Virus
2024 2023
2022
2021 2020
CERT-UA Uncovers New Malware Wave Distributing OCEANMAP, MASEPIE, STEELHOOK
29.12.23
Virus
The Hacker News

The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new
phishing campaign orchestrated by the Russia-linked APT28 group to deploy
previously undocumented malware such as OCEANMAP, MASEPIE, and STEELHOOK to
harvest sensitive information.
The activity, which was detected by the agency between December 15 and 25, 2023,
targets government entities with email messages urging recipients to click on a
link to view a document.
However, to the contrary, the links redirect to malicious web resources that
abuse JavaScript and the "search-ms:" URI protocol handler to drop a Windows
shortcut file (LNK) that launches PowerShell commands to activate an infection
chain for a new malware known as MASEPIE.
MASEPIE is a Python-based tool to download/upload files and execute commands,
with communications with the command-and-control (C2) server taking place over
an encrypted channel using the TCP protocol.
The attacks further pave the way for the deployment of additional malware,
including a PowerShell script called STEELHOOK that's capable of harvesting web
browser data and exporting it to an actor-controlled server in Base64-encoded
format.
Also delivered is a C#-based backdoor dubbed OCEANMAP that's designed to execute
commands using cmd.exe.
"The IMAP protocol is used as a control channel," CERT-UA said, adding
persistence is achieved by creating a URL file named "VMSearch.url" in the
Windows Startup folder.
"Commands, in Base64-encoded form, are contained in the 'Drafts' of the
corresponding email directories; each of the drafts contains the name of the
computer, the name of the user and the version of the OS. The results of the
commands are stored in the inbox directory."
The agency further pointed out that reconnaissance and lateral movement
activities are carried out within an hour of the initial compromise by taking
advantage of tools like Impacket and SMBExec.
The disclosure comes weeks after IBM X-Force revealed APT28's use of lures
related to the ongoing Israel-Hamas war to facilitate the delivery of a custom
backdoor called HeadLace.
In recent weeks, the prolific Kremlin-backed hacking group has also been
attributed to the exploitation of a now-patched critical security flaw in its
Outlook email service (CVE-2023-23397, CVSS score: 9.8) to gain unauthorized
access to victims' accounts within Exchange servers.
Microsoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks
29.12.23
Virus
The Hacker News
Microsoft on Thursday said it's once again disabling the
ms-appinstaller protocol handler by default following its abuse by multiple
threat actors to distribute malware.
"The observed threat actor activity abuses the current implementation of the
ms-appinstaller protocol handler as an access vector for malware that may lead
to ransomware distribution," the Microsoft Threat Intelligence team said.
It further noted that several cybercriminals are offering a malware kit for sale
as a service that leverages the MSIX file format and ms-appinstaller protocol
handler. The changes have gone into effect in App Installer version 1.21.3421.0
or higher.
The attacks take the form of signed malicious MSIX application packages that are
distributed via Microsoft Teams or malicious advertisements for legitimate
popular software on search engines like Google.
At least four different financially motivated hacking groups have been observed
taking advantage of the App Installer service since mid-November 2023, using it
as an entry point for follow-on human-operated ransomware activity -
Storm-0569, an initial access broker which propagates BATLOADER through search
engine optimization (SEO) poisoning with sites spoofing Zoom, Tableau,
TeamViewer, and AnyDesk, and uses the malware to deliver Cobalt Strike and
handoff the access to Storm-0506 for Black Basta ransomware deployment.
Storm-1113, an initial access broker that uses bogus MSIX installers
masquerading as Zoom to distribute EugenLoader (aka FakeBat), which acts as a
conduit for a variety of stealer malware and remote access trojans.
Sangria
Tempest (aka Carbon Spider and FIN7), which uses Storm-1113's EugenLoader to
drop Carbanak that, in turn, delivers an implant called Gracewire.
Alternatively, the group has relied on Google ads to lure users into downloading
malicious MSIX application packages from rogue landing pages to distribute
POWERTRASH, which is then used to load NetSupport RAT and Gracewire.
Storm-1674, an initial access broker that sends fake landing pages masquerading
as Microsoft OneDrive and SharePoint through Teams messages using the
TeamsPhisher tool, urging recipients to open PDF files that, when clicked,
prompts them to update their Adobe Acrobat Reader to download a malicious MSIX
installer that contains SectopRAT or DarkGate payloads.
Microsoft described
Storm-1113 as an entity that also dabbles in "as-a-service," providing malicious
installers and landing page frameworks mimicking well-known software to other
threat actors such as Sangria Tempest and Storm-1674.
In October 2023, Elastic Security Labs detailed another campaign in which
spurious MSIX Windows app package files for Google Chrome, Microsoft Edge,
Brave, Grammarly, and Cisco Webex were used to distribute a malware loader
dubbed GHOSTPULSE.
This is not the first time Microsoft has disabled the MSIX ms-appinstaller
protocol handler in Windows. In February 2022, the tech giant took the same step
to prevent threat actors from weaponizing it to deliver Emotet, TrickBot, and
Bazaloader.
"Threat actors have likely chosen the ms-appinstaller protocol handler vector
because it can bypass mechanisms designed to help keep users safe from malware,
such as Microsoft Defender SmartScreen and built-in browser warnings for
downloads of executable file formats," Microsoft said.
New Rugmi Malware Loader Surges with Hundreds of Daily Detections
28.12.23
Virus
The Hacker News
A new malware loader is being used by threat actors to
deliver a wide range of information stealers such as Lumma Stealer (aka
LummaC2), Vidar, RecordBreaker (aka Raccoon Stealer V2), and Rescoms.
Cybersecurity firm ESET is tracking the trojan under the name
Win/TrojanDownloader.Rugmi.
"This malware is a loader with three types of components: a downloader that
downloads an encrypted payload, a loader that runs the payload from internal
resources, and another loader that runs the payload from an external file on the
disk," the company said in its Threat Report H2 2023.
Telemetry data gathered by the company shows that detections for the Rugmi
loader spiked in October and November 2023, surging from single digit daily
numbers to hundreds per day.
Stealer malware is typically sold under a malware-as-a-service (MaaS) model to
other threat actors on a subscription basis. Lumma Stealer, for instance, is
advertised in underground forums for $250 a month. The most expensive plan costs
$20,000, but it also gives the customers access to the source code and the right
to sell it.
There is evidence to suggest that the codebase associated with Mars, Arkei, and
Vidar stealers has been repurposed to create Lumma.
Besides continuously adapting its tactics to evade detection, the off-the-shelf
tool is distributed through a variety of methods ranging from malvertising to
fake browser updates to cracked installations of popular software such as VLC
media player and OpenAI ChatGPT.
Another technique concerns the use of Discord's content delivery network (CDN)
to host and propagate the malware, as revealed by Trend Micro in October 2023.
This entails leveraging a combination of random and compromised Discord accounts
to send direct messages to prospective targets, offering them $10 or a Discord
Nitro subscription in exchange for their assistance on a project.
Users who agree to the offer are then urged to download an executable file
hosted on Discord CDN that masquerades as iMagic Inventory but, in reality,
contains the Lumma Stealer payload.
"Ready-made malware solutions contribute to the proliferation of malicious
campaigns because they make the malware available even to potentially less
technically skilled threat actors," ESET said.
"Offering a broader range of functions then serves to render Lumma Stealer even
more attractive as a product."
The disclosures come as McAfee Labs disclosed a new variant of NetSupport RAT,
which emerged from its legitimate progenitor NetSupport Manager and has since
been put to use by initial access brokers to gather information and perform
additional actions on victims of interest.
"The infection begins with obfuscated JavaScript files, serving as the initial
point of entry for the malware," McAfee said, adding it highlights the "evolving
tactics employed by cybercriminals."
The execution of the JavaScript file advances the attack chain by running
PowerShell commands to retrieve the remote control and stealer malware from an
actor-controlled server. The campaign's primary targets include the U.S. and
Canada.
Carbanak Banking Malware Resurfaces with New Ransomware Tactics
26.12.23
Virus
The Hacker News
The banking malware known as Carbanak has been observed
being used in ransomware attacks with updated tactics.
"The malware has adapted to incorporate attack vendors and techniques to
diversify its effectiveness," cybersecurity firm NCC Group said in an analysis
of ransomware attacks that took place in November 2023.
"Carbanak returned last month through new distribution chains and has been
distributed through compromised websites to impersonate various business-related
software."
Some of the impersonated tools include popular business-related software such as
HubSpot, Veeam, and Xero.
Carbanak, detected in the wild since at least 2014, is known for its data
exfiltration and remote control features. Starting off as a banking malware, it
has been put to use by the FIN7 cybercrime syndicate.
In the latest attack chain documented by NCC Group, the compromised websites are
designed to host malicious installer files masquerading as legitimate utilities
to trigger the deployment of Carbanak.
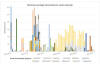
The development comes as 442 ransomware attacks were reported last month, up
from 341 incidents in October 2023. A total of 4,276 cases have been reported so
far this year, which is "less than 1000 incidents fewer than the total for 2021
and 2022 combined (5,198)."
The company's data shows that industrials (33%), consumer cyclicals (18%), and
healthcare (11%) emerged as the top targeted sectors, with North America (50%),
Europe (30%), and Asia (10%) accounting for most of the attacks.
As for the most commonly spotted ransomware families, LockBit, BlackCat, and
Play contributed to 47% (or 206 attacks) of 442 attacks. With BlackCat
dismantled by authorities this month, it remains to be seen what impact the move
will have on the threat landscape for the near future.
"With one month of the year still to go, the total number of attacks has
surpassed 4,000 which marks a huge increase from 2021 and 2022, so it will be
interesting to see if ransomware levels continue to climb next year," Matt Hull,
global head of threat intelligence at NCC Group, said.
The spike in ransomware attacks in November has also been corroborated by cyber
insurance firm Corvus, which said it identified 484 new ransomware victims
posted to leak sites.
"The ransomware ecosystem at large has successfully pivoted away from QBot," the
company said. "Making software exploits and alternative malware families part of
their repertoire is paying off for ransomware groups."
While the shift is the result of a law enforcement takedown of QBot's (aka
QakBot) infrastructure, Microsoft, last week, disclosed details of a low-volume
phishing campaign distributing the malware, underscoring the challenges in fully
dismantling these groups.
The development comes as Kaspersky revealed Akira ransomware's security measures
prevent its communication site from being analyzed by raising exceptions while
attempting to access the site using a debugger in the web browser.
The Russian cybersecurity company further highlighted ransomware operators'
exploitation of different security flaws in the Windows Common Log File System
(CLFS) driver – CVE-2022-24521, CVE-2022-37969, CVE-2023-23376, CVE-2023-28252
(CVSS scores: 7.8) – for privilege escalation.
Operation RusticWeb: Rust-Based Malware Targets Indian Government Entities
23.12.23
Virus
The Hacker News

Indian government entities and the defense sector have been targeted by a
phishing campaign that's engineered to drop Rust-based malware for intelligence
gathering.
The activity, first detected in October 2023, has been codenamed Operation
RusticWeb by enterprise security firm SEQRITE.
"New Rust-based payloads and encrypted PowerShell commands have been utilized to
exfiltrate confidential documents to a web-based service engine, instead of a
dedicated command-and-control (C2) server," security researcher Sathwik Ram
Prakki said.
Tactical overlaps have been uncovered between the cluster and those widely
tracked under the monikers Transparent Tribe and SideCopy, both of which are
assessed to be linked to Pakistan.
SideCopy is also a suspected subordinate element within Transparent Tribe. Last
month, SEQRITE detailed multiple campaigns undertaken by the threat actor
targeting Indian government bodies to deliver numerous trojans such as AllaKore
RAT, Ares RAT, and DRat.
Other recent attack chains documented by ThreatMon have employed decoy Microsoft
PowerPoint files as well as specially crafted RAR archives susceptible to
CVE-2023-38831 for malware delivery, enabling unbridled remote access and
control.
"The SideCopy APT Group's infection chain involves multiple steps, each
carefully orchestrated to ensure successful compromise," ThreatMon noted earlier
this year.
The latest set of attacks commences with a phishing email, leveraging social
engineering techniques to trick victims into interacting with malicious PDF
files that drop Rust-based payloads for enumerating the file system in the
background while displaying the decoy file to the victim.

Besides amassing files of interest, the malware is equipped to collect system
information and transmit them to the C2 server but lacks the features of other
advanced stealer malware available in the cybercrime underground.
A second infection chain identified by SEQRITE in December employs a similar
multi-stage process but substitutes the Rust malware with a PowerShell script
that takes care of the enumeration and exfiltration steps.
But in an interesting twist, the final-stage payload is launched via a Rust
executable that goes by the name "Cisco AnyConnect Web Helper." The gathered
information is ultimately uploaded to oshi[.]at domain, an anonymous public
file-sharing engine called OshiUpload.
"Operation RusticWeb could be linked to an APT threat as it shares similarities
with various Pakistan-linked groups," Ram Prakki said.
The disclosure comes nearly two months after Cyble uncovered a malicious Android
app utilized by the DoNot Team targeting individuals in the Kashmir region of
India.
The nation-state actor, also known by the names APT-C-35, Origami Elephant, and
SECTOR02, is believed to be of Indian origin and has a history of utilizing
Android malware to infiltrate devices belonging to people in Kashmir and
Pakistan.
The variant examined by Cyble is a trojanized version of an open-source GitHub
project called "QuranApp: Read and Explore" that comes fitted with a wide range
of spyware features to record audio and VoIP calls, capture screenshots, gather
data from various apps, download additional APK files, and track the victim's
location.
"The DoNot group's relentless efforts to refine their tools and techniques
underscore the ongoing threat they pose, particularly in their targeting of
individuals in the sensitive Kashmir region of India," Cyble said.
Decoy Microsoft Word Documents Used to Deliver Nim-Based Malware
23.12.23
Virus
The Hacker News

A new phishing campaign is leveraging decoy Microsoft Word documents as bait to
deliver a backdoor written in the Nim programming language.
"Malware written in uncommon programming languages puts the security community
at a disadvantage as researchers and reverse engineers' unfamiliarity can hamper
their investigation," Netskope researchers Ghanashyam Satpathy and Jan Michael
Alcantara said.
Nim-based malware has been a rarity in the threat landscape, although that has
been slowly changing in recent years as attackers continue to either develop
custom tools from scratch using the language or port existing versions of their
nefarious programs to it.
This has been demonstrated in the case of loaders such as NimzaLoader, Nimbda,
IceXLoader, as well as ransomware families tracked under the names Dark Power
and Kanti.
The attack chain documented by Netskope begins with a phishing email containing
a Word document attachment that, when opened, urges the recipient to enable
macros to activate the deployment of the Nim malware. The email sender disguises
themselves as a Nepali government official.
Once launched, the implant is responsible for enumerating running processes to
determine the existence of known analysis tools on the infected host and
promptly terminate itself should it find one.
Otherwise, the backdoor establishes connections with a remote server that mimics
a government domain from Nepal, including the National Information Technology
Center (NITC) and awaits further instructions. The command-and-control (C2)
servers are no longer accessible -
mail[.]mofa[.]govnp[.]org
nitc[.]govnp[.]org
mx1[.]nepal[.]govnp[.]org
dns[.]govnp[.]org
"Nim is a statically typed compiled programming language,"
the researchers said. "Aside from its familiar syntax, its cross-compilation
features allow attackers to write one malware variant and have it cross-compiled
to target different platforms."
The disclosure comes as Cyble revealed a social engineering campaign that
leverages messages on social media platforms to deliver a new Python-based
stealer malware called Editbot Stealer that's designed to harvest and exfiltrate
valuable data via an actor-controlled Telegram channel.

Even as threat actors are experimenting with new malware strains, phishing
campaigns have also been observed distributing known malware such as DarkGate
and NetSupport RAT via email and compromised websites with fake update lures
(aka RogueRaticate), particularly those from a cluster dubbed BattleRoyal.
Enterprise security firm Proofpoint said it identified at least 20 campaigns
that used DarkGate malware between September and November 2023, before switching
to NetSupport RAT earlier this month.
One attack sequence identified in early October 2023 particularly stands out for
chaining two traffic delivery systems (TDSs) – 404 TDS and Keitaro TDS – to
filter and redirect victims meeting their criteria to an actor-operated domain
hosting a payload that exploited CVE-2023-36025 (CVSS score: 8.8), a
high-severity Windows SmartScreen security bypass that was addressed by
Microsoft in November 2023.
This implies BattleRoyal weaponized this vulnerability as a zero-day a month
before it was publicly revealed by the tech giant.
DarkGate is designed to steal information and download additional malware
payloads, while NetSupport RAT, which started off as a bona fide remote
administration tool, has metamorphosed into a potent weapon wielded by
malevolent actors to infiltrate systems and establish unfettered remote control.
"Cybercriminal threat actors [are] adopting new, varied, and increasingly
creative attack chains – including the use of various TDS tools – to enable
malware delivery," Proofpoint said.
"Additionally, the use of both email and fake update lures shows the actor using
multiple types of social engineering techniques in an attempt to get users to
install the final payload."
DarkGate has also been put to use by other threat actors like TA571 and TA577,
both of which are known to disseminate a variety of malware, including AsyncRAT,
NetSupport, IcedID, PikaBot, and QakBot (aka Qbot).
"TA577 for example, one of the most prominent Qbot distributors, returned to
email threat data in September to deliver DarkGate malware and has since been
observed delivering PikaBot in campaigns that typically have tens of thousands
of messages," Selena Larson, senior threat intelligence analyst at Proofpoint,
told The Hacker News.
UAC-0099 Using WinRAR Exploit to Target Ukrainian Firms with LONEPAGE Malware
23.12.23
Virus
The Hacker News
The threat actor known as UAC-0099 has been linked to
continued attacks aimed at Ukraine, some of which leverage a high-severity flaw
in the WinRAR software to deliver a malware strain called LONEPAGE.
"The threat actor targets Ukrainian employees working for companies outside of
Ukraine," cybersecurity firm Deep Instinct said in a Thursday analysis.
UAC-0099 was first documented by the Computer Emergency Response Team of Ukraine
(CERT-UA) in June 2023, detailing its attacks against state organizations and
media entities for espionage motives.
The attack chains leveraged phishing messages containing HTA, RAR, and LNK file
attachments that led to the deployment of LONEPAGE, a Visual Basic Script (VBS)
malware that's capable of contacting a command-and-control (C2) server to
retrieve additional payloads such as keyloggers, stealers, and screenshot
malware.
"During 2022-2023, the mentioned group received unauthorized remote access to
several dozen computers in Ukraine," CERT-UA said at the time.
The latest analysis from Deep Instinct reveals that the use of HTA attachments
is just one of three different infection chains, the other two of which leverage
self-extracting (SFX) archives and bobby-trapped ZIP files. The ZIP files
exploit the WinRAR vulnerability (CVE-2023-38831, CVSS score: 7.8) to distribute
LONEPAGE.

In the former, the SFX file houses an LNK shortcut that's disguised as a DOCX
file for a court summons while using the icon for Microsoft WordPad to entice
the victim into opening it, resulting in the execution of malicious PowerShell
code that drops the LONEPAGE malware.
The other attack sequence uses a specially crafted ZIP archive that's
susceptible to CVE-2023-38831, with Deep Instinct finding two such artifacts
created by UAC-0099 on August 5, 2023, three days after WinRAR maintainers
released a patch for the bug.
"The tactics used by 'UAC-0099' are simple, yet effective," the company said.
"Despite the different initial infection vectors, the core infection is the same
— they rely on PowerShell and the creation of a scheduled task that executes a
VBS file."
The development comes as CERT-UA warned of a new wave of phishing messages
purporting to be outstanding Kyivstar dues to propagate a remote access trojan
known as Remcos RAT. The agency attributed the campaign to UAC-0050.
Microsoft Warns of New 'FalseFont' Backdoor Targeting the Defense Sector
23.12.23
Virus
The Hacker News
Organizations in the Defense Industrial Base (DIB) sector
are in the crosshairs of an Iranian threat actor as part of a campaign designed
to deliver a never-before-seen backdoor called FalseFont.
The findings come from Microsoft, which is tracking the activity under its
weather-themed moniker Peach Sandstorm (formerly Holmium), which is also known
as APT33, Elfin, and Refined Kitten.
"FalseFont is a custom backdoor with a wide range of functionalities that allow
operators to remotely access an infected system, launch additional files, and
send information to its [command-and-control] servers," the Microsoft Threat
Intelligence team said on X (previously Twitter).
The first recorded use of the implant was in early November 2023.
The tech giant further said that the latest development aligns with previous
activity from Peach Sandstorm and demonstrates a continued evolution of the
threat actor's tradecraft.
In a report published in September 2023, Microsoft linked the group to password
spray attacks carried out against thousands of organizations globally between
February and July 2023. The intrusions primarily singled out satellite, defense,
and pharmaceutical sectors.
The end goal, the company said, is to facilitate intelligence collection in
support of Iranian state interests. Peach Sandstorm is believed to have been
active since at least 2013.
The disclosure comes as the Israel National Cyber Directorate (INCD) accused
Iran and Hezbollah of attempting to unsuccessfully target Ziv Hospital through
hacking crews named Agrius and Lebanese Cedar.
The agency also revealed details of a phishing campaign in which a fake advisory
for a security flaw in F5 BIG-IP products is employed as a decoy to deliver
wiper malware on Windows and Linux systems.
The lure for the targeted attack is a critical authentication bypass
vulnerability (CVE-2023-46747, CVSS score: 9.8) that came to light in late
October 2023. The scale of the campaign is currently unknown.
Experts Detail Multi-Million Dollar Licensing Model of Predator Spyware
23.12.23
Virus
The Hacker News
A new analysis of the sophisticated commercial spyware
called Predator has revealed that its ability to persist between reboots is
offered as an "add-on feature" and that it depends on the licensing options
opted by a customer.
"In 2021, Predator spyware couldn't survive a reboot on the infected Android
system (it had it on iOS)," Cisco Talos researchers Mike Gentile, Asheer
Malhotra, and Vitor Ventura said in a report shared with The Hacker News.
"However, by April 2022, that capability was being offered to their customers."
Predator is the product of a consortium called the Intellexa Alliance, which
includes Cytrox (subsequently acquired by WiSpear), Nexa Technologies, and
Senpai Technologies. Both Cytrox and Intellexa were added to the Entity List by
the U.S. in July 2023 for "trafficking in cyber exploits used to gain access to
information systems."
The latest findings come more than six months after the cybersecurity vendor
detailed the inner workings of Predator and its harmonious equation with another
loader component called Alien.
"Alien is crucial to Predator's successful functioning, including the additional
components loaded by Predator on demand," Malhotra told The Hacker News at the
time. "The relationship between Alien and Predator is extremely symbiotic,
requiring them to continuously work in tandem to spy on victims."
Predator, which can target both Android and iOS, has been described as a "remote
mobile extraction system" that's sold on a licensing model that run into
millions of dollars based on the exploit used for initial access and the number
of concurrent infections, putting them out of reach of script kiddies and novice
criminals.
Spyware such as Predator and Pegasus, which is developed by NSO Group, often
rely on zero-day exploit chains in Android, iOS, and web browsers as covert
intrusion vectors. But as Apple and Google continue to plug the security gaps,
these exploit chains may be rendered ineffective, forcing them to go back to the
drawing board.

However, it's worth noting that the companies behind mercenary surveillance
tools can also procure either full or partial exploit chains from exploit
brokers and fashion them into an operational exploit that can be employed to
effectively breach target devices.
Another key aspect of Intellexa's business model is that offloads the work of
setting up the attack infrastructure to the customers themselves, leaving it
with room for plausible deniability should the campaigns come to light (as it
inevitably does).
"The delivery of Intellexa's supporting hardware is done at a terminal or
airport," the researchers said.
"This delivery method is known as Cost Insurance and Freight (CIF), which is
part of the shipping industry's jargon ('Incoterms'). This mechanism allows
Intellexa to claim that they have no visibility of where the systems are
deployed and eventually located."
On top of that, Intellexa possesses "first-hand knowledge" of whether their
customers are performing surveillance operations outside their own borders owing
to the fact that the operations are intrinsically connected to the license,
which, by default, is restricted to a single phone country code prefix.
This geographic limitation, nonetheless, can be loosened for an additional fee.

Cisco Talos noted that while public exposure of private-sector offensive actors
and their campaigns have been successful at attribution efforts, it has had
little impact on their ability to conduct and grow their business across the
world, even if it may affect their customers, such as governments.
"It may increase the costs by making them buy or create new exploit chains but
these vendors appear to have seamlessly acquired new exploit chains, enabling
them to remain in business by jumping from one set of exploits to another as a
means of initial access," the researchers said.
"What is needed is the public disclosure of technical analyses of the mobile
spyware and tangible samples enabling public scrutiny of the malware. Such
public disclosures will not only enable greater analyses and drive detection
efforts but also impose development costs on vendors to constantly evolve their
implants."
New JavaScript Malware Targeted 50,000+ Users at Dozens of Banks Worldwide
23.12.23
Virus
The Hacker News
A new piece of JavaScript malware has been observed attempting to steal users'
online banking account credentials as part of a campaign that has targeted more
than 40 financial institutions across the world.
The activity cluster, which employs JavaScript web injections, is estimated to
have led to at least 50,000 infected user sessions spanning North America, South
America, Europe, and Japan.
IBM Security Trusteer said it detected the campaign in March 2023.
"Threat actors' intention with the web injection module is likely to compromise
popular banking applications and, once the malware is installed, intercept the
users' credentials in order to then access and likely monetize their banking
information," security researcher Tal Langus said.
Attack chains are characterized by the use of scripts loaded from the threat
actor-controlled server ("jscdnpack[.]com"), specifically targeting a page
structure that's common to several banks. It's suspected the malware is
delivered to targets by some other means, e.g., via phishing emails or
malvertising.
When the victim visits a bank website, the login page is altered to incorporate
malicious JavaScript capable of harvesting the credentials and one-time
passwords (OTPs). The script is obfuscated to conceal its true intent.
"This web injection doesn't target banks with different login pages, but it does
send data about the infected machine to the server and can easily be modified to
target other banks," Langus said.
"The script's behavior is highly dynamic, continuously querying both the
command-and-control (C2) server and the current page structure and adjusting its
flow based on the information obtained."
The response from the server determines its next course of action, allowing it
to erase traces of the injections, and insert fraudulent user interface elements
to accept OTPs to bypass security protections as well as introduce an error
message saying online banking services will be unavailable for a time period of
12 hours.
IBM said it's an attempt to dissuade the victims from logging in to their
accounts, providing the threat actors with a window of opportunity to seize
control of the accounts and perform unauthorized actions.
While the exact origins of the malware are presently not known, the indicators
of compromise (IoCs) suggest a possible connection to a known stealer and loader
family known as DanaBot, which has been propagated via malicious ads on Google
Search and has acted as acted an initial access vector for ransomware.

"This sophisticated threat showcases advanced capabilities, particularly in
executing man-in-the-browser attacks with its dynamic communication, web
injection methods and the ability to adapt based on server instructions and
current page state," Langus said.
The development comes as Sophos shed more light on a pig butchering scheme in
which potential targets are lured into investing in a fake liquidity mining
service, uncovering a broader set of scams that has netted the actors nearly
$2.9 million worth of cryptocurrency this year as of November 15 from 90
victims.
"They appear to have been run by three separate threat activity groups using
identical fraudulent decentralized finance ('DeFi') app sites, suggesting that
they are part of or affiliated with a single [Chinese] organized crime ring,"
security researcher Sean Gallagher said.
According to data shared by Europol in its Internet Organized Crime Threat
Assessment (IOCTA) earlier this week, investment fraud and business email
compromise (BEC) fraud remain the most prolific online fraud schemes.
"A concerning threat around investment fraud is its use in combination with
other fraud schemes against the same victims," the agency said.
"Investment fraud is sometimes linked to romance scams: criminals slowly build a
relationship of trust with the victim and then convince them to invest their
savings on fraudulent cryptocurrency trading platforms, leading to large
financial losses."
On a related note, cybersecurity company Group-IB said it identified 1,539
phishing websites impersonating postal operators and delivery companies since
the start of November 2023. They are suspected to be created for a single scam
campaign.
In these attacks, users are sent SMS messages that mimic well-known postal
services and are prompted to visit the counterfeit websites to enter their
personal and payment details, citing urgent or failed deliveries.
The operation is also notable for incorporating various evasion methods to fly
under the radar. This includes limiting access to the scam websites based on
geographic locations, making sure that they work only on specific devices and
operating systems, and shortening the duration for which they are live.
"The campaign affects postal brands in 53 countries," Group-IB said. "Most of
the detected phishing pages target users in Germany (17.5%), Poland (13.7%),
Spain (12.5%), U.K. (4.2%), Turkey (3.4%) and Singapore (3.1%)."
New Go-Based JaskaGO Malware Targeting Windows and macOS Systems
21.12.23
Virus
The Hacker News
A new Go-based information stealer malware called JaskaGO
has emerged as the latest cross-platform threat to infiltrate both Windows and
Apple macOS systems.
AT&T Alien Labs, which made the discovery, said the malware is "equipped with an
extensive array of commands from its command-and-control (C&C) server."
Artifacts designed for macOS were first observed in July 2023, impersonating
installers for legitimate software such as CapCut. Other variants of the malware
have masqueraded as AnyConnect and security tools.
Upon installation, JaskaGO runs checks to determine if it is executing within a
virtual machine (VM) environment, and if so, executes a harmless task like
pinging Google or printing a random number in a likely effort to fly under the
radar.
In other scenarios, JaskaGO proceeds to harvest information from the victim
system and establishes a connection to its C&C for receiving further
instructions, including executing shell commands, enumerating running processes,
and downloading additional payloads.
It's also capable of modifying the clipboard to facilitate cryptocurrency theft
by substituting wallet addresses and siphoning files and data from web browsers.
"On macOS, JaskaGO employs a multi-step process to establish persistence within
the system," security researcher Ofer Caspi said, outlining its capabilities to
run itself with root permissions, disable Gatekeeper protections, and create a
custom launch daemon (or launch agent) to ensure it's automatically launched
during system startup.
It's currently not known how the malware is distributed and if it entails
phishing or malvertising lures. The scale of the campaign remains unclear as
yet.
"JaskaGO contributes to a growing trend in malware development leveraging the Go
programming language," Caspi said.
"Go, also known as Golang, is recognized for its simplicity, efficiency, and
cross-platform capabilities. Its ease of use has made it an attractive choice
for malware authors seeking to create versatile and sophisticated threats."
8220 Gang Exploiting Oracle WebLogic Server Vulnerability to Spread Malware
19.12.23
Virus
The Hacker News
The threat actors associated with the 8220 Gang have been
observed exploiting a high-severity flaw in Oracle WebLogic Server to propagate
their malware.
The security shortcoming is CVE-2020-14883 (CVSS score: 7.2), a remote code
execution bug that could be exploited by authenticated attackers to take over
susceptible servers.
"This vulnerability allows remote authenticated attackers to execute code using
a gadget chain and is commonly chained with CVE-2020-14882 (an authentication
bypass vulnerability also affecting Oracle Weblogic Server) or the use of
leaked, stolen, or weak credentials," Imperva said in a report published last
week.
The 8220 Gang has a history of leveraging known security flaws to distribute
cryptojacking malware. Earlier this May, the group was spotted utilizing another
shortcoming in Oracle WebLogic servers (CVE-2017-3506, CVSS score: 7.4) to rope
the devices into a crypto mining botnet.
Recent attack chains documented by Imperva entail the exploitation of
CVE-2020-14883 to specially craft XML files and ultimately run code responsible
for deploying stealer and coin mining malware such as Agent Tesla, rhajk, and
nasqa.

"The group appears to be opportunistic when selecting their targets, with no
clear trend in country or industry," Imperva security researcher Daniel Johnston
said.
Targets of the campaign include healthcare, telecommunications, and financial
services sectors in the U.S., South Africa, Spain, Columbia, and Mexico.
"The group relies on simple, publicly available exploits to target well-known
vulnerabilities and exploit easy targets to achieve their objectives," Johnston
added. "While considered unsophisticated, they are constantly evolving their
tactics and techniques to evade detection."
Rhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges
19.12.23 Virus
The Hacker News
The developers of the information stealer malware known
as Rhadamanthys are actively iterating on its features, broadening its
information-gathering capabilities and also incorporating a plugin system to
make it more customizable.
This approach not only transforms it into a threat capable of delivering
"specific distributor needs," but also makes it more potent, Check Point said in
a technical deep dive published last week.
Rhadamanthys, first documented by ThreatMon in October 2022, has been sold under
the malware-as-a-service (MaaS) model as early as September 2022 by an actor
under the alias "kingcrete2022."
Typically distributed through malicious websites mirroring those of genuine
software that are advertised through Google ads, the malware is capable of
harvesting a wide range of sensitive information from compromised hosts,
including from web browsers, crypto wallets, email clients, VPN, and instant
messaging apps.
"Rhadamanthys represents a step in the emerging tradition of malware that tries
to do as much as possible, and also a demonstration that in the malware
business, having a strong brand is everything," the Israeli cybersecurity firm
noted in March 2022.
A subsequent investigation into the off-the-shelf malware in August revealed
"design and implementation" overlap with that of the Hidden Bee coin miner.
"The similarity is apparent at many levels: custom executable formats, the use
of similar virtual filesystems, identical paths to some of the components,
reused functions, similar use of steganography, use of LUA scripts, and overall
analogous design," the researchers said, describing the malware's development as
"fast-paced and ongoing."
As of writing, the current working version of Rhadamanthys is 0.5.2, per the
description on the threat actor's Telegram channel.
Check Point's analysis of versions 0.5.0 and 0.5.1 reveals a new plugin system
that effectively makes it more of a Swiss Army knife, indicating a shift towards
modularization and customization. This also allows the stealer customers to
deploy additional tools tailored to their targets.
The stealer components are both active, capable of opening processes and
injecting additional payloads designed to facilitate information theft, and
passive, which are designed to search and parse specific files to retrieve saved
credentials.
Another noticeable aspect is the use of a Lua script runner that can load up to
100 Lua scripts to pilfer as much information as possible from cryptocurrency
wallets, email agents, FTP services, note-taking apps, instant messengers, VPNs,
two-factor authentication apps, and password managers.
Version 0.5.1 goes a step further, adding clipper functionality to alter
clipboard data matching wallet addresses to divert cryptocurrency payments to an
attacker-controlled wallet as well as an option to recover Google Account
cookies, following the footsteps of Lumma Stealer.
"The author keeps enriching the set of available features, trying to make it not
only a stealer but a multipurpose bot, by enabling it to load multiple
extensions created by a distributor," security researcher Aleksandra
"Hasherezade" Doniec said.
"The added features, such as a keylogger, and collecting information about the
system, are also a step towards making it a general-purpose spyware."
AsyncRAT's Code Injection into aspnet_compiler.exe#
The findings come as
Trend Micro detailed new AsyncRAT infection chains that leverage a legitimate
Microsoft process called aspnet_compiler.exe, which is used for precompiling
ASP.NET web applications, to stealthily deploy the remote access trojan (RAT)
via phishing attacks.
Similar to how Rhadamanthys carries out code injection into running processes,
the multi-stage process culminates in the AsyncRAT payload being injected into a
newly spawned aspnet_compiler.exe process to ultimately establish contact with a
command-and-control (C2) server.
"The AsyncRAT backdoor has other capabilities depending on the embedded
configuration," security researchers Buddy Tancio, Fe Cureg, and Maria Emreen
Viray said. "This includes anti-debugging and analysis checks, persistence
installation, and keylogging."
It's also designed to scan particular folders within the application directory,
browser extensions, and user data to check for the presence of crypto wallets.
On top of that, the threat actors have been observed relying on Dynamic DNS
(DDNS) to deliberately obfuscate their activities.
"The use of dynamic host servers allows threat actors to seamlessly update their
IP addresses, strengthening their ability to remain undetected within the
system," the researchers said.
QakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry
19.12.23
Virus
The Hacker News
A new wave of phishing messages distributing the QakBot
malware has been observed, more than three months after a law enforcement effort
saw its infrastructure dismantled by infiltrating its command-and-control (C2)
network.
Microsoft, which made the discovery, described it as a low-volume campaign that
began on December 11, 2023, and targeted the hospitality industry.
"Targets received a PDF from a user masquerading as an IRS employee," the tech
giant said in a series of posts shared on X (formerly Twitter).
"The PDF contained a URL that downloads a digitally signed Windows Installer
(.msi). Executing the MSI led to Qakbot being invoked using export 'hvsi'
execution of an embedded DLL."
Microsoft said that the payload was generated the same day the campaign started
and that it's configured with the previously unseen version 0x500.
Zscaler ThreatLabz, in a post shared on X, described the resurfaced QakBot as a
64-bit binary that utilizes AES for network encryption and sends POST requests
to the path /teorema505.
QakBot, also called QBot and Pinkslipbot, was disrupted as part of a coordinated
effort called Operation Duck Hunt after the authorities managed to gain access
to its infrastructure and instructed the infected computers to download an
uninstaller file to render the malware ineffective.

Traditionally distributed via spam email messages containing malicious
attachments or hyperlinks, QakBot is capable of harvesting sensitive information
as well as delivering additional malware, including ransomware.
In October 2023, Cisco Talos revealed that QakBot affiliates were leveraging
phishing lures to deliver a mix of ransomware, remote access trojans, and
stealer malware.
The return of QakBot mirrors that of Emotet, which also resurfaced in late 2021
months after it was dismantled by law enforcement and has remained an enduring
threat, albeit at a lower level.
While it remains to be seen if the malware will return to its former glory, the
resilience of such botnets underscores the need for organizations to avoid
falling victim to spam emails used in Emotet and QakBot campaigns.
New NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
15.12.23
Virus
The Hacker News
A novel multi-platform threat called NKAbuse has been
discovered using a decentralized, peer-to-peer network connectivity protocol
known as NKN (short for New Kind of Network) as a communications channel.
"The malware utilizes NKN technology for data exchange between peers,
functioning as a potent implant, and equipped with both flooder and backdoor
capabilities," Russian cybersecurity company Kaspersky said in a Thursday
report.
NKN, which has over 62,000 nodes, is described as a "software overlay network
built on top of today's Internet that enables users to share unused bandwidth
and earn token rewards." It incorporates a blockchain layer on top of the
existing TCP/IP stack.
While threat actors are known to take advantage of emerging communication
protocols for command-and-control (C2) purposes and evade detection, NKAbuse
leverages blockchain technology to conduct distributed denial-of-service (DDoS)
attacks and function as an implant inside compromised systems.
Specifically, it uses the protocol to talk to the bot master and receive/send
commands. The malware is implemented in the Go programming language, and
evidence points to it being used primarily to single out Linux systems,
including IoT devices.
It's currently not known how widespread the attacks are, but one instance
identified by Kaspersky entails the exploitation of a six-year-old critical
security flaw in Apache Struts (CVE-2017-5638, CVSS score: 10.0) to breach an
unnamed financial company.

Successful exploitation is followed by the delivery of an initial shell script
that's responsible for downloading the implant from a remote server, but not
before checking the operating system of the target host. The server hosting the
malware houses eight different versions of NKAbuse to support various CPU
architectures: i386, arm64, arm, amd64, mips, mipsel, mips64, and mips64el.
Another notable aspect is its lack of a self-propagation mechanism, meaning the
malware needs to be delivered to a target by another initial access pathway,
such as through the exploitation of security flaws.
"NKAbuse makes use of cron jobs to survive reboots," Kaspersky said. "To achieve
that, it needs to be root. It checks that the current user ID is 0 and, if so,
proceeds to parse the current crontab, adding itself for every reboot."
NKAbuse also incorporates a bevy of backdoor features that allow it to
periodically send a heartbeat message to the bot master, which contains
information about the system, capture screenshots of the current screen, perform
file operations, and run system commands.
"This particular implant appears to have been meticulously crafted for
integration into a botnet, yet it can adapt to functioning as a backdoor in a
specific host," Kaspersky said. "Moreover, its use of blockchain technology
ensures both reliability and anonymity, which indicates the potential for this
botnet to expand steadily over time, seemingly devoid of an identifiable central
controller."
"We are surprised to see NKN is used in such a way," Zheng "Bruce" Li,
co-founder of NKN, told The Hacker News. "We built NKN to provide true
peer-to-peer communication that is secure, private, decentralized, and massively
scalable. We are trying to learn more about the report to see if together we can
make the internet safe and neutral."
116 Malware Packages Found on PyPI Repository Infecting Windows and Linux
Systems
15.12.23
Virus
The Hacker News

Cybersecurity researchers have identified a set of 116 malicious packages on the
Python Package Index (PyPI) repository that are designed to infect Windows and
Linux systems with a custom backdoor.
"In some cases, the final payload is a variant of the infamous W4SP Stealer, or
a simple clipboard monitor to steal cryptocurrency, or both," ESET researchers
Marc-Etienne M.Léveillé and Rene Holt said in a report published earlier this
week.
The packages are estimated to have been downloaded over 10,000 times since May
2023.
The threat actors behind the activity have been observed using three techniques
to bundle malicious code into Python packages, namely via a test.py script,
embedding PowerShell in setup.py file, and incorporating it in obfuscated form
in the __init__.py file.
Irrespective of the method used, the end goal of the campaign is to compromise
the targeted host with malware, primarily a backdoor capable of remote command
execution, data exfiltration, and taking screenshots. The backdoor module is
implemented in Python for Windows and in Go for Linux.
Alternately, the attack chains also culminate in the deployment of W4SP Stealer
or a clipper malware designed to keep close tabs on a victim's clipboard
activity and swapping the original wallet address, if present, with an
attacker-controlled address.
The development is the latest in a wave of compromised Python packages attackers
have released to poison the open-source ecosystem and distribute a medley of
malware for supply chain attacks.
It's also the newest addition to a steady stream of bogus PyPI packages that
have acted as a stealthy channel for distributing stealer malware. In May 2023,
ESET revealed another cluster of libraries that were engineered to propagate
Sordeal Stealer, which borrows its features from W4SP Stealer.
Then, last month, malicious packages masquerading as seemingly innocuous
obfuscation tools were found to deploy a stealer malware codenamed BlazeStealer.
"Python developers should thoroughly vet the code they download, especially
checking for these techniques, before installing it on their systems," the
researchers cautioned.
The disclosure also follows the discovery of npm packages that were found
targeting an unnamed financial institution as part of an "advanced adversary
simulation exercise." The names of the modules, which contained an encrypted
blob, have been withheld to protect the identity of the organization.
"This decrypted payload contains an embedded binary that cleverly exfiltrates
user credentials to a Microsoft Teams webhook that is internal to the target
company in question," software supply chain security firm Phylum disclosed last
week.
New MrAnon Stealer Malware Targeting German Users via Booking-Themed Scam
12.12.23
Virus
The Hacker News

A phishing campaign has been observed delivering an information stealer malware
called MrAnon Stealer to unsuspecting victims via seemingly benign
booking-themed PDF lures.
"This malware is a Python-based information stealer compressed with cx-Freeze to
evade detection," Fortinet FortiGuard Labs researcher Cara Lin said. "MrAnon
Stealer steals its victims' credentials, system information, browser sessions,
and cryptocurrency extensions."
There is evidence to suggest that Germany is the primary target of the attack as
of November 2023, owing to the number of times the downloader URL hosting the
payload has been queried.
Masquerading as a company looking to book hotel rooms, the phishing email bears
a PDF file that, upon opening, activates the infection by prompting the
recipient to download an updated version of Adobe Flash.
Doing so results in the execution of .NET executables and PowerShell scripts to
ultimately run a pernicious Python script, which is capable of gathering data
from several applications and exfiltrating it to a public file-sharing website
and the threat actor's Telegram channel.
It's also capable of capturing information from instant messaging apps, VPN
clients, and files matching a desired list of extensions.

MrAnon Stealer is offered by the authors for $500 per month (or $750 for two
months), alongside a crypter ($250 per month) and a stealthy loader ($250 per
month).
"The campaign initially disseminated Cstealer in July and August but
transitioned to distributing MrAnon Stealer in October and November," Lin said.
"This pattern suggests a strategic approach involving the continued use of
phishing emails to propagate a variety of Python-based stealers."
The disclosure comes as the China-linked Mustang Panda is behind a
spear-phishing email campaign targeting the Taiwanese government and diplomats
with an aim to deploy SmugX, a new variant of the PlugX backdoor that was
previously uncovered by Check Point in July 2023.
Researchers Unveal GuLoader Malware's Latest Anti-Analysis Techniques
9.12.23
Virus
The Hacker News
Threat hunters have unmasked the latest tricks adopted by
a malware strain called GuLoader in an effort to make analysis more challenging.
"While GuLoader's core functionality hasn't changed drastically over the past
few years, these constant updates in their obfuscation techniques make analyzing
GuLoader a time-consuming and resource-intensive process," Elastic Security Labs
researcher Daniel Stepanic said in a report published this week.
First spotted in late 2019, GuLoader (aka CloudEyE) is an advanced
shellcode-based malware downloader that's used to distribute a wide range of
payloads, such as information stealers, while incorporating a bevy of
sophisticated anti-analysis techniques to dodge traditional security solutions.
A steady stream of open-source reporting into the malware in recent months has
revealed the threat actors behind it have continued to improve its ability to
bypass existing or new security features alongside other implemented features.
GuLoader is typically spread through phishing campaigns, where victims are
tricked into downloading and installing the malware through emails bearing ZIP
archives or links containing a Visual Basic Script (VBScript) file.
Israeli cybersecurity company Check Point, in September 2023, revealed that
"GuLoader is now sold under a new name on the same platform as Remcos and is
implicitly promoted as a crypter that makes its payload fully undetectable by
antiviruses."
One of the recent changes to the malware is an improvement of an anti-analysis
technique first disclosed by CrowdStroke in December 2022 and which is centered
around its Vectored Exception Handling (VEH) capability.
It's worth pointing out that the mechanism was previously detailed by both
McAfee Labs and Check Point in May 2023, with the former stating that "GuLoader
employs the VEH mainly for obfuscating the execution flow and to slow down the
analysis."
The method "consists of breaking the normal flow of code execution by
deliberately throwing a large number of exceptions and handling them in a vector
exception handler that transfers control to a dynamically calculated address,"
Check Point said.
GuLoader is far from the only malware family to have received constant updates.
Another notable example is DarkGate, a remote access trojan (RAT) that enables
attackers to fully compromise victim systems.
Sold as malware-as-a-service (MaaS) by an actor known as RastaFarEye on
underground forums for a monthly fee of $15,000, the malware uses phishing
emails containing links to distribute the initial infection vector: a VBScript
or Microsoft Software Installer (MSI) file.
Trellix, which analyzed the latest version of DarkGate (5.0.19), said it
"introduces a new execution chain using DLL side-loading and enhanced shellcodes
and loaders." Further, it comes with a complete rework of the RDP password theft
feature.
"The threat actor has been actively monitoring threat reports to perform quick
changes thus evading detections," security researchers Ernesto Fernández
Provecho, Pham Duy Phuc, Ciana Driscoll, and Vinoo Thomas said.
"Its adaptability, the speed with which it iterates, and the depth of its
evasion methods attest to the sophistication of modern malware threats."
The development comes as remote access trojans like Agent Tesla and AsyncRAT
have been observed being propagated using novel email-based infection chains
that leverage steganography and uncommon file types in an attempt to bypass
antivirus detection measures.

It also follows a report from the HUMAN Satori Threat Intelligence Team about
how an updated version of a malware obfuscation engine called ScrubCrypt (aka
BatCloak) is being used to deliver the RedLine stealer malware.
"The new ScrubCrypt build was sold to threat actors on a small handful of dark
web marketplaces, including Nulled Forum, Cracked Forum, and Hack Forums," the
company said.
N. Korea's Kimsuky Targeting South Korean Research Institutes with Backdoor
Attacks
9.12.23
Virus
The Hacker News
The North Korean threat actor known as Kimsuky has been
observed targeting research institutes in South Korea as part of a
spear-phishing campaign with the ultimate goal of distributing backdoors on
compromised systems.
"The threat actor ultimately uses a backdoor to steal information and execute
commands," the AhnLab Security Emergency Response Center (ASEC) said in an
analysis posted last week.
The attack chains commence with an import declaration lure that's actually a
malicious JSE file containing an obfuscated PowerShell script, a Base64-encoded
payload, and a decoy PDF document.
The next stage entails opening the PDF file as a diversionary tactic, while the
PowerShell script is executed in the background to launch the backdoor.
The malware, for its part, is configured to collect network information and
other relevant data (i.e., host name, user name, and operating system version)
and transmit the encoded details to a remote server.
It's also capable of running commands, executing additional payloads, and
terminating itself, turning it into a backdoor for remote access to the infected
host.
Kimsuky, active since at least 2012, started off targeting South Korean
government entities, think tanks, and individuals identified as experts in
various fields, before expanding its victimology footprint to encompass Europe,
Russia, and the U.S.
Earlier this month, the U.S. Treasury Department sanctioned Kimsuky for
gathering intelligence to support North Korea's strategic objectives, including
geopolitical events, foreign policy, and diplomatic efforts.
"Kimsuky has focused its intelligence collection activities on foreign policy
and national security issues related to the Korean peninsula, nuclear policy,
and sanctions," cybersecurity firm ThreatMon noted in a recent report.
The state-sponsored group has also been observed leveraging booby-trapped URLs
that, when clicked, download a bogus ZIP archive masquerading as an update for
the Chrome browser to deploy a malicious VBScript from Google Drive that employs
the cloud storage as a conduit for data exfiltration and command-and-control
(C2).
Lazarus Group Goes Phishing on Telegram#
The development comes as blockchain
security company SlowMist implicated the notorious North Korea-backed outfit
called the Lazarus Group in a widespread phishing campaign on Telegram targeting
the cryptocurrency sector.
"More recently, these hackers have escalated their tactics by posing as
reputable investment institutions to execute phishing scams against various
cryptocurrency project teams," the Singapore-based firm said.
After establishing rapport, the targets are deceived into downloading a
malicious script under the guise of sharing an online meeting link that
facilitates crypto theft.
It also follows a report from the Seoul Metropolitan Police Agency (SMPA) that
accused the Lazarus sub-cluster codenamed Andariel of stealing technical
information about anti-aircraft weapon systems from domestic defense companies
and laundering ransomware proceeds back to North Korea.

It is estimated that more than 250 files amounting to 1.2 terabytes have been
stolen in the attacks. To cover up the tracks, the adversary is said to have
used servers from a local company that "rents servers to subscribers with
unclear identities" as an entry point.
In addition, the group extorted 470 million won ($356,000) worth of bitcoin from
three South Korean firms in ransomware attacks and laundered them through
virtual asset exchanges such as Bithumb and Binance. It's worth noting that
Andariel has been linked to the deployment of Maui ransomware in the past.
New Stealthy 'Krasue' Linux Trojan Targeting Telecom Firms in Thailand
7.12.23
Virus
The Hacker News
A previously unknown Linux remote access trojan called
Krasue has been observed targeting telecom companies in Thailand by threat
actors to main covert access to victim networks at lease since 2021.
Named after a nocturnal female spirit of Southeast Asian folklore, the malware
is "able to conceal its own presence during the initialization phase," Group-IB
said in a report shared with The Hacker News.
The exact initial access vector used to deploy Krasue is currently not known,
although it's suspected that it could be via vulnerability exploitation,
credential brute-force attacks, or downloaded as part of a bogus software
package or binary. The scale of the campaign is
The malware's core functionalities are realized through a rootkit that allows it
to maintain persistence on the host without attracting any attention. The
rootkit is derived from open-source projects such as Diamorphine, Suterusu, and
Rooty.
This has raised the possibility that Krasue is either deployed as part of a
botnet or sold by initial access brokers to other cybercriminals, such as
ransomware affiliates, who are looking to obtain access to a specific target.
"The rootkit can hook the `kill()` syscall, network-related functions, and file
listing operations in order to hide its activities and evade detection,"
Group-IB malware analyst Sharmine Low said.

"Notably, Krasue uses RTSP (Real Time Streaming Protocol) messages to serve as a
disguised 'alive ping,' a tactic rarely seen in the wild."
The trojan's command-and-control (C2) communications further allow it to
designate a communicating IP as its master upstream C2 server, get information
about the malware, and even terminate itself.
Krasue also shares several source code similarities with another Linux malware
named XorDdos, indicating that it has been developed by the same author as the
latter, or by actors who had access to its source code.
"The information available is not enough to put forward a conclusive attribution
as to the creator of Krasue, or the groups that are leveraging it in the wild,
but the fact that these malicious programs are able to remain under the radar
for extended periods makes it clear that continuous vigilance and better
security measures are necessary," Low said.
Agent Racoon Backdoor Targets Organizations in Middle East, Africa, and U.S.
2.12.23
Virus
The Hacker News
Organizations in the Middle East, Africa, and the U.S.
have been targeted by an unknown threat actor to distribute a new backdoor
called Agent Racoon.
"This malware family is written using the .NET framework and leverages the
domain name service (DNS) protocol to create a covert channel and provide
different backdoor functionalities," Palo Alto Networks Unit 42 researcher Chema
Garcia said in a Friday analysis.
Targets of the attacks span various sectors such as education, real estate,
retail, non-profits, telecom, and governments. The activity has not been
attributed to a known threat actor, although it's assessed to be a nation-state
aligned owing to the victimology pattern and the detection and defense evasion
techniques used.
The cybersecurity firm is tracking the cluster under the moniker CL-STA-0002.
It's currently not clear how these organizations were breached, and when the
attacks took place.
Some of the other tools deployed by the adversary include a customized version
of Mimikatz called Mimilite as well as a new utility called Ntospy, which
utilizes a custom DLL module implementing a network provider to steal
credentials to a remote server.
"While the attackers commonly used Ntospy across the affected organizations, the
Mimilite tool and the Agent Racoon malware have only been found in nonprofit and
government-related organizations' environments," Garcia explained.

It's worth pointing out a previously identified threat activity cluster known as
CL-STA-0043 has also been linked to the use of Ntospy, with the adversary also
targeting two organizations that have been targeted by CL-STA-0002.
Agent Raccoon, executed by means of scheduled tasks, allows for command
execution, file uploading, and file downloading, while disguising itself as
Google Update and Microsoft OneDrive Updater binaries.
The command-and-control (C2) infrastructure used in connection with the implant
dates back to at least August 2020. An examination of VirusTotal submissions of
the Agent Racoon artifacts shows that the earliest sample was uploaded in July
2022.
Unit 42 said it also uncovered evidence of successful data exfiltration from
Microsoft Exchange Server environments, resulting in the theft of emails
matching different search criteria. The threat actor has also been found to
harvest victims' Roaming Profile.
"This tool set is not yet associated with a specific threat actor, and not
entirely limited to a single cluster or campaign," Garcia said.
Russian Hacker Vladimir Dunaev Convicted for Creating TrickBot Malware
2.12.23
Virus
The Hacker News
A Russian national has been found guilty in connection
with his role in developing and deploying a malware known as TrickBot, the U.S.
Department of Justice (DoJ) announced.
Vladimir Dunaev, 40, was arrested in South Korea in September 2021 and
extradited to the U.S. a month later.
"Dunaev developed browser modifications and malicious tools that aided in
credential harvesting and data mining from infected computers, facilitated and
enhanced the remote access used by TrickBot actors, and created a program code
to prevent the TrickBot malware from being detected by legitimate security
software," the DoJ said.
"During Dunaev's participation in the scheme, 10 victims in the Northern
District of Ohio, including Avon schools and a North Canton real-estate company,
were defrauded of more than $3.4 million via ransomware deployed by TrickBot."
Dunaev, who pleaded guilty to committing computer fraud and identity theft and
conspiracy to commit wire fraud and bank fraud, faces a maximum of 35 years in
prison. He is scheduled to be sentenced on March 20, 2024.
Dunaev is also the second TrickBot gang malware developer to be arrested after
Alla Witte, a Latvian national who, was sentenced to two years and eight months
in prison in June 2023.
The development came nearly three months after the U.K. and U.S. governments
sanctioned 11 individuals suspected of being part of the TrickBot cybercrime
group.
TrickBot, which started off as a banking trojan in 2016, evolved into a
multi-purpose tool capable of delivering additional payloads to infected hosts
and acting as an initial access facilitator for ransomware attacks.
After surviving law enforcement to dismantle the botnet, the infamous Conti
ransomware crew gained control over the operation. However, both Conti and
TrickBot suffered a major blow last year following Russia's invasion of Ukraine,
when Conti pledged allegiance to Russia.
This led to a series of leaks dubbed ContiLeaks and TrickLeaks that gave away
valuable information about their internal chats and infrastructure, ultimately
resulting in the shut down of Conti and its disintegration into numerous other
groups.
Qakbot Takedown Aftermath: Mitigations and Protecting Against Future Threats
1.12.23
Virus
The Hacker News
The U.S. Department of Justice (DOJ) and the FBI recently
collaborated in a multinational operation to dismantle the notorious Qakbot
malware and botnet. While the operation was successful in disrupting this
long-running threat, concerns have arisen as it appears that Qakbot may still
pose a danger in a reduced form. This article discusses the aftermath of the
takedown, provides mitigation strategies, and offers guidance on determining
past infections.
The Takedown and Its Limitations#
During the takedown operation, law
enforcement secured court orders to remove Qakbot malware from infected devices
remotely. It was discovered that the malware had infected a substantial number
of devices, with 700,000 machines globally, including 200,000 computers in the
U.S., being compromised at the time of the takedown. However, recent reports
suggest that Qakbot is still active but in a diminished state.
The absence of arrests during the takedown operation indicates that only the
command-and-control (C2) servers were affected, leaving the spam delivery
infrastructure untouched. Therefore, the threat actors behind Qakbot continue to
operate, presenting an ongoing threat.
Mitigations for Future Protection#
To safeguard against potential Qakbot
resurgence or similar threats, the FBI, and the Cybersecurity & Infrastructure
Security Agency (CISA) recommend several key mitigations:
Require Multi-Factor Authentication (MFA): Implement MFA for remote access to
internal networks, particularly in critical infrastructure sectors like
healthcare. MFA is highly effective in preventing automated cyberattacks.
Regularly Conduct Employee Security Training: Educate employees about security
best practices, including avoiding clicking on suspicious links. Encourage
practices like verifying the source of links and typing website names directly
into browsers.
Update Corporate Software: Keep operating systems,
applications, and firmware up to date. Use centralized patch management systems
to ensure timely updates and assess the risk for each network asset.
Eliminate Weak Passwords: Comply with NIST guidelines for employee password
policies and prioritize MFA over password reliance wherever possible.
Filter
Network Traffic: Block ingoing and outgoing communications with known malicious
IP addresses by implementing block/allow lists.
Develop a Recovery Plan:
Prepare and maintain a recovery plan to guide security teams in the event of a
breach.
Follow the "3-2-1" Backup Rule: Maintain at least three copies of
critical data, with two stored in separate locations and one stored off-site.
Checking for Past Infections#
For individuals concerned about past Qakbot
infections, there is some good news. The DOJ has recovered over 6.5 million
stolen passwords and credentials from Qakbot's operators. To check if your login
information has been exposed, you can use the following resources:
Have I Been Pwned: This widely known site allows you to check if your email
address has been compromised in data breaches. It now includes the Qakbot
dataset in its database.
Check Your Hack: Created by the Dutch National
Police using Qakbot's seized data, this site lets you enter your email address
and provides an automatic email notification if your address is found in the
dataset.
World's Worst Passwords List: Since Qakbot utilizes a list of common
passwords for brute-force attacks, you can check this list to ensure your
password is not among the worst.
Conclusion#
While the takedown of Qakbot
was a significant achievement, the threat landscape remains complex. There is a
possibility of Qakbot's resurgence, given its operators' adaptability and
resources. Staying vigilant and implementing security measures is crucial to
prevent future infections. BlackBerry's CylanceENDPOINT solution is recommended
to protect against Qakbot's execution, and specific rules within CylanceOPTICS
can enhance protection against threats like Qakbot.
Chinese Hackers Using SugarGh0st RAT to Target South Korea and Uzbekistan
1.12.23
Virus
The Hacker News

A suspected Chinese-speaking threat actor has been attributed to a malicious
campaign that targets the Uzbekistan Ministry of Foreign Affairs and South
Korean users with a remote access trojan called SugarGh0st RAT.
The activity, which commenced no later than August 2023, leverages two different
infection sequences to deliver the malware, which is a customized variant of
Gh0st RAT (aka Farfli).
It comes with features to "facilitate the remote administration tasks as
directed by the C2 and modified communication protocol based on the similarity
of the command structure and the strings used in the code," Cisco Talos
researchers Ashley Shen and Chetan Raghuprasad said.
The attacks commence with a phishing email bearing decoy documents, opening
which activates a multi-stage process that leads to the deployment of SugarGh0st
RAT.
The decoy documents are incorporated within a heavily obfuscated JavaScript
dropper that's contained within a Windows Shortcut file embedded in the RAR
archive email attachment.
"The JavaScript decodes and drops the embedded files into the %TEMP% folder,
including a batch script, a customized DLL loader, an encrypted SugarGh0st
payload, and a decoy document," the researchers said.
The decoy document is then displayed to the victim, while, in the background,
the batch script runs the DLL loader, which, in turn, side-loads it with a
copied version of a legitimate Windows executable called rundll32.exe to decrypt
and launch the SugarGh0st payload.
A second variant of the attack also begins with a RAR archive containing a
malicious Windows Shortcut file that masquerades as a lure, with the difference
being that the JavaScript leverages DynamicWrapperX to run shellcode that
launches SugarGh0st.
SugarGh0st, a 32-bit dynamic-link library (DLL) written in C++, establishes
contact with a hard-coded command-and-control (C2) domain, allowing it to
transmit system metadata to the server, launch a reverse shell, and run
arbitrary commands.
It can also enumerate and terminate processes, take screenshots, perform file
operations, and even clear the machine's event logs in an attempt to cover its
tracks and evade detection.
The campaign's links to China stem from Gh0st RAT's Chinese origins and the fact
that the fully functional backdoor has been widely adopted by Chinese threat
actors over the years, in part driven by the release of its source code in 2008.
Another smoking gun evidence is the use of Chinese names in the "last modified
by" field in the metadata of the decoy files.
"The Gh0st RAT malware is a mainstay in the Chinese threat actors' arsenal and
has been active since at least 2008," the researchers said.
"Chinese actors also have a history of targeting Uzbekistan. The targeting of
the Uzbekistan Ministry of Foreign Affairs also aligns with the scope of Chinese
intelligence activity abroad."
The development comes as Chinese state-sponsored groups have also increasingly
targeted Taiwan in the last six months, with the attackers repurposing
residential routers to mask their intrusions, according to Google.
Konni Group Using Russian-Language Malicious Word Docs in Latest Attacks
24.11.23
Virus
The Hacker News
A new phishing attack has been observed leveraging a
Russian-language Microsoft Word document to deliver malware capable of
harvesting sensitive information from compromised Windows hosts.
The activity has been attributed to a threat actor called Konni, which is
assessed to share overlaps with a North Korean cluster tracked as Kimsuky (aka
APT43).
"This campaign relies on a remote access trojan (RAT) capable of extracting
information and executing commands on compromised devices," Fortinet FortiGuard
Labs researcher Cara Lin said in an analysis published this week.
The cyber espionage group is notable for its targeting of Russia, with the modus
operandi involving the use of spear-phishing emails and malicious documents as
entry points for their attacks.
Recent attacks documented by Knowsec and ThreatMon have leveraged the WinRAR
vulnerability (CVE-2023-38831) as well as obfuscated Visual Basic scripts to
drop Konni RAT and a Windows Batch script capable of collecting data from the
infected machines.
"Konni's primary objectives include data exfiltration and conducting espionage
activities," ThreatMon said. "To achieve these goals, the group employs a wide
array of malware and tools, frequently adapting their tactics to avoid detection
and attribution."
The latest attack sequence observed by Fortinet involves a macro-laced Word
document that, when enabled, displays an article in Russian that's purportedly
about "Western Assessments of the Progress of the Special Military Operation."
The Visual Basic for Application (VBA) macro subsequently proceeds to launch an
interim Batch script that performs system checks, User Account Control (UAC)
bypass, and ultimately paves the way for the deployment of a DLL file that
incorporates information gathering and exfiltration capabilities.
"The payload incorporates a UAC bypass and encrypted communication with a C2
server, enabling the threat actor to execute privileged commands," Lin said.
Konni is far from the only North Korean threat actor to single out Russia.
Evidence gathered by Kaspersky, Microsoft, and SentinelOne shows that the
adversarial collective referred to as ScarCruft (aka APT37) has also targeted
trading companies and missile engineering firms located in the country.
The disclosure also arrives less than two weeks after Solar, the cybersecurity
arm of Russian state-owned telecom company Rostelecom, revealed that threat
actors from Asia – primarily those from China and North Korea – accounted for a
majority of attacks against the country's infrastructure.
"The North Korean Lazarus group is also very active on the territory of the
Russian Federation," the company said. "As of early November, Lazarus hackers
still have access to a number of Russian systems."
Alert: New WailingCrab Malware Loader Spreading via Shipping-Themed Emails
24.11.23
Virus
The Hacker News
Delivery- and shipping-themed email messages are being
used to deliver a sophisticated malware loader known as WailingCrab.
"The malware itself is split into multiple components, including a loader,
injector, downloader and backdoor, and successful requests to C2-controlled
servers are often necessary to retrieve the next stage," IBM X-Force researchers
Charlotte Hammond, Ole Villadsen, and Kat Metrick said.
WailingCrab, also called WikiLoader, was first documented by Proofpoint in
August 2023, detailing campaigns targeting Italian organizations that used the
malware to ultimately deploy the Ursnif (aka Gozi) trojan. It was spotted in the
wild in late December 2022.
The malware is the handiwork of a threat actor known as TA544, which is also
tracked as Bamboo Spider and Zeus Panda. IBM X-Force has named the cluster
Hive0133.
Actively maintained by its operators, the malware has been observed
incorporating features that prioritize stealth and allows it to resist analysis
efforts. To further lower the chances of detection, legitimate, hacked websites
are used for initial command-and-control (C2) communications.
What's more, components of the malware are stored on well-known platforms such
as Discord. Another noteworthy change to the malware since mid-2023 is the use
of MQTT, a lightweight messaging protocol for small sensors and mobile devices,
for C2.
The protocol is something of a rarity in the threat landscape, with it put to
use only in a few instances, as observed in the case of Tizi and MQsTTang in the
past.
The attack chains commence with emails bearing PDF attachments containing URLs
that, when clicked, download a JavaScript file designed to retrieve and launch
the WailingCrab loader hosted on Discord.
The loader is responsible for launching the next-stage shellcode, an injector
module that, in turn, kick-starts the execution of a downloader to deploy the
backdoor ultimately.
"In prior versions, this component would download the backdoor, which would be
hosted as an attachment on the Discord CDN," the researchers said.
"However, the latest version of WailingCrab already contains the backdoor
component encrypted with AES, and it instead reaches out to its C2 to download a
decryption key to decrypt the backdoor."
The backdoor, which acts as the malware's core, is designed to establish
persistence on the infected host and contact the C2 server using the MQTT
protocol to receive additional payloads.
On top of that, newer variants of the backdoor eschew a Discord-based download
path in favor of a shellcode-based payload directly from the C2 via MQTT.
"The move to using the MQTT protocol by WailingCrab represents a focused effort
on stealth and detection evasion," the researchers concluded. "The newer
variants of WailingCrab also remove the callouts to Discord for retrieving
payloads, further increasing its stealthiness."
"Discord has become an increasingly common choice for threat actors looking to
host malware, and as such it is likely that file downloads from the domain will
start coming under higher levels of scrutiny. Therefore, it is not surprising
that the developers of WailingCrab decided on an alternative approach."
The abuse of Discord's content delivery network (CDN) for distributing malware
hasn't gone unnoticed by the social media company, which told Bleeping Computer
earlier this month that it will switch to temporary file links by the end of the
year.
New Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
22.11.23
Virus
The Hacker News
A new variant of the Agent Tesla malware has been
observed delivered via a lure file with the ZPAQ compression format to harvest
data from several email clients and nearly 40 web browsers.
"ZPAQ is a file compression format that offers a better compression ratio and
journaling function compared to widely used formats like ZIP and RAR," G Data
malware analyst Anna Lvova said in a Monday analysis.
"That means that ZPAQ archives can be smaller, saving storage space and
bandwidth when transferring files. However, ZPAQ has the biggest disadvantage:
limited software support."
First appearing in 2014, Agent Tesla is a keylogger and remote access trojan
(RAT) written in .NET that's offered to other threat actors as part of a
malware-as-a-service (MaaS) model.
It's often used as a first-stage payload, providing remote access to a
compromised system and utilized to download more sophisticated second-stage
tools such as ransomware.
Agent Tesla is typically delivered via phishing emails, with recent campaigns
leveraging a six-year-old memory corruption vulnerability in Microsoft Office's
Equation Editor (CVE-2017-11882).

The latest attack chain begins with an email containing a ZPAQ file attachment
that purports to be a PDF document, opening which extracts a bloated .NET
executable that's mostly padded with zero bytes to artificially inflate the
sample size to 1 GB in an effort to bypass traditional security measures.
"The main function of the unarchived .NET executable is to download a file with
.wav extension and decrypt it," Lvova explained. "Using commonly used file
extensions disguises the traffic as normal, making it more difficult for network
security solutions to detect and prevent malicious activity."
The end goal of the attack is to infect the endpoint with Agent Teslathat's
obfuscated with .NET Reactor, a legitimate code protection software.
Command-and-control (C2) communications is accomplished via Telegram.
The development is a sign that threat actors are experimenting with uncommon
file formats for malware delivery, necessitating that users be on the lookout
for suspicious emails and keep their systems up-to-date.
"The usage of the ZPAQ compression format raises more questions than answers,"
Lvova said. "The assumptions here are that either threat actors target a
specific group of people who have technical knowledge or use less widely known
archive tools, or they are testing other techniques to spread malware faster and
bypass security software."
Kinsing Hackers Exploit Apache ActiveMQ Vulnerability to Deploy Linux Rootkits
22.11.23
Virus
The Hacker News
The Kinsing threat actors are actively exploiting a
critical security flaw in vulnerable Apache ActiveMQ servers to infect Linux
systems with cryptocurrency miners and rootkits.
"Once Kinsing infects a system, it deploys a cryptocurrency mining script that
exploits the host's resources to mine cryptocurrencies like Bitcoin, resulting
in significant damage to the infrastructure and a negative impact on system
performance," Trend Micro security researcher Peter Girnus said.
Kinsing refers to a Linux malware with a history of targeting misconfigured
containerized environments for cryptocurrency mining, often utilizing
compromised server resources to generate illicit profits for the threat actors.
The group is also known to quickly adapt its tactics to include newly disclosed
flaws in web applications to breach target networks and deliver crypto miners.
Earlier this month, Aqua disclosed the threat actor's attempts to exploit a
Linux privilege escalation flaw called Looney Tunables to infiltrate cloud
environments.

The latest campaign entails the abuse of CVE-2023-46604 (CVSS score: 10.0), an
actively exploited critical vulnerability in Apache ActiveMQ that enables remote
code execution, permitting the adversary to download and install the Kinsing
malware.
This is followed by retrieving additional payloads from an actor-controlled
domain while simultaneously taking steps to terminate competing cryptocurrency
miners already running on the infected system.
"Kinsing doubles down on its persistence and compromise by loading its rootkit
in /etc/ld.so.preload, which completes a full system compromise," Girnus said.
In light of the continued exploitation of the flaw, organizations running
affected versions of Apache ActiveMQ are recommended to update to a patched
version as soon as possible to mitigate potential threats.
The disclosure comes as the AhnLab Security Emergency response Center (ASEC) is
warning of cyber attacks targeting vulnerable Apache web servers for a
cryptojacking campaign that leverages Cobalt Strike or Gh0st RAT to deliver a
cryptocurrency miner.
NetSupport RAT Infections on the Rise - Targeting Government and Business
Sectors
21.11.23
Virus
The Hacker News
Threat actors are targeting the education, government and
business services sectors with a remote access trojan called NetSupport RAT.
"The delivery mechanisms for the NetSupport RAT encompass fraudulent updates,
drive-by downloads, utilization of malware loaders (such as GHOSTPULSE), and
various forms of phishing campaigns," VMware Carbon Black researchers said in a
report shared with The Hacker News.
The cybersecurity firm said it detected no less than 15 new infections related
to NetSupport RAT in the last few weeks.
While NetSupport Manager started off as a legitimate remote administration tool
for technical assistance and support, malicious actors have misappropriated the
tool to their own advantage, using it as a beachhead for subsequent attacks.
NetSupport RAT is typically downloaded onto a victim's computer via deceptive
websites and fake browser updates.
In August 2022, Sucuri detailed a campaign in which compromised WordPress sites
were being used to display fraudulent Cloudflare DDoS protection pages that led
to the distribution of NetSupport RAT.

The use of bogus web browser updates is a tactic often associated with the
deployment of a JavaScript-based downloader malware known as SocGholish (aka
FakeUpdates), which has also been observed propagating a loader malware
codenamed BLISTER.
The Javascript payload subsequently invokes PowerShell to connect to a remote
server and retrieve a ZIP archive file containing NetSupport RAT that, upon
installation, beacons out to a command-and-control (C2) server.
"Once installed on a victim's device, NetSupport is able to monitor behavior,
transfer files, manipulate computer settings, and move to other devices within
the network," the researchers said.
DarkGate and PikaBot Malware Resurrect QakBot's Tactics in New Phishing Attacks
21.11.23
Virus
The Hacker News
Phishing campaigns delivering malware families such as
DarkGate and PikaBot are following the same tactics previously used in attacks
leveraging the now-defunct QakBot trojan.
"These include hijacked email threads as the initial infection, URLs with unique
patterns that limit user access, and an infection chain nearly identical to what
we have seen with QakBot delivery," Cofense said in a report shared with The
Hacker News.
"The malware families used also follow suit to what we would expect QakBot
affiliates to use."
QakBot, also called QBot and Pinkslipbot, was shut down as part of a coordinated
law enforcement effort codenamed Operation Duck Hunt earlier this August.
The use of DarkGate and PikaBot in these campaigns is not surprising as they can
both act as conduits to deliver additional payloads to compromised hosts, making
them both an attractive option for cybercriminals.
PikaBot's parallels to QakBot were previously highlighted by Zscaler in its
analysis of the malware in May 2023, noting similarities in the "distribution
methods, campaigns, and malware behaviors."

DarkGate, for its part, incorporates advanced techniques to evade detection by
antivirus systems, alongside capabilities to log keystrokes, execute PowerShell,
and implement a reverse shell that allows its operators to commandeer an
infected host remotely.
"The connection is bidirectional, meaning the attackers can send commands and
receive responses in real-time, enabling them to navigate the victim's system,
exfiltrate data, or perform other malicious actions," Sekoia said in a new
technical report of the malware.
Cofense's analysis of the high-volume phishing campaign shows that it targets a
wide range of sectors, with the attack chains propagating a booby-trapped URL
pointing to a ZIP archive in hijacked email threads.
The ZIP archive contains a JavaScript dropper that, in turn, contacts a second
URL to download and run either the DarkGate or PikaBot malware.
A noteworthy variant of the attacks has been observed taking advantage of Excel
add-in (XLL) files in lieu of JavaScript droppers to deliver the final payloads.
"A successful DarkGate or PikaBot infection could lead to the delivery of
advanced crypto mining software, reconnaissance tools, ransomware, or any other
malicious file the threat actors wish to install on a victim's machine," Cofense
said.
LummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique
20.11.23
Virus
The Hacker News
The stealer malware known as LummaC2 (aka Lumma Stealer)
now features a new anti-sandbox technique that leverages the mathematical
principle of trigonometry to evade detection and exfiltrate valuable information
from infected hosts.
The method is designed to "delay detonation of the sample until human mouse
activity is detected," Outpost24 security researcher Alberto Marín said in a
technical report shared with The Hacker News.
Written in the C programming language, LummaC2 has been sold in underground
forums since December 2022. The malware has since received iterative updates
that make it harder to analyze via control flow flattening and even allow it to
deliver additional payloads.
The current version of LummaC2 (v4.0) also requires its customers to use a
crypter as an added concealing mechanism, not to mention prevent it from being
leaked in its raw form.
Another noteworthy update is the reliance on trigonometry to detect human
behavior on the infiltrated endpoint.
"This technique takes into consideration different positions of the cursor in a
short interval to detect human activity, effectively preventing detonation in
most analysis systems that do not emulate mouse movements realistically," Marín
said.
To do so, it extracts the current cursor position for five times after a
predefined interval of 300 milliseconds, and checks if every captured position
is different from its preceding one. The process is repeated indefinitely until
all consecutive cursor positions differ.
Once all the five cursor positions (P0, P1, P2, P3, and P4) meet the
requirements, LummaC2 treats them as Euclidean vectors and calculates the angle
that's formed between two consecutive vectors (P01-P12, P12-P23, and P23-P34).
"If all the calculated angles are lower than 45º, then LummaC2 v4.0 considers it
has detected 'human' mouse behavior and continues with its execution," Marín
said.
"However, if any of the calculated angles is bigger than 45º, the malware will
start the process all over again by ensuring there is mouse movement in a
300-millisecond period and capturing again 5 new cursor positions to process."
The development comes amid the emergence of new strains of information stealers
and remote access trojans such as BbyStealer, Trap Stealer, Predator AI, and
Sayler RAT that are designed to extract a wide range of sensitive data from
compromised systems.
Predator AI, an actively maintained project, is also notable for the fact that
it can be used to attack many popular cloud services such as AWS, PayPal,
Razorpay, and Twilio, in addition to incorporating a ChatGPT API to "make the
tool easier to use," SentinelOne noted earlier this month.
"The malware-as-a-service (MaaS) model, and its readily available scheme,
remains to be the preferred method for emerging threat actors to carry out
complex and lucrative cyberattacks," Marín said.
"Information theft is a significant focus within the realm of MaaS, [and]
represents a considerable threat that can lead to substantial financial losses
for both organizations and individuals."
8Base Group Deploying New Phobos Ransomware Variant via SmokeLoader
18.11.23
Virus
The Hacker News
The threat actors behind the 8Base ransomware are
leveraging a variant of the Phobos ransomware to conduct their financially
motivated attacks.
The findings come from Cisco Talos, which has recorded an increase in activity
carried out by cybercriminals.
"Most of the group's Phobos variants are distributed by SmokeLoader, a backdoor
trojan," security researcher Guilherme Venere said in an exhaustive two-part
analysis published Friday.
"This commodity loader typically drops or downloads additional payloads when
deployed. In 8Base campaigns, however, it has the ransomware component embedded
in its encrypted payloads, which is then decrypted and loaded into the
SmokeLoader process' memory."
8Base came into sharp focus in mid-2023, when a similar spike in activity was
observed by the cybersecurity community. It's said to be active at least since
March 2022.
A previous analysis from VMware Carbon Black in June 2023 identified parallels
between 8Base and RansomHouse, in addition to discovering a Phobos ransomware
sample that was found using the ".8base" file extension for encrypted files.
This raised the likelihood that 8Base is either a successor to Phobos or that
the threat actors behind the operation are merely using already existing
ransomware strains to conduct their attacks, akin to the Vice Society ransomware
group.
The latest findings from Cisco Talos show that SmokeLoader is used as a
launchpad to execute the Phobos payload, which then carries out steps to
establish persistence, terminate processes that may keep the target files open,
disable system recovery, and delete backups as well as shadow copies.
Another notable characteristic is the full encryption of files that are below
1.5 MB and partial encryption of files above the threshold to speed up the
encryption process.
Furthermore, the artifact incorporates a configuration with over 70 options
that's encrypted using a hard-coded key. The configuration unlocks additional
features such as User Account Control (UAC) bypass and reporting of a victim
infection to an external URL.
There is also a hard-coded RSA key used to protect the per-file AES key used in
the encryption, which Talos said could help enable decryption of files locked by
the ransomware.
"Once each file is encrypted, the key used in the encryption along with
additional metadata is then encrypted using RSA-1024 with a hard-coded public
key, and saved to the end of the file," Venere elaborated.
"It implies, however, that once the private RSA key is known, any file encrypted
by any Phobos variant since 2019 can reliably be decrypted."

Phobos, which first emerged in 2019, is an evolution of the Dharma (aka Crysis)
ransomware, with the ransomware predominantly manifesting as the variants Eking,
Eight, Elbie, Devos, and Faust, based on the volume of artifacts unearthed on
VirusTotal.
"The samples all contained the same source code and were configured to avoid
encrypting files that other Phobos affiliated already locked, but the
configuration changed slightly depending on the variant being deployed," Venere
said. "This is based on a file extension block list in the ransomware's
configuration settings."
Cisco Talos assesses that Phobos is closely managed by a central authority,
while being sold as a ransomware-as-a-service (RaaS) to other affiliates based
on the same RSA public key, the variations in the contact emails, and regular
updates to the ransomware's extension block lists.
"The extension blocklists appear to tell a story of which groups used that same
base sample over time," Venere said.
"The extension block lists found in the many Phobos samples [...] are
continually updated with new files that have been locked in previous Phobos
campaigns. This may support the idea that there is a central authority behind
the builder who keeps track of who used Phobos in the past. The intent could be
to prevent Phobos affiliates from interfering with one another's operations."
The development comes as FalconFeeds disclosed that a threat actor is
advertising a sophisticated ransomware product called UBUD that's developed in C
and features "strong anti-detection measures against virtual machines and
debugging tools."
It also follows a formal complaint filed by the BlackCat ransomware group with
the U.S. Securities and Exchange Commission (SEC), alleging that one of its
victims, MeridianLink, failed to comply with new disclosure regulations that
require impacted companies to report the incident within four business days,
DataBreaches.net reported.
The financial software company has since confirmed it was targeted in a cyber
attack on November 10, but noted it found no evidence of unauthorized access to
its systems.
While the SEC disclosure rules don't take effect until next month on December
18, the unusual pressure tactic is a sign that threat actors are closely
watching the space and are willing to bend government regulations to their
advantage and compel victims to pay up.
That said, it's worth noting that the enforcement exclusively applies in
situations where the companies have identified that the attacks have had a
"material" impact on their bottom lines.
Another prolific ransomware gang LockBit, in the meanwhile, has instituted new
negotiation rules starting October 2023, citing less-than-expected settlements
and larger discounts offered to victims due to the "different levels of
experience of affiliates."
"Establish a minimum ransom request depending on the company's yearly revenue,
for example at 3%, and prohibit discounts of more than 50%," the LockBit
operators said, according to a detailed report from Analyst1.
"Thus, if the company's revenue is $100 million USD, the initial ransom request
should start from $3 million USD with the final payout must be no less than $1.5
million USD."
Russian Cyber Espionage Group Deploys LitterDrifter USB Worm in Targeted Attacks
18.11.23
Virus
The Hacker News
Russian cyber espionage actors affiliated with the
Federal Security Service (FSB) have been observed using a USB propagating worm
called LitterDrifter in attacks targeting Ukrainian entities.
Check Point, which detailed Gamaredon's (aka Aqua Blizzard, Iron Tilden,
Primitive Bear, Shuckworm, and Winterflounder) latest tactics, branded the group
as engaging in large-scale campaigns that are followed by "data collection
efforts aimed at specific targets, whose selection is likely motivated by
espionage goals."
The LitterDrifter worm packs in two main features: automatically spreading the
malware via connected USB drives as well as communicating with the threat
actor's command-and-control (C&C) servers. It's also suspected to be an
evolution of a PowerShell-based USB worm that was previously disclosed by
Symantec in June 2023.
Written in VBS, the spreader module is responsible for distributing the worm as
a hidden file in a USB drive together with a decoy LNK that's assigned random
names. The malware gets its name LitterDrifter owing to the fact that the
initial orchestration component is named "trash.dll."
"Gamaredon's approach towards the C&C is rather unique, as it utilizes domains
as a placeholder for the circulating IP addresses actually used as C2 servers,"
Check Point explained.
LitterDrifter is also capable of connecting to a C&C server extracted from a
Telegram channel, a tactic it has repeatedly put to use since at least the start
of the year.
The cybersecurity firm said it also detected signs of possible infection outside
of Ukraine based on VirusTotal submissions from the U.S., Vietnam, Chile,
Poland, Germany, and Hong Kong.

Gamaredon has had an active presence this year, while continuously evolving its
attack methods. In July 2023, the adversary's rapid data exfiltration
capabilities came to light, what with the threat actor transmitting sensitive
information within an hour of the initial compromise.
"It's clear that LitterDrifter was designed to support a large-scale collection
operation," the company concluded. "It leverages simple, yet effective
techniques to ensure it can reach the widest possible set of targets in the
region."
The development comes as Ukraine's National Cybersecurity Coordination Center
(NCSCC) revealed attacks orchestrated by Russian state-sponsored hackers
targeting embassies across Europe, including Italy, Greece, Romania, and
Azerbaijan.
The intrusions, attributed to APT29 (aka BlueBravo, Cloaked Ursa, Cozy Bear,
Iron Hemlock, Midnight Blizzard, and The Dukes), involve the exploitation of the
recently disclosed WinRAR vulnerability (CVE-2023-38831) via benign-looking
lures that claim to offer BMWs for sale, a theme it has employed in the past.
The attack chain commences with sending victims phishing emails containing a
link to a specially crafted ZIP file that, when launched, exploits the flaw to
retrieve a PowerShell script from a remote server hosted on Ngrok.
"A concerning trend of exploiting CVE-2023-38831 vulnerability by Russian
intelligence services hacking groups demonstrates its growing popularity and
sophistication," NCSCC said.
Earlier this week, the Computer Emergency Response Team of Ukraine (CERT-UA)
unearthed a phishing campaign that propagates malicious RAR archives that
masquerades as a PDF document from the Security Service of Ukraine (SBU) but, in
reality, is an executable that leads to the deployment of Remcos RAT.
CERT-UA is tracking the activity under the moniker UAC-0050, which was also
linked to another spate of cyber attacks aimed at state authorities in the
country to deliver Remcos RAT in February 2023.
Beware: Malicious Google Ads Trick WinSCP Users into Installing Malware
17.11.23
Virus
The Hacker News

Threat actors are leveraging manipulated search results and bogus Google ads
that trick users who are looking to download legitimate software such as WinSCP
into installing malware instead.
Cybersecurity company Securonix is tracking the ongoing activity under the name
SEO#LURKER.
"The malicious advertisement directs the user to a compromised WordPress website
gameeweb[.]com, which redirects the user to an attacker-controlled phishing
site," security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a
report shared with The Hacker News.
The threat actors are believed to leverage Google's Dynamic Search Ads (DSAs),
which automatically generates ads based on a site's content to serve the
malicious ads that take the victims to the infected site.
The ultimate goal of the complex multi-stage attack chain is to entice users
into clicking on the fake, lookalike WinSCP website, winccp[.]net, and download
the malware.
"Traffic from the gaweeweb[.]com website to the fake winsccp[.]net website
relies on a correct referrer header being set properly," the researchers said.
"If the referrer is incorrect, the user is 'Rickrolled' and is sent to the
infamous Rick Astley YouTube video."
The final payload takes the form of a ZIP file ("WinSCP_v.6.1.zip") that comes
with a setup executable, which, when launched, employs DLL side-loading to load
and execute a DLL file named python311.dll that's present within the archive.

The DLL, for its part, downloads and executes a legitimate WinSCP installer to
keep up the ruse, while stealthily dropping Python scripts ("slv.py" and
"wo15.py") in the background to activate the malicious behavior. It's also
responsible for setting up persistence.
Both the Python scripts are designed to establish contact with a remote
actor-controlled server to receive further instructions that allow the attackers
to run enumeration commands on the host.
"Given the fact that the attackers were leveraging Google Ads to disperse
malware, it can be believed that the targets are limited to anyone seeking
WinSCP software," the researchers said.
"The geoblocking used on the site hosting the malware suggests that those in the
U.S. are victims of this attack."
This is not the first time Google's Dynamic Search Ads have been abused to
distribute malware. Late last month, Malwarebytes lifted the lid on a campaign
that targets users searching for PyCharm with links to a hacked website hosting
a rogue installer that paves the way for the deployment of information-stealing
malware.
Malvertising has grown in popularity among cybercriminals in the past few years,
with numerous malware campaigns using the tactic for attacks in recent months.
Earlier this week, Malwarebytes revealed an uptick in credit card skimming
campaigns in October 2023 that's estimated to have compromised hundreds of
e-commerce websites with an aim to steal financial information by injecting
convincing counterfeit payment pages.
27 Malicious PyPI Packages with Thousands of Downloads Found Targeting IT
Experts
17.11.23
Virus
The Hacker News
An unknown threat actor has been observed publishing
typosquat packages to the Python Package Index (PyPI) repository for nearly six
months with an aim to deliver malware capable of gaining persistence, stealing
sensitive data, and accessing cryptocurrency wallets for financial gain.
The 27 packages, which masqueraded as popular legitimate Python libraries,
attracted thousands of downloads, Checkmarx said in a new report. A majority of
the downloads originated from the U.S., China, France, Hong Kong, Germany,
Russia, Ireland, Singapore, the U.K., and Japan.
"A defining characteristic of this attack was the utilization of steganography
to hide a malicious payload within an innocent-looking image file, which
increased the stealthiness of the attack," the software supply chain security
firm said.
Some of the packages are pyefflorer, pyminor, pyowler, pystallerer, pystob, and
pywool, the last of which was planted on May 13, 2023.
A common denominator to these packages is the use of the setup.py script to
include references to other malicious packages (i.e., pystob and pywool) that
deploy a Visual Basic Script (VBScript) in order to download and execute a file
named "Runtime.exe" to achieve persistence on the host.
Embedded within the binary is a compiled file that's capable of gathering
information from web browsers, cryptocurrency wallets, and other applications.
An alternate attack chain observed by Checkmarx is said to have hidden the
executable code within a PNG image ("uwu.png"), which is subsequently decoded
and run to extract the public IP address and the universally unique identifier
(UUID) of the affected system.
Pystob and Pywool, in particular, were published under the guise of tools for
API management, only to exfiltrate the data to a Discord webhook and attempt to
maintain persistence by placing the VBS file in the Windows startup folder.
"This campaign serves as another stark reminder of the ever-present threats that
exist in today's digital landscape, particularly in areas where collaboration
and open exchange of code are foundational," Checkmarx said.
The development comes as ReversingLabs uncovered a new wave of protestware npm
packages that "hide scripts broadcasting messages of peace related to the
conflicts in Ukraine and in Israel and the Gaza Strip."

One of the packages, named @snyk/sweater-comb (version 2.1.1), determines the
geographic location of the host, and if it's found to be Russia, displays a
message criticizing the "unjustified invasion" of Ukraine through another module
called "es5-ext."
Another package, e2eakarev, has the description "free palestine protest package"
in the package.json file, and carries out similar checks to see if the IP
address resolves to Israel, and if so, log what's described as a "harmless
protest message" that urges developers to raise awareness about the Palestinian
struggle.
It's not just threat actors infiltrating open-source ecosystems. Earlier this
week, GitGuardian revealed the presence of 3,938 total unique secrets across
2,922 PyPI projects, of which 768 unique secrets were found to be valid.
This includes AWS keys, Azure Active Directory API keys, GitHub OAuth app keys,
Dropbox keys, SSH keys, and credentials associated with MongoDB, MySQL,
PostgreSQL, Coinbase, and Twilio.
What's more, many of these secrets were leaked more than once, spanning multiple
release versions, bringing the total number of occurrences to 56,866.
"Exposing secrets in open-source packages carries significant risks for
developers and users alike," GitGuardian's Tom Forbes said. "Attackers can
exploit this information to gain unauthorized access, impersonate package
maintainers, or manipulate users through social engineering tactics."
The continuous wave of attacks targeting the software supply chain has also
prompted the U.S. government to issue new guidance this month for software
developers and suppliers to maintain and provide awareness about software
security.
"It is recommended that acquisition organizations assign supply chain risk
assessments to their buying decisions given the recent high profile software
supply chain incidents," the Cybersecurity and Infrastructure Security Agency
(CISA), National Security Agency (NSA), and the Office of the Director of
National Intelligence (ODNI) said.
"Software developers and suppliers should improve their software development
processes and reduce the risk of harm to not just employees and shareholders,
but also to their users."
New Campaign Targets Middle East Governments with IronWind Malware
14.11.23
Virus
The Hacker News
Government entities in the Middle East are the target of
new phishing campaigns that are designed to deliver a new initial access
downloader dubbed IronWind.
The activity, detected between July and October 2023, has been attributed by
Proofpoint to a threat actor it tracks under the name TA402, which is also known
as Molerats, Gaza Cyber Gang, and shares tactical overlaps with a pro-Hamas
hacking crew known as APT-C-23 (aka Arid Viper).
"When it comes to state-aligned threat actors, North Korea, Russia, China, and
Iran generally reap the lion's share of attention," Joshua Miller, senior threat
researcher at Proofpoint, said in a statement shared with The Hacker News.
"But TA402, a Middle Eastern advanced persistent threat (APT) group that
historically has operated in the interests of the Palestinian Territories, has
consistently proven to be an intriguing threat actor capable of highly
sophisticated cyber espionage with a focus on intelligence collection."
Coinciding with the use of IronWind are consistent updates to its malware
delivery mechanisms, using Dropbox links, XLL file attachments, and RAR archives
to distribute IronWind.
The use of IronWind is a shift from prior attack chains, which were linked to
the propagation of a backdoor codenamed NimbleMamba in intrusions targeting
Middle Eastern governments and foreign policy think tanks.

TA402's latest campaigns are characterized by the use of a compromised email
account belonging to the Ministry of Foreign Affairs to send phishing lures
pointing to Dropbox links that facilitate the deployment of IronWind.
The downloader is engineered to contact an attacker-controlled server to fetch
additional payloads, including a post-exploitation toolkit called SharpSploit,
following a multi-stage sequence.
Subsequent social engineering campaigns in August and October 2023 have been
found to leverage XLL file and RAR archive attachments embedded in email
messages to trigger the deployment of IronWind. Another notable tactic employed
by the group is the reliance on geofencing techniques to complicate detection
efforts.
"The ongoing conflict in the Middle East does not appear to have hindered their
ongoing operations, as they continue to iterate and use new and clever delivery
methods to bypass detection efforts," Miller said.
"Using complex infection chains and drumming up new malware to attack their
targets, TA402 continues to engage in extremely targeted activity with a strong
focus on government entities based in the Middle East and North Africa."

The development comes as Cisco Talos revealed that cybercriminals have been
observed exploiting the "Release scores" feature of Google Forms quizzes to
deliver email and orchestrate elaborate cryptocurrency scams, highlighting the
creative ways threat actors resort to in order to meet their objectives.
"The emails originate from Google's own servers and consequently may have an
easier time bypassing anti-spam protections and finding the victim's inbox,"
security researcher Jaeson Schultz said last week.
Vietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
14.11.23
Virus
The Hacker News
The Vietnamese threat actors behind the Ducktail stealer
malware have been linked to a new campaign that ran between March and early
October 2023, targeting marketing professionals in India with an aim to hijack
Facebook business accounts.
"An important feature that sets it apart is that, unlike previous campaigns,
which relied on .NET applications, this one used Delphi as the programming
language," Kaspersky said in a report published last week.
Ducktail, alongside Duckport and NodeStealer, is part of a cybercrime ecosystem
operating out of Vietnam, with the attackers primarily using sponsored ads on
Facebook to propagate malicious ads and deploy malware capable of plundering
victims' login cookies and ultimately taking control of their accounts.
Such attacks primarily single out users who may have access to a Facebook
Business account. The fraudsters then use the unauthorized access to place
advertisements for financial gain, perpetuating the infections further.
In the campaign documented by the Russian cybersecurity firm, potential targets
looking for a career change are sent archive files containing a malicious
executable that's disguised with a PDF icon to trick them into launching the
binary.
Doing so results in the malicious file saving a PowerShell script named
param.ps1 and a decoy PDF document locally to the "C:\Users\Public" folder in
Windows.
"The script uses the default PDF viewer on the device to open the decoy, pauses
for five minutes, and then terminates the Chrome browser process," Kaspersky
said.
The parent executable also downloads and launches a rogue library named
libEGL.dll, which scans the "C:\ProgramData\Microsoft\Windows\Start
Menu\Programs" and "C:\ProgramData\Microsoft\Internet Explorer\Quick Launch\User
Pinned\TaskBar\" folders for any shortcut (i.e., LNK file) to a Chromium-based
web browser.

The next stage entails altering the browser's LNK shortcut file by suffixing a
"--load-extension" command line switch to launch a rogue extension that
masquerades as the legitimate Google Docs Offline add-on to fly under the radar.
The extension, for its part, is designed to send information about all open tabs
to an actor-controlled server registered in Vietnam and hijack the Facebook
business accounts.
Google Sues Scammers for Using Bard Lures to Spread Malware#
The findings
underscore a strategic shift in Ducktail's attack techniques and come as Google
filed a lawsuit against three unknown individuals in India and Vietnam for
capitalizing on the public's interest in generative AI tools such as Bard to
spread malware via Facebook and pilfer social media login credentials.
"Defendants distribute links to their malware through social media posts, ads
(i.e., sponsored posts), and pages, each of which purport to offer downloadable
versions of Bard or other Google AI products," the company alleged in its
complaint.
"When a user logged into a social media account clicks the links displayed in
Defendants' ads or on their pages, the links redirect to an external website
from which a RAR archive, a type of file, downloads to the user's computer."
The archive files include an installer file that's capable of installing a
browser extension adept at pilfering victims' social media accounts.
Earlier this May, Meta said it observed threat actors creating deceptive browser
extensions available in official web stores that claim to offer ChatGPT-related
tools and that it detected and blocked over 1,000 unique URLs from being shared
across its services.
New BiBi-Windows Wiper Targets Windows Systems in Pro-Hamas Attacks
13.11.23
Virus
The Hacker News
Cybersecurity researchers have warned about a Windows
version of a wiper malware that was previously observed targeting Linux systems
in cyber attacks aimed at Israel.
Dubbed BiBi-Windows Wiper by BlackBerry, the wiper is the Windows counterpart of
BiBi-Linux Wiper, which has been put to use by a pro-Hamas hacktivist group in
the wake of the Israel-Hamas war last month.
"The Windows variant [...] confirms that the threat actors who created the wiper
are continuing to build out the malware, and indicates an expansion of the
attack to target end user machines and application servers," the Canadian
company said Friday.
Slovak cybersecurity firm is tracking the actor behind the wiper under the name
BiBiGun, noting that the Windows variant (bibi.exe) is designed to overwrite
data in the C:\Users directory recursively with junk data and appends .BiBi to
the filename.
The BiBi-Windows Wiper artifact is said to have been compiled on October 21,
2023, two weeks after the onset of the war. The exact method by which it is
distributed is currently unknown.
Besides corrupting all files with the exception of those with .exe, .dll, and
.sys extensions, the wiper deletes shadow copies from the system, effectively
preventing the victims from recovering their files.
Another notable similarity with its Linux variant is its multithreading
capability.
"For the fastest possible destruction action, the malware runs 12 threads with
eight processor cores," Dmitry Bestuzhev, senior director of cyber threat
intelligence at BlackBerry, said.
It's not immediately clear if the wiper has been deployed in real-world attacks,
and if so, who the targets are.
The development comes as Security Joes, which first documented BiBi-Linux Wiper,
said the malware is part of a "larger campaign targeting Israeli companies with
the deliberate intent to disrupt their day-to-day operations using data
destruction."
The cybersecurity firm said it identified tactical overlaps between the
hacktivist group, who call themselves Karma, and another geopolitically
motivated actor codenamed Moses Staff (aka Cobalt Sapling), which is suspected
to be of Iranian origin.
"Although the campaign has primarily centered around Israeli IT and government
sectors up to this point, some of the participating groups, such as Moses Staff,
have a history of simultaneously targeting organizations across various business
sectors and geographical locations," Security Joes said.
Alert: 'Effluence' Backdoor Persists Despite Patching Atlassian Confluence
Servers
11.11.23
Virus
The Hacker News
Cybersecurity researchers have discovered a stealthy
backdoor named Effluence that's deployed following the successful exploitation
of a recently disclosed security flaw in Atlassian Confluence Data Center and
Server.
"The malware acts as a persistent backdoor and is not remediated by applying
patches to Confluence," Aon's Stroz Friedberg Incident Response Services said in
an analysis published earlier this week.
"The backdoor provides capability for lateral movement to other network
resources in addition to exfiltration of data from Confluence. Importantly,
attackers can access the backdoor remotely without authenticating to
Confluence."
The attack chain documented by the cybersecurity entity entailed the
exploitation of CVE-2023-22515 (CVSS score: 10.0), a critical bug in Atlassian
that could be abused to create unauthorized Confluence administrator accounts
and access Confluence servers.
Atlassian has since disclosed a second flaw known as CVE-2023-22518 (CVSS score:
10.0) that an attacker can also take advantage of to set up a rogue
administrator account, resulting in a complete loss of confidentiality,
integrity, and availability.
What makes the latest attack stand out is that the adversary gained initial
access via CVE-2023-22515 and embedded a novel web shell that grants persistent
remote access to every web page on the server, including the unauthenticated
login page, without the need for a valid user account.
The web shell, made up of a loader and payload, is passive, allowing requests to
pass through it unnoticed until a request matching a specific parameter is
provided, at which point it triggers its malicious behavior by executing a
series of actions.
This comprises creating a new admin account, purging logs to cover up the
forensic trail, running arbitrary commands on the underlying server,
enumerating, reading, and deleting files, and compiling extensive information
about the Atlassian environment.
The loader component, per Aon, acts as a normal Confluence plugin and is
responsible for decrypting and launching the payload.
"Several of the web shell functions depend on Confluence-specific APIs,"
security researcher Zachary Reichert said.
"However, the plugin and the loader mechanism appear to depend only on common
Atlassian APIs and are potentially applicable to JIRA, Bitbucket, or other
Atlassian products where an attacker can install the plugin."
New P2PInfect Worm Targets Redis Servers with Undocumented Breach Methods
31.7.23
Virus The
Hacker News
The P2PInfect peer-to-peer (P2) worm has been observed
employing previously undocumented initial access methods to breach susceptible
Redis servers and rope them into a botnet.
"The malware compromises exposed instances of the Redis data store by exploiting
the replication feature," Cado Security researchers Nate Bill and Matt Muir said
in a report shared with The Hacker News.
"A common attack pattern against Redis in cloud environments is to exploit this
feature using a malicious instance to enable replication. This is achieved via
connecting to an exposed Redis instance and issuing the SLAVEOF command."
The Rust-based malware was first documented by Palo Alto Networks Unit 42,
calling out the malware's ability to exploit a critical Lua sandbox escape
vulnerability (CVE-2022-0543, CVSS score: 10.0) to obtain a foothold into Redis
instances. The campaign is believed to have commenced on or after June 29, 2023.
However, the latest discovery suggests that the threat actors behind the
campaign are leveraging multiple exploits for initial access.
This is not the first time the SLAVEOF command has been abused in the wild.
Previously, threat actors associated with malware families such as H2Miner and
HeadCrab have abused the attack technique to illicitly mine cryptocurrency on
compromised hosts.
In doing so, the goal is to replicate a malicious instance and load a malicious
module to activate the infection.
Another initial access vector entails the registration of a malicious cron job
on the Redis host to download the malware from a remote server upon execution, a
method previously observed in attacks mounted by the WatchDog cryptojacking
group.
A successful breach is followed by the distribution of next-stage payloads that
allow the malware to alter iptables firewall rules at will, upgrade itself, and
potentially deploy cryptocurrency miners at a later date once the botnet has
grown to a specific size.
"The P2Pinfect malware makes use of a peer-to-peer
botnet," the researchers said. "Each infected server is treated as a node, which
then connects to other infected servers. This allows the entire botnet to gossip
with each other without using a centralized C2 server."
A notable trait of the botnet is its worming behavior, enabling it to expand its
reach by using a list of passwords to brute-force SSH servers and attempting to
exploit the Lua sandbox escape vulnerability or use the SLAVEOF command in the
case of Redis servers.
"P2Pinfect is well-designed and utilizes sophisticated techniques for
replication and C2," the researchers concluded. "The choice of using Rust also
allows for easier portability of code across platforms (with the Windows and
Linux binaries sharing a lot of the same code), while also making static
analysis of the code significantly harder."
Patchwork Hackers Target Chinese Research
Organizations Using EyeShell Backdoor
31.7.23
Virus The
Hacker News
Threat actors associated with the hacking crew known as
Patchwork have been spotted targeting universities and research organizations in
China as part of a recently observed campaign.
The activity, according to KnownSec 404 Team, entailed the use of a backdoor
codenamed EyeShell.
Patchwork, also known by the names Operation Hangover and Zinc Emerson, is
suspected to be a threat group that operates on behalf of India. Active since at
least December 2015, attack chains mounted by the outfit have a narrow focus and
tend to single out Pakistan and China with custom implants such as BADNEWS via
spear-phishing and watering hole attacks.
The adversarial collective has been found to share tactical overlaps with other
cyber-espionage groups with an Indian connection, including SideWinder and the
DoNot Team.
Earlier this May, Meta disclosed that it took down 50 accounts on Facebook and
Instagram operated by Patchwork, which took advantage of rogue messaging apps
uploaded to the Google Play Store to collect data from victims in Pakistan,
India, Bangladesh, Sri Lanka, Tibet, and China.
"Patchwork relied on a range of elaborate fictitious personas to socially
engineer people into clicking on malicious links and downloading malicious
apps," the social media giant said.

"These apps contained relatively basic malicious functionality with the access
to user data solely reliant on legitimate app permissions granted by the end
user. Notably, Patchwork created a fake review website for chat apps where they
listed the top five communication apps, putting their own, attacker-controlled
app at the top of the list."
Some of its activities have also been reported under the name ModifiedElephant,
according to Secureworks, referring to a set of attacks against human rights
activists, academics, and lawyers across India to conduct long-term surveillance
and plant "incriminating digital evidence" in connection with the 2018 Bhima
Koregaon violence in the state of Maharashtra.
EyeShell, detected alongside
BADNEWS, is a a .NET-based modular backdoor that comes with capabilities to
establish contact with a remote command-and-control (C2) server and execute
commands to enumerate files and directories, downloading and uploading files to
and from the host, execute a specified file, delete files, and capture
screenshots.
The findings come as the cybersecurity company also detailed another wave of
phishing attacks orchestrated by a group called Bitter aimed at aerospace,
military, large enterprises, national government affairs, and universities in
the country with a new backdoor known as ORPCBackdoor.
The South Asian threat actor was previously detected targeting the nuclear
energy industry in China with malware downloaders delivered via CHM and
Microsoft Excel Files that are designed to create persistence and retrieve
further payloads.
Fruity Trojan Uses Deceptive Software Installers to
Spread Remcos RAT
31.7.23
Virus The
Hacker News

Threat actors are creating fake websites hosting trojanized software installers
to trick unsuspecting users into downloading a downloader malware called Fruity
with the goal of installing remote trojans tools like Remcos RAT.
"Among the software in question are various instruments for fine-tuning CPUs,
graphic cards, and BIOS; PC hardware-monitoring tools; and some other apps,"
cybersecurity vendor Doctor Web said in an analysis.
"Such installers are used as a decoy and contain not only the software potential
victims are interested in, but also the trojan itself with all its components."
The exact initial access vector used in the campaign is unclear but it could
potentially range from phishing to drive-by downloads to malicious ads. Users
who land on the fake site are prompted to download a ZIP installer package.
The installer, besides activating the standard installation process, stealthily
drops the Fruity trojan, a Python-based malware that unpacks an MP3 file
("Idea.mp3") to load an image file ("Fruit.png") to activate the multi-stage
infection.
"This image file uses the steganography method to hide two executables (.dll
libraries) and the shellcode for the next-stage initialization inside it,"
Doctor Web said.
Fruity is also designed to bypass antivirus detection on the compromised host
and ultimately launch the Remcos RAT payload using a technique called process
doppelgänging.

That said, the attack sequence could be exploited to distribute all kinds of
malware, which makes it imperative that users stick to downloading software only
from trustworthy sources.
The development comes as Bitdfender disclosed details of a malspam campaign
delivering the Agent Tesla malware to harvest sensitive data from compromised
endpoints.
It also follows a surge in malvertising operations that have targeted customers
and businesses with tainted software boosted via ads on search engines.
This
includes a new wave of attacks dubbed Nitrogen in which fraudulent ISO archives
are distributed using bogus ads that impersonate download pages for applications
such as AnyDesk, WinSCP, Cisco AnyConnect, Slack, and TreeSize.
"This malvertising campaign leads to the propagation of the infection after
initial exposure," Bitdefender researchers Victor Vrabie and Alexandru Maximciuc
said.
"For as long as they dwell in the victim's network, the attackers' primary goal
is to obtain credentials, set up persistence on important systems and exfiltrate
data, with extortion as the end goal."
IcedID Malware Adapts and Expands Threat with Updated BackConnect Module
30.7.23
Virus The
Hacker News
The threat actors linked to the malware loader known as
IcedID have made updates to the BackConnect (BC) module that's used for
post-compromise activity on hacked systems, new findings from Team Cymru reveal.
IcedID, also called BokBot, is a strain of malware similar to Emotet and QakBot
that started off as a banking trojan in 2017, before switching to the role of an
initial access facilitator for other payloads. Recent versions of the malware
have been observed removing functionality related to online banking fraud to
prioritize ransomware delivery.
The BackConnect (BC) module, first documented by Netresec in October 2022,
relies on a proprietary command-and-control (C2) protocol to exchange commands
between a server and the infected host. The protocol, which comes with a VNC
component for remote access, has also been identified in other malware such as
the now-discontinued BazarLoader and QakBot.
In December 2022, Team Cymru reported the discovery of 11 BC C2s active since
July 1, 2022, noting that operators likely located in Moldova and Ukraine are
overseeing distinct elements of the BC protocol.
"For the past several months, BackConnect traffic caused by IcedID was easy to
detect because it occurred over TCP port 8080," Palo Alto Networks Unit 42 said
in late May 2023. "However, as early as April 11, 2023, BackConnect activity for
IcedID changed to TCP port 443, making it harder to find."
The latest analysis of the attack infrastructure from Team Cymru has revealed
that the number of BC C2s have shot up from 11 to 34 since January 23, 2023,
with the average uptime of a server significantly reducing from 28 days to eight
days.
"Since April 11, 2023, a total of 20 high confidence BC C2 servers were
identified, based on pivots from management infrastructure," the cybersecurity
firm said in a report shared with The Hacker News.
"The first observation is that the number of concurrent C2 servers in operation
has increased [...], with as many as four C2 servers receiving management
communications on a particular day."
A further examination of the traffic originating from BC C2 servers has
uncovered as many as eight candidate victims between late April 2023 and June
2023 that "communicated with three or more BC C2s over a relatively long period
of time."
It's also suspected that the same IcedID operator or affiliate is
accessing multiple victims within the same time frame, based on the volume of
traffic observed between the victims and the servers.
"It would appear BC is deployed alongside the usual IcedID loader and bot
infections," Josh Hopkins, head of S2 Threat Analyst Unit at Team Cymru, told
The Hacker News, adding "we see no clear distinction in infrastructure in how
it's accessed by victims and threat actors."
The cybersecurity firm also told the publication that two of the IcedID forks
that emerged in the wild in February 2023 sans the banking fraud and BackConnect
modules have not been detected in the wild recently, suggesting that they could
have been short-lived experiments.
"In examining management infrastructure associated with IcedID BC, we are also
able to discern a pattern of multiple distinct accesses from users we assess to
be both associated with the day to day operations of IcedID, and their
affiliates who interact with victim hosts post-compromise," Team Cymru said.
"The evidence in our NetFlow data suggests that certain IcedID victims are used
as proxies in spamming operations, enabled by BC's SOCKS capabilities. This is a
potential double blow for victims, not only are they compromised and incurring
data / financial loss, but they are also further exploited for the purposes of
spreading further IcedID campaigns."
Hackers Abusing Windows Search Feature to Install Remote Access Trojans
28.7.23
Virus The
Hacker News
A legitimate Windows search feature is being exploited by
malicious actors to download arbitrary payloads from remote servers and
compromise targeted systems with remote access trojans such as AsyncRAT and
Remcos RAT.
The novel attack technique, per Trellix, takes advantage of the "search-ms:" URI
protocol handler, which offers the ability for applications and HTML links to
launch custom local searches on a device, and the "search:" application
protocol, a mechanism for calling the desktop search application on Windows.
"Attackers are directing users to websites that exploit the 'search-ms'
functionality using JavaScript hosted on the page," security researchers
Mathanraj Thangaraju and Sijo Jacob said in a Thursday write-up. "This technique
has even been extended to HTML attachments, expanding the attack surface."
In such attacks, threat actors have been observed creating deceptive emails that
embed hyperlinks or HTML attachments containing a URL that redirects users to
compromised websites. This triggers the execution of JavaScript that makes use
of the URI protocol handlers to perform searches on an attacker-controlled
server.
It's worth noting that clicking on the link also generates a warning "Open
Windows Explorer?," approving which "the search results of remotely hosted
malicious shortcut files are displayed in Windows Explorer disguised as PDFs or
other trusted icons, just like local search results," the researchers explained.
"This smart technique conceals the fact that the user is being provided with
remote files and gives the user the illusion of trust. As a result, the user is
more likely to open the file, assuming it is from their own system, and
unknowingly execute malicious code."
Should a victim click on one of the shortcut files, it leads to the execution of
a rogue dynamic-link library (DLL) using the regsvr32.exe utility.
In an alternative variant of the campaign, the shortcut files are employed to
run PowerShell scripts, which, in turn, download additional payloads in the
background, while displaying a decoy PDF document to deceive victims.
Regardless of the method used, the infections lead to the installation of
AsyncRAT and Remcos RAT that can be used by the threat actors to remotely
commandeer the hosts, steal sensitive information, and even sell the access to
other attackers.
With Microsoft steadily taking steps to clamp down on
various initial access vectors, it's expected that adversaries could latch onto
the URI protocol handler method to evade traditional security defenses and
distribute malware.
"It is crucial to refrain from clicking on suspicious URLs or downloading files
from unknown sources, as these actions can expose systems to malicious payloads
delivered through the 'search' / 'search-ms' URI protocol handler," the
researchers said.
BlueBravo Deploys GraphicalProton Backdoor Against European Diplomatic Entities
28.7.23
Virus The
Hacker News

The Russian nation-state actor known as BlueBravo has been observed targeting
diplomatic entities throughout Eastern Europe with the goal of delivering a new
backdoor called GraphicalProton, exemplifying the continuous evolution of the
threat.
The phishing campaign is characterized by the use of legitimate internet
services (LIS) for command-and-control (C2) obfuscation, Recorded Future said in
a new report published Thursday. The activity was observed between March and May
2023.
BlueBravo, also known by the names APT29, Cloaked Ursa, and Midnight Blizzard
(formerly Nobelium), is attributed to Russia's Foreign Intelligence Service
(SVR), and has in the past used Dropbox, Firebase, Google Drive, Notion, and
Trello to evade detection and stealthily establish communications with infected
hosts.
To that end, GraphicalProton is the latest addition to a long list of malware
targeting diplomatic organizations after GraphicalNeutrino (aka SNOWYAMBER),
HALFRIG, and QUARTERRIG.
"Unlike GraphicalNeutrino, which used Notion for C2, GraphicalProton uses
Microsoft's OneDrive or Dropbox for communication," the cybersecurity firm said.
This marks an attempt on the part of BlueBravo operators to not only diversify
their tooling but also expand the portfolio of services misused for targeting
organizations that are of strategic interest to the nation.

"BlueBravo appears to prioritize cyber espionage efforts against European
government sector entities, possibly due to the Russian government's interest in
strategic data during and after the war in Ukraine."
The new malware strain, like GraphicalNeutrino, functions as a loader and is
staged within an ISO or ZIP file delivered via a phishing email bearing
vehicle-themed lures, overlapping with an intrusion set reported by Palo Alto
Networks Unit 42 earlier this month.
The ISO files contain .LNK files that
masquerade as .PNG images of a BMW car that's purportedly for sale, which, when
clicked, lead to the deployment of GraphicalProton for follow-on exploitation.
This is achieved by using Microsoft OneDrive as C2 and periodically polling a
folder in the storage service to fetch additional payloads.
"It is imperative for network defenders to be aware of the possibility of the
misuse of these services within their enterprise and to recognize instances in
which they may be used in similar efforts to exfiltrate information,"
researchers said.
The development comes as the Computer Emergency Response Team of Ukraine
(CERT-UA) warned of ongoing phishing attacks undertaken by a group called
UAC-0006 group, which the agency said is intensifying efforts to entice users
into installing a backdoor known as SmokeLoader.
New Malvertising Campaign Distributing Trojanized IT Tools via Google and Bing
Search Ads
27.7.23
Virus The
Hacker News

A new malvertising campaign has been observed leveraging ads on Google Search
and Bing to target users seeking IT tools like AnyDesk, Cisco AnyConnect VPN,
and WinSCP, and trick them into downloading trojanized installers with an aim to
breach enterprise networks and likely carry out future ransomware attacks.
Dubbed Nitrogen, the "opportunistic" activity is designed to deploy second-stage
attack tools such as Cobalt Strike, Sophos said in a Wednesday analysis.
Nitrogen was first documented by eSentire in June 2023, detailing an infection
chain that redirects users to compromised WordPress sites hosting malicious ISO
image files that ultimately culminate in the delivery of Python scripts and
Cobalt Strike Beacons onto the targeted system.
Then earlier this month, Trend Micro uncovered a similar attack sequence in
which a fraudulent WinSCP application functioned as a stepping stone for a
BlackCat ransomware attack.
"Throughout the infection chain, the threat actors use uncommon export
forwarding and DLL preloading techniques to mask their malicious activity and
hinder analysis," Sophos researchers Gabor Szappanos, Morgan Demboski, and
Benjamin Sollman said.
The Python scripts, once launched, establish a
Meterpreter reverse TCP shell, thereby allowing threat actors to remotely
execute code on the infected host, as well as download a Cobalt Strike Beacon to
facilitate post-exploitation.
"Abuse of pay-per-click advertisements displayed in search engine results has
become a popular tactic among threat actors," the researchers said. "The threat
actors are trying to cast a wide net to lure unsuspecting users seeking certain
IT utilities."

The findings also come against the backdrop of a spike in cybercriminals using
paid advertisements to lure users to malicious sites and trick them into
downloading a variety of malware such as BATLOADER, EugenLoader (aka FakeBat),
and IcedID, which are then used to spread information stealers and other
payloads.
To make matters worse, Sophos said it found on prominent criminal marketplaces a
"significant number of advertisements for, and discussion about, SEO poisoning,
malvertising, and related services" as well as sellers offering compromised
Google Ads accounts.
This illustrates that "marketplaces users have a keen interest in SEO poisoning
and malvertising" and that "it also negates the difficulty of trying to bypass
email filters and convincing users to click a link or download and open an
attachment."
Decoy Dog: New Breed of Malware Posing Serious
Threats to Enterprise Networks
26.7.23
Virus The
Hacker News

A deeper analysis of a recently discovered malware called Decoy Dog has revealed
that it's a significant upgrade over the Pupy RAT, an open-source remote access
trojan it's modeled on.
"Decoy Dog has a full suite of powerful, previously unknown capabilities –
including the ability to move victims to another controller, allowing them to
maintain communication with compromised machines and remain hidden for long
periods of time," Infoblox said in a Tuesday report. "Some victims have actively
communicated with a Decoy Dog server for over a year."
Other new features allow the malware to execute arbitrary Java code on the
client and connect to emergency controllers using a mechanism that's similar to
a traditional DNS domain generation algorithm (DGA), with the Decoy Dog domains
engineered to respond to replayed DNS queries from breached clients.
The sophisticated toolkit was first discovered by the cybersecurity firm in
early April 2023 after detecting anomalous DNS beaconing activity, revealing its
highly targeted attacks against enterprise networks.
The origins of Decoy Dog remain unclear as yet, but it's suspected to be
operated by a handful of nation-state hackers, who employ distinct tactics but
respond to inbound requests that match the structure of client communication.

Decoy Dog makes use of the domain name system (DNS) to perform
command-and-control (C2). An endpoint that's compromised by the malware
communicates with, and receives instructions from, a controller (i.e., a server)
via DNS queries and IP address responses.
The threat actors behind the operation are said to have made swift adjustments
to their attack infrastructure in response to the earlier disclosures, taking
down some of the DNS nameservers as well as registering new replacement domains
to establish remote persistence.
"Rather than shutting down their operation,
the actor transferred existing compromised clients to the new controllers,"
Infoblox noted. "This is an extraordinary response demonstrating the actor felt
it necessary to maintain access to their existing victims."
The first known deployment of Decoy Dog dates back to late-March or early-April
2022, following which three other clusters were detected as under the control of
different controllers. A total of 21 Decoy Dog domains have been detected to
date.
What's more, one set of controllers registered since April 2023 has adapted by
incorporating a geofencing technique to limit responses to client IP addresses
to certain locations, with observed activity limited to Russia and Eastern
Europe.
"The lack of insight into underlying victim systems and vulnerabilities being
exploited makes Decoy Dog an ongoing and serious threat," Dr. Renée Burton, head
of threat intelligence at Infoblox, said. "The best defense against this malware
is DNS."
Casbaneiro Banking Malware Goes Under the Radar
with UAC Bypass Technique
25.7.23
Virus The
Hacker News

The financially motivated threat actors behind the Casbaneiro banking malware
family have been observed making use of a User Account Control (UAC) bypass
technique to gain full administrative privileges on a machine, a sign that the
threat actor is evolving their tactics to avoid detection and execute malicious
code on compromised assets.
"They are still heavily focused on Latin American financial institutions, but
the changes in their techniques represent a significant risk to multi-regional
financial organizations as well," Sygnia said in a statement shared with The
Hacker News.
Casbaneiro, also known as Metamorfo and Ponteiro, is best known for its banking
trojan, which first emerged in mass email spam campaigns targeting the Latin
American financial sector in 2018.
Infection chains typically begin with a phishing email pointing to a
booby-trapped attachment that, when launched, activates a series of steps that
culminate in the deployment of the banking malware, alongside scripts that
leverage living-off-the-land (LotL) techniques to fingerprint the host and
gather system metadata.
Also downloaded at this stage is a binary called Horabot that's designed to
propagate the infection internally to other unsuspecting employees of the
breached organization.
"This adds credibility to the email sent, as there are no obvious anomalies in
the email headers (suspicious external domains), which would typically trigger
email security solutions to act and mitigate," the cybersecurity company said in
a previous report published in April 2022. "The emails include the same PDF
attachment used to compromise the previous victim hosts, and so the chain is
executed once more."
What's changed in recent attack waves is that the attack is kick-started by
spear-phishing email embedded with a link to an HTML file that redirects the
target to download a RAR file, a deviation from the use of malicious PDF
attachments with a download link to a ZIP file.
A second major change to the
modus operandi concerns the use of fodhelper.exe to achieve a UAC bypass and
attain high integrity level execution.
Sygnia said it also observed Casbaneiro attackers creating a mock folder on
C:\Windows[space]\system32 to copy the fodhelper.exe executable, although the
specially crafted path is said to have never been employed in the intrusion.
"It is possible that the attacker deployed the mock folder to bypass AV
detections or to leverage that folder for side-load DLLs with Microsoft-signed
binaries for UAC bypass," the company said.
The development marks the third time the mock trusted folder approach has been
detected in the wild in recent months, with the method used in campaigns
delivering a malware loader called DBatLoader as well as remote access trojans
like Warzone RAT (aka Ave Maria).
HotRat: New Variant of AsyncRAT Malware Spreading
Through Pirated Software
22.7.23
Virus The Hacker News

A new variant of AsyncRAT malware dubbed HotRat is being distributed via free,
pirated versions of popular software and utilities such as video games, image
and sound editing software, and Microsoft Office.
"HotRat malware equips attackers with a wide array of capabilities, such as
stealing login credentials, cryptocurrency wallets, screen capturing,
keylogging, installing more malware, and gaining access to or altering clipboard
data," Avast security researcher Martin a Milánek said.
The Czech cybersecurity firm said the trojan has been prevalent in the wild
since at least in October 2022, with a majority of the infections concentrated
in Thailand, Guyana, Libya, Suriname, Mali, Pakistan, Cambodia, South Africa,
and India.

The attacks entail bundling the cracked software available online via torrent
sites with a malicious AutoHotkey (AHK) script that initiates an infection chain
designed to deactivate antivirus solutions on the compromised host and
ultimately launch the HotRat payload using a Visual Basic Script loader.
HotRat, described as a comprehensive RAT malware, comes with nearly 20 commands,
each of which executes a .NET module retrieved from a remote server, allowing
the threat actors behind the campaign to extend its features as and when
required.
That said, it's worth noting that the attack requires administrative privileges
to successfully realize its goals.
"Despite the substantial risks involved, the irresistible temptation to acquire
high-quality software at no cost persists, leading many people to download
illegal software," Milánek said. "Therefore, distributing such software remains
an effective method for widely spreading malware."
Sophisticated BundleBot Malware Disguised as Google
AI Chatbot and Utilities
21.7.23
Virus The Hacker News

A new malware strain known as BundleBot has been stealthily operating under the
radar by taking advantage of .NET single-file deployment techniques, enabling
threat actors to capture sensitive information from compromised hosts.
"BundleBot is abusing the dotnet bundle (single-file), self-contained format
that results in very low or no static detection at all," Check Point said in a
report published this week, adding it is "commonly distributed via Facebook Ads
and compromised accounts leading to websites masquerading as regular program
utilities, AI tools, and games."
Some of these websites aim to mimic Google Bard, the company's conversational
generative artificial intelligence chatbot, enticing victims into downloading a
bogus RAR archive ("Google_AI.rar") hosted on legitimate cloud storage services
such as Dropbox.
The archive file, when unpacked, contains an executable file ("GoogleAI.exe"),
which is the .NET single-file, self-contained application ("GoogleAI.exe") that,
in turn, incorporates a DLL file ("GoogleAI.dll"), whose responsibility is to
fetch a password-protected ZIP archive from Google Drive.
The extracted content of the ZIP file ("ADSNEW-1.0.0.3.zip") is another .NET
single-file, self-contained application ("RiotClientServices.exe") that
incorporates the BundleBot payload ("RiotClientServices.dll") and a
command-and-control (C2) packet data serializer ("LirarySharing.dll").
"The assembly RiotClientServices.dll is a custom, new stealer/bot that uses the
library LirarySharing.dll to process and serialize the packet data that are
being sent to C2 as a part of the bot communication," the Israeli cybersecurity
company said.
The binary artifacts employ custom-made obfuscation and junk code in a bid to
resist analysis, and come with capabilities to siphon data from web browsers,
capture screenshots, grab Discord tokens, information from Telegram, and
Facebook account details.
Check Point said it also detected a second BundleBot sample that's virtually
identical in all aspects barring the use of HTTPS to exfiltrate the information
to a remote server in the form of a ZIP archive.
"The delivering method via Facebook Ads and compromised accounts is something
that has been abused by threat actors for a while, still combining it with one
of the capabilities of the revealed malware (to steal a victim's Facebook
account information) could serve as a tricky self-feeding routine," the company
noted.
Google AI Chatbot and Utilities
The development comes as Malwarebytes
uncovered a new campaign that employs sponsored posts and compromised verified
accounts that impersonate Facebook Ads Manager to entice users into downloading
rogue Google Chrome extensions that are designed to steal Facebook login
information.
Users who click on the embedded link are prompted to download a RAR archive file
containing an MSI installer file that, for its part, launches a batch script to
spawn a new Google Chrome window with the malicious extension loaded using the
"--load-extension" flag -

start chrome.exe --load-extension="%~dp0/nmmhkkegccagdldgiimedpiccmgmiedagg4"
"https://www.facebook.com/business/tools/ads-manager"
"That custom extension
is cleverly disguised as Google Translate and is considered 'Unpacked' because
it was loaded from the local computer, rather than the Chrome Web Store," Jérôme
Segura, director of threat intelligence at Malwarebytes, explained, noting it is
"entirely focused on Facebook and grabbing important pieces of information that
could allow an attacker to log into accounts."
The captured data is subsequently sent using the Google Analytics API to get
around content security policies (CSPs) to mitigate cross-site scripting (XSS)
and data injection attacks.
The threat actors behind the activity are suspected to be of Vietnamese origin,
who have, in recent months, exhibited acute interest in targeting Facebook
business and advertising accounts. Over 800 victims worldwide have been
impacted, with 310 of those located in the U.S.
"Fraudsters have a lot of time on their hands and spend years studying and
understanding how to abuse social media and cloud platforms, where it is a
constant arm's race to keep bad actors out," Segura said. "Remember that there
is no silver bullet and anything that sounds too good to be true may very well
be a scam in disguise."
Turla's New DeliveryCheck Backdoor Breaches Ukrainian Defense Sector
21.7.23 Virus
The Hacker News

The defense sector in Ukraine and Eastern Europe has been targeted by a novel
.NET-based backdoor called DeliveryCheck (aka CAPIBAR or GAMEDAY) that's capable
of delivering next-stage payloads.
The Microsoft threat intelligence team, in collaboration with the Computer
Emergency Response Team of Ukraine (CERT-UA), attributed the attacks to a
Russian nation-state actor known as Turla, which is also tracked under the names
Iron Hunter, Secret Blizzard (formerly Krypton), Uroburos, Venomous Bear, and
Waterbug. It's linked to Russia's Federal Security Service (FSB).
"DeliveryCheck is distributed via email as documents with malicious macros," the
company said in a series of tweets. "It persists via a scheduled task that
downloads and launches it in memory. It also contacts a C2 server to retrieve
tasks, which can include the launch of arbitrary payloads embedded in XSLT
stylesheets."
Successful initial access is also accompanied in some cases by the distribution
of a known Turla implant dubbed Kazuar, which is equipped to steal application
configuration files, event logs, and a wide range of data from web browsers.
The ultimate goal of the attacks is to exfiltrate messages from the Signal
messaging app for Windows, enabling the adversary to access sensitive
conversations, documents, and images on targeted systems.
A noteworthy aspect of DeliveryCheck is its ability to breach Microsoft Exchange
servers to install a server-side component using PowerShell Desired State
Configuration (DSC), a PowerShell management platform that helps administrators
to automate the configuration of Windows systems.
"DSC generates a Managed Object Format (MOF) file containing a PowerShell script
that loads the embedded .NET payload into memory, effectively turning a
legitimate server into a malware C2 center," Microsoft explained.
The
disclosure comes as the Cyber Police of Ukraine dismantled a massive bot farm
with more than 100 individuals allegedly spreading hostile propaganda justifying
the Russian invasion, leaking personal information belonging to Ukrainian
citizens, and engaging in various fraud schemes.
As part of the operation, searches were carried out in 21 locations, leading to
the seizure of computer equipment, mobile phones, more than 250 GSM gateways,
and about 150,000 SIM cards belonging to different mobile operators.
New P2PInfect Worm Targeting Redis Servers on Linux and Windows Systems
20.7.23 Virus
The Hacker News

Cybersecurity researchers have uncovered a new cloud targeting, peer-to-peer
(P2P) worm called P2PInfect that targets vulnerable Redis instances for
follow-on exploitation.
"P2PInfect exploits Redis servers running on both Linux and Windows Operating
Systems making it more scalable and potent than other worms," Palo Alto Networks
Unit 42 researchers William Gamazo and Nathaniel Quist said. "This worm is also
written in Rust, a highly scalable and cloud-friendly programming language."
It's estimated that as many as 934 unique Redis systems may be vulnerable to the
threat. The first known instance of P2PInfect was detected on July 11, 2023.
A notable characteristic of the worm is its ability to infects vulnerable Redis
instances by exploiting a critical Lua sandbox escape vulnerability,
CVE-2022-0543 (CVSS score: 10.0), which has been previously exploited to deliver
multiple malware families such as Muhstik, Redigo, and HeadCrab over the past
year.
The initial access afforded by a successful exploitation is then leveraged to
deliver a dropper payload that establishes peer-to-peer (P2P) communication to a
larger P2P network and fetch additional malicious binaries, including scanning
software for propagating the malware to other exposed Redis and SSH hosts.
"The infected instance then joins the P2P network to provide access to the other
payloads to future compromised Redis instances," the researchers said.

The malware also utilizes a PowerShell script to establish and maintain
communication between the compromised host and the P2P network, offering threat
actors persistent access. What's more, the Windows flavor of P2PInfect
incorporates a Monitor component to self-update and launch the new version.
It's not immediately known what the end goal of the campaign is, with Unit 42
noting that there is no definitive evidence of cryptojacking despite the
presence of the word "miner" in the toolkit's source code.
The activity has
not been attributed to any known threat actor groups notorious for striking
cloud environments like Adept Libra (aka TeamTNT), Aged Libra (aka Rocke),
Automated Libra (aka PURPLEURCHIN), Money Libra (aka Kinsing), Returned Libra
(aka 8220 Gang), or Thief Libra (aka WatchDog).
The development comes as misconfigured and vulnerable cloud assets are being
discovered within minutes by bad actors constantly scanning the internet to
mount sophisticated attacks.
"The P2PInfect worm appears to be well designed with several modern development
choices," the researchers said. "The design and building of a P2P network to
perform the auto-propagation of malware is not something commonly seen within
the cloud targeting or cryptojacking threat landscape."
Pakistani Entities Targeted in Sophisticated Attack Deploying ShadowPad Malware
18.7.23 Virus
The Hacker News

An unidentified threat actor compromised an application used by multiple
entities in Pakistan to deliver ShadowPad, a successor to the PlugX backdoor
that's commonly associated with Chinese hacking crews.
Targets included a Pakistan government entity, a public sector bank, and a
telecommunications provider, according to Trend Micro. The infections took place
between mid-February 2022 and September 2022.
The cybersecurity company said the incident could be the result of a
supply-chain attack, in which a legitimate piece of software used by targets of
interest is trojanized to deploy malware capable of gathering sensitive
information from compromised systems.
The attack chain takes the form of a malicious installer for E-Office, an
application developed by the National Information Technology Board (NITB) of
Pakistan to help government departments go paperless.
It's currently not clear how the backdoored E-Office installer was delivered to
the targets. That said, there's no evidence to date that the build environment
of the Pakistani government agency in question has been compromised.
This raises the possibility that the threat actor obtained the legitimate
installer and tampered it to include malware, and then subsequently lured
victims into running the trojanized version via social engineering attacks.
"Three files were added to the legitimate MSI installer:
Telerik.Windows.Data.Validation.dll, mscoree.dll, and mscoree.dll.dat," Trend
Micro researcher Daniel Lunghi said in an updated analysis published today.
Telerik.Windows.Data.Validation.dll is a valid applaunch.exe file signed by
Microsoft, which is vulnerable to DLL side-loading and is used to sideload
mscoree.dll that, in turn, loads mscoree.dll.dat, the ShadowPad payload.
Trend Micro said the obfuscation techniques used to conceal DLL and the
decrypted final-stage malware are an evolution of an approach previously exposed
by Positive Technologies in January 2021 in connection with a Chinese cyber
espionage campaign undertaken by the Winnti group (aka APT41).
Besides
ShadowPad, post-exploitation activities have entailed the use of Mimikatz to
dump passwords and credentials from memory.
Attribution to a known threat actor has been hampered by a lack of evidence,
although the cybersecurity company said it discovered malware samples such as
Deed RAT, which has been attributed to the Space Pirates (or Webworm) threat
actor.
"This whole campaign was the result of a very capable threat actor that managed
to retrieve and modify the installer of a governmental application to compromise
at least three sensitive targets," Lunghi said.
"The fact that the threat actor has access to a recent version of ShadowPad
potentially links it to the nexus of Chinese threat actors, although we cannot
point to a particular group with confidence."
FIN8 Group Using Modified Sardonic Backdoor for BlackCat Ransomware Attacks
18.7.23 Virus
The Hacker News

The financially motivated threat actor known as FIN8 has been observed using a
"revamped" version of a backdoor called Sardonic to deliver the BlackCat
ransomware.
According to the Symantec Threat Hunter Team, part of Broadcom, the development
is an attempt on the part of the e-crime group to diversify its focus and
maximize profits from infected entities. The intrusion attempt took place in
December 2022.
FIN8 is being tracked by the cybersecurity company under the name Syssphinx.
Known to be active since at least 2016, the adversary was originally attributed
to attacks targeting point-of-sale (PoS) systems using malware such as
PUNCHTRACK and BADHATCH.
The group resurfaced after more than a year in March 2021 with an updated
version of BADHATCH, following it up with a completely new bespoke implant
called Sardonic, which was disclosed by Bitdefender in August 2021.
"The C++-based Sardonic backdoor has the ability to harvest system information
and execute commands, and has a plugin system designed to load and execute
additional malware payloads delivered as DLLs," Symantec said in a report shared
with The Hacker News.
Unlike the previous variant, which was designed in C++, the latest iteration
packs in significant alterations, with most of the source code rewritten in C
and modified so as to deliberately avoid similarities.
In the incident analyzed by Symantec, Sardonic is embedded into a PowerShell
script that was deployed into the targeted system after obtaining initial
access. The script is designed to launch a .NET loader, which then decrypts and
executes an injector module to ultimately run the implant.
"The purpose of the injector is to start the backdoor in a newly created
WmiPrvSE.exe process," Symantec explained. "When creating the WmiPrvSE.exe
process, the injector attempts to start it in session-0 (best effort) using a
token stolen from the lsass.exe process."
Sardonic, besides supporting up to 10 interactive sessions on the infected host
for the threat actor to run malicious commands, supports three different plugin
formats to execute additional DLL and shellcode.
Some of the other features
of the backdoor include the ability to drop arbitrary files and exfiltrate file
contents from the compromised machine to an actor-controlled infrastructure.
This is not the first time FIN8 has been detected using Sardonic in connection
with a ransomware attack. In January 2022, Lodestone and Trend Micro uncovered
FIN8's use of the White Rabbit ransomware, which, in itself, is based on
Sardonic.
"Syssphinx continues to develop and improve its capabilities and malware
delivery infrastructure, periodically refining its tools and tactics to avoid
detection," Symantec said.
"The group's decision to expand from point-of-sale attacks to the deployment of
ransomware demonstrates the threat actors' dedication to maximizing profits from
victim organizations."
Malicious USB Drives Targetinging Global Targets
with SOGU and SNOWYDRIVE Malware
17.7.23
Virus The Hacker News
Cyber attacks using infected USB infection drives as an initial access vector
have witnessed a three-fold increase in the first half of 2023,
That's according to new findings from Mandiant, which detailed two such
campaigns – SOGU and SNOWYDRIVE – targeting both public and private sector
entities across the world.
SOGU is the "most prevalent USB-based cyber espionage attack using USB flash
drives and one of the most aggressive cyber espionage campaigns targeting both
public and private sector organizations globally across industry verticals," the
Google-owned threat intelligence firm said.
The activity has been attributed to a China-based cluster called TEMP.Hex, which
is also tracked under the names Camaro Dragon, Earth Preta, and Mustang Panda.
Targets include construction and engineering, business services, government,
health, transportation, and retail in Europe, Asia, and the U.S.
The infection chain detailed by Mandiant exhibits tactical commonalities with
another campaign detailed by Check Point, which took the wraps off a strain of
self-propagating malware called WispRider that spreads through compromised USB
drives and potentially breach air-gapped systems.
It all starts with a malicious USB flash drive plugged into a computer, leading
to the execution of PlugX (aka Korplug), which then decrypts and launches a
C-based backdoor called SOGU that exfiltrates files of interest, keystrokes, and
screenshots.

SNOWYDRIVE Targets Oil and Gas Organizations in Asia#
The second cluster to
leverage the USB infiltration mechanism is UNC4698, which has singled out oil
and gas organizations in Asia to deliver the SNOWYDRIVE malware to execute
arbitrary payloads on the hacked systems.
"Once SNOWYDRIVE is loaded, it
creates a backdoor on the host system, giving attackers the ability to remotely
issue system commands," Mandiant researchers Rommel Joven and Ng Choon Kiat
said. "It also spreads to other USB flash drives and propagates throughout the
network."
In these attacks, the victim is lured into clicking on a booby-trapped file that
masquerades as a legitimate executable, thereby activating a chain of malicious
actions, starting with a dropper that establishes a foothold, followed by
executing the SNOWYDRIVE implant.
Some of the functionalities of the backdoor consist of carrying out file and
directory searches, uploading and downloading files, and launching a reverse
shell.
"Organizations should prioritize implementing restrictions on access to external
devices such as USB drives," the researchers said. "If this is not possible,
they should at least scan these devices for malicious files or code before
connecting them to their internal networks."
WormGPT: New AI Tool Allows Cybercriminals to
Launch Sophisticated Cyber Attacks
17.7.23
Virus The Hacker News

With generative artificial intelligence (AI) becoming all the rage these days,
it's perhaps not surprising that the technology has been repurposed by malicious
actors to their own advantage, enabling avenues for accelerated cybercrime.
According to findings from SlashNext, a new generative AI cybercrime tool called
WormGPT has been advertised on underground forums as a way for adversaries to
launch sophisticated phishing and business email compromise (BEC) attacks.
"This tool presents itself as a blackhat alternative to GPT models, designed
specifically for malicious activities," security researcher Daniel Kelley said.
"Cybercriminals can use such technology to automate the creation of highly
convincing fake emails, personalized to the recipient, thus increasing the
chances of success for the attack."
The author of the software has described it as the "biggest enemy of the
well-known ChatGPT" that "lets you do all sorts of illegal stuff."
In the hands of a bad actor, tools like WormGPT could be a powerful weapon,
especially as OpenAI ChatGPT and Google Bard are increasingly taking steps to
combat the abuse of large language models (LLMs) to fabricate convincing
phishing emails and generate malicious code.
"Bard's anti-abuse restrictors in the realm of cybersecurity are significantly
lower compared to those of ChatGPT," Check Point said in a report this week.
"Consequently, it is much easier to generate malicious content using Bard's
capabilities."

Earlier this February, the Israeli cybersecurity firm disclosed how
cybercriminals are working around ChatGPT's restrictions by taking advantage of
its API, not to mention trade stolen premium accounts and sell brute-force
software to hack into ChatGPT accounts by using huge lists of email addresses
and passwords.
The fact that WormGPT operates without any ethical boundaries underscores the
threat posed by generative AI, even permitting novice cybercriminals to launch
attacks swiftly and at scale without having the technical wherewithal to do so.
Making matters worse, threat actors are promoting "jailbreaks" for ChatGPT,
engineering specialized prompts and inputs that are designed to manipulate the
tool into generating output that could involve disclosing sensitive information,
producing inappropriate content, and executing harmful code.
"Generative AI can create emails with impeccable grammar, making them seem
legitimate and reducing the likelihood of being flagged as suspicious," Kelley
said.
"The use of generative AI democratizes the execution of sophisticated BEC
attacks. Even attackers with limited skills can use this technology, making it
an accessible tool for a broader spectrum of cybercriminals."
The disclosure comes as researchers from Mithril Security "surgically" modified
an existing open-source AI model known as GPT-J-6B to make it spread
disinformation and uploaded it to a public repository like Hugging Face that
could then integrated into other applications, leading to what's called an LLM
supply chain poisoning.
The success of the technique, dubbed PoisonGPT, banks on the prerequisite that
the lobotomized model is uploaded using a name that impersonates a known
company, in this case, a typosquatted version of EleutherAI, the company behind
GPT-J.
TeamTNT's Cloud Credential Stealing Campaign Now Targets Azure and Google Cloud
14.7.23 Virus
The Hacker News
A malicious actor has been linked to a cloud credential stealing campaign in
June 2023 that's focused on Azure and Google Cloud Platform (GCP) services,
marking the adversary's expansion in targeting beyond Amazon Web Services (AWS).
The findings come from SentinelOne and Permiso, which said the "campaigns share
similarity with tools attributed to the notorious TeamTNT cryptojacking crew,"
although it emphasized that "attribution remains challenging with script-based
tools."
They also overlap with an ongoing TeamTNT campaign disclosed by Aqua called
Silentbob that leverages misconfigured cloud services to drop malware as part of
what's said to be a testing effort, while also linking SCARLETEEL attacks to the
threat actor, citing infrastructure commonalities.
"TeamTNT is scanning for credentials across multiple cloud environments,
including AWS, Azure, and GCP," Aqua noted.
The attacks, which single out public-facing Docker instances to deploy a
worm-like propagation module, are a continuation of an intrusion set that
previously targeted Jupyter Notebooks in December 2022.

As many as eight incremental versions of the credential harvesting script have
been discovered between June 15, 2023, and July 11, 2023, indicating an actively
evolving campaign.
The newer versions of the malware are designed to gather credentials from AWS,
Azure, Google Cloud Platform, Censys, Docker, Filezilla, Git, Grafana,
Kubernetes, Linux, Ngrok, PostgreSQL, Redis, S3QL, and SMB. The harvested
credentials are then exfiltrated to a remote server under the threat actor's
control.
SentinelOne said the credentials collection logic and the files
targeted bears similarities to a Kubelet-targeting campaign undertaken by
TeamTNT in September 2022.
Alongside the shell script malware, the threat actor has also been observed
distributing a Golang-based ELF binary that acts as a scanner to propagate the
malware to vulnerable targets. The binary further drops a Golang network
scanning utility called Zgrab.
"This campaign demonstrates the evolution of a seasoned cloud actor with
familiarity across many technologies," security researchers Alex Delamotte, Ian
Ahl, and Daniel Bohannon said. "The meticulous attention to detail indicates the
actor has clearly experienced plenty of trial and error."
"This actor is actively tuning and improving their tools. Based on the tweaks
observed across the past several weeks, the actor is likely preparing for larger
scale campaigns."
PicassoLoader Malware Used in Ongoing Attacks on Ukraine and Poland
14.7.23 Virus
The Hacker News

Government entities, military organizations, and civilian users in Ukraine and
Poland have been targeted as part of a series of campaigns designed to steal
sensitive data and gain persistent remote access to the infected systems.
The intrusion set, which stretches from April 2022 to July 2023, leverages
phishing lures and decoy documents to deploy a downloader malware called
PicassoLoader, which acts as a conduit to launch Cobalt Strike Beacon and njRAT.
"The attacks used a multistage infection chain initiated with malicious
Microsoft Office documents, most commonly using Microsoft Excel and PowerPoint
file formats," Cisco Talos researcher Vanja Svajcer said in a new report. "This
was followed by an executable downloader and payload concealed in an image file,
likely to make its detection more difficult."
Some of the activities have been attributed to a threat actor called GhostWriter
(aka UAC-0057 or UNC1151), whose priorities are said to align with the
Belarusian government.
It's worth noting that a subset of these attacks has already been documented
over the past year by Ukraine's Computer Emergency Response Team (CERT-UA) and
Fortinet FortiGuard Labs, one of which employed macro-laden PowerPoint documents
to deliver Agent Tesla malware in July 2022.
The infection chains aim to convince victims to enable macros, with the VBA
macro engineered to drop a DLL downloader known as PicassoLoader that
subsequently reaches out to an attacker-controlled site to fetch the next-stage
payload, a legitimate image file that embeds the final malware.
The disclosure comes as CERT-UA detailed a number of phishing operations
distributing the SmokeLoader malware as well as a smishing attack designed to
gain unauthorized control of targets' Telegram accounts.
Last month, CERT-UA disclosed a cyber espionage campaign aimed at state
organizations and media representatives in Ukraine that makes use of email and
instant messengers to distribute files, which, when launched, results in the
execution of a PowerShell script called LONEPAGE to fetch next-stage payloads
such as a browser stealer (THUMBCHOP) and a keylogger (CLOGFLAG).
GhostWriter is one among the many threat actors that have set their sights on
Ukraine. This also includes the Russian nation-state group APT28, which has been
observed using HTML attachments in phishing emails that prompt recipients to
change their UKR.NET and Yahoo! passwords due to suspicious activity detected in
their accounts so as to redirect them to bogus landing pages that ultimately
steal their credentials.
The development also follows the adoption of a "standard five-phase playbook" by
hackers associated with the Russian military intelligence (GRU) in their
disruptive operations against Ukraine in a "deliberate effort to increase the
speed, scale, and intensity" of their attacks.

This comprises taking advantage of living-on-the-edge infrastructure to gain
initial access, using living-off-the-land techniques to conduct reconnaissance,
lateral movement and information theft to limit their malware footprint and
evade detection, creating persistent, privileged access via group policy objects
(GPO), deploying wipers, and telegraphing their acts via hacktivist personas on
Telegram.
"The benefits the playbook affords are notably suited for a
fast-paced and highly contested operating environment, indicating that Russia's
wartime goals have likely guided the GRU's chosen tactical courses of action,"
Google-owned Mandiant said.
Coinciding with these unabated attack waves is a tailored phishing campaign
orchestrated by APT29 to target at least 22 diplomatic missions within Ukraine
using vehicle-themed lures since May 2023. Also called Cloaked Ursa, Cozy Bear,
or Midnight Blizzard, the group is publicly attributed to Russia's Foreign
Intelligence Service (SVR).
The attacks "use the legitimate sale of a BMW to target diplomats in Kyiv,
Ukraine, as its jumping off point," Palo Alto Networks Unit 42 said, with the
threat actor repurposing a flyer originally sent by a diplomat within the Polish
Ministry of Foreign Affairs to various embassies to pull off the scheme.
The email messages embed a link that claims to offer "more high quality photos"
of the car, but, when clicked, results in the download of malware that beacons
to Dropbox and Microsoft Graph API-based command-and-control (C2) servers for
follow-on activities, a known hallmark of the state-sponsored crew.
"Cloaked Ursa likely first collected and observed this legitimate advertising
flyer via one of the email's recipients' mail servers being compromised, or by
some other intelligence operation," the researchers said. "Upon seeing its value
as a generic yet broadly appealing phishing lure, they repurposed it. This is
staggering in scope for what generally are narrowly scoped and clandestine APT
operations."
Chinese Hackers Deploy Microsoft-Signed Rootkit to
Target Gaming Sector
12.7.23
Virus The Hacker News
Cybersecurity researchers have unearthed a novel rootkit signed by Microsoft
that's engineered to communicate with an actor-controlled attack infrastructure.
Trend Micro has attributed the activity cluster to the same actor that was
previously identified as behind the FiveSys rootkit, which came to light in
October 2021.
"This malicious actor originates from China and their main victims are the
gaming sector in China," Trend Micro's Mahmoud Zohdy, Sherif Magdy, and Mohamed
Fahmy said. Their malware seems to have passed through the Windows Hardware
Quality Labs (WHQL) process for getting a valid signature.
Multiple variants of the rootkit spanning eight different clusters have been
discovered, with 75 such drivers signed using Microsoft's WHQL program in 2022
and 2023.
Trend Micro's analysis of some of the samples has revealed the presence of debug
messages in the source code, indicating that the operation is still in the
development and testing phase.
In subsequent steps, the first-stage driver disables the User Account Control
(UAC) and Secure Desktop mode by editing the registry and initializes Winsock
Kernel (WSK) objects for initiating network communication with the remote
server.
It further periodically polls the server to retrieve more payloads and load them
directly into memory after decoding and decrypting the received data,
effectively functioning as a stealthy kernel driver loader that can bypass
detections.
"The main binary acts as a universal loader that allows the attackers to
directly load a second-stage unsigned kernel module," the researchers explained.
"Each second-stage plug-in is customized to the victim machine it's deployed on,
with some containing even a custom compiled driver for each machine. Each
plug-in has a specific set of actions to be carried out from the kernel space."
The plug-ins, for their part, come with different capabilities to achieve
persistence, disarm Microsoft Defender Antivirus, and deploy a proxy on the
machine and redirect web browsing traffic to a remote proxy server.

Much like FiveSys, the new rootkit detections have been confined exclusively to
China. One of the suspected entry points for these infections is said to be a
trojanized Chinese game, mirroring Cisco Talos' discovery of a malicious driver
called RedDriver.
The findings dovetail with other reports from Cisco Talos and Sophos about the
use of Microsoft-signed malicious kernel-mode drivers for post-exploitation
activities, with Chinese-speaking threat actors using open-source software
popular within the video game cheat development community to bypass restrictions
enforced by the tech giant.
As many as 133 malicious drivers signed with
legitimate digital certificates have been uncovered, 81 of which are capable of
terminating antivirus solutions on victims' systems. The remaining drivers are
rootkits designed to covertly monitor sensitive data sent over the internet.
The fact that these drivers are signed by the Windows Hardware Compatibility
Program (WHCP) means that attackers can install them on breached systems without
raising any alerts and proceed to carry out malicious activity virtually
unimpeded.
"Because drivers often communicate with the 'core' of the operating system and
load before security software, when they are abused, they can be particularly
effective at disabling security protections – especially when signed by a
trusted authority," Christopher Budd, director of threat research at Sophos
X-Ops, said.
Microsoft, in response to the disclosures, said it has implemented blocking
protections and suspended the partners' seller accounts involved in the incident
to safeguard users from future threats.
If anything, the development paints a picture of an evolving attack vector
that's being actively used by adversaries to obtain privileged access to Windows
machines and sidetep detection by security software.
"Malicious actors will continue to use rootkits to hide malicious code from
security tools, impair defenses, and fly under the radar for long periods of
time," the researchers said. "These rootkits will see heavy use from
sophisticated groups that have both the skills to reverse-engineer low-level
system components and the required resources to develop such tools."
New TOITOIN Banking Trojan Targeting Latin American Businesses
10.7.23
Virus The Hacker News

Businesses operating in the Latin American (LATAM) region are the target of a
new Windows-based banking trojan called TOITOIN since May 2023.
"This sophisticated campaign employs a trojan that follows a multi-staged
infection chain, utilizing specially crafted modules throughout each stage,"
Zscaler researchers Niraj Shivtarkar and Preet Kamal said in a report published
last week.
"These modules are custom designed to carry out malicious activities, such as
injecting harmful code into remote processes, circumventing User Account Control
via COM Elevation Moniker, and evading detection by Sandboxes through clever
techniques like system reboots and parent process checks."
The six-stage endeavor has all the hallmarks of a well-crafted attack sequence,
beginning with a phishing email containing an embedded link that points to a ZIP
archive hosted on an Amazon EC2 instance to evade domain-based detections.
The email messages leverage an invoice-themed lure to trick unwitting recipients
into opening them, thereby activating the infection. Within the ZIP archive is a
downloader executable that's engineered to set up persistence by means of an LNK
file in the Windows Startup folder and communicate with a remote server to
retrieve six next-stage payloads in the form of MP3 files.
The downloader is also responsible for generating a Batch script that restarts
the system after a 10-second timeout. This is done so as to "evade sandbox
detection since the malicious actions occur only after the reboot," the
researchers said.
Included among the fetched payloads is "icepdfeditor.exe," a valid signed binary
by ZOHO Corporation Private Limited, which, when executed, sideloads a rogue DLL
("ffmpeg.dll") codenamed the Krita Loader.

The loader, for its part, is designed to decode a JPG file downloaded alongside
the other payloads and launch another executable known as the InjectorDLL module
that reverses a second JPG file to form what's called the ElevateInjectorDLL
module.
The InjectorDLL component subsequently moves to inject ElevateInjectorDLL into
the "explorer.exe" process, following which a User Account Control (UAC) bypass
is carried out, if required, to elevate the process privileges and the TOITOIN
Trojan is decrypted and injected into the "svchost.exe" process.
"This
technique allows the malware to manipulate system files and execute commands
with elevated privileges, facilitating further malicious activities," the
researchers explained.
TOITOIN comes with capabilities to gather system information as well as harvest
data from installed web browsers such as Google Chrome, Microsoft Edge and
Internet Explorer, Mozilla Firefox, and Opera. Furthermore, it checks for the
presence of Topaz Online Fraud Detection (OFD), an anti-fraud module integrated
into banking platforms in the LATAM region.
The nature of the responses from the command-and-control (C2) server is
presently not known due to the fact that the server is no longer available.
"Through deceptive phishing emails, intricate redirect mechanisms, and domain
diversification, the threat actors successfully deliver their malicious
payload," the researchers said. "The multi-staged infection chain observed in
this campaign involves the use of custom-developed modules that employ various
evasion techniques and encryption methods."
RomCom RAT Targeting NATO and Ukraine Support
Groups
10.7.23 Virus
The Hacker News
The threat actors behind the RomCom RAT have been
suspected of phishing attacks targeting the upcoming NATO Summit in Vilnius as
well as an identified organization supporting Ukraine abroad.
The findings come from the BlackBerry Threat Research and Intelligence team,
which found two malicious documents submitted from a Hungarian IP address on
July 4, 2023.
RomCom, also tracked under the names Tropical Scorpius, UNC2596, and Void
Rabisu, was recently observed staging cyber attacks against politicians in
Ukraine who are working closely with Western countries and a U.S.-based
healthcare organization involved with aiding refugees fleeing the war-torn
country.
Attack chains mounted by the group are geopolitically motivated and have
employed spear-phishing emails to point victims to cloned websites hosting
trojanized versions of popular software. Targets include militaries, food supply
chains, and IT companies.
The latest lure documents identified by BlackBerry impersonate Ukrainian World
Congress, a legitimate non-profit,
("Overview_of_UWCs_UkraineInNATO_campaign.docx") and feature a bogus letter
declaring support for Ukraine's inclusion to NATO
("Letter_NATO_Summit_Vilnius_2023_ENG(1).docx").
"Although we haven't yet uncovered the initial infection vector, the threat
actor likely relied on spear-phishing techniques, engaging their victims to
click on a specially crafted replica of the Ukrainian World Congress website,"
the Canadian company said in an analysis published last week.
Opening the file triggers a sophisticated execution sequence that entails
retrieving intermediate payloads from a remote server, which, in turn, exploits
Follina (CVE-2022-30190), a now-patched security flaw affecting Microsoft's
Support Diagnostic Tool (MSDT), to achieve remote code execution.
The result
is the deployment of RomCom RAT, an executable written in C++ that's designed to
collect information about the compromised system and remote commandeer it.
"Based on the nature of the upcoming NATO Summit and the related lure documents
sent out by the threat actor, the intended victims are representatives of
Ukraine, foreign organizations, and individuals supporting Ukraine," BlackBerry
said.
"Based on the available information, we have medium to high confidence to
conclude that this is a RomCom rebranded operation, or that one or more members
of the RomCom threat group are behind this new campaign supporting a new threat
group."
Vishing Goes High-Tech: New 'Letscall' Malware
Employs Voice Traffic Routing
8.7.23
Virus The Hacker News
Researchers have issued a warning about an emerging and advanced form of voice
phishing (vishing) known as "Letscall." This technique is currently targeting
individuals in South Korea.
The criminals behind "Letscall" employ a multi-step attack to deceive victims
into downloading malicious apps from a counterfeit Google Play Store website.
Once the malicious software is installed, it redirects incoming calls to a call
center under the control of the criminals. Trained operators posing as bank
employees then extract sensitive information from unsuspecting victims.
To facilitate the routing of voice traffic, "Letscall" utilizes cutting-edge
technologies such as voice over IP (VOIP) and WebRTC. It also makes use of
Session Traversal Utilities for NAT (STUN) and Traversal Using Relays around NAT
(TURN) protocols, including Google STUN servers, to ensure high-quality phone or
video calls and bypass NAT and firewall restrictions.
The "Letscall" group consists of Android developers, designers, frontend and
backend developers, as well as call operators specializing in voice social
engineering attacks.
The malware operates in three stages: first, a downloader app prepares the
victim's device, paving the way for the installation of powerful spyware. This
spyware then triggers the final stage, which allows the rerouting of incoming
calls to the attackers' call center.

"The third stage has its own set of commands, which also includes Web socket
commands. Some of these commands relate to the manipulation of the address book,
such as creating and removing contacts. Other commands relate to creating,
modifying, and removing the filters that determine which calls should be
intercepted and which should be ignored," Dutch mobile security firm
ThreatFabric said in its report.
What sets "Letscall" apart is its utilization of advanced evasion techniques.
The malware incorporates Tencent Legu and Bangcle (SecShell) obfuscation during
the initial download. In later stages, it employs complex naming structures in
ZIP file directories and intentionally corrupts the manifest to confuse and
bypass security systems.

Criminals have developed systems that automatically call victims and play
pre-recorded messages to further deceive them. By combining mobile phone
infections with vishing techniques, these fraudsters can request micro-loans in
the victims' names while assuring them of suspicious activities and redirecting
calls to their centers.
The consequences of such attacks can be significant,
leaving victims burdened with substantial loans to repay. Financial institutions
often underestimate the severity of these invasions and fail to investigate
potential fraud.
Although this threat is currently limited to South Korea, researchers caution
that there are no technical barriers preventing these attackers from expanding
to other regions, including the European Union.
This new form of vishing attack underscores the constant evolution of criminal
tactics and their ability to exploit technology for malicious purposes. The
group responsible for the "Letscall" malware demonstrates intricate knowledge of
Android security and voice routing technologies.
Cybersecurity Agencies Sound Alarm on Rising
TrueBot Malware Attacks
7.7.23
Virus The Hacker News
Cybersecurity agencies have warned about the emergence of new variants of the
TrueBot malware. This enhanced threat is now targeting companies in the U.S. and
Canada with the intention of extracting confidential data from infiltrated
systems.
These sophisticated attacks exploit a critical vulnerability (CVE-2022-31199) in
the widely used Netwrix Auditor server and its associated agents.
This vulnerability enables unauthorized attackers to execute malicious code with
the SYSTEM user's privileges, granting them unrestricted access to compromised
systems.
The TrueBot malware, linked with cybercriminal collectives Silence and FIN11, is
deployed to siphon off data and disseminate ransomware, jeopardising the safety
of numerous infiltrated networks.
The cybercriminals gain their initial foothold by exploiting the cited
vulnerability, then proceed to install TrueBot. Once they have breached the
networks, they install the FlawedGrace Remote Access Trojan (RAT) to escalate
their privileges, establish persistence on the compromised systems, and conduct
additional operations.
"During FlawedGrace's execution phase, the RAT stores encrypted payloads within
the registry. The tool can create scheduled tasks and inject payloads into
msiexec[.]exe and svchost[.]exe, which are command processes that enable
FlawedGrace to establish a command and control (C2) connection to
92.118.36[.]199, for example, as well as load dynamic link libraries (DLLs) to
accomplish privilege escalation," the advisory says.
The cybercriminals initiate Cobalt Strike beacons within several hours of the
first intrusion. These beacons facilitate post-exploitation tasks, including
stealing data and installing ransomware or different malware payloads.
While previous versions of the TrueBot malware were typically spread through
malicious email attachments, the updated versions leverage the CVE-2022-31199
vulnerability to gain initial access.
This strategic shift allows the cyber threat actors to carry out attacks on a
broader scale within infiltrated environments. Importantly, the Netwrix Auditor
software is employed by more than 13,000 organizations worldwide, including
notable firms such as Airbus, Allianz, the UK NHS, and Virgin.
The advisory does not provide specific information about the victims or the
number of organizations affected by the TrueBot attacks.
The report also underlines the participation of the Raspberry Robin malware in
these TrueBot attacks, as well as other post-compromise malware like IcedID and
Bumblebee. By utilizing Raspberry Robin as a distribution platform, attackers
can reach more potential victims and amplify the impact of their malicious
activities.
Given that the Silence and TA505 groups are actively
infiltrating networks for monetary benefit, it is crucial for organizations to
implement suggested security measures.
To safeguard themselves against TrueBot malware and similar threats,
organizations should take the following recommendations into account:
Install updates: Organizations using Netwrix Auditor should install the
necessary updates to mitigate the CVE-2022-31199 vulnerability and update their
software to version 10.5 or above.
Enhance security protocols: Deploy
multi-factor authentication (MFA) for all employees and services.
Be vigilant
for signs of infiltration (IOCs): Security teams must actively scrutinize their
networks for indications of TrueBot contamination. The joint warning provides
guidelines to help in discovering and reducing the malware's impact.
Report
any incidents: If organizations detect IOCs or suspect a TrueBot infiltration,
they must act swiftly in accordance with the incident response actions laid out
in the warning and report the incident to CISA or the FBI.
Node.js Users Beware: Manifest Confusion Attack
Opens Door to Malware
5.7.23
Virus The Hacker News

The npm registry for the Node.js JavaScript runtime environment is susceptible
to what's called a manifest confusion attack that could potentially allow threat
actors to conceal malware in project dependencies or perform arbitrary script
execution during installation.
"A npm package's manifest is published independently from its tarball," Darcy
Clarke, a former GitHub and npm engineering manager, said in a technical
write-up published last week. "Manifests are never fully validated against the
tarball's contents."
"The ecosystem has broadly assumed the contents of the manifest and tarball are
consistent," Clarke added.
The problem, at its core, stems from the fact that the manifest and package
metadata are decoupled and that they are never cross-referenced against one
another, thereby leading to unexpected behavior and misuse when there is a
mismatch.
As a result, a threat actor could exploit this loophole to publish a module with
a manifest file (package.json) that contains hidden dependencies as well as run
install scripts, which could then pave the way for a supply chain attack and the
poisoning of a developer's environment.
"Manifest confusion becomes problematic in development environments without
effective DevSecOps workflows and tooling in place, especially when applications
blindly trust application manifests rather than the actual (vulnerable or
malicious) files contained within open source packages," Sonatype researcher and
journalist Ax Sharma said.
The finding underscores the fact that metadata contained within package manifest
files alone cannot be relied upon when downloading a package from the
open-source repository, necessitating that users take steps to scan packages for
any anomalous features and exploits.

GitHub, per Clarke, is said to be aware of the problem since at least early
November 2022, with the Microsoft subsidiary stating it plans to address it
internally as of March 2023. The issue, however, remains unresolved to date.
In the absence of an official fix, security researcher Felix Pankratz has made
available a Python script that can be used to test for mismatches between the
manifests in npm modules.
The development also comes as developer security company Snyk, in partnership
with Redhunt Labs, examined 11,900 repositories from the top 1,000 GitHub
organizations for insecure dependencies, uncovering 1,229,601 flaws in 15,584
vulnerable dependency files.
"Deserialization of untrusted data was the most
prevalent vulnerability type with a whopping 130,831 occurrences in Java
repositories, making it 40 percent of the total vulnerabilities identified," the
study said.
In JavaScript-based projects, prototype pollution emerged as the leading
shortcoming with 343,332 occurrences. Denial-of-service (DoS) flaws contributed
to the most in Python and Ruby projects with 19,652 and 56,331 occurrences,
respectively.
"The threat of vulnerable dependencies disrupting the state of security of
software supply chains is here to stay," security researchers Umair Nehri and
Vandana Verma Sehgal said. "So, developers must be careful with the dependencies
they use in their projects and keep them up-to-date to keep them patched from
any known vulnerabilities."
Chinese Hackers Use HTML Smuggling to Infiltrate
European Ministries with PlugX
4.7.23
Virus The Hacker News
A
Chinese nation-state group has been observed targeting Foreign Affairs
ministries and embassies in Europe using HTML smuggling techniques to deliver
the PlugX remote access trojan on compromised systems.
Cybersecurity firm Check Point said the activity, dubbed SmugX, has been ongoing
since at least December 2022, adding it's part of a broader trend of Chinese
adversaries shifting their focus to Europe.
"The campaign uses new delivery methods to deploy (most notably – HTML
Smuggling) a new variant of PlugX, an implant commonly associated with a wide
variety of Chinese threat actors," Check Point said.
"Although the payload itself remains similar to the one found in older PlugX
variants, its delivery methods result in low detection rates, which until
recently helped the campaign fly under the radar."
The exact identity of the threat actor behind the operation is a little hazy,
although existing clues point in the direction of Mustang Panda, which also
shares overlaps with clusters tracked as Earth Preta, RedDelta, and Check
Point's own designation Camaro Dragon.
However, the company said there is "insufficient evidence" at this stage to
conclusively attribute it to the adversarial collective.

The latest attack sequence is significant for the use of HTML Smuggling – a
stealthy technique in which legitimate HTML5 and JavaScript features are abused
to assemble and launch the malware – in the decoy documents attached to
spear-phishing emails.
"HTML smuggling employs HTML5 attributes that can work offline by storing a
binary in an immutable blob of data within JavaScript code," Trustwave noted
earlier this February. "The data blob, or the embedded payload, gets decoded
into a file object when opened via a web browser."
An analysis of the documents, which were uploaded to the VirusTotal malware
database, reveals that they are designed to target diplomats and government
entities in Czechia, Hungary, Slovakia, the U.K., Ukraine, and also likely
France and Sweden.
In one instance, the threat actor is said to have
employed an Uyghur-themed lure ("China Tries to Block Prominent Uyghur Speaker
at UN.docx") that, when opened, beacons to an external server by means of an
embedded, invisible tracking pixel to exfiltrate reconnaissance data.
The multi-stage infection process utilizes DLL side-loading methods to decrypt
and launch the final payload, PlugX.
Also called Korplug, the malware dates all the way back to 2008 and is a modular
trojan capable of accommodating "diverse plugins with distinct functionalities"
that enables the operators to carry out file theft, screen captures, keystroke
logging, and command execution.
"During the course of our investigating the samples, the threat actor dispatched
a batch script, sent from the C&C server, intended to erase any trace of their
activities," Check Point said.
"This script, named del_RoboTask Update.bat, eradicates the legitimate
executable, the PlugX loader DLL, and the registry key implemented for
persistence, and ultimately deletes itself. It is likely this is the result of
the threat actors becoming aware they were under scrutiny."
Evasive Meduza Stealer Targets 19 Password Managers and 76 Crypto Wallets
3.7.23 Virus
The Hacker News

In yet another sign of a lucrative crimeware-as-a-service (CaaS) ecosystem,
cybersecurity researchers have discovered a new Windows-based information
stealer called Meduza Stealer that's actively being developed by its author to
evade detection by software solutions.
"The Meduza Stealer has a singular objective: comprehensive data theft," Uptycs
said in a new report. "It pilfers users' browsing activities, extracting a wide
array of browser-related data."
"From critical login credentials to the valuable record of browsing history and
meticulously curated bookmarks, no digital artifact is safe. Even crypto wallet
extensions, password managers, and 2FA extensions are vulnerable."
Despite the similarity in features, Meduza boasts of a "crafty" operational
design that eschews the use of obfuscation techniques and promptly terminates
its execution on compromised hosts should a connection to the attacker's server
fail.
It's also designed to abort if a victim's location is in the stealer's
predefined list of excluded countries, which consists of the Commonwealth of
Independent States (CIS) and Turkmenistan.
Meduza Stealer, besides gathering data from 19 password manager apps, 76 crypto
wallets, 95 web browsers, Discord, Steam, and system metadata, harvests
miner-related Windows Registry entries as well as a list of installed games,
indicating a broader financial motive.

It's currently being offered for sale on underground forums such as XSS and
Exploit.in and a dedicated Telegram channel as a recurring subscription that
costs $199 per month, $399 for three months, or $1,199 for a lifetime license.
The information pilfered by the malware is made available through a
user-friendly web panel.
"This feature allows subscribers to download or delete the stolen data directly
from the web page, granting them an unprecedented level of control over their
ill-gotten information," the researchers said.
"This in-depth feature set showcases the sophisticated nature of the Meduza
Stealer and the lengths its creators are willing to go to ensure its success."
From MuddyC3 to PhonyC2: Iran's MuddyWater Evolves
with a New Cyber Weapon
30.6.23
Virus The Hacker News

The Iranian state-sponsored group dubbed MuddyWater has been attributed to a
previously unseen command-and-control (C2) framework called PhonyC2 that's been
put to use by the actor since 2021.
Evidence shows that the custom made, actively developed framework has been
leveraged in the February 2023 attack on Technion, an Israeli research
institute, cybersecurity firm Deep Instinct said in a report shared with The
Hacker News.
What's more, additional links have been unearthed between the Python 3-based
program and other attacks carried out by MuddyWater, including the ongoing
exploitation of PaperCut servers.
"It is structurally and functionally similar to MuddyC3, a previous MuddyWater
custom C2 framework that was written in Python 2," security researcher Simon
Kenin said. "MuddyWater is continuously updating the PhonyC2 framework and
changing TTPs to avoid detection."
MuddyWater, also known as Mango Sandstorm (previously Mercury), is a cyber
espionage group that's known to operate on behalf of Iran's Ministry of
Intelligence and Security (MOIS) since at least 2017.
The findings arrive nearly three months after Microsoft implicated the threat
actor for carrying out destructive attacks on hybrid environments, while also
calling out its collaboration with a related cluster tracked as Storm-1084 (aka
DEV-1084 or DarkBit) for reconnaissance, persistence, and lateral movement.
"Iran conducts cyber operations aiming at intelligence collection for strategic
purposes, essentially targeting neighboring states, in particular Iran's
geopolitical rivals such as Israel, Saudi Arabia, and Arabic Gulf countries, a
continued focus observed in all operations since 2011," French cybersecurity
company Sekoia said in an overview of pro-Iranian government cyber attacks.
Attack chains orchestrated by the group, like other Iran-nexus intrusion sets,
employ vulnerable public-facing servers and social engineering as the primary
initial access points to breach targets of interest.

"These include the use of charismatic sock puppets, the lure of prospective job
opportunities, solicitation by journalists, and masquerading as think tank
experts seeking opinions," Recorded Future noted last year. "The use of social
engineering is a central component of Iranian APT tradecraft when engaging in
cyber espionage and information operations."
Deep Instinct said it discovered the PhonyC2 framework in April 2023 on a server
that's related to broader infrastructure put to use by MuddyWater in its attack
targeting Technion earlier this year. The same server was also found to host
Ligolo, a staple reverse tunneling tool utilized by the threat actor.

The connection stems from the artifact names "C:\programdata\db.sqlite" and
"C:\programdata\db.ps1," which Microsoft described as customized PowerShell
backdoors used by MuddyWater and which are dynamically generated via the PhonyC2
framework for execution on the infected host.
PhonyC2 is a "post-exploitation framework used to generate various payloads that
connect back to the C2 and wait for instructions from the operator to conduct
the final step of the 'intrusion kill chain,'" Kenin said, calling it a
successor to MuddyC3 and POWERSTATS.
Some of the the notable commands
supported by the framework are as follows -
payload: Generate the payloads "C:\programdata\db.sqlite" and
"C:\programdata\db.ps1" as well as a PowerShell command to execute db.ps1,
which, in turn, executes db.sqlite
droper: Create different variants of
PowerShell commands to generate "C:\programdata\db.sqlite" by reaching out to
the C2 server and writing the encoded contents sent by the server to the file
Ex3cut3: Create different variants of PowerShell commands to generate
"C:\programdata\db.ps1" -- a script that contains the logic to decode db.sqlite
-- and the final-stage
list: Enumerate all connected machines to the C2
server
setcommandforall: Execute the same command across all connected hosts
simultaneously
use: Get a PowerShell shell on a remote computer to run more
commands
persist: Generate a PowerShell code to enable the operator to gain
persistence on the infected host so it will connect back to the server upon a
restart
"The framework generates for the operator different powershell
payloads," Mark Vaitzman, threat research team leader at Deep Instinct told The
Hacker News. "The operator needs to have initial access to a victim machine to
execute them. Some of the generated payloads connect back to the operator C2 to
allow persistence."
Muddywater is far from the only Iranian nation-state group to train its eyes on
Israel. In recent months, various entities in the country have been targeted by
at least three different actors such as Charming Kitten (aka APT35), Imperial
Kitten (aka Tortoiseshell), and Agrius (aka Pink Sandstorm).
"The C2 is what connects the initial phase of the attack to the final step,"
Vaitzman said. "For MuddyWater, the C2 framework is very important as it allows
them to stay stealthy and collect data from the victims. This is not the first
or last custom C2 framework they use during major attacks."
Newly Uncovered ThirdEye Windows-Based Malware Steals Sensitive Data
30.6.23 Virus
The Hacker News
A previously undocumented Windows-based information
stealer called ThirdEye has been discovered in the wild with capabilities to
harvest sensitive data from infected hosts.
Fortinet FortiGuard Labs, which made the discovery, said it found the malware in
an executable that masqueraded as a PDF file with a Russian name "CMK Правила
оформления больничных листов.pdf.exe," which translates to "CMK Rules for
issuing sick leaves.pdf.exe."
The arrival vector for the malware is presently unknown, although the nature of
the lure points to it being used in a phishing campaign. The very first ThirdEye
sample was uploaded to VirusTotal on April 4, 2023, with relatively fewer
features.
The evolving stealer, like other malware families of its kind, is equipped to
gather system metadata, including BIOS release date and vendor, total/free disk
space on the C drive, currently running processes, register usernames, and
volume information. The amassed details are then transmitted to a
command-and-control (C2) server.
A notable trait of the malware is that it uses the string "3rd_eye" to beacon
its presence to the C2 server.
There are no signs to suggest that ThirdEye has been utilized in the wild. That
having said, given that a majority of the stealer artifacts were uploaded to
VirusTotal from Russia, it's likely that the malicious activity is aimed at
Russian-speaking organizations.
"While this malware is not considered sophisticated, it's designed to steal
various information from compromised machines that can be used as
stepping-stones for future attacks," Fortinet researchers said, adding the
collected data is "valuable for understanding and narrowing down potential
targets."
The development comes as trojanized installers for the popular Super Mario Bros
video game franchise hosted on sketchy torrent sites are being used to propagate
cryptocurrency miners and an open-source stealer written in C# called Umbral
that exfiltrates data of interest using Discord Webhooks.
"The combination of mining and stealing activities leads to financial losses, a
substantial decline in the victim's system performance, and the depletion of
valuable system resources," Cyble said.

SeroXen infection chain
Video game users have also been targeted with
Python-based ransomware and a remote access trojan dubbed SeroXen, which has
been found to take advantage of a commercial batch file obfuscation engine known
as ScrubCrypt (aka BatCloak) to evade detection. Evidence shows that actors
associated with SeroXen's development have also contributed to the creation of
ScrubCrypt.
Cybersecurity
The malware, which was advertised for sale on a clearnet
website that was registered on March 27, 2023, prior to its shutdown in late
May, has further been promoted on Discord, TikTok, Twitter, and YouTube. A
cracked version of SeroXen has since found its way to criminal forums.
"Individuals are strongly advised to adopt a skeptical stance when encountering
links and software packages associated with terms such as 'cheats,' 'hacks,'
'cracks,' and other pieces of software related to gaining a competitive edge,"
Trend Micro noted in a new analysis of SeroXen.
"The addition of SeroXen and BatCloak to the malware arsenal of malicious actors
highlights the evolution of FUD obfuscators with a low barrier to entry. The
almost-amateur approach of using social media for aggressive promotion,
considering how it can be easily traced, makes these developers seem like
novices by advanced threat actors' standards."
Anatsa Banking Trojan Targeting Users in US, UK,
Germany, Austria, and Switzerland
27.6.23
Virus The Hacker News

A new Android malware campaign has been observed pushing the Anatsa banking
trojan to target banking customers in the U.S., U.K., Germany, Austria, and
Switzerland since the start of March 2023.
"The actors behind Anatsa aim to steal credentials used to authorize customers
in mobile banking applications and perform Device-Takeover Fraud (DTO) to
initiate fraudulent transactions," ThreatFabric said in an analysis published
Monday.
The Dutch cybersecurity company said Anatsa-infected Google Play Store dropper
apps have accrued over 30,000 installations to date, indicating that the
official app storefront has become an effective distribution vector for the
malware.

Anatsa, also known by the name TeaBot and Toddler, first emerged in early 2021,
and has been observed masquerading as seemingly innocuous utility apps like PDF
readers, QR code scanners, and two-factor authentication (2FA) apps on Google
Play to siphon users' credentials. It has since become one of the most prolific
banking malware, targeting over 400 financial institutions across the world.
The trojan features backdoor-like capabilities to steal data and also performs
overlay attacks in order to steal credentials as well as log activities by
abusing its permissions to Android's accessibility services API. It can further
bypass existing fraud control mechanisms to carry out unauthorized fund
transfers.
"Since transactions are initiated from the same device that targeted bank
customers regularly use, it has been reported that it is very challenging for
banking anti-fraud systems to detect it," ThreatFabric noted.
In the latest campaign observed by ThreatFabric, the dropper app, once
installed, makes a request to a GitHub page that points to another GitHub URL
hosting the malicious payload, which aims to trick victims by disguising
themselves as app add-ons. It's suspected that users are routed to these apps
through sketchy advertisements.
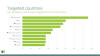
A notable aspect of the dropper is its use of the restricted
"REQUEST_INSTALL_PACKAGES" permission, which has been repeatedly exploited by
rogue apps distributed via the Google Play Store to install additional malware
on the infected device. The names of the apps are as follows -
All Document Reader & Editor
(com.mikijaki.documents.pdfreader.xlsx.csv.ppt.docs)
All Document Reader and
Viewer (com.muchlensoka.pdfcreator)
PDF Reader - Edit & View PDF
(lsstudio.pdfreader.powerfultool.allinonepdf.goodpdftools)
PDF Reader &
Editor (com.proderstarler.pdfsignature)
PDF Reader & Editor
(moh.filemanagerrespdf)
All the five dropper apps in question are said to
have been updated after their initial publication, likely in a stealthy attempt
to slip the malicious functionality after passing the app review process during
the first submission.
The list of top countries that are of interest to Anatsa based on the number of
financial applications targeted include the U.S., Italy, Germany, the U.K.,
France, the U.A.E., Switzerland, South Korea, Australia, and Sweden. Also
present in the list are Finland, Singapore, and Spain.
"The latest campaign by Anatsa reveals the evolving threat landscape that banks
and financial institutions face in today's digital world," ThreatFabric said.
"The recent Google Play Store distribution campaigns [...] demonstrate the
immense potential for mobile fraud and the need for proactive measures to
counter such threats."
Powerful JavaScript Dropper PindOS Distributes
Bumblebee and IcedID Malware
24.6.23
Virus The Hacker News

A new strain of JavaScript dropper has been observed delivering next-stage
payloads like Bumblebee and IcedID.
Cybersecurity firm Deep Instinct is tracking the malware as PindOS, which
contains the name in its "User-Agent" string.
Both Bumblebee and IcedID serve as loaders, acting as a vector for other malware
on compromised hosts, including ransomware. A recent report from Proofpoint
highlighted IcedID's abandoning of banking fraud features to solely focus on
malware delivery.
Bumblebee, notably, is a replacement for another loader called BazarLoader,
which has been attributed to the now-defunct TrickBot and Conti groups.
A report from Secureworks in April 2022 found evidence of collaboration between
several actors in the Russian cybercrime ecosystem, including that of Conti,
Emotet, and IcedID.
Deep Instinct's source code analysis of PindOS shows that it contains comments
in Russian, raising the possibility of a continued partnership between the
e-crime groups.

Described as a "surprisingly simple" loader, it's designed to download malicious
executables from a remote server. It makes use of two URLs, one of which
functions as a fallback in the event the first URL fails to fetch the DLL
payload.
"The retrieved payloads are generated pseudo-randomly 'on-demand' which results
in a new sample hash each time a payload is fetched," security researchers Shaul
Vilkomir-Preisman and Mark Vaitzman said.
The DLL files are ultimately
launched using rundll32.exe, a legitimate Windows tool to load and run DLLs.
"Whether PindOS is permanently adopted by the actors behind Bumblebee and IcedID
remains to be seen," the researchers concluded.
"If this 'experiment' is successful for each of these 'companion' malware
operators it may become a permanent tool in their arsenal and gain popularity
among other threat actors."
MULTI#STORM Campaign Targets India and U.S. with
Remote Access Trojans
23.6.23
Virus The Hacker News

A new phishing campaign codenamed MULTI#STORM has set its sights on India and
the U.S. by leveraging JavaScript files to deliver remote access trojans on
compromised systems.
"The attack chain ends with the victim machine infected with multiple unique RAT
(remote access trojan) malware instances, such as Warzone RAT and Quasar RAT,"
Securonix researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said.
"Both are used for command-and-control during different stages of the infection
chain."
The multi-stage attack chain commences when an email recipient clicks the
embedded link pointing to a password-protected ZIP file ("REQUEST.zip") hosted
on Microsoft OneDrive with the password "12345."
Extracting the archive file reveals a heavily obfuscated JavaScript file
("REQUEST.js") that, when double clicked, activates the infection by executing
two PowerShell commands that are responsible for retrieving two separate
payloads from OneDrive and executing them.
The first of the two files is a decoy PDF document that's displayed to the
victim while the second file, a Python-based executable, is stealthily run in
the background.
The binary acts as a dropper to extract and run the main payload packed inside
it in the form of Base64-encoded strings ("Storm.exe"), but not before setting
up persistence via Windows Registry modification.
Also decoded by the binary is a second ZIP file ("files.zip") that contains four
different files, each of which is designed to bypass User Account Control (UAC)
and escalate privileges by creating mock trusted directories.

Among the files is a batch file ("check.bat") that Securonix said shares several
commonalities with another loader called DBatLoader despite the difference in
the programming language used.
A second file named "KDECO.bat" executes a PowerShell command to instruct
Microsoft Defender to add an antivirus exclusion rule to skip the "C:\Users"
directory.
The attack culminates with the deployment of Warzone RAT (aka Ave
Maria), an off-the-shelf malware that's available for sale for $38 per month and
comes with an exhaustive list of features to harvest sensitive data and download
additional malware such as Quasar RAT.
"It's important to remain extra vigilant when it comes to phishing emails,
especially when a sense of urgency is stressed," the researchers said.
"This particular lure was generally unremarkable as it would require the user to
execute a JavaScript file directly. Shortcut files, or files using double
extensions would likely have a higher success rate."
Camaro Dragon Hackers Strike with USB-Driven
Self-Propagating Malware
23.6.23
Virus The Hacker News

The Chinese cyber espionage actor known as Camaro Dragon has been observed
leveraging a new strain of self-propagating malware that spreads through
compromised USB drives.
"While their primary focus has traditionally been Southeast Asian countries,
this latest discovery reveals their global reach and highlights the alarming
role USB drives play in spreading malware," Check Point said in new research
shared with The Hacker News.
The cybersecurity company, which found evidence of USB malware infections in
Myanmar, South Korea, Great Britain, India, and Russia, said the findings are
the result of a cyber incident that it investigated at an unnamed European
hospital in early 2023.
The probe found that the entity was not directly targeted by the adversary but
rather suffered a breach via an employee's USB drive, which became infected when
it was plugged into a colleague's computer at a conference in Asia.
"Consequently, upon returning to the healthcare institution in Europe, the
employee inadvertently introduced the infected USB drive, which led to spread of
the infection to the hospital's computer systems," the company said.
Camaro Dragon shares tactical similarities with that of activity clusters
tracked as Mustang Panda and LuminousMoth, with the adversarial crew recently
linked to a Go-based backdoor called TinyNote and a malicious router firmware
implant named HorseShell.
The latest infection chain comprises a Delphi launcher known as HopperTick
that's propagated via USB drives and its primary payload dubbed WispRider, which
is responsible for infecting the devices when they are attached to a machine.
"When a benign USB thumb drive is inserted into an infected computer, the
malware detects a new device inserted into the PC and manipulates its files,
creating several hidden folders at the root of the thumb drive," Check Point
researchers said.

WispRider, besides infecting the current host if not already, is tasked with
communicating with a remote server, compromising any newly connected USB
devices, executing arbitrary commands, and performing file operations.
Select variants of WispRider also function as a backdoor with capabilities to
bypass an Indonesian antivirus solution called Smadav as well as resort to DLL
side-loading by using components from security software like G-DATA Total
Security.
Another post-exploitation payload delivered alongside WispRider is a stealer
module referred to as disk monitor (HPCustPartUI.dll) that stages files with
predefined extensions (i.e., docx, mp3, wav, m4a, wma, aac, cda, and mid) for
exfiltration.
This is not the first time Chinese threat actors have been
observed taking advantage of USB devices as an infection vector to reach
environments far beyond the scope of the threat actor's primary interests.
In November 2022, Google-owned Mandiant attributed UNC4191, a threat actor with
a suspected China nexus, to a set of espionage attacks in the Philippines that
lead to the distribution of malware such as MISTCLOAK, DARKDEW, and BLUEHAZE.
A subsequent report from Trend Micro in March 2023 revealed overlaps between
UNC4191 and Mustang Panda, connecting the latter to the use of MISTCLOAK and
BLUEHAZE in spear-phishing campaigns targeting countries in Southeast Asia.
The development is a sign that the threat actors are actively changing their
tools, tactics, and procedures (TTPs) to bypass security solutions, while
simultaneously relying on a vast collection of custom tools to exfiltrate
sensitive data from victim networks.
"The Camaro Dragon APT group continues to employ USB devices as a method for
infecting targeted systems, effectively combining this technique with other
established tactics," the researchers said.
ScarCruft Hackers Exploit Ably Service for Stealthy
Wiretapping Attacks
22.6.23
Virus The Hacker News
The
North Korean threat actor known as ScarCruft has been observed using an
information-stealing malware with previous undocumented wiretapping features as
well as a backdoor developed using Golang that exploits the Ably real-time
messaging service.
"The threat actor sent their commands through the Golang backdoor that is using
the Ably service," the AhnLab Security Emergency response Center (ASEC) said in
a technical report. "The API key value required for command communication was
saved in a GitHub repository."
ScarCruft is a state-sponsored outfit with links to North Korea's Ministry of
State Security (MSS). It's known to be active since at least 2012.
Attack chains mounted by the group entail the use of spear-phishing lures to
deliver RokRAT, although it has leveraged a wide range of other custom tools to
harvest sensitive information.
In the latest intrusion detected by ASEC, the email comes bearing a Microsoft
Compiled HTML Help (.CHM) file -- a tactic first reported in March 2023 -- that,
when clicked, contacts a remote server to download a PowerShell malware known as
Chinotto.
Chinotto, in addition to being responsible for setting up persistence,
retrieving additional payloads, including a backdoor codenamed AblyGo (aka
SidLevel by Kaspersky) that abuses the Ably API service for command-and-control.
It doesn't end there, for AblyGo is used as a conduit to ultimately execute an
information stealer malware dubbed FadeStealer that comes with various features
to take screenshots, gather data from removable media and smartphones, log
keystrokes, and record microphone.
"The RedEyes group carries out attacks against specific individuals such as
North Korean defectors, human rights activists, and university professors," ASEC
said. "Their primary focus is on information theft."
"Unauthorized eavesdropping on individuals in South Korea is considered a
violation of privacy and is strictly regulated under relevant laws. Despite
this, the threat actor monitored everything victims did on their PC and even
conducted wiretapping."
CHM files have also been employed by other North
Korea-affiliated groups such as Kimsuky, what with SentinelOne disclosing a
recent campaign leveraging the file format to deliver a reconnaissance tool
called RandomQuery.
In a new set of attacks spotted by ASEC, the CHM files are configured to drop a
BAT file, which is then used to download next-stage malware and exfiltrate user
information from the compromised host.
Spear-phishing, which has been Kimsuky's preferred initial access technique for
over a decade, is typically preceded by broad research and meticulous
preparation, according to an advisory from U.S. and South Korean intelligence
agencies.
The findings also follow the Lazarus Group's active exploitation of security
flaws in software such as INISAFE CrossWeb EX, MagicLine4NX, TCO!Stream, and
VestCert that are widely used in South Korea to breach companies and deploy
malware.
Chinese Hacker Group 'Flea' Targets American
Ministries with Graphican Backdoor
22.6.23
Virus The Hacker News
Foreign affairs ministries in the Americas have been targeted by a Chinese
state-sponsored actor named Flea as part of a recent campaign that spanned from
late 2022 to early 2023.
The cyber attacks, per Broadcom's Symantec, involved a new backdoor codenamed
Graphican. Some of the other targets included a government finance department
and a corporation that markets products in the Americas as well as one
unspecified victim in an European country.
"Flea used a large number of tools in this campaign," the company said in a
report shared with The Hacker News, describing the threat actor as "large and
well-resourced." "As well as the new Graphican backdoor, the attackers leveraged
a variety of living-off-the-land tools, as well as tools that have been
previously linked to Flea."
Flea, also called APT15, BackdoorDiplomacy, ke3chang, Nylon Typhoon (formerly
Nickel), Playful Taurus, Royal APT, and Vixen Panda, is an advanced persistent
threat group that's known to strike governments, diplomatic missions, and
embassies since at least 2004.
Earlier this January, the group was attributed as behind a series of attacks
targeting Iranian government entities between July and late December 2022.
Then last month, it emerged that the Kenyan government had been singled out in a
far-reaching three-year-long intelligence-gathering operation aimed at key
ministries and state institutions in the country.
The nation-state crew has also been implicated in multiple Android surveillance
campaigns – SilkBean and BadBazaar – targeting Uyghurs in the People's Republic
of China and abroad, as detailed by Lookout in July 2020 and November 2022,
respectively.
Graphican is said to be an evolution of a known Flea backdoor called Ketrican,
features from which have since been merged with another implant known as Okrum
to spawn a new malware dubbed Ketrum.
The backdoor, despite having the same functionality, stands apart from Ketrican
for making use of Microsoft Graph API and OneDrive to obtain the details of
command-and-control (C&C) server.
"The observed Graphican samples did not have a hardcoded C&C server, rather they
connected to OneDrive via the Microsoft Graph API to get the encrypted C&C
server address from a child folder inside the "Person" folder," Symantec said.
"The malware then decoded the folder name and used it as a C&C server for the
malware."
It's worth pointing out that the abuse of Microsoft Graph API and OneDrive has
been previously observed in the case of both Russian and Chinese threat actors
like APT28 (aka Sofacy or Swallowtail) and Bad Magic (aka Red Stinger).
Graphican is equipped to poll the C&C server for new commands to run, including
creating an interactive command line that can be controlled from the server,
download files to the host, and set up covert processes to harvest data of
interest.
One among the other noteworthy tools used in the activity comprise an updated
version of the EWSTEW backdoor to extract sent and received emails on breached
Microsoft Exchange servers.
"The use of a new backdoor by Flea shows that this group, despite its long years
of operation, continues to actively develop new tools," Symantec said. "The
group has developed multiple custom tools over the years."
"The similarities in functionality between Graphican and the known Ketrican
backdoor may indicate that the group is not very concerned about having activity
attributed to it."
Experts Uncover Year-Long Cyber Attack on IT Firm
Utilizing Custom Malware RDStealer
21.6.23
Virus The Hacker News
A
highly targeted cyber attack against an East Asian IT company involved the
deployment of a custom malware written in Golang called RDStealer.
"The operation was active for more than a year with the end goal of compromising
credentials and data exfiltration," Bitdefender security researcher Victor
Vrabie said in a technical report shared with The Hacker News.
Evidence gathered by the Romanian cybersecurity firm shows that the campaign
started in early 2022. The target was an unspecified IT company located in East
Asia.
In the early phases, the operation relied on readily available remote access
trojans like AsyncRAT and Cobalt Strike, before transitioning to bespoke malware
in late 2021 or early 2022 in a bid to thwart detection.
A primary evasion tactic concerns the use of Microsoft Windows folders that are
likely to be excluded from scanning by security software (e.g., System32 and
Program Files) to store the backdoor payloads.
One of the sub-folders in question is "C:\Program Files\Dell\CommandUpdate,"
which is the directory for a legitimate Dell application called Dell Command |
Update.
Bitdefender said all the machines infected over the course of the incident were
manufactured by Dell, suggesting that the threat actors deliberately chose this
folder to camouflage the malicious activity.
This line of reasoning is bolstered by the fact that the threat actor registered
command-and-control (C2) domains such as "dell-a[.]ntp-update[.]com" with the
goal of blending in with the target environment.
The intrusion set is characterized by the use of a server-side backdoor called
RDStealer, which specializes in continuously gathering clipboard content and
keystroke data from the host.

But what makes it stand out is its capability to "monitor incoming RDP [Remote
Desktop Protocol] connections and compromise a remote machine if client drive
mapping is enabled."
Thus when a new RDP client connection is detected, commands are issued by
RDStealer to exfiltrate sensitive data, such as browsing history, credentials,
and private keys from apps like mRemoteNG, KeePass, and Google Chrome.
"This highlights the fact that threat actors actively seek credentials and saved
connections to other systems," Bitdefender's Marin Zugec said in a second
analysis.
What's more, the connecting RDP clients are infected with another
Golang-based custom malware known as Logutil to maintain a persistent foothold
on the victim network using DLL side-loading techniques and facilitate command
execution.
Not much is known about the threat actor other than the fact that it has been
active dating back to at least 2020.
"Cybercriminals continually innovate and explore novel methods to enhance the
reliability and stealthiness of their malicious activities," Zugec said.
"This attack serves as a testament to the increasing sophistication of modern
cyber attacks, but also underscores the fact that threat actors can leverage
their newfound sophistication to exploit older, widely adopted technologies."
New Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions
20.6.23 Virus
The Hacker News
A new information-stealing malware called Mystic Stealer
has been found to steal data from about 40 different web browsers and over 70
web browser extensions.
First advertised on April 25, 2023, for $150 per month, the malware also targets
cryptocurrency wallets, Steam, and Telegram, and employs extensive mechanisms to
resist analysis.
"The code is heavily obfuscated making use of polymorphic string obfuscation,
hash-based import resolution, and runtime calculation of constants," InQuest and
Zscaler researchers said in an analysis published last week.
Mystic Stealer, like many other crimeware solutions that are offered for sale,
focuses on pilfering data and is implemented in the C programming language. The
control panel has been developed using Python.
Updates to the malware in May 2023 incorporate a loader component that allows it
to retrieve and execute next-stage payloads fetched from a command-and-control
(C2) server, making it a more formidable threat.
C2 communications are achieved using a custom binary protocol over TCP. As many
as 50 operational C2 servers have been identified to date. The control panel,
for its part, serves as the interface for buyers of the stealer to access data
logs and other configurations.
Cybersecurity firm Cyfirma, which published a concurrent analysis of Mystic,
said, "the author of the product openly invites suggestions for additional
improvements in the stealer" through a dedicated Telegram channel, indicating
active efforts to court the cybercriminal community.
"It seems clear that the developer of Mystic Stealer is looking to produce a
stealer on par with the current trends of the malware space while attempting to
focus on anti-analysis and defense evasion," the researchers said.
The findings come as infostealers have emerged as a hot commodity in the
underground economy, often serving as the precursor by facilitating the
collection of credentials to enable initial access into target environments.
Put differently, stealers are used as a foundation by other cybercriminals to
launch financially motivated campaigns that employ ransomware and data extortion
elements.
The spike in popularity notwithstanding, off-the-shelf stealer malware are not
being marketed at affordable prices to appeal to a wider audience, they are also
evolving to become more lethal, packing in advanced techniques to fly under the
radar.

The ever-evolving and volatile nature of the stealer universe is best
exemplified by the steady introduction of new strains such as Album Stealer,
Aurora Stealer, Bandit Stealer, Devopt, Fractureiser, and Rhadamanthys in recent
months.
In a further sign of threat actor's attempts to evade detection, information
stealers and remote access trojans have been observed packaged within crypters
like AceCryptor, ScrubCrypt (aka BatCloak), and Snip3.
The development also comes as HP Wolf Security detailed a March 2023
ChromeLoader campaign codenamed Shampoo that's engineered to install a malicious
extension in Google Chrome and steal sensitive data, redirect searches, and
inject ads into a victim's browser session.
"Users encountered the malware
mainly from downloading illegal content, such as movies (Cocaine Bear.vbs),
video games, or other," security researcher Jack Royer said. "These websites
trick victims into running a malicious VBScript on their PCs that triggers the
infection chain."
The VBScript then proceeds to launch PowerShell code capable of terminating all
existing Chrome windows and opening a new session with the unpacked rogue
extension using the "--load-extension" command line argument.
It also follows the discovery of a new modular malware trojan christened Pikabot
that has the ability to execute arbitrary commands and inject payloads that are
provided by a C2 server, such as Cobalt Strike.
The implant, active since early 2023, has been found to share resemblances with
QBot with regard to distribution methods, campaigns, and malware behaviors,
although there is no conclusive evidence connecting the two families.
"Pikabot is a new malware family that implements an extensive set of
anti-analysis techniques and offers common backdoor capabilities to load
shellcode and execute arbitrary second-stage binaries," Zscaler said.
ChamelDoH: New Linux Backdoor Utilizing
DNS-over-HTTPS Tunneling for Covert CnC
17.6.23
Virus The Hacker News
The
threat actor known as ChamelGang has been observed using a previously
undocumented implant to backdoor Linux systems, marking a new expansion of the
threat actor's capabilities.
The malware, dubbed ChamelDoH by Stairwell, is a C++-based tool for
communicating via DNS-over-HTTPS (DoH) tunneling.
ChamelGang was first outed by Russian cybersecurity firm Positive Technologies
in September 2021, detailing its attacks on fuel, energy, and aviation
production industries in Russia, the U.S., India, Nepal, Taiwan, and Japan.
Attack chains mounted by the actor have leveraged vulnerabilities in Microsoft
Exchange servers and Red Hat JBoss Enterprise Application to gain initial access
and carry out data theft attacks using a passive backdoor called DoorMe.
"This is a native IIS module that is registered as a filter through which HTTP
requests and responses are processed," Positive Technologies said at the time.
"Its principle of operation is unusual: the backdoor processes only those
requests in which the correct cookie parameter is set."
The Linux backdoor discovered by Stairwell, for its part, is designed to capture
system information and is capable of remote access operations such as file
upload, download, deletion, and shell command execution.

What makes ChamelDoH unique is its novel communication method of using DoH,
which is used to perform Domain Name System (DNS) resolution via the HTTPS
protocol, to send DNS TXT requests to a rogue nameserver.
"Due to these DoH providers being commonly utilized DNS servers [i.e.,
Cloudflare and Google] for legitimate traffic, they cannot easily be blocked
enterprise-wide," Stairwell researcher Daniel Mayer said.
The use of DoH for command-and-control (C2) also offers additional benefits for
the threat actor in that the requests cannot be intercepted by means of an
adversary-in-the-middle (AitM) attack owing to the use of the HTTPS protocol.
This also means that security solutions cannot identify and prohibit malicious
DoH requests and sever the communications, thereby turning it to an encrypted
channel between a compromised host and the C2 server.
"The result of this tactic is akin to C2 via domain fronting, where traffic is
sent to a legitimate service hosted on a CDN, but redirected to a C2 server via
the request's Host header – both detection and prevention are difficult," Mayer
explained.
The California-based cybersecurity firm said it detected a total of 10 ChamelDoH
samples on VirusTotal, one of which was uploaded back on December 14, 2022.
The latest findings show that the "group has also devoted considerable time and
effort to researching and developing an equally robust toolset for Linux
intrusions," Mayer said.
Vidar Malware Using New Tactics to Evade Detection and Anonymize Activities
16.6.23 Virus
The Hacker News
The threat actors behind the Vidar malware have made changes to their backend
infrastructure, indicating attempts to retool and conceal their online trail in
response to public disclosures about their modus operandi.
"Vidar threat actors continue to rotate their backend IP infrastructure,
favoring providers in Moldova and Russia," cybersecurity company Team Cymru said
in a new analysis shared with The Hacker News.
Vidar is a commercial information stealer that's known to be active since late
2018. It's also a fork of another stealer malware called Arkei and is offered
for sale between $130 and $750 depending on the subscription tier.
Typically delivered through phishing campaigns and sites advertising cracked
software, the malware comes with a wide range of capabilities to harvest
sensitive information from infected hosts. Vidar has also been observed to be
distributed via rogue Google Ads and a malware loader dubbed Bumblebee.
Team Cymru, in a report published earlier January, noted that "Vidar operators
have split their infrastructure into two parts; one dedicated to their regular
customers and the other for the management team, and also potentially premium /
important users."
A key domain used by the Vidar actors is my-odin[.]com, which serves as the
one-stop destination to manage the panel, authenticate affiliates, and share
files.

While previously it was possible to download files from the site without any
authentication, performing the same action now redirects the user to a login
page. Another change involves updates to the IP address hosting the domain
itself.
This includes moving from 186.2.166[.]15 to 5.252.179[.]201 to 5.252.176[.]49 by
the end of March 2023, with the threat actors accessing the latter using VPN
servers around the same time.
"By using VPN infrastructure, which in at
least part was also utilized by numerous other benign users, it is apparent that
the Vidar threat actors may be taking steps to anonymize their management
activities by hiding in general Internet noise," Team Cymru noted.
The cybersecurity company said it also detected outbound connections from
5.252.176[.]49 to a legitimate website called blonk[.]co as well as a host
located in Russia (185.173.93[.]98:443).
The Vidar infrastructure has been found to receive yet another facelift
effective May 3, 2023, with the introduction of a new IP address
185.229.64[.]137 hosting the my-odin[.]com domain along with the use of TOR
relays by the operators to access their accounts and malware repositories.
The findings "provides further insight into the 'behind-the-scenes' operation of
Vidar, demonstrating the evolution of its management infrastructure as well as
evidence of steps taken by the threat actors to potentially cover their tracks,"
the company said.
Warning: GravityRAT Android Trojan Steals WhatsApp
Backups and Deletes Files
15.6.23
Virus The Hacker News

An updated version of an Android remote access trojan dubbed GravityRAT has been
found masquerading as messaging apps BingeChat and Chatico as part of a narrowly
targeted campaign since June 2022.
"Notable in the newly discovered campaign, GravityRAT can exfiltrate WhatsApp
backups and receive commands to delete files," ESET researcher Lukáš Štefanko
said in a new report published today.
"The malicious apps also provide legitimate chat functionality based on the
open-source OMEMO Instant Messenger app."
GravityRAT is the name given to a cross-platform malware that's capable of
targeting Windows, Android, and macOS devices. The Slovak cybersecurity firm is
tracking the activity under the name SpaceCobra.
The threat actor is suspected to be based in Pakistan, with recent attacks
involving GravityRAT targeting military personnel in India and among the
Pakistan Air Force by camouflaging it as cloud storage and entertainment apps,
as disclosed by Meta last month.
The use of chat apps as a lure to distribute the malware was previously
highlighted in November 2021 by Cyble, which analyzed a sample named "SoSafe
Chat" that was uploaded to the VirusTotal database from India.
The chat apps, while not available on Google Play, are distributed through rogue
websites promoting free messaging services: bingechat[.]net and
chatico[.]co[.]uk.
"This group used fictitious personas — posing as recruiters for both legitimate
and fake defense companies and governments, military personnel, journalists, and
women looking to make a romantic connection — in an attempt to build trust with
the people they targeted," Meta said in its Quarterly Adversarial Threat Report.

The modus operandi suggests that potential targets are contacted on Facebook and
Instagram with the goal of tricking them into clicking on the links and
downloading the malicious apps.
GravityRAT, like most Android backdoors, requests for intrusive permissions
under the garb of a seemingly legitimate app to harvest sensitive information
such as contacts, SMSes, call logs, files, location data, and audio recordings
without the victim's knowledge.
The captured data is ultimately exfiltrated to a remote server under the threat
actor's control. It's worth noting that using the app is conditional on having
an account.
What makes the new version of GravityRAT stand out is its
ability to steal WhatsApp backup files and receive instructions from the
command-and-control (C2) server to delete call logs, contact lists, and files
with particular extensions.
"These are very specific commands that are not typically seen in Android
malware," Štefanko pointed out.
The development comes as Android users in Vietnam have been victimized by a new
strain of banking cum stealer malware known as HelloTeacher that uses legitimate
messaging apps like Viber or Kik as a cover to siphon sensitive data and carry
out unauthorized fund transfers by abusing the accessibility services API.
Also discovered by Cyble is a cloud mining scam that "prompts users to download
a malicious application to start mining," only to take advantage of its
permissions to the accessibility services to gather sensitive information from
cryptocurrency wallets and banking apps.
The financial trojan, codenamed Roamer, exemplifies the trend of utilizing
phishing websites and Telegram channels as distribution vectors, thereby
effectively widening the potential victim pool.
"Users must exercise caution and refrain from following suspicious
cryptocurrency mining channels on platforms like Telegram, as these channels can
lead to substantial financial losses and compromise sensitive personal data,"
Cyble said.
New Golang-based Skuld Malware Stealing Discord and Browser Data from Windows
PCs
14.6.23 Virus
The Hacker News
A new Golang-based information stealer called Skuld has compromised Windows
systems across Europe, Southeast Asia, and the U.S.
"This new malware strain tries to steal sensitive information from its victims,"
Trellix researcher Ernesto Fernández Provecho said in a Tuesday analysis. "To
accomplish this task, it searches for data stored in applications such as
Discord and web browsers; information from the system and files stored in the
victim's folders."
Skuld, which shares overlaps with publicly available stealers like Creal
Stealer, Luna Grabber, and BlackCap Grabber, is the handiwork of a developer who
goes by the online alias Deathined on various social media platforms like
GitHub, Twitter, Reddit, and Tumblr.
Also spotted by Trellix is a Telegram group named deathinews, indicating that
these onlin avenues could be used to promote the offering in the future as a
service for other threat actors.
The malware, upon execution, checks if it's running in a virtual environment in
an attempt to thwart analysis. It further extracts the list of running processes
and compares it against a predefined blocklist. Should any process match with
those present in the blocklist, Skuld proceeds to terminate the matched process
as opposed to terminating itself.
Besides gathering system metadata, the malware possesses capabilities to harvest
cookies and credentials stored in web browsers as well as files present in the
Windows user profile folders, including Desktop, Documents, Downloads, Pictures,
Music, Videos, and OneDrive.
Artifacts analyzed by Trellix show that it's engineered to corrupt legitimate
files associated with Better Discord and Discord Token Protector and inject
JavaScript code into the Discord app to siphon backup codes, mirroring a
technique similar to that of another Rust-based infostealer recently documented
by Trend Micro.
Select samples of Skuld also incorporate a clipper module to
alter clipboard content and steal cryptocurrency assets by swapping the wallet
addresses, which the cybersecurity company theorized is likely in development.
Data exfiltration is achieved by means of an actor-controlled Discord webhook or
the Gofile upload service. In the case of the latter, a reference URL to steal
the uploaded ZIP file containing the stolen data is sent to the attacker using
the same Discord webhook functionality.

The development points to steady adoption of the Go programming language among
threat actors due to its "simplicity, efficiency, and cross-platform
compatibility," thereby making it an attractive vehicle to target multiple
operating systems and expand their victim pool.
"Additionally, Golang's compiled nature lets malware authors produce binary
executables that are more challenging to analyze and reverse engineer,"
Fernández Provecho noted. "This makes it harder for security researchers and
traditional anti-malware solutions to detect and mitigate these threats
effectively."
Fake Researcher Profiles Spread Malware through GitHub Repositories as PoC
Exploits
14.6.23
Virus The Hacker News

At least half of dozen GitHub accounts from fake researchers associated with a
fraudulent cybersecurity company have been observed pushing malicious
repositories on the code hosting service.
All seven repositories, which are still available as of writing, claim to be a
proof-of-concept (PoC) exploit for purported zero-day flaws in Discord, Google
Chrome, and Microsoft Exchange Server.
VulnCheck, which discovered the activity, said, "the individuals creating these
repositories have put significant effort into making them look legitimate by
creating a network of accounts and Twitter profiles, pretending to be part of a
non-existent company called High Sierra Cyber Security."
The cybersecurity firm said it first came across the rogue repositories in early
May when they were observed releasing similar PoC exploits for zero-day bugs in
Signal and WhatsApp. The two repositories have since been taken down.
Besides sharing some of the purported findings on Twitter in an attempt to build
legitimacy, the set of accounts have been found to use headshots of actual
security researchers from companies like Rapid7, suggesting that the threat
actors have gone to great lengths to execute the campaign.

The PoC is a Python script that's designed to download a malicious binary and
execute it on the victim's operating system, be it Windows or Linux.
The
list of GitHub repositories and fake Twitter accounts is below -
github.com/AKuzmanHSCS/Microsoft-Exchange-RCE
github.com/BAdithyaHSCS/Exchange-0-Day
github.com/DLandonHSCS/Discord-RCE
github.com/GSandersonHSCS/discord-0-day-fix
github.com/MHadzicHSCS/Chrome-0-day
github.com/RShahHSCS/Discord-0-Day-Exploit
github.com/SsankkarHSCS/Chromium-0-Day
twitter.com/AKuzmanHSCS
twitter.com/DLandonHSCS
twitter.com/GSandersonHSCS
twitter.com/MHadzicHSCS
"The attacker has made a lot of effort to create all these fake personas, only
to deliver very obvious malware," VulnCheck researcher Jacob Baines said. "It's
unclear if they have been successful, but given that they've continued to pursue
this avenue of attacks, it seems they believe they will be successful."
It's currently not known if this is the work of an amateur actor or an advanced
persistent threat (APT). But security researchers have previously come under the
radar of North Korean nation-state groups, as revealed by Google in January
2021.
If anything, the findings show the need for exercising caution when it comes to
downloading code from open source repositories. It's also essential that users
scrutinize the code prior to execution to ensure they don't pose any security
risks.
Cybercriminals Using Powerful BatCloak Engine to Make Malware Fully Undetectable
13.6.23 Virus
The Hacker News

A fully undetectable (FUD) malware obfuscation engine named BatCloak is being
used to deploy various malware strains since September 2022, while persistently
evading antivirus detection.
The samples grant "threat actors the ability to load numerous malware families
and exploits with ease through highly obfuscated batch files," Trend Micro
researchers said.
About 79.6% of the total 784 artifacts unearthed have no detection across all
security solutions, the cybersecurity firm added, highlighting BatCloak's
ability to circumvent traditional detection mechanisms.
The BatCloak engine forms the crux of an off-the-shelf batch file builder tool
called Jlaive, which comes with capabilities to bypass Antimalware Scan
Interface (AMSI) as well as compress and encrypt the primary payload to achieve
heightened security evasion.
The open-source tool, although taken down since it was made available via GitHub
and GitLab in September 2022 by a developer named ch2sh, has been advertised as
an "EXE to BAT crypter." It has since been cloned and modified by other actors
and ported to languages such as Rust.

The final payload is encapsulated using three loader layers – a C# loader, a
PowerShell loader, and a batch loader – the last of which acts as a starting
point to decode and unpack each stage and ultimately detonate the concealed
malware.
"The batch loader contains an obfuscated PowerShell loader and an encrypted C#
stub binary," researchers Peter Girnus and Aliakbar Zahravi said. "In the end,
Jlaive uses BatCloak as a file obfuscation engine to obfuscate the batch loader
and save it on a disk."
BatCloak is said to have received numerous updates and adaptations since its
emergence in the wild, its most recent version being ScrubCrypt, which was first
highlighted by Fortinet FortiGuard Labs in connection with a cryptojacking
operation mounted by the 8220 Gang.
"The decision to transition from an
open-source framework to a closed-source model, taken by the developer of
ScrubCrypt, can be attributed to the achievements of prior projects such as
Jlaive, as well as the desire to monetize the project and safeguard it against
unauthorized replication," the researchers said.
What's more, ScrubCrypt is designed to be interoperable with various well-known
malware families like Amadey, AsyncRAT, DarkCrystal RAT, Pure Miner, Quasar RAT,
RedLine Stealer, Remcos RAT, SmokeLoader, VenomRAT, and Warzone RAT.
"The evolution of BatCloak underscores the flexibility and adaptability of this
engine and highlights the development of FUD batch obfuscators," the researchers
concluded. "This showcases the presence of this technique across the modern
threat landscape."
New SPECTRALVIPER Backdoor Targeting Vietnamese Public Companies
10.6.23
Virus The Hacker News

Vietnamese public companies have been targeted as part of an ongoing campaign
that deploys a novel backdoor called SPECTRALVIPER.
"SPECTRALVIPER is a heavily obfuscated, previously undisclosed, x64 backdoor
that brings PE loading and injection, file upload and download, file and
directory manipulation, and token impersonation capabilities," Elastic Security
Labs said in a Friday report.
The attacks have been attributed to an actor it tracks as REF2754, which
overlaps with a Vietnamese threat group known as APT32, Canvas Cyclone (formerly
Bismuth), Cobalt Kitty, and OceanLotus.
Meta, in December 2020, linked the activities of the hacking crew to a
cybersecurity company named CyberOne Group.
In the latest infection flow unearthed by Elastic, the SysInternals ProcDump
utility is leveraged to load an unsigned DLL file that contains DONUTLOADER,
which, in turn, is configured to load SPECTRALVIPER and other malware such as
P8LOADER or POWERSEAL.
SPECTRALVIPER is designed to contact an actor-controlled server and awaits
further commands while also adopting obfuscation methods like control flow
flattening to resist analysis.

P8LOADER, written in C++, is capable of launching arbitrary payloads from a file
or from memory. Also used is a purpose-built PowerShell runner named POWERSEAL
that's equipped to run supplied PowerShell scripts or commands.
REF2754 is said to share tactical commonalities with another group dubbed
REF4322, which is known to primarily target Vietnamese entities to deploy a
post-exploitation implant referred to as PHOREAL (aka Rizzo).
The connections have raised the possibility that "both REF4322 and REF2754
activity groups represent campaigns planned and executed by a Vietnamese
state-affiliated threat."
The findings come as the intrusion set dubbed
REF2924 has been tied to yet another piece of malware called SOMNIRECORD that
employs DNS queries to communicate with a remote server and bypass network
security controls.
SOMNIRECORD, like NAPLISTENER, makes use of existing open source projects to
hone its capabilities, enabling it to retrieve information about the infected
machine, list all running processes, deploy a web shell, and launch any
executable already present in the system.
"The use of open source projects by the attacker indicates that they are taking
steps to customize existing tools for their specific needs and may be attempting
to counter attribution attempts," the company said.
Stealth Soldier: A New Custom Backdoor Targets North Africa with Espionage
Attacks
10.6.23
Virus The Hacker News

A new custom backdoor dubbed Stealth Soldier has been deployed as part of a set
of highly-targeted espionage attacks in North Africa.
"Stealth Soldier malware is an undocumented backdoor that primarily operates
surveillance functions such as file exfiltration, screen and microphone
recording, keystroke logging and stealing browser information," cybersecurity
company Check Point said in a technical report.
The ongoing operation is characterized by the use of command-and-control (C&C)
servers that mimic sites belonging to the Libyan Ministry of Foreign Affairs.
The earliest artifacts associated with the campaign date back to October 2022.
The attacks commence with potential targets downloading bogus downloader
binaries that are delivered via social engineering attacks and act as a conduit
for retrieving Stealth Soldier, while simultaneously displaying a decoy empty
PDF file.
The custom modular implant, which is believed to be used sparingly, enables
surveillance capabilities by gathering directory listings and browser
credentials, logging keystrokes, recording microphone audio, taking screenshots,
uploading files, and running PowerShell commands.

"The malware uses different types of commands: some are plugins that are
downloaded from the C&C and some are modules inside the malware," Check Point
said, adding the discovery of three versions of Stealth Soldier indicates that
it's being actively maintained by its operators.
Some of the components are no longer available for retrieval, but the screen
capture and browser credential stealer plugins are said to have been inspired by
open source projects available on GitHub.
What's more, the Stealth Soldier
infrastructure exhibits overlaps with infrastructure associated with another
phishing campaign dubbed Eye on the Nile, which targeted Egyptian journalists
and human rights activists in 2019.
The development signals the "first possible re-appearance of this threat actor"
since then, suggesting the group is geared towards surveillance against Egyptian
and Libyan targets.
"Given the modularity of the malware and the use of multiple stages of
infection, it is likely that the attackers will continue to evolve their tactics
and techniques and deploy new versions of this malware in the near future,"
Check Point said.
New PowerDrop Malware Targeting U.S. Aerospace Industry
7.6.23
Virus The Hacker News
An
unknown threat actor has been observed targeting the U.S. aerospace industry
with a new PowerShell-based malware called PowerDrop.
"PowerDrop uses advanced techniques to evade detection such as deception,
encoding, and encryption," according to Adlumin, which found the malware
implanted in an unnamed domestic aerospace defense contractor in May 2023.
"The name is derived from the tool, Windows PowerShell, used to concoct the
script, and 'Drop' from the DROP (DRP) string used in the code for padding."
PowerDrop is also a post-exploitation tool, meaning it's designed to gather
information from victim networks after obtaining initial access through other
means.
The malware employs Internet Control Message Protocol (ICMP) echo request
messages as beacons to initiate communications with a command-and-control (C2)
server.
The server, for its part, responds back with an encrypted command that's decoded
and run on the compromised host. A similar ICMP ping message is used for
exfiltrating the results of the instruction.
PowerDrop Malware
What's more, the PowerShell command is executed by means of
the Windows Management Instrumentation (WMI) service, indicating the adversary's
attempts to leverage living-off-the-land tactics to sidestep detection.
"While the core DNA of the threat is not particularly sophisticated, its ability
to obfuscate suspicious activity and evade detection by endpoint defenses smacks
of more sophisticated threat actors," Mark Sangster, vice president of strategy
at Adlumin, said.
Camaro Dragon Strikes with New TinyNote Backdoor for Intelligence Gathering
2.6.23 Virus
The Hacker News

The Chinese nation-state group known as Camaro Dragon has been linked to yet
another backdoor that's designed to meet its intelligence-gathering goals.
Israeli cybersecurity firm Check Point, which dubbed the Go-based malware
TinyNote, said it functions as a first-stage payload capable of "basic machine
enumeration and command execution via PowerShell or Goroutines."
What the malware lacks in terms of sophistication, it makes up for it when it
comes to establishing redundant methods to retain access to the compromised host
by means of multiple persistency tasks and varied methods to communicate with
different servers.
Camaro Dragon overlaps with a threat actor widely tracked as Mustang Panda, a
state-sponsored group from China that is known to be active since at least 2012.
The adversarial collective was recently in the spotlight for a custom bespoke
firmware implant called Horse Shell that co-opts TP-Link routers into a mesh
network capable of transmitting commands to and from the command-and-control
(C2) servers.
In other words, the goal is to obscure the malicious activity by using
compromised home routers as intermediate infrastructure that allows
communications with infected computers to emanate from a different node.
The latest findings demonstrate the evolution and growth in sophistication of
both attackers' evasion tactics and targeting, not to mention the extensive
mixture of custom tools used to breach the defenses of different targets.
The TinyNote backdoor is distributed using names related to foreign affairs
(e.g., "PDF_ Contacts List Of Invitated Deplomatic Members") and is believed to
target Southeast and East Asian embassies. It's also the first known Mustang
Panda artifact written in Golang.
A noteworthy aspect of the malware is its ability to specifically bypass an
Indonesian antivirus solution called Smadav, underscoring its high level of
preparation and deep knowledge of the victims' environments.
"The TinyNote backdoor highlights the targeted approach of Camaro Dragon and the
extensive research they conduct prior to infiltrating their intended victims'
systems," Check Point said.
"The simultaneous use of this backdoor together with other tools with different
levels of technical advancement implies that the threat actors are actively
seeking to diversify their attack arsenal."
The disclosure comes as ThreatMon uncovered APT41's (aka Wicked Panda) use of
living-off-the-land (LotL) techniques to launch a PowerShell backdoor by
leveraging a legitimate Windows executable called forfiles.
That's not all.
High-level government officials from G20 nations have emerged as a target of a
new phishing campaign orchestrated by another Chinese threat actor referred to
as Sharp Panda, per Cyble.
The emails contain booby-trapped versions of purported official documents, which
employ the remote template injection method to retrieve the next-stage
downloader from the C2 server using the Royal Road Rich Text Format (RTF)
weaponizer.
It's worth pointing out that the aforementioned infection chain is consistent
with previous Sharp Panda activity, as recently evidenced by Check Point in
attacks aimed at government entities in Southeast Asia.
What's more, the People's Liberation Army (PLA) of China has been found
leveraging open-source information available from the internet and other sources
for military intelligence purposes to gain a strategic advantage over the West.
"The PLA's use of OSINT very likely provides it an intelligence advantage, as
the West's open information environment allows the PLA to easily harvest large
quantities of open-source data, whereas Western militaries must contend with
China's closed information environment," Recorded Future noted.
The analysis draws from a list of 50 PLA and Chinese defense industry
procurement records that were published between January 2019 and January 2023.
"Commercial data providers should also be aware that China's military and
defense industry could be purchasing their data for intelligence purposes, and
should consider carrying out due diligence when selling their data to entities
in China," the company said.
Evasive QBot Malware Leverages Short-lived Residential IPs for Dynamic Attacks
1.6.23 Virus
The Hacker News

An analysis of the "evasive and tenacious" malware known as QBot has revealed
that 25% of its command-and-control (C2) servers are merely active for a single
day.
What's more, 50% of the servers don't remain active for more than a week,
indicating the use of an adaptable and dynamic C2 infrastructure, Lumen Black
Lotus Labs said in a report shared with The Hacker News.
"This botnet has adapted techniques to conceal its infrastructure in residential
IP space and infected web servers, as opposed to hiding in a network of hosted
virtual private servers (VPSs)," security researchers Chris Formosa and Steve
Rudd said.
QBot, also called QakBot and Pinkslipbot, is a persistent and potent threat that
started off as a banking trojan before evolving into a downloader for other
payloads, including ransomware. Its origins go back as far as 2007.
The malware arrives on victims' devices via spear-phishing emails, which either
directly incorporate lure files or contain embedded URLs that lead to decoy
documents.
The threat actors behind QBot have continuously improved their tactics over the
years to infiltrate victim systems using different methods such as email thread
hijacking, HTML smuggling, and employing uncommon attachment types to slip past
security barriers.
Another notable aspect of the operation is the modus operandi itself: QBot's
malspam campaigns play out in the form of bursts of intense activity followed by
periods of little to no attacks, only to resurface with a revamped infection
chain.
While phishing waves bearing QBot at the start of 2023 leveraged Microsoft
OneNote as an intrusion vector, recent attacks have employed protected PDF files
to install the malware on victim machines.
QakBot's reliance on compromised web servers and hosts existing in the
residential IP space for C2 translates to a brief lifespan and a high level of
turnover, leading to a scenario where 70 to 90 new servers emerge over a
seven-day period on average.
"Qakbot retains resiliency by repurposing
victim machines into C2s," the researchers said, adding it replenishes "the
supply of C2s through bots that subsequently turn to C2s."
According to data released by Team Cymru last month, a majority of Qakbot bot C2
servers are suspected to be compromised hosts that were purchased from a
third-party broker, with most of them located in India as of March 2023.
Black Lotus Labs' examination of the attack infrastructure has further revealed
the presence of a backconnect server that turns a "significant number" of the
infected bots into a proxy that can then be advertised for other malicious
purposes.
"Qakbot has persevered by adopting a field-expedient approach to build and
develop its architecture," the researchers concluded.
"While it may not rely on sheer numbers like Emotet, it demonstrates technical
craft by varying initial access methods and maintaining a resilient yet evasive
residential C2 architecture."
Malicious PyPI Packages Using Compiled Python Code to Bypass Detection
1.6.23 Virus
The Hacker News
Researchers have discovered a novel attack on the Python
Package Index (PyPI) repository that employs compiled Python code to sidestep
detection by application security tools.
"It may be the first supply chain attack to take advantage of the fact that
Python bytecode (PYC) files can be directly executed," ReversingLabs analyst
Karlo Zanki said in a report shared with The Hacker News.
The package in question is fshec2, which was removed from the third-party
software registry on April 17, 2023, following responsible disclosure on the
same day.
PYC files are compiled bytecode files that are generated by the Python
interpreter when a Python program is executed.
"When a module is imported for the first time (or when the source file has
changed since the current compiled file was created) a .pyc file containing the
compiled code should be created in a __pycache__ subdirectory of the directory
containing the .py file," explains the Python documentation.
The package, per the software supply chain security firm, contains three files –
_init_.py, main.py, and full.pyc – the last of which harbors malicious
functionality.
"The entry point of the package was found in the __init__.py file, which imports
a function from the other plaintext file, main.py, which contains Python source
code responsible for loading of the Python compiled module located in one of the
other files, full.pyc," Zanki pointed out.

This, in turn, is achieved by making use of the importlib package (as opposed to
a regular import) to load and execute the code present in the .pyc file.
An analysis of the reverse-engineered version of the PYC file reveals that it's
configured to collect usernames, hostnames, and directory listings, as well as
fetch commands to be executed on the host from a hard-coded server
(13.51.44[.]246).
ReversingLabs said it also observed the module download
and run another Python script that's responsible for fetching new commands
placed within a file that can be tweaked at will by the threat actor to issue
different instructions.
Further examination of the command-and-control server unearthed a
misconfiguration that made it possible to download the stolen files by their ID,
which are numbered in sequential order (starting from 1), sans any
authorization. This indicates that the attack was most likely not orchestrated
by a sophisticated actor.
The development is a continuation of efforts on the part of threat actors to
adopt different obfuscation techniques in order to evade detection from security
solutions.
"Loader scripts such as those discovered in the fshec2 package contain a minimal
amount of Python code and perform a simple action: loading of a compiled Python
module," Zanki said. "It just happens to be a malicious module."
N. Korean ScarCruft Hackers Exploit LNK Files to Spread RokRAT
1.6.23
Virus The Hacker News
Cybersecurity researchers have offered a closer look at the RokRAT remote access
trojan that's employed by the North Korean state-sponsored actor known as
ScarCruft.
"RokRAT is a sophisticated remote access trojan (RAT) that has been observed as
a critical component within the attack chain, enabling the threat actors to gain
unauthorized access, exfiltrate sensitive information, and potentially maintain
persistent control over compromised systems," ThreatMon said.
ScarCruft, active since at least 2012, is a cyber espionage group that operates
on behalf of the North Korean government, exclusively focusing on targets in its
southern counterpart.
The group is believed to be a subordinate element within North Korea's Ministry
of State Security (MSS). Attack chains mounted by the group have leaned heavily
on social engineering to spear-phish victims and deliver payloads onto target
networks.
This includes exploiting vulnerabilities in Hancom's Hangul Word Processor
(HWP), a productivity software widely used by public and private organizations
in South Korea, to deliver its signature malware dubbed RokRAT.

The Windows backdoor, also called DOGCALL, is actively developed and maintained,
and has since been ported to other operating systems such as macOS and Android.
Recent spear-phishing attacks, as evidenced by the AhnLab Security Emergency
response Center (ASEC) and Check Point, have used LNK files to trigger
multi-stage infection sequences that eventually result in the deployment of the
RokRAT malware.
RokRAT allows the adversary to harvest system metadata, take
screenshots, execute arbitrary commands received from a remote server, enumerate
directories, and exfiltrate files of interest.
The development comes as ASEC disclosed a ScarCruft attack that leverages a
Windows executable masquerading as a Hangul document to drop malware that is
configured to contact an external URL every 60 minutes.
"The URL registered in the task scheduler appears to be a normal homepage, but
it contains a web shell," ASEC noted.
RomCom RAT Using Deceptive Web of Rogue Software Sites for Covert Attacks
31.5.23 Virus
The Hacker News

The threat actors behind RomCom RAT are leveraging a network of fake websites
advertising rogue versions of popular software at least since July 2022 to
infiltrate targets.
Cybersecurity firm Trend Micro is tracking the activity cluster under the name
Void Rabisu, which is also known as Tropical Scorpius (Unit 42) and UNC2596
(Mandiant).
"These lure sites are most likely only meant for a small number of targets, thus
making discovery and analysis more difficult," security researchers Feike
Hacquebord, Stephen Hilt, Fernando Merces, and Lord Alfred Remorin said.
Some of the impersonated apps spotted so far include AstraChat, Devolutions'
Remote Desktop Manager, Gimp, GoTo Meeting, KeePass, OpenAI ChatGPT, Signal,
Veeam Backup & Replication, and WinDirStat.
RomCom RAT was first chronicled by Palo Alto Networks Unit 42 in August 2022,
linking it to a financially motivated group deploying Cuba Ransomware (aka
COLDDRAW). It's worth noting that there is no evidence to suggest that the
ransomware gang has any connection or affiliation with the Republic of Cuba.
The remote access trojan has since been used heavily in attacks targeting
Ukrainian state bodies and military systems via spoofed versions of legitimate
software. Other isolated targets have been located in the Americas and Asia.
Void Rabisu has also been observed abusing Google Ads to trick users into
visiting the lure sites as part of narrowly targeted attacks, making it the
latest addition in a long list of threat actors finding fresh avenues for
gaining initial access into victims' systems.

"RomCom used spear-phishing against a member of a European parliament in March
2022, but targeted a European defense company in October 2022 with a Google Ads
advertisement that led to an intermediary landing site that would redirect to a
RomCom lure site," Trend Micro said.
This points to the adversary mixing its targeting methodology to encompass
tactics associated with both cybercrime actors and nation-state groups.
The shift in RomCom RAT's usage as a backdoor for targeted intrusions has been
complemented by significant improvements to the malware that scales up the
number of supported commands from 20 to 49, enabling it to exert total control
over the compromised hosts.
This also includes the ability to download
additional payloads to take screenshots, grab crypto wallet data, siphon chat
messages and FTP credentials, and use a browser password stealer dubbed
StealDeal.
Another notable aspect of the attacks is the use of certificates to lend
credibility to the malicious software installers, with samples signed by
seemingly innocuous companies based in the U.S. and Canada.
"The line is blurring between cybercrime driven by financial gain and APT
attacks motivated by geopolitics, espionage, disruption, and warfare," the
researchers said.
"Since the rise of Ransomware-as-a-Service (RaaS), cybercriminals are not using
advanced tactics and targeted attacks that were previously thought to be the
domain of APT actors. Inversely, tactics and techniques that were previously
used by financially motivated actors are increasingly being used in attacks with
geopolitical goals."
Sneaky DogeRAT Trojan Poses as Popular Apps, Targets Indian Android Users
30.5.23 Virus
The Hacker News

A new open source remote access trojan (RAT) called DogeRAT targets Android
users primarily located in India as part of a sophisticated malware campaign.
The malware is distributed via social media and messaging platforms under the
guise of legitimate applications like Opera Mini, OpenAI ChatGOT, and Premium
versions of YouTube, Netflix, and Instagram.
"Once installed on a victim's device, the malware gains unauthorized access to
sensitive data, including contacts, messages, and banking credentials,"
cybersecurity firm CloudSEK said in a Monday report.
"It can also take control of the infected device, enabling malicious actions
such as sending spam messages, making unauthorized payments, modifying files,
and even remotely capturing photos through the device's cameras."
DogeRAT, like many other malware-as-a-service (MaaS) offerings, is promoted by
its India-based developer through a Telegram channel that has more than 2,100
subscribers since it was created on June 9, 2022.
This also includes a premium subscription that's sold for dirt-cheap prices
($30) with additional capabilities such as taking screenshots, stealing images,
capturing clipboard content, and logging keystrokes.

In a further attempt to make it more accessible to other criminal actors, the
free version of DogeRAT has been made available on GitHub, alongside screenshots
and video tutorials showcasing its functions.
"We do not endorse any illegal or unethical use of this tool," the developer
states in the repository's README.md file. "The user assumes all responsibility
for the use of this software."
Upon installation, the Java-based malware requests for intrusive permissions to
perform its data-gathering objectives, before exfiltrating it to a Telegram bot.
"This campaign is a stark reminder of the financial motivation driving scammers
to continually evolve their tactics," CloudSEK researcher Anshuman Das said.
"They are not just limited to creating phishing websites, but also distributing
modified RATs or repurposing malicious apps to execute scam campaigns that are
low-cost and easy to set up, yet yield high returns."
The findings come as Google-owned Mandiant detailed a new Android backdoor
called LEMONJUICE that's designed to enable remote control of and access to a
compromised device.
"The malware is capable of tracking device location, recording the microphone,
retrieving contact lists, accessing call, SMS, clipboard, and notification logs,
viewing installed applications, downloading and uploading files, viewing
connectivity status, and executing additional commands from the C2 server,"
researcher Jared Wilson said.
In a related development, Doctor Web uncovered over 100 apps containing a
spyware component called SpinOk that have been collectively downloaded more than
421 million times via the Google Play Store.
The module, which is distributed as a marketing software development kit (SDK),
is engineered to collect sensitive information stored in the devices as well as
copy and substitute clipboard contents.
Some of the most popular apps that have been found to contain the SpinOk trojan
are Noizz, Zapya, VFly, MVBit, Biugo, Crazy Drop, Cashzine, Fizzo Novel, CashEM,
and Tick.
AceCryptor: Cybercriminals' Powerful Weapon, Detected in 240K+ Attacks
30.5.23 Virus
The Hacker News
A crypter (alternatively spelled cryptor) malware dubbed
AceCryptor has been used to pack numerous strains of malware since 2016.
Slovak cybersecurity firm ESET said it identified over 240,000 detections of the
crypter in its telemetry in 2021 and 2022. This amounts to more than 10,000 hits
per month.
Some of the prominent malware families contained within AceCryptor are
SmokeLoader, RedLine Stealer, RanumBot, Raccoon Stealer, Stop ransomware, and
Amadey, among others.
The countries with the most detections include Peru, Egypt, Thailand, Indonesia,
Turkey, Brazil, Mexico, South Africa, Poland, and India.
AceCryptor was first highlighted by Avast in August 2022, detailing the use of
the malware to distribute Stop ransomware and RedLine Stealer on Discord in the
form of 7-Zip files.
Crypters are similar to packers, but instead of using compression, they are
known to obfuscate the malware code with encryption to make detection and
reverse engineering a lot more challenging.
They are also indicative of a trend where malware authors advertise such
capabilities for other threat actors, less technically sophisticated or
otherwise, who are looking to armor their creations.
"Even though threat actors can create and maintain their own custom cryptors,
for crimeware threat actors it often may be a time-consuming or technically
difficult task to maintain their cryptor in a so-called FUD (fully undetectable)
state," ESET researcher Jakub Kaloč said.
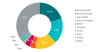
"Demand for such protection has created multiple crypter-as–a-service (CaaS)
options that pack malware."
AceCryptor-packed malware is delivered via trojanized installers of pirated
software, spam emails bearing malicious attachments, or other malware that has
already compromised a host.
It's also suspected to be sold as a CaaS, owing to the fact that it's used by
multiple threat actors to propagate a diverse range of malware families.
The
crypter is heavily obfuscated, incorporating a three-layer architecture to
progressively decrypt and unpack each stage and ultimately launch the payload,
while also featuring anti-VM, anti-debugging, and anti-analysis techniques to
fly under the radar.
The second layer, according to ESET, is said to have been introduced in 2019 as
an extra protection mechanism.
The findings come as another crypter service codenamed ScrubCrypt has been
leveraged by cryptojacking groups like the 8220 Gang to illicitly mine
cryptocurrency on infected hosts.
Earlier this January, Check Point also unearthed a packer known as TrickGate
that's used to deploy a wide range of malware such as TrickBot, Emotet, AZORult,
Agent Tesla, FormBook, Cerber, Maze, and REvil for over six years.
New GobRAT Remote Access Trojan Targeting Linux Routers in Japan
30.5.23
Virus The Hacker News

Linux routers in Japan are the target of a new Golang remote access trojan (RAT)
called GobRAT.
"Initially, the attacker targets a router whose WEBUI is open to the public,
executes scripts possibly by using vulnerabilities, and finally infects the
GobRAT," the JPCERT Coordination Center (JPCERT/CC) said in a report published
today.
The compromise of an internet-exposed router is followed by the deployment of a
loader script that acts as a conduit for delivering GobRAT, which, when
launched, masquerades as the Apache daemon process (apached) to evade detection.
The loader is also equipped to disable firewalls, establish persistence using
the cron job scheduler, and register an SSH public key in the
.ssh/authorized_keys file for remote access.
GobRAT, for its part, communicates with a remote server via the Transport Layer
Security (TLS) protocol to receive as many as 22 different encrypted commands
for execution.
Some of the major commands are as follows -
Obtain machine information
Execute reverse shell
Read/write files
Configure new command-and-control (C2) and protocol
Start SOCKS5 proxy
Execute file in /zone/frpc, and
Attempt to login to sshd, Telnet, Redis,
MySQL, PostgreSQL services running on another machine
The findings come
nearly three months after Lumen Black Lotus Labs revealed that business-grade
routers have been victimized to spy on victims in Latin America, Europe, and
North America using a malware called HiatusRAT.
New COSMICENERGY Malware Exploits ICS Protocol to Sabotage Power Grids
28.5.23 Virus
The Hacker News
A new strain of malicious software that's engineered to
penetrate and disrupt critical systems in industrial environments has been
unearthed.
Google-owned threat intelligence firm Mandiant dubbed the malware COSMICENERGY,
adding it was uploaded to the VirusTotal public malware scanning utility in
December 2021 by a submitter in Russia. There is no evidence that it has been
put to use in the wild.
"The malware is designed to cause electric power disruption by interacting with
IEC 60870-5-104 (IEC-104) devices, such as remote terminal units (RTUs), that
are commonly leveraged in electric transmission and distribution operations in
Europe, the Middle East, and Asia," the company said.
COSMICENERGY is the latest addition to specialized malware like Stuxnet, Havex,
Triton, IRONGATE, BlackEnergy2, Industroyer, and PIPEDREAM, which are capable of
sabotaging critical systems and wreaking havoc.
Mandiant said that there are circumstantial links that it may have been
developed as a red teaming tool by Russian telecom firm Rostelecom-Solar to
simulate power disruption and emergency response exercises that were held in
October 2021.
This raises the possibility that the malware was either developed to recreate
realistic attack scenarios against energy grid assets to test defenses or
another party reused code associated with the cyber range.
The second alternative is not unheard of, especially in light of the fact that
threat actors are known to adapt and repurpose legitimate red team and
post-exploitation tools for malicious ends.
COSMICENERGY's features are comparable to that of Industroyer – which has been
attributed to the Kremlin-backed Sandworm group – owing to its ability to
exploit an industrial communication protocol called IEC-104 to issue commands to
RTUs.
"Leveraging this access, an attacker can send remote commands to affect the
actuation of power line switches and circuit breakers to cause power
disruption," Mandiant said.
This is accomplished by means of two components
called PIEHOP and LIGHTWORK, which are two disruption tools written in Python
and C++, respectively, to transmit the IEC-104 commands to the connected
industrial equipment.
Another notable aspect of the industrial control system (ICS) malware is the
lack of intrusion and discovery capabilities, meaning it requires the operator
to perform an internal reconnaissance of the network to determine the IEC-104
device IP addresses to be targeted.
To pull off an attack, a threat actor would therefore have to infect a computer
within the network, find a Microsoft SQL Server that has access to the RTUs, and
obtain its credentials.
PIEHOP is then run on the machine to upload LIGHTWORK to the server, which sends
disruptive remote commands to modify the state of the units (ON or OFF) over
TCP. It also immediately deletes the executable after issuing the instructions.
The fact that an ICS malware family has been identified prior to it being
actively used in real-world attacks makes it an unusual find, Daniel Kapellmann
Zafra, analysis manager at Google Cloud's Mandiant Intelligence division, told
The Hacker News.
"While COSMICENERGY's capabilities are not significantly different from previous
OT malware families', its discovery highlights several notable developments in
the OT threat landscape," Mandiant said.
"The discovery of new OT malware presents an immediate threat to affected
organizations, since these discoveries are rare and because the malware
principally takes advantage of insecure by design features of OT environments
that are unlikely to be remedied any time soon."
"One of the main lessons from COSMICENERGY is that defenders should be familiar
with prior OT [operational technology] malware families, their capabilities, and
how they work," Kapellmann Zafra said.
"Knowledge about this can help defenders to sustain threat hunting and detection
programs that rigorously look for behaviors that are known to be suspicious in
OT networks."
New PowerExchange Backdoor Used in Iranian Cyber Attack on UAE Government
25.5.23 Virus
The Hacker News

An unnamed government entity associated with the United Arab Emirates (U.A.E.)
was targeted by a likely Iranian threat actor to breach the victim's Microsoft
Exchange Server with a "simple yet effective" backdoor dubbed PowerExchange.
According to a new report from Fortinet FortiGuard Labs, the intrusion relied on
email phishing as an initial access pathway, leading to the execution of a .NET
executable contained with a ZIP file attachment.
The binary, which masquerades as a PDF document, functions as a dropper to
execute the final payload, which then launches the backdoor.
PowerExchange, written in PowerShell, employs text files attached to emails for
command-and-control (C2) communication. It allows the threat actor to run
arbitrary payloads and upload and download files from and to the system.
The custom implant achieves this by making use of the Exchange Web Services
(EWS) API to connect to the victim's Exchange Server and uses a mailbox on the
server to send and receive encoded commands from its operator.
"The Exchange Server is accessible from the internet, saving C2 communication to
external servers from the devices in the organizations," Fortinet researchers
said. "It also acts as a proxy for the attacker to mask himself."
That said, it's currently not known how the threat actor managed to obtain the
domain credentials to connect to the target Exchange Server.
Fortinet's investigation also uncovered Exchange servers that were backdoored
with several web shells, one of which is called ExchangeLeech (aka
System.Web.ServiceAuthentication.dll), to achieve persistent remote access and
steal user credentials.
PowerExchange is suspected to be an upgraded version
of TriFive, which was previously used by the Iranian nation-stage actor APT34
(aka OilRig) in intrusions targeting government organizations in Kuwait.
Furthermore, communication via internet-facing Exchange servers is a
tried-and-tested tactic adopted by the OilRig actors, as observed in the case of
Karkoff and MrPerfectionManager.
"Using the victim's Exchange server for the C2 channel allows the backdoor to
blend in with benign traffic, thereby ensuring that the threat actor can easily
avoid nearly all network-based detections and remediations inside and outside
the target organization's infrastructure," the researchers said.
Legion Malware Upgraded to Target SSH Servers and AWS Credentials
24.5.23
Virus The Hacker News
An
updated version of the commodity malware called Legion comes with expanded
features to compromise SSH servers and Amazon Web Services (AWS) credentials
associated with DynamoDB and CloudWatch.
"This recent update demonstrates a widening of scope, with new capabilities such
the ability to compromise SSH servers and retrieve additional AWS-specific
credentials from Laravel web applications," Cado Labs researcher Matt Muir said
in a report shared with The Hacker News.
"It's clear that the developer's targeting of cloud services is advancing with
each iteration."
Legion, a Python-based hack tool, was first documented last month by the cloud
security firm, detailing its ability to breach vulnerable SMTP servers in order
to harvest credentials.
It's also known to exploit web servers running content management systems (CMS),
leverage Telegram as a data exfiltration point, and send spam SMS messages to a
list of dynamically-generated U.S. mobile numbers by making use of the stolen
SMTP credentials.
A notable addition to Legion is its ability to exploit SSH servers using the
Paramiko module. It also includes features to retrieve additional AWS-specific
credentials related to DynamoDB, CloudWatch, and AWS Owl from Laravel web
applications.
Another change relates to the inclusion of additional paths to
enumerate for the existence of .env files such as /cron/.env, /lib/.env,
/sitemaps/.env, /tools/.env, /uploads/.env, and /web/.env among others.
"Misconfigurations in web applications are still the primary method used by
Legion to retrieve credentials," Muir said.
"Therefore, it's recommended that developers and administrators of web
applications regularly review access to resources within the applications
themselves, and seek alternatives to storing secrets in environment files."
North Korean Kimsuky Hackers Strike Again with Advanced Reconnaissance Malware
24.5.23 Virus
The Hacker News
The North Korean advanced persistent threat (APT) group
known as Kimsuky has been observed using a piece of custom malware called
RandomQuery as part of a reconnaissance and information exfiltration operation.
"Lately, Kimsuky has been consistently distributing custom malware as part of
reconnaissance campaigns to enable subsequent attacks," SentinelOne researchers
Aleksandar Milenkoski and Tom Hegel said in a report published today.
The ongoing targeted campaign, per the cybersecurity firm, is primarily geared
towards information services as well as organizations supporting human rights
activists and North Korean defectors.
Kimsuky, active since 2012, has exhibited targeting patterns that align with
North Korea's operational mandates and priorities.
The intelligence collection missions have involved the use of a diverse set of
malware, including another reconnaissance program called ReconShark, as detailed
by SentinelOne earlier this month.
The latest activity cluster associated with the group commenced on May 5, 2023,
and leverages a variant of RandomQuery that's specifically designed to enumerate
files and siphon sensitive data.
RandomQuery, alongside FlowerPower and AppleSeed, are among the most frequently
distributed tools in Kimsuky's arsenal, with the former functioning as an
information stealer and a conduit for distributing remote access trojans like
TutRAT and xRAT.
The attacks begin with phishing emails that purport to be from Daily NK, a
prominent Seoul-based online publication that covers North Korean affairs, to
entice potential targets into opening a Microsoft Compiled HTML Help (CHM) file.
It's worth noting at this stage that CHM files have also been adopted as a lure
by a different North Korean nation-state actor referred to as ScarCruft.
Launching the CHM file leads to the execution of a Visual Basic Script that
issues a HTTP GET request to a remote server to retrieve the second-stage
payload, a VBScript flavor of RandomQuery.
The malware then proceeds to
harvest system metadata, running processes, installed applications, and files
from different folders, all of which are transmitted back to the
command-and-control (C2) server.
"This campaign also demonstrates the group's consistent approach of delivering
malware through CHM files," the researchers said.
"These incidents underscore the ever-changing landscape of North Korean threat
groups, whose remit not only encompasses political espionage but also sabotage
and financial threats."
The findings arrive days after the AhnLab Security Emergency response Center
(ASEC) uncovered a watering hole attack mounted by Kimsuky that entails setting
up a lookalike webmail system used by national policy research institutes to
harvest credentials entered by victims.
In a related development, Kimsuky has also been linked to attacks that weaponize
vulnerable Windows Internet Information Services (IIS) servers to drop the
Metasploit Meterpreter post-exploitation framework, which is then used to deploy
a Go-based proxy malware.
New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East
24.5.23 Virus
The Hacker News

An unknown threat actor has been observed leveraging a malicious Windows kernel
driver in attacks likely targeting the Middle East since at least May 2020.
Fortinet Fortiguard Labs, which dubbed the artifact WINTAPIX (WinTapix.sys),
attributed the malware with low confidence to an Iranian threat actor.
"WinTapix.sys is essentially a loader," security researchers Geri Revay and
Hossein Jazi said in a report published on Monday. "Thus, its primary purpose is
to produce and execute the next stage of the attack. This is done using a
shellcode."
Samples and telemetry data analyzed by Fortinet show that the campaign's primary
focus is on Saudi Arabia, Jordan, Qatar, and the United Arab Emirates. The
activity has not been tied to a known threat actor or group.
By using a malicious kernel mode driver, the idea is to subvert or disable
security mechanisms and gain entrenched access to the targeted host.
Such drivers run within the kernel memory and can, therefore, perform any
operation, including altering critical security mechanisms and running arbitrary
code with the highest privileges.
In other words, it offers a stealthy way to infiltrate deeper into the targeted
system, maintain persistence, and execute additional payloads or commands as
part of the threat actor's multi-stage attack.
_small.jpg)
A key security measure to mitigate against malicious drivers is Driver Signature
Enforcement, which ensures that only drivers signed by Microsoft can be loaded
on the system. The tech giant also maintains driver block rules to protect
against known vulnerable drivers.
WinTapix.sys, on the other hand, comes with an invalid signature, indicating
that the threat actor will have to first load a legitimate but vulnerable driver
in order to launch WINTAPIX.
But once it's loaded in the kernel,
WinTapix.sys is configured to inject an embedded shellcode into an appropriate
user mode process that, in turn, executes an encrypted .NET payload that's
specifically designed to target Microsoft Internet Information Services (IIS)
servers.
WINTAPIX, besides embedding the shellcode created using the open source Donut
project, establishes persistence by means of Windows Registry modifications that
allows it to be loaded even when the machine is booted in Safe Mode.
For its part, the .NET malware is equipped with backdoor and proxy features to
execute commands, carry out file download and upload, and function as a proxy to
pass data between two communication endpoints.
"Since Iranian threat actors are known to exploit Exchange servers to deploy
additional malware, it is also possible that this driver has been employed
alongside Exchange attacks," the researchers said.
"To that point, the compilation time of the drivers is also aligned with times
when Iranian threat actors were exploiting Exchange server vulnerabilities."
The development comes as the ALPHV (aka BlackCat or Noberus) ransomware group
has been observed taking advantage of a malicious signed driver to impair
security defenses and escape detection for extended periods of time.
The driver in question, ktgn.sys, is an updated version of POORTRY that's signed
using a stolen or leaked cross-signing certificate, cybersecurity firm Trend
Micro said in a report.
POORTRY is the name assigned to a Windows kernel driver that comes with
capabilities to terminate security software. Late last year, it was disclosed as
used by ransomware gangs and a threat actor known as UNC3944 (aka Roasted
0ktapus and Scattered Spider).
"Malicious actors that are actively seeking high-privilege access to the Windows
operating system use techniques that attempt to combat the increased protection
on users and processes via endpoint protection platform (EPP) and endpoint
detection and response (EDR) technologies," Trend Micro said.
"These malicious actors also tend to possess enough financial resources to
either purchase rootkits from underground sources or to buy code-signing
certificates to build a rootkit."
Meet 'Jack' from Romania! Mastermind Behind Golden Chickens Malware
20.5.23 Virus
The Hacker News
_small.png)
The identity of the second threat actor behind the Golden Chickens malware has
been uncovered courtesy of a fatal operational security blunder, cybersecurity
firm eSentire said.
The individual in question, who lives in Bucharest, Romania, has been given the
codename Jack. He is one of the two criminals operating an account on the
Russian-language Exploit.in forum under the name "badbullzvenom," the other
being "Chuck from Montreal."
eSentire characterized Jack as the true mastermind behind Golden Chickens.
Evidence unearthed by the Canadian company shows that he is also listed as the
owner of a vegetable and fruit import and export business.
"Like 'Chuck from Montreal,' 'Jack' uses multiple aliases for the underground
forums, social media, and Jabber accounts, and he too has gone to great lengths
to disguise himself," eSentire researchers Joe Stewart and Keegan Keplinger
said.
"'Jack' has taken great pains to obfuscate the Golden Chickens malware, trying
to make it undetectable by most [antivirus] companies, and strictly allowing
only a small number of customers to buy access to the Golden Chickens MaaS."
Golden Chickens (aka More_eggs) is a malware suite used by financially-motivated
cybercrime actors such as Cobalt Group and FIN6. The threat actors behind the
malware, also known as Venom Spider, operate under a malware-as-a-service (MaaS)
model.
The JavaScript malware is distributed via phishing campaigns and comes with
several components to harvest financial information, perform lateral movement,
and even drop a ransomware plugin for PureLocker called TerraCrypt.
Jack's online activities, according to eSentire, go all the way back to 2008,
when he was just 15 years old and signed up for various cybercrime forums as a
novice member. All his aliases are being collectively tracked as LUCKY.
The investigation, in putting together his digital trail, traces Jack's
progression from a teenager interested in building malicious programs to a
longtime hacker involved in developing password stealers, crypters, and
More_eggs.

Some of the earliest malware tools developed by Jack in 2008 consisted of Voyer,
which is capable of harvesting a user's Yahoo instant messages, and an
information stealer christened FlyCatcher that can record keystrokes.
A year later, Jack released a new password stealer dubbed CON that's designed to
siphon credentials from different web browsers, VPN, and FTP applications as
well as now-defunct messaging apps like MSN Messenger and Yahoo! Messenger.
Jack, later that same year, began advertising a crypter referred to as GHOST to
help other actors encrypt and obfuscate malware with the goal of evading
detection. The unexpected demise of his father in a car accident is believed to
have caused him to pause development of the tool in 2010.
Fast forward to 2012, Jack began to gain a reputation in the cybercriminal
community as a scammer for failing to provide adequate support to customers
purchasing the product from him.
He also cited "big life problems" in a forum post on April 27, 2012, stating he
is contemplating moving to Pakistan to work for the government as a security
specialist and that one among his crypter customers "works at pakistan guv"
[read government].
It's not immediately clear if Jack ended up going to Pakistan, but eSentire said
it spotted tactical overlaps between a 2019 campaign conducted by a Pakistani
threat actor known as SideCopy and Jack's VenomLNK malware, which functions as
the initial access vector for the More_eggs backdoor.
Jack is suspected to have crossed paths with "Chuck from Montreal" sometime
between late 2012 and October 4, 2013, the date on which a message was posted
from Chuck's badbullz account on the Lampeduza forum containing contact
information – a Jabber address – associated with LUCKY.
It's speculated that Jack brokered a deal with Chuck that would allow him to
post under Chuck's aliases "badbullz" and "badbullzvenom" on various underground
forums as a way to get around his notoriety as a ripper.
Lending credence to this hypothesis is the fact that one of LUCKY's new tools, a
kit for building macros called MULTIPLIER, was released in 2015 via the
badbullzvenom account, while the threat actor behind the LUCKY account ceased
posting through that handle.
"By using the badbullzvenom and badbullz accounts, and unbeknownst to forum
members, he is essentially starting with a clean slate, and he can continue to
build his credibility under the account aliases: badbullz and badbullzvenom,"
the researcher explained.
Subsequently in 2017, badbullzvenom (aka LUCKY) released a separate tool called
VenomKit, which has since evolved into the Golden Chickens MaaS. The malware's
ability to evade detection also caught the attention of Cobalt Group, a
Russia-based cybercrime gang that leveraged it to deploy Cobalt Strike in
attacks aimed at financial entities.
Two years later, another financially motivated threat actor labeled FIN6 (aka
ITG08 or Skeleton Spider) was observed using the Golden Chickens service to
anchor its intrusions targeting point-of-sale (POS) machines used by retailers
in Europe and the U.S.
The cybersecurity firm said it also found the identities of his wife, mother,
and two sisters. He and his wife are said to reside in an upscale part of
Bucharest, with his wife's social media accounts documenting their trips to
cities like London, Paris, and Milan. The photos further show them wearing
designer clothing and accessories.
"The threat actor who went by the alias LUCKY and who also shares the badbullz
and badbullzvenom accounts with the Montreal-based cybercriminal 'Chuck,' made
his fatal mistake when he used the Jabber account," the researchers said.
Developer Alert: NPM Packages for Node.js Hiding Dangerous TurkoRat Malware
19.5.23 Virus
The Hacker News
Two malicious packages discovered in the npm package
repository have been found to conceal an open source information stealer malware
called TurkoRat.
The packages – named nodejs-encrypt-agent and nodejs-cookie-proxy-agent – were
collectively downloaded approximately 1,200 times and were available for more
than two months before they were identified and taken down.
ReversingLabs, which broke down the details of the campaign, described TurkoRat
as an information stealer capable of harvesting sensitive information such as
login credentials, website cookies, and data from cryptocurrency wallets.
While nodejs-encrypt-agent came fitted with the malware inside,
nodejs-cookie-proxy-agent was found to disguise the trojan as a dependency under
the name axios-proxy.
nodejs-encrypt-agent was also engineered to masquerade as another legitimate npm
module known as agent-base, which has been downloaded over 25 million times to
date.
The list of the rogue packages and their associated versions are listed below -
nodejs-encrypt-agent (versions 6.0.2, 6.0.3, 6.0.4, and 6.0.5)
nodejs-cookie-proxy-agent (versions 1.1.0, 1.2.0, 1.2.1, 1.2.2, 1.2.3, and
1.2.4), and
axios-proxy (versions 1.7.3, 1.7.4, 1.7.7, 1.7.9, 1.8.9, and
1.9.9)
"TurkoRat is just one of many open source malware families that are
offered for 'testing' purposes, but can readily be downloaded and modified for
malicious use, as well," Lucija Valentić, threat researcher at ReversingLabs,
said.
The findings once again underscore the ongoing risk of threat actors
orchestrating supply chain attacks via open source packages and baiting
developers into downloading potentially untrusted code.
"Development organizations need to scrutinize the features and behaviors of the
open source, third-party and commercial code they are relying on in order to
track dependencies and detect potential malicious payloads in them," Valentić
said.
The growing use of malicious npm packages fits in with a broader pattern of
surging attacker interest in open source software supply chains, not to mention
highlighting the increasing sophistication of threat actors.
Even more worryingly, researchers from Checkmarx published new research this
month that showed how threat actors could impersonate authentic npm packages by
"using lowercase letters to mimic uppercase letters in the original package
names" (e.g., memoryStorageDriver vs memorystoragedriver).

"This malicious package impersonation takes the traditional 'Typosquatting,'
attack method to a new level, where attackers register package names that
consist of the exact same letters as the legitimate ones, with the only
difference being capitalization," researchers Teach Zornstein and Yehuda Gelb
said.
"This makes it even harder for users to detect the deception since it can be
easy to overlook the subtle differences in capitalization."
The supply chain security company found that 1,900 out of 3,815 packages with
capital letters in their titles could have been at risk of copycat attacks if
not for a fix pushed by the npm maintainers to address the problem, which,
Checkmarx said, has existed since December 2017.
The disclosure also follows another advisory from Check Point, which identified
three malicious extensions hosted on the VS Code extensions marketplace. They
have been purged as of May 14, 2023.
The add-ons, named prettiest java, Darcula Dark, and python-vscode, were
cumulatively downloaded over 46,000 times and incorporated features that allowed
the threat actors to steal credentials, system information, and establish a
remote shell on the victim's machine.
It's not just npm and VS Code marketplace, for a similar set of rogue libraries
have been unearthed from the Python Package Index (PyPI) software repository as
well.
Some of these packages were designed to distribute a cryptocurrency clipper
malware dubbed KEKW, while other typosquatted versions of the popular flask
framework included backdoor functions to receive commands from a remote server.
Another Python package uncovered by Israeli company Phylum this week was found
to contain a malicious dependency that harbored an encrypted payload to grab
Discord tokens and steal clipboard content in order to hijack cryptocurrency
transactions.
The package, referred to as chatgpt-api by its developer Patrick Pogoda and
accessible through GitHub, delivered on the functionality it advertised (i.e.,
interacting with OpenAI's ChatGPT tool) in an attempt to complete the ruse. The
repository is still available as of writing.
"For now this actor appears to be preying on the recent explosive rise in
popularity of [Large Language Models] with this chatgpt-api package," Phylum
said, adding the threat actor likely has an automated mechanism to upload new
iterations of the malicious dependency every time it's taken down and "maintain
a persistent infection."
Searching for AI Tools? Watch Out for Rogue Sites Distributing RedLine Malware
19.5.23 Virus
The Hacker News

Malicious Google Search ads for generative AI services like OpenAI ChatGPT and
Midjourney are being used to direct users to sketchy websites as part of a
BATLOADER campaign designed to deliver RedLine Stealer malware.
"Both AI services are extremely popular but lack first-party standalone apps
(i.e., users interface with ChatGPT via their web interface while Midjourney
uses Discord)," eSentire said in an analysis.
"This vacuum has been exploited by threat actors looking to drive AI app-seekers
to imposter web pages promoting fake apps."
BATLOADER is a loader malware that's propagated via drive-by downloads where
users searching for certain keywords on search engines are displayed bogus ads
that, when clicked, redirect them to rogue landing pages hosting malware.
The installer file, per eSentire, is rigged with an executable file (ChatGPT.exe
or midjourney.exe) and a PowerShell script (Chat.ps1 or Chat-Ready.ps1) that
downloads and loads RedLine Stealer from a remote server.
Once the installation is complete, the binary makes use of Microsoft Edge
WebView2 to load chat.openai[.]com or www.midjourney[.]com – the legitimate
ChatGPT and Midjourney URLs – in a pop-up window so as to not raise any red
flags.

The adversary's use of ChatGPT and Midjourney-themed lures to serve malicious
ads and ultimately drop the RedLine Stealer malware was also highlighted last
week by Trend Micro.

This is not the first time the operators behind BATLOADER have capitalized on
the AI craze to distribute malware. In March 2023, eSentire detailed a similar
set of attacks that leveraged ChatGPT lures to deploy Vidar Stealer and Ursnif.
The cybersecurity company further pointed out the abuse of Google Search ads has
fallen off from their early 2023 peak, suggesting that the tech giant is taking
active steps to curtail its exploitation.
The findings come weeks after Securonix uncovered a phishing campaign dubbed
OCX#HARVESTER that targeted the cryptocurrency sector between December 2022 and
March 2023 with More_eggs (aka Golden Chickens), a JavaScript downloader that's
used to serve additional payloads.
eSentire, in January, traced the identity of one of the key operators of the
malware-as-a-service (MaaS) to an individual located in Montreal, Canada. The
second threat actor associated with the group has since been identified as a
Romanian national who goes by the alias Jack.
CopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules
16.5.23 Virus
The Hacker News
The threat actors behind the CopperStealer malware
resurfaced with two new campaigns in March and April 2023 that are designed to
deliver two novel payloads dubbed CopperStealth and CopperPhish.
Trend Micro is tracking the financially motivated group under the name Water
Orthrus. The adversary is also assessed to be behind another campaign known as
Scranos, which was detailed by Bitdefender in 2019.
Active since at least 2021, Water Orthrus has a track record of leveraging
pay-per-install (PPI) networks to redirect victims landing on cracked software
download sites to drop an information stealer codenamed CopperStealer.
Another campaign spotted in August 2022 entailed the use of CopperStealer to
distribute Chromium-based web browser extensions that are capable of performing
unauthorized transactions and transferring cryptocurrency from victims' wallets
to ones under attackers' control.
The latest attack sequences documented by Trend Micro don't mark much of a
deviation, propagating CopperStealth by packaging it as installers for free
tools on Chinese software-sharing websites.
"CopperStealth's infection chain involves dropping and loading a rootkit, which
later injects its payload into explorer.exe and another system process,"
security researchers Jaromir Horejsi and Joseph C Chen said in a technical
report.
"These payloads are responsible for downloading and running additional tasks.
The rootkit also blocks access to blocklisted registry keys and prevents certain
executables and drivers from running."
The driver denylist contains byte sequences pertaining to Chinese security
software companies like Huorong, Kingsoft, and Qihoo 360.
CopperStealth also incorporates a task module that enables it to call out to a
remote server and retrieve the command to be executed on the infected machine,
equipping the malware to drop more payloads.
File Sharing Websites Act as Conduit for CopperPhish Phishing Kit#
The
CopperPhish campaign, detected worldwide in April 2023, takes advantage of an
analogous process to deploy the malware via PPI networks behind free anonymous
file-sharing websites.
"Visitors will be redirected to a download page designed by the PPI network
after clicking on its advertisements, which pretended to be a download link,"
the researchers said. "The downloaded file is PrivateLoader, which downloads and
runs many different malware."
The downloader service, which is also offered on a PPI basis, is then used to
retrieve and launch CopperPhish, a phishing kit that's responsible for
harvesting credit card information.
It achieves this by "starting a rundll32 process and injecting a simple program
with a browser window (written in Visual Basic) in it," which loads a phishing
page urging victims to scan a QR code in order to verify their identity and
enter a confirmation code to "restore your device's network."
"The window has no controls that can be used to minimize or close it," the
researchers explained. "The victim could close the browser's process in Task
Manager or Process Explorer, but they would also need to terminate the main
payload process, otherwise the browser process will happen again due to the
persistence thread."
Once the sensitive details are entered in the page, the CopperPhish malware
displays the message "the identity verification has passed" alongside a
confirmation code that the victim can enter on the aforementioned screen.
Providing the correct confirmation code also causes the malware to uninstall
itself and delete all the dropped phishing files from the machine.
"The credential verification and confirmation code are two useful features that
make this phishing kit more successful, as the victim cannot simply close the
window or enter fake information just to get rid of the window," the researchers
said.
The attribution to Water Orthrus is based on the fact that both CopperStealth
and CopperPhish share similar source code characteristics as that of
CopperStealer, raising the possibility that all three strains may have been
developed by the same author.
The disparate objectives of the campaigns represent the evolution of the threat
actor's tactics, indicating an attempt to add new capabilities to its arsenal
and expand its financial horizons.
The findings come as malicious Google ads are being used to entice users into
downloading fake installers for AI tools like Midjourney and OpenAI's ChatGPT
that ultimately drop stealers such as Vidar and RedLine.
They also follow the discovery of a new traffic-monetizing service called
TrafficStealer that leverages misconfigurations containers to redirect traffic
to websites and generate fake ad clicks as part of an illicit money-making
scheme.
CLR SqlShell Malware Targets MS SQL Servers for Crypto Mining and Ransomware
15.5.23 Virus
The Hacker News

Poorly managed Microsoft SQL (MS SQL) servers are the target of a new campaign
that's designed to propagate a category of malware called CLR SqlShell that
ultimately facilitates the deployment of cryptocurrency miners and ransomware.
"Similar to web shell, which can be installed on web servers, SqlShell is a
malware strain that supports various features after being installed on an MS SQL
server, such as executing commands from threat actors and carrying out all sorts
of malicious behavior," AhnLab Security Emergency response Center (ASEC) said in
a report published last week.
A stored procedure is a subroutine that contains a set of Structured Query
Language (SQL) statements for use across multiple programs in a relational
database management system (RDBMS).
CLR (short for common language runtime) stored procedures – available in SQL
Server 2005 and later – refer to stored procedures that are written in a .NET
language such as C# or Visual Basic.
The attack method discovered by the South Korean cybersecurity firm entails the
use of CLR stored procedure to install the malware in MS SQL servers using the
xp_cmdshell command, which spawns a Windows command shell and passes an
instruction as input for execution.

Some of the techniques employed by threat actors, including those associated
with LemonDuck, MyKings (aka DarkCloud or Smominru), and Vollgar, concern the
exploitation of internet-exposed MS SQL servers via brute-force and dictionary
attacks to run xp_cmdshell commands and OLE stored procedures and execute
malware.
The use of CLR stored procedures is the latest addition to this list, with
attackers taking advantage of SqlShell routines to download next-stage payloads
such as Metasploit and cryptocurrency miners like MrbMiner, MyKings, and
LoveMiner.
What's more, SqlShells named SqlHelper, CLRSQL, and CLR_module
have been used by different adversaries to escalate privileges on compromised
servers and launch ransomware, proxyware, and incorporate capabilities to carry
out reconnaissance efforts in targeted networks.
"SqlShell can install additional malware such as backdoors, coin miners, and
proxyware, or it can execute malicious commands received from threat actors in a
way similar to WebShell," ASEC said.
Researchers Uncover Powerful Backdoor and Custom Implant in Year-Long Cyber
Campaign
15.5.23
Virus The Hacker News
Government, aviation, education, and telecom sectors located in South and
Southeast Asia have come under the radar of a new hacking group as part of a
highly-targeted campaign that commenced in mid-2022 and continued into the first
quarter of 2023.
Symantec, by Broadcom Software, is tracking the activity under its insect-themed
moniker Lancefly, with the attacks making use of a "powerful" backdoor called
Merdoor.
Evidence gathered so far points to the custom implant being utilized as far back
as 2018. The ultimate goal of the campaign, based on the tools and the
victimology pattern, is assessed to be intelligence gathering.
"The backdoor is used very selectively, appearing on just a handful of networks
and a small number of machines over the years, with its use appearing to be
highly targeted," Symantec said in an analysis shared with The Hacker News.
"The attackers in this campaign also have access to an updated version of the
ZXShell rootkit."
While the exact initial intrusion vector used is currently not clear, it's
suspected to have involved the use of phishing lures, SSH brute-forcing, or the
exploitation of internet-exposed servers.
The attack chains ultimately lead to the deployment of ZXShell and Merdoor, a
fully-featured malware that can communicate with an actor-controlled server for
further commands and log keystrokes.
ZXShell, first documented by Cisco in October 2014, is a rootkit that comes with
various features to harvest sensitive data from infected hosts. The use of
ZXShell has been linked to various Chinese actors like APT17 (Aurora Panda) and
APT27 (aka Budworm or Emissary Panda) in the past.
"The source code of this rootkit is publicly available so it may be used by
multiple different groups," Symantec said. "The new version of the rootkit used
by Lancefly appears to be smaller in size, while it also has additional
functions and targets additional antivirus software to disable."
Another Chinese link comes from the fact that the ZXShell rootkit is signed by
the certificate "Wemade Entertainment Co. Ltd," which was previously reported by
Mandiant in August 2019 to be associated with APT41 (aka Winnti).
Lancefly's
intrusions have also been identified as employing PlugX and its successor
ShadowPad, the latter of which is a modular malware platform privately shared
among multiple Chinese state-sponsored actors since 2015.
That said, it's also known that certificate and tool sharing is prevalent among
Chinese state-sponsored groups, making attribution to a specific known attack
crew difficult.
"While the Merdoor backdoor appears to have been in existence for several years,
it appears to only have been used in a small number of attacks in that time
period," Symantec noted. "This prudent use of the tool may indicate a desire by
Lancefly to keep its activity under the radar."
XWorm Malware Exploits Follina Vulnerability in New Wave of Attacks
13.5.23 Virus
The Hacker News

Cybersecurity researchers have discovered an ongoing phishing campaign that
makes use of a unique attack chain to deliver the XWorm malware on targeted
systems.
Securonix, which is tracking the activity cluster under the name MEME#4CHAN,
said some of the attacks have primarily targeted manufacturing firms and
healthcare clinics located in Germany.
"The attack campaign has been leveraging rather unusual meme-filled PowerShell
code, followed by a heavily obfuscated XWorm payload to infect its victims,"
security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a new
analysis shared with The Hacker News.
The report builds on recent findings from Elastic Security Labs, which revealed
the threat actor's reservation-themed lures to deceive victims into opening
malicious documents capable of delivering XWorm and Agent Tesla payloads.
The attacks begin with phishing attacks to distribute decoy Microsoft Word
documents that, instead of using macros, weaponize the Follina vulnerability
(CVE-2022-30190, CVSS score: 7.8) to drop an obfuscated PowerShell script.
From there, the threat actors abuse the PowerShell script to bypass Antimalware
Scan Interface (AMSI), disable Microsoft Defender, establish persistence, and
ultimately launch the .NET binary containing XWorm.

Interestingly, one of the variables in the PowerShell script is named
"$CHOTAbheem," which is likely a reference to Chhota Bheem, an Indian animated
comedy adventure television series.
"Based on a quick check, it appears that the individual or group responsible for
the attack could have a Middle Eastern/Indian background, although the final
attribution has not yet been confirmed," the researchers told The Hacker News,
pointing out that such keywords could also be used as a cover.
XWorm is a commodity malware that's advertised for sale on underground forums
and comes with a wide range of features that allows it to siphon sensitive
information from infected hosts.
The malware is also a Swiss Army knife in that it can perform clipper, DDoS, and
ransomware operations, spread via USB, and drop additional malware.
The exact origins of the threat actor are currently unclear, although Securonix
said the attack methodology shares artifacts similar to that of TA558, which has
been observed striking the hospitality industry in the past.
"Though phishing emails rarely use Microsoft Office documents since Microsoft
made the decision to disable macros by default, today we're seeing proof that it
is still important to be vigilant about malicious document files, especially in
this case where there was no VBscript execution from macros," the researchers
said.
New Stealthy Variant of Linux Backdoor BPFDoor Emerges from the Shadows
13.5.23 Virus
The Hacker News
A previously undocumented and mostly undetected variant
of a Linux backdoor called BPFDoor has been spotted in the wild, cybersecurity
firm Deep Instinct said in a technical report published this week.
"BPFDoor retains its reputation as an extremely stealthy and difficult-to-detect
malware with this latest iteration," security researchers Shaul
Vilkomir-Preisman and Eliran Nissan said.
BPFDoor (aka JustForFun), first documented by PwC and Elastic Security Labs in
May 2022, is a passive Linux backdoor associated with a Chinese threat actor
called Red Menshen (aka DecisiveArchitect or Red Dev 18), which is known to
single out telecom providers across the Middle East and Asia since at least
2021.
The malware is specifically geared towards establishing persistent remote access
to compromised target environments for extended periods of time, with evidence
pointing to the hacking crew operating the backdoor undetected for years.
BPFDoor gets its name from the use of Berkeley Packet Filters (BPF) – a
technology that makes it possible to analyze and filter network traffic in Linux
systems – for network communications and process incoming commands.
In doing so, threat actors can penetrate a victim's system and execute arbitrary
code without being detected by firewalls, while simultaneously filtering out
unnecessary data.
Deep Instinct's findings come from a BPFDoor artifact that was uploaded to
VirusTotal on February 8, 2023. As of writing, only three security vendors have
flagged the ELF binary as malicious.
One of the key characteristics that make the new version of BPFDoor even more
evasive is its removal of many hard-coded indicators and instead incorporating a
static library for encryption (libtomcrypt) and a reverse shell for
command-and-control (C2) communication.

Upon launch, BPFDoor is configured to ignore various operating system signals to
prevent it from being terminated. It then allocates a memory buffer and creates
a special packet sniffing socket that monitors for incoming traffic with a
specific Magic Byte sequence by hooking a BPF filter onto the raw socket.
"When BPFdoor finds a packet containing its Magic Bytes in the filtered traffic,
it will treat it as a message from its operator and will parse out two fields
and will again fork itself," the researchers explained.
"The parent process will continue and monitor the filtered traffic coming
through the socket while the child will treat the previously parsed fields as a
command-and-control IP-Port combination and will attempt to contact it."
In the final stage, BPFDoor sets up an encrypted reverse shell session with the
C2 server and awaits further instructions to be executed on the compromised
machine.
The fact that BPFDoor has remained hidden for a long duration speaks to its
sophistication, what with threat actors increasingly developing malware
targeting Linux systems owing to their prevalence in enterprise and cloud
environments.
The development comes as Google announced a new extended Berkeley Packet Filter
(eBPF) fuzzing framework called Buzzer to help harden the Linux kernel and
ensure that sandboxed programs that run in a privileged context are valid and
safe.
The tech giant further said the testing method led to the discovery of a
security flaw (CVE-2023-2163) that could be exploited to achieve arbitrary
reading and writing of kernel memory.
Sophisticated DownEx Malware Campaign Targeting Central Asian Governments
12.5.23 Virus
The Hacker News

Government organizations in Central Asia are the target of a sophisticated
espionage campaign that leverages a previously undocumented strain of malware
dubbed DownEx.
Bitdefender, in a report shared with The Hacker News, said the activity remains
active, with evidence likely pointing to the involvement of Russia-based threat
actors.
The Romanian cybersecurity firm said it first detected the malware in a highly
targeted attack aimed at foreign government institutions in Kazakhstan in late
2022. Subsequently, another attack was observed in Afghanistan.
The use of a diplomat-themed lure document and the campaign's focus on data
exfiltration suggests the involvement of a state-sponsored group, although the
exact identity of the hacking outfit remains indeterminate at this stage.
The initial intrusion vector for the campaign is suspected to be a
spear-phishing email bearing a booby-trapped payload, which is a loader
executable that masquerades as a Microsoft Word file.
Opening the attachment leads to the extraction of two files, including a decoy
document that's displayed to the victim while a malicious HTML application
(.HTA) with embedded VBScript code runs in the background.
The HTA file, for its part, is designed to establish contact with a remote
command-and-control (C2) server to retrieve a next-stage payload. While the
exact nature of the malware is not unknown, it's said to be a backdoor to
establish persistence.

The attacks are also notable for employing a variety of custom tools for
carrying out post-exploitation activities. This includes -
Two C/C++-based binaries (wnet.exe and utility.exe) to enumerate all the
resources on a network,
A Python script (help.py) to establish an infinite
communication loop with the C2 server and receive instructions to steal files
with certain extensions, delete files created by other malware, and capture
screenshots, and
A C++-based malware (diagsvc.exe aka DownEx) that's chiefly
designed to exfiltrate files to the C2 server
Two other variants of DownEx
have also been earthed, the first of which executes an intermediate VBScript to
harvest and transmit the files in the form of a ZIP archive.
The other version, which is downloaded via a VBE script (slmgr.vbe) from a
remote server, eschews C++ for VBScript, but retains the same functionality as
the former.
"This is a fileless attack – the DownEx script is executed in memory and never
touches the disk," Bitdefender said. "This attack highlights the sophistication
of a modern cyberattack. Cybercriminals are finding new methods for making their
attacks more reliable."
SideCopy Using Action RAT and AllaKore RAT to infiltrate Indian Organizations
8.5.23 Virus
The Hacker News
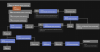
The suspected Pakistan-aligned threat actor known as SideCopy has been observed
leveraging themes related to the Indian military research organization as part
of an ongoing phishing campaign.
This involves using a ZIP archive lure pertaining to India's Defence Research
and Development Organization (DRDO) to deliver a malicious payload capable of
harvesting sensitive information, Fortinet FortiGuard Labs said in a new report.
The cyber espionage group, with activity dating back to at least 2019, targets
entities that align with Pakistan government interests. It's believed to share
overlaps with another Pakistani hacking crew called Transparent Tribe.
SideCopy's use of DRDO-related decoys for malware distribution was previously
flagged by Cyble and Chinese cybersecurity firm QiAnXin in March 2023, and again
by Team Cymru last month.
Interestingly, the same attack chains have been observed to load and execute
Action RAT as well as an open source remote access trojan known as AllaKore RAT.
The latest infection sequence documented by Fortinet is no different, leading to
the deployment of an unspecified strain of RAT that's capable of communicating
with a remote server and launching additional payloads.
The development is an indication that SideCopy has continued to carry out
spear-phishing email attacks that use Indian government and defense
forces-related social engineering lures to drop a wide range of malware.
SideCopy Hackers
Source: Team Cymru
Further analysis of the Action RAT
command-and-control (C2) infrastructure by Team Cymru has identified outbound
connections from one of the C2 server IP addresses to another address
66.219.22[.]252, which is geolocated in Pakistan.
The cybersecurity company also said it observed "communications sourced from 17
distinct IPs assigned to Pakistani mobile providers and four Proton VPN nodes,"
noting inbound connections to the IP address from IP addresses assigned to
Indian ISPs.
In all, as many as 18 distinct victims in India have been detected as connecting
to C2 servers associated with Action RAT and 236 unique victims, again located
in India, connecting to C2 servers associated with AllaKore RAT.
The latest findings lend credence to SideCopy's Pakistan links, not to mention
underscore the fact that the campaign has been successful in targeting Indian
users.
"The Action RAT infrastructure, connected to SideCopy, is managed by users
accessing the Internet from Pakistan," Team Cymru said. "Victim activity
predated the public reporting of this campaign, in some cases by several
months."
CERT-UA Warns of SmokeLoader and RoarBAT Malware Attacks Against Ukraine
8.5.23 Virus
The Hacker News

An ongoing phishing campaign with invoice-themed lures is being used to
distribute the SmokeLoader malware in the form of a polyglot file, according to
the Computer Emergency Response Team of Ukraine (CERT-UA).
The emails, per the agency, are sent using compromised accounts and come with a
ZIP archive that, in reality, is a polyglot file containing a decoy document and
a JavaScript file.
The JavaScript code is then used to launch an executable that paves for the
execution of the SmokeLoader malware. SmokeLoader, first detected in 2011, is a
loader whose main objective is to download or load a stealthier or more
effective malware onto infected systems.
CERT-UA attributed the activity to a threat actor it calls UAC-0006 and
characterized it as a financially motivated operation carried out with the goal
of stealing credentials and making unauthorized fund transfers.
In a related advisory, Ukraine's cybersecurity authority also revealed details
of destructive attacks orchestrated by a group known as UAC-0165 against public
sector organizations.
The attack, which targeted an unnamed state organization, entailed the use of a
new batch script-based wiper malware called RoarBAT that performs a recursive
search for files with a specific list of extensions and irrevocably deletes them
using the legitimate WinRAR utility.
This, in turn, was achieved by archiving the identified files using the "-df"
command-line option and subsequently purging the created archives. The batch
script was executed by means of a scheduled task.

Simultaneously, Linux systems were compromised using a bash script that
leveraged the dd utility to overwrite files with zero bytes, effectively
avoiding detection by security software.
"It was found that the operability of electronic computers (server equipment,
automated user workplaces, data storage systems) was impaired as a result of the
destructive impact carried out with the use of appropriate software," CERT-UA
said.
"Access to the ICS target of the attack is allegedly obtained by connecting to a
VPN using compromised authentication data. The successful implementation of the
attack was facilitated by the lack of multi-factor authentication when making
remote connections to VPN."
The agency further attributed UAC-0165 with moderate confidence to the notorious
Sandworm group (aka FROZENBARENTS, Seashell Blizzard, or Voodoo Bear), which has
a history of unleashing wiper attacks since the start of the Russo-Ukrainian war
last year.
The link to Sandworm stems from significant overlaps with another destructive
attack that hit the Ukrainian state news agency Ukrinform in January 2023, which
was tied to the adversarial collective.
The alerts come a week after CERT-UA cautioned of phishing attacks carried out
by the Russian state-sponsored group APT28 targeting government entities in the
country with fake Window update notifications.
Hackers Targeting Italian Corporate Banking Clients with New Web-Inject Toolkit
DrIBAN
5.5.23 Virus
The Hacker News
Italian corporate banking clients are the target of an
ongoing financial fraud campaign that has been leveraging a new web-inject
toolkit called drIBAN since at least 2019.
"The main goal of drIBAN fraud operations is to infect Windows workstations
inside corporate environments trying to alter legitimate banking transfers
performed by the victims by changing the beneficiary and transferring money to
an illegitimate bank account," Cleafy researchers Federico Valentini and
Alessandro Strino said.
The bank accounts, per the Italian cybersecurity firm, are either controlled by
the threat actors themselves or their affiliates, who are then tasked with
laundering the stolen funds.
The use of web injects is a time-tested tactic that makes it possible for
malware to inject custom scripts on the client side by means of a
man-in-the-browser (MitB) attack and intercept traffic to and from the server.
The fraudulent transactions are often realized by means of a technique called
Automated Transfer System (ATS) that's capable of bypassing anti-fraud systems
put in place by banks and initiating unauthorized wire transfers from a victim's
own computer.
Over the years, the operators behind drIBAN have gotten more savvy at avoiding
detection and developing effective social engineering strategies, in addition to
establishing a foothold for long periods in corporate bank networks.
Cleafy said 2021 was the year when the classic "banking trojan" operation
evolved into an advanced persistent threat. Furthermore, there are indications
that the activity cluster overlaps with a 2018 campaign mounted by an actor
tracked by Proofpoint as TA554 targeting users in Canada, Italy, and the U.K.

The attack chain begins with a certified email (or PEC email) in an attempt to
lull victims into a false sense of security. These phishing emails come bearing
an executable file that acts as a downloader for a malware called sLoad (aka
Starslord loader).
A PowerShell loader, sLoad is a reconnaissance tool that collects and
exfiltrates information from the compromised host, with the purpose of assessing
the target and dropping a more significant payload like Ramnit if the target is
deemed profitable.
"This 'enrichment phase' could continue for days or weeks, depending on the
number of infected machines," Cleafy noted. "Additional data will be exfiltrated
to make the resulting botnet more and more solid and consistent."
sLoad also leverages living-off-the-land (LotL) techniques by abusing legitimate
Windows tools like PowerShell and BITSAdmin as part of its evasion mechanisms.
Another characteristic of the malware is its ability to check against a
predefined list of corporate banking institutions to determine if the hacked
workstation is one among the targets, and if so, proceed with the infection.
"All the bots that successfully pass those steps will be selected by botnet
operators and considered as 'new candidates' for banking fraud operations moving
forward to the next stage, where Ramnit, one of the most advanced banking
trojans, will be installed," the researchers said.
Meta Takes Down Malware Campaign That Used ChatGPT as a Lure to Steal Accounts
4.5.23 Virus
The Hacker News
Meta said it took steps to take down more than 1,000 malicious URLs from being
shared across its services that were found to leverage OpenAI's ChatGPT as a
lure to propagate about 10 malware families since March 2023.
The development comes against the backdrop of fake ChatGPT web browser
extensions being increasingly used to steal users' Facebook account credentials
with an aim to run unauthorized ads from hijacked business accounts.
"Threat actors create malicious browser extensions available in official web
stores that claim to offer ChatGPT-based tools," Meta said. "They would then
promote these malicious extensions on social media and through sponsored search
results to trick people into downloading malware."
The social media giant said it has blocked several iterations of a multi-pronged
malware campaign dubbed Ducktail over the years, adding it issued a cease and
desist letter to individuals behind the operation who are located in Vietnam.
Trend Micro, in a series of tweets last week, detailed an information stealer
that's disguised as a Windows desktop client for ChatGPT to extract passwords,
session cookies, and history from Chromium-powered browsers. The company said
the malware shares similarities with Ducktail.
Besides ChatGPT, threat actors have also been observed shifting to other
"hot-button issues and popular topics" like Google Bard, TikTok marketing tools,
pirated software and movies, and Windows utilities to dupe people into clicking
on bogus links.
"These changes are likely an attempt by threat actors to ensure that any one
service has only limited visibility into the entire operation," Guy Rosen, chief
information security officer at Meta, said.

The attack chains are primarily engineered to target the personal accounts of
users who manage or are connected to business pages and advertising accounts on
Facebook.
Besides using social media for propagating the ChatGPT-themed malicious URLs,
the malware is hosted on a variety of legitimate services such as Buy Me a
Coffee, Discord, Dropbox, Google Drive, iCloud, MediaFire, Mega, Microsoft
OneDrive, and Trello.
Ducktail isn't the only stealer malware detected in the wild, for Meta disclosed
that it uncovered another novel strain dubbed NodeStealer that's capable of
plundering cookies and passwords from web browsers to ultimately compromise
Facebook, Gmail, and Outlook accounts.
The malware is assessed to be of Vietnamese origin, with Meta noting that it
"took action to disrupt it and help people who may have been targeted to recover
their accounts" within two weeks of it being deployed in late January 2023.
Samples analyzed by the Menlo Park-based company show that NodeStealer binary is
distributed via Windows executables disguised as PDF and XLSX files with
filenames relating to marketing and monthly budgets. The files, when opened,
deliver JavaScript code that's designed to exfiltrate sensitive data from
Chromium-based browsers.
NodeStealer gets its name from the use of the Node.js cross-platform JavaScript
runtime environment, which is bundled along with the main payload, to set up
persistence and execute the malware. No new artifacts have been identified as of
February 27, 2023.
"After retrieving the Facebook credentials from the target's browser data, the
malware uses it to make several unauthorized requests to Facebook URLs to
enumerate account information related to advertising," Meta said. "The stolen
information then enables the threat actor to assess and then use users'
advertising accounts to run unauthorized ads."
In an attempt to slip under the radar of the company's anti-abuse systems, the
rogue requests are made from the targeted user's device to the Facebook APIs,
lending a veneer of legitimacy to the activity.
To counter such threats, Meta said it's launching a new support tool that guides
users to identify and remove malware, enable businesses to verify connected
Business Manager accounts, and require additional authentication when accessing
a credit line or changing business administrators.
Chinese Hacker Group Earth Longzhi Resurfaces with Advanced Malware Tactics
4.5.23 Virus
The Hacker News

A Chinese state-sponsored hacking outfit has resurfaced with a new campaign
targeting government, healthcare, technology, and manufacturing entities based
in Taiwan, Thailand, the Philippines, and Fiji after more than six months of no
activity.
Trend Micro attributed the intrusion set to a cyber espionage group it tracks
under the name Earth Longzhi, which is a subgroup within APT41 (aka HOODOO or
Winnti) and shares overlaps with various other clusters known as Earth Baku,
SparklingGoblin, and GroupCC.
Earth Longzhi was first documented by the cybersecurity firm in November 2022,
detailing its attacks against various organizations located in East and
Southeast Asia as well as Ukraine.
Attack chains mounted by the threat actor leverage vulnerable public-facing
applications as entry points to deploy the BEHINDER web shell, and then leverage
that access to drop additional payloads, including a new variant of a Cobalt
Strike loader called CroxLoader.
"This recent campaign [...] abuses a Windows Defender executable to perform DLL
sideloading while also exploiting a vulnerable driver, zamguard.sys, to disable
security products installed on the hosts via a bring your own vulnerable driver
(BYOVD) attack," Trend Micro said.
It's by no means the first time Earth Longzhi has leveraged the BYOVD technique,
what with previous campaigns utilizing the vulnerable RTCore64.sys driver to
restrict the execution of security products.
The malware, dubbed SPHijacker, also employs a second method referred to as
"stack rumbling" to achieve the same objective, which entails making Windows
Registry changes to interrupt the process execution flow and deliberately cause
the targeted applications to crash upon launch.
"This technique is a type of [denial-of-service] attack that abuses undocumented
MinimumStackCommitInBytes values in the [Image File Execution Options] registry
key," Trend Micro explained.

"The value of MinimumStackCommitInBytes associated with a specific process in
the IFEO registry key will be used to define the minimum size of stack to commit
in initializing the main thread. If the stack size is too large, it will trigger
a stack overflow exception and terminate the current process."
The twin approaches are far from the only methods that can be used to impair
security products. Deep Instinct, last month, detailed a new code injection
technique christened Dirty Vanity that exploits the remote forking mechanism in
Windows to blindside endpoint detection systems.
What's more, the driver payload is installed as a kernel-level service using
Microsoft Remote Procedure Call (RPC) as opposed to Windows APIs to evade
detection.
Also observed in the attacks is the use of a DLL-based dropper named Roxwrapper
to deliver another Cobalt Strike loader labeled BigpipeLoader as well as a
privilege escalation tool (dwm.exe) that abuses the Windows Task Scheduler to
launch a given payload with SYSTEM privileges.
The specified payload, dllhost.exe, is a downloader that's capable of retrieving
next-stage malware from an actor-controlled server.
It's worth pointing out here that dwm.exe is based on an open source
proof-of-concept (PoC) available on GitHub, suggesting that the threat actor is
drawing inspiration from existing programs to hone its malware arsenal.
Trend Micro further said it identified decoy documents written in Vietnamese and
Indonesian, indicating potential attempts to target users in the two countries
in the future.
"Earth Longzhi remains active and continues to improve its tactics, techniques,
and procedures (TTPs)," security researchers Ted Lee and Hara Hiroaki noted.
"Organizations should stay vigilant against the continuous development of new
stealthy schemes by cybercriminals."
LOBSHOT: A Stealthy, Financial Trojan and Info Stealer Delivered through Google
Ads
3.5.23 Virus
The Hacker News

In yet another instance of how threat actors are abusing Google Ads to serve
malware, a threat actor has been observed leveraging the technique to deliver a
new Windows-based financial trojan and information stealer called LOBSHOT.
"LOBSHOT continues to collect victims while staying under the radar," Elastic
Security Labs researcher Daniel Stepanic said in an analysis published last
week.
"One of LOBSHOT's core capabilities is around its hVNC (Hidden Virtual Network
Computing) component. These kinds of modules allow for direct and unobserved
access to the machine."
The American-Dutch company attributed the malware strain to a threat actor known
as TA505 based on infrastructure historically connected to the group. TA505 is a
financially motivated e-crime syndicate that overlaps with activity clusters
tracked under the names Evil Corp, FIN11, and Indrik Spider.
The latest development is significant because it's a sign that TA505, which is
associated with the Dridex banking trojan, is once again expanding its malware
arsenal to perpetrate data theft and financial fraud.
LOBSHOT, with early samples dating back to July 2022, is distributed by means of
rogue Google ads for legitimate tools like AnyDesk that are hosted on a network
of lookalike landing pages maintained by the operators.
The malware incorporates dynamic import resolution (i.e., resolving the names of
necessary Windows APIs at runtime), anti-emulation checks, and string
obfuscation to evade detection by security software.
Once installed, it makes Windows Registry changes to set up persistence and
siphons data from over 50 cryptocurrency wallet extensions present in web
browsers like Google Chrome, Microsoft Edge, and Mozilla Firefox.

LOBSHOT's other notable features revolve around its ability to remotely access
the compromised host via an hVNC module and stealthily perform actions on it
without attracting the victim's attention.
"Threat groups are continuing to leverage malvertising techniques to masquerade
legitimate software with backdoors like LOBSHOT," Stepanic said.
"These kinds of malware seem small, but end up packing significant functionality
which helps threat actors move quickly during the initial access stages with
fully interactive remote control capabilities."
The findings also underscore how an increasing number of adversaries are
adopting malvertising and search engine optimization (SEO) poisoning as a
technique to redirect users to fake websites and download trojanized installers
of popular software.
According to data from eSentire, the threat actors behind GootLoader have been
linked to a string of attacks targeting law firms and corporate legal
departments in the U.S., Canada, the U.K., and Australia.
GootLoader, active since 2018 and which functions as an initial
access-as-a-service operation for ransomware attacks, employs SEO poisoning to
entice victims searching for agreements and contracts to infected WordPress
blogs that point to links containing the malware.
Besides implementing geofencing to target victims in select regions, the attack
chain is designed such that the malware can only be downloaded once per day from
the hijacked sites in order to elude discovery by incident responders.
GootLoader's use of the IP address method to screen already hacked victims,
eSentire found, could be used against it to preemptively block the end users' IP
addresses and prevent organizations from potential infections.
North Korea's ScarCruft Deploys RokRAT Malware via LNK File Infection Chains
3.5.23 Virus
The Hacker News
The North Korean threat actor known as ScarCruft started
experimenting with oversized LNK files as a delivery route for RokRAT malware as
early as July 2022, the same month Microsoft began blocking macros across Office
documents by default.
"RokRAT has not changed significantly over the years, but its deployment methods
have evolved, now utilizing archives containing LNK files that initiate
multi-stage infection chains," Check Point said in a new technical report.
"This is another representation of a major trend in the threat landscape, where
APTs and cybercriminals alike attempt to overcome the blocking of macros from
untrusted sources."
ScarCruft, also known by the names APT37, InkySquid, Nickel Foxcroft, Reaper,
RedEyes, and Ricochet Chollima, is a threat group that almost exclusively
targets South Korean individuals and entities as part of spear-phishing attacks
designed to deliver an array of custom tools.
The adversarial collective, unlike the Lazarus Group or Kimsuky, is overseen by
North Korea's Ministry of State Security (MSS), which is tasked with domestic
counterespionage and overseas counterintelligence activities, per Mandiant.
The group's primary malware of choice is RokRAT (aka DOGCALL), which has since
been adapted to other platforms such as macOS (CloudMensis) and Android
(RambleOn), indicating that the backdoor is being actively developed and
maintained.
RokRAT and its variants are equipped to carry out a wide range of activities
like credential theft, data exfiltration, screenshot capture, system information
gathering, command and shellcode execution, and file and directory management.

The collected information, some of which is stored in the form of MP3 files to
cover its tracks, is sent back using cloud services like Dropbox, Microsoft
OneDrive, pCloud, and Yandex Cloud in a bid to disguise the command-and-control
(C2) communications as legitimate.
Other bespoke malware used by the group include, but not limited to, Chinotto,
BLUELIGHT, GOLDBACKDOOR, Dolphin, and, most recently, M2RAT. It's also known to
use commodity malware such as Amadey, a downloader that can receive commands
from the attacker to download additional payloads, in a bid to confuse
attribution.
The use of LNK files as decoys to activate the infection sequences was also
highlighted by the AhnLab Security Emergency Response Center (ASEC) last week,
with the files containing PowerShell commands that deploy the RokRAT malware.
While the change in modus operandi signals ScarCruft's endeavors to keep up with
the shifting threat ecosystem, it has continued to leverage macro-based
malicious Word documents as recently as April 2023 to drop the malware,
mirroring a similar chain that was reported by Malwarebytes in January 2021.
Another attack wave observed at the beginning of November 2022, according to the
Israeli cybersecurity company, employed ZIP archives incorporating LNK files to
deploy the Amadey malware.
"[The LNK file] method can trigger an equally effective infection chain by a
simple double click, one that is more reliable than n-day exploits or the Office
macros which require additional clicks to launch," Check Point said.
"APT37 continues to pose a considerable threat, launching multiple campaigns
across the platforms and significantly improving its malware delivery methods."
The findings come as Kaspersky disclosed a new Go-based malware developed by
ScarCruft codenamed SidLevel that utilizes the cloud messaging service Ably as a
C2 mechanism for the first time and comes with "extensive capabilities to steal
sensitive information from victims."
"The group continues to target individuals related to North Korea, including
novelists, academic students, and also business people who appear to send funds
back to North Korea," the Russian cybersecurity firm noted in its APT Trends
Report for Q1 2023.
New Decoy Dog Malware Toolkit Uncovered: Targeting Enterprise Networks
1.5.23 Virus
The Hacker News

An analysis of over 70 billion DNS records has led to the discovery of a new
sophisticated malware toolkit dubbed Decoy Dog targeting enterprise networks.
Decoy Dog, as the name implies, is evasive and employs techniques like strategic
domain aging and DNS query dribbling, wherein a series of queries are
transmitted to the command-and-control (C2) domains so as to not arouse any
suspicion.
"Decoy Dog is a cohesive toolkit with a number of highly unusual characteristics
that make it uniquely identifiable, particularly when examining its domains on a
DNS level," Infoblox said in an advisory published late last month.
The cybersecurity firm, which identified the malware in early April 2023
following anomalous DNS beaconing activity, said its atypical characteristics
allowed it to map additional domains that are part of the attack infrastructure.
That said, the usage of Decoy Dog in the wild is "very rare," with the DNS
signature matching less than 0.0000027% of the 370 million active domains on the
internet, according to the California-based company.
One of the chief components of the toolkit is Pupy RAT, an open source trojan
that's delivered by means of a method called DNS tunneling, in which DNS queries
and responses are used as a C2 for stealthily dropping payloads.

It's worth noting that the use of the cross-platform Pupy RAT has been linked to
nation-state actors from China such as Earth Berberoka (aka GamblingPuppet) in
the past, although there's no evidence to suggest the actor's involvement in
this campaign.
Further investigation into Decoy Dog suggests that the operation had been set up
at least a year prior to its discovery, with three distinct infrastructure
configurations detected to date.
Another crucial aspect is the unusual DNS beaconing behavior associated with
Decoy Dog domains, such that they adhere to a pattern of periodic, but
infrequent, DNS requests so as to fly under the radar.
"Decoy Dog domains can be grouped together based on their shared registrars,
name servers, IPs, and dynamic DNS providers," Infoblox said.
"Given the other commonalities between Decoy Dog domains, this is indicative of
either one threat actor gradually evolving their tactics, or multiple threat
actors deploying the same toolkit on different infrastructure."
Vietnamese Threat Actor Infects 500,000 Devices Using 'Malverposting' Tactics
1.5.23 Virus
The Hacker News

A Vietnamese threat actor has been attributed as behind a "malverposting"
campaign on social media platforms to infect over 500,000 devices worldwide over
the past three months to deliver variants of information stealers such as
S1deload Stealer and SYS01stealer.
Malverposting refers to the use of promoted social media posts on services like
Facebook and Twitter to mass propagate malicious software and other security
threats. The idea is to reach a broader audience by paying for ads to "amplify"
their posts.
According to Guardio Labs, such attacks commence with the adversary creating new
business profiles and hijacking already popular accounts to serve ads that claim
to offer free adult-rated photo album downloads.
Within these ZIP archive files are purported images that are actually executable
files, which, when clicked, activate the infection chain and ultimately deploy
the stealer malware to siphon session cookies, account data, and other
information.
The attack chain is highly effective as it creates a "vicious circle" wherein
the information plundered using the stealer is used to create an ever-expanding
army of hijacked Facebook bot accounts that are then used to push more sponsored
posts, effectively scaling the scheme further.
To slip under the radar of Facebook, the threat actor has been found to pass off
the newly generated business profile pages as photographer accounts. A majority
of the infections have been reported in Australia, Canada, India, the U.K., and
the U.S.

The method through which the PHP-based stealer is deployed is said to be
constantly evolving to incorporate more detection evasion features, suggesting
that the threat actor behind the campaign is actively refining and retooling
their tactics in response to public disclosures.
"The malicious payload is quite sophisticated and varies all the time,
introducing new evasive techniques," Guardio Labs security researcher Nati Tal
said.
The findings come as Group-IB revealed details of an ongoing phishing operation
that's aimed at Facebook users by tricking them to enter their credentials on
fake copycat sites designed to steal their account credentials and take over the
profiles.

In a related development, Malwarebytes unearthed a malvertising campaign that
has been found to trick users searching for games and food recipes on Google to
serve malicious ads that redirect them to fake websites created on Weebly with
the goal of conducting a tech support scam.
ViperSoftX InfoStealer Adopts Sophisticated Techniques to Avoid Detection
28.4.23 Virus
The Hacker News
A significant number of victims in the consumer and
enterprise sectors located across Australia, Japan, the U.S., and India have
been affected by an evasive information-stealing malware called ViperSoftX.
ViperSoftX was first documented in 2020, with cybersecurity company Avast
detailing a campaign in November 2022 that leveraged the malware to distribute a
malicious Google Chrome extension capable of siphoning cryptocurrencies from
wallet applications.
Now a new analysis from Trend Micro has revealed the malware's adoption of "more
sophisticated encryption and basic anti-analysis techniques, such as byte
remapping and web browser communication blocking."
The arrival vector of ViperSoftX is typically a software crack or a key
generator (keygen), while also employing actual non-malicious software like
multimedia editors and system cleaner apps as "carriers."
One of the key steps performed by the malware before downloading a first-stage
PowerShell loader is a series of anti-virtual machine, anti-monitoring, and
anti-malware checks.

The loader then decrypts and executes a second-stage PowerShell script retrieved
from a remote server, which then takes care of launching the main routine
responsible for installing rogue browser extensions to exfiltrate passwords and
crypto wallet data.
The primary command-and-control (C&C) servers used for the second stage download
have been observed to change on a monthly basis, suggesting attempts on the part
of the actor to sidestep detection.
"It also uses some basic anti-C&C
analyses by disallowing communications using web browsers," Trend Micro
researcher Don Ovid Ladores said, adding the updated version of ViperSoftX scans
for the presence of KeePass 2 and 1Password password managers.
As mitigations, it's advised that users download software only from official
platforms and sources, and avoid downloading illegal software.
"The cybercriminals behind ViperSoftX are also skilled enough to execute a
seamless chain for malware execution while staying under the radar of
authorities by selecting one of the most effective methods for delivering
malware to consumers," Ovid Ladores added.
Tonto Team Uses Anti-Malware File to Launch Attacks on South Korean Institutions
28.4.23 Virus
The Hacker News

South Korean education, construction, diplomatic, and political institutions are
at the receiving end of new attacks perpetrated by a China-aligned threat actor
known as the Tonto Team.
"Recent cases have revealed that the group is using a file related to
anti-malware products to ultimately execute their malicious attacks," the AhnLab
Security Emergency Response Center (ASEC) said in a report published this week.
Tonto Team, active since at least 2009, has a track record of targeting various
sectors across Asia and Eastern Europe. Earlier this year, the group was
attributed to an unsuccessful phishing attack on cybersecurity company Group-IB.
The attack sequence discovered by ASEC starts with a Microsoft Compiled HTML
Help (.CHM) file that executes a binary file to side-load a malicious DLL file
(slc.dll) and launch ReVBShell, an open source VBScript backdoor also put to use
by another Chinese threat actor called Tick.
ReVBShell is subsequently leveraged to download a second executable, a
legitimate Avast software configuration file (wsc_proxy.exe), to side-load a
second rogue DLL (wsc.dll), ultimately leading to the deployment of the Bisonal
remote access trojan.
"The Tonto Team is constantly evolving through various means such as using
normal software for more elaborate attacks," ASEC said.
The use of CHM files
as a distribution vector for malware is not limited to Chinese threat actors
alone. Similar attack chains have been adopted by a North Korean nation-state
group known as ScarCruft in attacks aimed at its southern counterpart to
backdoor targeted hosts.
The adversary, also known as APT37, Reaper, and Ricochet Chollima, has since
also utilized LNK files to distribute the RokRAT malware, which is capable of
collecting user credentials and downloading additional payloads.
LimeRAT Malware Analysis: Extracting the Config
28.4.23
Virus The Hacker News
Remote Access Trojans (RATs) have taken the third leading position in ANY. RUN's
Q1 2023 report on the most prevalent malware types, making it highly probable
that your organization may face this threat.
Though LimeRAT might not be the most well-known RAT family, its versatility is
what sets it apart. Capable of carrying out a broad spectrum of malicious
activities, it excels not only in data exfiltration, but also in creating DDoS
botnets and facilitating crypto mining. Its compact footprint allows it to elude
endpoint detection systems, making it a stealthy adversary. Interestingly,
LimeRAT shares similarities with njRAT, which ANY.RUN ranks as the third most
popular malware family in terms of uploads during Q1 2023.
ANY.RUN researchers have recently conducted an in-depth analysis of a LimeRAT
sample and successfully extracted its configuration. In this article, we'll
provide a brief overview of that analysis.
Collected artifacts#
SHA1 14836dd608efb4a0c552a4f370e5aafb340e2a5d
SHA256
6d08ed6acac230f41d9d6fe2a26245eeaf08c84bc7a66fddc764d82d6786d334
MD5
d36f15bef276fd447e91af6ee9e38b28
SSDEEP
3072:DDiv2GSyn88sH888wQ2wmVgMk/211h36vEcIyNTY4WZd/w1UwIwEoTqPMinXHx+i:XOayyIPv4:
IOC Description
20[.]199.13.167:8080 LimeRAT's Command and Control
serverDomains:
IOC Description
https://pastebin[.]com/raw/sxNJt2ek
PasteBin used by LimeRAT to hide its original Command and Control serverMITRE
ATT&CK®
Tactic Technique Description
TA0005: Defense Evasion T1027:
Obfuscated Files or Information Malware is using obfuscator to strip its method
names, class names, etc.
TA0005: Defense Evasion T1027: Obfuscated Files or
Information Malware uses Base64 algorithm to encode and decode data
TA0005:
Defense Evasion T1027: Obfuscated Files or Information Malware uses AES
algorithm to encrypt and decrypt data
ANY.RUN is running a limited-time
offer, celebrating the 7th Cyberbirthdsay#
ANY.RUN is an interactive cloud
malware sandbox that can extract malware configs automatically for numerous
families, saving researchers hours of effort.
The service is celebrating its 7th anniversary and inviting all researchers to
try out advanced analysis features typically reserved for pro plans, completely
free until May 5th. This includes configuring the execution environment with
Windows 8, 10, or 11.
If you discover that ANY.RUN enhances your malware analysis workflow, they are
also offering a limited promotion, available until May 5th: receive 6 or 12
months of free usage when you sign up for a yearly or two-year subscription,
respectively.

Breaking down LimeRAT's decryption algorithm#
We'll share a condensed version
of the article here. For a complete walkthrough and the extended analysis, head
over to ANY. RUN's blog if you're interested in learning more about the workflow
they employed.
Since the sample under review was written in .NET, researchers utilized DnSpy to
examine the code. Immediately, it was obvious that obfuscation techniques were
being employed:

Sample overview in DnSpy; note that use of obfuscation techniques
Closer
examination of the code revealed a class resembling the malware configuration.
Within this class, was a field containing a string that was both base64 encoded
and encrypted.

Possibly, malware configuration class
Continuing the code inspection, ANY.RUN
researchers pinpointed a function responsible for decrypting the string. By
employing the "Read by" filter in DnSpy, they tracked down methods where the
string was being read, which led to a total of two methods. The first method
proved unfruitful, but the second one looked interesting:

The second x-ref is more interesting. It seems that it uses our string in
WebClient.DownloadString method
This method turned out to be responsible for
decryption. By closely examining it, it was possible to reconstruct the process
by which LimeRAT decrypts its configuration:
Instances of the RijndaelManaged and MD5CryptoServiceProvider classes are
instantiated. As per MSDN, RijndaelManaged is an outdated implementation of the
AES encryption algorithm (MITRE T1027), while MD5CryptoServiceProvider computes
MD5 hashes.
A 32-byte array, initialized with zeros, is generated to store
the AES key.
The key is created by first calculating the MD5 hash of a
distinct string within the configuration class (in our analysis, the string is
"20[.]199.13.167").
The initial 15 bytes, followed by the first 16 bytes of
the calculated hash, are copied into the previously established array. The final
element of the array remains zero.
The derived key is assigned to the key
property of the RijndaelManaged instance, while the Mode property is configured
as CipherMode.ECB.
Ultimately, the primary string undergoes decoding via the
Base64 algorithm and decryption using the AES256-ECB algorithm.
Decrypting
the string revealed a link to a PasteBin note:
https://pastebin[.]com/raw/sxNJt2ek. Within this note, was LimeRAT's Command and
Control (C2) server:
LimeRATs C2 discovered with decrypted data
To wrap up#
We hope you found
this brief overview of our LimeRAT configuration decryption process insightful.
For a more comprehensive examination, head over to the full article on ANY.RUN's
blog, to get additional context on the steps and check the decryption process
using CyberChef.
Also, remember that ANY. RUN's currently offering limited-time deals, featuring
discounts on subscriptions and an expanded feature set for free plans, including
the ability to configure execution environments with Windows 8, 10, and 11
operating systems. This offer expires on May 5th.
This is an ideal opportunity to test out ANY.RUN and determine if it streamlines
your workflow, or to secure a subscription at an unbeatable price and reap the
benefits of significant time savings through static and behavioral analysis.
To learn more about this offer, visit ANY.RUN plans.
Chinese Hackers Spotted Using Linux Variant of PingPull in Targeted Cyberattacks
28.4.23 Virus
The Hacker News
The Chinese nation-state group dubbed Alloy Taurus is
using a Linux variant of a backdoor called PingPull as well as a new
undocumented tool codenamed Sword2033.
That's according to findings from Palo Alto Networks Unit 42, which discovered
recent malicious cyber activity carried out by the group targeting South Africa
and Nepal.
Alloy Taurus is the constellation-themed moniker assigned to a threat actor
that's known for its attacks targeting telecom companies since at least 2012.
It's also tracked by Microsoft as Granite Typhoon (previously Gallium).
Last month, the adversary was attributed to a campaign called Tainted Love
targeting telecommunication providers in the Middle East as part of a broader
operation referred to as Soft Cell.
Recent cyber espionage attacks mounted by Alloy Taurus have also broadened their
victimology footprint to include financial institutions and government entities.
PingPull, first documented by Unit 42 in June 2022, is a remote access trojan
that employs the Internet Control Message Protocol (ICMP) for
command-and-control (C2) communications.
The Linux flavor of the malware, which was uploaded to VirusTotal on March 7,
2023, boasts of similar functionalities as its Windows counterpart, allowing it
to carry out file operations and run arbitrary commands by transmitting from the
C2 server a single upper case character between A and K, and M.
"Upon execution, this sample is configured to communicate with the domain
yrhsywu2009.zapto[.]org over port 8443 for C2," Unit 42 said. "It uses a
statically linked OpenSSL (OpenSSL 0.9.8e) library to interact with the domain
over HTTPS."

Interestingly, PingPull's parsing of the C2 instructions mirrors that of China
Chopper, a web shell widely used by Chinese threat actors, suggesting that the
threat actor is repurposing existing source code to devise custom tools.
A closer examination of the aforementioned domain has also revealed the
existence of another ELF artifact (i.e., Sword2033) that supports three basic
functions, including uploading and exfiltrating files to and from the system,
and executing commands.
The malware's links to Alloy Taurus stems from the
fact that the domain resolved to an IP address that was previously identified as
an active indicator of compromise (IoC) associated with a 2021 campaign
targeting companies operating in Southeast Asia, Europe, and Africa.
The targeting of South Africa, per the cybersecurity company, comes against the
backdrop of the country holding a joint 10-day naval drill with Russia and China
earlier this year.
"Alloy Taurus remains an active threat to telecommunications, finance, and
government organizations across Southeast Asia, Europe, and Africa," Unit 42
said.
"The identification of a Linux variant of PingPull malware, as well as recent
use of the Sword2033 backdoor, suggests that the group continues to evolve their
operations in support of their espionage activities."
Charming Kitten's New BellaCiao Malware Discovered in Multi-Country Attacks
26.4.23 Virus
The Hacker News

The prolific Iranian nation-state group known as Charming Kitten targeted
multiple victims in the U.S., Europe, the Middle East and India with a novel
malware dubbed BellaCiao, adding to its ever-expanding list of custom tools.
Discovered by Bitdefender Labs, BellaCiao is a "personalized dropper" that's
capable of delivering other malware payloads onto a victim machine based on
commands received from an actor-controlled server.
"Each sample collected was tied up to a specific victim and included hard-coded
information such as company name, specially crafted subdomains, or associated
public IP address," the Romanian cybersecurity firm said in a report shared with
The Hacker News.
Charming Kitten, also known as APT35, Cobalt Illusion, Educated Manticore,
ITG18, Mint Sandstorm (née Phosphorus), TA453, and Yellow Garuda, is an Iranian
state-sponsored APT group associated with the Islamic Revolutionary Guard Corps
(IRGC).
Over the years, the group has utilized various means to deploy backdoors in
systems belonging to a wide range of industry verticals.
The development comes as the threat actor was attributed by Microsoft to
retaliatory attacks aimed at critical infrastructure entities in the U.S.
between late 2021 to mid-2022 using bespoke malware such as harmPower, Drokbk,
and Soldier.
Then earlier this week, Check Point disclosed Mint Sandstorm's use of an updated
version of the PowerLess implant to strike organizations located in Israel using
Iraq-themed phishing lures.
"Custom-developed malware, also known as 'tailored' malware, is generally harder
to detect because it is specifically crafted to evade detection and contains
unique code," Bitdefender researcher Martin Zugec noted.
The exact modus operandi used to achieve initial intrusion is currently
undetermined, although it's suspected to entail the exploitation of known
vulnerabilities in internet-exposed applications like Microsoft Exchange Server
or Zoho ManageEngine.
A successful breach is followed by the threat actor attempting to disable
Microsoft Defender using a PowerShell command and establishing persistence on
the host via a service instance.
Bitdefender said it also observed Charming Kitten downloading two Internet
Information Services (IIS) modules capable of processing incoming instructions
and exfiltrating credentials.
BellaCiao, for its part, is also notable for
performing a DNS request every 24 hours to resolve a subdomain to an IP address
that's subsequently parsed to extract the commands to be executed on the
compromised system.
"The resolved IP address is like the real public IP address, but with slight
modifications that allow BellaCiao to receive further instructions," Zugec
explained.
Depending on the resolved IP address, the attack chain leads to the deployment
of a web shell that supports the ability to upload and download arbitrary files
as well as run commands.
Also spotted is a second variant of BellaCiao that substitutes the web shell for
a Plink tool – a command-line utility for PuTTY – that's designed to establish a
reverse proxy connection to a remote server and implements similar backdoor
features.
"The best protection against modern attacks involves implementing a
defense-in-depth architecture," Zugec concluded. "The first step in this process
is to reduce the attack surface, which involves limiting the number of entry
points that attackers can use to gain access to your systems and prompt patching
of newly discovered vulnerabilities."
Chinese Hackers Using MgBot Malware to Target International NGOs in Mainland
China
26.4.23 Virus
The Hacker News

The advanced persistent threat (APT) group referred to as Evasive Panda has been
observed targeting an international non-governmental organization (NGO) in
Mainland China with malware delivered via update channels of legitimate
applications like Tencent QQ.
The attack chains are designed to distribute a Windows installer for MgBot
malware, ESET security researcher Facundo Muñoz said in a new report published
today. The activity commenced in November 2020 and continued throughout 2021.
Evasive Panda, also known as Bronze Highland and Daggerfly, is a
Chinese-speaking APT group that has been attributed to a series of cyber
espionage attacks targeting various entities in China, Hong Kong, and other
countries located in East and South Asia since at least late December 2012.
The group's hallmark is the use of the custom MgBot modular malware framework,
which is capable of receiving additional components on the fly to expand on its
intelligence-gathering capabilities.
Some of the prominent capabilities of the malware include stealing files,
logging keystrokes, harvesting clipboard data, recording audio streams, and
credential theft from web browsers.
ESET, which discovered the campaign in January 2022 after a legitimate Chinese
application was used to deploy an installer for the MgBot backdoor, said the
targeted users were located in the Gansu, Guangdong, and Jiangsu provinces and
are members of an unnamed international NGO.
The trojanized application is the Tencent QQ Windows client software updater
("QQUrlMgr.exe") hosted on the domain "update.browser.qq[.]com." It's not
immediately clear how the threat actor managed to deliver the implant through
legitimate updates.
MgBot Malware
But it points to either of the two scenarios, a supply chain
compromise of Tencent QQ's update servers or a case of an
adversary-in-the-middle (AitM) attack, as detailed by Kaspersky in June 2022
involving a Chinese hacking crew dubbed LuoYu.
In recent years, many software supply chain attack has been orchestrated by
nation-state groups from Russia, China, and North Korea. The ability to gain a
large malicious footprint quickly has not been lost on these attackers, who are
increasingly targeting the IT supply chain to breach enterprise environments.
"AitM styles of interception would be possible if the attackers – either LuoYu
or Evasive Panda – were able to compromise vulnerable devices such as routers or
gateways," Muñoz elaborated.
"With access to ISP backbone infrastructure – through legal or illegal means –
Evasive Panda would be able to intercept and reply to the update requests
performed via HTTP, or even modify packets."
This is significant as the findings come less than a week after Broadcom-owned
Symantec detailed attacks mounted by the threat actor against telecom service
providers in Africa using the MgBot malware framework.
New All-in-One "EvilExtractor" Stealer for Windows Systems Surfaces on the Dark
Web
24.4.23 Virus
The Hacker News

A new "all-in-one" stealer malware named EvilExtractor (also spelled Evil
Extractor) is being marketed for sale for other threat actors to steal data and
files from Windows systems.
"It includes several modules that all work via an FTP service," Fortinet
FortiGuard Labs researcher Cara Lin said. "It also contains environment checking
and Anti-VM functions. Its primary purpose seems to be to steal browser data and
information from compromised endpoints and then upload it to the attacker's FTP
server."
The network security company said it has observed a surge in attacks spreading
the malware in the wild in March 2023, with a majority of the victims located in
Europe and the U.S. While marketed as an educational tool, EvilExtractor has
been adopted by threat actors for use as an information stealer.
Sold by an actor named Kodex on cybercrime forums like Cracked since October 22,
2022, it's continually updated and packs in various modules to siphon system
metadata, passwords and cookies from various web browsers as well as record
keystrokes and even act as a ransomware by encrypting files on the target
system.
The malware is also said to have been used as part of a phishing email campaign
detected by the company on March 30, 2023. The emails lure recipients into
launching an executable that masquerades as a PDF document under the pretext of
confirming their "account details."
The "Account_Info.exe" binary is an obfuscated Python program designed to launch
a .NET loader that uses a Base64-encoded PowerShell script to launch
EvilExtractor. The malware, besides gathering files, can also activate the
webcam and capture screenshots.
"EvilExtractor is being used as a comprehensive info stealer with multiple
malicious features, including ransomware," Lin said. "Its PowerShell script can
elude detection in a .NET loader or PyArmor. Within a very short time, its
developer has updated several functions and increased its stability."
The findings come as Secureworks Counter Threat Unit (CTU) detailed a
malvertising and SEO poisoning campaign used to deliver the Bumblebee malware
loader via trojanized installers of legitimate software.
Dark Web
Bumbleebee, documented first a year ago by Google's Threat Analysis
Group and Proofpoint, is a modular loader that's primarily propagating through
phishing techniques. It's suspected to be developed by actors associated with
the Conti ransomware operation as a replacement for BazarLoader.
The use of
SEO poisoning and malicious ads to redirect users searching for popular tools
like ChatGPT, Cisco AnyConnect, Citrix Workspace, and Zoom to rogue websites
hosting tainted installers has witnessed a spike in recent months after
Microsoft began blocking macros by default from Office files downloaded from the
internet.
In one incident described by the cybersecurity firm, the threat actor used the
Bumblebee malware to obtain an entry point and move laterally after three hours
to deploy Cobalt Strike and legitimate remote access software like AnyDesk and
Dameware. The attack was ultimately disrupted before it proceeded to the final
ransomware stage.
"To mitigate this and similar threats, organizations should ensure that software
installers and updates are only downloaded from known and trusted websites,"
Secureworks said. "Users should not have privileges to install software and run
scripts on their computers."
YouTube Videos Distributing Aurora Stealer Malware via Highly Evasive Loader
19.4.23 Virus
The Hacker News
Cybersecurity researchers have detailed the inner
workings of a highly evasive loader named "in2al5d p3in4er" (read: invalid
printer) that's used to deliver the Aurora information stealer malware.
"The in2al5d p3in4er loader is compiled with Embarcadero RAD Studio and targets
endpoint workstations using advanced anti-VM (virtual machine) technique,"
cybersecurity firm Morphisec said in a report shared with The Hacker News.
Aurora is a Go-based information stealer that emerged on the threat landscape in
late 2022. Offered as a commodity malware to other actors, it's distributed
through YouTube videos and SEO-poised fake cracked software download websites.
Clicking the links present in YouTube video descriptions redirects the victim to
decoy websites where they are enticed into downloading the malware under the
garb of a seemingly-legitimate utility.
The loader analyzed by Morphisec is designed to query the vendor ID of the
graphics card installed on a system, and compared it against a set of
allowlisted vendor IDs (AMD, Intel, or NVIDIA). If the value doesn't match, the
loader terminates itself.
The loader ultimately decrypts the final payload and injects it into a
legitimate process called "sihost.exe" using a technique called process
hollowing. Alternatively, some loader samples also allocate memory to write the
decrypted payload and invoke it from there.
"During the injection process, all loader samples resolve the necessary Win APIs
dynamically and decrypt these names using a XOR key: 'in2al5d p3in4er,'"
security researchers Arnold Osipov and Michael Dereviashkin said.

Another crucial aspect of the loader is its use of Embarcadero RAD Studio to
generate executables for multiple platforms, thereby enabling it to evade
detection.
"Those with the lowest detection rate on VirusTotal are compiled using
'BCC64.exe,' a new Clang based C++ compiler from Embarcadero," the Israeli
cybersecurity company said, pointing out its ability to evade sandboxes and
virtual machines.
"This compiler uses a different code base such as 'Standard Library'
(Dinkumware) and 'Runtime Library' (compiler-rt) and generates optimized code
which changes the entry point and execution flow. This breaks security vendors'
indicators, such as signatures composed from 'malicious/suspicious code block.'"
In a nutshell, the findings show that the threat actors behind in2al5d p3in4er
are leveraging social engineering methods for a high-impact campaign that
employs YouTube as a malware distribution channel and directs viewers to
convincing-looking fake websites to distribute the stealer malware.
The development comes as Intel 471 unearthed another malware loader AresLoader
that's marketed for $300/month as a service for criminal actors to push
information stealers disguised as popular software using a binder tool. The
loader is suspected to be developed by a group with ties to Russian hacktivism.
Some of the prominent malware families spread using AresLoader since January
2023 include Aurora Stealer, Laplas Clipper, Lumma Stealer, Stealc, and
SystemBC.
Israeli Spyware Vendor QuaDream to Shut Down Following Citizen Lab and Microsoft
Expose
18.4.23 Virus
The Hacker News
Israeli spyware vendor QuaDream is allegedly shutting
down its operations in the coming days, less than a week after its hacking
toolset was exposed by Citizen Lab and Microsoft.
The development was reported by the Israeli business newspaper Calcalist, citing
unnamed sources, adding the company "hasn't been fully active for a while" and
that it "has been in a difficult situation for several months."
The company's board of directors are looking to sell off its intellectual
property, the report further added.
QuaDream, which specializes in hacking Apple devices using "zero-click"
infections which do not require any action on the part of the victim, is also
said to have fired all its employees, with the firm undergoing significant
downsizing, according to Haaretz and The Jerusalem Post.
News of the purported shutdown comes as the firm's spyware framework – dubbed
REIGN – was outed as having been used against journalists, political opposition
figures, and NGO workers across North America, Central Asia, Southeast Asia,
Europe, and the Middle East.
Microsoft described REIGN as a "suite of exploits, malware, and infrastructure
designed to exfiltrate data from mobile devices."
The attacks entailed the exploitation of a now-patched flaw in iOS to deploy
sophisticated surveillanceware capable of surreptitiously gathering sensitive
information, including audio, pictures, passwords, files, and locations.
Apple told The Hacker News last week that there was no indication to suggest
that the exploit, codenamed ENDOFDAYS, had been put to use since the company
released iOS 14.4.2 in March 2021.
QuaDream, like its Israeli counterparts NSO Group and Candiru, is a
private-sector offensive actor (PSOA) that markets end-to-end hacking tools for
use by its customers to run their targeted cyber operations.
While the
company has largely managed to stay under the shadows, Haaretz reported in June
2021 that its spyware technology was sold to Saudi Arabia to carry out
zero-click attacks against targets of interest.
Then last year, Reuters revealed that QuaDream had independently developed an
exploit to break into iPhones that's comparable to the one provided by NSO Group
by leveraging a flaw in iMessage. Apple addressed the vulnerability in September
2021.
The upcoming closure also comes a little over a month after Haaretz shed light
on a previously unknown Israeli cyber mercenary company called NFV Systems for
selling its surveillance technologies to foreign countries without obtaining a
license from the Ministry of Defense.
New QBot Banking Trojan Campaign Hijacks Business Emails to Spread Malware
18.4.23 Virus
The Hacker News

A new QBot malware campaign is leveraging hijacked business correspondence to
trick unsuspecting victims into installing the malware, new findings from
Kaspersky reveal.
The latest activity, which commenced on April 4, 2023, has primarily targeted
users in Germany, Argentina, Italy, Algeria, Spain, the U.S., Russia, France,
the U.K., and Morocco.
QBot (aka Qakbot or Pinkslipbot) is a banking trojan that's known to be active
since at least 2007. Besides stealing passwords and cookies from web browsers,
it doubles up as a backdoor to inject next-stage payloads such as Cobalt Strike
or ransomware.
Distributed via phishing campaigns, the malware has seen constant updates during
its lifetime that pack in anti-VM, anti-debugging, and anti-sandbox techniques
to evade detection. It has also emerged as the most prevalent malware for the
month of March 2023, per Check Point.
"Early on, it was distributed through infected websites and pirated software,"
Kaspersky researchers said, explaining QBot's distribution methods. "Now the
banker is delivered to potential victims through malware already residing on
their computers, social engineering, and spam mailings."
Email thread hijacking attacks are not new. It occurs when cybercriminals insert
themselves into existing business conversations or initiate new conversations
based on information previously gleaned by compromised email accounts.
The goal is to entice victims into opening malicious links or malicious
attachments, in this case, an enclosed PDF file that masquerades as a Microsoft
Office 365 or Microsoft Azure alert.
Opening the document leads to the
retrieval of an archive file from an infected website that, in turn, contains an
obfuscated Windows Script File (.WSF). The script, for its part, incorporates a
PowerShell script that downloads malicious DLL from a remote server. The
downloaded DLL is the QBot malware.
The findings come as Elastic Security Labs unearthed a multi-stage social
engineering campaign that employs weaponized Microsoft Word documents to
distribute Agent Tesla and XWorm by means of a custom .NET-based loader.
FIN7 and Ex-Conti Cybercrime Gangs Join Forces in Domino Malware Attacks
18.4.23 Virus
The Hacker News

A new strain of malware developed by threat actors likely affiliated with the
FIN7 cybercrime group has been put to use by the members of the now-defunct
Conti ransomware gang, indicating collaboration between the two crews.
The malware, dubbed Domino, is primarily designed to facilitate follow-on
exploitation on compromised systems, including delivering a lesser-known
information stealer that has been advertised for sale on the dark web since
December 2021.
"Former members of the TrickBot/Conti syndicate [...] have been using Domino
since at least late February 2023 to deliver either the Project Nemesis
information stealer or more capable backdoors such as Cobalt Strike," IBM
Security X-Force security researcher Charlotte Hammond said in a report
published last week.
FIN7, also called Carbanak and ITG14, is a prolific Russian-speaking
cybercriminal syndicate that's known to employ an array of custom malware to
deploy additional payloads and broaden its monetization methods.
Recent analyses by Google-owned Mandiant, SentinelOne, and PRODAFT have revealed
the group's role as a precursor for Maze and Ryuk ransomware attacks, not to
mention exposing its connections to Black Basta, DarkSide, REvil, and LockBit
families.
The latest intrusion wave, spotted by IBM Security X-Force two months ago,
involves the use of Dave Loader, a crypter previously attributed to the Conti
group (aka Gold Blackburn, ITG23, or Wizard Spider), to deploy the Domino
backdoor.
Domino Malware Attacks
Domino's potential connections to FIN7 comes from
source code overlaps with DICELOADER (aka Lizar or Tirion), a time-tested
malware family attributed to the group. The malware, for its part, is designed
to gather basic sensitive information and retrieve encrypted payloads from a
remote server.
This next-stage artifact is a second loader codenamed Domino Loader, which
harbors an encrypted .NET information stealer referred to as Project Nemesis
that's capable of amassing sensitive data from clipboard, Discord, web browsers,
crypto wallets, VPN services, and other apps.
"Domino has been active in the wild since at least October 2022, which notably
is when Lizar observations began to decrease," Hammond pointed out, indicating
that the threat actors may be phasing out the latter in favor of the new
malware.
Another crucial link bridging Domino to FIN7 comes from a December 2022 campaign
that leveraged another loader called NewWorldOrder Loader to deliver both the
Domino and Carbanak backdoors.
The Domino backdoor and loader – both 64-bit
DLLs written in Visual C++ – are said to have been used to install Project
Nemesis since at least October 2022, prior to its use by ex-Conti members
earlier this year.
"This leads us to assess that the ITG14 members responsible for developing
Domino probably had a relationship with Project Nemesis and offered Domino and
the infostealer to the ex-Conti threat actors as a package," Hammond said. "The
ex-Conti members in turn likely used the Project Nemesis infostealer against
lower value targets."
The use of stealer malware by ransomware distributors is not without precedent.
In November 2022, Microsoft revealed intrusions mounted by a threat actor known
as DEV-0569 that leveraged BATLOADER malware to deliver Vidar and Cobalt Strike,
the latter of which eventually facilitated human-operated ransomware attacks
distributing Royal ransomware.
This has raised the possibility that information stealers are deployed during
lower priority infections (e.g., personal computers), while those belonging to
an Active Directory domain are served with Cobalt Strike.
"The use of malware with ties to multiple groups in a single campaign — such as
Dave Loader, Domino Backdoor, and Project Nemesis infostealer — highlights the
complexity involved in tracking threat actors but also provides insight into how
and with whom they operate," Hammond concluded.
Over 1 Million WordPress Sites Infected by Balada
Injector Malware Campaign
11.4.23
Virus The Hacker News
Over
one million WordPress websites are estimated to have been infected by an ongoing
campaign to deploy malware called Balada Injector since 2017.
The massive campaign, per GoDaddy's Sucuri, "leverages all known and recently
discovered theme and plugin vulnerabilities" to breach WordPress sites. The
attacks are known to play out in waves once every few weeks.
"This campaign is easily identified by its preference for String.fromCharCode
obfuscation, the use of freshly registered domain names hosting malicious
scripts on random subdomains, and by redirects to various scam sites," security
researcher Denis Sinegubko said.
The websites include fake tech support, fraudulent lottery wins, and rogue
CAPTCHA pages urging users to turn on notifications to 'Please Allow to verify,
that you are not a robot,' thereby enabling the actors to send spam ads.
The report builds on recent findings from Doctor Web, which detailed a Linux
malware family that exploits flaws in more than two dozen plugins and themes to
compromise vulnerable WordPress sites.
In the interim years, Balada Injector has relied on over 100 domains and a
plethora of methods to take advantage of known security flaws (e.g., HTML
injection and Site URL), with the attackers primarily attempting to obtain
database credentials in the wp-config.php file.
Additionally, the attacks are engineered to read or download arbitrary site
files – including backups, database dumps, log and error files – as well as
search for tools like adminer and phpmyadmin that could have been left behind by
site administrators upon completing maintenance tasks.
WordPress
The malware ultimately allows for the generation of fake WordPress
admin users, harvests data stored in the underlying hosts, and leaves backdoors
for persistent access.
Balada Injector further carries out broad searches from top-level directories
associated with the compromised website's file system to locate writable
directories that belong to other sites.
"Most commonly, these sites belong to the webmaster of the compromised site and
they all share the same server account and the same file permissions," Sinegubko
said. "In this manner, compromising just one site can potentially grant access
to several other sites 'for free.'"
Should these attack pathways turn out to be unavailable, the admin password is
brute-forced using a set of 74 predefined credentials. WordPress users are,
therefore, recommended to keep their website software up-to-date, remove unused
plugins and themes, and use strong WordPress admin passwords.
The findings
come weeks after Palo Alto Networks Unit 42 unearthed a similar malicious
JavaScript injection campaign that redirects site visitors to adware and scam
pages. More than 51,000 websites have been affected since 2022.
The activity, which also employs String.fromCharCode as an obfuscation
technique, leads victims to booby-trapped pages that trick them into enabling
push notifications by masquerading as a fake CAPTCHA check to serve deceptive
content.
"The injected malicious JS code was included on the homepage of more than half
of the detected websites," Unit 42 researchers said. "One common tactic used by
the campaign's operators was to inject malicious JS code on frequently used JS
filenames (e.g., jQuery) that are likely to be included on the homepages of
compromised websites."
"This potentially helps attackers target the website's legitimate users, since
they are more likely to visit the website's home page."
CryptoClippy: New Clipper Malware Targeting Portuguese Cryptocurrency Users
6.4.23 Virus
The Hacker News
Portuguese users are being targeted by a new malware
codenamed CryptoClippy that's capable of stealing cryptocurrency as part of a
malvertising campaign.
The activity leverages SEO poisoning techniques to entice users searching for
"WhatsApp web" to rogue domains hosting the malware, Palo Alto Networks Unit 42
said in a new report published today.
CryptoClippy, a C-based executable, is a type of cryware known as clipper
malware that monitors a victim's clipboard for content matching cryptocurrency
addresses and substituting them with a wallet address under the threat actor's
control.
"The clipper malware uses regular expressions (regexes) to identify what type of
cryptocurrency the address pertains to," Unit 42 researchers said.
"It then replaces the clipboard entry with a visually similar but
adversary-controlled wallet address for the appropriate cryptocurrency. Later,
when the victim pastes the address from the clipboard to conduct a transaction,
they actually are sending cryptocurrency directly to the threat actor."

The illicit scheme is estimated to have netted its operators about $983 so far,
with victims found across manufacturing, IT services, and real estate
industries.
It's worth noting that the use of poisoned search results to deliver malware has
been adopted by threat actors associated with the GootLoader malware.
Another approach used to determine suitable targets is a traffic direction
system (TDS), which checks if the preferred browser language is Portuguese, and
if so, takes the user to a rogue landing page.
Users who do not meet the requisite criteria are redirected to the legitimate
WhatsApp Web domain without any further malicious activity, thereby avoiding
detection.
The findings arrive days after SecurityScorecard detailed an information stealer
called Lumma that's capable of harvesting data from web browsers, cryptocurrency
wallets, and a variety of apps such as AnyDesk, FileZilla, KeePass, Steam, and
Telegram.
Hackers Using Self-Extracting Archives Exploit for Stealthy Backdoor Attacks
5.4.23 Virus
The Hacker News

An unknown threat actor used a malicious self-extracting archive (SFX) file in
an attempt to establish persistent backdoor access to a victim's environment,
new findings from CrowdStrike show.
SFX files are capable of extracting the data contained within them without the
need for dedicated software to display the file contents. It achieves this by
including a decompressor stub, a piece of code that's executed to unpack the
archive.
"However, SFX archive files can also contain hidden malicious functionality that
may not be immediately visible to the file's recipient, and could be missed by
technology-based detections alone," CrowdStrike researcher Jai Minton said.
In the case investigated by the cybersecurity firm, compromised credentials to a
system were used to run a legitimate Windows accessibility application called
Utility Manager (utilman.exe) and subsequently launch a password-protected SFX
file.
This, in turn, is made possible by configuring a debugger (another executable)
in the Windows Registry to a specific program (in this case, utilman.exe) so
that the debugger is automatically started every time the program is launched.
The abuse of utilman.exe is also noteworthy as it can be launched directly from
the Windows login screen by using the Windows logo key + U keyboard shortcut,
potentially enabling threat actors to configure backdoors via the Image File
Execution Options Registry key.
"Closer inspection of the SFX archive revealed that it functions as a
password-protected backdoor by abusing WinRAR setup options rather than
containing any malware," Minton explained.

Specifically, the file is engineered to run PowerShell (powershell.exe), Command
Prompt (cmd.exe), and Task Manager (taskmgr.exe) with NT AUTHORITY\SYSTEM
privileges by providing the right password to the archive.
"This type of attack is likely to remain undetected by traditional antivirus
software that is looking for malware inside of an archive (which is often also
password-protected) rather than the behavior from an SFX archive decompressor
stub," Minton added.
This is not the first time SFX files have been employed
in attacks as a means for attackers to stay undetected. In September 2022,
Kaspersky disclosed a malware campaign that utilized links to such
password-protected files to propagate RedLine Stealer.
A month later, the infamous Emotet botnet was observed sending out an SFX
archive that, once opened by a user, would automatically extract a second
password-protected SFX archive, enter the password, and execute its content
without further user interaction using a batch script.
To mitigate threats posed by this attack vector, it's recommended that SFX
archives are analyzed through unarchiving software to identify any potential
scripts or binaries that are set to extract and run upon execution.
Typhon Reborn Stealer Malware Resurfaces with Advanced Evasion Techniques
5.4.23 Virus
The Hacker News
The threat actor behind the information-stealing malware
known as Typhon Reborn has resurfaced with an updated version (V2) that packs in
improved capabilities to evade detection and resist analysis.
The new version is offered for sale on the criminal underground for $59 per
month, $360 per year, or alternatively, for $540 for a lifetime subscription.
"The stealer can harvest and exfiltrate sensitive information and uses the
Telegram API to send stolen data to attackers," Cisco Talos researcher Edmund
Brumaghin said in a Tuesday report.
Typhon was first documented by Cyble in August 2022, detailing its myriad
features, including hijacking clipboard content, capturing screenshots, logging
keystrokes, and stealing data from crypto wallet, messaging, FTP, VPN, browser,
and gaming apps.
Based on another stealer malware called Prynt Stealer, Typhon is also capable of
delivering the XMRig cryptocurrency miner. In November 2022, Palo Alto Networks
Unit 42 unearthed an updated version dubbed Typhon Reborn.
"This new version has increased anti-analysis techniques and it was modified to
improve the stealer and file grabber features," Unit 42 said, pointing out the
removal of existing features like keylogging and cryptocurrency mining in an
apparent attempt to lower the chances of detection.
The latest V2 variant, per Cisco Talos, was marketed by its developer on January
31, 2023, on the Russian language dark web forum XSS.
"Typhon Reborn stealer is a heavily refactored and improved version of the older
and unstable Typhon Stealer," the malware author said, in addition to touting
its inexpensive price and the absence of any backdoors.
Like other malware, V2 comes with options to avoid infecting systems that are
located in the Commonwealth of Independent States (CIS) countries. It, however,
notably excludes Ukraine and Georgia from the list.
Typhon Reborn Stealer Malware
Besides incorporating more anti-analysis and
anti-virtualization checks, Typhon Reborn V2 removes its persistence features,
instead opting to terminate itself after exfiltrating the data.
The malware ultimately transmits the collected data in a compressed archive via
HTTPS using the Telegram API, marking continued abuse of the messaging platform.
"Once the data has been successfully transmitted to the attacker, the archive is
then deleted from the infected system," Brumaghin said. "The malware then calls
[a self-delete function] to terminate execution."
The findings come as Cyble
disclosed a new Python-based stealer malware named Creal that targets
cryptocurrency users via phishing sites mimicking legitimate crypto mining
services like Kryptex.
The malware is no different from Typhon Reborn in that it's equipped to siphon
cookies and passwords from Chromium-based web browsers as well as data from
instant messaging, gaming, and crypto wallet apps.
That said, the malware's source code is available on GitHub, thereby allowing
other threat actors to alter the malware to suit their needs and making it a
potent threat.
"Creal Stealer is capable of exfiltrating data using Discord webhooks and
multiple file-hosting and sharing platforms such as Anonfiles and Gofile," Cyble
said in a report published last week.
"The trend of using open source code in malware is increasing among
cybercriminals, since it allows them to create sophisticated and customized
attacks with minimal expenses."
Arid Viper Hacking Group Using Upgraded Malware in Middle East Cyber Attacks
5.4.23 Virus
The Hacker News
The threat actor known as Arid Viper has been observed
using refreshed variants of its malware toolkit in its attacks targeting
Palestinian entities since September 2022.
Symantec, which is tracking the group under its insect-themed moniker Mantis,
said the adversary is "going to great lengths to maintain a persistent presence
on targeted networks."
Also known by the names APT-C-23 and Desert Falcon, the hacking group has been
linked to attacks aimed at Palestine and the Middle East at least since 2014.
Mantis has used an arsenal of homemade malware tools such as ViperRat,
FrozenCell (aka VolatileVenom), and Micropsia to execute and conceal its
campaigns across Windows, Android, and iOS platforms.
The threat actors are believed to be native Arabic speakers and based in
Palestine, Egypt, and Turkey, according to a report published by Kaspersky in
February 2015. Prior public reporting has also tied the group to the cyber
warfare division of Hamas.
In April 2022, high-profile Israeli individuals employed in sensitive defense,
law enforcement, and emergency services organizations were observed being
targeted with a novel Windows backdoor dubbed BarbWire.
Attack sequences mounted by the group typically employ spear-phishing emails and
fake social credentials to lure targets into installing malware on their
devices.
The most recent attacks detailed by Symantec entail the use of updated versions
of its custom Micropsia and Arid Gopher implants to breach targets before
engaging in credential theft and exfiltration of stolen data.
Arid Gopher, an executable coded in the Go programming language, is a variant of
the Micropsia malware that was first documented by Deep Instinct in March 2022.
The shift to Go is not unusual as it allows the malware to stay under the radar.
Micropsia, alongside its ability to launch secondary payloads (like Arid
Gopher), is also designed to log keystrokes, take screenshots, and save
Microsoft Office files within RAR archives for exfiltration using a bespoke
Python-based tool.
"Arid Gopher, like its predecessor Micropsia, is an
info-stealer malware, whose intent is to establish a foothold, collect sensitive
system information, and send it back to a C2 (command-and-control) network,"
Deep Instinct said at the time.
Evidence gathered by Symantec shows that Mantis moved to deploy three distinct
versions of Micropsia and Arid Gopher on three sets of workstations between
December 18, 2022, and January 12, 2023, as a way of retaining access.
Arid Gopher, for its part, has received regular updates and complete code
rewrites, with the attackers "aggressively mutating the logic between variants"
as a detection evasion mechanism.
"Mantis appears to be a determined adversary, willing to put time and effort
into maximizing its chances of success, as evidenced by extensive malware
rewriting and its decision to compartmentalize attacks against single
organizations into multiple separate strands to reduce the chances of the entire
operation being detected," Symantec concluded.
Chinese RedGolf Group Targeting Windows and Linux Systems with KEYPLUG Backdoor
1.4.23 Virus
The Hacker News
A Chinese state-sponsored threat activity group tracked
as RedGolf has been attributed to the use of a custom Windows and Linux backdoor
called KEYPLUG.
"RedGolf is a particularly prolific Chinese state-sponsored threat actor group
that has likely been active for many years against a wide range of industries
globally," Recorded Future told The Hacker News.
"The group has shown the ability to rapidly weaponize newly reported
vulnerabilities (e.g. Log4Shell and ProxyLogon) and has a history of developing
and using a large range of custom malware families."
The use of KEYPLUG by Chinese threat actors was first disclosed by Google-owned
Manidant in March 2022 in attacks targeting multiple U.S. state government
networks between May 2021 and February 2022.
Then in October 2022, Malwarebytes detailed a separate set of attacks targeting
government entities in Sri Lanka in early August that leveraged a novel implant
dubbed DBoxAgent to deploy KEYPLUG.
Both these campaigns were attributed to Winnti (aka APT41, Barium, Bronze Atlas,
or Wicked Panda), which Recorded Future said "closely overlaps" with RedGolf.
"We have not observed specific victimology as part of the latest highlighted
RedGolf activity," Recorded Future said. "However, we believe this activity is
likely being conducted for intelligence purposes rather than financial gain due
to the overlaps with previously reported cyberespionage campaigns."
The cybersecurity firm, in addition to detecting a cluster of KEYPLUG samples
and operational infrastructure (codenamed GhostWolf) used by the hacking group
from at least 2021 to 2023, noted its use of other tools like Cobalt Strike and
PlugX.

The GhostWolf infrastructure, for its part, consists of 42 IP addresses that
function as KEYPLUG command-and-control. The adversarial collective has also
been observed utilizing a mixture of both traditionally registered domains and
Dynamic DNS domains, often featuring a technology theme, to act as communication
points for Cobalt Strike and PlugX.
"RedGolf will continue to demonstrate a high operational tempo and rapidly
weaponize vulnerabilities in external-facing corporate appliances (VPNs,
firewalls, mail servers, etc.) to gain initial access to target networks," the
company said.
"Additionally, the group will likely continue to adopt new
custom malware families to add to existing tooling such as KEYPLUG."
To defend against RedGolf attacks, organizations are recommended to apply
patches regularly, monitor access to external facing network devices, track and
block identified command-and-control infrastructure, and configure intrusion
detection or prevention systems to monitor for malware detections.
The findings come as Trend Micro revealed that it discovered more than 200
victims of Mustang Panda (aka Earth Preta) attacks as part of a far-reaching
cyber espionage effort orchestrated by various sub-groups associated with the
threat actor since 2022.
A majority of the cyber strikes have been detected in Asia, followed by Africa,
Europe, the Middle East, Oceania, North America, and South America.
"There are strong indications of intertwined traditional intelligence tradecraft
and cyber collection efforts, indicative of a highly coordinated and
sophisticated cyber espionage operation," Trend Micro said.
AlienFox Malware Targets API Keys and Secrets from AWS, Google, and Microsoft
Cloud Services
1.4.23
Virus The Hacker News
A
new "comprehensive toolset" called AlienFox is being distributed on Telegram as
a way for threat actors to harvest credentials from API keys and secrets from
popular cloud service providers.
"The spread of AlienFox represents an unreported trend towards attacking more
minimal cloud services, unsuitable for crypto mining, in order to enable and
expand subsequent campaigns," SentinelOne security researcher Alex Delamotte
said in a report shared with The Hacker News.
The cybersecurity company characterized the malware as highly modular and
constantly evolving to accommodate new features and performance improvements.
The primary use of AlienFox is to enumerate misconfigured hosts via scanning
platforms like LeakIX and SecurityTrails, and subsequently leverage various
scripts in the toolkit to extract credentials from configuration files exposed
on the servers.
Specifically, it entails searching for susceptible servers associated with
popular web frameworks, including Laravel, Drupal, Joomla, Magento, Opencart,
Prestashop, and WordPress.
Recent versions of the tool incorporate the ability to establish persistence on
an Amazon Web Services (AWS) account and escalate privileges as well as automate
spam campaigns through the compromised accounts.

Attacks involving AlienFox are said to be opportunistic, with the scripts
capable of gathering sensitive data pertaining to AWS, Bluemail, Exotel, Google
Workspace, Mailgun, Mandrill, Microsoft 365, Sendgrid, Twilio, Zimbra, and Zoho.
Two such scripts are AndroxGh0st and GreenBot, which were previously documented
by Lacework and Permiso p0 Labs.
While Androxgh0st is designed to parse a configuration file for specific
variables and pull out their values for follow-on abuse, GreenBot (aka
Maintance) contains an "AWS persistence script that creates a new administrator
account and deletes the hijacked legitimate account."
Maintance further
incorporates licensing checks, suggesting that the script is being offered as a
commercial tool, and the ability to perform reconnaissance on the web server.
SentinelOne said it identified three different variants of the malware (from v2
to v4) dating back to February 2022. A notable functionality of AlienFoxV4 is
its ability to check if an email address is already linked to an Amazon.com
retail account, and if not, create a new account using that address.
To mitigate threats posed by AlienFox, organizations are recommended to adhere
to configuration management best practices and follow the principle of least
privilege (PoLP).
"The AlienFox toolset demonstrates another stage in the evolution of cybercrime
in the cloud," Delamotte said. "For victims, compromise can lead to additional
service costs, loss in customer trust, and remediation costs."
Trojanized TOR Browser Installers Spreading Crypto-Stealing Clipper Malware
29.3.23 Virus
The Hacker News

Trojanized installers for the TOR anonymity browser are being used to target
users in Russia and Eastern Europe with clipper malware designed to siphon
cryptocurrencies since September 2022.
"Clipboard injectors [...] can be silent for years, show no network activity or
any other signs of presence until the disastrous day when they replace a crypto
wallet address," Vitaly Kamluk, director of global research and analysis team
(GReAT) for APAC at Kaspersky, said.
Another notable aspect of clipper malware is that its nefarious functions are
not triggered unless the clipboard data meet specific criteria, making it more
evasive.
It's not immediately clear how the installers are distributed, but evidence
points to the use of torrent downloads or some unknown third-party source since
the Tor Project's website has been subjected to blockades in Russia in recent
years.
Regardless of the method used, the installer launches the legitimate executable,
while also simultaneously launching the clipper payload that's designed to
monitor the clipboard content.
"If the clipboard contains text, it scans the contents with a set of embedded
regular expressions," Kamluk noted. "Should it find a match, it is replaced with
one randomly chosen address from a hardcoded list."

Each sample is packed with thousands of possible replacement addresses that's
selected at random. It also comes with the ability to disable the malware by
means of a special hotkey combination (Ctrl+Alt+F10), an option likely added
during the testing phase.
The Russian cybersecurity firm said it recorded roughly 16,000 detections, of
which a majority are registered in Russia and Ukraine, followed by the U.S.,
Germany, Uzbekistan, Belarus, China, the Netherlands, the U.K., and France. In
all, the threat has been spotted in 52 countries worldwide.
The scheme is
estimated to have netted the operators almost $400,00 in illicit profits through
the theft of Bitcoin, Litecoin, Ether, and Dogecoin. The amount of Monero assets
plundered is not known owing to the privacy features built into the service.
It's suspected that the campaign could be larger in scope due to the possibility
that the threat actors could be leveraging other software installers and
hitherto unseen delivery methods to target unwary users.
To secure against such threats, it's always recommended to download software
only from reliable and trusted sources.
IcedID Malware Shifts Focus from Banking Fraud to Ransomware Delivery
28.3.23 Virus
The Hacker News

Multiple threat actors have been observed using two new variants of the IcedID
malware in the wild with more limited functionality that removes functionality
related to online banking fraud.
IcedID, also known as BokBot, started off as a banking trojan in 2017. It's also
capable of delivering additional malware, including ransomware.
"The well-known IcedID version consists of an initial loader which contacts a
Loader [command-and-control] server, downloads the standard DLL Loader, which
then delivers the standard IcedID Bot," Proofpoint said in a new report
published Monday.
One of the new versions is a Lite variant that was previously highlighted as
being dropped as a follow-on payload by the Emotet malware in November 2022.
Also newly observed in February 2023 is a Forked variant of IcedID.
Both these variants are designed to drop what's called a Forked version of
IcedID Bot that leaves out the web injects and backconnect functionality that
would typically be used for banking fraud, the enterprise security firm noted.
"It is likely a cluster of threat actors is using modified variants to pivot the
malware away from typical banking trojan and banking fraud activity to focus on
payload delivery, which likely includes prioritizing ransomware delivery,"
Proofpoint noted.
The February campaign has been tied to a new group christened TA581, with the
threat actor distributing the Forked variant using weaponized Microsoft OneNote
attachments. Another malware used by TA581 is the Bumblebee loader.
In all, the Forked IcedID variant has been employed in seven different campaigns
to date, some of which have been undertaken by initial access brokers (IABs).
The use of existing Emotet infections to deliver the Lite variant has raised the
possibility of a potential partnership between Emotet developers and IcedID
operators.
"While historically IcedID's main function was a banking trojan, the removal of
banking functionality aligns with the overall landscape shift away from banking
malware and an increasing focus on being a loader for follow-on infections,
including ransomware," the researchers said.
Stealthy DBatLoader Malware Loader Spreading Remcos RAT and Formbook in Europe
28.3.23 Virus
The Hacker News

A new phishing campaign has set its sights on European entities to distribute
Remcos RAT and Formbook via a malware loader dubbed DBatLoader.
"The malware payload is distributed through WordPress websites that have
authorized SSL certificates, which is a common tactic used by threat actors to
evade detection engines," Zscaler researchers Meghraj Nandanwar and Satyam Singh
said in a report published Monday.
The findings build upon a previous report from SentinelOne last month that
detailed phishing emails containing malicious attachments that masquerade as
financial documents to activate the infection chain.
Some of the file formats used to distribute the DBatLoader payload concern the
use of a multi-layered obfuscated HTML file and OneNote attachments.
The development adds to growing abuse of OneNote files as an initial vector for
malware distribution since late last year in response to Microsoft's decision to
block macros by default in files downloaded from the internet.
DBatLoader, also called ModiLoader and NatsoLoader, is a Delphi-based malware
that's capable of delivering follow-on payloads from cloud services like Google
Drive and Microsoft OneDrive, while also adopting image steganography techniques
to evade detection engines.

One notable aspect of the attack is the use of mock trusted directories such as
"C:\Windows \System32" (note the trailing space after Windows) to bypass User
Account Control (UAC) and escalate privileges.
A caveat here is that the directories cannot be directly created from within the
Windows Explorer user interface, instead requiring the attacker to rely on a
script to accomplish the task and copy to the folder a rogue DLL and a
legitimate executable (easinvoker.exe) that's vulnerable to DLL hijacking in
order to load the DLL payload.
This enables the attackers to conduct elevated activities without alerting
users, including establishing persistence and adding the "C:\Users" directory to
the Microsoft Defender exclusion list to avoid getting scanned.
To mitigate risks posed by DBatLoader, it's advised to monitor process
executions that involve filesystem paths with trailing spaces and consider
configuring Windows UAC to Always notify.
Malicious Python Package Uses Unicode Trickery to Evade Detection and Steal Data
25.3.23 Virus
The Hacker News
A malicious Python package on the Python Package Index (PyPI) repository has
been found to use Unicode as a trick to evade detection and deploy an
info-stealing malware.
The package in question, named onyxproxy, was uploaded to PyPI on March 15,
2023, and comes with capabilities to harvest and exfiltrate credentials and
other valuable data. It has since been taken down, but not before attracting a
total of 183 downloads.
According to software supply chain security firm Phylum, the package
incorporates its malicious behavior in a setup script that's packed with
thousands of seemingly legitimate code strings.
These strings include a mix of bold and italic fonts and are still readable and
can be parsed by the Python interpreter, only to activate the execution of the
stealer malware upon installation of the package.
"An obvious and immediate benefit of this strange scheme is readability," the
company noted. "Moreover, these visible differences do not prevent the code from
running, which it does."
This is made possible owing to the use of Unicode variants of what appears to be
the same character (aka homoglyphs) to camouflage its true colors (e.g., self
vs. 𝘀𝘦𝘭𝘧) among innocuous-looking functions and variables.
The use of Unicode to inject vulnerabilities into source code was previously
disclosed by Cambridge University researchers Nicholas Boucher and Ross Anderson
in an attack technique dubbed Trojan Source.
What the method lacks in sophistication, it makes up for it by creating a novel
piece of obfuscated code, despite exhibiting telltale signs of copy-paste
efforts from other sources.
The development highlights continued attempts on part of threat actors to find
new ways to slip through string-matching based defenses, leveraging "how the
Python interpreter handles Unicode to obfuscate their malware."
On a related note, Canadian cybersecurity company PyUp detailed the discovery of
three new fraudulent Python packages – aiotoolbox, asyncio-proxy, and pycolorz –
that were downloaded cumulatively over 1,000 times and designed to retrieve
obfuscated code from a remote server.
ScarCruft's Evolving Arsenal: Researchers Reveal New Malware Distribution
Techniques
22.3.23
Virus The Hacker News

The North Korean advanced persistent threat (APT) actor dubbed ScarCruft is
using weaponized Microsoft Compiled HTML Help (CHM) files to download additional
malware.
According to multiple reports from AhnLab Security Emergency response Center
(ASEC), SEKOIA.IO, and Zscaler, the development is illustrative of the group's
continuous efforts to refine and retool its tactics to sidestep detection.
"The group is constantly evolving its tools, techniques, and procedures while
experimenting with new file formats and methods to bypass security vendors,"
Zscaler researchers Sudeep Singh and Naveen Selvan said in a new analysis
published Tuesday.
ScarCruft, also tracked under the names APT37, Reaper, RedEyes, and Ricochet
Chollima, has exhibited an increased operational tempo since the start of the
year, targeting various South Korean entities for espionage purposes. It is
known to be active since at least 2012.
Last month, ASEC disclosed a campaign that employed HWP files that take
advantage of a security flaw in the Hangul word processing software to deploy a
backdoor referred to as M2RAT.
But new findings reveal the threat actor is also using other file formats such
as CHM, HTA, LNK, XLL, and macro-based Microsoft Office documents in its
spear-phishing attacks against South Korean targets.

These infection chains often serve to display a decoy file and deploy an updated
version of a PowerShell-based implant known as Chinotto, which is capable of
executing commands sent by a server and exfiltrating sensitive data.
Some of the new capabilities of Chinotto include capturing screenshots every
five seconds and logging keystrokes. The captured information is saved in a ZIP
archive and sent to a remote server.
The insights about ScarCruft's various
attack vectors come from a GitHub repository maintained by the adversarial
collective to host malicious payloads since October 2020.
"The threat actor was able to maintain a GitHub repository, frequently staging
malicious payloads for more than two years without being detected or taken
down," Zscaler researchers said.
Outside of malware distribution, ScarCruft has also been observed serving
credential phishing webpages targeting multiple email and cloud services such as
Naver, iCloud, Kakao, Mail.ru, and 163.com.

It's however not clear how these pages are accessed by the victims, raising the
possibility that they may have been embedded inside iframes on websites
controlled by the attacker or sent as HTML attachments via email.
Also discovered by SEKOIA.IO is a piece of malware named AblyGo, a backdoor
written in Go that utilizes the Ably real-time messaging framework to receive
commands.
The use of CHM files to smuggle malware appears to be catching on with other
North Korea-affiliated groups as well, with ASEC uncovering a phishing campaign
orchestrated by Kimsuky to distribute a backdoor responsible for harvesting
clipboard data and recording keystrokes.
Rogue NuGet Packages Infect .NET Developers with Crypto-Stealing Malware
22.3.23 Virus
The Hacker News
The NuGet repository is the target of a new "sophisticated and highly-malicious
attack" aiming to infect .NET developer systems with cryptocurrency stealer
malware.
The 13 rogue packages, which were downloaded more than 160,000 times over the
past month, have since been taken down.
"The packages contained a PowerShell script that would execute upon installation
and trigger a download of a 'second stage' payload, which could be remotely
executed," JFrog researchers Natan Nehorai and Brian Moussalli said.
While NuGet packages have been in the past found to contain vulnerabilities and
be abused to propagate phishing links, the development marks the first-ever
discovery of packages with malicious code.
Three of the most downloaded packages – Coinbase.Core, Anarchy.Wrapper.Net, and
DiscordRichPresence.API – alone accounted for 166,000 downloads, although it's
also possible that the threat actors artificially inflated the download counts
using bots to make them appear more legitimate.
The use of Coinbase and Discord underscores the continued reliance on
typosquatting techniques, in which fake packages are assigned names that are
similar to legitimate packages, in order to trick developers into downloading
them.
The malware incorporated within the software packages functions as a dropper
script and is designed to automatically run a PowerShell code that retrieves a
follow-on binary from a hard-coded server.

As an added obfuscation mechanism, some packages did not embed a malicious
payload directly, instead fetching it via another booby-trapped package as a
dependency.
Even more troublingly, the connection to the command-and-control (C2) server
occurs over HTTP (as opposed to HTTPS), rendering it vulnerable to an
adversary-in-the-middle (AiTM) attack.
The second-stage malware is what JFrog describes as a "completely custom
executable payload" that can be dynamically switched at will since it's
retrieved from the C2 server.
The second-stage delivers several capabilities
that include a crypto stealer and an auto-updater module that pings the C2
server for an updated version of the malware.
The findings come as the software supply chain has become an increasingly
lucrative pathway to compromise developers' systems and stealthily propagate
backdoored code to downstream users.
"This proves that no open source repository is safe from malicious actors,"
Shachar Menashe, senior director at JFrog Security Research, said in a statement
shared with The Hacker News.
".NET developers using NuGet are still at high risk of malicious code infecting
their environments and should take caution when curating open-source components
for use in their builds – and at every step of the software development
lifecycle – to ensure the software supply chain remains secure."
NAPLISTENER: New Malware in REF2924 Group's Arsenal for Bypassing Detection
22.3.23 Virus
The Hacker News

The threat group tracked as REF2924 has been observed deploying previously
unseen malware in its attacks aimed at entities in South and Southeast Asia.
The malware, dubbed NAPLISTENER by Elastic Security Labs, is an HTTP listener
programmed in C# and is designed to evade "network-based forms of detection."
REF2924 is the moniker assigned to an activity cluster linked to attacks against
an entity in Afghanistan as well as the Foreign Affairs Office of an ASEAN
member in 2022.
The threat actor's modus operandi suggests overlaps with another hacking group
dubbed ChamelGang, which was documented by Russian cybersecurity company
Positive Technologies in October 2021.
Attacks orchestrated by the group are said to have exploited internet-exposed
Microsoft Exchange servers to deploy backdoors such as DOORME, SIESTAGRAPH, and
ShadowPad.
DOORME, an Internet Information Services (IIS) backdoor module, provides remote
access to a contested network and executes additional malware and tools.
SIESTAGRAPH employs Microsoft's Graph API for command-and-control via Outlook
and OneDrive, and comes with capabilities to run arbitrary commands through
Command Prompt, upload and download files to and from OneDrive, and take
screenshots.
ShadowPad is a privately sold modular backdoor and a successor of PlugX,
enabling threat actors to maintain persistent access to compromised computers
and run shell commands and follow-on payloads.
The use of ShadowPad is noteworthy as it indicates a potential link to
China-based hacking groups, which are known to utilize the malware in various
campaigns over the years.
To this list of expanding malware arsenal used by REF2924 joins NAPLISTENER
("wmdtc.exe"), which masquerades as a legitimate service Microsoft Distributed
Transaction Coordinator ("msdtc.exe") in an attempt to fly under the radar and
establish persistent access.
"NAPLISTENER creates an HTTP request listener
that can process incoming requests from the internet, reads any data that was
submitted, decodes it from Base64 format, and executes it in memory," security
researcher Remco Sprooten said.
Code analysis suggests the threat actor borrows or repurposes code from open
source projects hosted on GitHub to develop its own tools, a sign that REF2924
may be actively honing a raft of cyber weapons.
The findings also come as a Vietnamese organization was targeted in late
December 2022 by a previously unknown Windows backdoor codenamed PIPEDANCE to
facilitate post-compromise and lateral movement activities, including deploying
Cobalt Strike.
New 'Bad Magic' Cyber Threat Disrupts Ukraine's Key Sectors Amid War
22.3.23 Virus
The Hacker News

Amid the ongoing war between Russia and Ukraine, government, agriculture, and
transportation organizations located in Donetsk, Lugansk, and Crimea have been
attacked as part of an active campaign that drops a previously unseen, modular
framework dubbed CommonMagic.
"Although the initial vector of compromise is unclear, the details of the next
stage imply the use of spear phishing or similar methods," Kaspersky said in a
new report.
The Russian cybersecurity company, which detected the attacks in October 2022,
is tracking the activity cluster under the name "Bad Magic."
Attack chains entail the use of booby-trapped URLS pointing to a ZIP archive
hosted on a malicious web server. The file, when opened, contains a decoy
document and a malicious LNK file that culminates in the deployment of a
backdoor named PowerMagic.
Written in PowerShell, PowerMagic establishes contact with a remote server and
executes arbitrary commands, the results of which are exfiltrated to cloud
services like Dropbox and Microsoft OneDrive.

PowerMagic also serves as a conduit to deliver the CommonMagic framework, a set
of executable modules that are designed to carry out specific tasks such as
interacting with the command-and-control (C2) server, encrypting and decrypting
C2 traffic, and executing plugins.
Two of the plugins discovered so far come with capabilities to capture
screenshots every three seconds and gather files of interest from connected USB
devices.
Kaspersky said it found no evidence linking the operation and its tooling to any
known threat actor or group. The earliest ZIP archive attachment dates back to
September 2021, indicating that the campaign may have flown under the radar for
more than 1.5 years.
"Geopolitics always affect the cyberthreat landscape and lead to the emergence
of new threats," Kaspersky's Leonid Besverzhenko said. "Although the malware and
techniques employed in the CommonMagic campaign are not particularly
sophisticated, the use of cloud storage as the command-and-control
infrastructure is noteworthy."
New ShellBot DDoS Malware Variants Targeting Poorly Managed Linux Servers
22.3.23 Virus
The Hacker News
Poorly managed Linux SSH servers are being targeted as
part of a new campaign that deploys different variants of a malware called
ShellBot.
"ShellBot, also known as PerlBot, is a DDoS Bot malware developed in Perl and
characteristically uses IRC protocol to communicate with the C&C server," AhnLab
Security Emergency response Center (ASEC) said in a report.
ShellBot is installed on servers that have weak credentials, but only after
threat actors make use of scanner malware to identify systems that have SSH port
22 open.
A list of known SSH credentials is used to initiate a dictionary attack to
breach the server and deploy the payload, after which it leverages the Internet
Relay Chat (IRC) protocol to communicate with a remote server.
This encompasses the ability to receive commands that allows ShellBot to carry
out DDoS attacks and exfiltrate harvested information.
ASEC said it identified three different ShellBot versions – LiGhT's Modded
perlbot v2, DDoS PBot v2.0, and PowerBots (C) GohacK – the first two of which
offer a variety of DDoS attack commands using HTTP, TCP, and UDP protocols.
PowerBots, on the other hand, comes with more backdoor-like capabilities to
grant reverse shell access and upload arbitrary files from the compromised host.
The findings come nearly three months after ShellBot was employed in attacks
aimed at Linux servers that also distributed cryptocurrency miners via a shell
script compiler.
"If ShellBot is installed, Linux servers can be used as
DDoS Bots for DDoS attacks against specific targets after receiving a command
from the threat actor," ASEC said. "Moreover, the threat actor could use various
other backdoor features to install additional malware or launch different types
of attacks from the compromised server."
The development also comes as Microsoft revealed a gradual increase in the
number of DDoS attacks targeting healthcare organizations hosted in Azure,
surging from 10-20 attacks in November 2022 to 40-60 attacks daily in February
2023.
New DotRunpeX Malware Delivers Multiple Malware Families via Malicious Ads
21.3.23 Virus
The Hacker News

A new piece of malware dubbed dotRunpeX is being used to distribute numerous
known malware families such as Agent Tesla, Ave Maria, BitRAT, FormBook,
LokiBot, NetWire, Raccoon Stealer, RedLine Stealer, Remcos, Rhadamanthys, and
Vidar.
"DotRunpeX is a new injector written in .NET using the Process Hollowing
technique and used to infect systems with a variety of known malware families,"
Check Point said in a report published last week.
Said to be in active development, dotRunpeX arrives as a second-stage malware in
the infection chain, often deployed via a downloader (aka loader) that's
transmitted through phishing emails as malicious attachments.
Alternatively, it's known to leverage malicious Google Ads on search result
pages to direct unsuspecting users searching for popular software such as
AnyDesk and LastPass to copycat sites hosting trojanized installers.
The latest DotRunpeX artifacts, first spotted in October 2022, add an extra
obfuscation layer by using the KoiVM virtualizing protector.
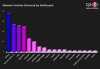
It's worth pointing out that the findings dovetail with a malvertising campaign
documented by SentinelOne last month in which the loader and the injector
components were collectively referred to as MalVirt.
Check Point's analysis has further revealed that "each dotRunpeX sample has an
embedded payload of a certain malware family to be injected," with the injector
specifying a list of anti-malware processes to be terminated.
This, in turn,
is made possible by abusing a vulnerable process explorer driver (procexp.sys)
that's incorporated into dotRunpeX so as to obtain kernel mode execution.
There are signs that dotRunpeX could be affiliated to Russian-speaking actors
based on the language references in the code. The most frequently delivered
malware families delivered by the emerging threat include RedLine, Raccoon,
Vidar, Agent Tesla, and FormBook.
Mispadu Banking Trojan Targets Latin America: 90,000+ Credentials Stolen
21.3.23 Virus
The Hacker News
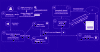
A banking trojan dubbed Mispadu has been linked to multiple spam campaigns
targeting countries like Bolivia, Chile, Mexico, Peru, and Portugal with the
goal of stealing credentials and delivering other payloads.
The activity, which commenced in August 2022, is currently ongoing, Ocelot Team
from Latin American cybersecurity firm Metabase Q said in a report shared with
The Hacker News.
Mispadu (aka URSA) was first documented by ESET in November 2019, describing its
ability to perpetrate monetary and credential theft and act as a backdoor by
taking screenshots and capturing keystrokes.
"One of their main strategies is to compromise legitimate websites, searching
for vulnerable versions of WordPress, to turn them into their
command-and-control server to spread malware from there, filtering out countries
they do not wish to infect, dropping different type of malware based on the
country being infected," researchers Fernando García and Dan Regalado said.
It's also said to share similarities with other banking trojans targeting the
region, like Grandoreiro, Javali, and Lampion. Attack chains involving the
Delphi malware leverage email messages urging recipients to open fake overdue
invoices, thereby triggering a multi-stage infection process.

Should a victim open the HTML attachment sent via the spam email, it verifies
that the file was opened from a desktop device and then redirects to a remote
server to fetch the first-stage malware.
The RAR or ZIP archive, when launched, is designed to make use of rogue digital
certificates – one which is the Mispadu malware and the other, an AutoIT
installer – to decode and execute the trojan by abusing the legitimate certutil
command-line utility.
Mispadu is equipped to gather the list of antivirus solutions installed on the
compromised host, siphon credentials from Google Chrome and Microsoft Outlook,
and facilitate the retrieval of additional malware.
This includes an
obfuscated Visual Basic Script dropper that serves to download another payload
from a hard-coded domain, a .NET-based remote access tool that can run commands
issued by an actor-controlled server, and a loader written in Rust that, in
turn, executes a PowerShell loader to run files directly from memory.
What's more, the malware utilizes malicious overlay screens to obtain
credentials associated with online banking portals and other sensitive
information.
Metabase Q noted that the certutil approach has allowed Mispadu to bypass
detection by a wide range of security software and harvest over 90,000 bank
account credentials from over 17,500 unique websites.
Emotet Rises Again: Evades Macro Security via OneNote Attachments
21.3.23
Virus The Hacker News
The
notorious Emotet malware, in its return after a short hiatus, is now being
distributed via Microsoft OneNote email attachments in an attempt to bypass
macro-based security restrictions and compromise systems.
Emotet, linked to a threat actor tracked as Gold Crestwood, Mummy Spider, or
TA542, continues to be a potent and resilient threat despite attempts by law
enforcement to take it down.
A derivative of the Cridex banking worm – which was subsequently replaced by
Dridex around the same time GameOver Zeus was disrupted in 2014 – Emotet has
evolved into a "monetized platform for other threat actors to run malicious
campaigns on a pay-per-install (PPI) model, allowing theft of sensitive data and
ransom extortion."
While Emotet infections have acted as a conduit to deliver Cobalt Strike,
IcedID, Qakbot, Quantum ransomware, and TrickBot, its return in late 2021 was
facilitated by means of TrickBot.
"Emotet is known for extended periods of inactivity, often occurring multiple
times per year, where the botnet maintains a steady-state but does not deliver
spam or malware," Secureworks notes in its profile of the actor.

The dropper malware is commonly distributed through spam emails containing
malicious attachments. But with Microsoft taking steps to block macros in
downloaded Office files, OneNote attachments have emerged as an appealing
alternative pathway.
"The OneNote file is simple but yet effective at social engineering users with a
fake notification stating that the document is protected," Malwarebytes
disclosed in a new alert. "When instructed to double-click on the View button,
victims will inadvertently double-click on an embedded script file instead."

The Windows Script File (WSF) is engineered to retrieve and execute the Emotet
binary payload from a remote server. Similar findings have been echoed by Cyble,
IBM X-Force, and Palo Alto Networks Unit 42.
That said, Emotet still continues to use booby-trapped documents containing
macros to deliver the malicious payload, employing social engineering lures to
entice users into enabling macros to activate the attack chain.
Such
documents have been observed to leverage a technique called decompression bomb
to conceal a very large file (over 550 MB) within ZIP archive attachments to fly
under the radar, according to multiple reports from Cyble, Deep Instinct,
Hornetsecurity, and Trend Micro.
This is achieved by padding 00-byte at the end of the document to artificially
inflate the file size so as to exceed the limitations imposed by anti-malware
solutions.
The latest development is a sign of the operators' flexibility and agility in
switching attachment types for initial delivery to evade detection signatures.
It also comes amid a spike in threat actors using OneNote documents to
distribute a wide range of malware such as AsyncRAT, Icedid, RedLine Stealer,
Qakbot, and XWorm.
According to Trellix, a majority of the malicious OneNote detections in 2023
have been reported in the U.S., South Korea, Germany, Saudi Arabia, Poland,
India, the U.K., Italy, Japan, and Croatia, with manufacturing, high-tech,
telecom, finance, and energy emerging as the top targeted sectors.
FakeCalls Vishing Malware Targets South Korean Users via Popular Financial Apps
18.3.23 Virus
The Hacker News
An Android voice phishing (aka vishing) malware campaign
known as FakeCalls has reared its head once again to target South Korean users
under the guise of over 20 popular financial apps.
"FakeCalls malware possesses the functionality of a Swiss army knife, able not
only to conduct its primary aim but also to extract private data from the
victim's device," cybersecurity firm Check Point said.
FakeCalls was previously documented by Kaspersky in April 2022, describing the
malware's capabilities to imitate phone conversations with a bank customer
support agent.
In the observed attacks, users who install the rogue banking app are enticed
into calling the financial institution by offering a fake low-interest loan.
At the point where the phone call actually happens, a pre-recorded audio with
instructions from the real bank is played. Simultaneously, the malware conceals
the phone number with the bank's legitimate number to give the impression that a
conversation is happening with an actual bank employee on the other end.
The ultimate goal of the campaign to get the victim's credit card information,
which the threat actors claim is required to qualify for the non-existent loan.
The malicious app also requests for intrusive permissions so as to harvest
sensitive data, including live audio and video streams, from the compromised
device, which are then exfiltrated to a remote server.
The latest FakeCalls samples further implement various techniques to stay under
the radar. One of the methods involves adding a large number of files inside
nested directories to the APK's asset folder, causing the length of the file
name and path to breach the 300-character limit.
"The malware developers took special care with the technical aspects of their
creation as well as implementing several unique and effective anti-analysis
techniques," Check Point said. "In addition, they devised mechanisms for
disguised resolution of the command-and-control servers behind the operations."

While the attack exclusively focuses on South Korea, the cybersecurity company
has warned that the same tactics can be repurposed to target other regions
across the world.
The findings also come as Cyble shed light on two Android banking trojans dubbed
Nexus and GoatRAT that can harvest valuable data and carry out financial fraud.
Nexus, a rebranded version of SOVA, also incorporates a ransomware module that
encrypts the stored files and can abuse Android's accessibility services to
extract seed phrases from cryptocurrency wallets.
In contrast, GoatRAT is
designed to target Brazilian banks and joins the likes of BrasDex and PixPirate
to commit fraudulent money transfer over the PIX payments platform while
displaying a fake overlay window to hide the activity.
The development is part of a growing trend where threat actors have unleashed
increasingly sophisticated banking malware to automate the whole process of
unauthorized money transfers on infected devices.
Cybersecurity company Kaspersky said it detected 196,476 new mobile banking
trojans and 10,543 new mobile ransomware trojans in 2022, with China, Syria,
Iran, Yemen, and Iraq emerging as the top countries attacked by mobile malware,
including adware.
Spain, Saudi Arabia, Australia, Turkey, China, Switzerland, Japan, Colombia,
Italy, and India lead the list of top countries infected by mobile financial
threats.
"Despite the decline in overall malware installers, the continued growth of
mobile banking Trojans is a clear indication that cybercriminals are focusing on
financial gain," Kaspersky researcher Tatyana Shishkova said.
YoroTrooper Stealing Credentials and Information from Government and Energy
Organizations
15.3.23
Virus The Hacker News

A previously undocumented threat actor dubbed YoroTrooper has been targeting
government, energy, and international organizations across Europe as part of a
cyber espionage campaign that has been active since at least June 2022.
"Information stolen from successful compromises include credentials from
multiple applications, browser histories and cookies, system information and
screenshots," Cisco Talos researchers Asheer Malhotra and Vitor Ventura said in
a Tuesday analysis.
Prominent countries targeted include Azerbaijan, Tajikistan, Kyrgyzstan,
Turkmenistan, and other Commonwealth of Independent States (CIS) nations.
The threat actor is believed to be Russian-speaking owing to the victimology
patterns and the presence of Cyrillic snippets in some of the implants.
That said, the YoroTrooper intrusion set has been found to exhibit tactical
overlaps with the PoetRAT team that was documented in 2020 as leveraging
coronavirus-themed baits to strike government and energy sectors in Azerbaijan.
YoroTrooper's data gathering goals are realized through a combination of
commodity and open source stealer malware such as Ave Maria (aka Warzone RAT),
LodaRAT, Meterpreter, and Stink, with the infection chains using malicious
shortcut files (LNKs) and decoy documents wrapped in ZIP or RAR archives that
are propagated via spear-phishing.

The LNK files function as simple downloaders to execute an HTA file retrieved
from a remote server, which is then used to display a lure PDF document, while
stealthily launching a dropper to deliver a custom stealer that uses Telegram as
an exfiltration channel.
The use of LodaRAT is notable as it indicates that
the malware is being employed by multiple operators despite its attribution to
another group called Kasablanka, which has also been observed distributing Ave
Maria in recent campaigns targeting Russia.
Other auxiliary tools deployed by YoroTrooper consist of reverse shells and a
C-based custom keylogger that's capable of recording keystrokes and saving them
to a file on disk.
"It is worth noting that while this campaign began with the distribution of
commodity malware such as Ave Maria and LodaRAT, it has evolved significantly to
include Python-based malware," the researchers said.
"This highlights an increase in the efforts the threat actor is putting in,
likely derived from successful breaches during the course of the campaign."
GoBruteforcer: New Golang-Based Malware Breaches Web Servers Via Brute-Force
Attacks
14.3.23
Virus The Hacker News

A new Golang-based malware dubbed GoBruteforcer has been found targeting web
servers running phpMyAdmin, MySQL, FTP, and Postgres to corral the devices into
a botnet.
"GoBruteforcer chose a Classless Inter-Domain Routing (CIDR) block for scanning
the network during the attack, and it targeted all IP addresses within that CIDR
range," Palo Alto Networks Unit 42 researchers said.
"The threat actor chose CIDR block scanning as a way to get access to a wide
range of target hosts on different IPs within a network instead of using a
single IP address as a target."
The malware is mainly designed to single out Unix-like platforms running x86,
x64 and ARM architectures, with GoBruteforcer attempting to obtain access via a
brute-force attack using a list of credentials hard-coded into the binary.

If the attack proves to be successful, an internet relay chat (IRC) bot is
deployed on the victim server to establish communications with an
actor-controlled server.
GoBruteforcer also leverages a PHP web shell already installed in the victim
server to glean more details about the targeted network.
That said, the
exact initial intrusion vector used to deliver both GoBruteforcer and the PHP
web shell is undetermined as yet. Artifacts collected by the cybersecurity
company suggest active development efforts to evolve its tactics and evade
detection.
The findings are yet another indication of how threat actors are increasingly
adopting Golang to develop cross-platform malware. What's more, GoBruteforcer's
multi-scan capability enables it to breach a broad set of targets, making it a
potent threat.
"Web servers have always been a lucrative target for threat actors," Unit 42
said. "Weak passwords could lead to serious threats as web servers are an
indispensable part of an organization. Malware like GoBruteforcer takes
advantage of weak (or default) passwords."
Warning: AI-generated YouTube Video Tutorials Spreading Infostealer Malware
13.3.23 Virus
The Hacker News

Threat actors have been increasingly observed using AI-generated YouTube Videos
to spread a variety of stealer malware such as Raccoon, RedLine, and Vidar.
"The videos lure users by pretending to be tutorials on how to download cracked
versions of software such as Photoshop, Premiere Pro, Autodesk 3ds Max, AutoCAD,
and other products that are licensed products available only to paid users,"
CloudSEK researcher Pavan Karthick M said.
Just as the ransomware landscape comprises core developers and affiliates who
are in charge of identifying potential targets and actually carrying out the
attacks, the information stealer ecosystem also consists of threat actors known
as traffers who are recruited to spread the malware using different methods.
One of the popular malware distribution channels is YouTube, with CloudSEK
witnessing a 200-300% month-over-month increase in videos containing links to
stealer malware in the description section.
These links are often obfuscated using URL shorteners like Bitly and Cuttly, or
alternatively hosted on MediaFire, Google Drive, Discord, GitHub, and Telegram's
Telegra.ph.
In several instances, threat actors leverage data leaks and social engineering
to hijack legitimate YouTube accounts and push malware, often targeting popular
accounts to reach a large audience in a short span of time.

"Uploading to such accounts lends video legitimacy as well," Karthick explained.
"However, such Youtubers will report their account taker to YouTube and gain
access back to their accounts within a few hours. But in a few hours, hundreds
of users could have fallen prey."

More ominously, anywhere between five to 10 crack download videos are uploaded
to the video platform every hour, with the threat actors employing search engine
optimization (SEO) poisoning techniques to make the videos appear at the top of
the list.
Threat actors have also been observed to add fake comments to the uploaded
videos to further mislead and entice users into downloading the cracked
software.
The development comes amid a surge in new information stealer
variants like SYS01stealer, S1deload, Stealc, Titan, ImBetter, WhiteSnake, and
Lumma that are offered for sale and come with capabilities to plunder sensitive
data under the guise of popular apps and services.
The findings also follow the discovery of a ready-to-use toolkit called R3NIN
Sniffer that can enable threat actors to siphon payment card data from
compromised e-commerce websites.
To mitigate risks posed by stealer malware, users are recommended to enable
multi-factor authentication, refrain from clicking on unknown links, and avoid
downloading or using pirated software.

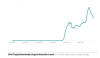



































































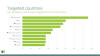





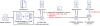



















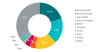



_small.jpg)
_small.png)