Security of U.S. Government Sites Improved Only Slightly: Report
28.11.2017 securityweek BigBrothers
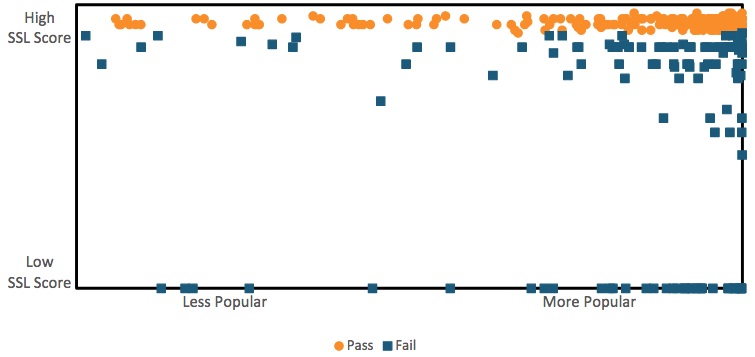
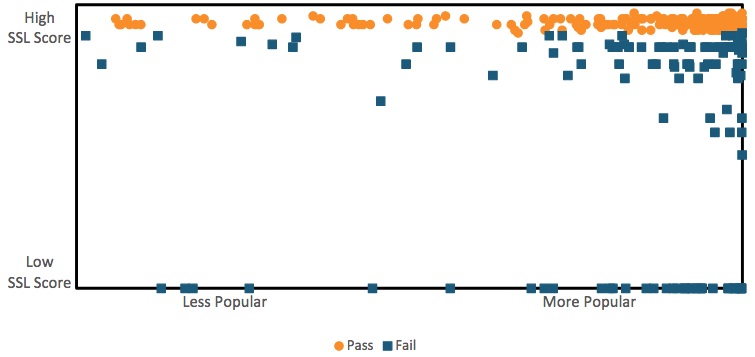
The security of websites owned by the United States government has improved only slightly in the past months, according to a report published on Monday by the Information Technology and Innovation Foundation (ITIF).
ITIF has analyzed nearly 300 of the most visited U.S. government websites to see if they are fast, secure, mobile friendly, and accessible for users with disabilities. In terms of security, the study focused on whether these sites use HTTPS, DNSSEC, and if they are affected by known vulnerabilities.
According to ITIF, of the government websites included in the top 100,000 of the Majestic Million ranking, 75% use HTTPS, which encrypts communications between the user’s browser and the site. This represents a 3% decrease compared to data from a report published by the organization in March. However, overall, the percentage of government sites that have properly implemented SSL has increased from 67% to 71%.
Of the 260 sites tested for both reports, 31% showed improvement in SSL deployment, while 14% were less secure.
The U.S. Department of Homeland Security (DHS) recently ordered all federal agencies to start using web and email security technologies such as HTTPS, DMARC and STARTTLS within the next few months.
ITIF’s report shows that 8% of websites have not implemented HTTPS at all, but this is still an improvement compared to the 14% from the previous report. The Department of Defense (defense.gov) is one of the agencies that recently rolled out HTTPS, and the International Trade Administration (trade.gov) is among those that still lack the security feature.
SSL tests, conducted by ITIF using Qualys’ SSL Server Test, also showed that some government websites have important vulnerabilities. For example, the Trade Representative (ustr.gov) and National Weather Service (weather.gov) sites are vulnerable to POODLE attacks, and trade.gov and tsunami.gov (Tsunami Warning Centers) are susceptible to DROWN attacks.
As for DNSSEC, the protocol designed to prevent attackers from redirecting users to malicious sites via DNS spoofing, ITIF found that 90% of U.S. government websites have it enabled. Since the previous report, 15 federal sites activated DNSSEC and two deactivated the feature.
“Of the top 100,000 websites reviewed only 70 percent passed both the DNSSEC and SSL test. Several of these top 100,000 websites did not have DNSSEC or HTTPS implemented. One example is the Administrative Office of the U.S. Courts (uscourts.gov), which also scored low in the security category in the initial report,” ITIF said in its 2017-benchmarking-us-government-websites.
Shortly after the DHS ordered federal agencies to improve their security, Agari analyzed government websites to see how many had implemented the DMARC anti-email spoofing protocol. In mid-October when the company published its report, nearly 82% of websites lacked DMARC entirely.
Trend Micro Acquires Application Security Firm Immunio
28.11.2017 securityweek IT
Cybersecurity firm Trend Micro announced on Tuesday that it has acquired Montréal, Canada-based web application security firm Immunio for an undisclosed sum.
The acquisition, Trend Micro says, will help increase the automated protection that it can provide customers throughout the DevOps lifecycle.
“We are excited to acquire Immunio’s application protection technology, their team of application security experts and their customers,” said Bill McGee, SVP and GM of Hybrid Cloud Security at Trend Micro. “Technology changes, like cloud computing and container platforms, are enabling faster application development. Immunio’s run-time application security allows our customers to increase protection against software vulnerabilities within the applications they are building.”
Announced at the AWS re:Invent conference this week, Trend Micro also said that it is enhancing its container-specific security capabilities, by supporting container image scanning, which allows security issues to be identified and resolved prior to production release.
According to Trend, the new capabilities integrated with the DevOps lifecycle, with Immunio bringing early detection and protection against application vulnerabilities, and container image scanning allowing for the publishing and protection of secure container images.
In March 2016, Trend Micro acquired the TippingPoint network security portfolio from Hewlett Packard Enterprise (HPE) for $300 million.
Majority of Android Apps Contain Embedded User-Tracking: Report
28.11.2017 securityweek Android
Seventy-five percent of 300 Android apps tested by Exodus Privacy and analyzed by the Yale Privacy Lab contain embedded trackers, including Uber, Tinder, Skype, Twitter, Spotify and Snapchat. The trackers are primarily used for targeted advertising, behavioral analytics and location tracking. They come as part of the app, and their presence and operation is likely unknown to the user at the time of installation.
Details are published in an analysis by the Yale Privacy Lab. It looked at 25 of the 44 trackers known to the French non-profit Exodus Privacy. Exodus analyzed 300 apps using its app scanning platform. According to its own research, the five most common embedded trackers are CrashLytics, DoubleClick, Localytics, Flurry and HockeyApp.
Despite this high number of trackers located by the research, Privacy Lab fears the problem could be worse. "The Exodus platform identifies trackers via signatures, like an anti-virus or spyware scanner, and thus can only detect trackers previously identified by researchers at the time of the scan." It fears that trackers can be added to apps in software updates after installation, and that new trackers will simply not yet be identified by Exodus.
It also adds, "Tracker companies openly advertise Software Development Kits (SDKs) compatible with multiple platforms. Thus, advertising trackers may be concurrently packaged for Android and iOS, as well as more obscure mobile platforms."
The analysis from Privacy Lab provides two examples that demonstrate its concern. Fidzup claims it has developed communication between a sonic emitter and a mobile phone. By diffusing a tone, inaudible to the human ear, inside a building Fidzup can detect the presence of mobile phones and therefore their owners. "Users installing 'Bottin Gourmand', a guide to restaurants and hotels in France," warns Privacy Lab, "would thus have their physical location tracked via retail outlet speakers as they move around Paris. Their experience would be shared by readers of car magazine app 'Auto Journal' and TV guide app 'TeleStar'."
This type of technology has probably been replaced by simple WiFi tracking; but, warns the research, closely resembles the practices of Teemo and SafeGraph. Teemo was embroiled in scandal earlier this year for studying the geolocation of 10 million French citizens, and SafeGraph, who collected 17 trillion location markers for 10 million smartphones during [Thanksgiving] last year.
However, the organization is particularly concerned about the use of trackers on the finances and healthcare of users. It cites Mon AXA, developed by a multinational insurance and finance firm, and found by Exodus to contain six trackers. Privacy Lab does not know what information is shared by these trackers. Other AXA apps, including 'HealthLook', 'AXA Banque', and 'My Doctor' also contain trackers.
Other health and finance apps that contain trackers include those from Aetna, the American Red Cross, WebMD, American Express, Discover, HSBC, Wells Fargo, and PayPal.
Privacy Lab is calling for greater transparency from Google over privacy and security practices for trackers. "Android users, and users of all app stores, deserve a trusted chain of software development, distribution, and installation that does not include unknown or masked third-party code."
Several Vulnerabilities Patched in PowerDNS
28.11.2017 securityweek Vulnerebility
Updates released for the authoritative nameserver and recursive nameserver components of PowerDNS patch several vulnerabilities that can be exploited for denial-of-service (DoS) attacks, records manipulation, modifying configurations, and cross-site scripting (XSS) attacks.
PowerDNS Recursor versions 4.0.0 through 4.0.6 are affected by a DNSSEC validation issue that can be exploited by a man-in-the-middle (MitM) attacker to forge signatures and alter DNS records (CVE-2017-15090).
Another flaw affecting these versions of Recursor is CVE-2017-15092, an XSS bug that allows a remote attacker to inject arbitrary HTML and JavaScript code into the Recursor web interface. The security hole can be exploited by sending specially crafted DNS queries to the server in order to alter the web interface or cause it to enter a DoS condition.
The Recursor is also impacted by a vulnerability that allows an authenticated attacker to inject new directives into its configuration (CVE-2017-15093). The last issue affecting this component is a DoS flaw caused by a memory leak that can occur when parsing specially crafted DNSSEC ECDSA keys (CVE-2017-15094). The vulnerability can be exploited by using an authoritative server to send specially crafted keys to the recursor.
The only security hole affecting PowerDNS Authoritative versions 4.0.4, 3.4.11 and prior is CVE-2017-15091, which allows an authenticated attacker to cause a DoS condition.
The vulnerabilities have been rated medium and low severity as they do not impact default configurations. Patches are included in PowerDNS Authoritative 4.0.5 and Recursor 4.0.7. Minimal fixes have also been provided for the 3.4.11 and 3.7.4 releases, but users of these versions have been advised to migrate to the 4.x branch.
These security holes were discovered by Finland-based cybersecurity services company Nixu during a source code audit, Chris Navarrete of Fortinet's Fortiguard Labs, Kees Monshouwer, and a researcher who uses the online moniker “everyman.”
U.S. Indicts Chinese For Hacking Siemens, Moody’s
28.11.2017 securityweek BigBrothers
U.S. authorities filed charges Monday against three China-based hackers for stealing sensitive information from U.S. based companies, including data from Siemens industrial groups and accessing a high-profile email account at Moody’s.
Wu Yingzhuo, Dong Hao and Xia Lei, who the Department of Justice (DOJ) says are Chinese nationals and residents of China, were indicted by a grand jury for a series of cyber-attacks against three corporate victims in the financial, engineering and technology industries between 2011 and May 2017.
Victims named in the indictment include Moody’s Analytics, Siemens, and GPS technology firm Trimble.
According to the FBI, the hackers work for Guangzhou Bo Yu Information Technology Company Limited, a firm that purports to be a China-based Internet security firm also known as “Boyusec.”
Tracked as APT3 by FireEye, and Gothic Panda by CrowdStrike, the group is also known as UPS Team, Buckeye and TG-0110, and has previously been linked to the Chinese Ministry of State Security (MSS).
“We’ve tracked their activity back to 2007 and they are one of the most technically advanced state-affiliated actors in China,” Adam Meyers, VP of Intelligence at CrowdStrike, told SecurityWeek. “Their previous targeting includes industries such as Aerospace, Defense, Energy, Technology, NGOs, etc., that are primarily aligned with China’s economic objectives.”
In November 2016, the Washington Free Beacon learned from Pentagon intelligence officials that Boyusec had been working with Chinese telecoms giant Huawei to develop spyware-laden security products that would be loaded onto computers and phones. The unnamed officials said Boyusec was “closely connected” to the Chinese Ministry of State Security.
According to the indictment, the hackers:
• Stole approximately 407 gigabytes of proprietary commercial data pertaining to Siemens’s energy, technology and transportation businesses.
• Accessed the internal email server of Moody’s Analytics and placed a forwarding rule in the email account of a prominent employee, and set it to forward all emails to and from the account to web-based email accounts controlled by the attackers.
• Stole at least 275 megabytes of data, including compressed data, which included hundreds of files that would have assisted a Trimble competitor in developing, providing and marketing a similar product without incurring millions of dollars in research and development costs.
“The primary goal of the co-conspirators’ unauthorized access to victim computers was to search for, identify, copy, package, and steal data from those computers, including confidential business and commercial information, work product, and sensitive victim employee information, such as usernames and passwords that could be used to extend unauthorized access within the victim systems,” the DOJ said. “For the three victim entities listed in the Indictment, such information included hundreds of gigabytes of data regarding the housing finance, energy, technology, transportation, construction, land survey, and agricultural sectors.”
Intrusion Truth previously conducted an analysis of APT3’s command and control (C&C) infrastructure, and analyzed domain registration data. Their research led to two individuals, named Wu Yingzhuo and Dong Hao, who apparently registered many of the domains used by the threat actor.
Researchers noticed last year that the group had shifted its attention from the U.S. and the U.K. to Hong Kong, where it had mainly targeted political entities using a backdoor dubbed “Pirpi.”
CrowdStrike has seen an uptick in activity by the group since 2016, Meyers said.
In addition to Pirpi, Symantec observed APT3 using various other tools, including keyloggers, remote command execution tools, system information harvesting tools, and browser password stealers. Researchers said the group appears to be focusing on file and print servers, which suggests they are mainly interested in stealing documents to support their espionage efforts.
“Defendants Wu, Dong and Xia launched coordinated and targeted cyber intrusions against businesses operating in the United States, including here in the Western District of Pennsylvania, in order to steal confidential business information,” said Acting U.S. Attorney Song. “These conspirators masked their criminal conspiracy by exploiting unwitting computers, called ‘hop points,’ conducting ‘spearphish’ email campaigns to gain unauthorized access to corporate computers, and deploying malicious code to infiltrate the victim computer networks.”
New Mirai Variant Emerges
28.11.2017 securityweek BotNet
A new variant of the Mirai malware has been observed over the past week targeting new sets of default credentials specific to ZyXEL devices, Qihoo 360 Netlab researchers warn.
Mirai became widely known about a year ago, when it started ensnaring insecure Internet of Things (IoT) devices into a botnet capable of launching massive distributed denial-of-service (DDoS) attacks. With its source code made public in early October 2016, Mirai had already infected devices in 164 countries by the end of that month.
To spread, Mirai scans the Internet for open ports associated with Telnet access on Internet-facing IoT products and attempts to connect to the discovered devices using a set of default username/password combinations.
In August this year, Akamai explained that Mirai is formed of smaller hives of related bots and command and control (C&C) servers, and parts of it can be used for different purposes. Thus, the botnet can be involved in multiple, simultaneous attacks, each orchestrated from a different C&C, likely by a different operator, and can also be rented to wannabe criminals.
“At least one botnet operator was offering access to the systems under its control for rent,” Akamai revealed.
Starting with last week, Netlab observed an increase in port 2323 and 23 scan traffic and “confidently” associated it with a new Mirai variant. The researchers also discovered that this new malware version is specifically searching for insecure ZyXEL devices.
According to the security researchers, the scanner was attempting to exploit two new default login credentials, namely admin/CentryL1nk and admin/QwestM0dem. The former, they explain, was first spotted less than a month ago in exploit-db, as part of an exploit targeting the ZyXEL PK5001Z modem.
What Netlab noticed was that the abuse of the two login credentials started on November 22 and reached its peak the next day, the same as the uptick on port 2323 and 23 scan traffic. Thus, they concluded that the two were related.
The security researchers also reveal that most of the scanner IPs appear to be located in Argentina, with nearly 100,000 unique scanners from that country observed over a period of nearly three days. This led them to conclude that the attack might have been focused on specific types of IoT devices widely deployed in Argentina.
Last year, the Mirai worm was involved in a similar attack where nearly 1 million of Deutsche Telekom’s fixed-line network customers experienced Internet disruptions.
Critical Code Execution Flaw Found in Exim
28.11.2017 securityweek Vulnerebility
Serious vulnerabilities that can be exploited for remote code execution and denial-of-service (DoS) attacks have been found in the popular mail transfer agent (MTA) software Exim.
Exim is an open source MTA for Unix systems created at the University of Cambridge. An analysis of more than one million mail servers conducted back in March showed that over 56 percent of them had been running Exim.
A researcher who uses the online moniker “Meh,” a member of the research team at Taiwan-based security firm DEVCORE, discovered that Exim is affected by a couple of potentially serious vulnerabilities.
One of them, tracked as CVE-2017-16943 and classified as critical, is a use-after-free bug related to a feature called “chunking.” It allows a remote attacker to execute arbitrary code or cause a DoS condition via specially crafted BDAT commands.
Chunking is a feature that allows sending emails in chunks. BDAT commands specify the length of the binary data packet so that the Simple Mail Transfer Protocol (SMTP) host does not have to continuously scan for the end of the data.
Sending specially crafted BDAT commands to the targeted mail server can trigger the use-after-free vulnerability and allow an attacker to execute arbitrary code. There are reportedly more than 400,000 servers with the vulnerable chunking feature visible on the Internet.
The second flaw discovered by Meh is CVE-2017-16944, a high severity issue that allows a remote attacker to cause a DoS condition using specially crafted BDAT commands.
In the advisory informing Exim users of the vulnerability, developers said the issue had been disclosed publicly before a patch could be released. Meh said he did not find an email address for privately reporting security holes so he reported it via the Exim bug tracker. However, the bug tracker did not have an option for setting reports to private and the researcher wrongly assumed that security bugs are set to private by default. Exim developers have taken steps to prevent such incidents in the future.
The details of the code execution vulnerability, along with proof-of concept (PoC) code, were posted to the Exim Bugzilla on November 23. A workaround that involves disabling the chunking feature and a patch were made available within two days. Only the source code patch is available – the fix for CVE-2017-16943 will likely be included in the next release.
Exim is currently at version 4.89 and the flaw was apparently introduced in 4.88 when the chunking feature was added. Developers are still working on a patch for CVE-2017-16944.
Just over a dozen vulnerabilities have been identified in Exim since 2010, and only five of them, reported several years ago, allow remote code execution without authentication.
McAfee to Acquire CASB Firm Skyhigh Networks
28.11.2017 securityweek IT
McAfee announced on Monday that it has agreed to acquire cloud access security broker (CASB) Skyhigh Networks for an undisclosed amount.
CASBs are the go-to solution for corporate cloud security. By controlling access to the corporate cloud they can apply visibility and security to what is within that cloud. But it is such a good solution that big security firms are rapidly buying up all the independent CASBs (such as Microsoft, Symantec, Forcepoint, Oracle, and Cisco).
It's reaching the stage where no large security firm can be without a CASB, and no CASB can survive and prosper without the support of a major security vendor.
"Skyhigh Networks had the foresight five years ago to realize that cybersecurity for cloud environments could not be an impediment to, or afterthought of, cloud adoption," said McAfee CEO Chris Young stated. "They pioneered an entirely new product category called cloud access security broker (CASB) that analysts describe as one of the fastest growing areas of information security investments of the last five years -- where Skyhigh continues to innovate and lead. Skyhigh's leadership in cloud security, combined with McAfee's security portfolio strength, will set the company apart in helping organizations operate freely and securely to reach their full potential."
Little about the mechanics of the agreement have been announced, beyond a statement that Skyhigh CEO "Rajiv Gupta will join McAfee CEO Chris Young's leadership team to run McAfee's new cloud business unit." However, both CEOs have provided a little more information in separate blogs.
"Combined with McAfee's endpoint security capabilities and operations center solutions with actionable threat intelligence, analytics and orchestration, we will be able to deliver a set of end-to-end security capabilities unique in the industry," writes Gupta.
"Cloud security has historically been an afterthought of, or impediment to, cloud adoption. With customers' most valuable asset, data, increasingly finding residence in the cloud, it's time security move to the forefront. At the same time, security cannot hinder cloud adoption, as the transformation the cloud promises extends far beyond the corridors of IT to every facet of modern business. Skyhigh had this prescience five years ago," wrote Young.
The combination of the two companies, with McAfee's traditional strength in endpoint security and a growing network security portfolio with Skyhigh's cloud security, should clearly benefit both organizations. "McAfee already claims a market-leading position in endpoint. With Skyhigh's leadership in securing the world's most valuable asset -- data -- in the cloud, the company sets itself apart," announces an associated Skyhigh FAQ.
But there is no information yet on how the products will work together -- just a placeholder from Skyhigh: "How will Skyhigh and McAfee's products work together? We have some exciting things in the works that we'll share over the coming months. Stay tuned!" If McAfee stays true to its stated intents, this will include bringing greater automation and orchestration to the cloud and associated endpoints.
McAfee separated from Intel in April 2017.
Thoma Bravo Acquires Barracuda Networks for $1.6 Billion
28.11.2017 securityweek IT
Private equity investment firm Thoma Bravo has entered an agreement to acquire security company Barracuda Networks for $1.6 billion in cash.
Barracuda shareholders will receive $27.55 for each share of common stock they hold, which exceeds the average stock price of $22.49 for the ten days leading up to November 27 by more than 22 percent.
The agreement was unanimously approved by Barracuda’s board of directors. Once the acquisition is completed – likely before the fiscal year ends on February 28, 2018 – Barracuda will operate as a privately-held company and it will continue to focus on email security and management, data protection, and network and application security solutions for cloud and hybrid environments.Barracuda acquired by Thoma Bravo
“We believe the proposed transaction offers an opportunity for us to accelerate our growth with our industry-leading security platform that's purpose-built for highly distributed, diverse cloud and hybrid environments. We will continue Barracuda's tradition of delivering easy-to-use, full-featured solutions that can be deployed in the way that makes sense for our customers,” said BJ Jenkins, CEO of Barracuda.
“Thoma Bravo has an excellent history of investing in growing security businesses, and this transaction speaks to the value and strength of Barracuda's security platform, which helps customers protect and manage their networks, applications, and data. I expect that our employees, customers, and partners will benefit from this partnership,” he added.
The news comes just weeks after Barracuda announced the acquisition of public cloud archiving and business insights provider Sonian in an effort to enhance the company’s email security and management capabilities.
Barracuda’s latest financial report shows that the company’s revenue in the second fiscal quarter grew 7% year-over-year to $94.3 million, and the number of active subscribers increased by 17% to nearly 350,000.
Cobalt Hackers Exploit 17-Year-Old Vulnerability in Microsoft Office
28.11.2017 securityweek Vulnerebility
The notorious Cobalt hacking group has started to exploit a 17-year-old vulnerability in Microsoft Office that was addressed earlier this month, security researchers claim.
Fixed in Microsoft's November 2017 Patch Tuesday security updates and found by Embedi security researchers in the Microsoft Equation Editor (EQNEDT32.EXE), the bug is identified as CVE-2017-11882.
The issue was found in a component that remained unchanged in Microsoft’s Office suite since November 9, 2000, and appears to have been patched manually instead of being corrected directly in the source code, an analysis 0patch published last week reveals.
An Office component designed to facilitate the creation of math and science equations, the Equation Editor was replaced in Office 2007 with new methods of displaying and editing equations. However, the old tool continues to be part of the popular Office suite to ensure compatibility with older documents.
The newly addressed vulnerability has recently started being exploited by the Cobalt hackers in live attacks, ReversingLabs, which managed to capture a RTF document specifically designed to exploit CVE-2017-11882, says.
The malicious file was observed contacting a remote server to grab a first-stage payload it would execute using MSHTA.exe. The executed code would then connect to the remote server to fetch a second-stage payload, a script that would drop an embedded, final payload.
This appears to be the Cobalt Strike backdoor, the group’s preferred malicious tool. The malware allows the attackers to execute remote commands on the infected systems.
Considering that unpatched EQNEDT32.EXE instances put Office users at risk, regardless of the Windows version their systems run. The 17 year-old bug was found to impact even machines running Windows 10 Creators Update, which explains why hackers are already exploiting the vulnerability.
What’s more, proof-of-concept exploits for the vulnerability were published soon after the vulnerability became public, so there’s no surprise in the fact that Cobalt has already started targeting the bug, especially since the hacking group is known to be a fast adopter of newly discovered exploits.
A financially-motivated group, Cobalt was first described in 2016 and is known to be targeting banks, financial exchanges, insurance companies, investment funds, and other financial organizations. The hackers use phishing emails carrying malicious documents or ZIP archives packing executables to distribute their malware.
Earlier this year, the group started abusing CVE-2017-0199, a vulnerability patched in April, expanded its operations to North America, and started using supply chain attacks. The group was initially focused only on Eastern Europe and Central and Southeast Asia, but is now hitting targets worldwide.
A report published last week revealed that the group started targeting banks themselves, instead of bank customers. The attacks were attempting to exploit CVE-2017-8759, a code injection/remote code execution vulnerability in Microsoft’s .NET Framework that was patched in September 2016.
Op In Our Sites – Europol and other agencies seize over 20,500 domains for selling counterfeit products
28.11.2017 securityaffairs CyberCrime
An joint operation conducted by Europol and other law enforcement agencies resulted in the seizure of more than 20,520 domains for selling counterfeit products.
The operation, dubbed “In Our Sites (Project TransAtlantic VIII),” allowed to seize domains that were offering for sale any kind of counterfeit product, including luxury products, sportswear, electronics, pharmaceuticals and online piracy on e-commerce platforms and social networks.
This is the eighth edition of this global operation against online counterfeiting and IP crimes.
Europol
✔
@Europol
Biggest hit against online piracy: Over 20520 domain names seized for illegally selling counterfeit goods to consumers, incl. luxury products, sportswear, electronics, pharmaceuticals & more. Europol @IPRCenter @DHSgov @ICEgov 💪 https://www.europol.europa.eu/newsroom/news/biggest-hit-against-online-piracy-over-20-520-internet-domain-names-seized-for-selling-counterfeit … #CyberMonday
3:28 PM - Nov 27, 2017
7 7 Replies 115 115 Retweets 156 156 likes
Twitter Ads info and privacy
The “In Our Sites (Project TransAtlantic VIII)” operation was conducted by the Europol in association with the Interpol, the US National Intellectual Property Rights Coordination Centre (NIPRCC), FBI, Department of Justice (DOJ), and law enforcement authorities from 27 European Member States.
An Intellectual Property (IP) crime is committed every time someone uses an intellectual property right without the owner’s authorization. According to the Europol, counterfeiting and piracy are the main categories of IP crimes, such kind of crimes is becoming one of the most profitable business for the Organised Crime Groups (OCGs) are increasingly involved in the violation of IPR and darknets have a key role in the criminal ecosystem.
According to the International Trademark Association around $460 billion worth of counterfeit goods were bought and sold in 2016.
“Targeting copyright-infringing websites that market dangerous counterfeit goods to consumers and engage in other forms of intellectual property theft will continue to be a priority for law enforcement,” said acting IPR Center Director Nick.
“Strengthening our collaboration with police authorities around the world and leaders of industry will reinforce the crackdown on IP crimes, and demonstrate that there is no safe haven for criminals committing these illicit activities.”
Europol hasn’t disclosed the list of seized domains that now display the official seals from the law enforcement agencies that participated in the operation.
Below the message presented by the visitors:
“This domain name has been seized
Operation in Our Sites-Project TransAtlantic VIII is a coordinated effort by the U.S., European, South American and Asian law enforcement agencies targeting websites and their operations that sell counterfeit goods.”

“This excellent result shows how important and effective cooperation between law enforcement authorities and private-sector partners is, and how vital it is if we are to ultimately make the internet a safer place for consumers. Through its Intellectual Property Crime Coordinated Coalition (IPC³), Europol will continue to work closely with its partners to strengthen the fight against intellectual property crime online and offline.’’ said Rob Wainwright, Executive Director of Europol.
According to data published by the Europol, the agency has seized a total of 7,776 websites in previous “In Our Sites” (IOS) editions.
“A total of 7776 websites have been seized in the previous editions. This year’s operation IOS VIII has seen a remarkable increase of up to 20 520 seized domain names that were illegally selling counterfeit merchandise online to consumers.” reads the press release issued by Europol. “This can be explained by the holistic approach which Europol followed with the aim of making the internet a safer place for consumers, by getting even more countries and private-sector partners to participate in this operation and provide referrals.”
The energy used to mine Bitcoin this year is bigger than the annual usage of almost 160 countries
28.11.2017 securityaffairs IT
According to PowerCompare.co.uk, the electricity used to mine Bitcoin this year is bigger than the annual usage of almost 160 countries.
While the price of cryptocurrencies such as the Bitcoin continues to increase the interest of investors and crooks in this new industry is demonstrated by disconcerting data that I’m going to share with you.
According to new research conducted by energy tariff comparison service PowerCompare.co.uk, the electricity used to mine Bitcoin this year is bigger than the annual usage of almost 160 countries. The energy consumption has already exceeded the amount used on average by states such as Ireland and most African nations.
“According to Digiconomist’s Bitcoin Energy Consumption Index, as of Monday November 20th, 2017 Bitcoin’s current estimated annual electricity consumption stands at 29.05TWh.” states the research.
“That’s the equivalent of 0.13% of total global electricity consumption. While that may not sound like a lot, it means Bitcoin mining is now using more electricity than 159 individual countries (as you can see from the map above). More than Ireland or Nigeria.”
Bitcoin transactions use so much energy that the electricity used for a single trade could power a home for almost a whole month, according to a paper from Dutch bank ING.
“By making sure that verifying transactions is a costly business, the integrity of the network can be preserved as long as benevolent nodes control a majority of computing power,” wrote ING senior economist Teunis Brosens.
“Together, they will dominate the verification (mining) process. To make the verification (mining) costly, the verification algorithm requires a lot of processing power and thus electricity.”
Comparing the amount of energy used for a Bitcoin transaction to run his home in the Netherlands, Brosens says: “This number needs some context. 200kWh is enough to run over 200 washing cycles. In fact, it’s enough to run my entire home over four weeks, which consumes about 45 kWh per week costing €39 of electricity (at current Dutch consumer prices).”
It is amazing if we compare this data other payment systems, for example Visa takes about 0.01kWh (10Wh) per transaction which is 20000 times less energy.
The following graph shows the 159 countries whose energy usage is less than bitcoin-mining consumption.

Source PowerCompare.co.uk
Which is the concept behind the mining process?
To prevent the falsification of the records or the ownership changing, participants of the Bitcoin network must sign off on transactions in “blocks”.
The process requests a significant computational capability and involves several computers to solve complex cryptographic problems, people who verify blocks are rewarded with freshly created bitcoin. This process is known as Bitcoin “mining.”
According to the initial design of the Bitcoin virtual currency scheme, it limits the overall number of coins in circulation to 21 million, this is possible because the cryptographic problems involved in the mining process get progressively harder.
On the other side, miners are turning to more powerful computers to solve the complex problems behind the mining process.
The vast majority of “mining” activities is done in China because the energy costs are cheaper compared to Europe or US.
“The top six biggest mining pools from Antpool to BTCC are all largely based in China,” said Mati Greenspan, an analyst with trading platform eToro. “Some rough estimates put China’s hashpower at more than 80% of the total network.”
Of course, the environmental impact of all this electric usage is not negligible, don’t forget that the electricity generated in China comes from CO2 emitting fossil fuels.
Below a few other interesting facts about Bitcoin mining and electricity consumption published:
In the past month alone, Bitcoin mining electricity consumption is estimated to have increased by 29.98%
If it keeps increasing at this rate, Bitcoin mining will consume all the world’s electricity by February 2020.
Estimated annualised global mining revenues: $7.2 billion USD (£5.4 billion)
Estimated global mining costs: $1.5 billion USD (£1.1 billion)
Number of Americans who could be powered by bitcoin mining: 2.4 million (more than the population of Houston)
Number of Britons who could be powered by bitcoin mining: 6.1 million (more than the population of Birmingham, Leeds, Sheffield, Manchester, Bradford, Liverpool, Bristol, Croydon, Coventry, Leicester & Nottingham combined) Or Scotland, Wales or Northern Ireland.
Bitcoin Mining consumes more electricity than 12 US states (Alaska, Hawaii, Idaho, Maine, Montana, New Hampshire, New Mexico, North Dakota, Rhode Island, South Dakota, Vermont and Wyoming)
US indicts Chinese hackers belonging to APT3 for espionage on Siemens and Moody’s
28.11.2017 securityaffairs APT
US authorities have filed official charges against three Chinese hackers part of the elite cyber-espionage unit APT3.
US authorities charged three China-based hackers for stealing sensitive information from US based companies, including Siemens AG, and accessing a high-profile email account at Moody’s.
The three Chinese citizens, Wu Yingzhuo, Dong Hao and Xia Lei, work for the Chinese cybersecurity company Guangzhou Bo Yu Information Technology Company Limited, also known as “Boyusec.”
While Wu and Dong are founding members and shareholders of the China-based company, Xia is just an employee.
Do you remember the Boyusec name?
Several reports published in May 2017 linked the Boyusec firm to the infamous APT3 group, a cyber-espionage group under the control of the Chinese Government.
The APT3, also known as UPS, Gothic Panda, and TG-011, has been active since 2010.

On May 9th, 2017, an unknown party using the alias ‘intrusiontruth’ published a series of blogs posts describing connections between the Pirpi RAT command and control components and shareholders of the Chinese security contractor Guangzhou Boyu Information Technology Company, aka Boyusec.
The names of two specific shareholders of Boyusec appear in the domain registration for the Pirpi C&C servers. This is particularly interesting because Boyusec supports the Chinese Ministry of State Security (MSS) by collecting civilian human intelligence. Think of them as an outsourcer for a government agency like the United States’ National Security Agency (NSA).
Also interesting is that in 2016 a Pentagon report described the relationship between Boyusec and network equipment manufacturer, Huawei. According to the report, the two companies were colluding to develop security equipment with embedded backdoors which would likely be used by Boyusec to compromise Huawei customers.
“In November 2016, the Washington Free Beacon reported that a Pentagon internal intelligence report had exposed a product that Boyusec and Huawei were jointly producing.” continues the analysis.”According to the Pentagon’s report, the two companies were working together to produce security products, likely containing a backdoor, that would allow Chinese intelligence “to capture data and control computer and telecommunications equipment.” The article quotes government officials and analysts stating that Boyusec and the MSS are “closely connected,” and that Boyusec appears to be a cover company for the MSS.”
The Chinese men have been charged in Pittsburgh with using malware to steal data from the international corporations, including Siemens AG, which has Pittsburgh offices.
The federal indictment filed in September was unsealed Monday, the men were charged by a grand jury for cyber-attacks against three corporations in the financial, engineering and technology industries between 2011 and May 2017. Victims are Moody’s Analytics, Siemens, and GPS technology firm Trimble.
“The primary goal of the co-conspirators’ unauthorized access to victim computers was to search for, identify, copy, package, and steal data from those computers, including confidential business and commercial information, work product, and sensitive victim employee information, such as usernames and passwords that could be used to extend unauthorized access within the victim systems,” the DOJ said. “For the three victim entities listed in the Indictment, such information included hundreds of gigabytes of data regarding the housing finance, energy, technology, transportation, construction, land survey, and agricultural sectors.”
According to the indictment, the hackers:
• Stole approximately 407 gigabytes of proprietary commercial data pertaining to Siemens’s energy, technology and transportation businesses.
• Accessed the internal email server of Moody’s Analytics and placed a forwarding rule in the email account of a prominent employee, and set it to forward all emails to and from the account to web-based email accounts controlled by the attackers.
• Stole at least 275 megabytes of data, including compressed data, which included hundreds of files that would have assisted a Trimble competitor in developing, providing and marketing a similar product without incurring millions of dollars in research and development costs.
All three indicted suspects are still at large and currently residing in China.
CZ.NIC testuje veřejný honeypot, který pomůže s detekováním malwaru
27.11.2017 Lupa.cz Zabezpečení
Pomoc se zkoumáním útoků a odhalováním chyb, které útočníci zneužívají. To si sdružení CZ.NIC slibuje od projektu Honeypot as a Service (HaaS), který začalo testovat v říjnu. Projekt má umožnit koncovým uživatelům přesměrovat útoky na jejich zařízení do centrálního honeypotu, ve kterém je pak experti mohou analyzovat a získané údaje použít ke zvýšení zabezpečení.
Jak to funguje? Případný dobrovolný zájemce se zaregistruje na webu projektu a do svého PC (nebo na linuxový server) si stáhne a nainstaluje proxy. Zdrojový kód aplikace (haas-mitmproxy) je dostupný na GitHubu. Po spuštění na počítači začne proxy přeposílat příchozí komunikaci z portu 22 na server HaaS, na kterém honeypot Cowrie simuluje zařízení a zaznamenává provedené příkazy.
„Projekt HaaS zahrnuje vytvoření sítě minimálně pěti set koncových uživatelů a techniky pro přesměrování těchto uživatelů na centrální honeypot. Cílem našeho výzkumu je pak zajistit, aby byl útočník co nejdéle přesvědčen, že útočí na skutečný cíl, tedy na počítač, server nebo router, nikoliv honeypot,“ popisuje Ladislav Lhotka z CZ.NIC.
Projekt momentálně běží v betatestu a jeho ostré spuštění by mělo přijít někdy v květnu příštího roku. Částkou 1,3 milionu na něj přispěla Technologická agentura ČR.
Postřehy z bezpečnosti: ještě pochybujete o nutnosti HTTPS?
27.11.2017 Root.cz Bezpečnost
Dnes se podíváme na jednu kontroverzní oslavu státního svátku, prozkoumáme nový seznam zranitelností webových aplikací a připomeneme si zajímavý výrok ve vývojářské konferenci linuxového jádra.
Kontroverzní oslava 17. listopadu
Pokud jste nedávný státní svátek slavili off-line, možná vám unikl poměrně kontroverzní způsob, jakým se k jeho oslavě připojil operátor O2. Při pokusu o přístup na webovou stránku nekončící českou doménou bylo HTTP spojení uneseno a místo skutečné odpovědi podvrženo přesměrování na captive portál, představující fiktivní železnou oponu. Teprve po kliknutí na odkaz na něm bylo možné pokračovat normálně.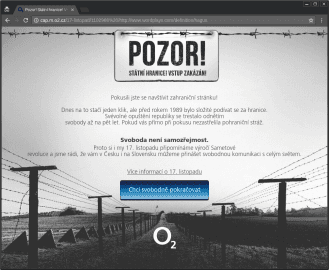
Kromě samotného faktu, že si tak velký telekomunikační operátor něco takového dovolil, je zarážející i zjištění, že vůbec má v síti nasazené zařízení, které takovéto zásahy umožňuje. Všechny doposud hypotetické úvahy o možnosti monitorování a transparentního pozměňování nešifrovaného provozu poskytovatelem přístupu k Internetu tak nyní dostávají naprosto reálné obrysy. Došlo tak k definitivnímu vyvrácení tradičního mýtu, že HTTPS je zbytečné pro čistě informační weby, kam se nikdo nepřihlašuje. Jednoduše HTTPS by mělo být všude.
Jak píše web DSL.sk, protokol HTTPS poněkud podcenili kolegové ze slovenské pobočky O2, kteří zorganizovali obdobnou akci. Na rozdíl od českého operátora webový server toho slovenského na adrese https://o2.sk posílá hlavičku HTTP Strict-Transport-security, která po dobu dvou let vynucuje použití HTTPS na všechny subdomény. No a vzhledem k tomu, že captive portál byl provozován na takové subdoméně, ale přitom HTTPS nepodporoval, zobrazila se některým uživatelům ze Slovenska při přístupu na zahraniční stránky pouze chybová zpráva, že web není dostupný.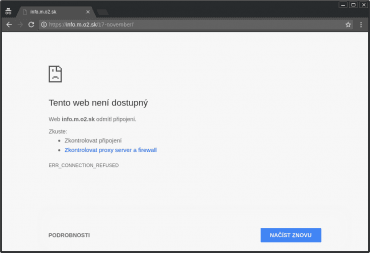
Jak bezpečný je Android Pay?
Autor: Dalibor Z. Chvátal
Platební karty J & T Banky v aplikaci Android Pay. (14. 11. 2017)
Služba Android Pay, která umožňuje jednoduché placení v obchodech prostřednictvím NFC, přišla i do Česka. Využívá funkci zvanou Host-based Card Emulation, která je dostupná v Androidu od verze 4.4. Tato funkce umožňuje aplikaci v telefonu přímo komunikovat s čtečkou bezkontaktních karet v poli NFC antény. Na rozdíl od předchozích řešení se tak eliminuje nutnost mít v zařízení tzv. secure element nebo speciální SIM kartu, která by prováděla kryptografické operace a bezpečně držela privátní klíče. Ty jsou nyní doručovány přes internet v podobě tzv. tokenů, kdy každý token je použitelný pouze pro jednu transakci.
Systém NFC plateb pomocí HCE není v Česku nový, představila jej už minulý rok ČSOB, následovaná Komerční bankou. Systém Android Pay se od těchto řešení liší především posunutím hranice bezpečnosti zase o něco níže. Zatímco dříve uvedené aplikace vyžadují pro platbu zadání speciálního PINu aplikace, případně použití otisku prstu a pouze jako doplňkovou službu nabízejí rychlé placení bez odemykání telefonu, Android Pay tento model obrací tak, že k platbám menších částek (zřejmě do 500 Kč) stačí pouze rozsvítit displej telefonu, pro platbu vyšších částek pak stačí pouze odemknout zámek displeje. Vzhledem k tomu, jak triviální bývají odemykací sekvence většiny uživatelů, se takové zabezpečení virtuální karty nezdá jako dostatečné.
Aplikace se také brání odcizení platebních tokenů tak, že se snaží detekovat nejen root oprávnění, ale na některých modelech telefonů i samotné odemčení zavaděče či použití alternativní ROM a v takovém případě se odmítne spustit. Uživatelé starších přístrojů, jejichž podpora ze strany výrobce už skončila, tak mají těžkou volbu, zda používat aktuální operační systém, jakým je například LineageOS a o možnost placení telefonem přijít, nebo zůstat u originálního firmwaru se známými zranitelnostmi, kde Android Pay funguje.
Nové vydání OWASP Top 10 zranitelností webových aplikací
Po čtyřech letech vydal projekt OWASP nový seznam 10 nejčastějších zranitelností webových aplikací. Na prvních dvou místech se pořadí nezměnilo, největšími problémy jsou stále Injection a chyby autentizace. Na třetí místo se ze šestého přesunulo vyzrazení citlivých dat. Obecně zpráva také hodnotí, že v poslední době jsou na vzestupu mikroslužby, které představují proti tradičním monolitickým webovým aplikacím nové bezpečnostní výzvy.
Dále je konstatováno, že dominantním jazykem se stává JavaScript, který se jednak používá na klientovi, kde často nahrazuje tradičnější zpracování požadavků na straně serveru, jednak i na serverech díky projektům jako Node.js.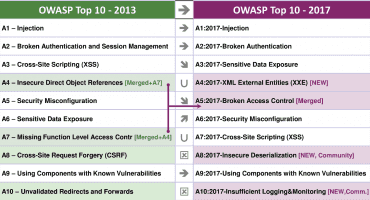
Porovnání seznamu Top10 2013 a 2017
A zase ty úniky
Minulý týden vyšlo najevo, že v říjnu 2016 došlo k úniku dat společnosti Uber. Útočníci se nějakým způsobem dostali k privátnímu repozitáři na GitHubu, ve kterém objevili přihlašovací jméno a heslo pro Amazon Web Services. V tomto úložišti bylo uloženo na 57 milionů osobních údajů zákazníků a řidičů, včetně 600 tisíc čísel řidičských průkazů. Ačkoli měla společnost povinnost o takovém úniku informovat federální úřady Spojených států, namísto toho zaplatila útočníkům sto tisíc dolarů za odstranění dat a celý incident ututlala. Jakou měla záruku, že k vymazání dat skutečně došlo, můžeme jen spekulovat.
O pár dní později se k podobnému úniku přiznala společnost Czechia.com. Únik se týká 6500 zákaznických účtů a byl zřejmě způsoben jistým zákazníkem, který objevil a zneužil chybu v zabezpečení managed serverů, kterými bylo možné získat interní databázi. Kuriózní je i způsob, jakým byl únik odhalen: Michal Špaček jej objevil náhodou, když hledal na webu SHA-1 hashe často používaných hesel.
Děravý procesor v procesoru
Je známou věcí, že v procesorech firmy Intel se od jisté doby vyskytuje další kompletní počítač zvaný Management Engine, ve kterém běží operační systém MINIX. Tento počítač provádí zejména servisní činnosti pro hlavní procesor, dále pak volitelně umožňuje vzdálenou správu, včetně přístupu ke konzoli hlavního počítače. Jeho možnosti zasahovat do činnosti hlavního procesoru jsou tedy téměř neomezené a jeho napadení by mohlo v nejhorším případě znamenat i zcela nedetekovanou kompromitaci.
Intel na základě nedávného auditu vydal opravu firmware a třese se, jaké další zranitelnosti ještě výzkumníci objeví. Oprava se obvykle distribuuje jako aktualizace BIOSu, je tedy třeba sledovat informace výrobce počítače. Není divu, že s takovým stavem se spousta uživatelů nespokojí a pokouší se nahradit proprietární firmware z co největší části open source softwarem.
Čtyři devítky nabízí soukromí i bezpečnost v DNS
Společnosti IBM, Packet Clearing House a Global Cyber Alliance nedávno představily projekt Quad 9. Ten nabízí veřejný rekurzivní DNS resolver na dobře zapamatovatelné IPv4 adrese 9.9.9.9 (IPv6 varianta 2620:fe::fe už tak jednoduchá k zapamatování není), který kromě ochrany soukromí – tvrdí, že nezaznamenávají žádné informace o uživatelích – nabízí také ochranu před škodlivými doménovými jmény, která slouží například ke komunikaci botnetů.
Služba je provozovaná prostřednictvím globálního anycastu ve více než stovce lokalit, plně podporuje IPv4 i IPv6 a také provádí validaci DNSSEC podpisů. V okamžiku oznámení služba nevalidovala ECDSA podpisy, tento problém však již byl odstraněn. V zájmu ochrany soukromí uživatelů služba dle svých slov neposílá autoritativním serverům rozšíření EDNS Client-Subnet, což velmi pravděpodobně způsobí neoptimální doručování obsahu z CDN sítí; zvlášť vzhledem k tomu, že podle našeho pozorování je vnější adresa nebližšího uzlu této služby až v USA.
Je na čase vypnout SMB verze 1
Minulý týden byla také odhalena zranitelnost balíku Samba ve všech verzích od 4.0.0. Chyba se týká implementace zastaralého protokolu SMB1 a umožňuje potenciálně spustit vlastní kód na serveru. Kromě aktualizace je možné problém vyřešit také vypnutím podpory zastaralého protokolu; to ostatně radí i odborník ze společnosti Microsoft.
Jedinými legitimními důvody, proč je potřeba SMBv1 držet, může být podpora Windows XP nebo Windows Server 2003, závislost softwaru na funkci Okolní počítače, případně podpora starých kopírek s funkcí Scan-to-share. Naopak nejnovější verze Windows už přichází bez podpory SMBv1.
Linus Torvalds: bezpečnostní problémy jsou jen chyby
V e-mailové konferenci vývojářů Linuxu se Linus Torvalds svým stylem ostře ohradil proti způsobu, jakým se někteří vývojáři snaží do zdrojového kódu protlačit bezpečnostní hardening.
NENÍ MOŽNÉ, aby si bezpečáci vymýšleli nějaká nová magická pravidla a nechali jádro zhavarovat, kdykoli dojde k jejich porušení.
Zdůrazňuje, že i bezpečnostní problémy jsou jen obyčejné chyby a primární úlohou hardeningu tedy má být takové chyby najít a upozornit na ně. Teprve po určité době, kdy je zřejmé, že nově zavedená omezení nezpůsobují problémy ve všech běžných podmínkách je možné zvážit zavedení drastičtějších opatření.
Pro pobavení
Half past twelve
And I'm watchin' the late show
In my flat all alone
How I hate to spend the evening on my own
…
Gimme, gimme, gimme a man after midnight
Won't somebody help me chase the shadows away
Kdo by neznal skladbu skupiny ABBA z roku 1979. Ovšem jen málokoho při poslechu textu napadne, že osamělá hrdinka sledující noční televizní vysílání v půl jedné ráno vlastně touží po čtení unixových manuálových stránek. Nevinný žertík, který tuhle skladbu připomíná, bohužel rozbíjí neinteraktivní volání příkazu man s přepínačem -w , a tak byl nakonec odstraněn. Ostatně, ať děláte co děláte, vždycky někomu znemožníte práci.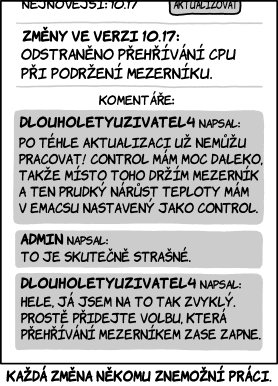
Autor: Randall Munroe, překlad xkcz.cz, podle licence: CC BY-NC 2.5
Službě Imgur unikly e-maily a hesla uživatelů, tři roky o tom nevěděla
27.11.2017 Lupa.cz Incidenty
Populární stránce Imgur, na které se ukládají obrázky, byly ukradeny přihlašovací e-maily a hesla k 1,7 milionu uživatelských účtů. Stalo se tak už v roce 2014, Imgur o tom nicméně dlouho nevěděl a o věci se dozvěděl až před pár dny. Nyní firma záležitost rozebírá na svém blogu.
Necelé dva miliony uživatelů jsou malá část registrovaných uživatelů Imgur, ten jich celkem má asi 150 milionů. Služba napadeným uživatelům hesla resetuje a o incidentu je postupně informuje.
Imgur prozatím nemá přesné informace, jak k úniku došlo. Provádí se šetření, které pak má vést také ke spolupráci s policií a úřady.
„Vždy jsme vaše hesla v naší databázi šifrovali, mohla ale být cracknuta pomocí brute force kvůli použití staršího algoritmu (SHA-256), který jsme tehdy používali. Algoritmus jsme v loňském roce aktualizovali na bcrypt,“ píše Imgur.
Researcher found a vulnerability in Facebook polls that allowed removal of any photo
27.11.2017 securityweek Social
The Iran-based security researcher Pouya Darabi discovered a method to delete any photo from Facebook exploiting a flaw in the polling feature.
The Iran-based security researcher Pouya Darabi received a $10,000 bounty from Facebook after reporting a critical vulnerability that could have been exploited to delete any photo from the social network.
Early this month, the social network giant announced a new feature for posting polls that include images and GIF animations. Darabi analyzed the new feature and discovered that it is affected by a vulnerability easily exploitable.
The expert analyzed the request sent to Facebook servers when a user creates a poll and discovered the presence of the identifiers of the image files added to the poll.

Replacing the image ID in the request with the ID of any photo on the social network it possible to set the image for the poll.
Darabi then discovered once the user that created the poll has deleted the post, the image whose ID was added to the request would also get removed from the social network.
“When this field value changes to any other images ID, that image will be shown in poll. After sending request with another user image ID, a poll containing that image would be created.” explained the researcher that published a video PoC.
“At the end when we try to delete the poll, victim’s image would be deleted with it by facebook as a poll property.”
Darabi reported the flaw to Facebook on November 3, the company issued a temporary fix in the same day. The permanent fix was completed in November 5, and on November 8 the expert received a $10,000 Bounty award.
Back in 2015, Darabi was awarded $15,000 for bypassing the Facebook cross-site request forgery (CSRF) protection systems, in 2016 he received another $7,500 award for a similar bug.