28.3.24 Vulnerebility The Hacker News
Microsoft Edge Bug Could Have Allowed Attackers to Silently Install Malicious Extensions
28.3.24 Vulnerebility The Hacker News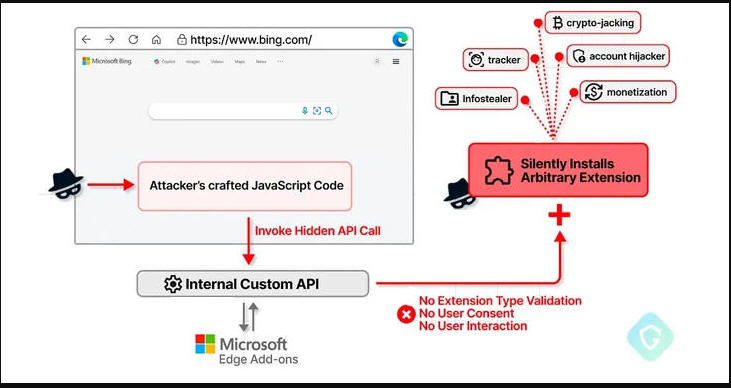
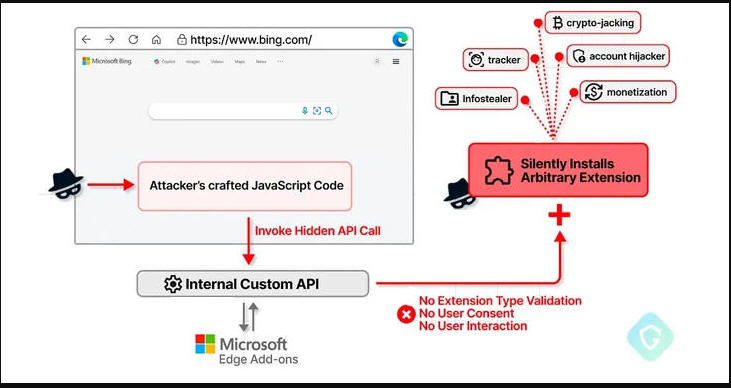
A now-patched security flaw in the Microsoft Edge web browser could have been abused to install arbitrary extensions on users' systems and carry out malicious actions.
"This flaw could have allowed an attacker to exploit a private API, initially intended for marketing purposes, to covertly install additional browser extensions with broad permissions without the user's knowledge," Guardio Labs security researcher Oleg Zaytsev said in a new report shared with The Hacker News.
Tracked as CVE-2024-21388 (CVSS score: 6.5), it was addressed by Microsoft in Edge stable version 121.0.2277.83 released on January 25, 2024, following responsible disclosure in November 2023. The Windows maker credited both Zaytsev and Jun Kokatsu for reporting the issue.
"An attacker who successfully exploited this vulnerability could gain the privileges needed to install an extension," Microsoft said in an advisory for the flaw, adding it "could lead to a browser sandbox escape."
Describing it as a privilege escalation flaw, the tech giant also emphasized that a successful exploitation of the bug requires an attacker to "take additional actions prior to exploitation to prepare the target environment."
According to Guardio's findings, CVE-2024-21388 allows a bad actor with the ability to run JavaScript on bing[.]com or microsoft[.]com pages to install any extensions from the Edge Add-ons store sans requiring user's consent or interaction.
This is made possible by the fact that the browser comes with privileged access to certain private APIs that make it possible to install an add-on as long as it's from the vendor's own extension marketplace.
One such API in the Chromium-based Edge browser is edgeMarketingPagePrivate, which is accessible from a set of allowlisted websites that belong to Microsoft, including bing[.]com, microsoft[.]com, microsoftedgewelcome.microsoft[.]com, and microsoftedgetips.microsoft[.]com, among others.
The API also packs in a method called installTheme() that, as the name implies, is designed to install a theme from the Edge Add-ons store by passing a unique theme identifier ("themeId") and its manifest file as input.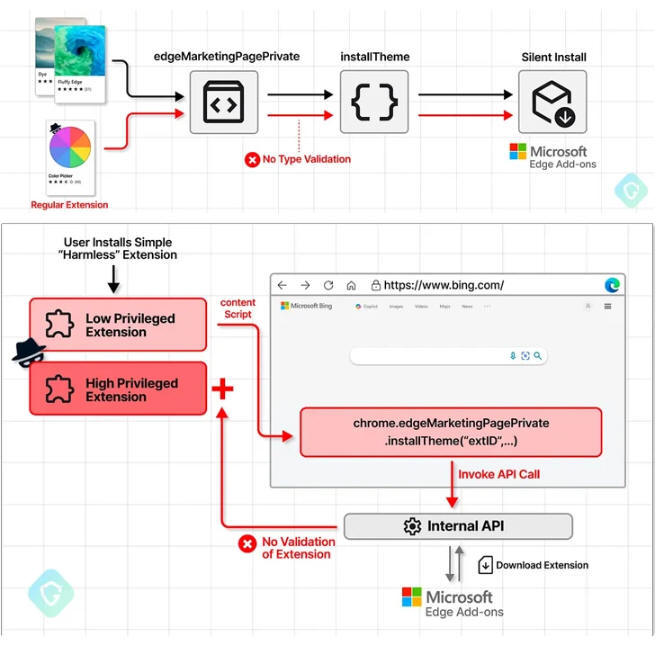
The bug identified by Guardio is essentially a case of insufficient validation, thereby enabling an attacker to provide any extension identifier from the storefront (as opposed to the themeId) and get it stealthily installed.
"As an added bonus, as this extension installation is not done quite in the manner it was originally designed for, there will be no need for any interaction or consent from the user," Zaytsev explained.
In a hypothetical attack scenario leveraging CVE-2024-21388, a threat actor could publish a seemingly harmless extension to the add-ons store and use it to inject a piece of malicious JavaScript code into bing[.]com – or any of the sites that are allowed to access the API – and install an arbitrary extension of their choice by invoking the API using the extension identifier.
Put differently, executing the specially crafted extension on the Edge browser and going to bing[.]com will automatically install the targeted extension without the victim's permission.
Guardio told The Hacker News that while there is no evidence of this bug being exploited in the wild, it highlights the need for balancing user convenience and security, and how browser customizations can inadvertently defeat security mechanisms and introduce several new attack vectors.
"It's relatively easy for attackers to trick users into installing an extension that appears harmless, not realizing it serves as the initial step in a more complex attack," Zaytsev said. "This vulnerability could be exploited to facilitate the installation of additional extensions, potentially for monetary gain."