed by Apple, which, earlier this month, announced an update to its next version of the operating system that aims to add more friction when attempting to open software that isn't signed correctly or notarized.
"In macOS Sequoia, users will no longer be able to Control-click to override Gatekeeper when opening software that isn't signed correctly or notarized," Apple said. "They'll need to visit System Settings > Privacy & Security to review security information for software before allowing it to run."
Hardware Backdoor Discovered in RFID Cards Used in Hotels and Offices Worldwide
23.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a hardware backdoor within a particular model of MIFARE Classic contactless cards that could allow authentication with an unknown key and open hotel rooms and office doors.
The attacks have been demonstrated against FM11RF08S, a new variant of MIFARE Classic that was released by Shanghai Fudan Microelectronics in 2020.
"The FM11RF08S backdoor enables any entity with knowledge of it to compromise all user-defined keys on these cards, even when fully diversified, simply by accessing the card for a few minutes," Quarkslab researcher Philippe Teuwen said.
The secret key is not only common to existing FM11RF08S cards, the investigation found that "the attacks could be executed instantaneously by an entity in a position to carry out a supply chain attack."
Compounding matters further, a similar backdoor has been identified in the previous generation, FM11RF08, that's protected with another key. The backdoor has been observed in cards dating back to November 2007.
An optimized version of the attack could speed up the process of cracking a key by five to six times by partially reverse engineering the nonce generation mechanism.
"The backdoor [...] allows the instantaneous cloning of RFID smart cards used to open office doors and hotel rooms around the world," the company said in a statement.
"Although the backdoor requires just a few minutes of physical proximity to an affected card to conduct an attack, an attacker in a position to carry out a supply chain attack could execute such attacks instantaneously at scale."
Consumers are urged to check if they are susceptible, especially in light of the fact that these cards are used widely in hotels across the U.S., Europe, and India.
The backdoor and its key "allows us to launch new attacks to dump and clone these cards, even if all their keys are properly diversified," Teuwen noted.
This is not the first time security issues have been unearthed in locking systems used in hotels. Earlier this March, Dormakaba's Saflok electronic RFID locks were found to harbor severe shortcomings that could be weaponized by threat actors to forge keycards and unlock doors.
New Malware PG_MEM Targets PostgreSQL Databases for Crypto Mining
22.8.24 Virus The Hacker News
Cybersecurity researchers have unpacked a new malware strain dubbed PG_MEM that's designed to mine cryptocurrency after brute-forcing their way into PostgreSQL database instances.
"Brute-force attacks on Postgres involve repeatedly attempting to guess the database credentials until access is gained, exploiting weak passwords," Aqua security researcher Assaf Morag said in a technical report.
"Once accessed, attackers can leverage the COPY ... FROM PROGRAM SQL command to execute arbitrary shell commands on the host, allowing them to perform malicious activities such as data theft or deploying malware."
The attack chain observed by the cloud security firm entails targeting misconfigured PostgreSQL databases to create an administrator role in Postgres and exploiting a feature called PROGRAM to run shell commands.
In addition, a successful brute-force attack is followed by the threat actor conducting initial reconnaissance and executing commands to strip the "postgres" user of superuser permissions, thereby restricting the privileges of other threat actors who might gain access through the same method.

The shell commands are responsible for dropping two payloads from a remote server ("128.199.77[.]96"), namely PG_MEM and PG_CORE, which are capable of terminating competing processes (e.g., Kinsing), setting up persistence on the host, and ultimately deploying the Monero cryptocurrency miner.
This is accomplished by making use of a PostgreSQL command called COPY, which allows for copying data between a file and a database table. It particularly weaponizes a parameter known as PROGRAM that enables the server to run the passed command and write the program execution results to the table.
"While [cryptocurrency mining] is the main impact, at this point the attacker can also run commands, view data, and control the server," Morag said.
"This campaign is exploiting internet facing Postgres databases with weak passwords. Many organizations connect their databases to the internet, weak password is a result of a misconfiguration, and lack of proper identity controls."
North Korean Hackers Deploy New MoonPeak Trojan in Cyber Campaign
21.8.24 Virus The Hacker News
A new remote access trojan called MoonPeak has been discovered as being used by a state-sponsored North Korean threat activity cluster as part of a new campaign.
Cisco Talos attributed the malicious cyber campaign to a hacking group it tracks as UAT-5394, which it said exhibits some level of tactical overlaps with a known nation-state actor codenamed Kimsuky.
MoonPeak, under active development by the threat actor, is a variant of the open-source Xeno RAT malware, which was previously deployed as part of phishing attacks that are designed to retrieve the payload from actor-controlled cloud services like Dropbox, Google Drive, and Microsoft OneDrive.
Some of the key features of Xeno RAT include the ability to load additional plugins, launch and terminate processes, and communicate with a command-and-control (C2) server.
Talos said the commonalities between the two intrusion sets either indicate UAT-5394 is actually Kimsuky (or its sub-group) or it's another hacking crew within the North Korean cyber apparatus that borrows its toolbox from Kimsuky.
Key to realizing the campaign is the use of new infrastructure, including C2 servers, payload-hosting sites, and test virtual machines, that have been created to spawn new iterations of MoonPeak.
"The C2 server hosts malicious artifacts for download, which is then used to access and set up new infrastructure to support this campaign," Talos researchers Asheer Malhotra, Guilherme Venere, and Vitor Ventura said in a Wednesday analysis.

"In multiple instances, we also observed the threat actor access existing servers to update their payloads and retrieve logs and information collected from MoonPeak infections."
The shift is seen as part of a broader pivot from using legitimate cloud storage providers to setting up their own servers. That said, the targets of the campaign are currently not known.
An important aspect to note here is that "the constant evolution of MoonPeak runs hand-in-hand with new infrastructure set up by the threat actors" and that each new version of the malware introduces more obfuscation techniques to thwart analysis and changes to the overall communication mechanism to prevent unauthorized connections.
"Simply put, the threat actors ensured that specific variants of MoonPeak only work with specific variants of the C2 server," the researchers pointed out.
"The timelines of the consistent adoption of new malware and its evolution such as in the case of MoonPeak highlights that UAT-5394 continues to add and enhance more tooling into their arsenal. The rapid pace of establishing new supporting infrastructure by UAT-5394 indicates that the group is aiming to rapidly proliferate this campaign and set up more drop points and C2 servers."
Styx Stealer Creator's OPSEC Fail Leaks Client List and Profit Details
21.8.24 Virus The Hacker News

In what's a case of an operational security (OPSEC) lapse, the operator behind a new information stealer called Styx Stealer leaked data from their own computer, including details related to the clients, profit information, nicknames, phone numbers, and email addresses.
Styx Stealer, a derivative of the Phemedrone Stealer, is capable of stealing browser data, instant messenger sessions from Telegram and Discord, and cryptocurrency wallet information, cybersecurity company Check Point said in an analysis. It first emerged in April 2024.
"Styx Stealer is most likely based on the source code of an old version of Phemedrone Stealer, which lacks some features found in newer versions such as sending reports to Telegram, report encryption, and more," the company noted.
"However, the creator of Styx Stealer added some new features: auto-start, clipboard monitor and crypto-clipper, additional sandbox evasion, and anti-analysis techniques, and re-implemented sending data to Telegram."
Advertised for $75 a month (or $230 for three months or $350 for a lifetime subscription) on a dedicated website ("styxcrypter[.]com"), licenses for the malware requires prospective buyers to reach out to a Telegram account (@styxencode). It's linked to a Turkey-based threat actor who goes by the alias STY1X on cybercrime forums.
Check Point said it was able to unearth connections between STY1X and a March 2024 spam campaign distributing Agent Tesla malware that targeted various sectors across China, India, the Philippines, and the U.A.E. The Agent Tesla activity has been attired to a threat actor named Fucosreal, whose approximate location is in Nigeria.
This was made possible owing to the fact that STY1X debugged the stealer on their own machine using a Telegram bot token provided by Fucosreal. This fatal error allowed the cybersecurity company to identify as many as 54 customers and 8 cryptocurrency wallets, likely belonging to STY1X, that are said to have been used to receive the payments.
"This campaign was notable for its use of the Telegram Bot API for data exfiltration, leveraging Telegram's infrastructure instead of traditional command-and-control (C&C) servers, which are more easily detectable and blockable," Check Point noted.
"However, this method has a significant flaw: each malware sample must contain a bot token for authentication. Decrypting the malware to extract this token provides access to all data sent via the bot, exposing the recipient account."
The disclosure comes amid the emergence of new stealer malware strains such as Ailurophile, Banshee Stealer, and QWERTY, even as well-known stealers like RedLine are being used in phishing attacks targeting Vietnamese oil and gas, industrial, electrical and HVAC manufacturers, paint, chemical, and hotel industries.
"RedLine is a well-known stealer that targets login credentials, credit card details, browser history, and even cryptocurrency wallets," Broadcom-owned Symantec said. "It is actively used by multiple groups and individuals around the world."
"Once installed, it collects data from the victim's computer and sends it to a remote server or Telegram channel controlled by the attackers."
New macOS Malware TodoSwift Linked to North Korean Hacking Groups
21.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new macOS malware strain dubbed TodoSwift that they say exhibits commonalities with known malicious software used by North Korean hacking groups.
"This application shares several behaviors with malware we've seen that originated in North Korea (DPRK) — specifically the threat actor known as BlueNoroff — such as KANDYKORN and RustBucket," Kandji security researcher Christopher Lopez said in an analysis.
RustBucket, which first came to light in July 2023, refers to an AppleScript-based backdoor that's capable of fetching next-stage payloads from a command-and-control (C2) server.
Late last year, Elastic Security Labs also uncovered another macOS malware tracked as KANDYKORN that was deployed in connection with a cyber attack targeting blockchain engineers of an unnamed cryptocurrency exchange platform.
Delivered by means of a sophisticated multi-stage infection chain, KANDYKORN possesses capabilities to access and exfiltrate data from a victim's computer. It's also designed to terminate arbitrary processes and execute commands on the host.
A common trait that connects the two malware families lies in the use of linkpc[.]net domains for C2 purposes. Both RustBucket and KANDYKORN are assessed to be the work of a hacking crew called the Lazarus Group (and its sub-cluster known as BlueNoroff).
"The DPRK, via units like the Lazarus Group, continues to target crypto-industry businesses with the goal of stealing cryptocurrency in order to circumvent international sanctions that hinder the growth of their economy and ambitions," Elastic said at the time.
"In this intrusion, they targeted blockchain engineers active on a public chat server with a lure designed to speak to their skills and interests, with the underlying promise of financial gain."
The latest findings from the Apple device management and security platform show that TodoSwift is distributed in the form of a signed file named TodoTasks, which consists of a dropper component.
This module is a GUI application written in SwiftUI that's engineered to display a weaponized PDF document to the victim, while covertly downloading and executing a second-stage binary, a technique employed in RustBucket as well.
The lure PDF is a harmless Bitcoin-related document hosted on Google Drive, whereas the malicious payload is retrieved from an actor-controlled domain ("buy2x[.]com"). Further investigation into the exact specifics of the binary remains ongoing.
"The use of a Google Drive URL and passing the C2 URL as a launch argument to the stage 2 binary is consistent with previous DPRK malware affecting macOS systems," Lopez said.
Czech Mobile Users Targeted in New Banking Credential Theft Scheme
21.8.24 Virus The Hacker News
Mobile users in the Czech Republic are the target of a novel phishing campaign that leverages a Progressive Web Application (PWA) in an attempt to steal their banking account credentials.
The attacks have targeted the Czech-based Československá obchodní banka (CSOB), as well as the Hungarian OTP Bank and the Georgian TBC Bank, according to Slovak cybersecurity company ESET.
"The phishing websites targeting iOS instruct victims to add a Progressive Web Application (PWA) to their home-screens, while on Android the PWA is installed after confirming custom pop-ups in the browser," security researcher Jakub Osmani said.
"At this point, on both operating systems, these phishing apps are largely indistinguishable from the real banking apps that they mimic."
What's notable about this tactic is that users are deceived into installing a PWA, or even WebAPKs in some cases on Android, from a third-party site without having to specifically allow side loading.
An analysis of the command-and-control (C2) servers used and the backend infrastructure reveals that two different threat actors are behind the campaigns.
These websites are distributed via automated voice calls, SMS messages, and social media malvertising via Facebook and Instagram. The voice calls warn users about an out-of-date banking app and ask them to select a numerical option, following which the phishing URL is sent.

Users who end up clicking on the link are displayed a lookalike page that mimics the Google Play Store listing for the targeted banking app, or a copycat site for the application, ultimately leading to the "installation" of the PWA or WebAPK app under the guise of an app update.
"This crucial installation step bypasses traditional browser warnings of 'installing unknown apps': this is the default behavior of Chrome's WebAPK technology, which is abused by the attackers," Osmani explained. "Furthermore, installing a WebAPK does not produce any of the 'installation from an untrusted source' warnings."
For those who are on Apple iOS devices, instructions are provided to add the bogus PWA app to the Home Screen. The end goal of the campaign is to capture the banking credentials entered on the app and exfiltrate them to an attacker-controlled C2 server or a Telegram group chat.
ESET said it recorded the first phishing-via-PWA instance in early November 2023, with subsequent waves detected in March and May 2024. The very first instance of the technique was observed in July 2023.
The disclosure comes as cybersecurity researchers have uncovered a new variant of the Gigabud Android trojan that's spread via phishing websites mimicking the Google Play Store or sites impersonating various banks or governmental entities.
"The malware has various capabilities such as the collection of data about the infected device, exfiltration of banking credentials, collection of screen recordings, etc.," Broadcom-owned Symantec said.
It also follows Silent Push's discovery of 24 different control panels for a variety of Android banking trojans such as ERMAC, BlackRock, Hook, Loot, and Pegasus (not to be confused with NSO Group's spyware of the same name) that are operated by a threat actor named DukeEugene.
Blind Eagle Hackers Exploit Spear-Phishing to Deploy RATs in Latin America
21.8.24 Virus The Hacker News
Cybersecurity researchers have shed light on a threat actor known as Blind Eagle that has persistently targeted entities and individuals in Colombia, Ecuador, Chile, Panama, and other Latin American nations.
Targets of these attacks span several sectors, including governmental institutions, financial companies, energy and oil and gas companies.
"Blind Eagle has demonstrated adaptability in shaping the objectives of its cyberattacks and the versatility to switch between purely financially motivated attacks and espionage operations," Kaspersky said in a Monday report.
Also referred to as APT-C-36, Blind Eagle is believed to be active since at least 2018. The suspected Spanish-speaking group is known for using spear-phishing lures to distribute various publicly available remote access trojans such as AsyncRAT, BitRAT, Lime RAT, NjRAT, Quasar RAT, and Remcos RAT.
Earlier this March, eSentire detailed the adversary's use of a malware loader called Ande Loader to propagate Remcos RAT and NjRAT.
The starting point is a phishing email impersonating legitimate governmental institutions and financial and banking entities that deceptively warns recipients to take urgent action by clicking on a link that purports to lead them to the official website of the entity being mimicked.
The email messages also include a PDF or Microsoft Word attachment that contains the same URL, and, in some cases, a few additional details designed to impart a heightened sign of urgency and lend it a veneer of legitimacy.
The first set of URLs directs the users to actor-controlled sites that host an initial dropper, but only after determining if the victim belongs to a country that is among the group's targets. Else, they are led to the site of the organization the attackers are impersonating.
"This geographical redirection prevents new malicious sites from being flagged, and thwarts hunting and analysis of these attacks," the Russian cybersecurity vendor said.

The initial dropper comes in the form of a compressed ZIP archive, which, in turn, embeds a Visual Basic Script (VBS) responsible for retrieving the next-stage payload from a hard-coded remote server. These servers can range from image hosting sites to Pastebin to legitimate services like Discord and GitHub.
The second-stage malware, often obfuscated using steganographic methods, is a DLL or a .NET injector that subsequently contacts yet another malicious server to retrieve the final stage trojan.
"The group often uses process injection techniques to execute the RAT in the memory of a legitimate process, thereby evading process-based defenses," Kaspersky said.
"The group's preferred technique is process hollowing. This technique consists in creating a legitimate process in a suspended state, then unmapping its memory, replacing it with a malicious payload, and finally resuming the process to start execution."
The use of modified versions of open-source RATs gives Blind Eagle the flexibility to modify their campaigns at will, using them for cyber espionage or capturing credentials for Colombian financial services from the victim's browser when the window titles are matched against a predefined list of strings in the malware.
On the other hand, altered versions of NjRAT have been observed fitted with keylogging and screenshot-capturing capabilities to harvest sensitive information. Furthermore, the updated version supports installing additional plugins sent from a server to augment its functionality.
The changes also extend to the attack chains. As recently as June 2024, AsyncRAT has been distributed through a malware loader dubbed Hijack Loader, suggesting a high level of adaptability on the part of the threat actors. It also serves to highlight the addition of new techniques to sustain their operations.
"As simple as BlindEagle's techniques and procedures may appear, their effectiveness allows the group to sustain a high level of activity," Kaspersky concluded. "By consistently executing cyber espionage and financial credential theft campaigns, Blind Eagle remains a significant threat in the region.
New UULoader Malware Distributes Gh0st RAT and Mimikatz in East Asia
20.8.24 Virus The Hacker News
A new type of malware called UULoader is being used by threat actors to deliver next-stage payloads like Gh0st RAT and Mimikatz.
The Cyberint Research Team, which discovered the malware, said it's distributed in the form of malicious installers for legitimate applications targeting Korean and Chinese speakers.
There is evidence pointing to UULoader being the work of a Chinese speaker due to the presence of Chinese strings in program database (PDB) files embedded within the DLL file.
"UULoader's 'core' files are contained in a Microsoft Cabinet archive (.cab) file which contains two primary executables (an .exe and a .dll) which have had their file header stripped," the company said in a technical report shared with The Hacker News.
One of the executables is a legitimate binary that's susceptible to DLL side-loading, which is used to sideload the DLL file that ultimately loads the final stage, an obfuscate file named "XamlHost.sys" that's nothing but remote access tools such as Gh0st RAT or the Mimikatz credential harvester.
Present within the MSI installer file is a Visual Basic Script (.vbs) that's responsible for launching the executable – e.g., Realtek – with some UULoader samples also running a decoy file as a distraction mechanism.
"This usually corresponds to what the .msi file is pretending to be," Cyberint said. "For example, if it tries to disguise itself as a 'Chrome update,' the decoy will be an actual legitimate update for Chrome."
This is not the first time bogus Google Chrome installers have led to the deployment of Gh0st RAT. Last month, eSentire detailed an attack chain targeting Chinese Windows users that employed a fake Google Chrome site to disseminate the remote access trojan.
The development comes as threat actors have been observed creating thousands of cryptocurrency-themed lure sites used for phishing attacks that target users of popular cryptocurrency wallet services like Coinbase, Exodus, and MetaMask, among others.

"These actors are using free hosting services such as Gitbook and Webflow to create lure sites on crypto wallet typosquatter subdomains," Broadcom-owned Symantec said. "These sites lure potential victims with information about crypto wallets and download links that actually lead to malicious URLs."
These URLs serve as a traffic distribution system (TDS) redirecting users to phishing content or to some innocuous pages if the tool determines the visitor to be a security researcher.
Phishing campaigns have also been masquerading as legitimate government entities in India and the U.S. to redirect users to phony domains that collect sensitive information, which can be leveraged in future operations for further scams, sending phishing emails, spreading disinformation/misinformation, or distributing malware.
Some of these attacks are noteworthy for the abuse of Microsoft's Dynamics 365 Marketing platform to create subdomains and send phishing emails, thereby slipping through email filters. These attacks have been codenamed Uncle Scam owing to the fact that these emails impersonate the U.S. General Services Administration (GSA).
Social engineering efforts have further cashed in on the popularity of the generative artificial intelligence (AI) wave to set up scam domains mimicking OpenAI ChatGPT to proliferate suspicious and malicious activity, including phishing, grayware, ransomware, and command-and-control (C2).
"Remarkably, over 72% of the domains associate themselves with popular GenAI applications by including keywords like gpt or chatgpt," Palo Alto Networks Unit 42 said in an analysis last month. "Among all traffic toward these [newly registered domains], 35% was directed toward suspicious domains."
Cybercriminals Exploit Popular Software Searches to Spread FakeBat Malware
20.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a surge in malware infections stemming from malvertising campaigns distributing a loader called FakeBat.
"These attacks are opportunistic in nature, targeting users seeking popular business software," the Mandiant Managed Defense team said in a technical report. "The infection utilizes a trojanized MSIX installer, which executes a PowerShell script to download a secondary payload."
FakeBat, also called EugenLoader and PaykLoader, is linked to a threat actor named Eugenfest. The Google-owned threat intelligence team is tracking the malware under the name NUMOZYLOD and has attributed the Malware-as-a-Service (MaaS) operation to UNC4536.
"UNC4536's modus operandi involves leveraging malvertising to distribute trojanized MSIX installers disguised as popular software like Brave, KeePass, Notion, Steam, and Zoom," Mandiant said. "These trojanized MSIX installers are hosted on websites designed to mimic legitimate software hosting sites, luring users into downloading them."

What makes the attack notable is the use of MSIX installers disguised as Brave, KeePass, Notion, Steam, and Zoom, which have the ability to execute a script before launching the main application by means of a configuration called startScript.
UNC4536 is essentially a malware distributor, meaning FakeBat acts as a delivery vehicle for next-stage payloads for their business partners, including FIN7.
"NUMOZYLOD gathers system information, including operating system details, domain joined, and antivirus products installed," Mandiant said. "In some variants, it gathers the public IPv4 and IPv6 address of the host and sends this information to its C2, [and] creates a shortcut (.lnk) in the StartUp folder as its persistence."
The disclosure comes a little over a month after Mandiant also detailed the attack lifecycle associated with anther malware downloader named EMPTYSPACE (aka BrokerLoader or Vetta Loader), which has been used by a financially motivated threat cluster dubbed UNC4990 to facilitate data exfiltration and cryptojacking activities targeting Italian entities.
Multi-Stage ValleyRAT Targets Chinese Users with Advanced Tactics
16.8.24 Virus The Hacker News

Chinese-speaking users are the target of an ongoing campaign that distributes malware known as ValleyRAT.
"ValleyRAT is a multi-stage malware that utilizes diverse techniques to monitor and control its victims and deploy arbitrary plugins to cause further damage," Fortinet FortiGuard Labs researchers Eduardo Altares and Joie Salvio said.
"Another noteworthy characteristic of this malware is its heavy usage of shellcode to execute its many components directly in memory, significantly reducing its file footprint in the victim's system."
Details about the campaign first emerged in June 2024, when Zscaler ThreatLabz detailed attacks involving an updated version of the malware.
Exactly how the latest iteration of ValleyRAT is distributed is currently not known, although previous campaigns have leveraged email messages containing URLs pointing to compressed executables.
The attack sequence is a multi-stage process that starts with a first-stage loader that impersonates legitimate applications like Microsoft Office to make them appear harmless (e.g., "工商年报大师.exe" or "补单对接更新记录txt.exe").
Launching the executable causes the decoy document to be dropped and the shellcode to be loaded for advancing to the next phase of the attack. The loader also takes steps to validate that it's not running in a virtual machine.
The shellcode is responsible for initiating a beaconing module that contacts a command-and-control (C2) server to download two components – RuntimeBroker and RemoteShellcode – alongside setting persistence on the host and gaining administrator privileges by exploiting a legitimate binary named fodhelper.exe and achieve a UAC bypass.
The second method used for privilege escalation concerns the abuse of the CMSTPLUA COM interface, a technique previously adopted by threat actors connected to the Avaddon ransomware and also observed in recent Hijack Loader campaigns.
In a further attempt to make sure that the malware runs unimpeded on the machine, it configures exclusion rules to Microsoft Defender Antivirus and proceeds to terminate various antivirus-related processes based on matching executable filenames.
RuntimeBroker's primary task is to retrieve from the C2 server a component named Loader, which functions the same way as the first-stage loader and executes the beaconing module to repeat the infection process.
The Loader payload also exhibits some distinct characteristics, including carrying out checks to see if it's running in a sandbox and scanning the Windows Registry for keys related to apps like Tencent WeChat and Alibaba DingTalk, reinforcing the hypothesis that the malware exclusively targets Chinese systems.
On the other hand, RemoteShellcode is configured to fetch the ValleyRAT downloader from the C2 server, which, subsequently, uses UDP or TCP sockets to connect to the server and receive the final payload.
ValleyRAT, attributed to a threat group called Silver Fox, is a fully-featured backdoor capable of remotely controlling compromised workstations. It can take screenshots, execute files, and load additional plugins on the victim system.
"This malware involves several components loaded in different stages and mainly uses shellcode to execute them directly in memory, significantly reducing its file trace in the system," the researchers said.
"Once the malware gains a foothold in the system, it supports commands capable of monitoring the victim's activities and delivering arbitrary plugins to further the threat actors' intentions."
The development comes amid ongoing malspam campaigns that attempt to exploit an old Microsoft Office vulnerability (CVE-2017-0199) to execute malicious code and deliver GuLoader, Remcos RAT, and Sankeloader.
"CVE-2017-0199 is still targeted to allow for execution of remote code from within an XLS file," Broadcom-owned Symantec said. "The campaigns delivered a malicious XLS file with a link from which a remote HTA or RTF file would be executed to download the final payload."
New Banshee Stealer Targets 100+ Browser Extensions on Apple macOS Systems
16.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered new stealer malware that's designed to specifically target Apple macOS systems.
Dubbed Banshee Stealer, it's offered for sale in the cybercrime underground for a steep price of $3,000 a month and works across both x86_64 and ARM64 architectures.
"Banshee Stealer targets a wide range of browsers, cryptocurrency wallets, and around 100 browser extensions, making it a highly versatile and dangerous threat," Elastic Security Labs said in a Thursday report.
The web browsers and crypto wallets targeted by the malware comprise Google Chrome, Mozilla Firefox, Brave, Microsoft Edge, Vivaldi, Yandex, Opera, OperaGX, Exodus, Electrum, Coinomi, Guarda, Wasabi Wallet, Atomic, and Ledger.
It's also equipped to harvest system information and data from iCloud Keychain passwords and Notes, as well as incorporate a slew of anti-analysis and anti-debugging measures to determine if it's running in a virtual environment in an attempt to evade detection.
Furthermore, it makes use of the CFLocaleCopyPreferredLanguages API to avoid infecting systems where Russian is the primary language.
Like other macOS malware strains such as Cuckoo and MacStealer, Banshee Stealer also leverages osascript to display a fake password prompt to trick users into entering their system passwords for privilege escalation.
Among the other notable features include the ability to collect data from various files matching .txt, .docx, .rtf, .doc, .wallet, .keys, and .key extensions from the Desktop and Documents folders. The gathered data is then exfiltrated in a ZIP archive format to a remote server ("45.142.122[.]92/send/").
"As macOS increasingly becomes a prime target for cybercriminals, Banshee Stealer underscores the rising observance of macOS-specific malware," Elastic said.
The disclosure comes as Hunt.io and Kandji detailed another macOS stealer strain that leverages SwiftUI and Apple's Open Directory APIs for capturing and verifying passwords entered by the user in a bogus prompt displayed in order to complete the installation process.
"It begins by running a Swift-based dropper that displays a fake password prompt to deceive users," Broadcom-owned Symantec said. "After capturing credentials, the malware verifies them using the OpenDirectory API and subsequently downloads and executes malicious scripts from a command-and-control server."

This development also follows the continued emergence of new Windows-based stealers such as Flame Stealer, even as fake sites masquerading as OpenAI's text-to-video artificial intelligence (AI) tool, Sora, are being used to propagate Braodo Stealer.
Separately, Israeli users are being targeted with phishing emails containing RAR archive attachments that impersonate Calcalist and Mako to deliver Rhadamanthys Stealer.
New Malware Hits 300,000 Users with Rogue Chrome and Edge Extensions
11.8.24 Virus The Hacker News
An ongoing, widespread malware campaign has been observed installing rogue Google Chrome and Microsoft Edge extensions via a trojan distributed via fake websites masquerading as popular software.
"The trojan malware contains different deliverables ranging from simple adware extensions that hijack searches to more sophisticated malicious scripts that deliver local extensions to steal private data and execute various commands," the ReasonLabs research team said in an analysis.
"This trojan malware, existing since 2021, originates from imitations of download websites with add-ons to online games and videos."
The malware and the extensions have a combined reach of at least 300,000 users of Google Chrome and Microsoft Edge, indicating that the activity has a broad impact.
At the heart of the campaign is the use of malvertising to push lookalike websites promoting known software like Roblox FPS Unlocker, YouTube, VLC media player, Steam, or KeePass to trick users searching for these programs into downloading a trojan, which serves as a conduit for installing the browser extensions.
The digitally signed malicious installers register a scheduled task that, in turn, is configured to execute a PowerShell script responsible for downloading and executing the next-stage payload fetched from a remote server.

This includes modifying the Windows Registry to force the installation of extensions from Chrome Web Store and Microsoft Edge Add-ons that are capable of hijacking search queries on Google and Microsoft Bing and redirecting them through attacker-controlled servers.
"The extension cannot be disabled by the user, even with Developer Mode 'ON,'" ReasonLabs said. "Newer versions of the script remove browser updates."
It also launches a local extension that is downloaded directly from a command-and-control (C2) server, and comes with extensive capabilities to intercept all web requests and send them to the server, receive commands and encrypted scripts, and inject and load scripts into all pages.
On top of that, it hijacks search queries from Ask.com, Bing, and Google, and funnels them through its servers and then on to other search engines.
Users who are affected the malware attack are recommended to delete the scheduled task that reactivates the malware each day, remove the Registry keys, and delete the below files and folders from the system -
C:\Windows\system32\Privacyblockerwindows.ps1
C:\Windows\system32\Windowsupdater1.ps1
C:\Windows\system32\WindowsUpdater1Script.ps1
C:\Windows\system32\Optimizerwindows.ps1
C:\Windows\system32\Printworkflowservice.ps1
C:\Windows\system32\NvWinSearchOptimizer.ps1 - 2024 version
C:\Windows\system32\kondserp_optimizer.ps1 - May 2024 version
C:\Windows\InternalKernelGrid
C:\Windows\InternalKernelGrid3
C:\Windows\InternalKernelGrid4
C:\Windows\ShellServiceLog
C:\windows\privacyprotectorlog
C:\Windows\NvOptimizerLog
This is not the first time similar campaigns have been observed in the wild. In December 2023, the cybersecurity company detailed another trojan installer delivered through torrents that installed malicious web extensions masquerading as VPN apps but are actually designed to run a "cashback activity hack."
New Go-based Backdoor GoGra Targets South Asian Media Organization
7.8.24 Virus The Hacker News
An unnamed media organization in South Asia was targeted in November 20233 using a previously undocumented Go-based backdoor called GoGra.
"GoGra is written in Go and uses the Microsoft Graph API to interact with a command-and-control (C&C) server hosted on Microsoft mail services," Symantec, part of Broadcom, said in a report shared with The Hacker News.
It's currently not clear how it's delivered to target environments. However, GoGra is specifically configured to read messages from an Outlook username "FNU LNU" whose subject line starts with the word "Input."
The message contents are then decrypted using the AES-256 algorithm in Cipher Block Chaining (CBC) mode using a key, following which it executes the commands via cmd.exe.
The results of the operation are then encrypted and sent to the same user with the subject "Output."
GoGra is said to be the work of a nation-state hacking group known as Harvester owing to its similarities to a custom .NET implant named Graphon that also utilizes the Graph API for C&C purposes.
The development comes as threat actors are increasingly taking advantage of legitimate cloud services to stay low-key and avoid having to purchase dedicated infrastructure.
Some of the other new malware families that have employed the technique are listed below -
A previously unseen data exfiltration tool deployed by Firefly in a cyber attack targeting a military organization in Southeast Asia. The harvested information is uploaded to Google Drive using a hard-coded refresh token.
A new backdoor dubbed Grager that was deployed against three organizations in Taiwan, Hong Kong, and Vietnam in April 2024. It uses the Graph API to communicate with a C&C server hosted on Microsoft OneDrive. The activity has been tentatively linked to a suspected Chinese threat actor tracked as UNC5330.
A backdoor known as MoonTag that contains functionality for communicating with the Graph API and is attributed to a Chinese-speaking threat actor
A backdoor called Onedrivetools that has been used against IT services companies in the U.S. and Europe. It uses the Graph API to interact with a C&C server hosted on OneDrive to execute received commands and save the output to OneDrive.
"Although leveraging cloud services for command and control is not a new technique, more and more attackers have started to use it recently," Symantec said, pointing to malware like BLUELIGHT, Graphite, Graphican, and BirdyClient.
"The number of actors now deploying threats that leverage cloud services suggests that espionage actors are clearly studying threats created by other groups and mimicking what they perceive to be successful techniques."
Chameleon Android Banking Trojan Targets Users Through Fake CRM App
7.8.24 Virus The Hacker News
Cybersecurity researchers have lifted the lid on a new technique adopted by threat actors behind the Chameleon Android banking trojan targeting users in Canada by masquerading as a Customer Relationship Management (CRM) app.
"Chameleon was seen masquerading as a CRM app, targeting a Canadian restaurant chain operating internationally," Dutch security outfit ThreatFabric said in a technical report published Monday.
The campaign, spotted in July 2024, targeted customers in Canada and Europe, indicating an expansion of its victimology footprint from Australia, Italy, Poland, and the U.K.
The use of CRM-related themes for the malicious dropper apps containing the malware points to the targets being customers in the hospitality sector and Business-to-Consumer (B2C) employees.
The dropper artifacts are also designed to bypass Restricted Settings imposed by Google in Android 13 and later in order to prevent sideloaded apps from requesting for dangerous permissions (e.g., accessibility services), a technique previously employed by SecuriDroper and Brokewell.
Once installed, the app displays a fake login page for a CRM tool and then displays a bogus error message urging the victims to reinstall the app, when, in reality, it deploys the Chameleon payload.

This step is followed by loading the phony CRM web page again, this time asking them to complete the login process, only to display a different error message stating "Your account is not activated yet. Contact the HR department."
Chameleon is equipped to conduct on-device fraud (ODF) and fraudulently transfer users' funds, while also leveraging overlays and its wide-ranging permissions to harvest credentials, contact lists, SMS messages, and geolocation information.
"If the attackers succeed in infecting a device with access to corporate banking, Chameleon gets access to business banking accounts and poses a significant risk to the organization," ThreatFabric said. "The increased likelihood of such access for employees whose roles involve CRM is the likely reason behind the choice of the masquerading during this latest campaign."
The development comes weeks after IBM X-Force detailed a Latin American banking malware campaign undertaken by the CyberCartel group to steal credentials and financial data as well as deliver a trojan named Caiman by means of malicious Google Chrome extensions.
"The ultimate objective of these malicious activities is to install a harmful browser plugin on the victim's browser and use the Man-in-the-Browser technique," the company said.
"This allows the attackers to illegally collect sensitive banking information, along with other relevant data such as compromised machine information and on-demand screenshots. Updates and configurations are disseminated via a Telegram channel by the threat actors."
New Android Spyware LianSpy Evades Detection Using Yandex Cloud
6.8.24 Virus The Hacker News
Users in Russia have been the target of a previously undocumented Android post-compromise spyware called LianSpy since at least 2021.
Cybersecurity vendor Kaspersky, which discovered the malware in March 2024, noted its use of Yandex Cloud, a Russian cloud service, for command-and-control (C2) communications as a way to avoid having a dedicated infrastructure and evade detection.
"This threat is equipped to capture screencasts, exfiltrate user files, and harvest call logs and app lists," security researcher Dmitry Kalinin said in a new technical report published Monday.
It's currently not clear how the spyware is distributed, but the Russian company said it's likely deployed through either an unknown security flaw or direct physical access to the target phone. The malware-laced apps are disguised as Alipay or an Android system service.
LianSpy, once activated, determines if it's running as a system app to operate in the background using administrator privileges, or else requests a wide range of permissions that allow it to access contacts, call logs, and notifications, and draw overlays atop the screen.
It also checks if it's executing in a debugging environment to set up a configuration that persists across reboots, followed by hiding its icon from the launcher and trigger activities such as taking screenshots, exfiltrating data, and updating its configuration to specify what kinds of information needs to be captured.
In some variants, this has been found to include options to gather data from instant messaging apps popular in Russia as well as allow or prohibit running the malware only if it's either connected to Wi-Fi or a mobile network, among others.
"To update the spyware configuration, LianSpy searches for a file matching the regular expression "^frame_.+\\.png$" on a threat actor's Yandex Disk every 30 seconds," Kalinin said. "If found, the file is downloaded to the application's internal data directory."
The harvested data is stored in encrypted form in an SQL database table, specifying the type of record and its SHA-256 hash, such that only a threat actor in possession of the corresponding private RSA key can decrypt the stolen information.
Where LianSpy showcases its stealth is in its ability to bypass the privacy indicators feature introduced by Google in Android 12, which requires apps requesting for microphone and camera permissions to display a status bar icon.
"LianSpy developers have managed to bypass this protection by appending a cast value to the Android secure setting parameter icon_blacklist, which prevents notification icons from appearing in the status bar," Kalinin pointed out.
"LianSpy hides notifications from background services it calls by leveraging the NotificationListenerService that processes status bar notifications and is able to suppress them."
Another sophisticated aspect of the malware entails the use of the su binary with a modified name "mu" to gain root access, raising the possibility that it's likely delivered through a previously unknown exploit or physical device access.
LianSpy's emphasis on flying under the radar is also evidenced in the fact that C2 communications are unidirectional, with the malware not receiving any incoming commands. The Yandex Disk service is used for both transmitting stolen data and storing configuration commands.
Credentials for Yandex Disk are updated from a hard-coded Pastebin URL, which varies across malware variants. The use of legitimate services adds a layer of obfuscation, effectively clouding attribution.
LianSpy is the latest addition to a growing list of spyware tools, which are often delivered to target mobile devices – be it Android or iOS – by leveraging zero-day flaws.
"Beyond standard espionage tactics like harvesting call logs and app lists, it leverages root privileges for covert screen recording and evasion," Kalinin said. "Its reliance on a renamed su binary strongly suggests secondary infection following an initial compromise."
New Android Trojan "BlankBot" Targets Turkish Users' Financial Data
5.8.24 Virus The Hacker News

Cybersecurity researchers have discovered a new Android banking trojan called BlankBot targeting Turkish users with an aim to steal financial information.
"BlankBot features a range of malicious capabilities, which include customer injections, keylogging, screen recording and it communicates with a control server over a WebSocket connection," Intel 471 said in an analysis published last week.
Discovered on July 24, 2024, BlankBot is said to be undergoing active development, with the malware abusing Android's accessibility services permissions to obtain full control over the infected devices.
Cybersecurity
The names of some of the malicious APK files containing BlankBot are listed below -
app-release.apk (com.abcdefg.w568b)
app-release.apk (com.abcdef.w568b)
app-release-signed (14).apk (com.whatsapp.chma14)
app.apk (com.whatsapp.chma14p)
app.apk (com.whatsapp.w568bp)
showcuu.apk (com.whatsapp.w568b)
Like the recently resurfaced Mandrake Android trojan, BlankBot implements a session-based package installer to circumvent the restricted settings feature introduced in Android 13 to block sideloaded applications from directly requesting dangerous permissions.
"The bot asks the victim to allow installing applications from the third-party sources, then it retrieves the Android package kit (APK) file stored inside the application assets directory with no encryption and proceeds with the package installation process," Intel 471 said.
The malware comes with a wide range of features to perform screen recording, keylogging, and inject overlays based on specific commands received from a remote server to harvest bank account credentials, payment data, and even the pattern used to unlock the device.
BlankBot is also capable of intercepting SMS messages, uninstalling arbitrary applications, and gathering data such as contact lists and installed apps. It further makes use of the accessibility services API to prevent the user from accessing device settings or launching antivirus apps.
"BlankBot is a new Android banking trojan still under development, as evidenced by the multiple code variants observed in different applications," the cybersecurity company said. "Regardless, the malware can perform malicious actions once it infects an Android device."
A Google spokesperson told The Hacker News that the company has not found any apps containing the malware on the Google Play Store.
“Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services,” the tech giant said. “Google Play Protect warns users and blocks apps that contain this malware, even when those apps come from sources outside of Play.”
The disclosure comes as Google outlined the various steps it's taking to combat threat actors' use of cell-site simulators like Stingrays to inject SMS messages directly into Android phones, a fraud technique referred to as SMS Blaster fraud.
Cybersecurity
"This method to inject messages entirely bypasses the carrier network, thus bypassing all the sophisticated network-based anti-spam and anti-fraud filters," Google said. "SMS Blasters expose a fake LTE or 5G network which executes a single function: downgrading the user's connection to a legacy 2G protocol."
The mitigation measures include a user option to disable 2G at the modem level and turn off null ciphers, the latter of which is an essential configuration for a False Base Station in order to inject an SMS payload.
Earlier this May, Google also said it's stepping up cellular security by alerting users if their cellular network connection is unencrypted and if criminals are using cell-site simulators to snoop on users or send them SMS-based fraud messages.
(The story was updated after publication to include a response from Google.)
New Windows Backdoor BITSLOTH Exploits BITS for Stealthy Communication
2.8.24 Virus The Hacker News

Cybersecurity researchers have discovered a previously undocumented Windows backdoor that leverages a built-in feature called Background Intelligent Transfer Service (BITS) as a command-and-control (C2) mechanism.
The newly identified malware strain has been codenamed BITSLOTH by Elastic Security Labs, which made the discovery on June 25, 2024, in connection with a cyber attack targeting an unspecified Foreign Ministry of a South American government. The activity cluster is being tracked under the moniker REF8747.
"The most current iteration of the backdoor at the time of this publication has 35 handler functions including keylogging and screen capture capabilities," security researchers Seth Goodwin and Daniel Stepanic said. "In addition, BITSLOTH contains many different features for discovery, enumeration, and command-line execution."
It's assessed that the tool – in development since December 2021 – is being used by the threat actors for data gathering purposes. It's currently not clear who is behind it, although a source code analysis has uncovered logging functions and strings that suggest the authors could be Chinese speakers.
Another potential link to China comes from the use of an open-source tool called RingQ. RingQ is used to encrypt the malware and prevent detection by security software, which is then decrypted and executed directly in memory.
In June 2024, the AhnLab Security Intelligence Center's (ASEC) revealed that vulnerable web servers are being exploited to drop web shells, which are then leveraged to deliver additional payloads, including a cryptocurrency miner via RingQ. The attacks were attributed to a Chinese-speaking threat actor.
The attack is also notable for the use of STOWAWAY to proxy encrypted C2 traffic over HTTP and a port forwarding utility called iox, the latter of which has been previously leveraged by a Chinese cyber espionage group dubbed Bronze Starlight (aka Emperor Dragonfly) in Cheerscrypt ransomware attacks.
BITSLOTH, which takes the form of a DLL file ("flengine.dll"), is loaded by means of DLL side-loading techniques by using a legitimate executable associated with Image-Line known as FL Studio ("fl.exe").
"In the latest version, a new scheduling component was added by the developer to control specific times when BITSLOTH should operate in a victim environment," the researchers said. "This is a feature we have observed in other modern malware families such as EAGERBEE."
A fully-featured backdoor, BITSLOTH is capable of running and executing commands, uploading and downloading files, performing enumeration and discovery, and harvesting sensitive data through keylogging and screen capturing.
It can also set the communication mode to either HTTP or HTTPS, remove or reconfigure persistence, terminate arbitrary processes, log users off from the machine, restart or shutdown the system, and even update or delete itself from the host. A defining aspect of the malware is its use of BITS for C2.
"This medium is appealing to adversaries because many organizations still struggle to monitor BITS network traffic and detect unusual BITS jobs," the researchers added.
Cybercriminals Abusing Cloudflare Tunnels to Evade Detection and Spread Malware
2.8.24 Virus The Hacker News
Cybersecurity companies are warning about an uptick in the abuse of Clouflare's TryCloudflare free service for malware delivery.
The activity, documented by both eSentire and Proofpoint, entails the use of TryCloudflare to create a one-time tunnel that acts as a conduit to relay traffic from an attacker-controlled server to a local machine through Cloudflare's infrastructure.
Attack chains taking advantage of this technique have been observed delivering a cocktail of malware families such as AsyncRAT, GuLoader, PureLogs Stealer, Remcos RAT, Venom RAT, and XWorm.
The initial access vector is a phishing email containing a ZIP archive, which includes a URL shortcut file that leads the message recipient to a Windows shortcut file hosted on a TryCloudflare-proxied WebDAV server.
The shortcut file, in turn, executes next-stage batch scripts responsible for retrieving and executing additional Python payloads, while simultaneously displaying a decoy PDF document hosted on the same WebDAV server to keep up the ruse.
"These scripts executed actions such as launching decoy PDFs, downloading additional malicious payloads, and changing file attributes to avoid detection," eSentire noted.
"A key element of their strategy was using direct syscalls to bypass security monitoring tools, decrypting layers of shellcode, and deploying the Early Bird APC queue injection to stealthily execute code and evade detection effectively."

According to Proofpoint, the phishing lures are written in English, French, Spanish, and German, with the email volumes ranging from hundreds to tens of thousands of messages that target organizations from across the world. The themes cover a broad range of topics such as invoices, document requests, package deliveries, and taxes.
The campaign, while attributed to one cluster of related activity, has not been linked to a specific threat actor or group, but the email security vendor assessed it to be financially motivated.
The exploitation of TryCloudflare for malicious ends was first recorded last year, when Sysdig uncovered a cryptojacking and proxyjacking campaign dubbed LABRAT that weaponized a now-patched critical flaw in GitLab to infiltrate targets and obscure their command-and-control (C2) servers using Cloudflare tunnels.
Furthermore, the use of WebDAV and Server Message Block (SMB) for payload staging and delivery necessitates that enterprises restrict access to external file-sharing services to only known, allow-listed servers.
"The use of Cloudflare tunnels provide the threat actors a way to use temporary infrastructure to scale their operations providing flexibility to build and take down instances in a timely manner," Proofpoint researchers Joe Wise and Selena Larson said.

"This makes it harder for defenders and traditional security measures such as relying on static blocklists. Temporary Cloudflare instances allow attackers a low-cost method to stage attacks with helper scripts, with limited exposure for detection and takedown efforts."
The findings come as the Spamhaus Project called on Cloudflare to review its anti-abuse policies following cybercriminals' exploitation of its services to mask malicious actions and enhance their operational security by means of what's called "living-off-trusted-services" (LoTS).
It said it "observes miscreants moving their domains, which are already listed in the DBL, to Cloudflare to disguise the backend of their operation, be it spamvertized domains, phishing, or worse."
Hackers Distributing Malicious Python Packages via Popular Developer Q&A Platform
1.8.24 Virus The Hacker News

In yet another sign that threat actors are always looking out for new ways to trick users into downloading malware, it has come to light that the question-and-answer (Q&A) platform known as Stack Exchange has been abused to direct unsuspecting developers to bogus Python packages capable of draining their cryptocurrency wallets.
"Upon installation, this code would execute automatically, setting in motion a chain of events designed to compromise and control the victim's systems, while also exfiltrating their data and draining their crypto wallets," Checkmarx researchers Yehuda Gelb and Tzachi Zornstain said in a report shared with The Hacker News.
The campaign, which began on June 25, 2024, specifically singled out cryptocurrency users involved with Raydium and Solana. The list of rogue packages uncovered as part of the activity is listed below -
raydium (762 downloads)
raydium-sdk (137 downloads)
sol-instruct (115 downloads)
sol-structs (292 downloads)
spl-types (776 downloads)
The packages have been collectively downloaded 2,082 times. They are no longer available for download from the Python Package Index (PyPI) repository.
The malware concealed within the package served a full-fledged information stealer, casting a wide net of data, including web browser passwords, cookies, and credit card details, cryptocurrency wallets, and information associated with messaging apps like Telegram, Signal, and Session.
It also packed in capabilities to capture screenshots of the system, and search for files containing GitHub recovery codes and BitLocker keys. The gathered information was then compressed and exfiltrated to two different Telegram bots maintained by the threat actor.
Separately, a backdoor component present in the malware granted the attacker persistent remote access to victims' machines, enabling potential future exploits and long-term compromise.
The attack chain spans multiple stages, with the "raydium" package listing "spl-types" as a dependency in an attempt to conceal the malicious behavior and give users the impression that it was legitimate.
A notable aspect of the campaign is the use of Stack Exchange as a vector to drive adoption by posting ostensibly helpful answers referencing the package in question to developer questions related to performing swap transactions in Raydium using Python.

"By choosing a thread with high visibility — garnering thousands of views—the attacker maximized their potential reach," the researchers said, adding it was done so to "lend credibility to this package and ensure its widespread adoption."
While the answer no longer exists on Stack Exchange, The Hacker News found references to "raydium" in another unanswered question posted on the Q&A site dated July 9, 2024: "I have been struggling for nights to get a swap on solana network running in python 3.10.2 installed solana, solders and Raydium but I can't get it to work," a user said.
References to "raydium-sdk" have also surfaced in a post titled "How to Buy and Sell Tokens on Raydium using Python: A Step-by-Step Solana Guide" that was shared by a user named SolanaScribe on the social publishing platform Medium on June 29, 2024.
It's currently not clear when the packages were removed from PyPI, as two other users have responded to the Medium post seeking help from the author about installing "raydium-sdk" as recently as six days ago. Checkmarx told The Hacker News that the post is not the work of the threat actor.
This is not the first time bad actors have resorted to such a malware distribution method. Earlier this May, Sonatype revealed how a package named pytoileur was promoted via another Q&A service called Stack Overflow to facilitate cryptocurrency theft.
If anything, the development is evidence that attackers are leveraging trust in these community-driven platforms to push malware, leading to large-scale supply chain attacks.
"A single compromised developer can inadvertently introduce vulnerabilities into an entire company's software ecosystem, potentially affecting the whole corporate network," the researchers said. "This attack serves as a wake-up call for both individuals and organizations to reassess their security strategies."
The development comes as Fortinet FortiGuard Labs detailed a malicious PyPI package called zlibxjson that packed features to steal sensitive information, such as Discord tokens, cookies saved in Google Chrome, Mozilla Firefox, Brave, and Opera, and stored passwords from the browsers. The library attracted a total of 602 downloads before it was pulled from PyPI.
"These actions can lead to unauthorized access to user accounts and the exfiltration of personal data, clearly classifying the software as malicious," security researcher Jenna Wang said.
New Android Banking Trojan BingoMod Steals Money, Wipes Devices
1.8.24 Virus The Hacker News

Cybersecurity researchers have uncovered a new Android remote access trojan (RAT) called BingoMod that not only performs fraudulent money transfers from the compromised devices but also wipes them in an attempt to erase traces of the malware.
Italian cybersecurity firm Cleafy, which discovered the RAT towards the end of May 2024, said the malware is under active development. It attributed the Android trojan to a likely Romanian-speaking threat actor owing to the presence of Romanian language comments in the source code associated with early versions.
"BingoMod belongs to the modern RAT generation of mobile malware, as its remote access capabilities allow threat actors (TAs) to conduct Account Takeover (ATO) directly from the infected device, thus exploiting the on-device fraud (ODF) technique," researchers Alessandro Strino and Simone Mattia said.
It's worth mentioning here that this technique has been observed in other Android banking trojans, such as Medusa (aka TangleBot), Copybara, and TeaBot (aka Anatsa).
BingoMod, like BRATA, also stands out for employing a self-destruction mechanism that's designed to remove any evidence of the fraudulent transfer on the infected device so as to hinder forensic analysis. While this functionality is limited to the device's external storage, it's suspected that the remote access features could be used to initiate a complete factory reset.

Some of the identified apps masquerade as antivirus tools and an update for Google Chrome. Once installed, the app prompts the user to grant it accessibility services permissions, using it to initiate malicious actions.
This includes executing the main payload and locking out the user from the main screen to collect device information, which is then exfiltrated to an attacker-controlled server. It also abuses the accessibility services API to steal sensitive information displayed on the screen (e.g., credentials and bank account balances) and give itself permission to intercept SMS messages.

To initiate money transfers directly from compromised devices, BingoMod establishes a socket-based connection with the command-and-control infrastructure (C2) to receive as many as 40 commands remotely to take screenshots using Android's Media Projection API and interact with the device in real-time.
This also means that the ODF technique relies on a live operator to perform a money transfer of up to €15,000 (~$16,100) per transaction as opposed to leveraging an Automated Transfer System (ATS) to carry out financial fraud at scale.
Another crucial aspect is the threat actor's emphasis on evading detection using code obfuscation techniques and the ability to uninstall arbitrary apps from the compromised device, indicating that the malware authors are prioritizing simplicity over advanced features.
"In addition to real-time screen control, the malware shows phishing capabilities through Overlay Attacks and fake notifications," the researchers said. "Unusually, overlay attacks are not triggered when specific target apps are opened but are initiated directly by the malware operator."
Google Chrome Adds App-Bound Encryption to Protect Cookies from Malware
1.8.24 Virus The Hacker News
Google has announced that it's adding a new layer of protection to its Chrome browser through what's called app-bound encryption to prevent information-stealing malware from grabbing cookies on Windows systems.
"On Windows, Chrome uses the Data Protection API (DPAPI) which protects the data at rest from other users on the system or cold boot attacks," Will Harris from the Chrome security team said. "However, the DPAPI does not protect against malicious applications able to execute code as the logged in user – which info-stealers take advantage of."
App-bound encryption is an improvement over DPAPI in that it interweaves an app's identity (i.e., Chrome in this case) into encrypted data to prevent another app on the system from accessing it when decryption is attempted.
"Because the app-bound service is running with system privileges, attackers need to do more than just coax a user into running a malicious app," Harris said. "Now, the malware has to gain system privileges, or inject code into Chrome, something that legitimate software shouldn't be doing."
Given that the method strongly binds the encryption key to the machine, it will not function correctly in environments where Chrome profiles roam between multiple machines. Organizations that support roaming profiles are encouraged to follow its best practices and configure the ApplicationBoundEncryptionEnabled policy.
The change, which went live last week with the release of Chrome 127, applies only to cookies, although Google said it intends to expand this protection to passwords, payment data, and other persistent authentication tokens.
Back in April, the tech giant outlined a technique that employs a Windows event log type called DPAPIDefInformationEvent to reliably detect access to browser cookies and credentials from another application on the system.
It's worth noting that the web browser secures passwords and cookies in Apple macOS and Linux systems using Keychain services and system-provided wallets such as kwallet or gnome-libsecret, respectively.
The development comes amid a slew of security improvements added to Chrome in recent months, including enhanced Safe Browsing, Device Bound Session Credentials (DBSC), and automated scans when downloading potentially suspicious and malicious files.
"App-bound encryption increases the cost of data theft to attackers and also makes their actions far noisier on the system," Harris said. "It helps defenders draw a clear line in the sand for what is acceptable behavior for other apps on the system."
It also follows Google's announcement that it no longer plans to deprecate third-party cookies in Chrome, prompting the World Wide Web Consortium (W3C) to reiterate that they enable tracking and that the decision undermines the progress achieved so far to make the web work without third-party cookies.
"Tracking and subsequent data collection and brokerage can support micro-targeting of political messages, which can have a detrimental impact on society," it said. "The unfortunate climb-down will also have secondary effects, as it is likely to delay cross-browser work on effective alternatives to third-party cookies."
Chinese Hackers Target Japanese Firms with LODEINFO and NOOPDOOR Malware
1.8.24 Virus The Hacker News
Japanese organizations are the target of a Chinese nation-state threat actor that leverages malware families like LODEINFO and NOOPDOOR to harvest sensitive information from compromised hosts while stealthily remaining under the radar in some cases for a time period ranging from two to three years.
Israeli cybersecurity company Cybereason is tracking the campaign under the name Cuckoo Spear, attributing it as related to a known intrusion set dubbed APT10, which is also known as Bronze Riverside, ChessMaster, Cicada, Cloudhopper, MenuPass, MirrorFace, Purple Typhoon (formerly Potassium), and Stone Panda.
"The actors behind NOOPDOOR not only utilized LODEINFO during the campaign, but also utilized the new backdoor to exfiltrate data from compromised enterprise networks," it said.
The findings come weeks after JPCERT/CC warned of cyber attacks mounted by the threat actor targeting Japanese entities using the two malware strains.
Earlier this January, ITOCHU Cyber & Intelligence disclosed that it had uncovered an updated version of the LODEINFO backdoor incorporating anti-analysis techniques, highlighting the use of spear-phishing emails to propagate the malware.
Trend Micro, which originally coined the term MenuPass to describe the threat actor, has characterized APT10 as an umbrella group comprising two clusters it calls Earth Tengshe and Earth Kasha. The hacking crew is known to be operational since at least 2006.

Image Source: Trend Micro
While Earth Tengshe is linked to campaigns distributing SigLoader and SodaMaster, Earth Kasha is attributed to the exclusive use of LODEINFO and NOOPDOOR. Both the sub-groups have been observed targeting public-facing applications with the aim of exfiltrating data and information in the network.
Earth Tengshe is also said to be related to another cluster codenamed Bronze Starlight (aka Emperor Dragonfly or Storm-0401), which has a history of operating short-lived ransomware families like LockFile, Atom Silo, Rook, Night Sky, Pandora, and Cheerscrypt.

Image Source: JPCERT/CC
On the other hand, Earth Kasha has been found to switch up its initial access methods by exploiting public-facing applications since April 2023, taking advantage of unpatched flaws in Array AG (CVE-2023-28461), Fortinet (CVE-2023-27997), and Proself (CVE-2023-45727) instances to distribute LODEINFO and NOOPDOOR (aka HiddenFace).
LODEINFO comes packed with several commands to execute arbitrary shellcode, log keystrokes, take screenshots, terminate processes, and exfiltrate files back to an actor-controlled server. NOOPDOOR, which shares code similarities with another APT10 backdoor known as ANEL Loader, features functionality to upload and download files, execute shellcode, and run more programs.
"LODEINFO appears to be used as a primary backdoor and NOOPDOOR acts as a secondary backdoor, keeping persistence within the compromised corporate network for more than two years," Cybereason said. "Threat actors maintain persistence within the environment by abusing scheduled tasks."
Cybercriminals Deploy 100K+ Malware Android Apps to Steal OTP Codes
1.8.24 Virus The Hacker News
A new malicious campaign has been observed making use of malicious Android apps to steal users' SMS messages since at least February 2022 as part of a large-scale campaign.
The malicious apps, spanning over 107,000 unique samples, are designed to intercept one-time passwords (OTPs) used for online account verification to commit identity fraud.
"Of those 107,000 malware samples, over 99,000 of these applications are/were unknown and unavailable in generally available repositories," mobile security firm Zimperium said in a report shared with The Hacker News. "This malware was monitoring one-time password messages across over 600 global brands, with some brands having user counts in the hundreds of millions of users."
Victims of the campaign have been detected in 113 countries, with India and Russia topping the list, followed by Brazil, Mexico, the U.S., Ukraine, Spain, and Turkey.
The starting point of the attack is the installation of a malicious app that a victim is tricked into installing on their device either through deceptive ads mimicking Google Play Store app listings or any of the 2,600 Telegram bots that serve as the distribution channel by masquerading as legitimate services (e.g., Microsoft Word).
Once installed, the app requests permission to access incoming SMS messages, following which it reaches out to one of the 13 command-and-control (C2) servers to transmit stolen SMS messages.
"The malware remains hidden, constantly monitoring new incoming SMS messages," the researchers said. "Its primary target is OTPs used for online account verification."
It's currently not clear who is behind the operation, although the threat actors have been observed accepting various payment methods, including cryptocurrency, to fuel a service called Fast SMS (fastsms[.]su) that allows customers to purchase access to virtual phone numbers.
It's likely that the phone numbers associated with the infected devices are being used without the owner's knowledge to register for various online accounts by harvesting the OTPs required for two-factor authentication (2FA).

In early 2022, Trend Micro shed light on a similar financially-motivated service that corralled Android devices into a botnet that could be used to "register disposable accounts in bulk or create phone-verified accounts for conducting fraud and other criminal activities."
A Google spokesperson told The Hacker News that Android users are automatically protected against known versions of this malware via Google Play Protect, which is enabled by default on devices that have Google Play Services.
"These stolen credentials serve as a springboard for further fraudulent activities, such as creating fake accounts on popular services to launch phishing campaigns or social engineering attacks," Zimperium said.
The findings highlight the continued abuse of Telegram, a popular instant messaging app with over 950 million monthly active users, by malicious actors for different purposes ranging from malware propagation to C2.
Earlier this month, Positive Technologies disclosed two SMS stealer families dubbed SMS Webpro and NotifySmsStealer that target Android device users in Bangladesh, India, and Indonesia with an aim to siphon messages to a Telegram bot maintained by the threat actors.
Also identified by the Russian cybersecurity company are stealer malware strains that masquerade as TrueCaller and ICICI Bank, and are capable of exfiltrating users' photos, device information, and notifications via the messaging platform.
"The chain of infection starts with a typical phishing attack on WhatsApp," security researcher Varvara Akhapkina said. "With few exceptions, the attacker uses phishing sites posing as a bank to get users to download apps from them."
Another malware that leverages Telegram as a C2 server is TgRAT, a Windows remote access trojan that has recently been updated to include a Linux variant. It's equipped to download files, take screenshots, and run commands remotely.
"Telegram is widely used as a corporate messenger in many companies," Doctor Web said. "Therefore, it is not surprising that threat actors can use it as a vector to deliver malware and steal confidential information: the popularity of the program and the routine traffic to Telegram's servers make it easy to disguise malware on a compromised network."
New Mandrake Spyware Found in Google Play Store Apps After Two Years
31.7.24 Virus The Hacker News
A new iteration of a sophisticated Android spyware called Mandrake has been discovered in five applications that were available for download from the Google Play Store and remained undetected for two years.
The applications attracted a total of more than 32,000 installations before being pulled from the app storefront, Kaspersky said in a Monday write-up. A majority of the downloads originated from Canada, Germany, Italy, Mexico, Spain, Peru, and the U.K.
"The new samples included new layers of obfuscation and evasion techniques, such as moving malicious functionality to obfuscated native libraries, using certificate pinning for C2 communications, and performing a wide array of tests to check if Mandrake was running on a rooted device or in an emulated environment," researchers Tatyana Shishkova and Igor Golovin said.
Mandrake was first documented by Romanian cybersecurity vendor Bitdefender in May 2020, describing its deliberate approach to infect a handful of devices while managing to lurk in the shadows since 2016. The malware has yet to be attributed to a threat actor or group.
Cybersecurity
The updated variants are characterized by the use of OLLVM to conceal the main functionality, while also incorporating an array of sandbox evasion and anti-analysis techniques to prevent the code from being executed in environments operated by malware analysts.
The list of apps containing Mandrake is below -
AirFS (com.airft.ftrnsfr)
Amber (com.shrp.sght)
Astro Explorer (com.astro.dscvr)
Brain Matrix (com.brnmth.mtrx)
CryptoPulsing (com.cryptopulsing.browser)
The apps pack in three stages: A dropper that launches a loader responsible for executing the core component of the malware after downloading and decrypting it from a command-and-control (C2) server.

The second-stage payload is also capable of collecting information about the device's connectivity status, installed applications, battery percentage, external IP address, and current Google Play version. Furthermore, it can wipe the core module and request for permissions to draw overlays and run in the background.
The third-stage supports additional commands to load a specific URL in a WebView and initiate a remote screen sharing session as well as record the device screen with the goal of stealing victims' credentials and dropping more malware.
"Android 13 introduced the 'Restricted Settings' feature, which prohibits sideloaded applications from directly requesting dangerous permissions," the researchers said. "To bypass this feature, Mandrake processes the installation with a 'session-based' package installer."
The Russian security company described Mandrake as an example of a dynamically evolving threat that's constantly refining its tradecraft to bypass defense mechanisms and evade detection.
"This highlights the threat actors' formidable skills, and also that stricter controls for applications before being published in the markets only translate into more sophisticated, harder-to-detect threats sneaking into official app marketplaces," it said.
When reached for comment, Google told The Hacker News that it's continuously shoring up Google Play Protect defenses as new malicious apps are flagged and that it's enhancing its capabilities to include live threat detection to tackle obfuscation and anti-evasion techniques.
"Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services," a Google spokesperson said. "Google Play Protect can warn users or block apps known to exhibit malicious behavior, even when those apps come from sources outside of Play."
Cybercriminals Target Polish Businesses with Agent Tesla and Formbook Malware
31.7.24 Virus The Hacker News
Cybersecurity researchers have detailed widespread phishing campaigns targeting small and medium-sized businesses (SMBs) in Poland during May 2024 that led to the deployment of several malware families like Agent Tesla, Formbook, and Remcos RAT.
Some of the other regions targeted by the campaigns include Italy and Romania, according to cybersecurity firm ESET.
"Attackers used previously compromised email accounts and company servers, not only to spread malicious emails but also to host malware and collect stolen data," ESET researcher Jakub Kaloč said in a report published today.
Cybersecurity
These campaigns, spread across nine waves, are notable for the use of a malware loader called DBatLoader (aka ModiLoader and NatsoLoader) to deliver the final payloads.
This, the Slovakian cybersecurity company said, marks a departure from previous attacks observed in the second half of 2023 that leveraged a cryptors-as-a-service (CaaS) dubbed AceCryptor to propagate Remcos RAT (aka Rescoms).
"During the second half of [2023], Rescoms became the most prevalent malware family packed by AceCryptor," ESET noted in March 2024. "Over half of these attempts happened in Poland, followed by Serbia, Spain, Bulgaria, and Slovakia."
The starting point of the attacks was phishing emails incorporating malware-laced RAR or ISO attachments that, upon opening, activated a multi-step process to download and launch the trojan.

In cases where an ISO file was attached, it would directly lead to the execution of DBatLoader. The RAR archive, on the other hand, contained an obfuscated Windows batch script enclosing a Base64-encoded ModiLoader executable that's disguised as a PEM-encoded certificate revocation list.
A Delphi-based downloader, DBatLoader is primarily designed to download and launch the next stage malware from either Microsoft OneDrive or compromised servers belonging to legitimate companies.
Regardless of what malware is deployed, Agent Tesla, Formbook, and Remcos RAT come with capabilities to siphon sensitive information, allowing the threat actors to "prepare the ground for their next campaigns."
The development comes as Kaspersky revealed that SMBs are being increasingly targeted by cybercriminals owing to their lack of robust cybersecurity measures as well as limited resources and expertise.
"Trojan attacks remain the most common cyberthreat, which indicates that attackers continue to target SMBs and favor malware over unwanted software," the Russian security vendor said last month.
"Trojans are particularly dangerous because they mimic legitimate software, which makes them harder to detect and prevent. Their versatility and ability to bypass traditional security measures make them a prevalent and effective tool for cyber attackers."
'Stargazer Goblin' Creates 3,000 Fake GitHub Accounts for Malware Spread
29.7.24 Virus The Hacker News
A threat actor known as Stargazer Goblin has set up a network of inauthentic GitHub accounts to fuel a Distribution-as-a-Service (DaaS) that propagates a variety of information-stealing malware and netting them $100,000 in illicit profits over the past year.
The network, which comprises over 3,000 accounts on the cloud-based code hosting platform, spans thousands of repositories that are used to share malicious links or malware, per Check Point, which has dubbed it "Stargazers Ghost Network."
Some of the malware families propagated using this method include Atlantida Stealer, Rhadamanthys, RisePro, Lumma Stealer, and RedLine, with the bogus accounts also engaged in starring, forking, watching, and subscribing to malicious repositories to give them a veneer of legitimacy.
The network is believed to have been active since August 2022 in some preliminary form, although an advertisement for the DaaS wasn't spotted in the dark until early July 2023.
"Threat actors now operate a network of 'Ghost' accounts that distribute malware via malicious links on their repositories and encrypted archives as releases," security researcher Antonis Terefos explained in an analysis published last week.
"This network not only distributes malware but also provides various other activities that make these 'Ghost' accounts appear as normal users, lending fake legitimacy to their actions and the associated repositories."
Different categories of GitHub accounts are responsible for distinct aspects of the scheme in an attempt to make their infrastructure more resilient to takedown efforts by GitHub when malicious payloads are flagged on the platform.
Cybersecurity
These include accounts that serve the phishing repository template, accounts providing the image for the phishing template, and accounts that push malware to the repositories in the form of a password-protected archive masquerading as cracked software and game cheats.
Should the third set of accounts be detected and banned by GitHub, Stargazer Goblin moves to update the first account's phishing repository with a new link to a new active malicious release, thereby allowing the operators to move forward with minimal disruption.
Besides liking new releases from multiple repositories and committing changes to the README.md files to modify the download links, there is evidence to suggest that some accounts part of the network have been previously compromised, with the credentials likely obtained via stealer malware.
"Most of the time, we observe that Repository and Stargazer accounts remain unaffected by bans and repository takedowns, whereas Commit and Release accounts are typically banned once their malicious repositories are detected," Terefos said.
"It's common to find Link-Repositories containing links to banned Release-Repositories. When this occurs, the Commit account associated with the Link-Repository updates the malicious link with a new one."
One of the campaigns discovered by Check Point involves the use of a malicious link to a GitHub repository that, in turn, points to a PHP script hosted on a WordPress site, which then delivers an HTML Application (HTA) file to ultimately execute Atlantida Stealer by means of a PowerShell script.
Other malware families propagated via the DaaS are Lumma Stealer, RedLine Stealer, Rhadamanthys, and RisePro. Check Point further noted that the GitHub accounts are part of a larger DaaS solution that operates similar 'Ghost' accounts on other platforms such as Discord, Facebook, Instagram, X, and YouTube.

"Stargazer Goblin created an extremely sophisticated malware distribution operation that avoids detection as GitHub is considered a legitimate website, bypasses suspicions of malicious activities, and minimizes and recovers any damage when GitHub disrupts their network," Terefos said.
"Utilizing multiple accounts and profiles performing different activities from starring to hosting the repository, committing the phishing template, and hosting malicious releases, enables the Stargazers Ghost Network to minimize their losses when GitHub performs any actions to disturb their operations as usually only one part of the whole operation is disrupted instead of all the involved accounts."
The development comes as unknown threat actors are targeting GitHub repositories, wiping their contents, and asking the victims to reach out to a user named Gitloker on Telegram as part of a new extortion operation that has been ongoing since February 2024.
The social engineering attack targets developers with phishing emails sent from "notifications@github.com," aiming to trick them into clicking on bogus links under the guise of a job opportunity at GitHub, following which they are prompted to authorize a new OAuth app that erases all the repositories and demands a payment in exchange for restoring access.
It also follows an advisory from Truffle Security that it's possible to access sensitive data from deleted forks, deleted repositories, and even private repositories on GitHub, urging organizations to take steps to secure against what it's calling a Cross Fork Object Reference (CFOR) vulnerability.
"A CFOR vulnerability occurs when one repository fork can access sensitive data from another fork (including data from private and deleted forks)," Joe Leon said. "Similar to an Insecure Direct Object Reference, in CFOR users supply commit hashes to directly access commit data that otherwise would not be visible to them."
In other words, a piece of code committed to a public repository may be accessible forever as long as there exists at least one fork of that repository. On top of that, it could also be used to access code committed between the time an internal fork is created and the repository is made public.
It's however worth noting that these are intentional design decisions taken by GitHub, as noted by the company in its own documentation -
Commits to any repository in a fork network can be accessed from any repository in the same fork network, including the upstream repository
When you change a private repository to public, all the commits in that repository, including any commits made in the repositories it was forked into, will be visible to everyone.
"The average user views the separation of private and public repositories as a security boundary, and understandably believes that any data located in a private repository cannot be accessed by public users," Leon said.
"Unfortunately, [...] that is not always true. What's more, the act of deletion implies the destruction of data. As we saw above, deleting a repository or fork does not mean your commit data is actually deleted."
Gh0st RAT Trojan Targets Chinese Windows Users via Fake Chrome Site
29.7.24 Virus The Hacker News

The remote access trojan known as Gh0st RAT has been observed being delivered by an "evasive dropper" called Gh0stGambit as part of a drive-by download scheme targeting Chinese-speaking Windows users.
These infections stem from a fake website ("chrome-web[.]com") serving malicious installer packages masquerading as Google's Chrome browser, indicating that users searching for the software on the web are being singled out.
Gh0st RAT is a long-standing malware that has been observed in the wild since 2008, manifesting in the form of different variants over the years in campaigns primarily orchestrated by China-nexus cyberespionage groups.
Some iterations of the trojan have also been previously deployed by infiltrating poorly-secured MS SQL server instances, using it as a conduit to install the Hidden open-source rootkit.
Cybersecurity
According to cybersecurity firm eSentire, which discovered the latest activity, the targeting of Chinese-speaking users is based on "the use of Chinese-language web lures and Chinese applications targeted for data theft and defense evasion by the malware."
The MSI installer downloaded from the phony website contains two files, a legitimate Chrome setup executable and a malicious installer ("WindowsProgram.msi"), the latter of which is used to launch shellcode that's responsible for loading Gh0stGambit.
The dropper, in turn, checks for the presence of security software (e.g., 360 Safe Guard and Microsoft Defender Antivirus) before establishing contact with a command-and-control (C2) server in order to retrieve Gh0st RAT.
"Gh0st RAT is written in C++ and has many features, including terminating processes, removing files, capturing audio and screenshots, remote command execution, keylogging, data exfiltration, hiding registry, files, and directories via the rootkit capabilities, and many more," eSentire said.
It's also capable of dropping Mimikatz, enabling RDP on the compromised hosts, accessing account identifiers associated with Tencent QQ, clearing Windows event logs, and erasing data from 360 Secure Browser, QQ Browser, and Sogou Explorer.
The Canadian company said the artifact shares overlaps with a Gh0st RAT variant tracked by the AhnLab Security Intelligence Center (ASEC) under the moniker HiddenGh0st.
"Gh0st RAT has seen widespread use and modification by APT and criminal groups over the past several years," eSentire said. "The recent findings highlight the distribution of this threat via drive-by downloads, deceiving users into downloading a malicious Chrome installer from a deceptive website."
"The continued success of drive-by downloads reinforces the need for ongoing security training and awareness programs."
The development comes as Broadcom-owned Symantec said it observed an increase in phishing campaigns likely leveraging Large Language Models (LLMs) to generate malicious PowerShell and HTML code used to download several loaders and stealers.
The emails contained "code used to download various payloads, including Rhadamanthys, NetSupport RAT, CleanUpLoader (Broomstick, Oyster), ModiLoader (DBatLoader), LokiBot, and Dunihi (H-Worm)," security researchers Nguyen Hoang Giang and Yi Helen Zhang said. "Analysis of the scripts used to deliver malware in these attacks suggests they were generated using LLMs."
Malicious PyPI Package Targets macOS to Steal Google Cloud Credentials
27.7.24 Virus The Hacker News

Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) repository that targets Apple macOS systems with the goal of stealing users' Google Cloud credentials from a narrow pool of victims.
The package, named "lr-utils-lib," attracted a total of 59 downloads before it was taken down. It was uploaded to the registry in early June 2024.
"The malware uses a list of predefined hashes to target specific macOS machines and attempts to harvest Google Cloud authentication data," Checkmarx researcher Yehuda Gelb said in a Friday report. "The harvested credentials are sent to a remote server."
An important aspect of the package is that it first checks if it has been installed on a macOS system, and only then proceeds to compare the system's Universally Unique Identifier (UUID) against a hard-coded list of 64 hashes.
If the compromised machine is among those specified in the predefined set, it attempts to access two files, namely application_default_credentials.json and credentials.db, located in the ~/.config/gcloud directory, which contain Google Cloud authentication data.

The captured information is then transmitted over HTTP to a remote server "europe-west2-workload-422915[.]cloudfunctions[.]net."
Checkmarx said it also found a fake profile on LinkedIn with the name "Lucid Zenith" that matched the package's owner and falsely claimed to be the CEO of Apex Companies, suggesting a possible social engineering element to the attack.
Exactly who is behind the campaign is currently not known. However, it comes more than two months after cybersecurity firm Phylum disclosed details of another supply chain attack involving a Python package called "requests-darwin-lite" that was also found to unleash its malicious actions after checking the UUID of the macOS host.
These campaigns are a sign that threat actors have prior knowledge of the macOS systems they want to infiltrate and are going to great lengths to ensure that the malicious packages are distributed only to those particular machines.
It also speaks to the tactics malicious actors employ to distribute lookalike packages, aiming to deceive developers into incorporating them into their applications.
"While it is not clear whether this attack targeted individuals or enterprises, these kinds of attacks can significantly impact enterprises," Gelb said. "While the initial compromise usually occurs on an individual developer's machine, the implications for enterprises can be substantial."
New Chrome Feature Scans Password-Protected Files for Malicious Content
26.7.24 Virus The Hacker News

Google said it's adding new security warnings when downloading potentially suspicious and malicious files via its Chrome web browser.
"We have replaced our previous warning messages with more detailed ones that convey more nuance about the nature of the danger and can help users make more informed decisions," Jasika Bawa, Lily Chen, and Daniel Rubery from the Chrome Security team said.
To that end, the search giant is introducing a two-tier download warning taxonomy based on verdicts provided by Google Safe Browsing: Suspicious files and Dangerous files.
Each category comes with its own iconography, color, and text to distinguish them from one another and help users make an informed choice.
Google is also adding what's called automatic deep scans for users who have opted-in to the Enhanced Protection mode of Safe Browsing in Chrome so that they don't have to be prompted each time to send the files to Safe Browsing for deep scanning before opening them.
In cases where such files are embedded within password-protected archives, users now have the option to "enter the file's password and send it along with the file to Safe Browsing so that the file can be opened and a deep scan may be performed."
Google emphasized that the files and their associated passwords are deleted a short time after the scan and that the collected data is only used for improving download protections.
"In Standard Protection mode, downloading a suspicious encrypted archive will also trigger a prompt to enter the file's password, but in this case, both the file and the password stay on the local device and only the metadata of the archive contents are checked with Safe Browsing," it said.
Chinese Hackers Target Taiwan and US NGO with MgBot Malware
24.7.24 Virus The Hacker News
Organizations in Taiwan and a U.S. non-governmental organization (NGO) based in China have been targeted by a Beijing-affiliated state-sponsored hacking group called Daggerfly using an upgraded set of malware tools.
The campaign is a sign that the group "also engages in internal espionage," Symantec's Threat Hunter Team, part of Broadcom, said in a new report published today. "In the attack on this organization, the attackers exploited a vulnerability in an Apache HTTP server to deliver their MgBot malware."
Daggerfly, also known by the names Bronze Highland and Evasive Panda, was previously observed using the MgBot modular malware framework in connection with an intelligence-gathering mission aimed at telecom service providers in Africa. It's known to be operational since 2012.
"Daggerfly appears to be capable of responding to exposure by quickly updating its toolset to continue its espionage activities with minimal disruption," the company noted.
The latest set of attacks are characterized by the use of a new malware family based on MgBot as well as an improved version of a known Apple macOS malware called MACMA, which was first exposed by Google's Threat Analysis Group (TAG) in November 2021 as distributed via watering hole attacks targeting internet users in Hong Kong by abusing security flaws in the Safari browser.
The development marks the first time the malware strain, which is capable of harvesting sensitive information and executing arbitrary commands, has been explicitly linked to a particular hacking group.
"The actors behind macOS.MACMA at least were reusing code from ELF/Android developers and possibly could have also been targeting Android phones with malware as well," SentinelOne noted in a subsequent analysis at the time.
MACMA's connections to Daggerly also stem from source code overlaps between the malware and Mgbot, and the fact that it connects to a command-and-control (C2) server (103.243.212[.]98) that has also been used by a MgBot dropper.
Another new malware in its arsenal is Nightdoor (aka NetMM and Suzafk), an implant that uses Google Drive API for C2 and has been utilized in watering hole attacks aimed at Tibetan users since at least September 2023. Details of the activity were first documented by ESET earlier this March.
"The group can create versions of its tools targeting most major operating system platform," Symantec said, adding it has "seen evidence of the ability to trojanize Android APKs, SMS interception tools, DNS request interception tools, and even malware families targeting Solaris OS."
The development comes as China's National Computer Virus Emergency Response Center (CVERC) claimed Volt Typhoon – which has been attributed by the Five Eyes nations as a China-nexus espionage group – to be an invention of the U.S. intelligence agencies, describing it as a misinformation campaign.
"Although its main targets are U.S. congress and American people, it also attempt[s] to defame China, sow discords [sic] between China and other countries, contain China's development, and rob Chinese companies," the CVERC asserted in a recent report.
PINEAPPLE and FLUXROOT Hacker Groups Abuse Google Cloud for Credential Phishing
23.7.24 Virus The Hacker News
A Latin America (LATAM)-based financially motivated actor codenamed FLUXROOT has been observed leveraging Google Cloud serverless projects to orchestrate credential phishing activity, highlighting the abuse of the cloud computing model for malicious purposes.
"Serverless architectures are attractive to developers and enterprises for their flexibility, cost effectiveness, and ease of use," Google said in its biannual Threat Horizons Report [PDF] shared with The Hacker News.
"These same features make serverless computing services for all cloud providers attractive to threat actors, who use them to deliver and communicate with their malware, host and direct users to phishing pages, and to run malware and execute malicious scripts specifically tailored to run in a serverless environment."
The campaign involved the use of Google Cloud container URLs to host credential phishing pages with the aim of harvesting login information associated with Mercado Pago, an online payments platform popular in the LATAM region.
FLUXROOT, per Google, is the threat actor known for distributing the Grandoreiro banking trojan, with recent campaigns also taking advantage of legitimate cloud services like Microsoft Azure and Dropbox to distribute the malware.
Separately, Google's cloud infrastructure has also been weaponized by another adversary named PINEAPPLE to propagate another stealer malware known as Astaroth (aka Guildma) as part of attacks targeting Brazilian users.
"PINEAPPLE used compromised Google Cloud instances and Google Cloud projects they created themselves to create container URLs on legitimate Google Cloud serverless domains such as cloudfunctions[.]net and run.app," Google noted. "The URLs hosted landing pages redirecting targets to malicious infrastructure that dropped Astaroth."
Furthermore, the threat actor is said to have attempted to bypass email gateway protections by making use of mail forwarding services that do not drop messages with failed Sender Policy Framework (SPF) records, or incorporating unexpected data in the SMTP Return-Path field in order to trigger a DNS request timeout and cause email authentication checks to fail.
The search giant said it took steps to mitigate the activities by taking down the malicious Google Cloud projects and updating its Safe Browsing lists.
The weaponization of cloud services and infrastructure by threat actors – ranging from illicit cryptocurrency mining as a consequence of weak configurations to ransomware – has been fueled by the enhanced adoption of cloud across industries.
Furthermore, the approach has the added benefit of allowing adversaries to blend into normal network activities, making detection a lot more challenging.
"Threat actors take advantage of the flexibility and ease of deployment of serverless platforms to distribute malware and host phishing pages," the company said. "Threat actors abusing cloud services shift their tactics in response to defenders' detection and mitigation measures."
SocGholish Malware Exploits BOINC Project for Covert Cyberattacks
23.7.24 Virus The Hacker News

The JavaScript downloader malware known as SocGholish (aka FakeUpdates) is being used to deliver a remote access trojan called AsyncRAT as well as a legitimate open-source project called BOINC.
BOINC, short for Berkeley Open Infrastructure Network Computing Client, is an open-source "volunteer computing" platform maintained by the University of California with an aim to carry out "large-scale distributed high-throughput computing" using participating home computers on which the app is installed.
"It's similar to a cryptocurrency miner in that way (using computer resources to do work), and it's actually designed to reward users with a specific type of cryptocurrency called Gridcoin, designed for this purpose," Huntress researchers Matt Anderson, Alden Schmidt, and Greg Linares said in a report published last week.
These malicious installations are designed to connect to an actor-controlled domain ("rosettahome[.]cn" or "rosettahome[.]top"), essentially acting as a command-and-control (C2) server to collect host data, transmit payloads, and push further commands. As of July 15, 10,032 clients are connected to the two domains.
The cybersecurity firm said while it hasn't observed any follow-on activity or tasks being executed by the infected hosts, it hypothesized that the "host connections could be sold off as initial access vectors to be used by other actors and potentially used to execute ransomware."
SocGholish attack sequences typically begin when users land on compromised websites, where they are prompted to download a fake browser update that, upon execution, triggers the retrieval of additional payloads to the infiltrated machines.
The JavaScript downloader, in this case, activates two disjointed chains, one that leads to the deployment of a fileless variant of AsyncRAT and the other resulting in the BOINC installation.

The BOINC app, which is renamed as "SecurityHealthService.exe" or "trustedinstaller.exe" to evade detection, sets up persistence using a scheduled task by means of a PowerShell script.
The misuse of BOINC for malicious purposes hasn't gone unnoticed by the project maintainers, who are currently investigating the problem and finding a way to "defeat this malware." Evidence of the abuse dates back to at least June 26, 2024.
"The motivation and intent of the threat actor by loading this software onto infected hosts isn't clear at this point," the researchers said.
"Infected clients actively connecting to malicious BOINC servers present a fairly high risk, as there's potential for a motivated threat actor to misuse this connection and execute any number of malicious commands or software on the host to further escalate privileges or move laterally through a network and compromise an entire domain."
The development comes as Check Point said it's been tracking the use of compiled V8 JavaScript by malware authors to sidestep static detections and conceal remote access trojans, stealers, loaders, cryptocurrency miners, wipers, and ransomware.
"In the ongoing battle between security experts and threat actors, malware developers keep coming up with new tricks to hide their attacks," security researcher Moshe Marelus said. "It's not surprising that they've started using V8, as this technology is commonly used to create software as it is very widespread and extremely hard to analyze."
Cybercriminals Exploit CrowdStrike Update Mishap to Distribute Remcos RAT Malware
21.7.24 Virus The Hacker News
Cybersecurity firm CrowdStrike, which is facing the heat for causing worldwide IT disruptions by pushing out a flawed update to Windows devices, is now warning that threat actors are exploiting the situation to distribute Remcos RAT to its customers in Latin America under the guise of a providing a hotfix.
The attack chains involve distributing a ZIP archive file named "crowdstrike-hotfix.zip," which contains a malware loader named Hijack Loader (aka DOILoader or IDAT Loader) that, in turn, launches the Remcos RAT payload.
Specifically, the archive file also includes a text file ("instrucciones.txt") with Spanish-language instructions that urges targets to run an executable file ("setup.exe") to recover from the issue.
"Notably, Spanish filenames and instructions within the ZIP archive indicate this campaign is likely targeting Latin America-based (LATAM) CrowdStrike customers," the company said, attributing the campaign to a suspected e-crime group.
On Friday, CrowdStrike acknowledged that a routine sensor configuration update pushed to its Falcon platform for Windows devices on July 19 at 04:09 UTC inadvertently triggered a logic error that resulted in a Blue Screen of Death (BSoD), rendering numerous systems inoperable and sending businesses into a tailspin.
The event impacted customers running Falcon sensor for Windows version 7.11 and above, who were online between 04:09 and 05:27 a.m. UTC.
Malicious actors have wasted no time capitalizing on the chaos created by the event to set up typosquatting domains impersonating CrowdStrike and advertise services to companies affected by the issue in return for a cryptocurrency payment.
Customers who are impacted are recommended to "ensure they are communicating with CrowdStrike representatives through official channels and adhere to technical guidance the CrowdStrike support teams have provided."
Pro-Houthi Group Targets Yemen Aid Organizations with Android Spyware
19.7.24 Virus The Hacker News
A suspected pro-Houthi threat group targeted at least three humanitarian organizations in Yemen with Android spyware designed to harvest sensitive information.
These attacks, attributed to an activity cluster codenamed OilAlpha, entail a new set of malicious mobile apps that come with their own supporting infrastructure, Recorded Future's Insikt Group said.
Targets of the ongoing campaign include, CARE International, the Norwegian Refugee Council (NRC), and the Saudi Arabian King Salman Humanitarian Aid and Relief Centre.
"The OilAlpha threat group is highly likely active and executing targeted activity against humanitarian and human rights organizations operating in Yemen, and potentially throughout the Middle East," the cybersecurity company said.
OilAlpha was first documented in May 2023 in connection with an espionage campaign targeting development, humanitarian, media, and non-governmental organizations in the Arabian peninsula.
These attacks leveraged WhatsApp to distribute malicious Android APK files by passing them off as associated with legitimate organizations like UNICEF, ultimately leading to the deployment of a malware strain named SpyNote (aka SpyMax).

The latest wave, identified in early June 2024, comprises apps that claim to be related to humanitarian relief programs and masquerade as entities like CARE International and the NRC, both of which have an active presence in Yemen.
Once installed, these apps – which harbor the SpyMax trojan – request intrusive permissions, thereby facilitating the theft of victim data.
OilAlpha's operations also include a credential harvesting component that utilizes a bunch of fake login pages impersonating these organizations in an effort to harvest users' login information. It's suspected that the goal is to carry out espionage efforts by accessing accounts associated with the affected organizations.
"Houthi militants have continually sought to restrict the movement and delivery of international humanitarian assistance and have profited from taxing and re-selling aid materials," Recorded Future said.
"One possible explanation for the observed cyber targeting is that it is intelligence-gathering to facilitate efforts to control who gets aid and how it is delivered."
The development arrives weeks after Lookout implicated a Houthi-aligned threat actor to another surveillanceware operation that delivers an Android data-gathering tool called GuardZoo to targets in Yemen and other countries in the Middle East.
'Konfety' Ad Fraud Uses 250+ Google Play Decoy Apps to Hide Malicious Twins
16.7.24 Virus The Hacker News
Details have emerged about a "massive ad fraud operation" that leverages hundreds of apps on the Google Play Store to perform a host of nefarious activities.
The campaign has been codenamed Konfety – the Russian word for Candy – owing to its abuse of a mobile advertising software development kit (SDK) associated with a Russia-based ad network called CaramelAds.
"Konfety represents a new form of fraud and obfuscation, in which threat actors operate 'evil twin' versions of 'decoy twin' apps available on major marketplaces," HUMAN's Satori Threat Intelligence Team said in a technical report shared with The Hacker News.
While the decoy apps, totaling more than 250 in number, are harmless and distributed via the Google Play Store, their respective "evil twins" are disseminated through a malvertising campaign designed to facilitate ad fraud, monitor web searches, install browser extensions, and sideload APK files code onto users' devices.
The most unusual aspect of the campaign is that the evil twin masquerades as the decoy twin by spoofing the latter's app ID and advertising publisher IDs for rendering ads. Both the decoy and evil twin sets of apps operate on the same infrastructure, allowing the threat actors to exponentially scale their operations as required.
That having said, not only do the decoy apps behave normally, a majority of them do not even render ads. They also incorporate a GDPR consent notice.
"This 'decoy/evil twin' mechanism for obfuscation is a novel way for threat actors to represent fraudulent traffic as legitimate," HUMAN researchers said. "At its peak, Konfety-related programmatic volume reached 10 billion requests per day."
Put differently, Konfety takes advantage of the SDK's ad rendering capabilities to commit ad fraud by making it a lot more challenging to distinguish malicious traffic from legitimate traffic.
The Konfety evil twin apps are said to be propagated via a malvertising campaign promoting APK mods and other software like Letasoft Sound Booster, with the booby-trapped URLs hosted on attacker-controlled domains, compromised WordPress sites, and other platforms that allow content uploads, including Docker Hub, Facebook, Google Sites, and OpenSea.

Users who end up clicking on these URLs are redirected to a domain that tricks them into downloading the malicious evil twin app, which, in turn, acts as a dropper for a first-stage that's decrypted from the assets of the APK file and is used to set up command-and-control (C2) communications.
The initial stager further attempts to hide the app's icon from the device's home screen and runs a second-stage DEX payload that performs fraud by serving out-of-context, full-screen video ads when the user is either on their home screen or using another app.
"The crux of the Konfety operation lies in the evil twin apps," the researchers said. "These apps mimic their corresponding decoy twin apps by copying their app ID/package names and publisher IDs from the decoy twin apps."
"The network traffic derived from the evil twin applications is functionally identical to network traffic derived from the decoy twin applications; the ad impressions rendered by the evil twins use the package name of the decoy twins in the request."
Other capabilities of the malware include weaponizing the CaramelAds SDK to visit websites using the default web browser, luring users by sending notifications that prompt them into clicking on the bogus links, or sideloading modified versions of other advertising SDKs.
That's not all. Users installing the Evil Twins apps are urged to add a search toolbar widget to the device home screen, which surreptitiously monitors their searches by sending the data to domains named vptrackme[.]com and youaresearching[.]com.
"Threat actors understand that hosting malicious apps on stores is not a stable technique, and are finding creative and clever ways to evade detection and commit sustainable long term fraud," the researchers concluded. "Actors setting up mediation SDK companies and spreading the SDK to abuse high-quality publishers is a growing technique."
Malicious npm Packages Found Using Image Files to Hide Backdoor Code
16.7.24 Virus The Hacker News
Cybersecurity researchers have identified two malicious packages on the npm package registry that concealed backdoor code to execute malicious commands sent from a remote server.
The packages in question – img-aws-s3-object-multipart-copy and legacyaws-s3-object-multipart-copy – have been downloaded 190 and 48 times each. As of writing, they have been taken down by the npm security team.
"They contained sophisticated command and control functionality hidden in image files that would be executed during package installation," software supply chain security firm Phylum said in an analysis.
The packages are designed to impersonate a legitimate npm library called aws-s3-object-multipart-copy, but come with an altered version of the "index.js" file to execute a JavaScript file ("loadformat.js").
For its part, the JavaScript file is designed to process three images -- that feature the corporate logos for Intel, Microsoft, and AMD -- with the image corresponding to Microsoft's logo used to extract and execute the malicious content.
The code works by registering the new client with a command-and-control (C2) server by sending the hostname and operating system details. It then attempts to execute attacker-issued commands periodically every five seconds.
In the final stage, the output of the commands' execution is exfiltrated back to the attacker via a specific endpoint.
"In the last few years, we've seen a dramatic rise in the sophistication and volume of malicious packages published to open source ecosystems," Phylum said.
"Make no mistake, these attacks are successful. It is absolutely imperative that developers and security organizations alike are keenly aware of this fact and are deeply vigilant with regard to open source libraries they consume."
DarkGate Malware Exploits Samba File Shares in Short-Lived Campaign
13.7.24 Virus The Hacker News
Cybersecurity researchers have shed light on a short-lived DarkGate malware campaign that leveraged Samba file shares to initiate the infections.
Palo Alto Networks Unit 42 said the activity spanned the months of March and April 2024, with the infection chains using servers running public-facing Samba file shares hosting Visual Basic Script (VBS) and JavaScript files. Targets included North America, Europe, and parts of Asia.
"This was a relatively short-lived campaign that illustrates how threat actors can creatively abuse legitimate tools and services to distribute their malware," security researchers Vishwa Thothathri, Yijie Sui, Anmol Maurya, Uday Pratap Singh, and Brad Duncan said.
DarkGate, which first emerged in 2018, has evolved into a malware-as-a-service (MaaS) offering used by a tightly controlled number of customers. It comes with capabilities to remotely control compromised hosts, execute code, mine cryptocurrency, launch reverse shells, and drop additional payloads.
Attacks involving the malware have particularly witnessed a surge in recent months in the aftermath of the multinational law enforcement takedown of the QakBot infrastructure in August 2023.

The campaign documented by Unit 42 commences with Microsoft Excel (.xlsx) files that, when opened, urge targets to click on an embedded Open button, which, in turn, fetches and runs VBS code hosted on a Samba file share.
The PowerShell script is configured to retrieve and execute a PowerShell script, which is then used to download an AutoHotKey-based DarkGate package.
Alternate sequences using JavaScript files instead of VBS are no different in that they are also engineered to download and run the follow-up PowerShell script.
DarkGate works by scanning for various anti-malware programs and checking the CPU information to determine if it's running on a physical host or a virtual environment, thereby allowing it to hinder analysis. It also examines the host's running processes to determine the presence of reverse engineering tools, debuggers, or virtualization software.
"DarkGate C2 traffic uses unencrypted HTTP requests, but the data is obfuscated and appears as Base64-encoded text," the researchers said.
"As DarkGate continues to evolve and refine its methods of infiltration and resistance to analysis, it remains a potent reminder of the need for robust and proactive cybersecurity defenses."
60 New Malicious Packages Uncovered in NuGet Supply Chain Attack
12.7.24 Virus The Hacker News
Threat actors have been observed publishing a new wave of malicious packages to the NuGet package manager as part of an ongoing campaign that began in August 2023, while also adding a new layer of stealth to evade detection.
The fresh packages, about 60 in number and spanning 290 versions, demonstrate a refined approach from the previous set that came to light in October 2023, software supply chain security firm ReversingLabs said.
The attackers pivoted from using NuGet's MSBuild integrations to "a strategy that uses simple, obfuscated downloaders that are inserted into legitimate PE binary files using Intermediary Language (IL) Weaving, a .NET programming technique for modifying an application's code after compilation," security researcher Karlo Zanki said.
The end goal of the counterfeit packages, both old and new, is to deliver an off-the-shelf remote access trojan called SeroXen RAT. All the identified packages have since been taken down.

The latest collection of packages is characterized by the use of a novel technique called IL weaving that makes it possible to inject malicious functionality to a Portable Executable (PE) .NET binary associated with a legitimate NuGet package.
This includes taking popular open-source packages like Guna.UI2.WinForms and patching it with the aforementioned method to create an imposter package that's named "Gսոa.UI3.Wіnfօrms," which uses homoglyphs to substitute the letters "u," "n," "i," and "o" with their equivalents "ս" (\u057D), "ո" (\u0578), "і" (\u0456). and "օ" (\u0585).
"Threat actors are constantly evolving the methods and tactics they use to compromise and infect their victims with malicious code that is used to extract sensitive data or provide attackers with control over IT assets," Zanki said.
"This latest campaign highlights new ways in which malicious actors are scheming to fool developers as well as security teams into downloading and using malicious or tampered with packages from popular open source package managers like NuGet."
New Poco RAT Targets Spanish-Speaking Victims in Phishing Campaign
11.7.24 Virus The Hacker News
Spanish language victims are the target of an email phishing campaign that delivers a new remote access trojan (RAT) called Poco RAT since at least February 2024.
The attacks primarily single out mining, manufacturing, hospitality, and utilities sectors, according to cybersecurity company Cofense.
"The majority of the custom code in the malware appears to be focused on anti-analysis, communicating with its command-and-control center (C2), and downloading and running files with a limited focus on monitoring or harvesting credentials," it said.
Infection chains begin with phishing messages bearing finance-themed lures that trick recipients into clicking on an embedded URL pointing to a 7-Zip archive file hosted on Google Drive.
Other methods observed include the use of HTML or PDF files directly attached to the emails or downloaded via another embedded Google Drive link. The abuse of legitimate services by threat actors is not a new phenomenon as it allows them to bypass secure email gateways (SEGs).
The HTML files propagating Poco RAT, in turn, contain a link that, upon clicking, leads to the download of the archive containing the malware executable.
"This tactic would likely be more effective than simply providing a URL to directly download the malware as any SEGs that would explore the embedded URL would only download and check the HTML file, which would appear to be legitimate," Cofense noted.
The PDF files are no different in that they also contain a Google Drive link that harbors Poco RAT.
Once launched, the Delphi-based malware establishes persistence on the compromised Windows host and contacts a C2 server in order to deliver additional payloads. It's so named owing to its use of the POCO C++ Libraries.
The use of Delphi is a sign that the unidentified threat actors behind the campaign are focusing on Latin America, which is known to be targeted by banking trojans written in the programming language.
This connection is strengthened by the fact that the C2 server does not respond to requests originating from infected computers that are not geolocated to the region.
The development comes as malware authors are increasingly using QR codes embedded with PDF files to trick users into visiting phishing pages that are designed to harvest Microsoft 365 login credentials.
It also follows social engineering campaigns that use deceptive sites advertising popular software to deliver malware such as RATs and information stealers like AsyncRAT and RisePro.
Similar data theft attacks have also targeted internet users in India with bogus SMS messages falsely claiming of package delivery failures and instructing them to click on a provided link to update their details.
The SMS phishing campaign has been attributed to a Chinese-speaking threat actor called Smishing Triad, which has a history of using compromised or purposefully registered Apple iCloud accounts (e.g., "fredyma514@hlh-web.de") to send smishing messages for carrying out financial fraud.
"The actors registered domain names impersonating the India Post around June, but were not actively using them, likely preparing for a large-scale activity, which became visible by July," Resecurity said. "The goal of this campaign is to steal massive amounts of personal identifiable information (PII) and payment data."
ViperSoftX Malware Disguises as eBooks on Torrents to Spread Stealthy Attacks
10.7.24 Virus The Hacker News

The sophisticated malware known as ViperSoftX has been observed being distributed as eBooks over torrents.
"A notable aspect of the current variant of ViperSoftX is that it uses the Common Language Runtime (CLR) to dynamically load and run PowerShell commands, thereby creating a PowerShell environment within AutoIt for operations," Trellix security researchers Mathanraj Thangaraju and Sijo Jacob said.
"By utilizing CLR, ViperSoftX can seamlessly integrate PowerShell functionality, allowing it to execute malicious functions while evading detection mechanisms that might otherwise flag standalone PowerShell activity."
Initially detected by Fortinet in 2020, ViperSoftX is known for its ability to exfiltrate sensitive information from compromised Windows hosts. Over the years, the malware has become a relevant example of threat actors continuously innovating their tactics in an attempt to stay stealthy and circumvent defenses.
This is exemplified by the increased complexity and the adoption of advanced anti-analysis techniques such as byte remapping and web browser communication blocking, as documented by Trend Micro in April 2023.
As recently as May 2024, malicious campaigns have leveraged ViperSoftX as a delivery vehicle to distribute Quasar RAT and another information stealer named TesseractStealer.
Attack chains propagating the malware are known to employ cracked software and torrent sites, but the use of eBook lures is a newly observed approach. Present within the supposed eBook RAR archive file is a hidden folder as well as a deceptive Windows shortcut file that purports to be a benign document.
Executing the shortcut file initiates a multi-stage infection sequence that begins with the extraction of PowerShell code that unhides the concealed folder and sets up persistence on the system to launch an AutoIt script that, in turn, interacts with the .NET CLR framework, to decrypt and run a secondary PowerShell script, which is ViperSoftX.
"AutoIt does not by default support the .NET Common Language Runtime (CLR)," the researchers said. "However, the language's user-defined functions (UDF) offer a gateway to the CLR library, granting malevolent actors access to PowerShell's formidable capabilities."
ViperSoftX harvests system information, scans for cryptocurrency wallets via browser extensions, captures clipboard contents, and dynamically downloads and runs additional payloads and commands based on responses received from a remote server. It also comes with self-deletion mechanisms to challenge detection.
"One of the hallmark features of ViperSoftX is its adept use of the Common Language Runtime (CLR) to orchestrate PowerShell operations within the AutoIt environment," the researchers said. "This integration enables seamless execution of malicious functions while evading detection mechanisms that would typically flag standalone PowerShell activity."
"Furthermore, ViperSoftX's ability to patch the Antimalware Scan Interface (AMSI) before executing PowerShell scripts underscores its determination to circumvent traditional security measures."
GuardZoo Malware Targets Over 450 Middle Eastern Military Personnel
9.7.24 Virus The Hacker News
Military personnel from Middle East countries are the target of an ongoing surveillanceware operation that delivers an Android data-gathering tool called GuardZoo.
The campaign, believed to have commenced as early as October 2019, has been attributed to a Houthi-aligned threat actor based on the application lures, command-and-control (C2) server logs, targeting footprint, and the attack infrastructure location, according to Lookout.
More than 450 victims have been impacted by the malicious activity, with targets located in Egypt, Oman, Qatar, Saudi Arabia, Turkey, the U.A.E., and Yemen. Telemetry data indicates that most of the infections have been recorded in Yemen.
GuardZoo is a modified version of an Android remote access trojan (RAT) named Dendroid RAT that was first discovered by Broadcom-owned Symantec in March 2014. The entire source code associated with the crimeware solution was leaked later that August.

Originally marketed as a commodity malware for a one-off price of $300, it comes with capabilities to call a phone number, delete call logs, open web pages, record audio and calls, access SMS messages, take and upload photos and videos, and even initiate an HTTP flood attack.
"However, many changes were made to the code base in order to add new functionalities and remove unused functions," Lookout researchers Alemdar Islamoglu and Kyle Schmittle said in a report shared with The Hacker News. "GuardZoo doesn't use the leaked PHP web panel from Dendroid RAT for Command and Control (C2) but instead uses a new C2 backend created with ASP.NET."
Attack chains distributing GuardZoo leverage WhatsApp and WhatsApp Business as distribution vectors, with the initial infections also taking place via direct browser downloads. The booby-trapped Android apps bear military and religious themes to entice users into downloading them.
The updated version of the malware supports more than 60 commands that allow it to fetch additional payloads, download files and APKs, upload files (PDF, DOC, DOCX, XLX, XLSX, and PPT), and images, change C2 address, and terminate, update, or delete itself from the compromised device.
"GuardZoo has been using the same dynamic DNS domains for C2 operations since October 2019," the researchers said. "These domains resolve to IP addresses registered to YemenNet and they change regularly."
Trojanized jQuery Packages Found on npm, GitHub, and jsDelivr Code Repositories
9.7.24 Virus The Hacker News
Unknown threat actors have been found propagating trojanized versions of jQuery on npm, GitHub, and jsDelivr in what appears to be an instance of a "complex and persistent" supply chain attack.
"This attack stands out due to the high variability across packages," Phylum said in an analysis published last week.
"The attacker has cleverly hidden the malware in the seldom-used 'end' function of jQuery, which is internally called by the more popular 'fadeTo' function from its animation utilities."
As many as 68 packages have been linked to the campaign. They were published to the npm registry starting from May 26 to June 23, 2024, using names such as cdnjquery, footersicons, jquertyi, jqueryxxx, logoo, and sytlesheets, among others.
There is evidence to suggest that each of the bogus packages were manually assembled and published due to the sheer number of packages published from various accounts, the differences in naming conventions, the inclusion of personal files, and the long time period over which they were uploaded.
This is unlike other commonly observed methods in which attackers tend to follow a predefined pattern that underscores an element of automation involved in creating and publishing the packages.
The malicious changes, per Phylum, have been introduced in a function named "end," allowing the threat actor to exfiltrate website form data to a remote URL.
Further investigation has found the trojanized jQuery file to be hosted on a GitHub repository associated with an account called "indexsc." Also present in the same repository are JavaScript files containing a script pointing to the modified version of the library.
"It's worth noting that jsDelivr constructs these GitHub URLs automatically without needing to upload anything to the CDN explicitly," Phylum said.
"This is likely an attempt by the attacker to make the source look more legitimate or to sneak through firewalls by using jsDelivr instead of loading the code directly from GitHub itself."
The development comes as Datadog identified a series of packages on the Python Package Index (PyPI) repository with capabilities to download a second-stage binary from an attacker-controlled server depending on the CPU architecture.
Dark Web Malware Logs Expose 3,300 Users Linked to Child Abuse Sites
8.7.24 Virus The Hacker News

An analysis of information-stealing malware logs published on the dark web has led to the discovery of thousands of consumers of child sexual abuse material (CSAM), indicating how such information could be used to combat serious crimes.
"Approximately 3,300 unique users were found with accounts on known CSAM sources," Recorded Future said in a proof-of-concept (PoC) report published last week. "A notable 4.2% had credentials for multiple sources, suggesting a higher likelihood of criminal behavior."
Over the past few years, off-the-shelf info-stealer variants have become a pervasive and ubiquitous threat targeting various operating systems with an aim to siphon sensitive information such as credentials, cryptocurrency wallets, payment card data, and screenshots.
This is evidenced in the rise of new stealer malware strains such as Kematian Stealer, Neptune Stealer, 0bj3ctivity, Poseidon (formerly RodStealer), Satanstealer, and StrelaStealer.
Distributed via phishing, spam campaigns, cracked software, fake update websites, SEO poisoning, and malvertising, data harvested using such programs typically find their way onto the dark web in the form of stealer logs from where they are purchased by other cybercriminals to further their schemes.
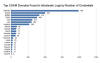
"Employees regularly save corporate credentials on personal devices or access personal resources on organizational devices, increasing the risk of infection," Flare noted in a report last July.
"A complex ecosystem exists in which malware-as-a-service (MaaS) vendors sell info-stealer malware on illicit Telegram channels, threat actors distribute it through fake cracked software or phishing emails, and they then sell infected device logs on specialized dark web marketplaces."
Recorded Future's Insikt Group said it was able to identify 3,324 unique credentials used to access known CSAM domains between February 2021 and February 2024, using them to unmask three individuals who have been found to maintain accounts at no less than four websites.
The fact that stealer logs also comprise cryptocurrency wallet addresses means it could be used to determine if the addresses have been used to procure CSAM and other harmful material.
Furthermore, countries like Brazil, India, and the U.S. had the highest counts of users with credentials to known CSAM communities, although the company said that it could be due to an "overrepresentation due to dataset sourcing."
"Info-stealer malware and stolen credentials are projected to remain a cornerstone of the cybercriminal economy due to the high demand by threat actors seeking initial access to targets," it said, adding it has shared its findings with law enforcement.
"Info-stealer logs can be used by investigators and law enforcement partners to track child exploitation on the dark web and provide insight into a part of the dark web that is especially difficult to trace."
Experts Warn of Mekotio Banking Trojan Targeting Latin American Countries
8.7.24 Virus The Hacker News

Financial institutions in Latin America are being threatened by a banking trojan called Mekotio (aka Melcoz).
That's according to findings from Trend Micro, which said it recently observed a surge in cyber attacks distributing the Windows malware.
Mekotio, known to be actively put to use since 2015, is known to target Latin American countries like Brazil, Chile, Mexico, Spain, Peru, and Portugal with an aim to steal banking credentials.
First documented by ESET in August 2020, it's part of a tetrade of banking trojans targeting the region Guildma, Javali, and Grandoreiro, the latter of which was dismantled by law enforcement earlier this year.
"Mekotio shares common characteristics for this type of malware, such as being written in Delphi, using fake pop-up windows, containing backdoor functionality and targeting Spanish- and Portuguese-speaking countries," the Slovakian cybersecurity firm said at the time.
The malware operation suffered a blow in July 2021 when Spanish law enforcement agencies arrested 16 individuals belonging to a criminal network in connection with orchestrating social engineering campaigns targeting European users that delivered Grandoreiro and Mekotio.
Attack chains involve the use of tax-themed phishing emails that aim to trick recipients into opening malicious attachments or clicking on bogus links that lead to the deployment of an MSI installer file, which, in turn, makes use of an AutoHotKey (AHK) script to launch the malware.
It's worth noting that the infection process marks a slight deviation from the one previously detailed by Check Point in November 2021, which made use of an obfuscated batch script that runs a PowerShell script to download a second-stage ZIP file containing the AHK script.
Once installed, Mekotio harvests system information and establishes contact with a command-and-control (C2) server to receive further instructions.

It's main objective is to siphon banking credentials by displaying fake pop-ups that impersonate legitimate banking sites. It can also capture screenshots, log keystrokes, steal clipboard data, and establish persistence on the host using scheduled tasks.
The stolen information can then be used by the threat actors to gain unauthorized access to users' bank accounts and perform fraudulent transactions.
"The Mekotio banking trojan is a persistent and evolving threat to financial systems, especially in Latin American countries," Trend Micro said. "It uses phishing emails to infiltrate systems, with the goal of stealing sensitive information while also maintaining a strong foothold on compromised machines."
The development comes as Mexican cybersecurity firm Scitum disclosed details of a new Latin American banking trojan codenamed Red Mongoose Daemon that, similar to Mekotio, utilizes MSI droppers distributed via phishing emails masquerading as invoices and tax notes.
"The main objective of Red Mongoose Daemon is to steal victims' banking information by spoofing PIX transactions through overlapping windows," the company said. "This trojan is aimed at Brazilian end users and employees of organizations with banking information."
"Red Mongoose Daemon has capabilities for manipulating and creating windows, executing commands, controlling the computer remotely, manipulating web browsers, hijacking clipboards, and impersonating Bitcoin wallets by replacing copied wallets with the ones used by cybercriminals."
GootLoader Malware Still Active, Deploys New Versions for Enhanced Attacks
5.7.24 Virus The Hacker News

The malware known as GootLoader continues to be in active use by threat actors looking to deliver additional payloads to compromised hosts.
"Updates to the GootLoader payload have resulted in several versions of GootLoader, with GootLoader 3 currently in active use," cybersecurity firm Cybereason said in an analysis published last week.
"While some of the particulars of GootLoader payloads have changed over time, infection strategies and overall functionality remain similar to the malware's resurgence in 2020."
GootLoader, a malware loader part of the Gootkit banking trojan, is linked to a threat actor named Hive0127 (aka UNC2565). It abuses JavaScript to download post-exploitation tools and is distributed via search engine optimization (SEO) poisoning tactics.
It typically serves as a conduit for delivering various payloads such as Cobalt Strike, Gootkit, IcedID, Kronos, REvil, and SystemBC.

In recent months, the threat actors behind GootLoader have also unleashed their own command-and-control (C2) and lateral movement tool dubbed GootBot, indicating that the "group is expanding their market to gain a wider audience for their financial gains."
Attack chains involve compromising websites to host the GootLoader JavaScript payload by passing it off as legal documents and agreements, which, when launched, sets up persistence using a scheduled task and executes additional JavaScript to kick-start a PowerShell script for collecting system information and awaiting further instructions.
"Sites that host these archive files leverage Search Engine Optimization (SEO) poisoning techniques to lure in victims that are searching for business-related files such as contract templates or legal documents," security researchers Ralph Villanueva, Kotaro Ogino, and Gal Romano said.
The attacks are also notable for making use of source code encoding, control flow obfuscation, and payload size inflation in order to resist analysis and detection. Another technique entails embedding the malware in legitimate JavaScript library files like jQuery, Lodash, Maplace.js, and tui-chart.
"GootLoader has received several updates during its life cycle, including changes to evasion and execution functionalities," the researchers concluded.
Microsoft MSHTML Flaw Exploited to Deliver MerkSpy Spyware Tool
4.7.24 Virus The Hacker News

Unknown threat actors have been observed exploiting a now-patched security flaw in Microsoft MSHTML to deliver a surveillance tool called MerkSpy as part of a campaign primarily targeting users in Canada, India, Poland, and the U.S.
"MerkSpy is designed to clandestinely monitor user activities, capture sensitive information, and establish persistence on compromised systems," Fortinet FortiGuard Labs researcher Cara Lin said in a report published last week.
The starting point of the attack chain is a Microsoft Word document that ostensibly contains a job description for a software engineer role.
Cybersecurity
But opening the file triggers the exploitation of CVE-2021-40444, a high-severity flaw in MSHTML that could result in remote code execution without requiring any user interaction. It was addressed by Microsoft as part of Patch Tuesday updates released in September 2021.
In this case, it paves the way for the download of an HTML file ("olerender.html") from a remote server that, in turn, initiates the execution of an embedded shellcode after checking the operating system version.
"Olerender.html" takes advantage of "'VirtualProtect' to modify memory permissions, allowing the decoded shellcode to be written into memory securely," Lin explained.
"Following this, 'CreateThread' executes the injected shellcode, setting the stage for downloading and executing the next payload from the attacker's server. This process ensures that the malicious code runs seamlessly, facilitating further exploitation."
The shellcode serves as a downloader for a file that's deceptively titled "GoogleUpdate" but, in reality, harbors an injector payload responsible for evading detection by security software and loading MerkSpy into memory.
The spyware establishes persistence on the host through Windows Registry changes such that it's launched automatically upon system startup. It also comes with capabilities to clandestinely capture sensitive information, monitor user activities, and exfiltrate data to external servers under the threat actors' control.
Cybersecurity
This includes screenshots, keystrokes, login credentials stored in Google Chrome, and data from the MetaMask browser extension. All this information is transmitted to the URL "45.89.53[.]46/google/update[.]php."
The development comes as Symantec detailed a smishing campaign targeting users in the U.S. with sketchy SMS messages that purport to be from Apple and aim to trick them into clicking on bogus credential harvesting pages ("signin.authen-connexion[.]info/icloud") in order to continue using the services.
"The malicious website is accessible from both desktop and mobile browsers," the Broadcom-owned company said. "To add a layer of perceived legitimacy, they have implemented a CAPTCHA that users must complete. After this, users are directed to a webpage that mimics an outdated iCloud login template."
FakeBat Loader Malware Spreads Widely Through Drive-by Download Attacks
3.7.24 Virus The Hacker News
The loader-as-a-service (LaaS) known as FakeBat has become one of the most widespread loader malware families distributed using the drive-by download technique this year, findings from Sekoia reveal.
"FakeBat primarily aims to download and execute the next-stage payload, such as IcedID, Lumma, RedLine, SmokeLoader, SectopRAT, and Ursnif," the company said in a Tuesday analysis.
Drive-by attacks entail the use of methods like search engine optimization (SEO) poisoning, malvertising, and nefarious code injections into compromised sites to entice users into downloading bogus software installers or browser updates.
The use of malware loaders over the past few years dovetails with the growing use of landing pages impersonating legitimate software websites by passing them off as legitimate installers. This ties into the larger aspect that phishing and social engineering remain one of the threat actors' main ways to acquire initial access.
FakeBat, also known as EugenLoader and PaykLoader, has been offered to other cybercriminals under a LaaS subscription model on underground forums by a Russian-speaking threat actor named Eugenfest (aka Payk_34) since at least December 2022.
The loader is designed to bypass security mechanisms and provides customers with options to generate builds using templates to trojanize legitimate software as well as monitor installations over time through an administration panel.
While the earlier versions made use of an MSI format for the malware builds, recent iterations observed since September 2023 have switched to an MSIX format and added a digital signature to the installer with a valid certificate to sidestep Microsoft SmartScreen protections.
The malware is available for $1,000 per week and $2,500 per month for the MSI format, $1,500 per week and $4,000 per month for the MSIX format, and $1,800 per week and $5,000 per month for the combined MSI and signature package.

Sekoia said it detected different activity clusters disseminating FakeBat by three primary approaches: Impersonating popular software through malicious Google ads, fake web browser updates via compromised sites, and social engineering schemes on social networks. This encompasses campaigns likely related to the FIN7 group, Nitrogen, and BATLOADER.
"In addition to hosting payloads, FakeBat [command-and-control] servers highly likely filter traffic based on characteristics such as the User-Agent value, the IP address, and the location," Sekoia said. "This enables the distribution of the malware to specific targets."
The disclosure comes as the AhnLab Security Intelligence Center (ASEC) detailed a malware campaign distributing another loader named DBatLoader (aka ModiLoader and NatsoLoader) through invoice-themed phishing emails.
It also follows the discovery of infection chains propagating Hijack Loader (aka DOILoader and IDAT Loader) via pirated movie download sites to ultimately deliver the Lumma information stealer.
"This IDATLOADER campaign is using a complex infection chain containing multiple layers of direct code-based obfuscation alongside innovative tricks to further hide the maliciousness of the code," Kroll researcher Dave Truman said.
"The infection hinged around utilizing Microsoft's mshta.exe to execute code buried deep within a specially crafted file masquerading as a PGP Secret Key. The campaign made use of novel adaptations of common techniques and heavy obfuscation to hide the malicious code from detection."
Phishing campaigns have further been observed delivering Remcos RAT, with a new Eastern European threat actor dubbed Unfurling Hemlock leveraging loaders and emails to drop binary files that act as a "cluster bomb" to spread different malware strains at once.
"The malware being distributed using this technique is mostly comprised of stealers, such as RedLine, RisePro, and Mystic Stealer, and loaders such as Amadey and SmokeLoader," Outpost24 researcher Hector Garcia said.
"Most of the first stages were detected being sent via email to different companies or being dropped from external sites that were contacted by external loaders."
South Korean ERP Vendor's Server Hacked to Spread Xctdoor Malware
3.7.24 Virus The Hacker News
An unnamed South Korean enterprise resource planning (ERP) vendor's product update server has been found to be compromised to deliver a Go-based backdoor dubbed Xctdoor.
The AhnLab Security Intelligence Center (ASEC), which identified the attack in May 2024, did not attribute it to a known threat actor or group, but noted that the tactics overlap with that of Andariel, a sub-cluster within the infamous Lazarus Group.
The similarities stem from the North Korean adversary's prior use of the ERP solution to distribute malware like HotCroissant – which is identical to Rifdoor – in 2017 by inserting a malicious routine into a software update program.
In the recent incident analyzed by ASEC, the same executable is said to have been tampered with to execute a DLL file from a specific path using the regsvr32.exe process as opposed to launching a downloader.
The DLL file, Xctdoor, is capable of stealing system information, including keystrokes, screenshots, and clipboard content, and executing commands issued by the threat actor.
"Xctdoor communicates with the [command-and-control] server using the HTTP protocol, while the packet encryption employs the Mersenne Twister (MT19937) algorithm and the Base64 algorithm," ASEC said.
Also used in the attack is a malware called XcLoader, which serves as an injector malware responsible for injecting Xctdoor into legitimate processes (e.g., "explorer.exe").
ASEC said it further detected cases where poorly secured web servers have been compromised to install XcLoader since at least March 2024.
The development comes as the another North Korea-linked threat actor referred to as Kimusky has been observed employing a previously undocumented backdoor codenamed HappyDoor that has been put to use as far back as July 2021.
Attack chains distributing the malware leverage spear-phishing emails as a starting point to disseminate a compressed file, which contains an obfuscated JavaScript or dropper that, when executed, creates and runs HappyDoor alongside a decoy file.
HappyDoor, a DLL file executed via regsvr32.exe, is equipped to communicate with a remote server over HTTP and facilitate information theft, download/upload files, as well as update and terminate itself.
It also follows a "massive" malware distribution campaign orchestrated by the Konni cyber espionage group (aka Opal Sleet, Osmium, or TA406) targeting South Korea with phishing lures impersonating the national tax service to deliver malware capable of stealing sensitive information, security researcher Idan Tarab said.
CapraRAT Spyware Disguised as Popular Apps Threatens Android Users
1.7.24 Virus The Hacker News
The threat actor known as Transparent Tribe has continued to unleash malware-laced Android apps as part of a social engineering campaign to target individuals of interest.
"These APKs continue the group's trend of embedding spyware into curated video browsing applications, with a new expansion targeting mobile gamers, weapons enthusiasts, and TikTok fans," SentinelOne security researcher Alex Delamotte said in a new report shared with The Hacker News.
The campaign, dubbed CapraTube, was first outlined by the cybersecurity company in September 2023, with the hacking crew employing weaponized Android apps impersonating legitimate apps like YouTube to deliver a spyware called CapraRAT, a modified version of AndroRAT with capabilities to capture a wide range of sensitive data.
Transparent Tribe, suspected to be of Pakistan origin, has leveraged CapraRAT for over two years in attacks targeting the Indian government and military personnel. The group has a history of leaning into spear-phishing and watering hole attacks to deliver a variety of Windows and Android spyware.
"The activity highlighted in this report shows the continuation of this technique with updates to the social engineering pretexts as well as efforts to maximize the spyware's compatibility with older versions of the Android operating system while expanding the attack surface to include modern versions of Android," Delamotte explained.
The list of new malicious APK files identified by SentinelOne is as follows -
Crazy Game (com.maeps.crygms.tktols)
Sexy Videos (com.nobra.crygms.tktols)
TikToks (com.maeps.vdosa.tktols)
Weapons (com.maeps.vdosa.tktols)
CapraRAT uses WebView to launch a URL to either YouTube or a mobile gaming site named CrazyGames[.]com, while, in the background, it abuses its permissions to access locations, SMS messages, contacts, and call logs; make phone calls; take screenshots; or record audio and video.
A notable change to the malware is that permissions such as READ_INSTALL_SESSIONS, GET_ACCOUNTS, AUTHENTICATE_ACCOUNTS, and REQUEST_INSTALL_PACKAGES are no longer requested, suggesting that the threat actors are aiming to use it as a surveillance tool than a backdoor.
"The updates to the CapraRAT code between the September 2023 campaign and the current campaign are minimal, but suggest the developers are focused on making the tool more reliable and stable," Delamotte said.
"The decision to move to newer versions of the Android OS are logical, and likely align with the group's sustained targeting of individuals in the Indian government or military space, who are unlikely to use devices running older versions of Android, such as Lollipop which was released 8 years ago."
The disclosure comes as Promon disclosed a novel type of Android banking malware called Snowblind that, in ways similar to FjordPhantom, attempts to bypass detection methods and make use of the operating system's accessibility services API in a surreptitious manner.
"Snowblind [...] performs a normal repackaging attack but uses a lesser-known technique based on seccomp that is capable of bypassing many anti-tampering mechanisms," the company said.
"Interestingly, FjordPhantom and Snowblind target apps from Southeast Asia and leverage powerful new attack techniques. That seems to indicate that malware authors in that region have become extremely sophisticated."
Cybersecurity
"The updates to the CapraRAT code between the September 2023 campaign and the current campaign are minimal, but suggest the developers are focused on making the tool more reliable and stable," Delamotte said.
"The decision to move to newer versions of the Android OS are logical, and likely align with the group's sustained targeting of individuals in the Indian government or military space, who are unlikely to use devices running older versions of Android, such as Lollipop which was released 8 years ago."
The disclosure comes as Promon disclosed a novel type of Android malware called Snowblind that, in ways similar to FjordPhantom, attempts to bypass detection methods and make use of the operating system's accessibility services API in a surreptitious manner.
"Snowblind [...] performs a normal repackaging attack but uses a lesser-known technique based on seccomp that is capable of bypassing many anti-tampering mechanisms," the company said.
"Interestingly, FjordPhantom and Snowblind target apps from Southeast Asia and leverage powerful new attack techniques. That seems to indicate that malware authors in that region have become extremely sophisticated."
Indian Software Firm's Products Hacked to Spread Data-Stealing Malware
1.7.24 Virus The Hacker News
Installers for three different software products developed by an Indian company named Conceptworld have been trojanized to distribute information-stealing malware.
The installers correspond to Notezilla, RecentX, and Copywhiz, according to cybersecurity firm Rapid7, which discovered the supply chain compromise on June 18, 2024. The issue has since been remediated by Conceptworld as of June 24 within 12 hours of responsible disclosure.
"The installers had been trojanized to execute information-stealing malware that has the capability to download and execute additional payloads," the company said, adding the malicious versions had a larger file size than their legitimate counterparts.
Specifically, the malware is equipped to steal browser credentials and cryptocurrency wallet information, log clipboard contents and keystrokes, and download and execute additional payloads on infected Windows hosts. It also sets up persistence using a scheduled task to execute the main payload every three hours.
It's currently not clear how the official domain "conceptworld[.]com" was breached to stage the counterfeit installers. However, once installed, the user is prompted to proceed with the installation process associated with the actual software, while it's also designed to drop and execute a binary "dllCrt32.exe" that's responsible for running a batch script "dllCrt.bat."
Besides establishing persistence on the machine, it's configured to execute another file ("dllBus32.exe"), which, in turn, establishes connections with a command-and-control (C2) server and incorporates functionality to steal sensitive data as well as retrieve and run more payloads.
This includes gathering credentials and other information from Google Chrome, Mozilla Firefox, and multiple cryptocurrency wallets (e.g., Atomic, Coinomi, Electrum, Exodus, and Guarda). It's also capable of harvesting files matching a specific set of extensions (.txt, .doc, .png, and .jpg), logging keystrokes, and grabbing clipboard contents.
"The malicious installers observed in this case are unsigned and have a file size that is inconsistent with copies of the legitimate installer," Rapid7 said.
Users who have downloaded an installer for Notezilla, RecentX, or Copywhiz in June 2024 are recommended to examine their systems for signs of compromise and take appropriate action – such as re-imaging the affected ones – to undo the nefarious modifications.
New Medusa Android Trojan Targets Banking Users Across 7 Countries
27.6.24 Virus The Hacker News

researchers have discovered an updated version of an Android banking trojan called Medusa that has been used to target users in Canada, France, Italy, Spain, Turkey, the U.K., and the U.S.
The new fraud campaigns, observed in May 2024 and active since July 2023, manifested through five different botnets operated by various affiliates, firm Cleafy said in an analysis published last week.
The new Medusa samples feature a "lightweight permission set and new features, such as the ability to display a full-screen overlay and remotely uninstall applications," security researchers Simone Mattia and Federico Valentini said.
Medusa, also known as TangleBot, is a sophisticated Android malware first discovered in July 2020 targeting financial entities in Turkey. It comes with capabilities to read SMS messages, log keystrokes, capture screenshots, record calls, share the device screen in real-time, and perform unauthorized fund transfers using overlay attacks to steal banking credentials.
In February 2022, ThreatFabric uncovered Medusa campaigns leveraging similar delivery mechanisms as that of FluBot (aka Cabassous) by masquerading the malware as seemingly harmless package delivery and utility apps. It's suspected that the threat actors behind the Trojan are from Turkey.
Cleafy's latest analysis reveals not only improvements to the malware, but also the use of dropper apps to disseminate Medusa under the guise of fake updates. Furthermore, legitimate services like Telegram and X are used as dead drop resolvers to retrieve the command-and-control (C2) server used for data exfiltration.
A notable change is the reduction in the number of permissions sought in an apparent effort to lower the chances of detection. That said, it still requires Android's accessibility services API, which allows it to stealthily enable other permissions as required and avoid raising user suspicion.

Another modification is the ability to set a black screen overlay on the victim's device to give the impression that the device is locked or powered off and use it as a cover to carry out malicious activities.
Medusa botnet clusters typically rely on tried-and-tested approaches such as phishing to spread the malware. However, newer waves have been observed propagating it via dropper apps downloaded from untrusted sources, underscoring continued efforts on the part of threat actors to evolve their tactics.
"Minimizing the required permissions evades detection and appears more benign, enhancing its ability to operate undetected for extended periods," the researchers said. "Geographically, the malware is expanding into new regions, such as Italy and France, indicating a deliberate effort to diversify its victim pool and broaden its attack surface."
The development comes as Symantec revealed that fictitious Chrome browser updates for Android are being used as a lure to drop the Cerberus banking trojan. Similar campaigns distributing bogus Telegram apps via phony websites ("telegroms[.]icu") have also been observed distributing another Android malware dubbed SpyMax.
Once installed, the app prompts the user to enable the accessibility services, allowing it to gather keystrokes, precise locations, and even the speed at which the device is moving. The collected information is then compressed and exported to an encoded C2 server.
"SpyMax is a remote administration tool (RAT) that has the capability to gather personal/private information from the infected device without consent from the user and sends the same to a remote threat actor," K7 Security Labs said. "This enables the threat actors to control victims' devices that impacts the confidentiality and integrity of the victim's privacy and data."
New Cyberthreat 'Boolka' Deploying BMANAGER Trojan via SQLi Attacks
25.6.24 Virus The Hacker News

A previously undocumented threat actor dubbed Boolka has been observed compromising websites with malicious scripts to deliver a modular trojan codenamed BMANAGER.
"The threat actor behind this campaign has been carrying out opportunistic SQL injection attacks against websites in various countries since at least 2022," Group-IB researchers Rustam Mirkasymov and Martijn van den Berk said in a report published last week.
"Over the last three years, the threat actors have been infecting vulnerable websites with malicious JavaScript scripts capable of intercepting any data entered on an infected website."
Boolka gets its name from the JavaScript code inserted into the website that beacons out to a command-and-control server named "boolka[.]tk" every time an unsuspecting visitor lands on the infected site.
The JavaScript is also designed to collect and exfiltrate user inputs and interactions in a Base64-encoded format, indicating the use of the malware to grab sensitive details like credentials and other personal information.
Furthermore, it redirects users to a bogus loading page that prompts victims to download and install a browser extension when, in reality, it drops a downloader for the BMANAGER trojan, which, in turn, attempts to fetch the malware from a hard-coded URL. The malware delivery framework is based on the BeEF framework.

The trojan, for its part, serves as a conduit to deploy four additional modules, including BMBACKUP (harvest files from particular paths), BMHOOK (record which applications are running and have keyboard focus), BMLOG (log keystrokes), and BMREADER (export stolen data). It also sets up persistence on the host using scheduled tasks.
"Most samples make use of a local SQL database," the researchers noted. "The path and name of this database is hard-coded in the samples to be located at: C:\Users\{user}\AppData\Local\Temp\coollog.db, with user being the username of the logged in user."
Boolka is the third actor after GambleForce and ResumeLooters to leverage SQL injection attacks to steal sensitive data in recent months.
"Starting from opportunistic SQL injection attacks in 2022 to the development of his own malware delivery platform and trojans like BMANAGER, Boolka's operations demonstrate the group's tactics have grown more sophisticated over time," the researchers concluded.
"The injection of malicious JavaScript snippets into vulnerable websites for data exfiltration, and then the use of the BeEF framework for malware delivery, reflects the step-by-step development of the attacker's competencies."
Multiple WordPress Plugins Compromised: Hackers Create Rogue Admin Accounts
25.6.24 Virus The Hacker News
Multiple WordPress plugins have been backdoored to inject malicious code that makes it possible to create rogue administrator accounts with the aim of performing arbitrary actions.
"The injected malware attempts to create a new administrative user account and then sends those details back to the attacker-controlled server," Wordfence security researcher Chloe Chamberland said in a Monday alert.
"In addition, it appears the threat actor also injected malicious JavaScript into the footer of websites that appears to add SEO spam throughout the website."
The admin accounts have the usernames "Options" and "PluginAuth," with the account information exfiltrated to the IP address 94.156.79[.]8.
It's currently not known how the unknown attackers behind the campaign managed to compromise the plugins, but the earliest signs of the software supply chain attack date back to June 21, 2024.
The plugins in question are no longer available for download from the WordPress plugin directory pending ongoing review -
Social Warfare 4.4.6.4 – 4.4.7.1 (Patched version: 4.4.7.3) - 30,000+ installs
Blaze Widget 2.2.5 – 2.5.2 (Patched version: N/A) - 10+ installs
Wrapper Link Element 1.0.2 – 1.0.3 (Patched version: N/A) - 1,000+ installs
Contact Form 7 Multi-Step Addon 1.0.4 – 1.0.5 (Patched version: N/A) - 700+ installs
Simply Show Hooks 1.2.1 (Patched version: N/A) - 4,000+ installs
Users of the aforementioned plugins are advised to inspect their sites for suspicious administrator accounts and delete them, in addition to removing any malicious code.
Multiple Threat Actors Deploying Open-Source Rafel RAT to Target Android Devices
25.6.24 Virus The Hacker News
Multiple threat actors, including cyber espionage groups, are employing an open-source Android remote administration tool called Rafel RAT to meet their operational objectives by masquerading it as Instagram, WhatsApp, and various e-commerce and antivirus apps.
"It provides malicious actors with a powerful toolkit for remote administration and control, enabling a range of malicious activities from data theft to device manipulation," Check Point said in an analysis published last week.
It boasts a wide range of features, such as the ability to wipe SD cards, delete call logs, siphon notifications, and even act as ransomware.
The use of Rafel RAT by DoNot Team (aka APT-C-35, Brainworm, and Origami Elephant) was previously highlighted by the Israeli company in cyber attacks that leveraged a design flaw in Foxit PDF Reader to trick users into downloading malicious payloads.
The campaign, which took place in April 2024, is said to have utilized military-themed PDF lures to deliver the malware.
Check Point said it identified around 120 different malicious campaigns, some targeting high-profile entities, that span various countries like Australia, China, Czechia, France, Germany, India, Indonesia, Italy, New Zealand, Pakistan, Romania, Russia, and the U.S.

"The majority of victims had Samsung phones, with Xiaomi, Vivo, and Huawei users comprising the second-largest group among the targeted victims," it noted, adding no less than 87.5% of the infected devices are running out-of-date Android versions that no longer receive security fixes.
Typical attack chains involve the use of social engineering to manipulate victims into granting the malware-laced apps intrusive permissions in order to hoover sensitive data like contact information, SMS messages (e.g., 2FA codes), location, call logs, and the list of installed applications, among others.
Rafel RAT primarily makes use of HTTP(S) for command-and-control (C2) communications, but it can also utilize Discord APIs to contact the threat actors. It also comes with an accompanying PHP-based C2 panel that registered users can leverage to issue commands to compromised devices.
The tool's effectiveness across various threat actors is corroborated by its deployment in a ransomware operation carried out by an attacker likely originating from Iran, who sent a ransom note written in Arabic through an SMS that urged a victim in Pakistan to contact them on Telegram.

"Rafel RAT is a potent example of the evolving landscape of Android malware, characterized by its open-source nature, extensive feature set, and widespread utilization across various illicit activities," Check Point said.
"The prevalence of Rafel RAT highlights the need for continual vigilance and proactive security measures to safeguard Android devices against malicious exploitation."
Warning: New Adware Campaign Targets Meta Quest App Seekers
23.6.24 Virus The Hacker News

A new campaign is tricking users searching for the Meta Quest (formerly Oculus) application for Windows into downloading a new adware family called AdsExhaust.
"The adware is capable of exfiltrating screenshots from infected devices and interacting with browsers using simulated keystrokes," firm eSentire said in an analysis, adding it identified the activity earlier this month.
"These functionalities allow it to automatically click through advertisements or redirect the browser to specific URLs, generating revenue for the adware operators."
The initial infection chain involves surfacing the bogus website ("oculus-app[.]com") on Google search results pages using search engine optimization (SEO) poisoning techniques, prompting unsuspecting site visitors to download a ZIP archive ("oculus-app.EXE.zip") containing a Windows batch script.
The batch script is designed to fetch a second batch script from a command-and-control (C2) server, which, in turn, contains a command to retrieve another batch file. It also creates scheduled tasks on the machine to run the batch scripts at different times.
This step is followed by the download of the legitimate app onto the compromised host, while simultaneously additional Visual Basic Script (VBS) files and PowerShell scripts are dropped to gather IP and system information, capture screenshots, and exfiltrate the data to a remote server ("us11[.]org/in.php").
The response from the server is the PowerShell-based AdsExhaust adware that checks if Microsoft's Edge browser is running and determines the last time a user input occurred.
"If Edge is running and the system is idle and exceeds 9 minutes, the script can inject clicks, open new tabs, and navigate to URLs embedded in the script," eSentire said. "It then randomly scrolls up and down the opened page."
It's suspected that this behavior is intended to trigger elements such as ads on the web page, especially considering AdsExhaust performs random clicks within specific coordinates on the screen.
The adware is also capable of closing the opened browser if mouse movement or user interaction is detected, creating an overlay to conceal its activities to the victim, and searching for the word "Sponsored" in the currently opened Edge browser tab in order to click on the ad with the goal of inflating ad revenue.
Furthermore, it's equipped to fetch a list of keywords from a remote server and perform Google searches for those keywords by launching Edge browser sessions via the Start-Process PowerShell command.
"AdsExhaust is an adware threat that cleverly manipulates user interactions and hides its activities to generate unauthorized revenue," the Canadian company noted.
"It contains multiple techniques, such as retrieving malicious code from the C2 server, simulating keystrokes, capturing screenshots, and creating overlays to remain undetected while engaging in harmful activities."
The development comes as similar fake IT support websites surfaced via search results are being used to deliver Hijack Loader (aka IDAT Loader), which ultimately leads to a Vidar Stealer infection.
What makes the attack stand out is that the threat actors are also leveraging YouTube videos to advertise the phony site and using bots to post fraudulent comments, giving it a veneer of legitimacy to users looking for solutions to address a Windows update error (error code 0x80070643).
"This highlights the effectiveness of social engineering tactics and the need for users to be cautious about the authenticity of the solutions they find online," eSentire said.
The disclosure also comes on the heels of a malpsam campaign targeting users in Italy with invoice-themed ZIP archive lures to deliver a Java-based remote access trojan named Adwind (aka AlienSpy, Frutas, jRAT, JSocket, Sockrat, and Unrecom).
"Upon extraction the user is served with .HTML files such as INVOICE.html or DOCUMENT.html that lead to malicious .jar files," Broadcom-owned Symantec said.
"The final dropped payload is Adwind remote access trojan (RAT) that allows the attackers control over the compromised endpoint as well as confidential data collection and exfiltration."
Chinese Hackers Deploy SpiceRAT and SugarGh0st in Global Espionage Campaign
23.6.24 Virus The Hacker News

A previously undocumented Chinese-speaking threat actor codenamed SneakyChef has been linked to an espionage campaign primarily targeting government entities across Asia and EMEA (Europe, Middle East, and Africa) with SugarGh0st malware since at least August 2023.
"SneakyChef uses lures that are scanned documents of government agencies, most of which are related to various countries' Ministries of Foreign Affairs or embassies," Cisco Talos researchers Chetan Raghuprasad and Ashley Shen said in an analysis published today.
Activities related to the hacking crew were first highlighted by the company in late November 2023 in connection with an attack campaign that singled out South Korea and Uzbekistan with a custom variant of Gh0st RAT called SugarGh0st.
A subsequent analysis from Proofpoint last month uncovered the use of SugarGh0st RAT against U.S. organizations involved in artificial intelligence efforts, including those in academia, private industry, and government services. It's tracking the cluster under the name UNK_SweetSpecter.
It's worth mentioning at this stage that SneakyChef refers to the same campaign that Palo Alto Networks Unit 42 has codenamed Operation Diplomatic Specter. The activity, per the security vendor, has been ongoing since at least late 2022, striking governmental entities in the Middle East, Africa, and Asia.
Talos said that it has since observed the same malware being used to likely focus on various government entities across Angola, India, Latvia, Saudi Arabia, and Turkmenistan based on the lure documents used in the spear-phishing campaigns, indicating a widening of the scope of the countries targeted.
In addition to leveraging attack chains that make use of Windows Shortcut (LNK) files embedded within RAR archives to deliver SugarGh0st, the new wave has been found to employ a self-extracting RAR archive (SFX) as an initial infection vector to launch a Visual Basic Script (VBS) that ultimately executes the malware by means of a loader while simultaneously displaying the decoy file.

The attacks against Angola are also notable for the fact that it utilizes a new remote access trojan codenamed SpiceRAT using lures from Neytralny Turkmenistan, a Russian-language newspaper in Turkmenistan.
SpiceRAT, for its part, employs two different infection chains for propagation, one of which uses an LNK file present inside a RAR archive that deploys the malware using DLL side-loading techniques.
"When the victim extracts the RAR file, it drops the LNK and a hidden folder on their machine," the researchers said. "After a victim opens the shortcut file, which masqueraded as a PDF document, it executes an embedded command to run the malicious launcher executable from the dropped hidden folder."
The launcher then proceeds to display the decoy document to the victim and run a legitimate binary ("dxcap.exe"), which subsequently sideloads a malicious DLL responsible for loading SpiceRAT.
The second variant entails the use of an HTML Application (HTA) that drops a Windows batch script and a Base64-encoded downloader binary, with the former launching the executable by means of a scheduled task every five minutes.

The batch script is also engineered to run another legitimate executable "ChromeDriver.exe" every 10 minutes, which then sideloads a rogue DLL that, in turn, loads SpiceRAT. Each of these components – ChromeDriver.exe, the DLL, and the RAT payload – are extracted from a ZIP archive retrieved by the downloader binary from a remote server.
SpiceRAT also takes advantage of the DLL side-loading technique to start a DLL loader, which captures the list of running processes to check if it's being debugged, followed by running the main module from memory.
"With the capability to download and run executable binaries and arbitrary commands, SpiceRAT significantly increases the attack surface on the victim's network, paving the way for further attacks," Talos said.
Experts Uncover New Evasive SquidLoader Malware Targeting Chinese Organizations
20.6.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new evasive malware loader named SquidLoader that spreads via phishing campaigns targeting Chinese organizations.
AT&T LevelBlue Labs, which first observed the malware in late April 2024, said it incorporates features that are designed to thwart static and dynamic analysis and ultimately evade detection.
Attack chains leverage phishing emails that come with attachments that masquerade as Microsoft Word documents, but, in reality, are binaries that pave the way for the execution of the malware, which is then used to fetch second-stage shellcode payloads from a remote server, including Cobalt Strike.
"These loaders feature heavy evasion and decoy mechanisms which help them remain undetected while also hindering analysis," security researcher Fernando Dominguez said. "The shellcode that is delivered is also loaded in the same loader process, likely to avoid writing the payload to disk and thus risk being detected."
Cybersecurity
Some of the defensive evasion techniques adopted by SquidLoader encompass the use of encrypted code segments, pointless code that remains unused, Control Flow Graph (CFG) obfuscation, debugger detection, and performing direct syscalls instead of calling Windows NT APIs.
Loader malware has become a popular commodity in the criminal underground for threat actors looking to deliver and launch additional payloads to compromised hosts, while bypassing antivirus defenses and other security measures.
Last year, Aon's Stroz Friedberg incident detailed a loader known as Taurus Loader that has been observed distributing the Taurus information stealer as well as AgentVX, a trojan with capabilities to execute more malware and set up persistence using Windows Registry changes, and gather data.
The development comes as a new in-depth analysis of a malware loader and backdoor referred to as PikaBot has highlighted that it continues to be actively developed by its developers since its emergence in February 2023.
Cybersecurity
"The malware employs advanced anti-analysis techniques to evade detection and harden analysis, including system checks, indirect syscalls, encryption of next-stage and strings, and dynamic API resolution," Sekoia said. "The recent updates to the malware have further enhanced its capabilities, making it even more challenging to detect and mitigate."
It also follows findings from BitSight that the infrastructure related to another loader malware called Latrodectus has gone offline in the wake of a law enforcement effort dubbed Operation Endgame that saw over 100 botnet servers, including those associated with IcedID, SystemBC, PikaBot, SmokeLoader, Bumblebee, and TrickBot, dismantled.
The cybersecurity company said it observed nearly 5,000 distinct victims spread across 10 different campaigns, with a majority of the victims located in the U.S., the U.K., the Netherlands, Poland, France, Czechia, Japan, Australia, Germany, and Canada.
New Rust-based Fickle Malware Uses PowerShell for UAC Bypass and Data Exfiltration
20.6.24 Virus The Hacker News
A new Rust-based information stealer malware called Fickle Stealer has been observed being delivered via multiple attack chains with the goal of harvesting sensitive information from compromised hosts.
Fortinet FortiGuard Labs said it's aware of four different distribution methods -- namely VBA dropper, VBA downloader, link downloader, and executable downloader -- with some of them using a PowerShell script to bypass User Account Control (UAC) and execute Fickle Stealer.
The PowerShell script ("bypass.ps1" or "u.ps1") is also designed to periodically send information about the victim, including country, city, IP address, operating system version, computer name, and username to a Telegram bot controlled by the attacker.
The stealer payload, which is protected using a packer, runs a series of anti-analysis checks to determine if it's running in a sandbox or a virtual machine environment, following which it beacons out to a remote server to exfiltrate data in the form of JSON strings.
Fickle Stealer is no different from other variants in that it's designed to gather information from crypto wallets, web browsers powered by Chromium and the Gecko browser engine (i.e, Google Chrome, Microsoft Edge, Brave, Vivaldi, and Mozilla Firefox), and applications like AnyDesk, Discord, FileZilla, Signal, Skype, Steam, and Telegram.
It's also designed to export files matching the extensions .txt, .kdbx, .pdf, .doc, .docx, .xls, .xlsx, .ppt, .pptx, .odt, .odp, and wallet.dat.

"In addition to some popular applications, this stealer searches sensitive files in parent directories of common installation directories to ensure comprehensive data gathering," security researcher Pei Han Liao said. "It also receives a target list from the server, which makes Fickle Stealer more flexible."
The disclosure comes as Symantec disclosed details of an open-source Python stealer called AZStealer that comes with the functionality to steal a wide variety of information. Available on GitHub, it has been advertised as the "best undetected Discord stealer."
"All stolen information is zipped and depending on the size of the archive exfiltrated directly through Discord webhooks or first uploaded to Gofile online files storage and after that exfiltrated via Discord," the Broadcom-owned company said.
"AZStealer will also attempt the theft of document files with predefined targeted extensions or those having specific keywords such as password, wallet, backup, etc. in the filename."
ZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
1.5.24 Virus The Hacker News
The authors behind the resurfaced ZLoader malware have added a feature that was originally present in the Zeus banking trojan that it's based on, indicating that it's being actively developed.
"The latest version, 2.4.1.0, introduces a feature to prevent execution on machines that differ from the original infection," Zscaler ThreatLabz researcher Santiago Vicente said in a technical report. "A similar anti-analysis feature was present in the leaked ZeuS 2.X source code, but implemented differently."
ZLoader, also called Terdot, DELoader, or Silent Night, emerged after a nearly two-year hiatus around September 2023 following its takedown in early 2022.
A modular trojan with capabilities to load next-stage payloads, recent versions of the malware have added RSA encryption as well as updates to its domain generation algorithm (DGA).
The latest sign of ZLoader's evolution comes in the form of an anti-analysis feature that restricts the binary's execution to the infected machine.
The feature, present in artifacts with versions greater than 2.4.1.0, causes the malware to abruptly terminate if they are copied and executed on another system post-initial infection. This is accomplished by means of a Windows Registry check for a specific key and value.
"The Registry key and value are generated based on a hardcoded seed that is different for each sample," Vicente said.
"If the Registry key/value pair is manually created (or this check is patched), ZLoader will successfully inject itself into a new process. However, it will terminate again after executing only a few instructions. This is due to a secondary check in ZLoader's MZ header."
This means that ZLoader's execution will be stalled in a different machine unless the seed and MZ header values are set correctly and all the Registry and disk paths/names from the originally compromised system are replicated.
Zscaler said the technique used by Zloader to store the installation information and avoid being run on a different host shares similarities with ZeuS version 2.0.8, albeit implemented in a different manner, which relied on a data structure called PeSettings to store the configuration instead of the Registry.
"In recent versions, ZLoader has adopted a stealthy approach to system infections," Vicente said. "This new anti-analysis technique makes ZLoader even more challenging to detect and analyze."
The development comes as threat actors are utilizing fraudulent websites hosted on popular legitimate platforms like Weebly to spread stealer malware and steal data via black hat search engine optimization (SEO) techniques.
"This catapults their fraudulent site to the top of a user's search results, increasing the likelihood of inadvertently selecting a malicious site and potentially infecting their system with malware," Zscaler researcher Kaivalya Khursale said.
A notable aspect of these campaigns is that the infection only proceeds to the payload delivery stage if the visit originates from search engines like Google, Bing, DuckDuckGo, Yahoo, or AOL, and if bogus sites are not accessed directly.
Over the past two months, email-based phishing campaigns have also been observed targeting organizations in the U.S., Turkey, Mauritius, Israel, Russia, and Croatia with Taskun malware, which acts as a facilitator for Agent Tesla, per findings from Veriti.
Millions of Malicious 'Imageless' Containers Planted on Docker Hub Over 5 Years
1.5.24 Virus The Hacker News
Cybersecurity researchers have discovered multiple campaigns targeting Docker Hub by planting millions of malicious "imageless" containers over the past five years, once again underscoring how open-source registries could pave the way for supply chain attacks.
"Over four million of the repositories in Docker Hub are imageless and have no content except for the repository documentation," JFrog security researcher Andrey Polkovnichenko said in a report shared with The Hacker News.
What's more, the documentation has no connection whatsoever to the container. Instead, it's a web page that's designed to lure users into visiting phishing or malware-hosting websites.
Of the 4.6 million imageless Docker Hub repositories uncovered, 2.81 million of them are said to have been used as landing pages to redirect unsuspecting users to fraudulent sites as part of three broad campaigns -
Downloader (repositories created in the first half of 2021 and September 2023), which advertises links to purported pirated content or cheats for video games but either directly links to malicious sources or a legitimate one that, in turn, contains JavaScript code that redirects to the malicious payload after 500 milliseconds.
E-book phishing (repositories created in mid-2021), which redirects users searching for e-books to a website ("rd.lesac.ru") that, in turn, urges them to enter their financial information to download the e-book.
Website (thousands of repositories created daily from April 2021 to October 2023), which contains a link to an online diary-hosting service called Penzu in some cases, or a harmless piece of text, suggesting that it could have been used during early testing phases.
The payload delivered as part of the downloader campaign is designed to contact a command-and-control (C2) server and transmit system metadata, following which the server responds with a link to cracked software.

It's suspected that the attacks may be part of a larger malware operation, which could involve adware or monetization schemes that derive monetary benefit out of distributing third-party software.
On the other hand, the exact goal of the website cluster is currently unclear, with the campaign also propagated on sites that have a lax content moderation policy.
JFrog said it counted a total of 208,739 fake accounts that the threat actors used to create the malicious and unwanted repositories. Docker has since taken down all of them following responsible disclosure.
"The most concerning aspect of these three campaigns is that there is not a lot that users can do to protect themselves at the outset, other than exercising caution," Shachar Menashe, senior director of security research at JFrog, said in a statement shared with The Hacker News.
"We're essentially looking at a malware playground that in some cases has been three years in the making. These threat actors are highly motivated and are hiding behind the credibility of the Docker Hub name to lure victims."
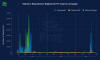
With threat actors taking painstaking efforts to poison well known utilities, as evidenced in the case of the XZ Utils compromise, it's imperative that developers exercise caution when it comes to downloading packages from open-source ecosystems/
"As Murphy's Law suggests, if something can be exploited by malware developers, it inevitably will be, so we expect that these campaigns can be found in more repositories than just Docker Hub," Menashe said.
Bogus npm Packages Used to Trick Software Developers into Installing Malware
30.4.24 Virus The Hacker News
An ongoing social engineering campaign is targeting software developers with bogus npm packages under the guise of a job interview to trick them into downloading a Python backdoor.
Cybersecurity firm Securonix is tracking the activity under the name DEV#POPPER, linking it to North Korean threat actors.
"During these fraudulent interviews, the developers are often asked to perform tasks that involve downloading and running software from sources that appear legitimate, such as GitHub," security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said. "The software contained a malicious Node JS payload that, once executed, compromised the developer's system."
Details of the campaign first emerged in late November 2023, when Palo Alto Networks Unit 42 detailed an activity cluster dubbed Contagious Interview in which the threat actors pose as employers to lure software developers into installing malware such as BeaverTail and InvisibleFerret through the interview process.
Then earlier this February, software supply chain security firm Phylum uncovered a set of malicious packages on the npm registry that delivered the same malware families to siphon sensitive information from compromised developer systems.
It's worth noting that Contagious Interview is said to be disparate from Operation Dream Job (aka DeathNote or NukeSped), with Unit 42 telling The Hacker News that the former is "focused on targeting developers, mainly through fake identities in freelance job portals, and the next stages involve the use of developer tools and npm packages leading to [...] BeaverTail and InvisibleFerret."
Operation Dream Job, linked to the prolific Lazarus Group from North Korea, is a long-running offensive campaign that sends unsuspecting professionals employed in various sectors like aerospace, cryptocurrency, defense, and others malicious files dressed as job offers to distribute malware.
First uncovered by Israeli cybersecurity firm ClearSky at the start of 2020, it also exhibits overlaps with two other Lazarus clusters known as Operation In(ter)ception and Operation North Star.
The attack chain detailed by Securonix starts with a ZIP archive hosted on GitHub that's likely sent to the target as part of the interview. Present within the file is a seemingly innocuous npm module that harbors a malicious JavaScript file codenamed BeaverTail that acts as an information stealer and a loader for a Python backdoor called InvisibleFerret that's retrieved from a remote server.
The implant, besides gathering system information, is capable of command execution, file enumeration and exfiltration, and clipboard and keystroke logging.
The development is a sign that North Korean threat actors continue to hone a raft of weapons for their cyber attack arsenal, consistently updating their tradecraft with improved abilities to hide their actions and blend in on host systems and networks, not to mention siphon off data and turn compromises into financial gain.
"When it comes to attacks which originate through social engineering, it's critical to maintain a security-focused mindset, especially during intense and stressful situations like job interviews," Securonix researchers said.
"The attackers behind the DEV#POPPER campaigns abuse this, knowing that the person on the other end is in a highly distracted and in a much more vulnerable state."
North Korea's Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
27.4.24 Virus The Hacker News
The North Korea-linked threat actor known as Lazarus Group employed its time-tested fabricated job lures to deliver a new remote access trojan called Kaolin RAT as part of attacks targeting specific individuals in the Asia region in summer 2023.
The malware could, "aside from standard RAT functionality, change the last write timestamp of a selected file and load any received DLL binary from [command-and-control] server," Avast security researcher Luigino Camastra said in a report published last week.
The RAT acts as a pathway to deliver the FudModule rootkit, which has been recently observed leveraging a now-patched admin-to-kernel exploit in the appid.sys driver (CVE-2024-21338, CVSS score: 7.8) to obtain a kernel read/write primitive and ultimately disable security mechanisms.
The Lazarus Group's use of job offer lures to infiltrate targets is not new. Dubbed Operation Dream Job, the long-running campaign has a track record of using various social media and instant messaging platforms to deliver malware.
These initial access vectors trick targets into launching a malicious optical disc image (ISO) file bearing three files, one of which masquerades as an Amazon VNC client ("AmazonVNC.exe") that, in reality, is a renamed version of a legitimate Windows application called "choice.exe."
The two other files, named "version.dll" and "aws.cfg," act as a catalyst to kick-start the infection chain. Specifically, the executable "AmazonVNC.exe" is used to side-load "version.dll," which, in turn, spawns an IExpress.exe process and injects into it a payload residing within "aws.cfg."
The payload is designed to download shellcode from a command-and-control (C2) domain ("henraux[.]com"), which is suspected to be an actual-but-hacked website belonging to an Italian company that specializes in excavating and processing marble and granite.
While the exact nature of the shellcode is unclear, it's said to be used to launch RollFling, a DLL-based loader that serves to retrieve and launch the next-stage malware named RollSling, which was disclosed by Microsoft last year in connection with a Lazarus Group campaign exploiting a critical JetBrains TeamCity flaw (CVE-2023-42793, CVSS score: 9.8).
RollSling, executed directly in memory in a likely attempt to evade detection by security software, represents the next phase of the infection procedure. Its primary function is to trigger the execution of a third loader dubbed RollMid that's also run in the system's memory.

RollMid comes fitted with capabilities to set the stage for the attack and establish contact with a C2 server, which involves a three-step process of its own as follows -
Communicate with the first C2 server to fetch a HTML file containing the address of the second C2 server
Communicate with the second C2 server to fetch a PNG image that embeds a malicious component using a technique called steganography
Transmit data to the third C2 server using the address specified in the concealed data within the image
Retrieve an additional Base64-encoded data blob from the third C2 server, which is the Kaolin RAT
The technical sophistication behind the multi-stage sequence, while no doubt complex and intricate, borders on overkill, Avast opined, with the Kaolin RAT paving the way for the deployment of the FudModule rootkit after setting up communications with the RAT's C2 server.
On top of that, the malware is equipped to enumerate files; carry out file operations; upload files to the C2 server; alter a file's last modified timestamp; enumerate, create, and terminate processes; execute commands using cmd.exe; download DLL files from the C2 server; and connect to an arbitrary host.
"The Lazarus group targeted individuals through fabricated job offers and employed a sophisticated toolset to achieve better persistence while bypassing security products," Camastra said.
"It is evident that they invested significant resources in developing such a complex attack chain. What is certain is that Lazarus had to innovate continuously and allocate enormous resources to research various aspects of Windows mitigations and security products. Their ability to adapt and evolve poses a significant challenge to cybersecurity efforts."
eScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
25.4.24 Virus The Hacker News
A new malware campaign has been exploiting the updating mechanism of the eScan antivirus software to distribute backdoors and cryptocurrency miners like XMRig through a long-standing threat codenamed GuptiMiner targeting large corporate networks.
Cybersecurity firm Avast said the activity is the work of a threat actor with possible connections to a North Korean hacking group dubbed Kimsuky, which is also known as Black Banshee, Emerald Sleet, and TA427.
"GuptiMiner is a highly sophisticated threat that uses an interesting infection chain along with a couple of techniques that include performing DNS requests to the attacker's DNS servers, performing sideloading, extracting payloads from innocent-looking images, signing its payloads with a custom trusted root anchor certification authority, among others," Avast said.
The intricate and elaborate infection chain, at its core, leverages a security shortcoming in the update mechanism of Indian antivirus vendor eScan to propagate the malware by means of an adversary-in-the-middle (AitM) attack.
Specifically, it entails hijacking the updates by substituting the package file with a malicious version by taking advantage of the fact that the downloads were not signed and secured using HTTPS. The issue, which went unnoticed for at least five years, has been rectified as of July 31, 2023.
The rogue DLL ("updll62.dlz") executed by the eScan software side-loads a DLL ("version.dll") to activate a multi-stage sequence starting with a PNG file loader that, in turn, employs malicious DNS servers to contact a command-and-control (C2) server and fetch a PNG file with appended shellcode.
"GuptiMiner hosts their own DNS servers for serving true destination domain addresses of C&C servers via DNS TXT responses," researchers Jan Rubín and Milánek said.
"As the malware connects to the malicious DNS servers directly, the DNS protocol is completely separated from the DNS network. Thus, no legitimate DNS server will ever see the traffic from this malware."
The PNG file is then parsed to extract the shellcode, which is then responsible for executing a Gzip loader that's designed to decompress another shellcode using Gzip and execute it in a separate thread.
The third-stage malware, dubbed Puppeteer, pulls all the strings, ultimately deploying the XMRig cryptocurrency miner and backdoors on the infected systems.

Avast said it encountered two different types of backdoors that come fitted with features to enable lateral movement, accept commands from the threat actor, and deliver additional components as required.
"The first is an enhanced build of PuTTY Link, providing SMB scanning of the local network and enabling lateral movement over the network to potentially vulnerable Windows 7 and Windows Server 2008 systems on the network," the researchers explained.
"The second backdoor is multi-modular, accepting commands from the attacker to install more modules as well as focusing on scanning for stored private keys and crypto wallets on the local system."
The deployment of XMRig has been described as "unexpected" for what's otherwise a complex and meticulously executed operation, raising the possibility that the miner acts as a distraction to prevent victims from discovering the true extent of the compromise.
GuptiMiner, known to be active since at least 2018, also makes use of various techniques like anti-VM and anti-debug tricks, code virtualization, dropping the PNG loader during system shutdown events, storing payloads in Windows Registry, and adding a root certificate to Windows' certificate store to make the PNG loader DLLs appear trustworthy.
The links to Kimusky come from an information stealer that, while not distributed by GuptiMiner or via the infection flow, has been used "across the whole GuptiMiner campaign" and shares overlaps with a keylogger previously identified as utilized by the group.
It's currently not clear who the targets of the campaign are, but GuptiMiner artifacts have been uploaded to VirusTotal from India and Germany as early as April 2018, with Avast telemetry data highlighting new infections likely originating from out-of-date eScan clients.
The findings come as the Korean National Police Agency (KNPA) called out North Korean hacking crews such as Lazarus, Andariel, and Kimsuky for targeting the defense sector in the country and exfiltrating valuable data from some of them.
A report from the Korea Economic Daily said the threat actors penetrated the networks of 83 South Korean defense contractors and stole confidential information from about 10 of them from October 2022 to July 2023.
CoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
24.4.24 Virus The Hacker News

A new ongoing malware campaign has been observed distributing three different stealers, such as CryptBot, LummaC2, and Rhadamanthys hosted on Content Delivery Network (CDN) cache domains since at least February 2024.
Cisco Talos has attributed the activity with moderate confidence to a threat actor tracked as CoralRaider, a suspected Vietnamese-origin group that came to light earlier this month.
This assessment is based on "several overlaps in tactics, techniques, and procedures (TTPs) of CoralRaider's Rotbot campaign, including the initial attack vector of the Windows Shortcut file, intermediate PowerShell decryptor and payload download scripts, the FoDHelper technique used to bypass User Access Controls (UAC) of the victim machine," the company said.
Targets of the campaign span various business verticals across geographies, including the U.S., Nigeria, Pakistan, Ecuador, Germany, Egypt, the U.K., Poland, the Philippines, Norway, Japan, Syria, and Turkey.
Attack chains involve users downloading files masquerading as movie files via a web browser, raising the possibility of a large-scale attack.
"This threat actor is using a Content Delivery Network (CDN) cache to store the malicious files on their network edge host in this campaign, avoiding request delay," Talos researchers Joey Chen, Chetan Raghuprasad, and Alex Karkins said. "The actor is using the CDN cache as a download server to deceive network defenders."

The initial access vector for the drive-by downloads is suspected to be phishing emails, using them as a conduit to propagate booby-trapped links pointing to ZIP archives containing a Windows shortcut (LNK) file.
The shortcut file, in turn, runs a PowerShell script to fetch a next-stage HTML application (HTA) payload hosted on the CDN cache, which subsequently runs Javascript code to launch an embedded PowerShell loader that takes steps to fly under the radar and ultimately downloads and runs one of the three stealer malware.
The modular PowerShell loader script is designed to bypass the User Access Controls (UAC) in the victim's machine using a known technique called FodHelper, which has also been put to use by Vietnamese threat actors linked to another stealer known as NodeStealer that's capable of stealing Facebook account data.
The stealer malware, regardless of what's deployed, grabs victims' information, such as system and browser data, credentials, cryptocurrency wallets, and financial information.
What's notable about the campaign is that it utilizes an updated version of CryptBot that packs in new anti-analysis techniques and also captures password manager application databases and authenticator application information.
Hackers Target Middle East Governments with Evasive "CR4T" Backdoor
19.4.24 Virus The Hacker News
Government entities in the Middle East have been targeted as part of a previously undocumented campaign to deliver a new backdoor dubbed CR4T.
Russian cybersecurity company Kaspersky said it discovered the activity in February 2024, with evidence suggesting that it may have been active since at least a year prior. The campaign has been codenamed DuneQuixote.
"The group behind the campaign took steps to prevent collection and analysis of its implants and implemented practical and well-designed evasion methods both in network communications and in the malware code," Kaspersky said.
The starting point of the attack is a dropper, which comes in two variants -- a regular dropper that's either implemented as an executable or a DLL file and a tampered installer file for a legitimate tool named Total Commander.
Regardless of the method used, the primary function of the dropper is to extract an embedded command-and-control (C2) address that's decrypted using a novel technique to prevent the server address from being exposed to automated malware analysis tools.
Specifically, it entails obtaining the filename of the dropper and stringing it together with one of the many hard-coded snippets from Spanish poems present in the dropper code. The malware then calculates the MD5 hash of the combined string, which acts as the key to decode the C2 server address.
The dropper subsequently establishes connections with the C2 server and downloads a next-stage payload after providing a hard-coded ID as the User-Agent string in the HTTP request.
"The payload remains inaccessible for download unless the correct user agent is provided," Kaspersky said. "Furthermore, it appears that the payload may only be downloaded once per victim or is only available for a brief period following the release of a malware sample into the wild."
The trojanized Total Commander installer, on the other hand, carries a few differences despite retaining the main functionality of the original dropper.
It does away with the Spanish poem strings and implements additional anti-analysis checks that prevent a connection to the C2 server should the system have a debugger or a monitoring tool installed, the position of the cursor does not change after a certain time, the amount of RAM available is less than 8 GB, and the disk capacity is less than 40 GB.
CR4T ("CR4T.pdb") is a C/C++-based memory-only implant that grants attackers access to a console for command line execution on the infected machine, performs file operations, and uploads and downloads files after contacting the C2 server.
Kaspersky said it also unearthed a Golang version of CR4T with identical features, in addition to possessing the ability to execute arbitrary commands and create scheduled tasks using the Go-ole library.
On top of that, the Golang CR4T backdoor is equipped to achieve persistence by utilizing the COM objects hijacking technique and leverage the Telegram API for C2 communications.
The presence of the Golang variant is an indication that the unidentified threat actors behind DuneQuixote are actively refining their tradecraft with cross-platform malware.
"The 'DuneQuixote' campaign targets entities in the Middle East with an interesting array of tools designed for stealth and persistence," Kaspersky said.
"Through the deployment of memory-only implants and droppers masquerading as legitimate software, mimicking the Total Commander installer, the attackers demonstrate above average evasion capabilities and techniques."
OfflRouter Malware Evades Detection in Ukraine for Almost a Decade
19.4.24 Virus The Hacker News
Select Ukrainian government networks have remained infected with a malware called OfflRouter since 2015.
Cisco Talos said its findings are based on an analysis of over 100 confidential documents that were infected with the VBA macro virus and uploaded to the VirusTotal malware scanning platform since 2018. More than 20 such documents have been uploaded since 2022.
"The documents contained VBA code to drop and run an executable with the name 'ctrlpanel.exe,'" security researcher Vanja Svajcer said. "The virus is still active in Ukraine and is causing potentially confidential documents to be uploaded to publicly accessible document repositories."
A striking aspect of OfflRouter is its inability to spread via email, necessitating that it be propagated via other means, such as sharing documents and removable media, including USB memory sticks containing the infected documents.
"It would require manual user intervention to send an infected document as an email attachment," a Talos researcher told The Hacker News. "That could be the reason why the virus stayed under the radar for such a long time as it is not very noisy."
"We can only speculate as to why there is no automated spreading by email. That said, if the malware was attached to a document sent via email, the virus would still attempt to infect files located on removable media."
These design choices, intentional or otherwise, are said to have confined the spread of OfflRouter within Ukraine's borders and to a few organizations, thus escaping detection for almost 10 years.
It's currently not known who is responsible for the malware and there are no indications that it was developed by someone from Ukraine.
Whoever it is, they have been described as inventive yet inexperienced owing to the unusual propagation mechanism and the presence of several mistakes in the source code.
OfflRouter has been previously highlighted by MalwareHunterTeam as early as May 2018 and again by the Computer Security Incident Response Team Slovakia (CSIRT.SK) in August 2021, detailing infected documents uploaded to the National Police of Ukraine's website.
The modus operandi has remained virtually unchanged, with the VBA macro-embedded Microsoft Word documents dropping a .NET executable named "ctrlpanel.exe," which then infects all files with the .DOC (not .DOCX) extension found on the system and other removable media with the same macro.
"The infection iterates through a list of the document candidates to infect and uses an innovative method to check the document infection marker to avoid multiple infection processes – the function checks the document creation metadata, adds the creation times, and checks the value of the sum," Svajcer said.

"If the sum is zero, the document is considered already infected."
That said, the attack becomes successful only when VBA macros are enabled. Microsoft, as of July 2022, has been blocking macros by default in Office documents downloaded from the internet, prompting threat actors to seek other initial access pathways.
While Microsoft's preventive measure limits the success of such macro-based attacks, Cisco Talos told the publication that many organizations in the affected region, including government entities, are not using up-to-date Office versions.
"The main issue we tried to raise is not that a virus is active and affects Microsoft Office, but that users can unknowingly upload confidential documents to public repositories," it said. "Users need to double check for the malware infection."
Another key function of the malware is to make Windows Registry modifications so as to ensure that the executable runs every time upon booting the system.
"The virus targets only documents with the filename extension .DOC, the default extension for the OLE2 documents, and it will not try to infect other filename extensions," Svajcer said. "The default Word document filename extension for the more recent Word versions is .DOCX, so few documents will be infected as a result."
That's not all. Ctrlpanel.exe is also equipped to search for potential plugins (with the extension .ORP) present on removable drives and execute them on the machine, which implies the malware is expecting the plugins to be delivered via USB drives or CD-ROMs.
One the contrary, if the plugins are already present on a host, OfflRouter takes care of encoding them, copying the files to the root folder of the attached removable media with the filename extension .ORP, and manipulating them to make them hidden so that they are not visible through the File Explorer when plugging them into another device.
That said, one major unknown is whether the initial vector is a document or the executable module ctrlpanel.exe.
"The advantage of the two-module virus is that it can be spread as a standalone executable or as an infected document," Svajcer said.
"It may even be advantageous to initially spread as an executable as the module can run standalone and set the registry keys to allow execution of the VBA code and changing of the default saved file formats to .DOC before infecting documents. That way, the infection may be a bit stealthier."
Malicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
18.4.24 Virus The Hacker News
A new Google malvertising campaign is leveraging a cluster of domains mimicking a legitimate IP scanner software to deliver a previously unknown backdoor dubbed MadMxShell.
"The threat actor registered multiple look-alike domains using a typosquatting technique and leveraged Google Ads to push these domains to the top of search engine results targeting specific search keywords, thereby luring victims to visit these sites," Zscaler ThreatLabz researchers Roy Tay and Sudeep Singh said.
As many as 45 domains are said to have been registered between November 2023 and March 2024, with the sites masquerading as port scanning and IT management software such as Advanced IP Scanner, Angry IP Scanner, IP scanner PRTG, and ManageEngine.
While this is not the first time threat actors are banking on malvertising techniques to serve malware via lookalike sites, the development marks the first time the delivery vehicle is being used to propagate a sophisticated Windows backdoor.
Thus, users who end up searching for such tools are displayed bogus sites that include JavaScript code designed to download a malicious file ("Advanced-ip-scanner.zip") upon clicking the download button.
Present within the ZIP archive is a DLL file ("IVIEWERS.dll") and an executable ("Advanced-ip-scanner.exe"), the latter of which uses DLL side-loading to load the DLL and activate the infection sequence.
The DLL file is responsible for injecting the shellcode into the "Advanced-ip-scanner.exe" process via a technique called process hollowing, following which the injected EXE file unpacks two additional files – OneDrive.exe and Secur32.dll.
OneDrive.exe, a legitimate signed Microsoft binary, is then abused to sideload Secur32.dll, and ultimately execute the shellcode backdoor, but not before setting up persistence on the host by means of a scheduled task and disabling Microsoft Defender Antivirus.
The backdoor – so named for its use of DNS MX queries for command-and-control (C2) – is designed to gather system information, run commands via cmd.exe, and perform basic file manipulation operations such as reading, writing, and deleting files.

It sends requests to the C2 server ("litterbolo[.]com") by encoding the data in the subdomain(s) of the Fully Qualified Domain Name (FQDN) in a DNS mail exchange (MX) query packet and receives commands encoded within the response packet.
"The backdoor uses techniques such as multiple stages of DLL side-loading and DNS tunneling for command-and-control (C2) communication as a means to evade endpoint and network security solutions, respectively," Tay and Singh said.
"In addition, the backdoor uses evasive techniques like anti-dumping to prevent memory analysis and hinder forensics security solutions."
There is currently no indication of where the malware operators originate from or what their intentions are, but Zscaler said it identified two accounts created by them on criminal underground forums like blackhatworld[.]com and social-eng[.]ru using the email address wh8842480@gmail[.]com, which was also used to register a domain spoofing Advanced IP Scanner.
Specifically, the threat actor has been found engaging in posts offering ways to set up unlimited Google AdSense threshold accounts way back in June 2023, indicating their interest in launching their own long-lasting malvertising campaign.
"Google Ads threshold accounts and techniques for abusing them are often traded on BlackHat forums," the researchers said. "Many times they offer a way for the threat actor to add as many credits as possible to run Google Ads campaigns."
"This allows the threat actors to run campaigns without actually paying until the threshold limit. A reasonably high threshold limit lets the threat actor run the ad campaign for a significant amount of time."
TA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
16.4.24 Virus The Hacker News
The threat actor tracked as TA558 has been observed leveraging steganography as an obfuscation technique to deliver a wide range of malware such as Agent Tesla, FormBook, Remcos RAT, LokiBot, GuLoader, Snake Keylogger, and XWorm, among others.
"The group made extensive use of steganography by sending VBSs, PowerShell code, as well as RTF documents with an embedded exploit, inside images and text files," Russian cybersecurity company Positive Technologies said in a Monday report.
The campaign has been codenamed SteganoAmor for its reliance on steganography and the choice of file names such as greatloverstory.vbs and easytolove.vbs.
A majority of the attacks have targeted industrial, services, public, electric power, and construction sectors in Latin American countries, although companies located in Russia, Romania, and Turkey have also been singled out.
The development comes as TA558 has also been spotted deploying Venom RAT via phishing attacks aimed at enterprises located in Spain, Mexico, the United States, Colombia, Portugal, Brazil, Dominican Republic, and Argentina.
It all starts with a phishing email containing a booby-trapped email Microsoft Excel attachment that exploits a now-patched security flaw in Equation Editor (CVE-2017-11882) to download a Visual Basic Script that, in turn, fetches the next-stage payload from paste[.]ee.
The obfuscated malicious code takes care of downloading two images from an external URL that come embedded with a Base64-encoded component that ultimately retrieves and executes the Agent Tesla malware on the compromised host.

Beyond Agent Tesla, other variants of the attack chain have led to an assortment of malware such as FormBook, GuLoader, LokiBot, Remcos RAT, Snake Keylogger, and XWorm, which are designed for remote access, data theft, and delivery of secondary payloads.
The phishing emails are sent from legitimate-but-compromised SMTP servers to lend the messages a little credibility and minimize the chances of them getting blocked by email gateways. In addition, TA558 has been found to use infected FTP servers to stage the stolen data.
The disclosure comes against the backdrop of a series of phishing attacks targeting government organizations in Russia, Belarus, Kazakhstan, Uzbekistan, Kyrgyzstan, Tajikistan, and Armenia with a malware dubbed LazyStealer to harvest credentials from Google Chrome.
Positive Technologies is tracking the activity cluster under the name Lazy Koala in reference to the name of the user (joekoala), who is said to control the Telegram bots that receive the stolen data.
That said, the victim geography and the malware artifacts indicate potential links to another hacking group tracked by Cisco Talos under the name YoroTrooper (aka SturgeonPhisher).
"The group's main tool is a primitive stealer, whose protection helps to evade detection, slow down analysis, grab all the stolen data, and send it to Telegram, which has been gaining popularity with malicious actors by the year," security researcher Vladislav Lunin said.
The findings also follow a wave of social engineering campaigns that are designed to propagate malware families like FatalRAT and SolarMarker.
Hive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
16.4.24 Virus The Hacker News
Two individuals have been arrested in Australia and the U.S. in connection with an alleged scheme to develop and distribute a remote access trojan called Hive RAT (previously Firebird).
The U.S. Justice Department (DoJ) said the malware "gave the malware purchasers control over victim computers and enabled them to access victims' private communications, their login credentials, and other personal information."
A 24-year-old individual named Edmond Chakhmakhchyan (aka "Corruption") from Van Nuys in Los Angeles, California, was taken into custody after he was caught selling a license of Hive RAT to an undercover employee of a law enforcement agency.
He has been charged with one count of conspiracy and one count of advertising a device as an interception device, each of which carries a penalty of five years in prison. Chakhmakhchyan pleaded not guilty and was ordered to stand trial on June 4, 2024.
Court documents allege a partnership between the malware's creator and the defendant under which the latter would post advertisements for the malware on a cybercrime forum called Hack Forums, accept cryptocurrency payments from customers, and offer product support.
Hive RAT comes with capabilities to terminate programs, browse files, record keystrokes, access incoming and outgoing communications, and steal victim passwords and other credentials for bank accounts and cryptocurrency wallets from victims' machines without their knowledge or consent.
"Chakhmakhchyan exchanged electronic messages with purchasers and explained to one buyer that the malware 'allowed the Hive RAT user to access another person's computer without that person knowing about the access,'" the DoJ said.
The Australian Federal Police (AFP), which announced charges of its own against a citizen for their purported involvement in the creation and sale of Hive RAT, said its investigation into the matter began in 2020.
The unnamed suspect faces 12 charges, including one count of producing data with intent to commit a computer offense, one count of controlling data with intent to commit a computer offense, and 10 counts of supplying data with intent to commit a computer offense. The maximum penalty for each of these offenses is three years imprisonment.
"Remote Access Trojans are one of the most harmful cyber threats in the online environment – once installed onto a device, a RAT can provide criminals with full access to, and control of the device," AFP Acting Commander Cybercrime Sue Evans said.
"This could include anything from committing crimes anonymously, watching victims through camera devices, wiping hard drives, or stealing banking credentials and other sensitive information."
Nebraska Man Indicted in Cryptojacking Scheme#
The development comes as federal prosecutors in the U.S. indicted Charles O. Parks III (aka "CP3O"), 45, for operating a massive illegal cryptojacking operation, defrauding "two well-known providers of cloud computing services" out of more than $3.5 million in computing resources to mine cryptocurrency worth nearly $1 million.
The indictment charges the Parks with wire fraud, money laundering, and engaging in unlawful monetary transactions. He was arrested on April 13, 2024. The wire fraud and money laundering charges carry a maximum sentence of 20 years' imprisonment. He also faces a 10 years' imprisonment on the unlawful monetary transactions charges.
While the DoJ does not explicitly state what cloud providers were targeted in the fraudulent operation, it noted that the companies are based in the Washington state cities of Seattle and Redmond – the corporate headquarters for Amazon and Microsoft.
"From in or about January 2021 through August 2021, Parks created and used a variety of names, corporate affiliations and email addresses, including emails with domains from corporate entities he operated [...] to register numerous accounts with the cloud providers and to gain access to massive amounts of computing processing power and storage that he did not pay for," the DoJ said.
The illicitly obtained resources were then used to mine cryptocurrencies such as Ether (ETH), Litecoin (LTC) and Monero (XMR), which were laundered through a network of cryptocurrency exchanges, a non-fungible token (NFT) marketplace, an online payment provider, and traditional bank accounts to conceal digital transaction trail.
The ill-gotten proceeds, prosecutors said, were ultimately converted into dollars, which Parks used to make various extravagant purchases that included a Mercedes Benz luxury car, jewelry, and first-class hotel and travel expenses.
"Parks tricked the providers into approving heightened privileges and benefits, including elevated levels of cloud computing services and deferred billing accommodations, and deflected inquiries from the providers regarding questionable data usage and mounting unpaid subscription balances," the DoJ said.
Hackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
13.4.24 Virus The Hacker News
Threat actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software dating back to March 26, 2024, nearly three weeks before it came to light yesterday.
The network security company's Unit 42 division is tracking the activity under the name Operation MidnightEclipse, attributing it as the work of a single threat actor of unknown provenance.
The security vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), is a command injection flaw that enables unauthenticated attackers to execute arbitrary code with root privileges on the firewall.
It's worth noting that the issue is applicable only to PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 firewall configurations that have GlobalProtect gateway and device telemetry enabled.
Operation MidnightEclipse entails the exploitation of the flaw to create a cron job that runs every minute to fetch commands hosted on an external server ("172.233.228[.]93/policy" or "172.233.228[.]93/patch"), which are then executed using the bash shell.
The attackers are said to have manually managed an access control list (ACL) for the command-and-control (C2) server to ensure that it can only be accessed from the device communicating with it.
While the exact nature of the command is unknown, it's suspected that the URL serves as a delivery vehicle for a Python-based backdoor on the firewall that Volexity – which discovered in-the-wild exploitation of CVE-2024-3400 on April 10, 2024 – is tracking as UPSTYLE and is hosted on a different server ("144.172.79[.]92" and "nhdata.s3-us-west-2.amazonaws[.]com").
The Python file is designed to write and launch another Python script ("system.pth"), which subsequently decodes and runs the embedded backdoor component that's responsible for executing the threat actor's commands in a file called "sslvpn_ngx_error.log." The results of the operation are written to a separate file named "bootstrap.min.css."
The most interesting aspect of the attack chain is that both the files used to extract the commands and write the results are legitimate files associated with the firewall -
/var/log/pan/sslvpn_ngx_error.log
/var/appweb/sslvpndocs/global-protect/portal/css/bootstrap.min.css
As for how the commands are written to the web server error log, the threat actor forges specially crafted network requests to a non-existent web page containing a specific pattern. The backdoor then parses the log file and searches for the line matching the same regular expression ("img\[([a-zA-Z0-9+/=]+)\]") to decode and run the command within it.
"The script will then create another thread that runs a function called restore," Unit 42 said. "The restore function takes the original content of the bootstrap.min.css file, as well as the original access and modified times, sleeps for 15 seconds and writes the original contents back to the file and sets the access and modified times to their originals."

The main goal appears to be to avoid leaving traces of the command outputs, necessitating that the results are exfiltrated within 15 seconds before the file is overwritten.
Volexity, in its own analysis, said it observed the threat actor remotely exploiting the firewall to create a reverse shell, download additional tooling, pivot into internal networks, and ultimately exfiltrate data. The exact scale of the campaign is presently unclear. The adversary has been assigned the moniker UTA0218 by the company.
"The tradecraft and speed employed by the attacker suggests a highly capable threat actor with a clear playbook of what to access to further their objectives," the American cybersecurity firm said.
"UTA0218's initial objectives were aimed at grabbing the domain backup DPAPI keys and targeting active directory credentials by obtaining the NTDS.DIT file. They further targeted user workstations to steal saved cookies and login data, along with the users' DPAPI keys."
Organizations are recommended to look for signs of lateral movement internally from their Palo Alto Networks GlobalProtect firewall device.
The development has also prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to add the flaw to its Known Exploited Vulnerabilities (KEV) catalog, requiring federal agencies to apply the patches by April 19 to mitigate potential threats. Palo Alto Networks is expected to release fixes for the flaw no later than April 14.
"Targeting edge devices remains a popular vector of attack for capable threat actors who have the time and resources to invest into researching new vulnerabilities," Volexity said.
"It is highly likely UTA0218 is a state-backed threat actor based on the resources required to develop and exploit a vulnerability of this nature, the type of victims targeted by this actor, and the capabilities displayed to install the Python backdoor and further access victim networks."
Popular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
13.4.24 Virus The Hacker News
"Test files" associated with the XZ Utils backdoor have made their way to a Rust crate known as liblzma-sys, new findings from Phylum reveal.
liblzma-sys, which has been downloaded over 21,000 times to date, provides Rust developers with bindings to the liblzma implementation, an underlying library that is part of the XZ Utils data compression software. The impacted version in question is 0.3.2.
"The current distribution (v0.3.2) on Crates.io contains the test files for XZ that contain the backdoor," Phylum noted in a GitHub issue raised on April 9, 2024.
"The test files themselves are not included in either the .tar.gz nor the .zip tags here on GitHub and are only present in liblzma-sys_0.3.2.crate that is installed from Crates.io."
Following responsible disclosure, the files in question ("tests/files/bad-3-corrupt_lzma2.xz" and "tests/files/good-large_compressed.lzma") have since been removed from liblzma-sys version 0.3.3 released on April 10. The previous version of the crate has been pulled from the registry.
"The malicious tests files were committed upstream, but due to the malicious build instructions not being present in the upstream repository, they were never called or executed," Snyk said in an advisory of its own.
The backdoor in XZ Utils was discovered in late March when Microsoft engineer Andres Freund identified malicious commits to the command-line utility impacting versions 5.6.0 and 5.6.1 released in February and March 2024, respectively. The popular package is integrated into many Linux distributions.

The code commits, made by a now-suspended GitHub user named JiaT75 (aka Jia Tan), essentially made it possible to circumvent authentication controls within SSH to execute code remotely, potentially allowing the operators to take over the system.
"The overall compromise spanned over two years," SentinelOne researchers Sarthak Misraa and Antonio Pirozzi said in an analysis published this week. "Under the alias Jia Tan, the actor began contributing to the xz project on October 29, 2021."
"Initially, the commits were innocuous and minor. However, the actor gradually became a more active contributor to the project, steadily gaining reputation and trust within the community."
According to Russian cybersecurity company Kaspersky, the trojanized changes take the form of a multi-stage operation.
"The source code of the build infrastructure that generated the final packages was slightly modified (by introducing an additional file build-to-host.m4) to extract the next stage script that was hidden in a test case file (bad-3-corrupt_lzma2.xz)," it said.

"These scripts in turn extracted a malicious binary component from another test case file (good-large_compressed.lzma) that was linked with the legitimate library during the compilation process to be shipped to Linux repositories."
The payload, a shell script, is responsible for the extraction and the execution of the backdoor, which, in turn, hooks into specific functions – RSA_public_decrypt, EVP_PKEY_set1_RSA, and RSA_get0_key – that will allow it to monitor every SSH connection to the infected machine.
The primary goal of the backdoor slipped into liblzma is to manipulate Secure Shell Daemon (sshd) and monitor for commands sent by an attacker at the start of an SSH session, effectively introducing a way to achieve remote code execution.
While the early discovery of the backdoor averted what could have been a widespread compromise of the Linux ecosystem, the development is once again a sign that open-source package maintainers are being targeted by social engineering campaigns with the goal of staging software supply chain attacks.
In this case, it materialized in the form of a coordinated activity that presumably featured several sockpuppet accounts that orchestrated a pressure campaign aimed at forcing the project's longtime maintainer to bring on board a co-maintainer to add more features and address issues.
"The flurry of open source code contributions and related pressure campaigns from previously unknown developer accounts suggests that a coordinated social engineering campaign using phony developer accounts was used to sneak malicious code into a widely used open-source project," ReversingLabs said.
SentinelOne researchers revealed that the subtle code changes made by JiaT75 between versions 5.6.0 and 5.6.1 suggest that the modifications were engineered to enhance the backdoor's modularity and plant more malware.
As of April 9, 2024, the source code repository associated with XZ Utils has been restored on GitHub, nearly two weeks after it was disabled for a violation of the company's terms of service.
The attribution of the operation and the intended targets are currently unknown, although in light of the planning and sophistication behind it, the threat actor is suspected to be a state-sponsored entity.
"It's evident that this backdoor is highly complex and employs sophisticated methods to evade detection," Kaspersky said.
Raspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
11.4.24 Virus The Hacker News
Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March 2024.
"Historically, Raspberry Robin was known to spread through removable media like USB drives, but over time its distributors have experimented with other initial infection vectors," HP Wolf Security researcher Patrick Schläpfer said in a report shared with The Hacker News.
Raspberry Robin, also called QNAP worm, was first spotted in September 2021 that has since evolved into a downloader for various other payloads in recent years, such as SocGholish, Cobalt Strike, IcedID, BumbleBee, and TrueBot, and also serving as a precursor for ransomware.
While the malware was initially distributed by means of USB devices containing LNK files that retrieved the payload from a compromised QNAP device, it has since adopted other methods such as social engineering and malvertising.
It's attributed to an emerging threat cluster tracked by Microsoft as Storm-0856, which has links to the broader cybercrime ecosystem comprising groups like Evil Corp, Silence, and TA505.
The latest distribution vector entails the use of WSF files that are offered for download via various domains and subdomains.
It's currently not clear how the attackers are directing victims to these URLs, although it's suspected that it could be either via spam or malvertising campaigns.
The heavily obfuscated WSF file functions as a downloader to retrieve the main DLL payload from a remote server using the curl command, but not before a series of anti-analysis and anti-virtual machine evaluations are carried out to determine if it's being run in a virtualized environment.
It's also designed to terminate the execution if the build number of the Windows operating system is lower than 17063 (which was released in December 2017) and if the list of running processes includes antivirus processes associated with Avast, Avira, Bitdefender, Check Point, ESET, and Kaspersky.
What's more, it configures Microsoft Defender Antivirus exclusion rules in an effort to sidestep detection by adding the entire main drive to the exclusion list and preventing it from being scanned.
"The scripts itself are currently not classified as malicious by any an-virus scanners on VirusTotal, demonstrating the evasiveness of the malware and the risk of it causing a serious infection with Raspberry Robin," HP said.
"The WSF downloader is heavily obfuscated and uses many an-analysis techniques enabling the malware to evade detection and slow down analysis."
Attackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
9.4.24 Virus The Hacker News
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as Venom RAT, Remcos RAT, XWorm, NanoCore RAT, and a stealer that targets crypto wallets.
The email messages come with Scalable Vector Graphics (SVG) file attachments that, when clicked, activate the infection sequence, Fortinet FortiGuard Labs said in a technical report.
The modus operandi is notable for the use of the BatCloak malware obfuscation engine and ScrubCrypt to deliver the malware in the form of obfuscated batch scripts.
BatCloak, offered for sale to other threat actors since late 2022, has its foundations in another tool called Jlaive. Its primary feature is to load a next-stage payload in a manner that circumvents traditional detection mechanisms.
ScrubCrypt, a crypter that was first documented by Fortinet in March 2023 in connection with a cryptojacking campaign orchestrated by the 8220 Gang, is assessed to be one of the iterations of BatCloak, according to research from Trend Micro last year.
In the latest campaign analyzed by the cybersecurity firm, the SVG file serves as a conduit to drop a ZIP archive that contains a batch script likely created using BatCloak, which then unpacks the ScrubCrypt batch file to ultimately execute Venom RAT, but not before setting up persistence on the host and taking steps to bypass AMSI and ETW protections.

A fork of Quasar RAT, Venom RAT allows attackers to seize control of the compromised systems, gather sensitive information, and execute commands received from a command-and-control (C2) server.
"While Venom RAT's primary program may appear straightforward, it maintains communication channels with the C2 server to acquire additional plugins for various activities," security researcher Cara Lin said. This includes Venom RAT v6.0.3 with keylogger capabilities, NanoCore RAT, XWorm, and Remcos RAT.
"This [Remcos RAT] plugin was distributed from VenomRAT's C2 using three methods: an obfuscated VBS script named 'remcos.vbs,' ScrubCrypt, and Guloader PowerShell," Lin added.
Also delivered using the plugin system is a stealer that gathers information about the system and exfiltrates data from folders associated with wallets and applications like Atomic Wallet, Electrum, Ethereum, Exodus, Jaxx Liberty (retired as of March 2023), Zcash, Foxmail, and Telegram to a remote server.
"This analysis reveals a sophisticated attack leveraging multiple layers of obfuscation and evasion techniques to distribute and execute VenomRAT via ScrubCrypt," Lin said.
"The attackers employ a variety of methods, including phishing emails with malicious attachments, obfuscated script files, and Guloader PowerShell, to infiltrate and compromise victim systems. Furthermore, deploying plugins through different payloads highlights the versatility and adaptability of the attack campaign."
Watch Out for 'Latrodectus' - This Malware Could Be In Your Inbox
8.4.24 Virus The Hacker News
Threat hunters have discovered a new malware called Latrodectus that has been distributed as part of email phishing campaigns since at least late November 2023.
"Latrodectus is an up-and-coming downloader with various sandbox evasion functionality," researchers from Proofpoint and Team Cymru said in a joint analysis published last week, adding it's designed to retrieve payloads and execute arbitrary commands.
There is evidence to suggest that the malware is likely written by the same threat actors behind the IcedID malware, with the downloader put to use by initial access brokers (IABs) to facilitate the deployment of other malware.
Latrodectus has been primarily linked to two different IABs tracked by Proofpoint under the names TA577 (aka Water Curupira) and TA578, the former of which has also been linked to the distribution of QakBot and PikaBot.
As of mid-January 2024, it's been employed almost exclusively by TA578 in email threat campaigns, in some cases delivered via a DanaBot infection.
TA578, known to be active since at least May 2020, has been linked to email-based campaigns delivering Ursnif, IcedID, KPOT Stealer, Buer Loader, BazaLoader, Cobalt Strike, and Bumblebee.
Attack chains leverage contact forms on websites to send legal threats regarding alleged copyright infringement to targeted organizations. The links embedded in the messages direct the recipients to a bogus website to trick them into downloading a JavaScript file that's responsible for launching the main payload using msiexec.
"Latrodectus will post encrypted system information to the command-and-control server (C2) and request the download of the bot," the researchers said. "Once the bot registers with the C2, it sends requests for commands from the C2."

It also comes with capabilities to detect if it's running in a sandboxed environment by checking if the host has a valid MAC address and there are at least 75 running processes on systems running Windows 10 or newer.
Like in the case of IcedID, Latrodectus is designed to send the registration information in a POST request to the C2 server where the fields are HTTP parameters stringed together and encrypted, after which it awaits further instructions from the server.
The commands allow the malware to enumerate files and processes, execute binaries and DLL files, run arbitrary directives via cmd.exe, update the bot, and even shut down a running process.
A further examination of the attacker infrastructure reveals that the first C2 servers came alive on September 18, 2023. These servers, in turn, are configured to communicate with an upstream Tier 2 server that was set up around August 2023.
Latrodectus' connections to IcedID stems from the fact that the T2 server "maintains connections with backend infrastructure associated with IcedID" and use of jump boxes previously associated with IcedID operations.
"Latrodectus will become increasingly used by financially motivated threat actors across the criminal landscape, particularly those who previously distributed IcedID," Team Cymru assessed.
Mispadu Trojan Targets Europe, Thousands of Credentials Compromised
3.4.24 Virus The Hacker News

The banking trojan known as Mispadu has expanded its focus beyond Latin America (LATAM) and Spanish-speaking individuals to target users in Italy, Poland, and Sweden.
Targets of the ongoing campaign include entities spanning finance, services, motor vehicle manufacturing, law firms, and commercial facilities, according to Morphisec.
"Despite the geographic expansion, Mexico remains the primary target," security researcher Arnold Osipov said in a report published last week.
"The campaign has resulted in thousands of stolen credentials, with records dating back to April 2023. The threat actor leverages these credentials to orchestrate malicious phishing emails, posing a significant threat to recipients."
Mispadu, also called URSA, came to light in 2019, when it was observed carrying out credential theft activities aimed at financial institutions in Brazil and Mexico by displaying fake pop-up windows. The Delphi-based malware is also capable of taking screenshots and capturing keystrokes.
Typically distributed via spam emails, recent attack chains have leveraged a now-patched Windows SmartScreen security bypass flaw (CVE-2023-36025, CVSS score: 8.8) to compromise users in Mexico.
The infection sequence analyzed by Morphisec is a multi-stage process that commences with a PDF attachment present in invoice-themed emails that, when opened, prompts the recipient to click on a booby-trapped link to download the complete invoice, resulting in the download of a ZIP archive.
The ZIP comes with either an MSI installer or an HTA script that's responsible for retrieving and executing a Visual Basic Script (VBScript) from a remote server, which, in turn, downloads a second VBScript that ultimately downloads and launches the Mispadu payload using an AutoIT script but after it's decrypted and injected into memory by means of a loader.
"This [second] script is heavily obfuscated and employs the same decryption algorithm as mentioned in the DLL," Osipov said.
"Before downloading and invoking the next stage, the script conducts several Anti-VM checks, including querying the computer's model, manufacturer, and BIOS version, and comparing them to those associated with virtual machines."
The Mispadu attacks are also characterized by the use of two distinct command-and-control (C2) servers, one for fetching the intermediate and final-stage payloads and another for exfiltrating the stolen credentials from over 200 services. There are currently more than 60,000 files in the server.
The development comes as the DFIR Report detailed a February 2023 intrusion that entailed the abuse of malicious Microsoft OneNote files to drop IcedID, using it to drop Cobalt Strike, AnyDesk, and the Nokoyawa ransomware.
Microsoft, exactly a year ago, announced that it would start blocking 120 extensions embedded within OneNote files to prevent its abuse for malware delivery.
YouTube Videos for Game Cracks Serve Malware#
The findings also come as enterprise security firm Proofpoint said several YouTube channels promoting cracked and pirated video games are acting as a conduit to deliver information stealers such as Lumma Stealer, Stealc, and Vidar by adding malicious links to video descriptions.
"The videos purport to show an end user how to do things like download software or upgrade video games for free, but the link in the video descriptions leads to malware," security researcher Isaac Shaughnessy said in an analysis published today.
There is evidence to suggest that such videos are posted from compromised accounts, but there is also the possibility that the threat actors behind the operation have created short-lived accounts for dissemination purposes.
All the videos include Discord and MediaFire URLs that point to password-protected archives that ultimately lead to the deployment of the stealer malware.
Proofpoint said it identified multiple distinct activity clusters propagating stealers via YouTube with an aim to single out non-enterprise users. The campaign has not been attributed to a single threat actor or group.
"The techniques used are similar, however, including the use of video descriptions to host URLs leading to malicious payloads and providing instructions on disabling antivirus, and using similar file sizes with bloating to attempt to bypass detections," Shaughnessy said.
Malicious Code in XZ Utils for Linux Systems Enables Remote Code Execution
2.4.24 Virus The Hacker News
The malicious code inserted into the open-source library XZ Utils, a widely used package present in major Linux distributions, is also capable of facilitating remote code execution, a new analysis has revealed.
The audacious supply chain compromise, tracked as CVE-2024-3094 (CVSS score: 10.0), came to light last week when Microsoft engineer and PostgreSQL developer Andres Freund alerted to the presence of a backdoor in the data compression utility that gives remote attackers a way to sidestep secure shell authentication and gain complete access to an affected system.
XZ Utils is a command-line tool for compressing and decompressing data in Linux and other Unix-like operating systems.
The malicious code is said to have been deliberately introduced by one of the project maintainers named Jia Tan (aka Jia Cheong Tan or JiaT75) in what appears to be a meticulous attack spanning multiple years. The GitHub user account was created in 2021. The identity of the actor(s) is presently unknown.
"The threat actor started contributing to the XZ project almost two years ago, slowly building credibility until they were given maintainer responsibilities," Akamai said in a report.
In a further act of clever social engineering, sockpuppet accounts like Jigar Kumar and Dennis Ens are believed to have been used to send feature requests and report a variety of issues in the software in order to force the original maintainer – Lasse Collin of the Tukaani Project – to add a new co-maintainer to the repository.
Enter Jia Tan, who introduced a series of changes to XZ Utils in 2023, which eventually made their way to release version 5.6.0 in February 2024. They also harbored a sophisticated backdoor.

Source: Thomas Roccia
"As I have hinted in earlier emails, Jia Tan may have a bigger role in the project in the future," Collin said in an exchange with Kumar in June 2022.
"He has been helping a lot off-list and is practically a co-maintainer already. :-) I know that not much has happened in the git repository yet but things happen in small steps. In any case some change in maintainership is already in progress at least for XZ Utils."
The backdoor affects XZ Utils 5.6.0 and 5.6.1 release tarballs, the latter of which contains an improved version of the same implant. Collins has since acknowledged the project's breach, stating both the tarballs were created and signed by Jia Tan and that they had access only to the now-disabled GitHub repository.
"This is clearly a very complex state-sponsored operation with impressive sophistication and multi-year planning," firmware security company Binarly said. "Such a complex and professionally designed comprehensive implantation framework is not developed for a one-shot operation."

A deeper examination of the backdoor by open-source cryptographer Filippo Valsorda has also revealed that the affected versions allow specific remote attackers to send arbitrary payloads through an SSH certificate which will be executed in a manner that circumvents authentication protocols, effectively seizing control over the victim machine.
"It appears as though the backdoor is added to the SSH daemon on the vulnerable machine, enabling a remote attacker to execute arbitrary code," Akamai said. "This means that any machine with the vulnerable package that exposes SSH to the internet is potentially vulnerable."
Needless to say, the accidental discovery by Freund is one of the most significant supply chain attacks discovered to date and could have been a severe security disaster had the package been integrated into stable releases of Linux distributions.
"The most notable part of this supply chain attack is the extreme levels of dedication of the attacker, working more than two years to establish themselves as a legitimate maintainer, offering to pick up work in various OSS projects and committing code across multiple projects in order to avoid detection," JFrog said.
As with the case of Apache Log4j, the incident once again highlights the reliance on open-source software and volunteer-run projects, and the consequences that could entail should they suffer a compromise or have a major vulnerability.
"The bigger 'fix' is for organizations to adopt tools and processes that allow them to identify signs of tampering and malicious features within both open source and commercial code used in their own development pipeline," ReversingLabs said.
Massive Phishing Campaign Strikes Latin America: Venom RAT Targeting Multiple Sectors
2.4.24 Virus The Hacker News

The threat actor known as TA558 has been attributed to a new massive phishing campaign that targets a wide range of sectors in Latin America with the goal of deploying Venom RAT.
The attacks primarily singled out hotel, travel, trading, financial, manufacturing, industrial, and government verticals in Spain, Mexico, United States, Colombia, Portugal, Brazil, Dominican Republic, and Argentina.
Active since at least 2018, TA558 has a history of targeting entities in the LATAM region to deliver a variety of malware such as Loda RAT, Vjw0rm, and Revenge RAT.
The latest infection chain, according to Perception Point researcher Idan Tarab, leverages phishing emails as an initial access vector to drop Venom RAT, a fork of Quasar RAT that comes with capabilities to harvest sensitive data and commandeer systems remotely.
The disclosure comes as threat actors have been increasingly observed using the DarkGate malware loader following the law enforcement takedown of QakBot last year to target financial institutions in Europe and the U.S.
"Ransomware groups utilize DarkGate to create an initial foothold and to deploy various types of malware in corporate networks," EclecticIQ researcher Arda Büyükkaya noted.
"These include, but are not limited to, info-stealers, ransomware, and remote management tools. The objective of these threat actors is to increase the number of infected devices and the volume of data exfiltrated from a victim."

It also follows the emergence of malvertising campaigns designed to deliver malware like FakeUpdates (aka SocGholish), Nitrogen, and Rhadamanthys.
Earlier this month, Israeli ad security company GeoEdge revealed that a notorious malvertising group tracked as ScamClub "has shifted its focus towards video malvertising assaults, resulting in a surge in VAST-forced redirect volumes since February 11, 2024."
The attacks entail the malicious use of Video Ad Serving Templates (VAST) tags – which are used for video advertising – to redirect unsuspecting users to fraudulent or scam pages but only upon successful passage of certain client-side and server-side fingerprinting techniques.
A majority of the victims are located in the U.S. (60.5%), followed by Canada (7.2%), the U.K. (4.8%), Germany (2.1%), and Malaysia (1.7%), among others.
Hackers Target macOS Users with Malicious Ads Spreading Stealer Malware
31.3.24 Virus The Hacker News
Malicious ads and bogus websites are acting as a conduit to deliver two different stealer malware, including Atomic Stealer, targeting Apple macOS users.
The ongoing infostealer attacks targeting macOS users may have adopted different methods to compromise victims' Macs, but operate with the end goal of stealing sensitive data, Jamf Threat Labs said in a report published Friday.
One such attack chain targets users searching for Arc Browser on search engines like Google to serve bogus ads that redirect users to look-alike sites ("airci[.]net") that serve the malware.
"Interestingly, the malicious website cannot be accessed directly, as it returns an error," security researchers Jaron Bradley, Ferdous Saljooki, and Maggie Zirnhelt said. "It can only be accessed through a generated sponsored link, presumably to evade detection."
The disk image file downloaded from the counterfeit website ("ArcSetup.dmg") delivers Atomic Stealer, which is known to request users to enter their system passwords via a fake prompt and ultimately facilitate information theft.
Jamf said it also discovered a phony website called meethub[.]gg that claims to offer a free group meeting scheduling software, but actually installs another stealer malware capable of harvesting users' keychain data, stored credentials in web browsers, and information from cryptocurrency wallets.
Much like Atomic stealer, the malware – which is said to overlap with a Rust-based stealer family known as Realst – also prompts the user for their macOS login password using an AppleScript call to carry out its malicious actions.
Attacks leveraging this malware are said to have approached victims under the pretext of discussing job opportunities and interviewing them for a podcast, subsequently asking them to download an app from meethub[.]gg to join a video conference provided in the meeting invites.
"These attacks are often focused on those in the crypto industry as such efforts can lead to large payouts for attackers," the researchers said. "Those in the industry should be hyper-aware that it's often easy to find public information that they are asset holders or can easily be tied to a company that puts them in this industry."
The development comes as MacPaw's cybersecurity division Moonlock Lab disclosed that malicious DMG files ("App_v1.0.4.dmg") are being used by threat actors to deploy a stealer malware designed to extract credentials and data from various applications.
This is accomplished by means of an obfuscated AppleScript and bash payload that's retrieved from a Russian IP address, the former of which is used to launch a deceptive prompt (as mentioned above) to trick users into providing the system passwords.
"Disguised as a harmless DMG file, it tricks the user into installation via a phishing image, persuading the user to bypass macOS's Gatekeeper security feature," security researcher Mykhailo Hrebeniuk said.
The development is an indication that macOS environments are increasingly under threat from stealer attacks, with some strains even boasting of sophisticated anti-virtualization techniques by activating a self-destructing kill switch to evade detection.
In recent weeks, malvertising campaigns have also been observed pushing the FakeBat loader (aka EugenLoader) and other information stealers like Rhadamanthys via a Go-based loader through decoy sites for popular software such as Notion and PuTTY.
Urgent: Secret Backdoor Found in XZ Utils Library, Impacts Major Linux Distros
30.3.24 Virus The Hacker News
RedHat on Friday released an "urgent security alert" warning that two versions of a popular data compression library called XZ Utils (previously LZMA Utils) have been backdoored with malicious code designed to allow unauthorized remote access.
The software supply chain compromise, tracked as CVE-2024-3094, has a CVSS score of 10.0, indicating maximum severity. It impacts XZ Utils versions 5.6.0 (released February 24) and 5.6.1 (released March 9).
"Through a series of complex obfuscations, the liblzma build process extracts a prebuilt object file from a disguised test file existing in the source code, which is then used to modify specific functions in the liblzma code," the IBM subsidiary said in an advisory.
"This results in a modified liblzma library that can be used by any software linked against this library, intercepting and modifying the data interaction with this library."
Specifically, the nefarious code baked into the code is designed to interfere with the sshd daemon process for SSH (Secure Shell) via the systemd software suite, and potentially enable a threat actor to break sshd authentication and gain unauthorized access to the system remotely "under the right circumstances."
Microsoft security researcher Andres Freund has been credited with discovering and reporting the issue on Friday. The heavily obfuscated malicious code is said to have been introduced over a series of four commits to the Tukaani Project on GitHub by a user named JiaT75.

"Given the activity over several weeks, the committer is either directly involved or there was some quite severe compromise of their system," Freund said. "Unfortunately the latter looks like the less likely explanation, given they communicated on various lists about the 'fixes.'"
Microsoft-owned GitHub has since disabled the XZ Utils repository maintained by the Tukaani Project "due to a violation of GitHub's terms of service." There are currently no reports of active exploitation in the wild.
Evidence shows that the packages are only present in Fedora 41 and Fedora Rawhide, and do not impact Red Hat Enterprise Linux (RHEL), Debian Stable, Amazon Linux, and SUSE Linux Enterprise and Leap.
Out of an abundance of caution, Fedora Linux 40 users have been recommended to downgrade to a 5.4 build. Some of the other Linux distributions impacted by the supply chain attack are below -
Kali Linux (between March 26 and 29)
openSUSE Tumbleweed and openSUSE MicroOS (between March 7 and 28)
Debian testing, unstable, and experimental versions (from 5.5.1alpha-0.1 to 5.6.1-1)
The development has prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to issue an alert of its own, urging users to downgrade XZ Utils to an uncompromised version (e.g., XZ Utils 5.4.6 Stable).
Linux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
29.3.24 Virus The Hacker News
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new findings from Kaspersky reveal.
DinodasRAT, also known as XDealer, is a C++-based malware that offers the ability to harvest a wide range of sensitive data from compromised hosts.
In October 2023, Slovak cybersecurity firm ESET revealed that a governmental entity in Guyana has been targeted as part of a cyber espionage campaign dubbed Operation Jacana to deploy the Windows version of the implant.
Then last week, Trend Micro detailed a threat activity cluster it tracks as Earth Krahang and which has shifted to using DinodasRAT since 2023 in its attacks aimed at several government entities worldwide.
The use of DinodasRAT has been attributed to various China-nexus threat actors, including LuoYu, once again reflecting the tool sharing prevalent among hacking crews identified as acting on behalf of the country.

Kaspersky said it discovered a Linux version of the malware (V10) in early October 2023. Evidence gathered so far shows that the first known variant (V7) dates back to 2021.
It's mainly designed to target Red Hat-based distributions and Ubuntu Linux. Upon execution, it establishes persistence on the host by using SystemV or SystemD startup scripts and periodically contacts a remote server over TCP or UDP to fetch the commands to be run.
DinodasRAT is equipped to perform file operations, change command-and-control (C2) addresses, enumerate and terminate running processes, execute shell commands, download a new version of the backdoor, and even uninstall itself.
It also takes steps to evade detection by debugging and monitoring tools, and like its Windows counterpart, utilizes the Tiny Encryption Algorithm (TEA) to encrypt C2 communications.
"DinodasRAT's primary use case is to gain and maintain access via Linux servers rather than reconnaissance," Kaspersky said. "The backdoor is fully functional, granting the operator complete control over the infected machine, enabling data exfiltration and espionage."
Russian Hackers Use 'WINELOADER' Malware to Target German Political Parties
23.3.24 Virus The Hacker News
The WINELOADER backdoor used in recent cyber attacks targeting diplomatic entities with wine-tasting phishing lures has been attributed as the handiwork of a hacking group with links to Russia's Foreign Intelligence Service (SVR), which was responsible for breaching SolarWinds and Microsoft.
The findings come from Mandiant, which said Midnight Blizzard (aka APT29, BlueBravo, or Cozy Bear) used the malware to target German political parties with phishing emails bearing a logo from the Christian Democratic Union (CDU) around February 26, 2024.
"This is the first time we have seen this APT29 cluster target political parties, indicating a possible area of emerging operational focus beyond the typical targeting of diplomatic missions," researchers Luke Jenkins and Dan Black said.
WINELOADER was first disclosed by Zscaler ThreatLabz last month as part of a cyber espionage campaign that's believed to have been ongoing since at least July 2023. It attributed the activity to a cluster dubbed SPIKEDWINE.
Attack chains leverage phishing emails with German-language lure content that purports to be an invite for a dinner reception to trick recipients into clicking on a phony link and downloading a rogue HTML Application (HTA) file, a first-stage dropper called ROOTSAW (aka EnvyScout) that acts as a conduit to deliver WINELOADER from a remote server.
"The German-language lure document contains a phishing link directing victims to a malicious ZIP file containing a ROOTSAW dropper hosted on an actor-controlled compromised website," the researchers said. "ROOTSAW delivered a second-stage CDU-themed lure document and a next stage WINELOADER payload."
WINELOADER, invoked via a technique called DLL side-loading using the legitimate sqldumper.exe, comes equipped with abilities to contact an actor-controlled server and fetch additional modules for execution on the compromised hosts.
It's said to share similarities with known APT29 malware families like BURNTBATTER, MUSKYBEAT, and BEATDROP, suggesting the work of a common developer.
WINELOADER, per the Google Cloud subsidiary, has also been employed in an operation targeting diplomatic entities in the Czech Republic, Germany, India, Italy, Latvia, and Peru in late January 2024.
"ROOTSAW continues to be the central component of APT29's initial access efforts to collect foreign political intelligence," the company said.
"The first-stage malware's expanded use to target German political parties is a noted departure from the typical diplomatic focus of this APT29 subcluster, and almost certainly reflects the SVR's interest in gleaning information from political parties and other aspects of civil society that could advance Moscow's geopolitical interests."
The development comes as German prosecutors have charged a military officer, named Thomas H, with espionage offenses after he was allegedly caught spying on behalf of Russian intelligence services and passing on unspecified sensitive information. He was arrested in August 2023.
"From May 2023, he approached the Russian Consulate General in Bonn and the Russian Embassy in Berlin several times on his own initiative and offered to cooperate," the Office of the Federal Prosecutor said. "On one occasion, he transmitted information that he had obtained in the course of his professional activities for forwarding to a Russian intelligence service."
New StrelaStealer Phishing Attacks Hit Over 100 Organizations in E.U. and U.S.
22.3.24 Virus The Hacker News
Cybersecurity researchers have detected a new wave of phishing attacks that aim to deliver an ever-evolving information stealer referred to as StrelaStealer.
The campaigns impact more than 100 organizations in the E.U. and the U.S., Palo Alto Networks Unit 42 researchers said in a new report published today.
"These campaigns come in the form of spam emails with attachments that eventually launch the StrelaStealer's DLL payload," the company said in a report published today.
"In an attempt to evade detection, attackers change the initial email attachment file format from one campaign to the next, to prevent detection from the previously generated signature or patterns."
First disclosed in November 2022, StrelaStealer is equipped to siphon email login data from well-known email clients and exfiltrate them to an attacker-controlled server.
Since then, two large-scale campaigns involving the malware have been detected in November 2023 and January 2024 targeting high tech, finance, professional and legal, manufacturing, government, energy, insurance, and construction sectors in the E.U. and the U.S.
These attacks also aim to deliver a new variant of the stealer that packs in better obfuscation and anti-analysis techniques, while being propagated via invoice-themed emails bearing ZIP attachments, marking a shift from ISO files.
Present within the ZIP archives is a JavaScript file that drops a batch file, which, in turn, launches the stealer DLL payload using rundll32.exe, a legitimate Windows component responsible for running 32-bit dynamic-link libraries.
The stealer malware also relies on a bag of obfuscation tricks to render analysis difficult in sandboxed environments.
"With each new wave of email campaigns, threat actors update both the email attachment, which initiates the infection chain, and the DLL payload itself," the researchers said.
The disclosure comes as Broadcom-owned Symantec revealed that fake installers for well known applications or cracked software hosted on GitHub, Mega or Dropbox are serving as a conduit for a stealer malware known as Stealc.
Phishing campaigns have also been observed delivering Revenge RAT and Remcos RAT (aka Rescoms), with the latter delivered by means of a cryptors-as-a-service (CaaS) called AceCryptor, per ESET.

"During the second half of [2023], Rescoms became the most prevalent malware family packed by AceCryptor," the cybersecurity firm said, citing telemetry data. "Over half of these attempts happened in Poland, followed by Serbia, Spain, Bulgaria, and Slovakia."
Other prominent off-the-shelf malware packed inside AceCryptor in H2 2023 include SmokeLoader, STOP ransomware, RanumBot, Vidar, RedLine, Tofsee, Fareit, Pitou, and Stealc. It's worth noting that many of these malware strains have also been disseminated via PrivateLoader.
Another social engineering scam observed by Secureworks Counter Threat Unit (CTU) has been found to target individuals seeking information about recently deceased individuals on search engines with fake obituary notices hosted on bogus websites, driving traffic to the sites through search engine optimization (SEO) poisoning in order to ultimately push adware and other unwanted programs.
"Visitors to these sites are redirected to e-dating or adult entertainment websites or are immediately presented with CAPTCHA prompts that install web push notifications or popup ads when clicked," the company said.
"The notifications display false virus alert warnings from well-known antivirus applications like McAfee and Windows Defender, and they persist in the browser even if the victim clicks one of the buttons."
"The buttons link to legitimate landing pages for subscription-based antivirus software programs, and an affiliate ID embedded in the hyperlink rewards threat actors for new subscriptions or renewals."
While the activity is currently limited to filling fraudsters' coffers via affiliate programs, the attack chains could be easily repurposed to deliver information stealers and other malicious programs.
The development also follows the discovery a new activity cluster tracked as Fluffy Wolf that's capitalizing on phishing emails containing an executable attachment to deliver a cocktail of threats, such as MetaStealer, Warzone RAT, XMRig miner, and a legitimate remote desktop tool called Remote Utilities.
The campaign is a sign that even unskilled threat actors can leverage malware-as-a-service (MaaS) schemes to conduct successful attacks at scale and plunder sensitive information, which can then be monetized further for profit.
"Although mediocre in terms of technical skills, these threat actors achieve their goals by using just two sets of tools: legitimate remote access services and inexpensive malware," BI.ZONE said.
Russian Hackers May Have Targeted Ukrainian Telecoms with Upgraded 'AcidPour' Malware
22.3.24 Virus The Hacker News
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne show.
The cybersecurity firm also confirmed connections between the malware and AcidRain, tying it to threat activity clusters associated with Russian military intelligence.
"AcidPour's expanded capabilities would enable it to better disable embedded devices including networking, IoT, large storage (RAIDs), and possibly ICS devices running Linux x86 distributions," security researchers Juan Andres Guerrero-Saade and Tom Hegel said.
AcidPour is a variant of AcidRain, a wiper that was used to render Viasat KA-SAT modems operable at the onset of the Russo-Ukrainian war in early 2022 and cripple Ukraine's military communications.
It also builds upon the latter's features, while targeting Linux systems running on x86 architecture. AcidRain, on the other hand, is compiled for MIPS architecture.
Where AcidRain was more generic, AcidPour incorporates logic to target embedded devices, Storage Area Networks (SANs), Network Attached Storage (NAS) appliances, and dedicated RAID arrays.
That said, both the strains overlap when it comes to the use of the reboot calls and the method employed for recursive directory wiping. Also identical is the IOCTLs-based device-wiping mechanism that also shares commonalities with another malware linked to Sandworm known as VPNFilter.
"One of the most interesting aspects of AcidPour is its coding style, reminiscent of the pragmatic CaddyWiper broadly utilized against Ukrainian targets alongside notable malware like Industroyer 2," the researchers said.
The C-based malware comes with a self-delete function that overwrites itself on disk at the beginning of its execution, while also employing an alternate wiping approach depending on the device type.

AcidPour has been attributed to a hacking crew tracked as UAC-0165, which is associated with Sandworm and has a track record of striking Ukrainian critical infrastructure.
The Computer Emergency Response Team of Ukraine (CERT-UA), in October 2023, implicated the adversary to attacks targeting at least 11 telecommunication service providers in the country between May and September of last year.
"[AcidPour] could have been used in 2023," Hegel told The Hacker News. "It's likely the actor has made use of AcidRain/AcidPour related tooling consistently throughout the war. A gap in this perspective speaks to the level of insight the public often has to cyber intrusions – generally quite limited and incomplete."
The ties to Sandworm are further bolstered by the fact that a threat actor known as Solntsepyok (aka Solntsepek or SolntsepekZ) claimed to have infiltrated four different telecommunication operators in Ukraine and disrupted their services on March 13, 2024, three days prior to the discovery of AcidPour.
Solntsepyok, according to the State Special Communications Service of Ukraine (SSSCIP), is a Russian advanced persistent threat (APT) with likely ties to the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU), which also operates Sandworm.
It's worth pointing out that Solntsepyok has also been accused of hacking into Kyivstar's systems as early as May 2023. The breach came to light in late December.
While it's currently not clear if AcidPour was used in the latest set of attacks, the discovery suggests that threat actors are constantly refining their tactics to stage destructive assaults and inflict significant operational impact.
"This progression reveals not only a refinement in the technical capabilities of these threat actors but also their calculated approach to select targets that maximize follow-on effects, disrupting critical infrastructure and communications," the researchers said.
Over 800 npm Packages Found with Discrepancies, 18 Exploitable to 'Manifest Confusion'
21.3.24 Virus The Hacker News
New research has discovered over 800 packages in the npm registry which have discrepancies from their registry entries, out of which 18 have been found to exploit a technique called manifest confusion.
The findings come from cybersecurity firm JFrog, which said the issue could be exploited by threat actors to trick developers into running malicious code.
"It's an actual threat since developers may be tricked into downloading packages that look innocent, but whose hidden dependencies are actually malicious," security researcher Andrey Polkovnichenko told The Hacker News.
Manifest confusion was first documented in July 2023, when security researcher Darcy Clarke found that mismatches in manifest and package metadata could be weaponized to stage software supply chain attacks.
The problem stems from the fact that the npm registry does not validate whether the manifest file contained in the tarball (package.json) matches the manifest data provided to the npm server during the publishing process via an HTTP PUT request to the package URI endpoint.
As a result, a threat actor could take advantage of this lack of cross verification to supply a different manifest containing hidden dependencies that's processed during package installation to stealthily install malicious dependencies onto the developer's system.
"The visible, or 'fake,' manifest can mislead developers and even audit tools that rely on the data available in the npm registry database," JFrog said. "In reality, the installer takes the file package.json from the tarball, which may be different from the visible one supplied in the HTTP PUT request."

The company said it identified more than 800 packages where there was a mismatch between the manifest in the npm registry and the package.json file inside the tarball.
While many of these mismatches are the result of protocol specification differences or variations in the scripts section of the package file, 18 of them are said to have been designed to exploit manifest confusion.
A notable package in question is yatai-web-ui, which is designed to send an HTTP request to a server with information about the IP address of the machine in which the package was installed.
The findings show that the attack vector seems to have never been put to use by threat actors. That said, it's crucial that developers take steps to ensure the packages are free of suspicious behaviors.
"Since this issue was not resolved by npm, trusting packages only by how they look on npm's website, might be risky," Polkovnichenko said.
"Organizations should introduce procedures that verify that all packages that enter the organization or are used by their dev teams are safe and can be trusted. Specifically in the case of manifest confusion, it's required that every package is analyzed to see if there are any hidden dependencies."
AndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
21.3.24 Virus The Hacker News
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that's used to target Laravel applications and steal sensitive data.
"It works by scanning and taking out important information from .env files, revealing login details linked to AWS and Twilio," Juniper Threat Labs researcher Kashinath T Pattan said.
"Classified as an SMTP cracker, it exploits SMTP using various strategies such as credential exploitation, web shell deployment, and vulnerability scanning."
AndroxGh0st has been detected in the wild since at least 2022, with threat actors leveraging it to access Laravel environment files and steal credentials for various cloud-based applications like Amazon Web Services (AWS), SendGrid, and Twilio.
Attack chains involving the Python malware are known to exploit known security flaws in Apache HTTP Server, Laravel Framework, and PHPUnit to gain initial access and for privilege escalation and persistence.
Earlier this January, U.S. cybersecurity and intelligence agencies warned of attackers deploying the AndroxGh0st malware to create a botnet for "victim identification and exploitation in target networks."
"Androxgh0st first gains entry through a weakness in Apache, identified as CVE-2021-41773, allowing it to access vulnerable systems," Pattan explained.
"Following this, it exploits additional vulnerabilities, specifically CVE-2017-9841 and CVE-2018-15133, to execute code and establish persistent control, essentially taking over the targeted systems."
Androxgh0st is designed to exfiltrate sensitive data from various sources, including .env files, databases, and cloud credentials. This allows threat actors to deliver additional payloads to compromised systems.
Juniper Threat Labs said it has observed an uptick in activity related to the exploitation of CVE-2017-9841, making it essential that users move quickly to update their instances to the latest version.

A majority of the attack attempts targeting its honeypot infrastructure originated from the U.S., U.K., China, the Netherlands, Germany, Bulgaria, Kuwait, Russia, Estonia, and India, it added.
The development comes as the AhnLab Security Intelligence Center (ASEC) revealed that vulnerable WebLogic servers located in South Korea are being targeted by adversaries and used them as download servers to distribute a cryptocurrency miner called z0Miner and other tools like fast reverse proxy (FRP).
It also follows the discovery of a malicious campaign that infiltrates AWS instances to create over 6,000 EC2 instances within minutes and deploy a binary associated with a decentralized content delivery network (CDN) known as Meson Network.
The Singapore-based company, which aims to create the "world's largest bandwidth marketplace," works by allowing users to exchange their idle bandwidth and storage resources with Meson for tokens (i.e., rewards).
"This means miners will receive Meson tokens as a reward for providing servers to the Meson Network platform, and the reward will be calculated based on the amount of bandwidth and storage brought into the network," Sysdig said in a technical report published this month.
"It isn't all about mining cryptocurrency anymore. Services like Meson network want to leverage hard drive space and network bandwidth instead of CPU. While Meson may be a legitimate service, this shows that attackers are always on the lookout for new ways to make money."
With cloud environments increasingly becoming a lucrative target for threat actors, it is critical to keep software up to date and monitor for suspicious activity.
Threat intelligence firm Permiso has also released a tool called CloudGrappler, that's built on top of the foundations of cloudgrep and scans AWS and Azure for flagging malicious events related to well-known threat actors.
New BunnyLoader Malware Variant Surfaces with Modular Attack Features
20.3.24 Virus The Hacker News
Cybersecurity researchers have discovered an updated variant of a stealer and malware loader called BunnyLoader that modularizes its various functions as well as allow it to evade detection.
"BunnyLoader is dynamically developing malware with the capability to steal information, credentials and cryptocurrency, as well as deliver additional malware to its victims," Palo Alto Networks Unit 42 said in a report published last week.
The new version, dubbed BunnyLoader 3.0, was announced by its developer named Player (or Player_Bunny) on February 11, 2024, with rewritten modules for data theft, reduced payload size, and enhanced keylogging capabilities.
BunnyLoader was first documented by Zscaler ThreatLabz in September 2023, describing it as malware-as-a-service (MaaS) designed to harvest credentials and facilitate cryptocurrency theft. It was initially offered on a subscription basis for $250 per month.
The malware has since undergone frequent updates that are aimed at evading antivirus defenses as well as expanding on its data gathering functions, with BunnyLoader 2.0 released by the end of the same month.
The third generation of BunnyLoader goes a step further by not only incorporating new denial-of-service (DoS) features to mount HTTP flood attacks against a target URL, but also splitting its stealer, clipper, keylogger, and DoS modules into distinct binaries.
"Operators of BunnyLoader can choose to deploy these modules or use BunnyLoader's built-in commands to load their choice of malware," Unit 42 explained.
Infection chains delivering BunnyLoader have also become progressively more sophisticated, leveraging a previously undocumented dropper to loader PureCrypter, which then forks into two separate branches.
While one branch launches the PureLogs loader to ultimately deliver the PureLogs stealer, the second attack sequence drops BunnyLoader to distribute another stealer malware called Meduza.

"In the ever changing landscape of MaaS, BunnyLoader continues to evolve, demonstrating the need for threat actors to frequently retool to evade detection," Unit 42 researchers said.
The development comes amid the continued use of SmokeLoader malware (aka Dofoil or Sharik) by a suspected Russian cybercrime crew called UAC-006 to target the Ukrainian government and financial entities. It's known to be active since 2011.
As many as 23 phishing attack waves delivering SmokeLoader were recorded between May and November 2023, according to an exhaustive report published by Ukraine's State Cyber Protection Center (SCPC).
"Primarily a loader with added information-stealing capabilities, SmokeLoader has been linked to Russian cybercrime operations and is readily available on Russian cybercrime forums," Unit 42 said.
Adding to BunnyLoader and SmokeLoader are two new information stealer malware codenamed Nikki Stealer and GlorySprout, the latter of which is developed in C++ and offered for $300 for a lifetime access. According to RussianPanda, the stealer is a clone of Taurus Stealer.
"A notable difference is that GlorySprout, unlike Taurus Stealer, does not download additional DLL dependencies from C2 servers," the researcher said. "Additionally, GlorySprout lacks the Anti-VM feature that is present in Taurus Stealer."
The findings also follow the discovery of a new variant of WhiteSnake Stealer that allows for the theft of critical sensitive data from compromised systems. "This new version has removed the string decryption code and made the code easy to understand," SonicWall said.
Suspected Russian Data-Wiping 'AcidPour' Malware Targeting Linux x86 Devices
19.3.24 Virus The Hacker News
A new variant of a data wiping malware called AcidRain has been detected in the wild that's specifically designed for targeting Linux x86 devices.
The malware, dubbed AcidPour, is compiled for Linux x86 devices, SentinelOne's Juan Andres Guerrero-Saade said in a series of posts on X.
"The new variant [...] is an ELF binary compiled for x86 (not MIPS) and while it refers to similar devices/strings, it's a largely different codebase," Guerrero-Saade noted.
AcidRain first came to light in the early days of the Russo-Ukrainian war, with the malware deployed against KA-SAT modems from U.S. satellite company Viasat.
An ELF binary compiled for MIPS architectures is capable of wiping the filesystem and different known storage device files by recursively iterating over common directories for most Linux distributions.
The cyber attack was subsequently attributed to Russia by the Five Eyes nations, along with Ukraine and the European Union.
AcidPour, as the new variant is called, is designed to erase content from RAID arrays and Unsorted Block Image (UBI) file systems through the addition of file paths like "/dev/dm-XX" and "/dev/ubiXX," respectively.
It's currently not clear who the intended victims are, although SentinelOne said it notified Ukrainian agencies. The exact scale of the attacks is presently unknown.
The discovery once again underscores the use of wiper malware to cripple targets, even as threat actors are diversifying their attack methods for maximum impact.
New DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
19.3.24 Virus The Hacker News
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information.
Cybersecurity company Securonix, which dubbed the campaign DEEP#GOSU, said it's likely associated with the North Korean state-sponsored group tracked as Kimsuky.
"The malware payloads used in the DEEP#GOSU represent a sophisticated, multi-stage threat designed to operate stealthily on Windows systems especially from a network-monitoring standpoint," security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a technical analysis shared with The Hacker News.
"Its capabilities included keylogging, clipboard monitoring, dynamic payload execution, and data exfiltration, and persistence using both RAT software for full remote access, scheduled tasks as well as self-executing PowerShell scripts using jobs."
A notable aspect of the infection procedure is that it leverages legitimate services such as Dropbox or Google Docs for command-and-control (C2), thus allowing the threat actor to blend undetected into regular network traffic.
On top of that, the use of such cloud services to stage the payloads allows for updating the functionality of the malware or delivering additional modules.
The starting point is said to be a malicious email attachment containing a ZIP archive with a rogue shortcut file (.LNK) that masquerades as a PDF file ("IMG_20240214_0001.pdf.lnk").
The .LNK file comes embedded with a PowerShell script as well as a decoy PDF document, with the former also reaching out to an actor-controlled Dropbox infrastructure to retrieve and execute another PowerShell script ("ps.bin").
The second-stage PowerShell script, for its part, fetches a new file from Dropbox ("r_enc.bin"), a .NET assembly file in binary form that's actually an open-source remote access trojan known as TruRat (aka TutRat or C# RAT) with capabilities to record keystrokes, manage files, and facilitate remote control.
It's worth noting that Kimsuky has employed TruRat in at least two campaigns uncovered by the AhnLab Security Intelligence Center (ASEC) last year.
Also retrieved by the PowerShell script from Dropbox is a VBScript ("info_sc.txt"), which, in turn, is designed to run arbitrary VBScript code retrieved from the cloud storage service, including a PowerShell script ("w568232.ps12x").
The VBScript is also designed to use Windows Management Instrumentation (WMI) to execute commands on the system, and set up scheduled tasks on the system for persistence.

Another noteworthy aspect of the VBScript is the use of Google Docs to dynamically retrieve configuration data for the Dropbox connection, allowing the threat actor to change the account information without having to alter the script itself.
The PowerShell script downloaded as a result is equipped to gather extensive information about the system and exfiltrate the details via a POST request to Dropbox.
"The purpose of this script appears to be designed to serve as a tool for periodic communication with a command-and-control (C2) server via Dropbox," the researchers said. "Its main purposes include encrypting and exfiltrating or downloading data."
In other words, it acts as a backdoor to control the compromised hosts and continuously keep a log of user activity, including keystrokes, clipboard content, and the foreground window.
The development comes as security researcher Ovi Liber detailed North Korea-linked ScarCruft's embedding of malicious code within Hangul Word Processor (HWP) lure documents present in phishing emails to distribute malware like RokRAT.

"The email contains a HWP Doc which has an embedded OLE object in the form of a BAT script," Liber said. "Once the user clicks on the OLE object, the BAT script executes which in turn creates a PowerShell-based reflective DLL injection attack on the victims machine."
It also follows Andariel's exploitation of a legitimate remote desktop solution called MeshAgent to install malware like AndarLoader and ModeLoader, a JavaScript malware meant for command execution.
"This is the first confirmed use of a MeshAgent by the Andariel group," ASEC said. "The Andariel group has been continuously abusing the asset management solutions of domestic companies to distribute malware in the process of lateral movement, starting with Innorix Agent in the past."
Andariel, also known by the names Nicket Hyatt or Silent Chollima, is a sub-cluster within the notorious Lazarus Group, actively orchestrating attacks for both cyber espionage and financial gain.
The prolific state-sponsored threat actor has since been observed laundering a chunk of the crypto assets stolen from the hack of crypto exchange HTX and its cross-chain bridge (aka HECO Bridge) through Tornado Cash. The breach led to the theft of $112.5 million in cryptocurrency in November 2023.
"Following common crypto-laundering patterns, the stolen tokens were immediately swapped for ETH, using decentralized exchanges," Elliptic said. "The stolen funds then lay dormant until March 13, 2024, when the stolen crypto assets began to be sent through Tornado Cash."
The blockchain analytics firm said that Tornado Cash's continuation of its operations despite sanctions have likely made it an attractive proposition for the Lazarus Group to conceal its transaction trail following the shutdown of Sinbad in November 2023.
"The mixer operates through smart contracts running on decentralized blockchains, so it cannot be seized and shut down in the same way that centralized mixers such as Sinbad.io have been," it noted.
Hackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
18.3.24 Virus The Hacker News
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware called AZORult in order to facilitate information theft.
"It uses an unorthodox HTML smuggling technique where the malicious payload is embedded in a separate JSON file hosted on an external website," Netskope Threat Labs researcher Jan Michael Alcantara said in a report published last week.
The phishing campaign has not been attributed to a specific threat actor or group. The cybersecurity company described it as widespread in nature, carried out with an intent to collect sensitive data for selling them in underground forums.
AZORult, also called PuffStealer and Ruzalto, is an information stealer first detected around 2016. It's typically distributed via phishing and malspam campaigns, trojanized installers for pirated software or media, and malvertising.
Once installed, it's capable of gathering credentials, cookies, and history from web browsers, screenshots, documents matching a list of specific extensions (.TXT, .DOC, .XLS, .DOCX, .XLSX, .AXX, and .KDBX), and data from 137 cryptocurrency wallets. AXX files are encrypted files created by AxCrypt, while KDBX refers to a password database created by the KeePass password manager.
The latest attack activity involves the threat actor creating counterfeit Google Docs pages on Google Sites that subsequently utilize HTML smuggling to deliver the payload.
HTML smuggling is the name given to a stealthy technique in which legitimate HTML5 and JavaScript features are abused to assemble and launch the malware by "smuggling" an encoded malicious script.
Thus, when a visitor is tricked into opening the rogue page from a phishing email, the browser decodes the script and extracts the payload on the host device, effectively bypassing typical security controls such as email gateways that are known to only inspect for suspicious attachments.
The AZORult campaign takes this approach a notch higher by adding a CAPTCHA barrier, an approach that not only gives a veneer of legitimacy but also serves as an additional layer of protection against URL scanners.
The downloaded file is a shortcut file (.LNK) that masquerades as a PDF bank statement, launching which kicks off a series of actions to execute a series of intermediate batch and PowerShell scripts from an already compromised domain.

One of the PowerShell scripts ("agent3.ps1") is designed to fetch the AZORult loader ("service.exe"), which, in turn, downloads and executes another PowerShell script ("sd2.ps1") containing the stealer malware.
"It executes the fileless AZORult infostealer stealthily by using reflective code loading, bypassing disk-based detection and minimizing artifacts," Michael Alcantara said. "It uses an AMSI bypass technique to evade being detected by a variety of host-based anti-malware products, including Windows Defender."
"Unlike common smuggling files where the blob is already inside the HTML code, this campaign copies an encoded payload from a separate compromised site. Using legitimate domains like Google Sites can help trick the victim into believing the link is legitimate."
The findings come as Cofense revealed the use of malicious SVG files by threat actors in recent campaigns to disseminate Agent Tesla and XWorm using an open-source program called AutoSmuggle that simplifies the process of crafting HTML or SVG smuggled files.
AutoSmuggle "takes a file such as an exe or an archive and 'smuggles' it into the SVG or HTML file so that when the SVG or HTML file is opened, the 'smuggled' file is delivered," the company explained.
Phishing campaigns have also been observed employing shortcut files packed within archive files to propagate LokiBot, an information stealer analogous to AZORult with features to harvest data from web browsers and cryptocurrency wallets.
"The LNK file executes a PowerShell script to download and execute the LokiBot loader executable from a URL. LokiBot malware has been observed using image steganography, multi-layered packing and living-off-the-land (LotL) techniques in past campaigns," SonicWall disclosed last week.
In another instance highlighted by Docguard, malicious shortcut files have been found to initiate a series of payload downloads and ultimately deploy AutoIt-based malware.
That's not all. Users in the Latin American region are being targeted as part of an ongoing campaign in which the attackers impersonate Colombian government agencies to send booby-trapped emails with PDF documents that accuse the recipients of flouting traffic rules.
Present within the PDF file is a link that, upon click, results in the download of a ZIP archive containing a VBScript. When executed, the VBScript drops a PowerShell script responsible for fetching one of the remote access trojans like AsyncRAT, njRAT, and Remcos.
Hackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
17.3.24 Virus The Hacker News

Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro.
The campaign, codenamed gitgub, includes 17 repositories associated with 11 different accounts, according to G DATA. The repositories in question have since been taken down by the Microsoft-owned subsidiary.
"The repositories look similar, featuring a README.md file with the promise of free cracked software," the German cybersecurity company said.
"Green and red circles are commonly used on Github to display the status of automatic builds. Gitgub threat actors added four green Unicode circles to their README.md that pretend to display a status alongside a current date and provide a sense of legitimacy and recency."
The list of repositories is as follows, with each of them pointing to a download link ("digitalxnetwork[.]com") containing a RAR archive file -
andreastanaj/AVAST
andreastanaj/Sound-Booster
aymenkort1990/fabfilter
BenWebsite/-IObit-Smart-Defrag-Crack
Faharnaqvi/VueScan-Crack
javisolis123/Voicemod
lolusuary/AOMEI-Backupper
lolusuary/Daemon-Tools
lolusuary/EaseUS-Partition-Master
lolusuary/SOOTHE-2
mostofakamaljoy/ccleaner
rik0v/ManyCam
Roccinhu/Tenorshare-Reiboot
Roccinhu/Tenorshare-iCareFone
True-Oblivion/AOMEI-Partition-Assistant
vaibhavshiledar/droidkit
vaibhavshiledar/TOON-BOOM-HARMONY
The RAR archive, which requires the victims to supply a password mentioned in the repository's README.md file, contains an installer file, which unpacks the next-stage payload, an executable file that's inflated to 699 MB in an effort to crash analysis tools like IDA Pro.
The actual contents of the file – amounting to a mere 3.43 MB – act as a loader to inject RisePro (version 1.6) into either AppLaunch.exe or RegAsm.exe.
RisePro burst into the spotlight in late 2022 when it was distributed using a pay-per-install (PPI) malware downloader service known as PrivateLoader.
Written in C++, it's designed to gather sensitive information from infected hosts and exfiltrate it to two Telegram channels, which are often used by threat actors to extract victims' data. Interestingly, recent research from Checkmarx showed that it's possible to infiltrate and forward messages from an attacker's bot to another Telegram account.
The development comes as Splunk detailed the tactics and techniques adopted by Snake Keylogger, describing it as a stealer malware that "employs a multifaceted approach to data exfiltration."
"The use of FTP facilitates the secure transfer of files, while SMTP enables the sending of emails containing sensitive information," Splunk said. "Additionally, integration with Telegram offers a real-time communication platform, allowing for immediate transmission of stolen data."
Stealer malware have become increasingly popular, often becoming the primary vector for ransomware and other high impact data breaches. According to a report from Specops published this week, RedLine, Vidar, and Raccoon have emerged as the most widely-used stealers, with RedLine alone accounting for the theft of more than 170.3 million passwords in the last six months.
"The current rise of information-stealing malware is a stark reminder of constantly evolving digital threats," Flashpoint noted in January 2024. "While the motivations behind its use is almost always rooted in financial gain, stealers are continually adapting while being more accessible and easier to use."
Malicious Ads Targeting Chinese Users with Fake Notepad++ and VNote Installers
15.3.24 Virus The Hacker News

Chinese users looking for legitimate software such as Notepad++ and VNote on search engines like Baidu are being targeted with malicious ads and bogus links to distribute trojanized versions of the software and ultimately deploy Geacon, a Golang-based implementation of Cobalt Strike.
"The malicious site found in the notepad++ search is distributed through an advertisement block," Kaspersky researcher Sergey Puzan said.
"Opening it, an attentive user will immediately notice an amusing inconsistency: the website address contains the line vnote, the title offers a download of Notepad‐‐ (an analog of Notepad++, also distributed as open-source software), while the image proudly shows Notepad++. In fact, the packages downloaded from here contain Notepad‐‐."
The website, named vnote.fuwenkeji[.]cn, contains download links to Windows, Linux, and macOS versions of the software, with the link to the Windows variant pointing to the official Gitee repository containing the Notepad-- installer ("Notepad--v2.10.0-plugin-Installer.exe").
The Linux and macOS versions, on the other hand, lead to malicious installation packages hosted on vnote-1321786806.cos.ap-hongkong.myqcloud[.]com.

In a similar fashion, the fake look-alike websites for VNote ("vnote[.]info" and "vnotepad[.]com") lead to the same set of myqcloud[.]com links, in this case, also pointing to a Windows installer hosted on the domain. That said, the links to the potentially malicious versions of VNote are no longer active.
An analysis of the modified Notepad-- installers reveals that they are designed to retrieve a next-stage payload from a remote server, a backdoor that exhibits similarities with Geacon.
It's capable of creating SSH connections, performing file operations, enumerating processes, accessing clipboard content, executing files, uploading and downloading files, taking screenshots, and even entering into sleep mode. Command-and-control (C2) is facilitated by means of HTTPS protocol.
The development comes as malvertising campaigns have also acted as a conduit for other malware such as FakeBat (aka EugenLoader) malware with the help of MSIX installer files masquerading as Microsoft OneNote, Notion, and Trello.
Ande Loader Malware Targets Manufacturing Sector in North America
14.3.24 Virus The Hacker News
The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans (RATs) like Remcos RAT and NjRAT.
The attacks, which take the form of phishing emails, targeted Spanish-speaking users in the manufacturing industry based in North America, eSentire said.
Blind Eagle (aka APT-C-36) is a financially motivated threat actor that has a history of orchestrating cyber attacks against entities in Colombia and Ecuador to deliver an assortment of RATs, including AsyncRAT, BitRAT, Lime RAT, NjRAT, Remcos RAT, and Quasar RAT.
The latest findings mark an expansion of the threat actor's targeting footprint, while also leveraging phishing bearing RAR and BZ2 archives to activate the infection chain.
The password-protected RAR archives come with a malicious Visual Basic Script (VBScript) file that's responsible for establishing persistence in the Windows Startup folder and launching the Ande Loader, which, in turn, loads the Remcos RAT payload.
In an alternative attack sequence observed by the Canadian cybersecurity firm, a BZ2 archive containing a VBScript file is distributed via a Discord content delivery network (CDN) link. The Ande Loader malware, in this case, drops NjRAT instead of Remcos RAT.
"Blind Eagle threat actor(s) have been using crypters written by Roda and Pjoao1578," eSentire said. "One of the crypters developed by Roda has the hardcoded server hosting both injector components of the crypter and additional malware that was used in the Blind Eagle campaign."
The development comes as SonicWall shed light on the inner workings of another loader malware family called DBatLoader, detailing its use of a legitimate-but-vulnerable driver associated with RogueKiller AntiMalware software (truesight.sys) to terminate security software as part of a Bring Your Own Vulnerable Driver (BYOVD) attack and ultimately deliver Remcos RAT.
"The malware is received inside an archive as an email attachment and is highly obfuscated, containing multiple layers of encryption data," the company noted earlier this month.
PixPirate Android Banking Trojan Using New Evasion Tactic to Target Brazilian Users
13.3.24 Virus The Hacker News
The threat actors behind the PixPirate Android banking trojan are leveraging a new trick to evade detection on compromised devices and harvest sensitive information from users in Brazil.
The approach allows it to hide the malicious app's icon from the home screen of the victim's device, IBM said in a technical report published today.
"Thanks to this new technique, during PixPirate reconnaissance and attack phases, the victim remains oblivious to the malicious operations that this malware performs in the background," security researcher Nir Somech said.
PixPirate, which was first documented by Cleafy in February 2023, is known for its abuse of Android's accessibility services to covertly perform unauthorized fund transfers using the PIX instant payment platform when a targeted banking app is opened.
The constantly mutating malware is also capable of stealing victims' online banking credentials and credit card information, as well as capturing keystrokes and intercepting SMS messages to access two-factor authentication codes.
Typically distributed via SMS and WhatsApp, the attack flow entails the use of a dropper (aka downloader) app that's engineered to deploy the main payload (aka droppee) to pull off the financial fraud.
"Usually, the downloader is used to download and install the droppee, and from this point on, the droppee is the main actor conducting all fraudulent operations and the downloader is irrelevant," Somech explained.
"In the case of PixPirate, the downloader is responsible not only for downloading and installing the droppee but also for running and executing it. The downloader plays an active part in the malicious activities of the droppee as they communicate with each other and send commands to execute."
The downloader APK app, once launched, prompts the victim to update the app to either retrieve the PixPirate component from an actor-controlled server or install it if it's embedded within itself.

What's changed in the latest version of the droppee is the absence of activity with the action "android.intent.action.Main" and the category "android.intent.category.LAUNCHER" that allows a user to launch an app from the home screen by tapping its icon.
Put differently, the infection chain requires both the downloader and the droppee to work in tandem, with the former responsible for running the PixPirate APK by binding to a service exported by the droppee.
"Later, to maintain persistence, the droppee is also triggered to run by the different receivers that it registered," Somech said. "The receivers are set to be activated based on different events that occur in the system and not necessarily by the downloader that initially triggered the droppee to run."
"This technique allows the PixPirate droppee to run and hide its existence even if the victim removes the PixPirate downloader from their device."
The development comes as Latin American (LATAM) banks have become the target of a new malware called Fakext that employs a rogue Microsoft Edge extension named SATiD to carry out man-in-the-browser and web injection attacks with the goal of grabbing credentials entered in the targeted bank site.
It's worth noting that SAT ID is a service offered by Mexico's Tax Administration Service (SAT) to generate and update electronic signatures for filing taxes online.
In select cases, Fakext is engineered to display an overlay that urges the victim to download a legitimate remote access tool by purporting to be the bank's IT support team, ultimately enabling the threat actors to conduct financial fraud.
The campaign – active since at least November 2023 – singles out 14 banks operating in the region, a majority of which are located in Mexico. The extension has since been taken down from the Edge Add-ons store.
Alert: Cybercriminals Deploying VCURMS and STRRAT Trojans via AWS and GitHub
13.3.24 Virus The Hacker News

A new phishing campaign has been observed delivering remote access trojans (RAT) such as VCURMS and STRRAT by means of a malicious Java-based downloader.
"The attackers stored malware on public services like Amazon Web Services (AWS) and GitHub, employing a commercial protector to avoid detection of the malware," Fortinet FortiGuard Labs researcher Yurren Wan said.
An unusual aspect of the campaign is VCURMS' use of a Proton Mail email address ("sacriliage@proton[.]me") for communicating with a command-and-control (C2) server.
The attack chain commences with a phishing email that urges recipients to click on a button to verify payment information, resulting in the download of a malicious JAR file ("Payment-Advice.jar") hosted on AWS.
Executing the JAR file leads to the retrieval of two more JAR files, which are then run separately to launch the twin trojans.
Besides sending an email with the message "Hey master, I am online" to the actor-controlled address, VCURMS RAT periodically checks the mailbox for emails with specific subject lines to extract the command to be executed from the body of the missive.
This includes running arbitrary commands using cmd.exe, gathering system information, searching and uploading files of interest, and downloading additional information stealer and keylogger modules from the same AWS endpoint.
The information stealer comes fitted with capabilities to siphon sensitive data from apps like Discord and Steam, credentials, cookies, and auto-fill data from various web browsers, screenshots, and extensive hardware and network information about the compromised hosts.
VCURMS is said to share similarities with another Java-based infostealer codenamed Rude Stealer, which emerged in the wild late last year. STRRAT, on the other hand, has been detected in the wild since at least 2020, often propagated in the form of fraudulent JAR files.
"STRRAT is a RAT built using Java, which has a wide range of capabilities, such as serving as a keylogger and extracting credentials from browsers and applications," Wan noted.
The disclosure comes as Darktrace revealed a novel phishing campaign that's taking advantage of automated emails sent from the Dropbox cloud storage service via "no-reply@dropbox[.]com" to propagate a bogus link mimicking the Microsoft 365 login page.
"The email itself contained a link that would lead a user to a PDF file hosted on Dropbox, that was seemingly named after a partner of the organization," the company said. "the PDF file contained a suspicious link to a domain that had never previously been seen on the customer's environment, 'mmv-security[.]top.'"
Malware Campaign Exploits Popup Builder WordPress Plugin to Infect 3,900+ Sites
12.3.24 Virus The Hacker News
A new malware campaign is leveraging a high-severity security flaw in the Popup Builder plugin for WordPress to inject malicious JavaScript code.
According to Sucuri, the campaign has infected more than 3,900 sites over the past three weeks.
"These attacks are orchestrated from domains less than a month old, with registrations dating back to February 12th, 2024," security researcher Puja Srivastava said in a report dated March 7.
Infection sequences involve the exploitation of CVE-2023-6000, a security vulnerability in Popup Builder that could be exploited to create rogue admin users and install arbitrary plugins.
The shortcoming was exploited as part of a Balada Injector campaign earlier this January, compromising no less than 7,000 sites.
The latest set of attacks lead to the injection of malicious code, which comes in two different variants and is designed to redirect site visitors to other sites such as phishing and scam pages.
WordPress site owners are recommended to keep their plugins up-to-date as well as scan their sites for any suspicious code or users, and perform appropriate cleanup.
"This new malware campaign serves as a stark reminder of the risks of not keeping your website software patched and up-to-date," Srivastava said.
The development comes as WordPress security firm Wordfence disclosed a high-severity bug in another plugin known as Ultimate Member that can be weaponized to inject malicious web scripts.
The cross-site scripting (XSS) flaw, tracked as CVE-2024-2123 (CVSS score: 7.2), impacts all versions of the plugin, including and prior to 2.8.3. It has been patched in version 2.8.4, released on March 6, 2024.
The flaw stems from insufficient input sanitization and output escaping, thereby allowing unauthenticated attackers to inject arbitrary web scripts in pages that will be executed every time a user visits them.
"Combined with the fact that the vulnerability can be exploited by attackers with no privileges on a vulnerable site, this means that there is a high chance that unauthenticated attackers could gain administrative user access on sites running the vulnerable version of the plugin when successfully exploited," Wordfence said.
It's worth noting that the plugin maintainers addressed a similar flaw (CVE-2024-1071, CVSS score: 9.8) in version 2.8.3 released on February 19.
It also follows the discovery of an arbitrary file upload vulnerability in the Avada WordPress theme (CVE-2024-1468, CVSS score: 8.8) and possibly executes malicious code remotely. It has been resolved in version 7.11.5.
"This makes it possible for authenticated attackers, with contributor-level access and above, to upload arbitrary files on the affected site's server which may make remote code execution possible," Wordfence said.
New Banking Trojan CHAVECLOAK Targets Brazilian Users via Phishing Tactics
12.3.24 Virus The Hacker News
Users in Brazil are the target of a new banking trojan known as CHAVECLOAK that's propagated via phishing emails bearing PDF attachments.
"This intricate attack involves the PDF downloading a ZIP file and subsequently utilizing DLL side-loading techniques to execute the final malware," Fortinet FortiGuard Labs researcher Cara Lin said.
The attack chain involves the use of contract-themed DocuSign lures to trick users into opening PDF files containing a button to read and sign the documents.
In reality, clicking the button leads to the retrieval of an installer file from a remote link that's shortened using the Goo.su URL shortening service.
Present within the installer is an executable named "Lightshot.exe" that leverages DLL side-loading to load "Lightshot.dll," which is the CHAVECLOAK malware that facilitates the theft of sensitive information.
This includes gathering system metadata and running checks to determine whether the compromised machine is located in Brazil and, if so, periodically monitoring the foreground window to compare it against a predefined list of bank-related strings.
If it matches, a connection is established with a command-and-control (C2) server and proceeds to harvest various kinds of information and exfiltrate them to distinct endpoints on the server depending on the financial institution.
"The malware facilitates various actions to steal a victim's credentials, such as allowing the operator to block the victim's screen, log keystrokes, and display deceptive pop-up windows," Lin said.
"The malware actively monitors the victim's access to specific financial portals, including several banks and Mercado Bitcoin, which encompasses both traditional banking and cryptocurrency platforms."
Fortinet said it also uncovered a Delphi variant of CHAVECLOAK, once again highlighting the prevalence of Delphi-based malware targeting Latin America.
"The emergence of the CHAVECLOAK banking Trojan underscores the evolving landscape of cyberthreats targeting the financial sector, specifically focusing on users in Brazil," Lin concluded.
The findings come amid an ongoing mobile banking fraud campaign against the U.K., Spain, and Italy that entails using smishing and vishing (i.e., SMS and voice phishing) tactics to deploy an Android malware called Copybara with the goal of performing unauthorized banking transfers to a network of bank accounts operated by money mules.
"TAs [Threat actors] have been caught using a structured way of managing all the ongoing phishing campaigns via a centralized web panel known as 'Mr. Robot,'" Cleafy said in a report published last week.

"With this panel, TAs can enable and manage multiple phishing campaigns (against different financial institutions) based on their needs."
The C2 framework also allows attackers to orchestrate tailored attacks on distinct financial institutions using phishing kits that are engineered to mimic the user interface of the targeted entity, while also adopting anti-detection methods via geofencing and device fingerprinting to limit connections only from mobile devices.

The phishing kit – which serves as a fake login page – is responsible for capturing retail banking customer credentials and phone numbers and sending the details to a Telegram group.
Some of the malicious infrastructure used for the campaign is designed to deliver Copybara, which is managed using a C2 panel named JOKER RAT that displays all the infected devices and their geographical distribution over a live map.
It also allows the threat actors to remotely interact in real-time with an infected device using a VNC module, in addition to injecting fake overlays on top of banking apps to siphon credentials, logging keystrokes by abusing Android's accessibility services, and intercepting SMS messages.
On top of that, JOKER RAT comes with an APK builder that makes it possible to customize the rogue app's name, package name, and icons.
"Another feature available inside the panel is the 'Push Notification,' probably used to send to the infected devices fake push notifications that look like a bank notification to entice the user to open the bank's app in such a way that the malware can steal credentials," Cleafy researchers Francesco Iubatti and Federico Valentini said.
The growing sophistication of on-device fraud (ODF) schemes is further evidenced by a recently disclosed TeaBot (aka Anatsa) campaign that managed to infiltrate the Google Play Store under the guise of PDF reader apps.
"This application serves as a dropper, facilitating the download of a banking trojan of the TeaBot family through multiple stages," Iubatti said. "Before downloading the banking trojan, the dropper performs advanced evasion techniques, including obfuscation and file deletion, alongside multiple checks about the victim countries."
New Python-Based Snake Info Stealer Spreading Through Facebook Messages
7.3.24 Virus The Hacker News

Facebook messages are being used by threat actors to a Python-based information stealer dubbed Snake that's designed to capture credentials and other sensitive data.
"The credentials harvested from unsuspecting users are transmitted to different platforms such as Discord, GitHub, and Telegram," Cybereason researcher Kotaro Ogino said in a technical report.
Details about the campaign first emerged on the social media platform X in August 2023. The attacks entail sending prospective users seemingly innocuous RAR or ZIP archive files that, upon opening, activate the infection sequence.
The intermediate stages involve two downloaders – a batch script and a cmd script – with the latter responsible for downloading and executing the information stealer from an actor-controlled GitLab repository.
Cybereason said it detected three different variants of the stealer, the third one being an executable assembled by PyInstaller. The malware, for its part, is designed to gather data from different web browsers, including Cốc Cốc, suggesting a Vietnamese focus.
The collected information, which comprises credentials and cookies, is then exfiltrated in the form of a ZIP archive via the Telegram Bot API. The stealer is also designed to dump cookie information specific to Facebook, an indication that the threat actor is likely looking to hijack the accounts for their own purposes.
The Vietnamese connection is further bolstered by the naming convention of the GitHub and GitLab repositories and the fact that the source code contains references to the Vietnamese language.

"All of the variants support Cốc Cốc Browser, which is a well known Vietnamese Browser used widely by the Vietnamese community," Ogino said.
Over the past year, multiple information stealers targeting Facebook cookies have appeared in the wild, counting S1deload Stealer, MrTonyScam, NodeStealer, and VietCredCare.
The development comes as Meta has come under criticism in the U.S. for failing to assist victims whose accounts have been hacked into, calling on the company to take immediate action to address a "dramatic and persistent spike" in account takeover incidents.
It also follows a discovery that threat actors are "using a cloned game cheat website, SEO poisoning, and a bug in GitHub to trick would-be-game-hackers into running Lua malware," according to OALABS Research.
Specifically, the malware operators are leveraging a GitHub vulnerability that allows an uploaded file associated with an issue on a repository to persist even in scenarios where the issue is never saved.
"This means that anyone can upload a file to any git repository on GitHub, and not leave any trace that the file exists except for the direct link," the researchers said, adding the malware comes fitted with capabilities for command-and-control (C2) communications.
Watch Out for Spoofed Zoom, Skype, Google Meet Sites Delivering Malware
7.3.24 Virus The Hacker News

Threat actors have been leveraging fake websites advertising popular video conferencing software such as Google Meet, Skype, and Zoom to deliver a variety of malware targeting both Android and Windows users since December 2023.
"The threat actor is distributing Remote Access Trojans (RATs) including SpyNote RAT for Android platforms, and NjRAT and DCRat for Windows systems," Zscaler ThreatLabz researchers said.
The spoofed sites are in Russian and are hosted on domains that closely resemble their legitimate counterparts, indicating that the attackers are using typosquatting tricks to lure prospective victims into downloading the malware.
They also come with options to download the app for Android, iOS, and Windows platforms. While clicking on the button for Android downloads an APK file, clicking on the Windows app button triggers the download of a batch script.
The malicious batch script is responsible for executing a PowerShell script, which, in turn, downloads and executes the remote access trojan.
Currently, there is no evidence that the threat actor is targeting iOS users, given that clicking on the button for the iOS app takes the user to the legitimate Apple App Store listing for Skype.
"A threat actor is using these lures to distribute RATs for Android and Windows, which can steal confidential information, log keystrokes, and steal files," the researchers said.
The development comes as the AhnLab Security Intelligence Center (ASEC) revealed that a new malware dubbed WogRAT targeting both Windows and Linux is abusing a free online notepad platform called aNotepad as a covert vector for hosting and retrieving malicious code.

It's said to be active from at least late 2022, targeting Asian countries like China, Hong Kong, Japan, and Singapore, among others. That said, it's currently not known how the malware is distributed in the wild.
"When WogRAT is run for the first time, it collects basic information of the infected system and sends them to the C&C server," ASEC said. "The malware then supports commands such as executing commands, sending results, downloading files, and uploading these files."
It also coincides with high-volume phishing campaigns orchestrated by a financially motivated cybercriminal actor known as TA4903 to steal corporate credentials and likely follow them with business email compromise (BEC) attacks. The adversary has been active since at least 2019, with the activities intensifying post mid-2023.
"TA4903 routinely conducts campaigns spoofing various U.S. government entities to steal corporate credentials," Proofpoint said. "The actor also spoofs organizations in various sectors including construction, finance, healthcare, food and beverage, and others."
Attack chains involve the use of QR codes (aka quishing) for credential phishing as well as relying on the EvilProxy adversary-in-the-middle (AiTM) phishing kit to bypass two-factor authentication (2FA) protections.
Once a target mailbox is compromised, the threat actor has been observed searching for information relevant to payments, invoices, and bank information, with the ultimate goal of hijacking existing email threads and performing invoice fraud.
Phishing campaigns have also functioned as a conduit for other malware families like DarkGate, Agent Tesla, and Remcos RAT, the last of which leverages steganographic decoys to drop the malware on compromised hosts.
U.S. Cracks Down on Predatory Spyware Firm for Targeting Officials and Journalists
6.3.24 Virus The Hacker News
The U.S. Department of Treasury's Office of Foreign Assets Control (OFAC) sanctioned two individuals and five entities associated with the Intellexa Alliance for their role in "developing, operating, and distributing" commercial spyware designed to target government officials, journalists, and policy experts in the country.
"The proliferation of commercial spyware poses distinct and growing security risks to the United States and has been misused by foreign actors to enable human rights abuses and the targeting of dissidents around the world for repression and reprisal," the agency said.
"The Intellexa Consortium, which has a global customer base, has enabled the proliferation of commercial spyware and surveillance technologies around the world, including to authoritarian regimes."
The Intellexa Alliance is a consortium of several companies, including Cytrox, linked to a mercenary spyware solution called Predator. In July 2023, the U.S. government added Cytrox and Intellexa, as well as their corporate holdings in Hungary, Greece, and Ireland, to the Entity List.
Predator, much like NSO Group's Pegasus, can infiltrate Android and iOS devices using zero-click attacks that require no user interaction. Once installed, the spyware makes it possible for the operators to harvest sensitive data and surveil targets of interest.
OFAC said unspecified foreign actors had deployed Predator against U.S. government officials, journalists, and policy experts.
"In the event of a successful Predator infection, the spyware's operators can access and retrieve sensitive information including contacts, call logs, and messaging information, microphone recordings, and media from the device," the Treasury Department said.
The sanctions designations apply to the following individuals and entities -
Tal Jonathan Dilian (Dilian), the founder of the Intellexa Consortium
Sara Aleksandra Fayssal Hamou (Hamou), a corporate off-shoring specialist who has provided managerial services to the Intellexa Consortium
Intellexa S.A., a Greece-based software development company
Intellexa Limited, an Ireland-based company
Cytrox AD, a North Macedonia-based company that's responsible for the development of Predator
Cytrox Holdings Zartkoruen Mukodo Reszvenytarsasag (Cytrox Holdings ZRT), a Hungary-based entity
Thalestris Limited, an Ireland-based entity that holds distribution rights to the Predator spyware
It's worth noting that Intellexa S.A., Intellexa Limited, Cytrox AD, and Cytrox Holdings ZRT were added to the aforementioned economic blocklist last year.
The development comes as new revelations about Predator's multi-tiered delivery infrastructure from Recorded Future, and Sekoia prompted the operators to shut down their servers.
The sanctions targeting the makers of Predator also arrived after the U.S. government unveiled a new policy last month that will allow it to impose visa restrictions on foreign individuals involved in the misuse of commercial spyware.
Citizen Lab security researcher John Scott-Railton described the OFAC designations as a huge deal, stating they mark the "first time they're used against a mercenary spyware company."
"The United States remains focused on establishing clear guardrails for the responsible development and use of these technologies while also ensuring the protection of human rights and civil liberties of individuals around the world," said Under Secretary of the Treasury for Terrorism and Financial Intelligence Brian E. Nelson.
Hackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
6.3.24 Virus The Hacker News
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK.
According to a report shared by Kroll with The Hacker News, TODDLERSHARK overlaps with known Kimsuky malware such as BabyShark and ReconShark.
"The threat actor gained access to the victim workstation by exploiting the exposed setup wizard of the ScreenConnect application," security researchers Keith Wojcieszek, George Glass, and Dave Truman said.
"They then leveraged their now 'hands on keyboard' access to use cmd.exe to execute mshta.exe with a URL to the Visual Basic (VB) based malware."
The ConnectWise flaws in question are CVE-2024-1708 and CVE-2024-1709, which came to light last month and have since come under heavy exploitation by multiple threat actors to deliver cryptocurrency miners, ransomware, remote access trojans, and stealer malware.
Kimsuky, also known as APT43, ARCHIPELAGO, Black Banshee, Emerald Sleet (previously Thallium), KTA082, Nickel Kimball, and Velvet Chollima, has steadily expanded its malware arsenal to include new tools, the most recent being GoBear and Troll Stealer.
BabyShark, first discovered in late 2018, is launched using an HTML Application (HTA) file. Once launched, the VB script malware exfiltrates system information to a command-and-control (C2) server, maintains persistence on the system, and awaits further instruction from the operator.
Then in May 2023, a variant of BabyShark dubbed ReconShark was observed being delivered to specifically targeted individuals through spear-phishing emails. TODDLERSHARK is assessed to be the latest evolution of the same malware due to code and behavioral similarities.
The malware, besides using a scheduled task for persistence, is engineered to capture and exfiltrate sensitive information about the compromised hosts, thereby acting as a valuable reconnaissance tool.
TODDLERSHARK "exhibits elements of polymorphic behavior in the form of changing identity strings in code, changing the position of code via generated junk code, and using uniquely generate C2 URLs, which could make this malware hard to detect in some environments," the researchers said.
The development comes as South Korea's National Intelligence Service (NIS) accused its northern counterpart of allegedly compromising the servers of two domestic (and unnamed) semiconductor manufacturers and pilfering valuable data.
The digital intrusions took place in December 2023 and February 2024. The threat actors are said to have targeted internet-exposed and vulnerable servers to gain initial access, subsequently leveraging living-off-the-land (LotL) techniques rather than dropping malware in order to better evade detection.
"North Korea may have begun preparations for its own production of semiconductors due to difficulties in procuring semiconductors due to sanctions against North Korea and increased demand due to the development of weapons such as satellite missiles," NIS said.
New BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
2.3.24 Virus The Hacker News
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive domain mimicking VMware.
"This latest version of Bifrost aims to bypass security measures and compromise targeted systems," Palo Alto Networks Unit 42 researchers Anmol Maurya and Siddharth Sharma said.
BIFROSE is one of the long-standing threats that has been active since 2004. It has been offered for sale in underground forums for up to $10,000 in the past, according to a report from Trend Micro in December 2015.
The malware has been put to use by a state-backed hacking group from China tracked as BlackTech (aka Circuit Panda, HUAPI, Manga Taurus, Palmerworm, PLEAD, Red Djinn, and Temp.Overboard), which has a history of striking organizations in Japan, Taiwan, and the U.S.
It's suspected that the threat actor purchased the source code or gained access to it around 2010, and repurposed the malware for use in its own campaigns via custom backdoors like KIVARS and XBOW.
Linux variants of BIFROSE (aka ELF_BIFROSE) have been observed since at least 2020 with capabilities to launch remote shells, download/upload files, and perform file operations.
"Attackers typically distribute Bifrost through email attachments or malicious websites," the researchers said. "Once installed on a victim's computer, Bifrost allows the attacker to gather sensitive information, like the victim's hostname and IP address."
What makes the latest variant noteworthy is that it reaches out to a command-and-control (C2) server with the name "download.vmfare[.]com" in an attempt to masquerade as VMware. The deceptive domain is resolved by contacting a Taiwan-based public DNS resolver with the IP address 168.95.1[.]1.
Unit 42 said it detected a spike in Bifrost activity since October 2023, identifying no less than 104 artifacts in its telemetry. It further discovered an Arm version of the malware, suggesting the threat actors are likely looking to expand their attack surface.

"With new variants that employ deceptive domain strategies like typosquatting, a recent spike in Bifrost activity highlights the dangerous nature of this malware," the researchers said.
The development comes as McAfee Labs detailed a new GuLoader campaign that propagates the malware through malicious SVG file attachments in email messages. The malware has also been observed being distributed via VBS scripts as part of a multi-stage payload delivery.
"This recent surge highlights its evolving tactics for broader reach and evasion," Trustwave SpiderLabs said in a post on X earlier this week.

The Bifrost and GuLoader attacks coincide with the release of a new version of the Warzone RAT, which recently had two of its operators arrested and its infrastructure dismantled by the U.S. government.
GTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
1.3.24 Virus The Hacker News

Threat hunters have discovered a new Linux malware called GTPDOOR that's designed to be deployed in telecom networks that are adjacent to GPRS roaming exchanges (GRX)
The malware is novel in the fact that it leverages the GPRS Tunnelling Protocol (GTP) for command-and-control (C2) communications.
GPRS roaming allows subscribers to access their GPRS services while they are beyond the reach of their home mobile network. This is facilitated by means of a GRX that transports the roaming traffic using GTP between the visited and the home Public Land Mobile Network (PLMN).
Security researcher haxrob, who discovered two GTPDOOR artifacts uploaded to VirusTotal from China and Italy, said the backdoor is likely linked to a known threat actor tracked as LightBasin (aka UNC1945), which was previously disclosed by CrowdStrike in October 2021 in connection with a series of attacks targeting the telecom sector to steal subscriber information and call metadata.

"When run, the first thing GTPDOOR does is process-name stomps itself – changing its process name to '[syslog]' – disguised as syslog invoked from the kernel," the researcher said. "It suppresses child signals and then opens a raw socket [that] will allow the implant to receive UDP messages that hit the network interfaces."
Put differently, GTPDOOR allows a threat actor that already has established persistence on the roaming exchange network to contact a compromised host by sending GTP-C Echo Request messages with a malicious payload.
This magic GTP-C Echo Request message acts as a conduit to transmit a command to be executed on the infected machine and return the results back to the remote host.
GTPDOOR "Can be covertly probed from an external network to elicit a response by sending a TCP packet to any port number," the researcher noted. "If the implant is active a crafted empty TCP packet is returned along with information if the destination port was open/responding on the host."
"This implant looks like it is designed to sit on compromised hosts that directly touch the GRX network – these are the systems that communicate to other telecommunication operator networks via the GRX."
New Backdoor Targeting European Officials Linked to Indian Diplomatic Events
1.3.24 Virus The Hacker News
A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new backdoor called WINELOADER.
The adversary, according to a report from Zscaler ThreatLabz, used a PDF file in emails that purported to come from the Ambassador of India, inviting diplomatic staff to a wine-tasting event on February 2, 2024.
The PDF document was uploaded to VirusTotal from Latvia on January 30, 2024. That said, there is evidence to suggest that this campaign may have been active at least since July 6, 2023, going by the discovery of another similar PDF file uploaded from the same country.
"The attack is characterized by its very low volume and the advanced tactics, techniques, and procedures (TTPs) employed in the malware and command-and-control (C2) infrastructure," security researchers Sudeep Singh and Roy Tay said.

Central to the novel attack is the PDF file that comes embedded with a malicious link that masquerades as a questionnaire, urging the recipients to fill it out in order to participate. Clicking on the link paves the way for an HTML application ("wine.hta") that contains obfuscated JavaScript code to retrieve an encoded ZIP archive bearing WINELOADER from the same domain.
The malware is packed with a core module that's designed to Execute modules from the C2 server, inject itself into another dynamic-link library (DLL), and update the sleep interval between beacon requests.
A notable aspect of the cyber incursions is the use of compromised websites for C2 and hosting intermediate payloads. It's suspected that the "C2 server only responds to specific types of requests at certain times," thereby making the attacks more evasive.
"The threat actor put additional effort into remaining undetected by evading memory forensics and automated URL scanning solutions," the researchers said.
Lazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
1.3.24 Virus The Hacker News

The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of infecting developer systems with malware.
The packages, now taken down, are pycryptoenv, pycryptoconf, quasarlib, and swapmempool. They have been collectively downloaded 3,269 times, with pycryptoconf accounting for the most downloads at 1,351.
"The package names pycryptoenv and pycryptoconf are similar to pycrypto, which is a Python package used for encryption algorithms in Python," JPCERT/CC researcher Shusei Tomonaga said. "Therefore, the attacker probably prepared the malware-containing malicious packages to target users' typos in installing Python packages."
The disclosure comes days after Phylum uncovered several rogue packages on the npm registry that have been used to single out software developers as part of a campaign codenamed Contagious Interview.
An interesting commonality between the two sets of attacks is that the malicious code is concealed within a test script ("test.py"). In this case, however, the test file is merely a smokescreen for what's an XOR-encoded DLL file, which, in turn, creates two DLL files named IconCache.db and NTUSER.DAT.
The attack sequence then uses NTUSER.DAT to load and execute IconCache.db, a malware called Comebacker that's responsible for establishing connections with a command-and-control (C2) server to fetch and run a Windows executable file.
JPCERT/CC said the packages are a continuation of a campaign that Phylum first detailed in November 2023 as leveraging crypto-themed npm modules to deliver Comebacker.
"Attackers may be targeting users' typos to have the malware downloaded," Tomonaga said. "When you install modules and other kinds of software in your development environment, please do so carefully to avoid installing unwanted packages."
Chinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
29.2.24 Virus The Hacker News
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security flaws in Ivanti Connect Secure VPN appliances.
UNC5325 abused CVE-2024-21893 to deliver a wide range of new malware called LITTLELAMB.WOOLTEA, PITSTOP, PITDOG, PITJET, and PITHOOK, as well as attempted to maintain persistent access to compromised appliances, Mandiant said.
The Google-owned threat intelligence firm has assessed with moderate confidence that UNC5325 is associated with UNC3886 owing to source code overlaps in LITTLELAMB.WOOLTEA and PITHOOK with malware used by the latter.
It's worth pointing out that UNC3886 has a track record of leveraging zero-day flaws in Fortinet and VMware solutions to deploy a variety of implants like VIRTUALPITA, VIRTUALPIE, THINCRUST, and CASTLETAP.
"UNC3886 has primarily targeted the defense industrial base, technology, and telecommunication organizations located in the U.S. and [Asia-Pacific] regions," Mandiant researchers said.
The active exploitation of CVE-2024-21893 – a server-side request forgery (SSRF) vulnerability in the SAML component of Ivanti Connect Secure, Ivanti Policy Secure, and Ivanti Neurons for ZTA – by UNC5325 is said to have occurred as early as January 19, 2024, targeting a limited number of devices.
The attack chain entails combining CVE-2024-21893 with a previously disclosed command injection vulnerability tracked as CVE-2024-21887 to gain unauthorized access to susceptible appliances, ultimately leading to the deployment of a new version of BUSHWALK.
Some instances have also involved the misuse of legitimate Ivanti components, such as SparkGateway plugins, to drop additional payloads. This includes the PITFUEL plugin to load a malicious shared object codenamed LITTLELAMB.WOOLTEA, which comes with capabilities to persist across system upgrade events, patches, and factory resets.
“While the limited attempts observed to maintain persistence have not been successful to date due to a lack of logic in the malware’s code to account for an encryption key mismatch, it further demonstrates the lengths UNC5325 will go to maintain access to priority targets and highlights the importance of ensuring network appliances have the latest updates and patches,” the company pointed out.
It further acts as a backdoor that supports command execution, file management, shell creation, SOCKS proxy, and network traffic tunneling.
Also observed is another malicious SparkGateway plugin dubbed PITDOG that injects a shared object known as PITHOOK in order to persistently execute an implant referred to as PITSTOP that's designed for shell command execution, file write, and file read on the compromised appliance.

Mandiant described the threat actor as having demonstrated a "nuanced understanding of the appliance and their ability to subvert detection throughout this campaign" and using living-off-the-land (LotL) techniques to fly under the radar.
The cybersecurity firm said it expects "UNC5325 as well as other China-nexus espionage actors to continue to leverage zero day vulnerabilities on network edge devices as well as appliance-specific malware to gain and maintain access to target environments."
Links Found Between Volt Typhoon and UTA0178#
The disclosure comes as industrial cybersecurity company Dragos attributed China-sponsored Volt Typhoon (aka Voltzite) to reconnaissance and enumeration activities aimed at multiple U.S.-based electric companies, emergency services, telecommunication providers, defense industrial bases, and satellite services.
"Voltzite's actions towards U.S. electric entities, telecommunications, and GIS systems signify clear objectives to identify vulnerabilities within the country's critical infrastructure that can be exploited in the future with destructive or disruptive cyber attacks," it said.
Volt Typhoon's victimology footprint has since expanded to include African electric transmission and distribution providers, with evidence connecting the adversary to UTA0178, a threat activity group linked to the zero-day exploitation of Ivanti Connect Secure flaws in early December 2023.

The cyber espionage actor, which heavily relies on LotL methods to sidestep detection, joins two other new groups, namely Gananite and Laurionite, that came to light in 2023, conducting long-term reconnaissance and intellectual property theft operations targeting critical infrastructure and government entities.
"Voltzite uses very minimal tooling and prefers to conduct their operations with as little a footprint as possible," Dragos explained. "Voltzite heavily focuses on detection evasion and long-term persistent access with the assessed intent of long-term espionage and data exfiltration."
(The story has been updated after publication to emphasize that the attempts to achieve persistence on the VPN appliances were unsuccessful.)
Open-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
28.2.24 Virus The Hacker News
An "intricately designed" remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other actors at no extra cost.
Written in C# and compatible with Windows 10 and Windows 11 operating systems, the open-source RAT comes with a "comprehensive set of features for remote system management," according to its developer, who goes by the name moom825.
It includes a SOCKS5 reverse proxy and the ability to record real-time audio, as well as incorporate a hidden virtual network computing (hVNC) module along the lines of DarkVNC, which allows attackers to gain remote access to an infected computer.
"Xeno RAT is developed entirely from scratch, ensuring a unique and tailored approach to remote access tools," the developer states in the project description. Another notable aspect is that it has a builder that enables the creation of bespoke variants of the malware.
It's worth noting that moom825 is also the developer of another C#-based RAT called DiscordRAT 2.0, which has been distributed by threat actors within a malicious npm package named node-hide-console-windows, as disclosed by ReversingLabs in October 2023.
Cybersecurity firm Cyfirma, in a report published last week, said it observed Xeno RAT being disseminated via the Discord content delivery network (CDN), once again underscoring how a rise in affordable and freely available malware is driving an increase in campaigns utilizing RATs.

"The primary vector in the form of a shortcut file, disguised as a WhatsApp screenshot, acts as a downloader," the company said. "The downloader downloads the ZIP archive from Discord CDN, extracts, and executes the next stage payload."
The multi-stage sequence leverages a technique called DLL side-loading to launch a malicious DLL, while simultaneously taking steps to establish persistence and evade analysis and detection.
The development comes as the AhnLab Security Intelligence Center (ASEC) revealed the use of a Gh0st RAT variant called Nood RAT that's used in attacks targeting Linux systems, allowing adversaries to harvest sensitive information.

"Nood RAT is a backdoor malware that can receive commands from the C&C server to perform malicious activities such as downloading malicious files, stealing systems' internal files, and executing commands," ASEC said.
"Although simple in form, it is equipped with the encryption feature to avoid network packet detection and can receive commands from threat actors to carry out multiple malicious activities."
New IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
27.2.24 Virus The Hacker News

Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as Remcos RAT using a malware loader called IDAT Loader.
The attack has been attributed to a threat actor tracked by the Computer Emergency Response Team of Ukraine (CERT-UA) under the moniker UAC-0184.
"The attack, as part of the IDAT Loader, used steganography as a technique," Morphisec researcher Michael Dereviashkin said in a report shared with The Hacker News. "While steganographic, or 'Stego' techniques are well-known, it is important to understand their roles in defense evasion, to better understand how to defend against such tactics."
IDAT Loader, which overlaps with another loader family called Hijack Loader, has been used to serve additional payloads like DanaBot, SystemBC, and RedLine Stealer in recent months. It has also been used by a threat actor tracked as TA544 to distribute Remcos RAT and SystemBC via phishing attacks.
The phishing campaign – first disclosed by CERT-UA in early January 2024 – entail using war-themed lures as a starting point to kick-start an infection chain that leads to the deployment of IDAT Loader, which, in turn, uses an embedded steganographic PNG to locate and extract Remcos RAT.
The development comes as CERT-UA revealed that defense forces in the country have been targeted via the Signal instant messaging app to distribute a booby-trapped Microsoft Excel document that executes COOKBOX, a PowerShell-based malware that's capable of loading and executing cmdlets. CERT-UA has attributed the activity to a cluster dubbed UAC-0149.
It also follows the resurgence of malware campaigns propagating PikaBot malware since February 8, 2024, using an updated variant that appears to be currently under active development.
"This version of the PikaBot loader uses a new unpacking method and heavy obfuscation," Elastic Security Labs said. "The core module has added a new string decryption implementation, changes to obfuscation functionality, and various other modifications."
North Korean Hackers Targeting Developers with Malicious npm Packages
27.2.24 Virus The Hacker News
A set of fake npm packages discovered on the Node.js repository has been found to share ties with North Korean state-sponsored actors, new findings from Phylum show.
The packages are named execution-time-async, data-time-utils, login-time-utils, mongodb-connection-utils, and mongodb-execution-utils.
One of the packages in question, execution-time-async, masquerades as its legitimate counterpart execution-time, a library with more than 27,000 weekly downloads. Execution-time is a Node.js utility used to measure execution time in code.
It "actually installs several malicious scripts including a cryptocurrency and credential stealer," Phylum said, describing the campaign as a software supply chain attack targeting developers. The package was downloaded 302 times since February 4, 2024, before being taken down.
In an interesting twist, the threat actors made efforts to conceal the obfuscated malicious code in a test file, which is designed to fetch next-stage payloads from a remote server, steal credentials from web browsers like Brave, Google Chrome, and Opera, and retrieve a Python script, which, in turn, downloads other scripts -
~/.n2/pay, which can run arbitrary commands, download and launch ~/.n2/bow and ~/.n2/adc, terminate Brave and Google Chrome, and even delete itself
~/.n2/bow, which is a Python-based browser password stealer
~/.n2/adc, which installs AnyDesk on Windows
Phylum said it identified comments in the source code ("/Users/ninoacuna/") that made it possible to track down a now-deleted GitHub profile with the same name ("Nino Acuna" or binaryExDev) containing a repository called File-Uploader.
Present within the repository were Python scripts referencing the same IP addresses (162.218.114[.]83 – subsequently changed to 45.61.169[.]99) used to fetch the aforementioned Python scripts.

It's suspected that the attack is a work in progress, as at least four more packages with identical features have made their way to the npm package repository, attracting a total of 325 downloads -
data-time-utils - 52 downloads starting from February 15
login-time-utils - 171 downloads starting from February 15
mongodb-connection-utils - 51 downloads starting from February 19
mongodb-execution-utils - 51 downloads starting from February 19
Connections to North Korean Actors Emerge#
Phylum, which also analyzed the two GitHub accounts that binaryExDev follows, uncovered another repository known as mave-finance-org/auth-playground, which has been forked no less than a dozen times by other accounts.

While forking a repository in itself is not out of the ordinary, an unusual aspect of some of these forked repositories were that they were renamed as "auth-demo" or "auth-challenge," raising the possibility that the original repository may have been shared as part of a coding test for a job interview.
The repository was later moved to banus-finance-org/auth-sandbox, Dexbanus-org/live-coding-sandbox, and mave-finance/next-assessment, indicating attempts to actively get around GitHub's takedown attempts. All these accounts have been removed.
What's more, the next-assessment package was found to contain a dependency "json-mock-config-server" that's not listed on the npm registry, but rather served directly from the domain npm.mave[.]finance.
It's worth noting that Banus claims to be a decentralized perpetual spot exchange based in Hong Kong, with the company even posting a job opportunity for a senior frontend developer on February 21, 2024. It's currently not clear if this is a genuine job opening or if it's an elaborate social engineering scheme.
The connections to North Korean threat actors come from the fact that the obfuscated JavaScript embedded in the npm package overlaps with another JavaScript-based malware dubbed BeaverTail that's propagated via a similar mechanism. The campaign was codenamed Contagious Interview by Palo Alto Networks Unit 42 in November 2023.
Contagious Interview is a little different from Operation Dream Job – which is linked to the Lazarus Group – in that it's mainly focuses on targeting developers through fake identities in freelance job portals to trick them into installing rogue npm packages, Michael Sikorski, vice president and CTO of Palo Alto Networks Unit 42, told The Hacker News at the time.
One of the developers who fell victim to the campaign has since confirmed to Phylum that the repository is shared under the guise of a live coding interview, although they said they never installed it on their system.
"More than ever, it is important for both individual developers as well as software development organizations to remain vigilant against these attacks in open-source code," the company said.
Banking Trojans Target Latin America and Europe Through Google Cloud Run
27.2.24 Virus The Hacker News

Cybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various banking trojans such as Astaroth (aka Guildma), Mekotio, and Ousaban (aka Javali) to targets across Latin America (LATAM) and Europe.
"The infection chains associated with these malware families feature the use of malicious Microsoft Installers (MSIs) that function as droppers or downloaders for the final malware payload(s)," Cisco Talos researchers disclosed last week.
The high-volume malware distribution campaigns, observed since September 2023, have employed the same storage bucket within Google Cloud for propagation, suggesting potential links between the threat actors behind the distribution campaigns.
Google Cloud Run is a managed compute platform that enables users to run frontend and backend services, batch jobs, deploy websites and applications, and queue processing workloads without having to manage or scale the infrastructure.
"Adversaries may view Google Cloud Run as an inexpensive, yet effective way to deploy distribution infrastructure on platforms that most organizations likely do not prevent internal systems from accessing," the researchers said.
A majority of the systems used to send phishing messages originate from Brazil, followed by the U.S., Russia, Mexico, Argentina, Ecuador, South Africa, France, Spain, and Bangladesh. The emails bear themes related to invoices or financial and tax documents, in some cases purporting to be from local government tax agencies.
Embedded within these messages are links to a website hosted on run[.]app, resulting in the delivery of a ZIP archive containing a malicious MSI file either directly or via 302 redirects to a Google Cloud Storage location, where the installer is stored.
The threat actors have also been observed attempting to evade detection using geofencing tricks by redirecting visitors to these URLs to a legitimate site like Google when accessing them with a U.S. IP address.
Besides leveraging the same infrastructure to deliver both Mekotio and Astaroth, the infection chain associated with the latter acts as a conduit to distribute Ousaban.
Astaroth, Mekotio, and Ousaban are all designed to single out financial institutions, keeping tabs on users' web browsing activity as well as logging keystrokes and taking screenshots should one of the target bank websites be open.
Ousaban has a history of weaponizing cloud services to its advantage, having previously employed Amazon S3 and Microsoft Azure to download second-stage payloads, and Google Docs to retrieve command-and-control (C2) configuration.
The development comes amid phishing campaigns propagating malware families such as DCRat, Remcos RAT, and DarkVNC that are capable of harvesting sensitive data and taking control of compromised hosts.
It also follows an uptick in threat actors deploying QR codes in phishing and email-based attacks (aka quishing) to trick potential victims into installing malware on their mobile devices.

"In a separate attack, the adversaries sent targets spear-phishing emails with malicious QR codes pointing to fake Microsoft Office 365 login pages that eventually steal the user's login credentials when entered," Talos said.
"QR code attacks are particularly dangerous because they move the attack vector off a protected computer and onto the target's personal mobile device, which usually has fewer security protections in place and ultimately has the sensitive information that attackers are after."
Phishing campaigns have also set their eyes on the oil and gas sector to deploy an information stealer called Rhadamanthys, which has currently reached version 0.6.0, highlighting a steady stream of patches and updates by its developers.
"The campaign starts with a phishing email using a vehicle incident report to lure victims into interacting with an embedded link that abuses an open redirect on a legitimate domain, primarily Google Maps or Google Images," Cofense said.
Users who click on the link are then redirected to a website hosting a bogus PDF file, which, in reality, is a clickable image that contacts a GitHub repository and downloads a ZIP archive containing the stealer executable.
"Once a victim attempts to interact with the executable, the malware will unpack and start a connection with a command-and-control (C2) location that collects any stolen credentials, cryptocurrency wallets, or other sensitive information," the company added.
Other campaigns have abused email marketing tools like Twilio's SendGrid to obtain client mailing lists and take advantage of stolen credentials to send out convincing-looking phishing emails, per Kaspersky.
"What makes this campaign particularly insidious is that the phishing emails bypass traditional security measures," the Russian cybersecurity company noted. "Since they are sent through a legitimate service and contain no obvious signs of phishing, they may evade detection by automatic filters."
These phishing activities are further fueled by the easy availability of phishing kits such as Greatness and Tycoon, which have become a cost-effective and scalable means for aspiring cyber criminals to mount malicious campaigns.
"Tycoon Group [phishing-as-a-service] is sold and marketed on Telegram for as low as $120," Trustwave SpiderLabs researcher Rodel Mendrez said last week, noting the service first came into being around August 2023.
"Its key selling features include the ability to bypass Microsoft two-factor authentication, achieve 'link speed at the highest level,' and leveraging Cloudflare to evade antibot measures, ensuring the persistence of undetected phishing links."
Dormant PyPI Package Compromised to Spread Nova Sentinel Malware
24.2.24 Virus The Hacker News
A dormant package available on the Python Package Index (PyPI) repository was updated nearly after two years to propagate an information stealer malware called Nova Sentinel.
The package, named django-log-tracker, was first published to PyPI in April 2022, according to software supply chain security firm Phylum, which detected an anomalous update to the library on February 21, 2024.
While the linked GitHub repository hasn't been updated since April 10, 2022, the introduction of a malicious update suggests a likely compromise of the PyPI account belonging to the developer.
Django-log-tracker has been downloaded 3,866 times to date, with the rogue version (1.0.4) downloaded 107 times on the date it was published. The package is no longer available for download from PyPI.
"In the malicious update, the attacker stripped the package of most of its original content, leaving only an __init__.py and example.py file behind," the company said.
The changes, simple and self-explanatory, involve fetching an executable named "Updater_1.4.4_x64.exe" from a remote server ("45.88.180[.]54"), followed by launching it using the Python os.startfile() function.

The binary, for its part, comes embedded with Nova Sentinel, a stealer malware that was first documented by Sekoia in November 2023 as being distributed in the form of fake Electron apps on bogus sites offering video game downloads.
"What's interesting about this particular case [...] is that the attack vector appeared to be an attempted supply-chain attack via a compromised PyPI account," Phylum said.
"If this had been a really popular package, any project with this package listed as a dependency without a version specified or a flexible version specified in their dependency file would have pulled the latest, malicious version of this package."
Russian Government Software Backdoored to Deploy Konni RAT Malware
22.2.24 Virus The Hacker News
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored to deliver a remote access trojan called Konni RAT (aka UpDog).
The findings come from German cybersecurity company DCSO, which linked the activity as originating from the Democratic People's Republic of Korea (DPRK)-nexus actors targeting Russia.
The Konni (aka Opal Sleet, Osmium, or TA406) activity cluster has an established pattern of deploying Konni RAT against Russian entities, with the threat actor also linked to attacks directed against MID at least since October 2021.
In November 2023, Fortinet FortiGuard Labs revealed the use of Russian-language Microsoft Word documents to deliver malware capable of harvesting sensitive information from compromised Windows hosts.
DCSO said the packaging of Konni RAT within software installers is a technique previously adopted by the group in October 2023, when it was found to leverage a backdoored Russian tax filing software named Spravki BK to distribute the trojan.
"In this instance, the backdoored installer appears to be for a tool named 'Statistika KZU' (Cтатистика КЗУ)," the Berlin-based company said.

"On the basis of install paths, file metadata, and user manuals bundled into the installer, [...] the software is intended for internal use within the Russian Ministry of Foreign Affairs (MID), specifically for the relaying of annual report files from overseas consular posts (КЗУ — консульские загранучреждения) to the Consular Department of the MID via a secure channel."
The trojanized installer is an MSI file that, when launched, initiates the infection sequence to establish contact with a command-and-control (C2) server to await further instructions.

The remote access trojan, which comes with capabilities for file transfers and command execution, is believed to have been put to use as early as 2014, and has also been utilized by other North Korean threat actors known as Kimsuky and ScarCruft (aka APT37).
It's currently not clear how the threat actors managed to obtain the installer, given that it's not publicly obtainable. But it's suspected that the long history of espionage operations targeting Russia may have helped them identify prospective tools for subsequent attacks.
While North Korea's targeting of Russia is not new, the development comes amid growing geopolitical proximity between the two countries. State media from the Hermit Kingdom reported this week that Russian President Vladimir Putin has given leader Kim Jong Un a luxury Russian-made car.
"To some extent, this should not come as a surprise; increasing strategic proximity would not be expected to fully overwrite extant DPRK collection needs, with an ongoing need on the part of the DPRK to be able to assess and verify Russian foreign policy planning and objectives," DCSO said.
New Malicious PyPI Packages Caught Using Covert Side-Loading Tactics
21.2.24 Virus The Hacker News
Cybersecurity researchers have discovered two malicious packages on the Python Package Index (PyPI) repository that were found leveraging a technique called DLL side-loading to circumvent detection by security software and run malicious code.
The packages, named NP6HelperHttptest and NP6HelperHttper, were each downloaded 537 and 166 times, respectively, before they were taken down.
"The latest discovery is an example of DLL sideloading executed by an open-source package that suggests the scope of software supply chain threats is expanding," ReversingLabs researcher Petar Kirhmajer said in a report shared with The Hacker News.
The name NP6 is notable as it refers to a legitimate marketing automation solution made by ChapsVision. In particular, the fake packages are typosquats of NP6HelperHttp and NP6HelperConfig, which are helper tools published by one of ChapsVision's employees to PyPI.
In other words, the goal is to trick developers searching for NP6HelperHttp and NP6HelperConfig into downloading their rogue counterparts.

Contained within the two libraries is a setup.py script that's designed to download two files, an actual executable from Beijing-based Kingsoft Corporation ("ComServer.exe") that's vulnerable to DLL side-loading and the malicious DLL to be side-loaded ("dgdeskband64.dll").
In side-loading the DLL, the aim is to avoid detection of the malicious code, as observed previously in the case of an npm package called aabquerys that also leveraged the same technique to execute code capable of deploying a remote access trojan.
The DLL, for its part, reaches out to an attacker-controlled domain ("us.archive-ubuntu[.]top") to fetch a GIF file that, in reality, is a piece of shellcode for a Cobalt Strike Beacon, a post-exploitation toolkit used for red teaming.
There is evidence to suggest that the packages are part of a wider campaign that involves the distribution of similar executables that are susceptible to DLL side-loading.
"Development organizations need to be aware of the threats related to supply chain security and open-source package repositories," security researcher Karlo Zanki said.
"Even if they are not using open-source package repositories, that doesn't mean that threat actors won't abuse them to impersonate companies and their software products and tools."
Malicious 'SNS Sender' Script Abuses AWS for Bulk Smishing Attacks
17.2.24 Virus The Hacker News
A malicious Python script known as SNS Sender is being advertised as a way for threat actors to send bulk smishing messages by abusing Amazon Web Services (AWS) Simple Notification Service (SNS).
The SMS phishing messages are designed to propagate malicious links that are designed to capture victims' personally identifiable information (PII) and payment card details, SentinelOne said in a new report, attributing it to a threat actor named ARDUINO_DAS.
"The smishing scams often take the guise of a message from the United States Postal Service (USPS) regarding a missed package delivery," security researcher Alex Delamotte said.
SNS Sender is also the first tool observed in the wild that leverages AWS SNS to conduct SMS spamming attacks. SentinelOne said that it identified links between ARDUINO_DAS and more than 150 phishing kits offered for sale.
The malware requires a list of phishing links stored in a file named links.txt in its working directory, in addition to a list of AWS access keys, the phone numbers to target, the sender ID (aka display name), and the content of the message.
The mandatory inclusion of sender ID for sending the scam texts is noteworthy because support for sender IDs varies from country to country. This suggests that the author of SNS Sender is likely from a country where the sender ID is a conventional practice.
"For example, carriers in the United States don't support sender IDs at all, but carriers in India require senders to use sender IDs," Amazon says in its documentation.
There is evidence to suggest that this operation may have been active since at least July 2022, going by bank logs containing references to ARDUINO_DAS that have been shared on carding forums like Crax Pro.
A vast majority of the phishing kits are USPS-themed, with the campaigns directing users to bogus package tracking pages that prompt users to enter their personal and credit/debit card information, as evidenced by security researcher @JCyberSec_ on X (formerly Twitter) in early September 2022.
"Do you think the deploying actor knows all the kits have a hidden backdoor sending the logs to another place?," the researcher further noted.
If anything, the development represents commodity threat actors' ongoing attempts to exploit cloud environments for smishing campaigns. In April 2023, Permiso revealed an activity cluster that took advantage of previously exposed AWS access keys to infiltrate AWS servers and send SMS messages using SNS.
The findings also follow the discovery of a new dropper codenamed TicTacToe that's likely sold as a service to threat actors and has been observed being used to propagate a wide variety of information stealers and remote access trojans (RATs) targeting Windows users throughout 2023.
Fortinet FortiGuard Labs, which shed light on the malware, said it's deployed by means of a four-stage infection chain that starts with an ISO file embedded within email messages.
Another relevant example of threat actors continuously innovating their tactics concerns the use of advertising networks to stage effective spam campaigns and deploy malware such as DarkGate.
"The threat actor proxied links through an advertising network to evade detection and capture analytics about their victims," HP Wolf Security said. "The campaigns were initiated through malicious PDF attachments posing as OneDrive error messages, leading to the malware."
The infosec arm of the PC maker also highlighted the misuse of legitimate platforms like Discord to stage and distribute malware, a trend that has become increasingly common in recent years, prompting the company to switch to temporary file links by the end of last year.
"Discord is known for its robust and reliable infrastructure, and it is widely trusted," Intel 471 said. "Organizations often allowlist Discord, meaning that links and connections to it are not restricted. This makes its popularity among threat actors unsurprising given its reputation and widespread use."
Russian Turla Hackers Target Polish NGOs with New TinyTurla-NG Backdoor
17.2.24 Virus The Hacker News
The Russia-linked threat actor known as Turla has been observed using a new backdoor called TinyTurla-NG as part of a three-month-long campaign targeting Polish non-governmental organizations in December 2023.
"TinyTurla-NG, just like TinyTurla, is a small 'last chance' backdoor that is left behind to be used when all other unauthorized access/backdoor mechanisms have failed or been detected on the infected systems," Cisco Talos said in a technical report published today.
TinyTurla-NG is so named for exhibiting similarities with TinyTurla, another implant used by the adversarial collective in intrusions aimed at the U.S., Germany, and Afghanistan since at least 2020. TinyTurla was first documented by the cybersecurity company in September 2021.
Turla, also known by the names Iron Hunter, Pensive Ursa, Secret Blizzard (formerly Krypton), Snake, Uroburos, and Venomous Bear, is a Russian state-affiliated threat actor linked to the Federal Security Service (FSB).
In recent months, the threat actor has singled out the defense sector in Ukraine and Eastern Europe with a novel .NET-based backdoor called DeliveryCheck, while also upgrading its staple second-stage implant referred to as Kazuar, which it has put to use as early as 2017.
The latest campaign involving TinyTurla-NG dates back to December 18, 2023, and is said to have been ongoing up until January 27, 2024. However, it's suspected that the activity may have actually commenced in November 2023 based on the malware compilation dates.
It's currently not known how the backdoor is distributed to victim environments, but it has been found to employ compromised WordPress-based websites as command-and-control (C2) endpoints to fetch and execute instructions, enabling it to run commands via PowerShell or Command Prompt (cmd.exe) as well as download/upload files.
TinyTurla-NG also acts as a conduit to deliver PowerShell scripts dubbed TurlaPower-NG that are designed to exfiltrate key material used to secure the password databases of popular password management software in the form of a ZIP archive.
"This campaign appears to be highly targeted and focused on a small number of organizations, of which until now we can only confirm Poland based ones," a Cisco Talos researcher told The Hacker News, noting that the assessment is based on the current visibility.
"This campaign is highly compartmentalized, a few compromised websites acting as C2s contact a few samples, meaning that it's not easy to pivot from one sample/C2 to others using the same infrastructure that would give us confidence they are related."
The disclosure comes as Microsoft and OpenAI revealed that nation-state actors from Russia are exploring generative artificial intelligence (AI) tools, including large language models (LLMs) like ChatGPT, to understand satellite communication protocols, radar imaging technologies, and seek support with scripting tasks.
Chinese Hackers Using Deepfakes in Advanced Mobile Banking Malware Attacks
17.2.24 Virus The Hacker News
A Chinese-speaking threat actor codenamed GoldFactory has been attributed to the development of highly sophisticated banking trojans, including a previously undocumented iOS malware called GoldPickaxe that's capable of harvesting identity documents, facial recognition data, and intercepting SMS.
"The GoldPickaxe family is available for both iOS and Android platforms," Singapore-headquartered Group-IB said in an extensive report shared with The Hacker News. "GoldFactory is believed to be a well-organized Chinese-speaking cybercrime group with close connections to Gigabud."
Active since at least mid-2023, GoldFactory is also responsible for another Android-based banking malware called GoldDigger and its enhanced variant GoldDiggerPlus as well as GoldKefu, an embedded trojan inside GoldDiggerPlus.
Social engineering campaigns distributing the malware have been found to target the Asia-Pacific region, specifically Thailand and Vietnam, by masquerading as local banks and government organizations.
In these attacks, prospective victims are sent smishing and phishing messages and guided to switch the conversation to instant messaging apps like LINE, before sending bogus URLs that lead to the deployment of GoldPickaxe on the devices.
Some of these malicious apps targeting Android are hosted on counterfeit websites resembling Google Play Store pages or fake corporate websites to complete the installation process.
GoldPickaxe for iOS, however, employs a different distribution scheme, with successive iterations leveraging Apple's TestFlight platform and booby-trapped URLs that prompt users to download an Mobile Device Management (MDM) profile to grant complete control over the iOS devices and install the rogue app.
Both these propagation mechanisms were disclosed by the Thailand Banking Sector CERT (TB-CERT) and the Cyber Crime Investigation Bureau (CCIB), respectively, in November 2023.

The sophistication of GoldPickaxe is also evident in the fact that it's designed to get around security measures imposed by Thailand that require users to confirm larger transactions using facial recognition to prevent fraud.
"GoldPickaxe prompts the victim to record a video as a confirmation method in the fake application," security researchers Andrey Polovinkin and Sharmine Low said. "The recorded video is then used as raw material for the creation of deepfake videos facilitated by face-swapping artificial intelligence services."
Furthermore, the Android and iOS flavors of the malware are equipped to collect the victim's ID documents and photos, intercept incoming SMS messages, and proxy traffic through the compromised device. It's suspected that the GoldFactory actors use their own devices to sign-in to the bank application and perform unauthorized fund transfers.

That having said, the iOS variant exhibits fewer functionalities when compared to its Android counterpart owing to the closed nature of the iOS operating system and relatively stricter nature of iOS permissions.
The Android version – considered an evolutionary successor of GoldDiggerPlus – also poses as over 20 different applications from Thailand's government, the financial sector, and utility companies to steal login credentials from these services. However, it's currently not clear what the threat actors do with this information.
Another notable aspect of the malware is its abuse of Android's accessibility services to log keystrokes and extract on-screen content.

GoldDigger also shares code-level similarities to GoldPickaxe, although it is chiefly designed to steal banking credentials, while the latter is geared more towards gathering of personal information from victims. No GoldDigger artifacts aimed at iOS devices have been identified to date.
"The primary feature of GoldDigger is that it targets over 50 applications from Vietnamese financial companies, including their packages' names in the trojan," the researchers said. "Whenever the targeted applications open, it will save the text displayed or written on the UI, including passwords, when they are entered."
The base version of GoldDigger, which was first discovered in June 2023 and continues to be still in circulation, has since paved the way for more upgraded variants, including GoldDiggerPlus, which comes embedded with another trojan APK component dubbed GoldKefu, to unleash the malicious actions.
GoldDiggerPlus is said to have emerged in September 2023, with GoldKefu impersonating a popular Vietnamese messaging app to siphon banking credentials associated with 10 financial institutions.
The Android trojan, which is used in conjunction with GoldKefu, uses fake overlays to collect the login information if the most recently opened application belongs to the target list, unlike GoldDigger which relies mainly on Android's accessibility services.
Goldkefu also integrates with the Agora Software Development Kit (SDK) to facilitate interactive voice and video calls and trick victims into contacting a bogus bank customer service by sending fake alerts that induce a false sense of urgency by claiming that a fund transfer to the tune of 3 million Thai Baht has taken place on their accounts.

If anything, the development is a sign that the mobile malware landscape remains a lucrative market for cybercriminals looking for quick financial gain, even as they find ways to circumvent defensive measures erected by banks to counter such threats. It also demonstrates the ever-shifting and dynamic nature of social engineering schemes that aim to deliver malware to victims' devices.
To mitigate the risks posed by GoldFactory and its suite of mobile banking malware, it's strongly advised not to click on suspicious links, install any app from untrusted sites, as they are a common vector for malware, and periodically review the permissions given to apps, particularly those requesting for Android's accessibility services.
"GoldFactory is a resourceful team adept at various tactics, including impersonation, accessibility keylogging, fake banking websites, fake bank alerts, fake call screens, identity, and facial recognition data collection," the researchers said. "The team comprises separate development and operator groups dedicated to specific regions."
"The gang has well-defined processes and operational maturity and constantly enhances its toolset to align with the targeted environment showcasing a high proficiency in malware development."
Bumblebee Malware Returns with New Tricks, Targeting U.S. Businesses
17.2.24 Virus The Hacker News
The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new phishing campaign observed in February 2024.
Enterprise security firm Proofpoint said the activity targets organizations in the U.S. with voicemail-themed lures containing links to OneDrive URLs.
"The URLs led to a Word file with names such as "ReleaseEvans#96.docm" (the digits before the file extension varied)," the company said in a Tuesday report. "The Word document spoofed the consumer electronics company Humane."
Opening the document leverages VBA macros to launch a PowerShell command to download and execute another PowerShell script from a remote server that, in turn, retrieves and runs the Bumblebee loader.
Bumblebee, first spotted in March 2022, is mainly designed to download and execute follow-on payloads such as ransomware. It has been put to use by multiple crimeware threat actors that previously observed delivering BazaLoader (aka BazarLoader) and IcedID.
It's also suspected to be developed by threat actors the Conti and TrickBot cybercrime syndicate as a replacement for BazarLoader. In September 2023, Intel 471 disclosed a Bumblebee distribution campaign that employed Web Distributed Authoring and Versioning (WebDAV) servers to disseminate the loader.
The attack chain is notable for its reliance on macro-enabled documents in the attack chain, especially considering Microsoft began blocking macros in Office files downloaded from the internet by default starting July 2022, prompting threat actors to modify and diversify their approaches.
The macro-based attack is also markedly different from pre-hiatus campaigns in which the phishing emails came with zipped LNK files bearing Bumblebee executables or HTML attachments that leveraged HTML smuggling to drop a RAR file, which exploited the WinRAR flaw tracked as CVE-2023-38831 to install the loader.
The return of Bumblebee also coincides with the reappearance of new variants of QakBot, ZLoader, and PikaBot, with samples of QakBot distributed in the form of Microsoft Software Installer (MSI) files.
"The .MSI drops a Windows .cab (Cabinet) archive, which in turn contains a DLL," cybersecurity firm Sophos said on Mastodon. "The .MSI extracts the DLL from the .cab, and executes it using shellcode. The shellcode causes the DLL to spawn a second copy of itself and inject the bot code into the second instance's memory space."
The latest QakBot artifacts have been found to harden the encryption used to conceal strings and other information, including employing a crypter malware called DaveCrypter, making it more challenging to analyze. The new generation also reinstates the ability to detect whether the malware was running inside a virtual machine or sandbox.
Another crucial modification includes encrypting all communications between the malware and the command-and-control (C2) server using AES-256, a stronger method than was used in versions prior to the dismantling of QakBot's infrastructure in late August 2023.
"The takedown of the QakBot botnet infrastructure was a victory, but the bot's creators remain free, and someone who has access to QakBot's original source code has been experimenting with new builds and testing the waters with these latest variants," Andrew Brandt, principal researcher at Sophos X-Ops, said.
"One of the most notable changes involve a change to the encryption algorithm the bot uses to conceal default configurations hardcoded into the bot, making it more difficult for analysts to see how the malware operates; the attackers are also restoring previously deprecated features, such as virtual machine (VM) awareness, and testing them out in these new versions."
QakBot has also emerged as the second most prevalent malware for January 2024, trailing behind FakeUpdates (aka SocGholish) but ahead of other families like Formbook, Nanocore, AsyncRAT, Remcos RAT, and Agent Tesla.
The development comes as Malwarebytes revealed a new campaign in which phishing sites mimicking financial institutions like Barclays trick potential targets into downloading legitimate remote desktop software like AnyDesk to purportedly resolve non-existent issues and ultimately allow threat actors to gain control of the machine.
DarkMe Malware Targets Traders Using Microsoft SmartScreen Zero-Day Vulnerability
17.2.24 Virus The Hacker News

A newly disclosed security flaw in the Microsoft Defender SmartScreen has been exploited as a zero-day by an advanced persistent threat actor called Water Hydra (aka DarkCasino) targeting financial market traders.
Trend Micro, which began tracking the campaign in late December 2023, said it entails the exploitation of CVE-2024-21412, a security bypass vulnerability related to Internet Shortcut Files (.URL).
"In this attack chain, the threat actor leveraged CVE-2024-21412 to bypass Microsoft Defender SmartScreen and infect victims with the DarkMe malware," the cybersecurity firm said in a Tuesday report.
Microsoft, which addressed the flaw in its February Patch Tuesday update, said an unauthenticated attacker could exploit the flaw by sending the targeted user a specially crafted file in order to bypass displayed security checks.
However, successful exploitation banks on the prerequisite that the threat actor convinces the victim to click on the file link to view the attacker-controlled content.
The infection procedure documented by Trend Micro weaponizes CVE-2024-21412 to drop a malicious installer file ("7z.msi") by clicking on a booby-trapped URL ("fxbulls[.]ru") distributed via forex trading forums under the pretext of sharing a link to a stock chart image that, in reality, is an internet shortcut file ("photo_2023-12-29.jpg.url").
"The landing page on fxbulls[.]ru contains a link to a malicious WebDAV share with a filtered crafted view," security researchers Peter Girnus, Aliakbar Zahravi, and Simon Zuckerbraun said.
"When users click on this link, the browser will ask them to open the link in Windows Explorer. This is not a security prompt, so the user might not think that this link is malicious."
The clever trick that makes this possible is the threat actor's abuse of the search: application protocol, which is used for calling the desktop search application on Windows and has been abused in the past to deliver malware.
The rogue internet shortcut file, for its part, points to another internet shortcut file hosted on a remote server ("2.url"), which, in turn, points to a CMD shell script within a ZIP archive hosted on the same server ("a2.zip/a2.cmd").
This unusual referencing stems from the fact that "calling a shortcut within another shortcut was sufficient to evade SmartScreen, which failed to properly apply Mark of the Web (MotW), a critical Windows component that alerts users when opening or running files from an untrusted source."
The end goal of the campaign is to deliver a Visual Basic trojan known as DarkMe stealthily in the background while displaying the stock graph to the victim to keep up the ruse upon completion of the exploitation and infection chain.
DarkMe comes with capabilities to download and execute additional instructions, alongside registering itself with a command-and-control (C2) server and gathering information from the compromised system.
The development comes amid a new trend where zero-days found by cybercrime groups end up getting incorporated into attack chains deployed by nation-state hacking groups to launch sophisticated attacks.
"Water Hydra possess the technical knowledge and tools to discover and exploit zero-day vulnerabilities in advanced campaigns, deploying highly destructive malware such as DarkMe," the researchers said.
Glupteba Botnet Evades Detection with Undocumented UEFI Bootkit
17.2.24 Virus The Hacker News
The Glupteba botnet has been found to incorporate a previously undocumented Unified Extensible Firmware Interface (UEFI) bootkit feature, adding another layer of sophistication and stealth to the malware.
"This bootkit can intervene and control the [operating system] boot process, enabling Glupteba to hide itself and create a stealthy persistence that can be extremely difficult to detect and remove," Palo Alto Networks Unit 42 researchers Lior Rochberger and Dan Yashnik said in a Monday analysis.
Glupteba is a fully-featured information stealer and backdoor capable of facilitating illicit cryptocurrency mining and deploying proxy components on infected hosts. It's also known to leverage the Bitcoin blockchain as a backup command-and-control (C2) system, making it resilient to takedown efforts.
Some of the other functions allow it to deliver additional payloads, siphon credentials, and credit card data, perform ad fraud, and even exploit routers to gain credentials and remote administrative access.
Over the past decade, the modular malware has metamorphosed into a sophisticated threat employing elaborate multi-stage infection chains to sidestep detection by security solutions.
A November 2023 campaign observed by the cybersecurity firm entails the use of pay-per-install (PPI) services such as Ruzki to distribute Glupteba. In September 2022, Sekoia linked Ruzki to activity clusters leveraging PrivateLoader as a conduit to propagate next-stage malware.
This takes the form of large-scale phishing attacks in which PrivateLoader is delivered under the guise of installation files for cracked software, which then loads SmokeLoader that, in turn, launches RedLine Stealer and Amadey, with the latter ultimately dropping Glupteba.

"Threat actors often distribute Glupteba as part of a complex infection chain spreading several malware families at the same time," the researchers explained. "This infection chain often starts with a PrivateLoader or SmokeLoader infection that loads other malware families, then loads Glupteba."
In a sign that the malware is being actively maintained, Glupteba comes fitted with a UEFI bootkit by incorporating a modified version of an open-source project called EfiGuard, which is capable of disabling PatchGuard and Driver Signature Enforcement (DSE) at boot time.
It's worth pointing out that previous versions of the malware were found to "install a kernel driver the bot uses as a rootkit, and make other changes that weaken the security posture of an infected host."
Glupteba's resurfaced campaign in 2023 has been described as widespread and affecting multiple regions and industries spread across countries as varied as Greece, Nepal, Bangladesh, Brazil, Korea, Algeria, Ukraine, Slovakia, Turkey, Italy, and Sweden.
"Glupteba malware continues to stand out as a notable example of the complexity and adaptability exhibited by modern cybercriminals," the researchers said.
"The identification of an undocumented UEFI bypass technique within Glupteba underscores this malware's capacity for innovation and evasion. Furthermore, with its role in distributing Glupteba, the PPI ecosystem highlights the collaboration and monetization strategies employed by cybercriminals in their attempts at mass infections."
PikaBot Resurfaces with Streamlined Code and Deceptive Tactics
17.2.24 Virus The Hacker News
The threat actors behind the PikaBot malware have made significant changes to the malware in what has been described as a case of "devolution."
"Although it appears to be in a new development cycle and testing phase, the developers have reduced the complexity of the code by removing advanced obfuscation techniques and changing the network communications," Zscaler ThreatLabz researcher Nikolaos Pantazopoulos said.
PikaBot, first documented by the cybersecurity firm in May 2023, is a malware loader and a backdoor that can execute commands and inject payloads from a command-and-control (C2) server as well as allow the attacker to control the infected host.
It is also known to halt its execution should the system's language be Russian or Ukrainian, indicating that the operators are either based in Russia or Ukraine.
In recent months, both PikaBot and another loader called DarkGate have emerged as attractive replacements for threat actors such as Water Curupira (aka TA577) to obtain initial access to target networks via phishing campaigns and drop Cobalt Strike.
Zscaler's analysis of a new version of PikaBot (version 1.18.32) observed this month has revealed its continued focus on obfuscation, albeit with simpler encryption algorithms, and insertion of junk code between valid instructions as part of its efforts to resist analysis.
Another crucial modification observed in the latest iteration is that the entire bot configuration -- which is similar to that of QakBot -- is stored in plaintext in a single memory block as opposed to encrypting each element and decoding them at runtime.
A third change concerns the C2 server network communications, with the malware developers tweaking the command IDs and the encryption algorithm used to secure the traffic.
"Despite its recent inactivity, PikaBot continues to be a significant cyber threat and in constant development," the researchers concluded.
"However, the developers have decided to take a different approach and decrease the complexity level of PikaBot's code by removing advanced obfuscation features."
The development comes as Proofpoint alerted of an ongoing cloud account takeover (ATO) campaign that has targeted dozens of Microsoft Azure environments and compromised hundreds of user accounts, including those belonging to senior executives.
The activity, underway since November 2023, singles out users with individualized phishing lures bearing decoy files that contain links to malicious phishing web pages for credential harvesting, and use them for follow-on data exfiltration, internal and external phishing, and financial fraud.
U.S. DoJ Dismantles Warzone RAT Infrastructure, Arrests Key Operators
12.2.24 Virus The Hacker News

The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan (RAT) called Warzone RAT.
The domains – www.warzone[.]ws and three others – were "used to sell computer malware used by cybercriminals to secretly access and steal data from victims' computers," the DoJ said.
Alongside the takedown, the international law enforcement effort has arrested and indicted two individuals in Malta and Nigeria for their involvement in selling and supporting the malware and helping other cybercriminals use the RAT for malicious purposes.
The defendants, Daniel Meli (27) and Prince Onyeoziri Odinakachi (31) have been charged with unauthorized damage to protected computers, with the former also accused of "illegally selling and advertising an electronic interception device and participating in a conspiracy to commit several computer intrusion offenses."
Cybersecurity
Meli is alleged to have offered malware services at least since 2012 through online hacking forums, sharing e-books, and helping other criminals use RATs to carry out cyber attacks. Prior to Warzone RAT, he had sold another RAT known as Pegasus RAT.
Like Meli, Odinakachi also provided online customer support to purchasers of Warzone RAT malware between June 2019 and no earlier than March 2023. Both individuals were arrested on February 7, 2024.
Warzone RAT, also known as Ave Maria, was first documented by Yoroi in January 2019 as part of a cyber attack targeting an Italian organization in the oil and gas sector towards the end of 2018 using phishing emails bearing bogus Microsoft Excel files exploiting a known security flaw in the Equation Editor (CVE-2017-11882).
Sold under the malware-as-a-service (Maas) model for $38 a month (or $196 for a year), it functions as an information stealer and facilitates remote control, thereby allowing threat actors to commandeer the infected hosts for follow-on exploitation.
Some of the notable features of the malware include the ability to browse victim file systems, take screenshots, record keystrokes, steal victim usernames and passwords, and activate the computer's webcams without the victim's knowledge or consent.
"Ave Maria attacks are initiated via phishing emails, once the dropped payload infects the victim's machine with the malware, it establishes communication with the attacker's command-and-control (C2) server on non-HTTP protocol, after decrypting its C2 connection using RC4 algorithm," Zscaler ThreatLabz said in early 2023.
Cybersecurity
On one of the now-dismantled websites, which had the tagline "Serving you loyally since 2018," the developers of the C/C++ malware described it as reliable and easy to use. They also provided the ability for customers to contact them via email (solmyr@warzone[.]ws), Telegram (@solwz and @sammysamwarzone), Skype (vuln.hf), as well as via a dedicated "client area."
An additional contact avenue was Discord, where the users were asked to get in touch with an account with the ID Meli#4472. Another Telegram account linked to Meli was @daniel96420.
Outside of cybercrime groups, the malware has also been put to use by several advanced threat actors like YoroTrooper as well as those associated with Russia over the past year.
The DoJ said the U.S. Federal Bureau of Investigation (FBI) covertly purchased copies of Warzone RAT and confirmed its nefarious functions. The coordinated exercise involved assistance from authorities in Australia, Canada, Croatia, Finland, Germany, Japan, Malta, the Netherlands, Nigeria, Romania, and Europol.
New Coyote Trojan Targets 61 Brazilian Banks with Nim-Powered Attack
9.2.24 Virus The Hacker News
Sixty-one banking institutions, all of them originating from Brazil, are the target of a new banking trojan called Coyote.
"This malware utilizes the Squirrel installer for distribution, leveraging Node.js and a relatively new multi-platform programming language called Nim as a loader to complete its infection," Russian cybersecurity firm Kaspersky said in a Thursday report.
What makes Coyote a different breed from other banking trojans of its kind is the use of the open-source Squirrel framework for installing and updating Windows apps. Another notable departure is the shift from Delphi – which is prevalent among banking malware families targeting Latin America – to an uncommon programming language like Nim.
In the attack chain documented by Kaspersky, a Squirrel installer executable is used as a launchpad for a Node.js application compiled with Electron, which, in turn, runs a Nim-based loader to trigger the execution of the malicious Coyote payload by means of DLL side-loading.
The malicious dynamic-link library, named "libcef.dll," is side-loaded by means of a legitimate executable named "obs-browser-page.exe," which is also included in the Node.js project. It's worth noting that the original libcef.dll is part of the Chromium Embedded Framework (CEF).
Coyote, once executed, "monitors all open applications on the victim's system and waits for the specific banking application or website to be accessed," subsequently contacting an actor-controlled server to fetch next-stage directives.

It has the capability to execute a wide range of commands to take screenshots, log keystrokes, terminate processes, display fake overlays, move the mouse cursor to a specific location, and even shut down the machine. It can also outright block the machine with a bogus "Working on updates..." message while executing malicious actions in the background.
"The addition of Nim as a loader adds complexity to the trojan's design," Kaspersky said. "This evolution highlights the increasing sophistication within the threat landscape and shows how threat actors are adapting and using the latest languages and tools in their malicious campaigns."
The development comes as Brazilian law enforcement authorities dismantled the Grandoreiro operation and issued five temporary arrest warrants and 13 search and seizure warrants for the masterminds behind the malware across five Brazilian states.
It also follows the discovery of a new Python-based information stealer that's related to the Vietnamese architects associated with MrTonyScam and distributed via booby-trapped Microsoft Excel and Word documents.
The stealer "collects browsers' cookies and login data [...] from a wide range of browsers, from familiar browsers such as Chrome and Edge to browsers focused on the local market, like the Cốc Cốc browser," Fortinet FortiGuard Labs said in a report published this week.
Stealthy Zardoor Backdoor Targets Saudi Islamic Charity Organization
9.2.24 Virus The Hacker News

An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to drop a previously undocumented backdoor called Zardoor.
Cisco Talos, which discovered the activity in May 2023, said the campaign has likely persisted since at least March 2021, adding it has identified only one compromised target to date, although it's suspected that there could be other victims.
"Throughout the campaign, the adversary used living-off-the-land binaries (LoLBins) to deploy backdoors, establish command-and-control (C2), and maintain persistence," security researchers Jungsoo An, Wayne Lee, and Vanja Svajcer said, calling out the threat actor's ability to maintain long-term access to victim environments without attracting attention.
The intrusion targeting the Islamic charitable organization involved the periodic exfiltration of data roughly twice a month. The exact initial access vector used to infiltrate the entity is currently unknown.

The foothold obtained, however, has been leveraged to drop Zardoor for persistence, followed by establishing C2 connections using open-source reverse proxy tools such as Fast Reverse Proxy (FRP), sSocks, and Venom.
"Once a connection was established, the threat actor used Windows Management Instrumentation (WMI) to move laterally and spread the attacker's tools — including Zardoor — by spawning processes on the target system and executing commands received from the C2," the researchers said.
The as-yet-undetermined infection pathway paves the way for a dropper component that, in turn, deploys a malicious dynamic-link library ("oci.dll") that's responsible for delivering two backdoor modules, "zar32.dll" and "zor32.dll."
While the former is the core backdoor element that facilitates C2 communications, the latter ensures that "zar32.dll" has been deployed with administrator privileges. Zardoor is capable of exfiltrating data, executing remotely fetched executables and shellcode, updating the C2 IP address, and deleting itself from the host.
The origins of the threat actor behind the campaign are unclear, and it does not share any tactical overlaps with a known, publicly reported threat actor at this time. That said, it's assessed to be the work of an "advanced threat actor."
HijackLoader Evolves: Researchers Decode the Latest Evasion Methods
8.2.24 Virus The Hacker News

The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to be increasingly used by other threat actors to deliver additional payloads and tooling.
"The malware developer used a standard process hollowing technique coupled with an additional trigger that was activated by the parent process writing to a pipe," CrowdStrike researchers Donato Onofri and Emanuele Calvelli said in a Wednesday analysis. "This new approach has the potential to make defense evasion stealthier."
HijackLoader was first documented by Zscaler ThreatLabz in September 2023 as having been used as a conduit to deliver DanaBot, SystemBC, and RedLine Stealer. It's also known to share a high degree of similarity with another loader known as IDAT Loader.
Both the loaders are assessed to be operated by the same cybercrime group. In the intervening months, HijackLoader has been propagated via ClearFake and put to use by TA544 (aka Narwhal Spider, Gold Essex, and Ursnif Gang) to deliver Remcos RAT and SystemBC via phishing messages.
"Think of loaders like wolves in sheep's clothing. Their purpose is to sneak in, introduce and execute more sophisticated threats and tools," Liviu Arsene, director of threat research and reporting at CrowdStrike, said in a statement shared with The Hacker News.
"This recent variant of HijackLoader (aka IDAT Loader) steps up its sneaking game by adding and experimenting with new techniques. This is similar to enhancing its disguise, making it stealthier, more complex, and more difficult to analyze. In essence, they're refining their digital camouflage."
The starting point of the multi-stage attack chain is an executable ("streaming_client.exe") that checks for an active internet connection and proceeds to download a second-stage configuration from a remote server.
The executable then loads a legitimate dynamic-link library (DLL) specified in the configuration to activate shellcode responsible for launching the HijackLoader payload via a combination of process doppelgänging and process hollowing techniques that increases the complexity of analysis and the defense evasion capabilities.
"The HijackLoader second-stage, position-independent shellcode then performs some evasion activities to bypass user mode hooks using Heaven's Gate and injects subsequent shellcode into cmd.exe," the researchers said.
"The injection of the third-stage shellcode is accomplished via a variation of process hollowing that results in an injected hollowed mshtml.dll into the newly spawned cmd.exe child process."
Heaven's Gate refers to a stealthy trick that allows malicious software to evade endpoint security products by invoking 64-bit code in 32-bit processes in Windows, effectively bypassing user-mode hooks.
One of the key evasion techniques observed in HijackLoader attack sequences is the use of a process injection mechanism called transacted hollowing, which has been previously observed in malware such as the Osiris banking trojan.
"Loaders are meant to act as stealth launch platforms for adversaries to introduce and execute more sophisticated malware and tools without burning their assets in the initial stages," Arsene said.
"Investing in new defense evasion capabilities for HijackLoader (aka IDAT Loader) is potentially an attempt to make it stealthier and fly below the radar of traditional security solutions. The new techniques signal both a deliberate and experimental evolution of the existing defense evasion capabilities while also increasing the complexity of analysis for threat researchers."
Beware: Fake Facebook Job Ads Spreading 'Ov3r_Stealer' to Steal Crypto and Credentials
6.2.24 Virus The Hacker News
Threat actors are leveraging bogus Facebook job advertisements as a lure to trick prospective targets into installing a new Windows-based stealer malware codenamed Ov3r_Stealer.
"This malware is designed to steal credentials and crypto wallets and send those to a Telegram channel that the threat actor monitors," Trustwave SpiderLabs said in a report shared with The Hacker News.
Ov3r_Stealer is capable of siphoning IP address-based location, hardware info, passwords, cookies, credit card information, auto-fills, browser extensions, crypto wallets, Microsoft Office documents, and a list of antivirus products installed on the compromised host.
While the exact end goal of the campaign is unknown, it's likely that the stolen information is offered for sale to other threat actors. Another possibility is that Ov3r_Stealer could be updated over time to act as a QakBot-like loader for additional payloads, including ransomware.
The starting point of the attack is a weaponized PDF file that purports to be a file hosted on OneDrive, urging users to click on an "Access Document" button embedded into it.
Trustwave said it identified the PDF file being shared on a fake Facebook account impersonating Amazon CEO Andy Jassy as well as via Facebook ads for digital advertising jobs.
Users who end up clicking on the button are served an internet shortcut (.URL) file that masquerades as a DocuSign document hosted on Discord's content delivery network (CDN). The shortcut file then acts as a conduit to deliver a control panel item (.CPL) file, which is then executed using the Windows Control Panel process binary ("control.exe").
The execution of the CPL file leads to the retrieval of a PowerShell loader ("DATA1.txt") from a GitHub repository to ultimately launch Ov3r_Stealer.

It's worth noting at this stage that a near-identical infection chain was recently disclosed by Trend Micro as having put to use by threat actors to drop another stealer called Phemedrone Stealer by exploiting the Microsoft Windows Defender SmartScreen bypass flaw (CVE-2023-36025, CVSS score: 8.8).
The similarities extend to the GitHub repository used (nateeintanan2527) and the fact that Ov3r_Stealer shares code-level overlaps with Phemedrone.
"This malware has recently been reported, and it may be that Phemedrone was re-purposed and renamed to Ov3r_Stealer," Trustwave said. "The main difference between the two is that Phemedrone is written in C#."
The findings come as Hudson Rock revealed that threat actors are advertising their access to law enforcement request portals of major organizations like Binance, Google, Meta, and TikTok by exploiting credentials obtained from infostealer infections.
They also follow the emergence of a category of infections called CrackedCantil that take leverage cracked software as an initial access vector to drop loaders like PrivateLoader and SmokeLoader, when subsequently act as a delivery mechanism for information stealers, crypto miners, proxy botnets, and ransomware.
HeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
2.2.24 Virus The Hacker News
Cybersecurity researchers have detailed an updated version of the malware HeadCrab that's known to target Redis database servers across the world since early September 2021.
The development, which comes exactly a year after the malware was first publicly disclosed by Aqua, is a sign that the financially-motivated threat actor behind the campaign is actively adapting and refining their tactics and techniques to stay ahead of the detection curve.
The cloud security firm said that "the campaign has almost doubled the number of infected Redis servers," with an additional 1,100 compromised servers, up from 1,200 reported at the start of 2023.
HeadCrab is designed to infiltrate internet-exposed Redis servers and wrangle them into a botnet for illicitly mining cryptocurrency, while also leveraging the access in a manner that allows the threat actor to execute shell commands, load fileless kernel modules, and exfiltrate data to a remote server.
While the origins of the threat actor are presently not known, they make it a point to note in a "mini blog" embedded into the malware that the mining activity is "legal in my country" and that they do it because "it almost doesn't harm human life and feelings (if done right)."
The operator, however, acknowledges that it's a "parasitic and inefficient way" of making money, adding their aim is to make $15,000 per year.
"An integral aspect of the sophistication of HeadCrab 2.0 lies in its advanced evasion techniques," Aqua researchers Asaf Eitani and Nitzan Yaakov said. "In contrast to its predecessor (named HeadCrab 1.0), this new version employs a fileless loader mechanism, demonstrating the attacker's commitment to stealth and persistence."

It's worth noting that the previous iteration utilized the SLAVEOF command to download and save the HeadCrab malware file to disk, thereby leaving artifact traces on the file system.
HeadCrab 2.0, on the other hand, receives the malware's content over the Redis communication channel and stores it in a fileless location in a bid to minimize the forensic trail and make it much more challenging to detect.
Also changed in the new variant is the use of the Redis MGET command for command-and-control (C2) communications for added covertness.
"By hooking into this standard command, the malware gains the ability to control it during specific attacker-initiated requests," the researchers said.
"Those requests are achieved by sending a special string as an argument to the MGET command. When this specific string is detected, the malware recognizes the command as originating from the attacker, triggering the malicious C2 communication."
Describing HeadCrab 2.0 as an escalation in the sophistication of Redis malware, Aqua said its ability to masquerade its malicious activities under the guise of legitimate commands poses new problems for detection.
"This evolution underscores the necessity for continuous research and development in security tools and practices," the researchers concluded. "The engagement by the attacker and the subsequent evolution of the malware highlights the critical need for vigilant monitoring and intelligence gathering."
Hackers Exploiting Ivanti VPN Flaws to Deploy KrustyLoader Malware
1.2.24 Virus The Hacker News
A pair of recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) virtual private network (VPN) devices have been exploited to deliver a Rust-based payload called KrustyLoader that's used to drop the open-source Sliver adversary simulation tool.
The security vulnerabilities, tracked as CVE-2023-46805 (CVSS score: 8.2) and CVE-2024-21887 (CVSS score: 9.1), could be abused in tandem to achieve unauthenticated remote code execution on susceptible appliances.
As of January 26, patches for the two flaws have been delayed, although the software company has released a temporary mitigation through an XML file.
Volexity, which first shed light on the shortcomings, said they have been weaponized as zero-days since December 3, 2023, by a Chinese nation-state threat actor it tracks under the name UTA0178. Google-owned Mandiant has assigned the moniker UNC5221 to the group.
Following public disclosure earlier this month, the vulnerabilities have come under broad exploitation by other adversaries to drop XMRig cryptocurrency miners as well as Rust-based malware.
Synacktiv's analysis of the Rust malware, codenamed KrustyLoader, has revealed that it functions as a loader to download Sliver from a remote server and execute it on the compromised host.
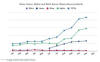
Image Credit: Recorded Future
Sliver, developed by cybersecurity company BishopFox, is a Golang-based cross-platform post-exploitation framework that has emerged as a lucrative option for threat actors in comparison to other well-known alternatives like Cobalt Strike.
That said, Cobalt Strike continues to be the top offensive security tool observed among attacker-controlled infrastructure in 2023, followed by Viper, and Meterpreter, according to a report published by Recorded Future earlier this month.
"Both Havoc and Mythic have also become relatively popular but are still observed in far lower numbers than Cobalt Strike, Meterpreter, or Viper," the company said. "Four other well-known frameworks are Sliver, Havoc, Brute Ratel (BRc4), and Mythic."
Brazilian Feds Dismantle Grandoreiro Banking Trojan, Arresting Top Operatives
31.1.24 Virus The Hacker News
A Brazilian law enforcement operation has led to the arrest of several Brazilian operators in charge of the Grandoreiro malware.
The Federal Police of Brazil said it served five temporary arrest warrants and 13 search and seizure warrants in the states of São Paulo, Santa Catarina, Pará, Goiás, and Mato Grosso.
Slovak cybersecurity firm ESET, which provided additional assistance in the effort, said it uncovered a design flaw in Grandoreiro's network protocol that helped it to identify the victimology patterns.
Grandoreiro is one of the many Latin American banking trojans such as Javali, Melcoz, Casabeniero, Mekotio, and Vadokrist, primarily targeting countries like Spain, Mexico, Brazil, and Argentina. It's known to be active since 2017.
In late October 2023, Proofpoint revealed details of a phishing campaign that distributed an updated version of the malware to targets in Mexico and Spain.
The banking trojan has capabilities to both steal data through keyloggers and screenshots as well as siphon bank login information from overlays when an infected victim visits pre-determined banking sites targeted by the threat actors. It can also display fake pop-up windows and block the victim's screen.
Attack chains typically leverage phishing lures bearing decoy documents or malicious URLs that, when opened or clicked, lead to the deployment of malware, which then establishes contact with a command-and-control (C&C) server for remotely controlling the machine in a manual fashion.
"Grandoreiro periodically monitors the foreground window to find one that belongs to a web browser process," ESET said.

"When such a window is found and its name matches any string from a hardcoded list of bank-related strings, then and only then the malware initiates communication with its C&C server, sending requests at least once a second until terminated."
The threat actors behind the malware are also known to employ a domain generation algorithm (DGA) since around October 2020 to dynamically identify a destination domain for C&C traffic, making it harder to block, track, or take over the infrastructure.
A majority of the IP addresses these domains resolve to are provided primarily by Amazon Web Services (AWS) and Microsoft Azure, with the life span of the C&C IP addresses ranging anywhere between 1 day to 425 days. On average, there are 13 active and three new C&C IP addresses per day, respectively.
ESET also said that Grandoreiro's flawed implementation of its RealThinClient (RTC) network protocol for C&C made it possible to get information about the number of victims that are connected to the C&C server, which is 551 unique victims in a day on average mainly spread across Brazil, Mexico, and Spain.
Further investigation has found that an average number of 114 new unique victims connect to the C&C servers each day.
"The disruption operation led by the Federal Police of Brazil aimed at individuals who are believed to be high up in the Grandoreiro operation hierarchy," ESET said.
New ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
31.1.24 Virus The Hacker News
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet's infrastructure was dismantled in April 2022.
A new variant of the malware is said to have been in development since September 2023, Zscaler ThreatLabz said in an analysis published this month.
"The new version of Zloader made significant changes to the loader module, which added RSA encryption, updated the domain generation algorithm, and is now compiled for 64-bit Windows operating systems for the first time," researchers Santiago Vicente and Ismael Garcia Perez said.
ZLoader, also known by the names Terdot, DELoader, or Silent Night, is an offshoot of the Zeus banking trojan that first surfaced in 2015, before pivoting to functioning as a loader for next-stage payloads, including ransomware.
Typically distributed via phishing emails and malicious search engine ads, ZLoader suffered a huge blow after a group of companies led by Microsoft's Digital Crimes Unit (DCU) seized control of 65 domains that were used to control and communicate with the infected hosts.
The latest versions of the malware, tracked as 2.1.6.0 and 2.1.7.0, incorporate junk code and string obfuscation to resist analysis efforts. Each ZLoader artifact is also expected to have a specific filename for it to be executed on the compromised host.
"This could evade malware sandboxes that rename sample files," the researchers noted.
In addition to encrypting the static configuration using RC4 with a hard-coded alphanumeric key to conceal information related to the campaign name and the command-and-control (C2) servers, the malware has been observed relying on an updated version of the domain generation algorithm as a fallback measure in the event the primary C2 servers are inaccessible.
The backup communications method was first discovered in ZLoader version 1.1.22.0, which was propagated as part of phishing campaigns detected in March 2020.
"Zloader was a significant threat for many years and its comeback will likely result in new ransomware attacks," the researchers said. "The operational takedown temporarily stopped the activity, but not the threat group behind it."
The development comes as Red Canary warned of an increase in the volume of campaigns leveraging MSIX files to deliver malware such as NetSupport RAT, ZLoader, and FakeBat (aka EugenLoader), since July 2023, prompting Microsoft to disable the protocol handler by default in late December 2023.
It also follows the emergence of new stealer malware families such as Rage Stealer and Monster Stealer that are being used as an initial access pathway for information theft and as a launching pad for more severe cyber attacks.
Malicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines
29.1.24 Virus The Hacker News
Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that deliver an information stealing malware called WhiteSnake Stealer on Windows systems.
The malware-laced packages are named nigpal, figflix, telerer, seGMM, fbdebug, sGMM, myGens, NewGends, and TestLibs111. They have been uploaded by a threat actor named "WS."
"These packages incorporate Base64-encoded source code of PE or other Python scripts within their setup.py files," Fortinet FortiGuard Labs said in an analysis published last week.
"Depending on the victim devices' operating system, the final malicious payload is dropped and executed when these Python packages are installed."
While Windows systems are infected with WhiteSnake Stealer, compromised Linux hosts are served a Python script designed to harvest information. The activity, which predominantly targets Windows users, overlaps with a prior campaign that JFrog and Checkmarx disclosed last year.
"The Windows-specific payload was identified as a variant of the [...] WhiteSnake malware, which has an Anti-VM mechanism, communicates with a C&C server using the Tor protocol, and is capable of stealing information from the victim and executing commands," JFrog noted in April 2023.
It's also designed to capture data from web browsers, cryptocurrency wallets, and apps like WinSCP, CoreFTP, Windscribe, Filezilla, AzireVPN, Snowflake, Steam, Discord, Signal, and Telegram.

Checkmarx is tracking the threat actor behind the campaign under the moniker PYTA31, stating the end goal is to exfiltrate sensitive and particularly crypto wallet data from the target machines.
Some of the newly published rogue packages have also been observed incorporating clipper functionality to overwrite clipboard content with attacker-owned wallet addresses to carry out unauthorized transactions. A few others have been configured to steal data from browsers, applications, and crypto services.
Fortinet said the finding "demonstrates the ability of a single malware author to disseminate numerous info-stealing malware packages into the PyPI library over time, each featuring distinct payload intricacies."
The disclosure comes as ReversingLabs discovered two malicious packages on the npm package registry have been found to leverage GitHub to store Base64-encrypted SSH keys stolen from developer systems on which they were installed.
Npm Trojan Bypasses UAC, Installs AnyDesk with "Oscompatible" Package
19.1.24 Virus The Hacker News
A malicious package uploaded to the npm registry has been found deploying a sophisticated remote access trojan on compromised Windows machines.
The package, named "oscompatible," was published on January 9, 2024, attracting a total of 380 downloads before it was taken down.
oscompatible included a "few strange binaries," according to software supply chain security firm Phylum, including a single executable file, a dynamic-link library (DLL) and an encrypted DAT file, alongside a JavaScript file.
This JavaScript file ("index.js") executes an "autorun.bat" batch script but only after running a compatibility check to determine if the target machine runs on Microsoft Windows.
If the platform is not Windows, it displays an error message to the user, stating the script is running on Linux or an unrecognized operating system, urging them to run it on "Windows Server OS."
The batch script, for its part, verifies if it has admin privileges, and if not, runs a legitimate Microsoft Edge component called "cookie_exporter.exe" via a PowerShell command.
Attempting to run the binary will trigger a User Account Control (UAC) prompt asking the target to execute it with administrator credentials.
In doing so, the threat actor carries out the next stage of the attack by running the DLL ("msedge.dll") by taking advantage of a technique called DLL search order hijacking.
The trojanized version of the library is designed to decrypt the DAT file ("msedge.dat") and launch another DLL called "msedgedat.dll," which, in turn, establishes connections with an actor-controlled domain named "kdark1[.]com" to retrieve a ZIP archive.
The ZIP file comes fitted with the AnyDesk remote desktop software as well as a remote access trojan ("verify.dll") that's capable of fetching instructions from a command-and-control (C2) server via WebSockets and gathering sensitive information from the host.
It also "installs Chrome extensions to Secure Preferences, configures AnyDesk, hides the screen, and disables shutting down Windows, [and] captures keyboard and mouse events," Phylum said.
While "oscompatible" appears to be the only npm module employed as part of the campaign, the development is once again a sign that threat actors are increasingly targeting open-source software (OSS) ecosystems for supply chain attacks.
"From the binary side, the process of decrypting data, using a revoked certificate for signing, pulling other files from remote sources, and attempting to disguise itself as a standard Windows update process all along the way is relatively sophisticated compared to what we normally see in OSS ecosystems," the company said.
The disclosure comes as cloud security firm Aqua revealed that 21.2% of the top 50,000 most downloaded npm packages are deprecated, exposing users to security risks. In other words, the deprecated packages are downloaded an estimated 2.1 billion times weekly.
This includes archived and deleted GitHub repositories associated with the packages as well as those that are maintained without a visible repository, commit history, and issue tracking.
"This situation becomes critical when maintainers, instead of addressing security flaws with patches or CVE assignments, opt to deprecate affected packages," security researchers Ilay Goldman and Yakir Kadkoda said.
"What makes this particularly concerning is that, at times, these maintainers do not officially mark the package as deprecated on npm, leaving a security gap for users who may remain unaware of potential threats."
New Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
19.1.24 Virus The Hacker News
Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well as the 9Hits Viewer software as part of a multi-pronged monetization strategy.
"This is the first documented case of malware deploying the 9Hits application as a payload," cloud security firm Cado said, adding the development is a sign that adversaries are always on the lookout for diversifying their strategies to make money off compromised hosts.
9Hits advertises itself as a "unique web traffic solution" and an "automatic traffic exchange" that allows members of the service to drive traffic to their sites in exchange for purchasing credits.
This is accomplished by means of a software called 9Hits Viewer, which runs a headless Chrome browser instance to visit websites requested by other members, for which they earn credits to pay for generating traffic to their sites.
The exact method used to spread the malware to vulnerable Docker hosts is currently unclear, but it's suspected to involve the use of search engines like Shodan to scan for prospective targets.
The servers are then breached to deploy two malicious containers via the Docker API and fetch off-the-shelf images from the Docker Hub library for the 9Hits and XMRig software.
"This is a common attack vector for campaigns targeting Docker, where instead of fetching a bespoke image for their purposes they pull a generic image off Dockerhub (which will almost always be accessible) and leverage it for their needs," security researcher Nate Bill said.
The 9Hits container is then used to execute code to generate credits for the attacker by authenticating with 9Hits using their session token and extracting the list of sites to visit.
The threat actors have also configured the scheme to allow visiting adult sites or sites that show popups, but prevent it from visiting cryptocurrency-related sites.
The other container is used to run an XMRig miner that connects to a private mining pool, making it impossible to determine the campaign's scale and profitability.
"The main impact of this campaign on compromised hosts is resource exhaustion, as the XMRig miner will use all available CPU resources it can while 9hits will use a large amount of bandwidth, memory, and what little CPU is left," Bill said.
"The result of this is that legitimate workloads on infected servers will be unable to perform as expected. In addition, the campaign could be updated to leave a remote shell on the system, potentially causing a more serious breach."
Remcos RAT Spreading Through Adult Games in New Attack Wave
17.1.24 Virus The Hacker News

The remote access trojan (RAT) known as Remcos RAT has been found being propagated via webhards by disguising it as adult-themed games in South Korea.
WebHard, short for web hard drive, is a popular online file storage system used to upload, download, and share files in the country.
While webhards have been used in the past to deliver njRAT, UDP RAT, and DDoS botnet malware, the AhnLab Security Emergency Response Center's (ASEC) latest analysis shows that the technique has been adopted to distribute Remcos RAT.
In these attacks, users are tricked into opening booby-trapped files by passing them off as adult games, which, when launched, execute malicious Visual Basic scripts in order to run an intermediate binary named "ffmpeg.exe."
This results in the retrieval of Remcos RAT from an actor-controlled server.

A sophisticated RAT, Remcos (aka Remote Control and Surveillance) facilitates unauthorized remote control and surveillance of compromised hosts, enabling threat actors to exfiltrate sensitive data.
This malware, although originally marketed by Germany-based firm Breaking Security in 2016 as a bonafide remote administration tool, has metamorphosed into a potent weapon wielded by adversaries actors to infiltrate systems and establish unfettered control.
"Remcos RAT has evolved into a malicious tool employed by threat actors across various campaigns," Cyfirma noted in an analysis in August 2023.
"The malware's multifunctional capabilities, including keylogging, audio recording, screenshot capture, and more, highlight its potential to compromise user privacy, exfiltrate sensitive data, and manipulate systems. The RAT's ability to disable User Account Control (UAC) and establish persistence further amplifies its potential impact."
Threat Actors Increasingly Abusing GitHub for Malicious Purposes
12.1.24 Virus The Hacker News
The ubiquity of GitHub in information technology (IT) environments has made it a lucrative choice for threat actors to host and deliver malicious payloads and act as dead drop resolvers, command-and-control, and data exfiltration points.
"Using GitHub services for malicious infrastructure allows adversaries to blend in with legitimate network traffic, often bypassing traditional security defenses and making upstream infrastructure tracking and actor attribution more difficult," Recorded Future said in a report shared with The Hacker News.
The cybersecurity firm described the approach as "living-off-trusted-sites" (LOTS), a spin on the living-off-the-land (LotL) techniques often adopted by threat actors to conceal rogue activity and fly under the radar.
Prominent among the methods by which GitHub is abused relates to payload delivery, with some actors leveraging its features for command-and-control (C2) obfuscation. Last month, ReversingLabs detailed a number of rogue Python packages that relied on a secret gist hosted on GitHub to receive malicious commands on the compromised hosts.
While full-fledged C2 implementations in GitHub are uncommon in comparison to other infrastructure schemes, its use by threat actors as a dead drop resolver – wherein the information from an actor-controlled GitHub repository is used to obtain the actual C2 URL – is a lot more prevalent, as evidenced in the case of malware like Drokbk and ShellBox.
Also rarely observed is the abuse of GitHub for data exfiltration, which, per Recorded Future, is likely due to file size and storage limitations and concerns around discoverability.
Outside of these four main schemes, the platform's offerings are put to use in various other ways in order to meet infrastructure-related purposes. For instance, GitHub Pages have been used as phishing hosts or traffic redirectors, with some campaigns utilizing GitHub repositories as a backup C2 channel.
The development speaks to the broader trend of legitimate internet services such as Google Drive, Microsoft OneDrive, Dropbox, Notion, Firebase, Trello, and Discord being exploited by threat actors. This also extends to other source code and version control platforms like GitLab, BitBucket, and Codeberg.
"There is no universal solution for GitHub abuse detection," the company said. "A mix of detection strategies is needed, influenced by specific environments and factors such as the availability of logs, organizational structure, service usage patterns, and risk tolerance, among
Alert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware
10.1.24 Virus The Hacker News

A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware as part of spam campaigns in 2023.
"PikaBot's operators ran phishing campaigns, targeting victims via its two components — a loader and a core module — which enabled unauthorized remote access and allowed the execution of arbitrary commands through an established connection with their command-and-control (C&C) server," Trend Micro said in a report published today.
The activity began in the first quarter of 2023 that lasted till the end of June, before ramping up again in September. It also overlaps with prior campaigns that have used similar tactics to deliver QakBot, specifically those orchestrated by cybercrime groups known as TA571 and TA577.
It's believed that the increase in the number of phishing campaigns related to PikaBot is the result of QakBot's takedown in August, with DarkGate emerging as another replacement.
PikaBot is primarily a loader, which means it's designed to launch another payload, including Cobalt Strike, a legitimate post-exploitation toolkit that typically acts as a precursor for ransomware deployment.
The attack chains leverage a technique called email thread hijacking, employing existing email threads to trick recipients into opening malicious links or attachments, effectively activating the malware execution sequence.
The ZIP archive attachments, which either contain JavaScript or IMG files, are used as a launchpad for PikaBot. The malware, for its part, checks the system's language and halts execution should it be either Russian or Ukrainian.
In the next step, it collects details about the victim's system and forwards them to a C&C server in JSON format. Water Curupira's campaigns are for the purpose of dropping Cobalt Strike, which subsequently lead to the deployment of Black Basta ransomware.
"The threat actor also conducted several DarkGate spam campaigns and a small number of IcedID campaigns during the early weeks of the third quarter of 2023, but has since pivoted exclusively to PikaBot," Trend Micro said.
Beware! YouTube Videos Promoting Cracked Software Distribute Lumma Stealer
9.1.24 Virus The Hacker News

Threat actors are resorting to YouTube videos featuring content related to cracked software in order to entice users into downloading an information stealer malware called Lumma.
"These YouTube videos typically feature content related to cracked applications, presenting users with similar installation guides and incorporating malicious URLs often shortened using services like TinyURL and Cuttly," Fortinet FortiGuard Labs researcher Cara Lin said in a Monday analysis.
This is not the first time pirated software videos on YouTube have emerged as an effective bait for stealer malware. Previously similar attack chains were observed delivering stealers, clippers, and crypto miner malware.
In doing so, threat actors can leverage the compromised machines for not only information and cryptocurrency theft, but also abuse the resources for illicit mining.
In the latest attack sequence documented by Fortinet, users searching for cracked versions of legitimate video editing tools like Vegas Pro on YouTube are prompted to click on a link located in the video's description, leading to the download of a bogus installer hosted on MediaFire.

The ZIP installer, once unpacked, features a Windows shortcut (LNK) masquerading as a setup file that downloads a .NET loader from a GitHub repository, which, in turn, loads the stealer payload, but not before performing a series of anti-virtual machine and anti-debugging checks.
Lumma Stealer, written in C and offered for sale on underground forums since late 2022, is capable of harvesting and exfiltrating sensitive data to an actor-controlled server.
The development comes as Bitdefender warned of stream-jacking attacks on YouTube in which cybercriminals take over high-profile accounts via phishing attacks that deploy the RedLine Stealer malware to siphon their credentials and session cookies, and ultimately promote various crypto scams.
It also follows the discovery of an 11-month-old AsyncRAT campaign that employs phishing lures to download an obfuscated JavaScript file that's then utilized to drop the remote access trojan.
"The victims and their companies are carefully selected to broaden the impact of the campaign," AT&T Alien Labs researcher Fernando Martinez said. "Some of the identified targets manage key infrastructure in the U.S."
Syrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
9.1.24 Virus The Hacker News
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that's equipped to bypass security software and stealthily launch hidden applications.
"The developers operate on multiple hacker forums and social media platforms, showcasing an active and sophisticated presence," cybersecurity firm Cyfirma said in a report published last week.
The actors, assessed to be of Syrian origin and linked to the development of another RAT known as S500 RAT, also run a Telegram channel offering various services such as the distribution of cracked RATs, leaked databases, carding activities, and the sale of Facebook and X (formerly Twitter) bots.
The social media bots are then utilized by other cyber criminals to promote various illicit services by automatically engaging with and commenting on user content.
In-the-wild detections of Silver RAT v1.0 were first observed in November 2023, although the threat actor's plans to release the trojan were first made official a year before. It was cracked and leaked on Telegram around October 2023.
The C#-based malware boasts of a wide range of features to connect to a command-and-control (C2) server, log keystrokes, destroy system restore points, and even encrypt data using ransomware. There are also indications that an Android version is in the works.

"While generating a payload using Silver RAT's builder, threat actors can select various options with a payload size up to a maximum of 50kb," the company noted. "Once connected, the victim appears on the attacker-controlled Silver RAT panel, which displays the logs from the victim based on the functionalities chosen."
An interesting evasion feature built into Silver RAT is its ability to delay the execution of the payload by a specific time as well as covertly launch apps and take control of the compromised host.
Further analysis of the malware author's online footprint shows that one of the members of the group is likely in their mid-20s and based in Damascus.
"The developer [...] appears supportive of Palestine based on their Telegram posts, and members associated with this group are active across various arenas, including social media, development platforms, underground forums, and Clearnet websites, suggesting their involvement in distributing various malware," Cyfirma said.
New Bandook RAT Variant Resurfaces, Targeting Windows Machines
5.1.24 Virus The Hacker News

A new variant of remote access trojan called Bandook has been observed being propagated via phishing attacks with an aim to infiltrate Windows machines, underscoring the continuous evolution of the malware.
Fortinet FortiGuard Labs, which identified the activity in October 2023, said the malware is distributed via a PDF file that embeds a link to a password-protected .7z archive.
"After the victim extracts the malware with the password in the PDF file, the malware injects its payload into msinfo32.exe," security researcher Pei Han Liao said.
Bandook, first detected in 2007, is an off-the-shelf malware that comes with a wide range of features to remotely gain control of the infected systems.
In July 2021, Slovak cybersecurity firm ESET detailed a cyber espionage campaign that leveraged an upgraded variant of Bandook to breach corporate networks in Spanish-speaking countries such as Venezuela.

The starting point of the latest attack sequence is an injector component that's designed to decrypt and load the payload into msinfo32.exe, a legitimate Windows binary that gathers system information to diagnose computer issues.
The malware, besides making Windows Registry changes to establish persistence on the compromised host, establishes contact with a command-and-control (C2) server to retrieve additional payloads and instructions.
"These actions can be roughly categorized as file manipulation, registry manipulation, download, information stealing, file execution, invocation of functions in DLLs from the C2, controlling the victim's computer, process killing, and uninstalling the malware," Han Liao said.
Beware: 3 Malicious PyPI Packages Found Targeting Linux with Crypto Miners
5.1.24 Virus The Hacker News

Three new malicious packages have been discovered in the Python Package Index (PyPI) open-source repository with capabilities to deploy a cryptocurrency miner on affected Linux devices.
The three harmful packages, named modularseven, driftme, and catme, attracted a total of 431 downloads over the past month before they were taken down.
"These packages, upon initial use, deploy a CoinMiner executable on Linux devices," Fortinet FortiGuard Labs researcher Gabby Xiong said, adding the campaign shares overlaps with a prior campaign that involved the use of a package called culturestreak to deploy a crypto miner.
The malicious code resides in the __init__.py file, which decodes and retrieves the first stage from a remote server, a shell script ("unmi.sh") that fetches a configuration file for the mining activity as well as the CoinMiner file hosted on GitLab.
The ELF binary file is then executed in the background using the nohup command, thus ensuring that the process continues to run after exiting the session.
"Echoing the approach of the earlier 'culturestreak' package, these packages conceal their payload, effectively reducing the detectability of their malicious code by hosting it on a remote URL," Xiong said. "The payload is then incrementally released in various stages to execute its malicious activities."
The connections to the culturestreak package also stems from the fact that the configuration file is hosted on the domain papiculo[.]net and the coin mining executables are hosted on a public GitLab repository.
One notable improvement in the three new packages is the introduction of an extra stage by concealing their nefarious intent in the shell script, thereby helping it evade detection by security software and lengthening the exploitation process.
"Moreover, this malware inserts the malicious commands into the ~/.bashrc file," Xiong said. "This addition ensures the malware's persistence and reactivation on the user's device, effectively extending the duration of its covert operation. This strategy aids in the prolonged, stealthy exploitation of the user's device for the attacker's benefit."
UAC-0050 Group Using New Phishing Tactics to Distribute Remcos RAT
5.1.24 Virus The Hacker News

The threat actor known as UAC-0050 is leveraging phishing attacks to distribute Remcos RAT using new strategies to evade detection from security software.
"The group's weapon of choice is Remcos RAT, a notorious malware for remote surveillance and control, which has been at the forefront of its espionage arsenal," Uptycs security researchers Karthickkumar Kathiresan and Shilpesh Trivedi said in a Wednesday report.
"However, in their latest operational twist, the UAC-0050 group has integrated a pipe method for interprocess communication, showcasing their advanced adaptability."
UAC-0050, active since 2020, has a history of targeting Ukrainian and Polish entities via social engineering campaigns that impersonate legitimate organizations to trick recipients into opening malicious attachments.
In February 2023, the Computer Emergency Response Team of Ukraine (CERT-UA) attributed the adversary to a phishing campaign designed to deliver Remcos RAT.
Over the past few months, the same trojan has been distributed as part of at least three different phishing waves, with one such attack also leading to the deployment of an information stealer called Meduza Stealer.
The analysis from Uptycs is based on a LNK file it discovered on December 21, 2023. While the exact initial access vector is currently unknown, it's suspected to have involved phishing emails targeting Ukrainian military personnel that claim to advertise consultancy roles with the Israel Defense Forces (IDF).

The LNK file in question collects information regarding antivirus products installed on the target computer, and then proceeds to retrieve and execute an HTML application named "6.hta" from a remote server using mshta.exe, a Windows-native binary for running HTA files.
This step paves the way for a PowerShell script that unpacks another PowerShell script to download two files called "word_update.exe" and "ofer.docx" from the domain new-tech-savvy[.]com.
Running word_update.exe causes it to create a copy of itself with the name fmTask_dbg.exe and establish persistence by creating a shortcut to the new executable in the Windows Startup folder.
The binary also employs unnamed pipes to facilitate the exchange of data between itself and a newly spawned child process for cmd.exe in order to ultimately decrypt and launch the Remcos RAT (version 4.9.2 Pro), which is capable of harvesting system data and cookies and login information from web browsers like Internet Explorer, Mozilla Firefox, and Google Chrome.
"Leveraging pipes within the Windows operating system provides a covert channel for data transfer, skillfully evading detection by Endpoint Detection and Response (EDR) and antivirus systems," the researchers said.
"Although not entirely new, this technique marks a significant leap in the sophistication of the group's strategies."
Malware Using Google MultiLogin Exploit to Maintain Access Despite Password Reset
3.1.24 Virus The Hacker News

Information stealing malware are actively taking advantage of an undocumented Google OAuth endpoint named MultiLogin to hijack user sessions and allow continuous access to Google services even after a password reset.
According to CloudSEK, the critical exploit facilitates session persistence and cookie generation, enabling threat actors to maintain access to a valid session in an unauthorized manner.
The technique was first revealed by a threat actor named PRISMA on October 20, 2023, on their Telegram channel. It has since been incorporated into various malware-as-a-service (MaaS) stealer families, such as Lumma, Rhadamanthys, Stealc, Meduza, RisePro, and WhiteSnake.
The MultiLogin authentication endpoint is primarily designed for synchronizing Google accounts across services when users sign in to their accounts in the Chrome web browser (i.e., profiles).
A reverse engineering of the Lumma Stealer code has revealed that the technique targets the "Chrome's token_service table of WebData to extract tokens and account IDs of chrome profiles logged in," security researcher Pavan Karthick M said. "This table contains two crucial columns: service (GAIA ID) and encrypted_token."

This token:GAIA ID pair is then combined with the MultiLogin endpoint to regenerate Google authentication cookies.
When reached for comment, Google acknowledged the existence of the attack method but noted that users can revoke the stolen sessions by logging out of the impacted browser.
"Google is aware of recent reports of a malware family stealing session tokens," the company told The Hacker News. "Attacks involving malware that steal cookies and tokens are not new; we routinely upgrade our defenses against such techniques and to secure users who fall victim to malware. In this instance, Google has taken action to secure any compromised accounts detected."
"However, it's important to note a misconception in reports that suggests stolen tokens and cookies cannot be revoked by the user," it further added. "This is incorrect, as stolen sessions can be invalidated by simply signing out of the affected browser, or remotely revoked via the user's devices page. We will continue to monitor the situation and provide updates as needed."
The company further recommended users turn on Enhanced Safe Browsing in Chrome to protect against phishing and malware downloads.
New JinxLoader Targeting Users with Formbook and XLoader Malware
1.1.24 Virus The Hacker News

A new Go-based malware loader called JinxLoader is being used by threat actors to deliver next-stage payloads such as Formbook and its successor XLoader.
The disclosure comes from cybersecurity firms Palo Alto Networks Unit 42 and Symantec, both of which highlighted multi-step attack sequences that led to the deployment of JinxLoader through phishing attacks.
"The malware pays homage to League of Legends character Jinx, featuring the character on its ad poster and [command-and-control] login panel," Symantec said. "JinxLoader's primary function is straightforward – loading malware."
Unit 42 revealed in late November 2023 that the malware service was first advertised on hackforums[.]net on April 30, 2023, for $60 a month, $120 a year, or for a lifetime fee of $200.
The attacks begin with phishing emails impersonating Abu Dhabi National Oil Company (ADNOC), urging recipients to open password-protected RAR archive attachments that, upon opening, drop the JinxLoader executable, which subsequently acts as a gateway for Formbook or XLoader.
The development comes as ESET revealed a spike in infections, delivering another novice loader malware family dubbed Rugmi to propagate a wide range of information stealers.
It also comes amid a surge in campaigns distributing DarkGate and PikaBot, with a threat actor known as TA544 (aka Narwal Spider) leveraging new variants of loader malware called IDAT Loader to deploy Remcos RAT or SystemBC malware.
What's more, the threat actors behind the Meduza Stealer have released an updated version of the malware (version 2.2) on the dark web with expanded support for browser-based cryptocurrency wallets and an improved credit card (CC) grabber.
In a sign that stealer malware continues to be a lucrative market for cybercriminals, researchers have discovered a new stealer family known as Vortex Stealer that's capable of exfiltrating browser data, Discord tokens, Telegram sessions, system information, and files that are less than 2 MB in size.
"Stolen information will be archived and uploaded to Gofile or Anonfiles; the malware will also post it onto the author's Discord using webhooks," Symantec said. "It's also capable of posting to Telegram via a Telegram bot."