
- BotNet -
Last update 23.09.2017 19:27:30
Introduction List Kategorie Subcategory 0 1 2 3 4 5 6 7 8
Huge Russia-Linked botnet VPNFilter ready to launch a massive attack on Ukraine
24.5.2018 securityaffairs BotNet
Security firm Talos along with other cybersecurity firms and law enforcement agencies have uncovered a huge botnet dubbed VPNFilter, composed of more than 500,000 compromised routers and network-attached storage (NAS) devices.
The experts believe the VPNFilter was developed by Russia and the associated malware appears to be very sophisticated, at the time they discovered more than 500,000 compromised devices across 54 countries.
“For several months, Talos has been working with public- and private-sector threat intelligence partners and law enforcement in researching an advanced, likely state-sponsored or state-affiliated actor’s widespread use of a sophisticated modular malware system we call ‘VPNFilter.'” reads the blog post published by Talos.
“We have not completed our research, but recent events have convinced us that the correct way forward is to now share our findings so that affected parties can take the appropriate action to defend themselves.”
Even if the experts are still investigating the botnet, they decided to publish an initial report fearing an imminent massive attack powered by VPNFilter.
Researchers believe the nation-state malware was developed by the same author of the BlackEnergy malware.
Many infected devices have been discovered in Ukraine and their number in the country continues to increase. On May 8, Talos researchers observed a spike in VPNFilter infection activity, most infections in Ukraine and the majority of compromised devices contacted a separate stage 2 C2 infrastructure at the IP 46.151.209[.]33.
The experts discovered the VPNFilter malware has infected devices manufactured by Linksys, MikroTik, Netgear, QNAP, and TP-Link.
At the time of writing, the experts haven’t yet identified the attack vector.
VPNFilter is a multi-stage, modular strain of malware that has a wide range of capabilities for both cyber espionage and sabotage purpose.
“As of this writing, we are aware of two plugin modules: a packet sniffer for collecting traffic that passes through the device, including theft of website credentials and monitoring of Modbus SCADA protocols, and a communications module that allows stage 2 to communicate over Tor.” continues the report.
“We assess with high confidence that several other plugin modules exist, but we have yet to discover them.”

Experts are particularly concerned by the destructive features implemented by the malware that could allow attackers to burn users’ devices to cover up their tracks.
Experts believe that the attack could be launched by threat actors during the Ukrainian celebration of the Constitution Day, last year the NotPetya wiper attack was launched on the same period.
“VPNFilter is an expansive, robust, highly capable, and dangerous threat that targets devices that are challenging to defend. Its highly modular framework allows for rapid changes to the actor’s operational infrastructure, serving their goals of misattribution, intelligence collection, and finding a platform to conduct attacks,” Talos concluded.
Botnets Target Zero-Days in GPON Routers
23.5.2018 securityweek BotNet
Two unpatched vulnerabilities in Dasan’s Gigabit-capable Passive Optical Network (GPON) routers are being exploited by Internet of Things (IoT) botnets, security researchers warn.
Tracked as CVE-2018-10561 and CVE-2018-10562, the two vulnerabilities were publicly disclosed in early May and impact hundreds of thousands of devices. The flaws can be exploited remotely, providing an attacker with full control of the impacted devices.
South Korea-based Dasan Networks hasn’t released a fix for these issues as of now, yet the first attempts to exploit the bugs were registered within days after the disclosure. An unofficial patch for the bugs was made available a couple of weeks back.
Last week, Fortinet alerted on Wicked, a new variant of Mirai that has added exploits for the GPON vulnerabilities to its arsenal. The security firm also revealed that a botnet iteration called Omni was being dropped onto the compromised devices.
According to researchers from Qihoo 360 Netlab, there were five botnets targeting the two GPON vulnerabilities last week, namely Hajime, Mettle, Mirai, Muhstik, and Satori.
Now, the security researchers reveal that an older botnet called TheMoon has joined the GPON party as well. Active since at least 2014, the botnet has merged at least 6 different IoT exploits last year, and appears to continue to evolve.
“A very special thing about this round is the attacking payload. It is different from all previous ones, so it looks like a 0day. And we tested this payload on two different versions of GPON home router, all work. All these make TheMoon totally different, and we chose not to disclose the attack payload details,” Netlab notes.
Trend Micro also reports Mirai-like scanning activity in Mexico, with GPON routers being the target. This is unsurprising, given that most of the Internet-exposed Dasan routers affected by the two flaws are located in Mexico, Kazakhstan, and Vietnam.
“Unlike the previous activity, the targets for this new scanning procedure are distributed. However, based on the username and password combinations we found in our data, we concluded that the target devices still consist of home routers or IP cameras that use default passwords,” Trend Micro notes.
However, the attacks also attempt to compromise the targeted devices using vulnerabilities, the security firm notes. A downloading script is used to fetch malware variants for four different architectures, namely ARM, ARMv7, MIPS and MIPS little-endian, common architectures in embedded and IoT devices.
Updated – The new Wicked Mirai botnet leverages at least three new exploits
20.5.2018 securityaffairs BotNet
Security experts from Fortinet have spotted a new variant of the Mirai botnet dubbed ‘Wicked Mirai’, it includes new exploits and spread a new bot.
The name Wicked Mirai comes from the strings in the code, the experts discovered that this new variant includes at least three new exploits compared to the original one.
“The FortiGuard Labs team has seen an increasing number of Mirai variants, thanks to the source code being made public two years ago.” reads the analysis published by Fortinet.
“Some made significant modifications, such as adding the capability to turn infected devices into swarms of malware proxies and cryptominers. Others integrated Mirai code with multiple exploits targeting both known and unknown vulnerabilities, similar to a new variant recently discovered by FortiGuard Labs, which we now call WICKED.”

The Mirai botnet was first spotted in 2016 by the experts at MalwareMustDie, at the time it was used to power massive DDoS attacks in the wild. The Mirai’s source code was leaked online in October 2016, since then many other variants emerged in the wild, including Satori, Masuta, and Okiru.
According to Fortinet, the author of the Wicked Mirai is the same as the other variants.
Mirai botnets are usually composed of three main modules: Attack, Killer, and Scanner. Fortinet focused its analysis on the Scanner module that is responsible for the propagation of the malware.
The original Mirai leveraged brute force attempts to compromise other IOT devices, while the WICKED Mirai uses known exploits.
The Wicked Mirai would scan ports 8080, 8443, 80, and 81 by initiating a raw socket SYN connection to IoT devices. Once it has established a connection, the bot will attempt to exploit the device and download its payload by writing the exploit strings to the socket through the write() syscall.
The experts discovered that the exploit to be used depends on the specific port the bot was able to connect to. Below the list of devices targeted by the Wicked Mirai
Port 8080: Netgear DGN1000 and DGN2200 v1 routers (also used by Reaper botnet)
Port 81: CCTV-DVR Remote Code Execution
Port 8443: Netgear R7000 and R6400 Command Injection (CVE-2016-6277)
Port 80: Invoker shell in compromised web servers
The analysis of the code revealed the presence of the string SoraLOADER, which suggested it might attempt to distribute the Sora botnet. Further investigation allowed the researchers to contradict this hypothesis and confirmed the bot would actually connect to a malicious domain to download the Owari Mirai bot.
“After a successful exploit, this bot then downloads its payload from a malicious web site, in this case, hxxp://185[.]246[.]152[.]173/exploit/owari.{extension}. This makes it obvious that it aims to download the Owari bot, another Mirai variant, instead of the previously hinted at Sora bot.” reads the analysis.
“However, at the time of analysis, the Owari bot samples could no longer be found in the website directory. In another turn of events, it turns out that they have been replaced by the samples shown below, which were later found to be the Omni bot.”
The analysis of the website’s /bins directory revealed other Omni samples, which were apparently delivered using the GPON vulnerability CVE-2018-10561.

Searching for a link between Wicked, Sora, Owari, and Omni, the security researchers at Fortinet found an interview with Owari/Sora IoT Botnet author dated back to April.
The vxer, who goes by the online handle of “Wicked,” that at the time said he abandoned the Sora botnet and was working on Owari one.
The conversation suggests the author abandoned both Sora and Owari bots and he is currently working on the Omni project.
“Based on the author’s statements in the above-mentioned interview as to the different botnets being hosted in the same host, we can essentially confirm that the author of the botnets Wicked, Sora, Owari, and Omni are one and the same. This also leads us to the conclusion that while the WICKED bot was originally meant to deliver the Sora botnet, it was later repurposed to serve the author’s succeeding projects,” Fortinet concludes.
Update May 19, 2018 – Spaeaking with MalwareMustDie
I have contacted Malware Must Die for a comment on the Wicked Mirai botnet.
Below the observations he shared with me:
Same coder.
The author put all of the high-possibility exploit code in Mirai
GPON was seemed used on separate pwn scheme by different script outside of the Mirai, but being used to infect Mirai.
MalwareMustDie researchers told me that they passed the identity of the author to the related country LEA. They explained to me that even if they made several reports to the authorities, law enforcement failed in preventing the diffusion of the malicious code. The experts showed me official report to LEA dated back January 2018, when they alerted authorities of propagations of new Mirai variants.
“the ID of the actor was passed to the related country LEA from our team that investigated result too since we published the Satori/Okiru variant a while ago, way before ARC CPU variant was spotted.” MMD told me.
“So by the release of the OWARI, SORA, and WICKED, this is what will happen if we let the malware actor running loose unarrested. More damage will be created and they just don’t know how to stop them self.”
Satori Botnet is targeting exposed Ethereum mining pools running the Claymore mining software
19.5.2018 securityaffairs BotNet
While a new variant of the dreaded Mirai botnet, so-called Wicked Mirai, emerged in the wild the operators of the Mirai Satori botnet appear very active.
Experts observed hackers using the Satori botnet to mass-scan the Internet for exposed Ethereum mining pools, they are scanning for devices with port 3333 exposed online.
The port 3333 is a port commonly used for remote management by a large number of cryptocurrency-mining equipment.
The activities were reported by several research teams, including Qihoo 360 Netlab, SANS ISC, and GreyNoise Intelligence.

360 Netlab
@360Netlab
Do you see port 3333 scan traffic going up? Satori botnet is scanning it now, see our Scanmon trend https://scan.netlab.360.com/#/dashboard?tsbeg=1525536000000&tsend=1526140800000&dstport=3333&toplistname=srcip&topn=10&sortby=sum …, and try a dns lookup for one of the control domain it is using now, dig any http://c.sunnyjuly.gq , I personally like yesterday's TXT result more
8:32 PM - May 11, 2018
30
19 people are talking about this
Twitter Ads info and privacy
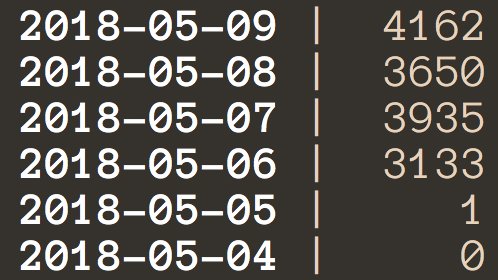
Starting from May 11, experts are observing the spike in activity of the Satori botnet.
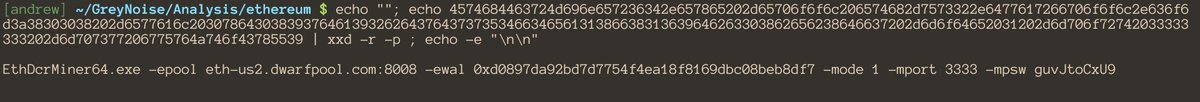
According to the researchers at GreyNoise, threat actors are focused on equipment running the Claymore mining software, once the attackers have found a server running this software they will push instructions to force the device to join the ‘dwarfpool’ mining pool using the ETH wallet controlled by the attackers.
GreyNoise Intelligence
@GreyNoiseIO
12 May
GreyNoise observed a large spike of TCP port 3333 scan traffic today. This is the default port for the "Claymore" dual Ethereum/Decred cryptocurrency miner. pic.twitter.com/5g6vVbPLNq
GreyNoise Intelligence
@GreyNoiseIO
Once the attacker identifies a server running the Claymore software they push instructions to reconfigure the device to join the "dwarfpool" mining pool and use the attacker's ETH wallet (https://etherscan.io/address/0xd0897da92bd7d7754f4ea18f8169dbc08beb8df7 …) pic.twitter.com/0IVo7CKsjf
12:43 AM - May 12, 2018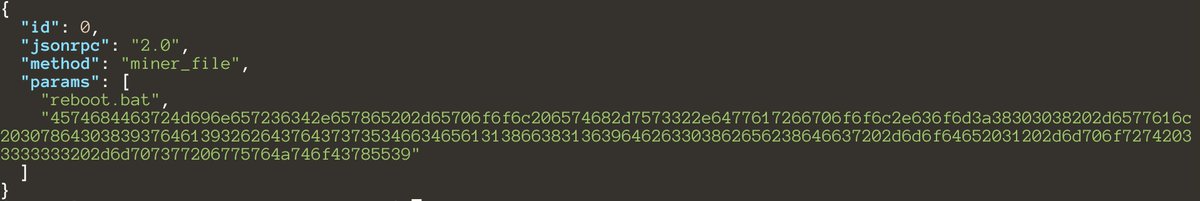
2
See GreyNoise Intelligence's other Tweets
Twitter Ads info and privacy
The experts noticed that most of the devices involved in the mass scanning are compromised GPON routers located in Mexico.
The experts monitored five botnets using the compromised GPON routers to scan for Claymore miners, one of them is the Satori botnet that is leveraging an exploit for the attack.
GreyNoise Intelligence
@GreyNoiseIO
12 May
Replying to @GreyNoiseIO
Effective 6:43 PM EST the attacker has only mined ~$200 worth of ETH
GreyNoise Intelligence
@GreyNoiseIO
Interestingly, 95% of the devices scanning for port 3333 today are located in the same residential ISP in Mexico (https://twitter.com/Telmex ) as the majority of the hosts affected by the GPON vulnerability disclosed earlier this week. https://twitter.com/GreyNoiseIO/status/994486111178252288 …
12:45 AM - May 12, 2018
1
See GreyNoise Intelligence's other Tweets
Twitter Ads info and privacy
GreyNoise Intelligence
@GreyNoiseIO
GreyNoise has observed ~13,000 compromised home routers probing the Internet for the '/GponForm/diag_Form' URI over the past 96 hours, likely related to the weaponization of CVE-2018-10561. Most devices are located in the "Uninet" ISP in Mexico.
Ref: https://github.com/f3d0x0/GPON
9:55 AM - May 10, 2018
20
22 people are talking about this
Twitter Ads info and privacy
Below the details of the five botnets published by Netlab 360:
Satori: Satori is the infamous variant of the mirai botnet.
We first observed this botnet coming after the GPON vulnerable devices at 2018-05-10 05:51:18, several hours before our last publish.
It has quickly overtakes muhstik as the No.1 player.
Mettle: A malicious campaign based on IP addresses in Vietnam (C2 210.245.26.180:4441, scanner 118.70.80.143) and mettle open source control module
Hajime: Hajime pushed an update which adds the GPON’s exploits
Two Mirai variants: At least two malicious branches are actively exploiting this vulnerability to propagate mirai variants. One of them has been called omni by newskysecurity team.
imgay: This appears like a botnet that is under development. Its function is not finished yet.
“In our previous article, we mentioned since this GPON Vulnerability (CVE-2018-10561, CVE-2018-10562 ) announced, there have been at least five botnets family mettle, muhstik, mirai, hajime, satori actively exploit the vulnerability to build their zombie army in just 10 days.” reads a blog post published by Netlab 360.
“From our estimate, only 2% all GPON home router is affected, most of which located in Mexico.”
“The source of this scan is about 17k independent IP addresses, mainly from Uninet SA de CV, telmex.com, located in Mexico,”
Researchers at SANS ISC that analyzed the Satori botnet activity discovered the bot is currently exploiting the CVE-2018-1000049 remote code execution flaw that affects the Nanopool Claymore Dual Miner software.
The experts observed the availability online of proof-of-concept code for the CVE-2018-1000049 vulnerability.
“The scan is consistent with a vulnerability, CVE 2018-1000049, released in February [2]. The JSON RPC remote management API does provide a function to upload “reboot.bat”, a script that can then be executed remotely. The attacker can upload and execute an arbitrary command using this feature.” reads the analysis published by the SANS ISC.
“The port the API is listening on is specified when starting the miner, but it defaults to 3333. The feature allows for a “read-only” mode by specifying a negative port, which disables the most dangerous features. There doesn’t appear to be an option to require authentication.”
"Wicked" Variant of Mirai Botnet Emerges
18.5.2018 securityweek BotNet
A new variant of the Mirai Internet of Things (IoT) botnet has emerged, which features new exploits in its arsenal and distributing a new bot, Fortinet researchers warn.
Called Wicked, based on strings found in the code, the malware has added three new exploits compared to Mirai and appears to be the work of the same developer behind other Mirai variants.
The Mirai botnet was first spotted in the third quarter of 2016, when it fueled some of the largest distributed denial of service (DDoS) attacks at the time. The malware’s source code was leaked online in October 2016, and numerous variants have been observed ever since: Masuta, Satori, Okiru, and others.
Similar to other botnets based on Mirai, the newly discovered Wicked iteration contains three main modules: Attack, Killer, and Scanner. Unlike Mirai, however, which used brute force to gain access to vulnerable IoT devices, Wicked uses known and available exploits, many of which are already old, the security researchers discovered.
Wicked would scan ports 8080, 8443, 80, and 81 by initiating a raw socket SYN connection to the target device. Upon establishing a connection, the malware attempts to exploit the device and upload a payload to it by writing the exploit strings to the socket.
The used exploit depends on the specific port that the connection was established to. On port 8080, the malware uses Netgear DGN1000 and DGN2200 v1 router exploits (also used by Reaper botnet), on port 81 it uses a CCTV-DVR Remote Code Execution exploit, on port 8443 a Netgear R7000 and R6400 Command Injection (CVE-2016-6277), and on port 80 an invoker shell in compromised web servers.
Wicked contains the string SoraLOADER, which initially suggested it might attempt to distribute the Sora botnet. Instead, the researchers discovered that the malware would actually connect to a malicious domain to download the Owari bot, a different Mirai variant.
Although the website was confirmed to have distributed Owari, the security researchers couldn’t retrieve bot samples from the website directory. Furthermore, they discovered that the samples had been replaced by another malware family, the Omni bot.
Looking through the website’s /bins directory, the security researchers discovered other Omni samples, which were apparently delivered using the Gigabit-capable Passive Optical Network (GPON) vulnerability CVE-2018-10561.
While looking for the connections between Wicked, Sora, Owari, and Omni, the security researchers found an April interview with the developer behind Sora and Owari, who goes by the online handle of “Wicked” himself. At the time, the malware author said that Sora was abandoned, but work on Owari would continue, with no new projects planned.
Based on their findings and the malware author’s saying, Fortinet believes that both Sora and Owari bots have been abandoned, and that Omni is the current project the developer works on.
“Based on the author’s statements in the above-mentioned interview as to the different botnets being hosted in the same host, we can essentially confirm that the author of the botnets Wicked, Sora, Owari, and Omni are one and the same. This also leads us to the conclusion that while the WICKED bot was originally meant to deliver the Sora botnet, it was later repurposed to serve the author’s succeeding projects,” Fortinet concludes.
The new Wicked Mirai botnet leverages at least three new exploits
18.5.2018 securityaffairs BotNet
Security experts from Fortinet have spotted a new variant of the Mirai botnet dubbed ‘Wicked Mirai’, it includes new exploits and spread a new bot.
The name Wicked Mirai comes from the strings in the code, the experts discovered that this new variant includes at least three new exploits compared to the original one.
“The FortiGuard Labs team has seen an increasing number of Mirai variants, thanks to the source code being made public two years ago.” reads the analysis published by Fortinet.
“Some made significant modifications, such as adding the capability to turn infected devices into swarms of malware proxies and cryptominers. Others integrated Mirai code with multiple exploits targeting both known and unknown vulnerabilities, similar to a new variant recently discovered by FortiGuard Labs, which we now call WICKED.”

The Mirai botnet was first spotted in 2016 by the experts at MalwareMustDie, at the time it was used to power massive DDoS attacks in the wild. The Mirai’s source code was leaked online in October 2016, since then many other variants emerged in the wild, including Satori, Masuta, and Okiru.
According to Fortinet, the author of the Wicked Mirai is the same as the other variants.
Mirai botnets are usually composed of three main modules: Attack, Killer, and Scanner. Fortinet focused its analysis on the Scanner module that is responsible for the propagation of the malware.
The original Mirai leveraged brute force attempts to compromise other IOT devices, while the WICKED Mirai uses known exploits.
The Wicked Mirai would scan ports 8080, 8443, 80, and 81 by initiating a raw socket SYN connection to IoT devices. Once it has established a connection, the bot will attempt to exploit the device and download its payload by writing the exploit strings to the socket through the write() syscall.
The experts discovered that the exploit to be used depends on the specific port the bot was able to connect to. Below the list of devices targeted by the Wicked Mirai
Port 8080: Netgear DGN1000 and DGN2200 v1 routers (also used by Reaper botnet)
Port 81: CCTV-DVR Remote Code Execution
Port 8443: Netgear R7000 and R6400 Command Injection (CVE-2016-6277)
Port 80: Invoker shell in compromised web servers
The analysis of the code revealed the presence of the string SoraLOADER, which suggested it might attempt to distribute the Sora botnet. Further investigation allowed the researchers to contradict this hypothesis and confirmed the bot would actually connect to a malicious domain to download the Owari Mirai bot.
“After a successful exploit, this bot then downloads its payload from a malicious web site, in this case, hxxp://185[.]246[.]152[.]173/exploit/owari.{extension}. This makes it obvious that it aims to download the Owari bot, another Mirai variant, instead of the previously hinted at Sora bot.” reads the analysis.
“However, at the time of analysis, the Owari bot samples could no longer be found in the website directory. In another turn of events, it turns out that they have been replaced by the samples shown below, which were later found to be the Omni bot.”
The analysis of the website’s /bins directory revealed other Omni samples, which were apparently delivered using the GPON vulnerability CVE-2018-10561.

Searching for a link between Wicked, Sora, Owari, and Omni, the security researchers at Fortinet found a conversation with Owari/Sora IoT Botnet author dated back to April.
The vxer, who goes by the online handle of “Wicked,” that at the time said he abandoned the Sora botnet and was working on Owari one.
The conversation suggests the author abandoned both Sora and Owari bots and he is currently working on the Omni project.
“Based on the author’s statements in the above-mentioned interview as to the different botnets being hosted in the same host, we can essentially confirm that the author of the botnets Wicked, Sora, Owari, and Omni are one and the same. This also leads us to the conclusion that while the WICKED bot was originally meant to deliver the Sora botnet, it was later repurposed to serve the author’s succeeding projects,” Fortinet concludes.
Hide 'N Seek IoT Botnet Can Survive Device Reboots
8.5.2018 securityweek BotNet
The Internet of Things (IoT) botnet known as Hide 'N Seek that first emerged in January can now achieve persistence on infected devices, Bitdefender reports.
Discovered toward the end of April, the latest version of the malware also includes code that allows it to target more vulnerabilities and new types of devices, the security firm discovered, adding that it targets 10 different architectures and a broad range of models.
The botnet has so far infected 90,000 unique devices starting in January, and could become a major threat if weaponized.
When first observed in January, the botnet didn’t have a persistence module, meaning it was not able to survive a device reboot. This, however, changed in the last version: if it manages to successfully compromise a device via Telnet, the malware copies itself to /etc/init.d/ and adds itself to startup, so it is executed when the operating system launches.
The malware also abuses web based vulnerabilities to target specific devices like IPTV cameras, but persistence is only achieved if the infection took place via Telnet, because root privileges are required to copy the binary to the init.d directory, Bitdefender Senior E-Threat Analyst Bogdan Botezatu explains.
The malware targets a broad range of devices via the Telnet service. According to Bitdefender, the bot has 10 different binaries compiled for x86, x64, ARM (Little Endian and Big Endian), SuperH, PPC and other platforms.
The latest Hide 'N Seek version can compromise more IPTV camera models by targeting vulnerabilities in Wansview NCS601W IP camera (a cloud-only device) and AVTECH IP Camera, NVR and DVR (the maker’s products have been targeted by other IoT malware as well).
Responding to a SecurityWeek inquiry, Botezatu revealed that the Hide 'N Seek malware targets a long list of weak or default credentials frequently found in IoT devices.
“The list is extremely long and features several camera models, but the hardcoded credentials also target several router models. In addition to specific models, the bot also attempts these credentials against Telnet for all sorts of devices. The fact that it has binaries compiled for 10 platforms and architectures shows that the attacker is aiming at enrolling as many devices, regardless of type, maker, and model,” Botezatu said.
“We've notified vendors about this,” he added.
Over the past three months, Hide 'N Seek has been growing steadily although some devices left the botnet, while others joined it. Most likely, the botnet lost those devices “that could not be exploited in a way to offer persistence,” Botezatu said.
From February to May, however, Bitdefender’s security researchers identified almost 65,000 infected devices.
Botezatu told SecurityWeek that five versions of the botnet have been observed thus far. However, there haven’t been major changes in the list of supported commands compared to the earlier versions, and no support for distributed denial of service (DDoS), the most commonly encountered purpose of IoT botnets, has been added to Hide 'N Seek either.
“Based on the evidence at hand, we presume that this botnet is in the growth phase, as operators are trying to seize as many devices as possible before adding weaponized features to the binary,” Botezatu revealed.
As for the current geographic distribution of the bots, most of them are located in China, with Russia, Brazil, the United States, and Italy rounding up top five, followed by India, Poland, Bulgaria, France, and Republic of Korea.
Necurs Spam Botnet operators adopt a new technique to avoid detection
28.4.2018 securityaffairs BotNet
Operators behind the Necurs botnet, the world’s largest spam botnet, are currently using a new evasion technique attempting to surprise the unprepared defenses.
Necurs is the world’s largest spam botnet, it is composed of millions of infected computers worldwide.
Necurs was not active for a long period at the beginning of 2017 and resumed its activity in April 2017. The Necurs botnet was used in the past months to push some malware, including Locky, Jaff, GlobeImposter, Dridex , Scarab and the Trickbot.
In February security experts observed the Necurs botnet was used to send out an amazing number of messages offering companionship waiting for Valentine’s day.
According to the IBM X-Force team, the campaign started in mid-January, it leveraged the overall Necurs botnet that has been estimated as composed of 6 million bots.
Now the botnet made the headlines again, the author implemented a new evasion technique. Crooks are sending out an email to a potential victim containing an archive file that once unzipped will present a file with the extension of .URL.
The .URL extension is associated with Windows shortcut file that opens an URL into a browser, in the campaign observed by the experts it points to a remote script file that downloads and executes a final payload.
In this last campaign, Necurs is delivering the Quant Loader to the victims to download another malware.
“As security vendors are wise to Necurs’s traditional infection chain (a script, a macro, or archives containing certain file formats), the malware has started using an internet shortcut or .URL file to bypass detection.” reads the analysis published by Trend Micro.
“Previously, Necurs’s JavaScript downloader downloads the final payload. But in its latest iteration, the remote script downloads QUANTLOADER (detected by Trend Micro as TROJ_QUANT) – a different downloader – which then downloads the final payload. This is another layer added to Necurs’s infection chain.”
The abuse of .URL files is a novelty for Necurs operators. according to the researchers, this technique implements a simplified infection chain compared to spam techniques used in the past.
“Last year, we also saw how Necurs pushed double-zipped attachments that either contained JavaScript, Visual Basic scripts, or macro files with the capability to download its final payload.” continues the analysis.
“In an attempt to evade spam detection through its attachments, Necurs used archives that included .ZIP files to disguise the script downloader, which was later enclosed in another .ZIP to hide itself.”

This simple infection chain allows avoiding anti-malware solutions that scan emails, looking for malicious links, boobytrapped attachments or other malicious patterns associated with an attack.
Of course, once uncovered the new campaign, the security firms will update existing detection rules to rapidly discovers attacks and neutralize the spam campaign.
Malware researchers added that crooks are using the standard folder icon to hide .URL files to deceive victims on their malicious nature.
Once the victim has clicked on the archive it extracts a file that appears to the victims as a new folder on their PC. When the victims click on the folder to explore its content they will start the infection chain.
“Notice that aside from the icons disguised as folders, the filenames were also crafted to resemble typical folder names such as IMG-20180404-9AC4DD, SCN-20180404-268CC1, and PIC-20180404-ADEEEE shown in Figure 2, to name a few.” states Trend Micro.

Now that you know this new technique … open the eyes and remain vigilant.
Experts uncovered a proxy botnet composed of over 65,000 routers exposed via UPnP protocol
14.4.2018 securityaffairs BotNet
Security researchers at Akamai have discovered a proxy botnet composed of more than 65,000 routers exposed to the Internet via the Universal Plug and Play (UPnP) protocol.
Crooks have compromised the devices of this multi-purpose proxy botnet to conduct a wide range of malicious activities, including spamming and phishing, click fraud, account takeover and credit card fraud, distributed denial of service (DDoS) attacks, malware distribution, and also bypassing censorship,
While the researchers were investigating attacks against its customers they discovered that vulnerable devices have NAT injections that allow attackers to abuse them.
“While researching UPnP-enabled devices detected as participants in attacks against Akamai customers, we discovered that some devices appeared to be more susceptible to this vulnerability than others, and contained malicious NAT injections.” reads the analysis published by Akamai. “These injections were present on a handful of the devices found in the wild, and appeared to be part of an organized and widespread abuse campaign”

Akamai discovered over 4.8 million devices that were found to be vulnerable to simple UDP SSDP inquiries. Of these, roughly 765,000 (16% of total) were confirmed to also
expose their vulnerable TCP implementations while over 65,000 (1.3% of total) were discovered to have NAT injections.
“These injections appeared to point to multiple services and servers around the Internet. A majority of the injections appear to target TCP ports 53 (15.9M for DNS), 80 (9.5M for HTTP), and 443 (155K for HTTPS).” continues the analysis. “A wide range of devices are affected, most of them being consumer-grade networking hardware. “73 brands/manufacturers and close to 400 models [were affected].”
The UPnP communication protocol is widely adopted even if it is known to be vulnerable. In early 2013, researchers at Rapid7 published an interesting whitepaper entitled “Security Flaws in Universal Plug and Play” that evaluated the global exposure of UPnP-enabled network devices.
The report highlighted that over 23 million IPs related to Portable UPnP SDK were vulnerable to remote code execution just through a single UDP packet, over 6,900 product versions from over 1,500 vendors were vulnerable through UPnP due to the exposure of UPnP SOAP service to the internet.
Abusing the protocol attackers can control the traffic in and out the networks, UPnP allows the automated negotiation and configuration of port opening/forwarding within a NATed networking environment.
The malicious botnet uncovered by Akamai is composed of vulnerable devices including malicious NAT injections, it turns routers into proxies, for this reason, the experts called the injected devices UPnProxy.
“The injected NAT entries were designed to be working in sets across various devices. Thus, across the 65,000 infected devices, 17,599 unique endpoint IP addresses were discovered.” continues the report. “The most-identified IP was injected over 18.8 million times across 23,286 devices, while the second-most-injected IP appeared over 11 million times across 59,943 devices.”
According to Akamai, part of this proxy botnet was already discovered by researchers at Symantec while investigating into the “Inception Framework” used by an APT group, in that circumstance Symantec research confirmed that the UPnProxy instances were used obfuscate the operators’ true locations.
The APT associated with Inception Framework is still active and continuously evolved its arsenal and TTPs.
In order to check if your router has been compromised for UPnProxying is to scan the endpoint and audit your NAT table entries.
Many frameworks and libraries available online could be used for this purpose.
Multi-Purpose Proxy Botnet Ensnares 65,000 Routers
13.4.2018 securityweek BotNet
More than 65,000 routers exposed to the Internet via the Universal Plug and Play (UPnP) protocol are being abused by cybercriminals as part of a large, multi-purpose proxy botnet, Akamai has discovered.
The vulnerable devices were found to have NAT injections that allow malicious actors to abuse them for various purposes, such as bypassing censorship, spamming and phishing, click fraud, account takeover and credit card fraud, distributed denial of service (DDoS) attacks, malware distribution, and more.
The 65,000 injected devices, Akamai reveals, are part of a larger set of over 4.8 million devices that were found to be vulnerable to simple UDP SSDP (the UDP portion of UPnP) inquiries. Around 765,000 of the devices were also found to expose their vulnerable TCP implementations, the security firm says.
Most of the impacted devices are consumer-grade networking hardware coming from 73 brands / manufacturers. Nearly 400 models were found vulnerable, but other manufacturers and devices are also believed to be affected by these vulnerable UPnP implementations, Akamai reveals in a report (PDF).
Designed to allow better communication between devices on a LAN, the UPnP protocol is widely used, but is also long-known to be vulnerable. In fact, flawed implementations have been exposed for over a decade, with a 2013 report revealing tens of millions of vulnerable devices on the Internet.
The protocol allows for automated negotiation and configuration of port opening/forwarding within a NATed networking environment, meaning that devices on the network can open ports to expedite routing of traffic in and out of the network. Some of the exposed services, however, are privileged and meant to only be used by trusted devices on a LAN.
Some of the vulnerable devices include malicious NAT injections that appear to be part of an organized and widespread abuse campaign. The purpose of these injections is to turn routers into proxies, which led researchers to call injected devices UPnProxy.
The injected NAT entries were designed to be working in sets across various devices. Thus, across the 65,000 infected devices, 17,599 unique endpoint IP addresses were discovered. The most-identified IP was injected over 18.8 million times across 23,286 devices, while the second-most-injected IP appeared over 11 million times across 59,943 devices.
The injections were designed to point to multiple services and servers around the Internet and most of them targeted TCP ports 53 (15.9M for DNS), 80 (9.5M for HTTP), and 443 (155K for HTTPS).
The multi-purpose proxy botnet, Akamai says, appears related to the Inception Framework threat actor that was first exposed in 2014. The group was previously observed targeting Energy and Defense sectors, along with organizations in the Consultancy/Security, Aerospace, Research, and Media sectors, in addition to embassies.
In a report earlier this year, Symantec revealed that the actor has continued to operate over the past years, despite an apparent silence. The group has changed its tools and techniques, uses modular malware in attacks, and has widened its use of cloud service providers for command and control purposes.
Symantec also said that the group was abusing Internet of Things devices to hide behind proxies, leveraging the UPnP protocol to hijack vulnerable routers.
Akamai used Symantec’s findings as a starting point for their research and discovered two clusters of highly chained proxies within the injected devices. One of them is more evenly distributed, supposedly using smaller nodes as final hop before exiting the chain to their final destinations. The other, however, routes to a much larger collection of outward medium and small nodes, making tracking more difficult.
“The UPnProxy vulnerability, like many of the problems we’ve seen recently, was caused by unauthenticated services being exposed to the public Internet in ways they were never meant to be. Attackers have taken several aspects of known issues with UPnP and combined them to create a powerful proxy network to hide their traffic. While this is neither a remote exploit that allows the attacker to take over a computer nor a new reflection vector for DDoS, it is still a significant concern because of how it allows the origin of traffic to be hidden,” Akamai notes.
Financial Services DDoS Attacks Tied to Reaper Botnet
6.4.2018 securityweek BotNet
Recorded Future's "Insikt" threat intelligence research group has linked the Mirai variant IoTroop (aka Reaper) botnet with attacks on the Netherlands financial sector in January 2018.
The existence of IoTroop was first noted by Check Point in October 2017. At that point the botnet had not been used to deliver any known DDoS attacks, and its size was disputed. What was clear, however, was its potential for growth.
In January 2018, the financial services sector in the Netherlands was hit by a number of DDoS attacks. Targets included ABN Amro, Rabobank and Ing; but at that time the source of the attack was unknown.
Insikt researchers now report that at least one these financial services attacks -- and possibly more -- was the first known use of IoTroop to deliver a DDoS attack. "IoTroop is a powerful internet of things (IoT) botnet," reports Insikt, "primarily comprised of compromised home routers, TVs, DVRs, and IP cameras exploiting vulnerabilities in products from major vendors including MikroTik, Ubiquity and GoAhead."
The attack itself was not excessively high by modern standards. "The initial attack was a DNS amplification attack with traffic volumes peaking at 30Gb/s," reports Insikt -- far short of the 1.7Tb/s attack that occurred in February.
If the IoTroop assumption is correct, it is clear the botnet has evolved extensively since its discovery last year. Fortinet's SVP products and solutions reported last month, "the Reaper [IoTroop] exploit was built using a flexible Lua engine and scripts, which means that instead of being limited to the static, pre-programmed attacks of previous exploits, its code can be easily updated on the fly, allowing massive, in-place botnets to run new and more malicious attacks as soon as they become available."
Insikt reports that the malware can use at least a dozen vulnerabilities and can be updated by the attackers as new vulnerabilities are exposed. "Our analysis," it says, "shows the botnet involved in the first company attack was 80% comprised of compromised MikroTik routers with the remaining 20% composed of various IoT devices ranging from vulnerable Apache and IIS web servers to routers from Ubiquity, Cisco and ZyXEL. We also discovered Webcams, TVs and DVRs among the 20% of IoT devices, which included products from major vendors such as MikroTik, GoAhead, Ubiquity, Linksys, TP-Link and Dahua."
This list adds new devices now vulnerable to IoTroop in addition to those noted in the original October 2017 research -- which suggests, says Insikt, "a widespread and rapidly evolving botnet that appears to be leveraging publicly disclosed vulnerabilities in many IoT devices."
Insikt's research shows the January attack was delivered from 139 different countries, showing a widespread targeting of vulnerable IoT devices around the world. More than half of the attacking clients are located in the Russian Federation, Brazil, Ukraine, China and the U.S.; but this probably has no relevance other than popularity of MikroTik devices in those countries.
Insikt believes that its analysis of the January DDoS attacks makes it almost certain that at least one and probably more were delivered by IoTroop; but that the new devices included within the botnet show its continuing evolution. "The similarity in device composition with the IoTroop/Reaper botnet," it says, "suggest IoTroop has evolved to exploit vulnerabilities in additional IoT devices and is likely to continue to do so in the future in order to build up the botnet to facilitate larger DDoS attacks against the financial sector."
The research also found seven IP addresses that it believes are likely to be controllers for the botnet. Insikt urges industry to monitor these addresses for malicious activity since they "are likely to be engaged in aggressive scanning for new vulnerable IoT infrastructure to commandeer as well as be responsible for any Denial of Service, attack commands issued to the botnet clients."
Protecting consumer IoT devices is less simple, since consumers notoriously adopt an unpack, plug and play approach to new devices. Nevertheless, Recorded Future urges all users to immediately change default manufacturer passwords, to patch firmware wherever possible and required, to invest in a VPN for devices that have remote access (such as IP cameras), and -- perhaps less easily for consumers -- to disable unnecessary services such as Telnet.
The Big Business of Bad Bots
30.3.2018 securityweek BotNet
Bad bots are big news largely because of the FBI investigation into Russia's involvement in the 2016 presidential election. But bad bots are a bigger problem than automated tweeting: 42.2% of all website traffic comes from bots; and 21.8% of it is down to bad bots.
Distil Networks' 2018 Bad Bot Report, based on an analysis of hundreds of billions of bad bot requests, shows that bad bot traffic increased by 9.5% in 2017. Bad bots differ from good bots, whose traffic also increased by 8.8% to 20.4%. It means that only -- on average -- 57.8% of visiting traffic comes from a genuine human being interested in the website content.
Good bots are those that all websites require. They include the search engine page indexing bots from Google and Bing, and they bring humans to the site. Bad bots, however, are secretive and nefarious. They come from outright criminals and commercial competitors; and their purpose is to detract and/or steal from the website.
Distil highlights eight different bad bot functions: price scraping, content scraping, account takeover, account creation, credit card fraud, denial of service, gift card balance checking, and denial of inventory. They fall into three primary categories: competitive, organized criminal, and nuisance.
Price scraping and content scraping are generally competitor attacks. Price scraping allows competitors to maintain price levels slightly lower to score more highly in search engine rankings. Content scraping is simply the theft of proprietary content to augment another site's own content.
Account takeover bots are automated attempts at illegal log-ins. They can deliver brute-force attacks cycling through the most popular passwords to see if one of them works, or they can use the process known as credential stuffing.
Distil reports a 300% increase in credential stuffing bad bots in the weeks following a new major credential theft. This involves the automatic application of stolen passwords on different websites. "Here," notes the report, "bot operators make two assumptions. The first is that people reuse their credentials on many websites. The second is that newly stolen credentials are more likely to still be active. This is why businesses should anticipate bad bots running those credentials against their website after every breach."
Account creation bad bots simply generate vast numbers of new accounts -- for example, on Twitter -- to spam out messages or amplify propaganda.
Credit card fraud bots test out credit card numbers, trying to identify missing information -- such as the expiry date and the CVV.
The denial of service bad bot can be either competitive or nuisance. It can be used to reduce the performance of a competitor, or to disrupt the service of a small website either because of a grudge, or simply because it is possible. It can be effected either from a small number of attacking IP addresses, or from a larger number of rotating addresses. Automated defenses often fail because the number of accesses from each IP address is below the warning threshold before it moves to other addresses, while manual whack-a-mole IP blocking simply cannot keep up.
Gift card balance checking bots are used to steal money from gift card accounts that contain a balance.
'Denial of inventory' is a relatively new competitor attack prompted by the growth of ecommerce. In this attack, bots place stock items in online shopping baskets, taking them out stock lists. If the item is no longer available, then visiting human buyers will go elsewhere to make the purchase.
Bad bots are a difficult problem. Many website owners are not aware of them, while common defenses have little effect. Geo-blocking, for example, is only somewhat effective. Many sites block all Russian traffic. While this will inevitably include some bad bot traffic, it may also exclude some genuine human traffic. Russia is, however, the most blocked country.
In reality, the greatest source of bad bot traffic is the U.S. (although the operators may be elsewhere). According to Distil, 45.2% of all bad bot traffic originates in the United States (China is second, but way down with just 10.5%). This is because nobody, anywhere in the world, is likely to block all traffic coming from the U.S.
"This year bots took over public conversation, as the FBI continues its investigation into Russia's involvement in the 2016 U.S. presidential election and new legislation made way for stricter regulations," said Tiffany Olson Jones, CEO of Distil Networks. "Yet, as awareness grows, bot traffic and sophistication continue to escalate at an alarming rate. Despite bad bot awareness being at an all-time high, this year's Bad Bot Report illustrates that no industry is immune to automated threats and constant vigilance is required in order to thwart attacks of this kind."
TrickBot Gets Computer Locking Capabilities
23.3.2018 securityweek BotNet
A recently observed variant of the TrickBot banking Trojan has added a new module that can lock a victim’s computer for extortion purposes, Webroot reports.
First observed in late 2016 and said to be the work of cybercriminals behind the notorious Dyre Trojan, TrickBot has seen numerous updates that expanded not only its capabilities, but also its target list.
Last year, the malware received an update that added worm-like capabilities, allowing it to spread locally via Server Message Block (SMB).
Webroot now says that the malware attempts to leverage NSA-linked exploits released by Shadow Brokers last year in order to move laterally within compromised networks.
The new TrickBot variant installs itself into the %APPDATA%\TeamViewer\ directory, and once up and running, creates a “Modules” folder to store encrypted plug and play modules and configuration files.
While many of the modules have been already documented, the new Trojan variant also includes a module internally called spreader_x86.dll that Webroot hasn’t seen before. Featuring a large rdata section that contains two additional files, the spreader module contains an executable called SsExecutor_x86.exe and an additional module named screenLocker_x86.dll.
Spreader_x86.dll, the security researchers have discovered, was clearly designed to allow the malware to spread laterally through an infected network by leveraging the NSA-linked exploits.
“This module appears to make use of lateral movement in an attempt to set up the embedded executable as a service on the exploited system. Additionally, the TrickBot authors appear to be still developing this module as parts of the modules reflective dll injection mechanism are stolen from GitHub,” Webroot notes.
The SsExecutor_x86.exe part of the new module is meant to be executed after exploitation, to achieve persistence by modifying registry to add a link to the copied binary to the start-up path of each user account.
Written in Delphi, ScreenLocker_x86.dll represents TrickBot’s first ever attempt at “locking” the victim’s machine. The module exports two functions: a reflective DLL loading function and MyFunction, which appears to be the work in progress.
Should TrickBot indeed gain the locking functionality, it would mean that its developers have decided to switch to a new business model, similar to that employed by ransomware operators.
Locking the computer before stealing the victim’s banking credentials would prevent the credit card or bank theft, which suggests that the cybercriminals might be planning to extort victims to unlock their computers.
The security researchers suggest that, in corporate networks where users are unlikely to be regularly visiting targeted banking URLs, TrickBot would find it difficult to steal banking credentials. Thus, the potential of locking hundreds of machines could prove a more successful money-making model.
“It is notable that this locking functionality is only deployed after lateral movement, meaning that it would be used to primarily target unpatched corporate networks. In a corporate setting (with unpatched machines) it is highly likely that backups would not exist as well. The authors appear to be getting to know their target audience and how to best extract money from them,” Webroot points out.
The RottenSys botnet is already composed of nearly 5 million Android devices
15.3.2018 securityaffairs BotNet
RottenSys – A Chinese crime ring is building a huge botnet that is already composed of nearly 5 million Android device.
Researchers at Check Point discovered attackers infecting the device with a strain of malware dubbed RottenSys that aggressively display ads on victims’ devices.
“The Check Point Mobile Security Team has discovered a new widespread malware family targeting nearly 5 million users for fraudulent ad-revenues. They have named it ‘RottenSys’ for in the sample we encountered it was initially disguised as a System Wi-Fi service.” reads the analysis of Check Point.
The experts started the investigation after finding an unusual self-proclaimed system Wi-Fi service (系统WIFI服务) on a Xiaomi Redmi phone. The researchers discovered the service does not provide any secure Wi-Fi, instead, it asks for many Android permissions.
The RottenSys malware implements two evasion techniques:
The first technique consists of postponing operations for a set time.
The second technique uses a dropper which does not display any malicious activity at first. Once the device is active and the dropper contacts the Command and Control (C&C) server which sends it a list of additional components required for its activity.
The malicious code relies on two open-source projects:
The Small virtualization framework. RottenSys uses Small to create virtualized containers for its components, with this trick the malware could run parallel tasks, overwhelming Android OS limitations.
The MarsDaemon library that keeps apps “undead.” MarsDaemon is used to keep processes alive, even after users close them. Using it the malware is always able to inject ad.
According to the experts, the botnet will have extensive capabilities including silently installing additional apps and UI automation, there is the risk that crooks will use it to carry on more dangerous activities such as ransomware distribution.
“This botnet will have extensive capabilities including silently installing additional apps and UI automation. Interestingly, a part of the controlling mechanism of the botnet is implemented in Lua scripts. Without intervention, the attackers could re-use their existing malware distribution channel and soon grasp control over millions of devices.” continues the analysis.
The RottenSys malware was first spotted in September 2016, the number of victims grew across the time, today the number of infected systems is 4,964,460.
At the time, the malicious code only targets the Chinese users, it is bundled in Chinese apps and it is infecting mostly phones mobile devices, such as Huawei, Xiaomi, OPPO, vivo, LeEco, and Coolpad.

Attackers are financially motivated, according to Check Point botnet operators are currently making around $115,000 every ten days. The experts calculated the revenue from these impressions and clicks according to the conservative estimation of 20 cents for each click and 40 cents for every thousand impressions.
Further info is included in the report published by Check Point.
Gozi Banking Trojan Uses "Dark Cloud" Botnet for Distribution
7.3.2018 securityweek BotNet Virus
The well-known Gozi ISFB banking Trojan recently started using the elusive "Dark Cloud" botnet for distribution, Talos warns.
Gozi has been around for several years and had its source code leaked online on two occasions over the past years, which led to the development of a new Trojan in 2016, GozNym. The malware has continued to remain active and even adopted new techniques in recent campaigns, such as the use of the Dark Cloud infrastructure.
The campaigns Talos has observed over the past few months are relatively low-volume, target specific organizations, and reveal significqant effort into the creation of convincing emails. Not only are the distribution and the command and control (C&C) infrastructure active for short periods of time only, but the actors behind them also move to new domains and IP addresses fast, even for individual emails sent as part of the same campaign.
The spam emails carry Microsoft Word documents as attachments. When opened, the files display a decoy image claiming that the document was created using Office 365 and that the user should "Enable Editing" and then "Enable Content" to view it. If the victim follows through, embedded macros are executed to download and run the malware.
The VBA macro is usually executed when the document is closed, in an attempt to bypass sandbox detection. The macro downloads an HTA file from a remote server, which is executed without alerting the user. The infection process continues with the execution of an obfuscated JavaScript script to run a PowerShell script to download and execute the final payload on the victim's machine.
The vast majority of the malicious documents used in campaigns in the fourth quarter of 2017 are individualized. Although they appear similar, differences exist in embedded macro, code, and even color of the decoy image.
Talos also discovered that the campaigns have been ongoing for a couple of years, and that the image in the documents has been changed from time to time, the same as the VBA code in the malicious macros. The researchers even observed localized documents in some cases, suggesting that “the separate attacks are highly customized and targeted.”
The final payload is usually a banking Trojan based on the Gozi ISFB code base, but other malware families (CryptoShuffler, Sennoma and SpyEye) were also observed.
The malware loader used in these attacks uses anti-virtualization and carries two versions of the same DLL, each targeting a different architecture. Depending on the victim machine, the loader injects either the 32-bit or the 64-bit DLL into the explorer.exe process.
The distribution infrastructure used in these campaigns overlaps with that of Dark Cloud, a botnet initially analyzed in 2016. The botnet, Talos notes, is used in the distribution and administration of various malware families, including Gozi ISFB and Nymaim.
In July 2016, a SentinelOne report on the Furtim-related SFG malware also revealed a connection between the Qbot (Qakbot or Quakbot) malware and Dark Cloud.
The botnet uses fast flux techniques to make the tracking of its backend infrastructure more difficult. “By frequently changing the DNS records associated with the malicious domains, attackers can make use of an extensive network of proxies, continuously changing the address of the IP being used to handle communications to the web servers the attacker controls,” Talos explains.
By looking at the domains and IP addresses associated with the infrastructure, the researchers discovered that it was serving a variety of cybercriminal activities, including carding forums, malware delivery and control, and spam.
Talos also discovered that the attackers aren’t using proxies and hosts in Western Europe, Central Europe, and North America, but mainly those located in Eastern Europe, Asia, and the Middle East.
“Gozi ISFB is a banking Trojan that has been used extensively by attackers who are targeting organizations around the world. It has been around for the past several years, and ongoing campaigns indicate that it will not be going away any time soon. Attackers are continuing to modify their techniques and finding effective new ways to obfuscate their malicious server infrastructure in an attempt to make analysis and tracking more difficult,” Talos concludes.
OMG botnet, the first Mirai variant that sets up proxy servers on vulnerable devices
23.2.2018 securityaffairs BotNet
Researchers at Fortinet have discovered the OMG botnet, the first Mirai variant that sets up proxy servers on the compromised IoT devices.
A new variant of the infamous Mirai botnet appeared in the threat landscape, it was discovered by researchers at Fortinet that referred it as OMG because of strings containing “OOMGA” in the configuration table.
“For this reason, we decided to name this variant OMG.”“The table, originally encrypted, was decrypted using 0xdeadbeef as the cipher key seed, using the same procedure adopted for the original Mirai. The first thing we noticed are the strings /bin/busybox OOMGA and OOMGA: applet not found.” wrote Fortinet.
The name Mirai was given to the Mirai bot because of the strings /bin/busybox MIRAI and MIRAI: applet not found, which are commands to determine if it has successfully brute-forced its way into the targeted IoT device. These strings are similar with other variations such as Satori/Okiru, Masuta, etc.”
The Mirai botnet was first spotted in August 2016 by the security researcher MalwareMustDie, it was specifically designed to compromise vulnerable or poorly protected IoT. Once Mirai malware compromises an IoT device it recruits it into a botnet primarily used for launching DDoS attacks, such as the one that hit Dyn DNS service.
In October 2016, the Mirai source code was leaked and threat actors in the wild started customizing their Mirai botnet.
The OMG botnet includes most of Mirai’s features and modules, including the attack, killer, and scanner modules, but also adds new ones.
According to Fortinet its configuration includes two strings used to add a firewall rule to ensure traffic on two random ports is allowed.
“This variant also adds and removes some configurations that can be found in the original Mirai code. Two notable additions are the two strings that are used to add a firewall rule to allow traffic on two random ports, which we will discuss in the latter part of the article.” continues the analysis.

After initialization, OMG connects to the command and control (C&C) server, the configuration table analyzed in the post contains the CnC server string, ccnew.mm.my, which resolves to 188.138.125.235.
The malware connects to the C&C port 50023, then it sends a defined data message (0x00000000) to the server to identify itself as a new bot.
In response, the server sends a 5-byte long data string, where the first byte is a command on how the newly recruited device should be used as a proxy server, the two options are:
1 for attack
>1 to terminate the connection.
The OMG botnet leverages the open source software 3proxy as its proxy server and during the set up phase the bot adds firewall rules to allow traffic on the two random ports.
“This variant of Mirai uses 3proxy, an open source software, to serve as its proxy server. The set up begins by generating two random ports that will be used for the http_proxy_portand socks_proxy_port. Once the ports are generated, they are reported to the CnC.” continues the analysis.
“For the proxy to work properly, a firewall rule must be added to allow traffic on the generated ports. As mentioned earlier, two strings containing the command for adding and removing a firewall rule to enable this were added to the configuration table .”
Fortinet experts believe the operators behind the OMG botnet sell access to the IoT proxy server, they highlighted that this is the first Mirai variant that sets up proxy servers on vulnerable IoT devices.
“With this development, we believe that more and more Mirai-based bots are going to emerge with new ways of monetization,” concluded Fortinet.
Further details, including IoCs are reported in the blog post published by Fortinet.
Mirai Variant Sets Up Proxy Servers on Compromised Devices
22.2.2018 securityweek BotNet IoT
A newly observed variant of the infamous Mirai botnet is capable of setting up proxy servers on the infected Internet of Things (IoT) devices, Fortinet warns.
Mirai is a distributed denial of service (DDoS)-capable malware family that emerged in late 2016. Targeting IoT devices to add them to a botnet and launch powerful attacks, Mirai has been involved on some massive incidents right from the start.
Referred to as OMG because of strings containing "OOMGA" it its configuration table, the malware keeps most of Mirai’s capabilities, but also adds its own features to the mix.
Unlike Mirai, the OMG variant’s configuration includes two strings used to add a firewall rule to ensure traffic on two random ports is allowed, Fortinet discovered.
However, the new malware variation keeps Mirai’s original attack, killer, and scanner modules, which means that it is capable of performing all of the operations that Mirai could, such as killing processes (telnet, ssh, http, and other processes related to other bots), telnet brute-force login, and DDoS attacks.
After initialization, OMG connects to the command and control (C&C) server on port 50023. Once the connection has been established, the malware sends a defined data message to the server to identify itself as a new bot.
The server responds with a 5-byte long data string, where the first byte is a command on how the newly recruited device should be used: 0 if it should be used as a proxy server, 1 for attack, and >1 to terminate the connection.
OMG, the security researchers discovered, uses open source software 3proxy as its proxy server. During setup, it generates two random ports for the http_proxy_port and socks_proxy_port, reports them to the C&C, and adds a firewall rule to allow traffic on these ports.
After enabling the firewall rule, the malware sets up 3proxy with the predefined configuration embedded in its code. The researchers believe the attackers sell access to the IoT proxy server (because the C&C server wasn’t active during investigation, the researchers only performed static analysis).
“This is the first time we have seen a modified Mirai capable of DDOS attacks as well as setting up proxy servers on vulnerable IoT devices. With this development, we believe that more and more Mirai-based bots are going to emerge with new ways of monetization,” Fortinet concludes.
'DoubleDoor' IoT Botnet Uses Two Backdoor Exploits
16.2.2018 securityweek BotNet
A newly discovered Internet of Things (IoT) botnet is using two exploits to ensure it can not only bypass authentication on targeted devices, but also render additional protections useless, NewSky Security has discovered.
Dubbed DoubleDoor, the botnet allows attackers to takeover devices even if the user has authentication enabled and has added a firewall for additional protection. Specifically, the malware abuses CVE-2015–7755, a Juniper Networks SmartScreen OS exploit, and CVE-2016–10401, a Zyxel modem backdoor exploit (also abused by the Hide ‘N Seek botnet).
What NewSky Security discovered was that the botnet first deploys the infamous Juniper Networks exploit, which essentially allows it to get past firewall authentication. The backdoor was initially discovered in the ScreenOS software running on NetScreen firewalls.
Through this backdoor, the telnet and SSH daemons of Netscreen firewalls become accessible with the hardcoded password <<< %s(un=’%s’) = %u and any username, regardless of whether a valid one or not. In the initial attack cycle of DoubleDoor, the attack was implemented using the username “netscreen,” NewSky's researchers say.
Next, the botnet attempts to deploy the backdoor for ZyXEL PK5001Z devices, which is pretty straight forward as well, using a hardcoded su password as zyad5001. This is a privilege escalation exploit, and the botnet’s operators were also observed performing a “password based attack to get a basic privilege account like admin:CenturyL1nk before going for the superuser,” the researchers say.
The DoubleDoor botnet was also observed performing reconnaissance to ensure the attack was successful and control of the IoT device was achieved.
“DoubleDoor botnet takes care of this, by using a randomized string in every attack. Lack of any standard string will make sure it is not very easy to classify the recon activity as malicious. The strings have one thing in common though, they are always 8 in length,” the security researchers note.
The botnet is currently in a nascent phase, with attacks observed only between Jan. 18 and Jan. 27, 2018. Most of the attacks were observed originating from South Korean IPs. The botnet’s attacks are expected to remain low, mainly because they are only effective if the victim runs a specific unpatched version of Juniper ScreenOS firewall and uses unpatched Zyxel modems.
“Double layer of IoT protection is more common in corporate environments, which don’t rely on built-in IoT authentication and like to protect it with another layer of firewall. Although such corporate devices can be lesser in number, getting control of corporate environment routers can be more valuable for an attacker as it can lead to targeted IoT attacks,” the researchers say.
Necurs botnet is behind seasonal campaigns of Valentine’s Day-themed spam
14.2.2018 securityaffairs BotNet
Necurs botnet made headline again, the experts at IBM X-Force research team observed a spike in seasonal campaigns of Valentine’s Day-themed spam emails.
Necurs botnet made headline again, the experts at IBM X-Force research team observed a spike in the activity of the infamous botnet.
Necurs was not active for a long period at the beginning of 2017 and resumed it activity in April 2017. The Necurs botnet was used in the past months to push many other malware, including Locky, Jaff, GlobeImposter, Dridex , Scarab and the Trickbot.
Scammers are mow using the Necurs botnet to send out an amazing number of messages offering companionship waiting for Valentine’s day.
Crooks are using the spam messages to trick victims into sharing personal photos that are used later by cybercriminals to blackmail the victims.
According to the IBM X-Force team, the campaign started in mid-January, it leverages the overall Necurs botnet that is composed of 6 million bots.
“The current campaign from Necurs reached over 230 million spam messages within a matter of two weeks as the botnet spewed tens of millions of messages in two major bouts. The first surge started on Jan. 16 and ran through Jan. 18; the second started on Jan. 27 and died down on Feb. 3.” reads the analysis published by X-Force researchers.
The expert spotted two current campaigns that sent out a total 230 million spam messages in 14 days-period.

The first campaign reached a peak between Jan. 16 and Jan. 18 and the second one began on Jan. 27 and lasted through Feb. 3. Researchers observed an average 30 million spam messages were sent each day.
“Looking at the messages being sent out in excess of 30 million emails a day, the current campaign delivers short email blurbs from supposed Russian women living in the U.S. While typical spam email is notorious for bad spelling and grammar, these samples are rather well-worded.” continues the analysis.”
The experts determined that the spam messages are being sent from about 950,000 unique IP addresses, Most of IP are hosted in Vietnam and India while the top sender IP address is hosted via a Pakistani-based ISP.
“Together, Vietnam and India hosted 55 percent of the IPs from which the spam originated. It’s worth noting that spammers constantly shuffle the resources they leverage and the originating IPs logged in one campaign are not likely to be used in the next one. This is how fraudsters avoid blacklists and blocking.” added the researchers.
After the takedowns of the Andromeda and Avalanche botnets, Necurs remains the largest spam distributor in the cybercrime ecosystem. Crooks will continue to leverage the Necurs botnet for their spam campaigns, for this reason, the most effective countermeasure is to increase employee awareness on such kind of threats.
ADB.Miner, the Android mining botnet that targets devices with ADB interface open
6.2.2018 securityaffairs BotNet
Security researchers at Qihoo 360’s Netlab have spotted a new Android mining botnet that targets devices with ADB interface open.
Security researchers at Qihoo 360’s Netlab have spotted a new Android mining botnet over the weekend. The malicious code ADB.Miner targets Android devices by scanning for open ADB debugging interface (port 5555) and infects them with a Monero cryptocurrency miner.
The port 5555 is the working port ADB debug interface on Android device that should be shut down normally. The devices infected by ADB.miner are devices where users or vendors have voluntary enabled the debugging port 5555.
“Spread of time : the earliest time of infection can be traced back to near January 31. This current wave of helminthic infections has been detected by our system from around 15:00 on the afternoon of 2018-02-03 and is still on the rise.” reads the analysis published by Netlab.
“Infected port : 5555, is the working port adb debug interface on Android device, the port should be shut down normally, but unknown part of the cause led to the wrong port opened.”
Starting from February 3, the expert noticed a rapid growth of the volume of scan traffic on port 5555 associated with the ADB.Miner:

Once the ADB.Miner has infected a device, the compromised system start scanning the Internet for other devices to infect.
According to the experts, ADB.miner borrowed the scanning code implemented by the Mirai botnet, this is the first time that the Mirai code is used by an Android threat.
The researchers did not reveal the way the malware infects the Android devices, it is likely it exploits a flaw in the ADB interface.
The number of infected devices is rapidly growing, according to different caliber statistics, there are 2.75 ~ 5.5k, and this figure is rapidly growing.
The two sources reported by Netlab are:
Statistics from scanmon : 2.75k, mainly from China (40%) and South Korea (31%).
Statistics from our botnet tracking system: 5.5k
At the time of writing the number of ADB.miner scans reached 75,900 unique IP addresses.

Most IP addresses scanning the port 5555 are located in China (~40%) and South Korea (~30%).
The operators of the botnet are using the following Monero wallet address:
44XT4KvmobTQfeWa6PCQF5RDosr2MLWm43AsaE3o5iNRXXTfDbYk2VPHTVedTQHZyfXNzMn8YYF2466d3FSDT7gJS8gdHAr
That still has not received the first payment for the mine.
Alleged Kelihos Botnet Mastermind Extradited to U.S.
5.2.2018 securityweek BotNet
A 37-year-old Russian national accused of being the mastermind behind the notorious Kelihos botnet has been extradited from Spain to the United States.
The U.S. Justice Department announced that Peter Yuryevich Levashov, also known as Petr Levashov, Pyotr Levashov, Peter Severa, Petr Severa and Sergey Astakhov, of St. Petersburg, Russia, was arraigned on Friday in Connecticut. He has pleaded not guilty to the charges brought against him.
Levashov was arrested in April 2017 by Spanish authorities based on a U.S. warrant and has been in custody ever since. The suspect had been on holiday at the time of his arrest, which coincided with a takedown operation targeting the Kelihos botnet. He was indicted roughly two weeks later by a federal grand jury in Connecticut.
Russia had attempted to block his extradition to the United States. Levashov claimed that he had previously worked for President Vladimir Putin's United Russia party, and feared that he would be killed if extradited to the U.S. Initial media reports said his arrest may be linked to the U.S. election hacks, but officials denied there was any connection.
The suspect has been charged on eight counts, including causing intentional damage to a protected computer, conspiracy, accessing protected computers in furtherance of fraud, wire fraud, threatening to damage a protected computer, fraud in connection with email, and aggravated identity theft. He faces more than 50 years in prison for these charges.
According to U.S. authorities, Levashov controlled and operated the Kelihos botnet, using it to send spam, harvest personal information, and deliver other malware. At the time of his arrest, investigators said the botnet at times had ensnared as many as 100,000 computers, including many in the United States.
While some security firms track Kelihos as Waldac, many have classified it as a successor of Waledac, a botnet disrupted by authorities in 2010.
Another Russian national who will be extradited to the United States is Alexander Vinnik, owner of the cryptocurrency exchange BTC-e. Greece’s Supreme Court recently approved the extradition of Vinnik, who is said to have laundered $4 billion using bitcoins.
Yevgeni Nikulin, who U.S. authorities say hacked into the systems of LinkedIn, Formspring and Dropbox, will also soon be extradited after a high court in the Czech Republic upheld an earlier ruling authorizing his extradition.
JenX botnet leverages Grand Theft Auto videogame community to infect devices
3.2.2018 securityaffairs BotNet
Researchers at security firm Radware have spotted a new IoT botnet, dubbed JenX, the leverages the Grand Theft Auto videogame community to infect devices.
Researchers at security firm Radware have spotted a new IoT botnet, dubbed JenX, that exploits vulnerabilities triggered by the Satori botnet and is leveraging the Grand Theft Auto videogame community to infect devices.
The activity of the Satori botnet has been observed in 2017 by researchers from Check Point security, it uses A Zero-Day vulnerability (CVE-2017-17215) in the Huawei home router HG532.
JenX exploits the CVE-2014-8361 (Realtek SDK Miniigd UPnP SOAP command execution) and CVE-2017-17215 (Huawei Router HG532 arbitrary command execution). that affect Huawei and Realtek routers.
“A new botnet recently started recruiting IoT devices. The botnet uses hosted servers to find and infect new victims leveraging one of two known vulnerabilities that have become popular in IoT botnets recently:
CVE-2014-8361 “Realtek SDK Miniigd UPnP SOAP Command Execution” vulnerability and related exploit.
CVE-2017–17215 “Huawei Router HG532 – Arbitrary Command Execution” vulnerability and related exploit.” states Radware in a blog post.
“Both exploit vectors are known from the Satori botnet and based on code that was part of a recent public Pastebin post by the “Janit0r,” author of “BrickerBot.”
JenX also implemented some techniques used by the recently discovered PureMasuta botnet.
The command-and-control server is hosted at the site San Calvicie, which offers multiplayer mod support for Grand Theft Auto: San Andreas, and also DDoS-for-hire service.
JenX is a DDoS botnet, the DDoS option offered by San Calvicie is called “Corriente Divina.”
The users of the website can rent a GTA San Andreas multiplayer modded server for $16 and a Teamspeak server goes for $9. Adding $20 it is possible to power massive DDoS attacks that can peak 290 and 300 Gbps.
“The Corriente Divina (‘divine stream’) option is described as ‘God’s wrath will be employed against the IP that you provide us,” wrote Radware’s Cyber Security expert Pascal Geenens. “It provides a DDoS service with a guaranteed bandwidth of 90-100 Gbps and attack vectors including Valve Source Engine Query and 32 bytes floods, TS3 scripts and a ‘Down OVH’ option which most probably refers to attacks targeting the hosting service of OVH, a cloud hosting provider that also was a victim of the original Mirai attacks back in September 2016. OVH is well known for hosting multi-player gaming servers such as Minecraft, which was the target of the Mirai attacks at the time.”

Differently from Satori and PureMasuta botnets, JenX has a centralized infrastructure, it uses a central server to perform the scanning of new hosts.
“The drawback of the central approach is a less than linear growth with the number of deployed servers. Much slower compared to the exponential growth rate of and less aggressive than distributed scanning botnets,” continues the analysis.
The presence of a central server that coordinates the activity makes it easy for law enforcement and security firms to take down the botnet. Of course, threat actors can deploy the control server to the Dark Web making hard take over from law enforcement.
Even if the JenX is able to power massive DDoS attacks, for now, is doesn’t represent a serious threat because it aims to disrupt services from competing for GTA SA multiplayer servers.
“The botnet is supposed to serve a specific purpose and be used to disrupt services from competing GTA SA multiplayer servers. I do not believe that this will be the botnet that will take down the internet,” Geenens concluded.
“But it does contain some interesting new evolutions and it adds to a list of IoT botnets that is growing longer and faster every month! That said, there is nothing that stops one from using the cheap $20 per target service to perform 290Gbps attacks on business targets and even government related targets. I cannot believe the San Calvicie group would oppose to it.”
New Botnet Is Recruiting IoT Devices
2.2.2018 securityweek BotNet
A new botnet is recruiting Internet of Things (IoT) devices by exploiting two vulnerabilities already popular among IoT botnets, Radware has discovered.
Dubbed JenX, the threat is abusing the CVE-2014-8361 (Realtek SDK Miniigd UPnP SOAP Command Execution) and CVE-2017–17215 (Huawei Router HG532 – Arbitrary Command Execution) vulnerabilities. Both of these security issues were previously abused by the Mirai variant Satori.
The new threat also uses techniques associated with the recently detailed PureMasuta variant of Mirai, which recently had its source code published on an invite-only dark forum.
The botnet’s command and control (C&C) server also provides gaming mod servers and distributed denial of service (DDoS) services, Radware's researchers discovered.
The DDoS feature includes attack vectors such as Valve Source Engine Query and 32bytes floods, TS3 scripts, and a Down OVH option (likely a reference the Mirai attack on a cloud hosting provider OVH in September 2016). The miscreants guarantee attack volumes of 290-300Gbps, supposedly leveraging the power of the new botnet.
JenX uses servers to perform the scanning and exploit operations, unlike previously observed IoT botnets such as Mirai, Hajime, Persirai, Reaper, Satori, and Masuta, which leverage infected systems for scanning and exploiting (which also fuels an exponential growth of the botnet).
Because it does not include scanning and exploit payloads, JenX’ code is unsophisticated and lighter on the delivery, Radware says. With centralized scan and exploit functionality, the operators also have increased flexibility to expand and improve the functionality without impacting the size of the bot.
Because there are fewer nodes scanning and exploiting, the botnet is less noisy and can better avoid being detected by honeypots. This also makes it more difficult to estimate the botnet’s size, without accessing the C&C server, the security researchers say. On top of that, the botnet only impacts the victim’s network connection when instructed to perform an attack.
“The drawback of the central approach is a less than linear growth with the number of deployed servers. Much slower compared to the exponential growth rate of and less aggressive than distributed scanning botnets,” Radware notes.
The malware is protected with anti-debugging detection and its binary forks three processes obfuscated in the process table much like Mirai. All processes listen to a port bound to localhost while one opens a TCP socket to the C&C at 80.82.70.202 on port 127. The bot uses XOR obfuscation with the exact same key used in PureMasuta.
When executed, the malware connects to the C&C server located by the hostname ‘skids.sancalvicie.com’ using the TCP session (the domain is registered to Calvos S.L.). The server supposedly provides a command line interface.
The code has indicators of a Valve Source Engine Query attack payload, likely because of the GTA San Andreas multiplayer servers on the domain. The attack vector was included in the original Mirai code that went public in October 2016, and Radware believes the botnet is being built by the San Calvicie hacker group and served through their Clearnet website.
“Unless you frequently play GTA San Andreas, you will probably not be directly impacted. The botnet is supposed to serve a specific purpose and be used to disrupt services from competing GTA SA multiplayer servers. I do not believe that this will be the botnet that will take down the internet! But it does contain some interesting new evolutions and it adds to a list of IoT botnets that is growing longer and faster every month,” Radware’s Pascal Geenens note.
Two providers informed on the issue have already taken down the exploit servers hosted in their datacenters, but some servers remain active and the botnet is still operational, Geenens says. However, should the attackers decide to move their exploit servers to the darknet, the botnet’s takedown would be much more difficult, as was the case with BrickerBot.
“JenX, in particular, can be easily concealed and hardened against takedowns. As they opted for a central scan and exploit paradigm, the hackers can easily move their exploit operations to bulletproof hosting providers who provide anonymous VPS and dedicated servers from offshore zones. These providers do not care about abuse,” Geenens says.
DDG, the second largest mining botnet targets Redis and OrientDB servers
2.2.2018 securityaffairs BotNet
Researchers at Qihoo 360’s Netlab analyzed a new campaign powered by the DDG botnet, the second largest mining botnet of ever, that targets Redis and OrientDB servers.
A new Monero-mining botnet dubbed DDG was spotted in the wild, the malware targets Redis and OrientDB servers.
According to the researchers at Qihoo 360’s Netlab, the DDG botnet was first detected in 2016 and is continuously updated throughout 2017.
“Starting 2017-10-25, we noticed there was a large scale ongoing scan targeting the OrientDB databases. Further analysis found that this is a long-running botnet whose main goal is to mine Monero CryptoCurrency. We name it DDG.Mining.Botnet after its core function module name DDG.” reads the analysis published by Netlab.
The miner has already infected nearly 4,400 servers and has mined over $925,000 worth of Monero since March 2017, DDG is among the largest mining botnets.
Yesterday I wrote about the greatest mining botnet called Smominru that has infected over 526,000 Windows machines, its operators had already mined approximately 8,900 Monero ($2,346,271 at the current rate).
The malware exploits the remote code execution vulnerability CVE-2017-11467 to compromise OrientDB databases and targets Redis servers via a brute-force attack.
Crooks are focusing their efforts on attacks against servers that usually have significant computing capabilities.
The attack chain described by the researchers from Qihoo 360’s Netlab is composed of the following steps:
Initial Scanning: The attacker (ss2480.2) exploits the known RCE vulnerability of the OrientDB database and drops the attack payload
Stage 1: Attackers modify local Crontab scheduled tasks, download and execute i.sh (hxxp: //218.248.40.228:8443/i.sh) on the primary server and keep it synchronized every 5 minutes
Stage 2: DDG traverses the built-in file hub_iplist.txt, check the connectivity of every single entry and try to download the corresponding Miner program wnTKYg from the one can be successfully connected (wnTKYg.noaes if the native CPU does not support AES-NI)
Mining Stage: The Miner program begins to use the computing resources of the compromised host to begin mining for the attacker’s wallet.
The following image shows the DDG Mining Botnet attack process:

The researchers conducted sinkholing of the botnet traffic and observed 4,391 IP addresses of compromised servers from all countries. Most of the infections is in China (73%), followed by the United States (11%), the botnet is mainly composed of compromised Redis databases (88%).
Cybercriminals are using three wallet addresses, the botnet mined 3,395 Monero ($925,000), but researchers also discovered another wallet containing 2,428 Monero ($660,000).
“The total income is Monroe 3,395 or 5,760. These tokens are worth USD 925,383 or 1,569,963 today. Note: There is an issue for the second wallet, where “Total Paid” is not consistent with the summary of all tractions’ amount. We cannot confirm which number is more accurate, so we show both numbers here.” continues the analysis.
Further information including the IoCs are included in the technical report published by Qihoo 360’s Netlab.
Crypto-Mining Botnet Ensnares 500,000 Windows Machines
2.2.2018 securityweek BotNet
Focused on mining Monero crypto-currency, a new botnet has managed to ensnare over half a million machines to date, Proofpoint reports.
Dubbed Smominru, the botnet managed to infect over 526,000 Windows hosts to date, most of which are believed to be servers. After conducting a sinkholing operation, the security researchers discovered that the infected machines are distributed worldwide, with the highest numbers in Russia, India, and Taiwan.
The Monero miner, which is also known as Ismo, has been observed since the end of May 2017 spreading via EternalBlue, the National Security Agency-linked exploit that targets a vulnerability (CVE-2017-0144) in Windows’ Server Message Block (SMB) on port 445. The exploit was previously used in other global attacks, including WannaCry and NotPetya.
The miner itself has been detailed numerous times before, and was associated with various attacks, including those perpetrated by an established Chinese crime group (Hex Men).
What makes it stand out in the crowd is the use of Windows Management Infrastructure for infection, a method recently noticed in the WannaMine crypto-mining worm too (which also uses EternalBlue to spread).
The hash power associated with the Monero payment address for Smominru reveals that the botnet was likely twice the size of Adylkuzz, the first crypto-mining botnet to abuse EternalBlue. According to Proofpoint, Smominru’s operators already mined around 8,900 Monero (between $2.8 million and $3.6 million), at a rate of around 24 Monero per day.
In a recent report diving into the huge financial gains crypto-miner operators register, Talos revealed that an adversary controlling 1,000 systems would make around $90,000 per year. The security firm also says it “has observed botnets consisting of millions of infected systems,” which “could be leveraged to generate more than $100 million per year theoretically.”
While investigating Smominru, Proofpoint discovered that at least 25 of the hosts were attempting to infect new machines via EternalBlue (the hosts are placed behind the network autonomous system AS63199).
Last week, NetLab 360 security researchers published a post on what they call the MyKings botnet, which appears to be none other than Smominru, based on the used Monero address. NetLab revealed that the mining operation was performed by a sub-botnet, while another was focused on scanning and spreading, capable of mobilizing over 2400 host IP addresses.
According to Proofpoint, some of the distribution attacks are likely performed using MySQL, while others supposedly leverage the NSA-linked exploit EsteemAudit (CVE-2017-0176).
Both NetLab and Proofpoint findings fall in line with GuardiCore’s report on the Hex Men, a group using three malware families, namely Hex, Hanako and Taylor, each targeting different SQL servers with its own goals, scale and target services.
The botnet’s command and control (C&C) infrastructure is hosted behind SharkTech, Proofpoint’s security researchers have discovered. The company was informed on the issue.
MineXMR was also contacted regarding the Monero address associated with Smominru, and the mining pool banned the address. This prompted the botnet operators to register new domains and mining to a new address on the same pool. This switch apparently resulted in the operators losing control over one third of the bots.
“Because most of the nodes in this botnet appear to be Windows servers, the performance impact on potentially critical business infrastructure may be high, as can the cost of increased energy usage by servers running much closer to capacity. The operators of this botnet are persistent, use all available exploits to expand their botnet, and have found multiple ways to recover after sinkhole operations,” Proofpoint notes.
The use of standalone coin miners and coin mining modules in existing malware has proliferated rapidly over the past year, fueled by the surge in value crypto-coins such as Bitcoin and Monero have registered. With Bitcoin resource-intensive to mine outside of dedicated mining farms, Monero has registered massive interest from cybercriminals.
Smominru’s operators have likely registered significant profits from their operation and the resilience of the botnet and its infrastructure suggest that the activities will continue, the researchers say. The potential impacts on infected nodes will continue as well, and other botnets featuring similar purpose and methods might emerge as well, the researchers say.
“We repeatedly see threat actors ‘follow the money’ - over the last several months, the money has been in cryptocurrency and actors are turning their attention to a variety of illicit means to obtain both Bitcoins and alternatives,” Kevin Epstein, VP Threat Operations, Proofpoint, said in an emailed comment.
“This Monero mining botnet is extremely large, made up mostly of Microsoft Windows servers spread around the globe. Taking down the botnet is very difficult given its distributed nature and the persistence of its operators. For businesses, preventing infection through robust patching,” Epstein concluded.